Abstract
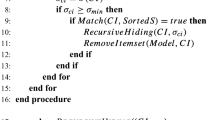
Privacy-preserving data mining (PPDM) has become an important issue to hide the confidential or private data before it is shared or published in recent years. In this paper, a novel algorithm is proposed to hide sensitive itemsets through item deletion. Three side effects of hiding failures, missing itemsets, and artificial itemsets are considered to evaluate whether the transactions or the itemsets are required to be deleted for hiding sensitive itemsets. Experiments are then conducted to show the performance of the proposed algorithm in execution time, number of deleted transactions, and number of side effects.
Access this chapter
Tax calculation will be finalised at checkout
Purchases are for personal use only
Preview
Unable to display preview. Download preview PDF.
Similar content being viewed by others
References
Agrawal, R., Imielinski, T., Swami, A.: Database mining: A performance perspective. IEEE Transactions on Knowledge and Data Engineering 5, 914–925 (1993)
Agrawal, R., Srikant, R.: Fast algorithms for mining association rules in large databases. In: The International Conference on Very Large Data Bases, pp. 487–499 (1994)
Atallah, M., Bertino, E., Elmagarmid, A., Ibrahim, M., Verykios, V.: Disclosure limitation of sensitive rules. In: The Workshop on Knowledge and Data Engineering Exchange, pp. 45–52 (1999)
Agrawal, R., Srikant, R.: Privacy-Preserving Data Mining. In: ACM SIGMOD International Conference on Management of Data, pp. 439–450 (2000)
Amiri, A.: Dare to share: Protecting sensitive knowledge with data sanitization. Decision Support Systems 43, 181–191 (2007)
Berkhin, P.: A survey of clustering data mining techniques. Grouping Multidimensional Data, 25–71 (2006)
Dasseni, E., Verykios, V.S., Elmagarmid, A.K., Bertino, E.: Hiding association rules by using confidence and support. In: Moskowitz, I.S. (ed.) IH 2001. LNCS, vol. 2137, p. 369. Springer, Heidelberg (2001)
Gkoulalas-Divanis, A., Verykios, V.S.: An integer programming approach for frequent itemset hiding. In: ACM International Conference on Information and Knowledge Management, pp. 748–757 (2006)
Duraiswamy, K., Manjula, D., Maheswari, N.: Advanced approach in sensitive rule hiding. CCSE Modern Applied Science 3, 98–107 (2009)
Gkoulalas-Divanis, A., Verykios, V.S.: Exact knowledge hiding through database extension. IEEE Transactions on Knowledge and Data Engineering 21, 699–713 (2009)
Han, J., Fu, Y.: Mining multiple-level association rules in large databases. IEEE Transactions on Knowledge and Data Engineering 11, 798–805 (1999)
Han, J., Pei, J., Yin, Y., Mao, R.: Mining frequent patterns without candidate generation: a frequent-pattern tree approach. Data Mining and Knowledge Discovery 8, 53–87 (2004)
Hong, T.P., Lin, C.W., Wu, Y.L.: Incrementally fast updated frequent pattern trees. Expert Systems with Applications 34, 2424–2435 (2008)
Hong, T.P., Lin, C.W., Yang, K.T., Wang, S.L.: A lattice-based data sanitization approach. IEEE International Conference on Systems, Man, and Cybernetics, 2325–2329 (2011)
Hong, T.P., Lin, C.W., Yang, K.T., Wang, S.L.: Using TF-IDF to hide sensitive itemsets. Applied Intelligence 38, 502–510 (2013)
Kotsiantis, S.B.: Supervised machine learning: A review of classification techniques. In: The Conference on Emerging Artificial Intelligence Applications in Computer Engineering: Real Word AI Systems with Applications in eHealth, HCI, Information Retrieval and Pervasive Technologies, pp. 3–24 (2007)
Leary, D.E.O.: Knowledge discovery as a threat to database security. Knowledge Discovery in Databases, pp. 507–516 (1991)
Lin, C.W., Hong, T.P., Lu, W.H.: An effective tree structure for mining high utility itemsets. Expert Systems with Applications 38, 7419–7424 (2011)
Lin, C.W., Hong, T.P., Chang, C.C., Wang, S.L.: A greedy-based approach for hiding sensitive itemsets by transaction insertion. Journal of Information Hiding and Multimedia Signal Processing 4, 201–227 (2013)
Lin, C.W., Hong, T.P.: A survey of fuzzy web mining. Wiley Interdisciplinary Reviews: Data Mining and Knowledge Discovery 3, 190–199 (2013)
Modi, C.N., Rao, U.P., Patel, D.R.: Maintaining privacy and data quality in privacy preserving association rule mining. In: International Conference on Computing Communication and Networking Technologies, pp. 1–6 (2010)
Wu, Y.H., Chiang, C.M., Chen, A.L.P.: Hiding sensitive association rules with limited side effects. IEEE Transactions on Knowledge and Data Engineering 19, 29–42 (2007)
Zheng, Z., Kohavi, R., Mason, L.: Real world performance of association rule algorithms. In: ACM SIGKDD International Conference on Knowledge Discovery and Data Mining, pp. 401–406 (2001)
Author information
Authors and Affiliations
Corresponding author
Editor information
Editors and Affiliations
Rights and permissions
Copyright information
© 2014 Springer International Publishing Switzerland
About this paper
Cite this paper
Lin, CW., Hong, TP., Hsu, HC. (2014). Hiding Sensitive Itemsets with Minimal Side Effects in Privacy Preserving Data Mining. In: Pan, JS., Snasel, V., Corchado, E., Abraham, A., Wang, SL. (eds) Intelligent Data analysis and its Applications, Volume I. Advances in Intelligent Systems and Computing, vol 297. Springer, Cham. https://doi.org/10.1007/978-3-319-07776-5_10
Download citation
DOI: https://doi.org/10.1007/978-3-319-07776-5_10
Publisher Name: Springer, Cham
Print ISBN: 978-3-319-07775-8
Online ISBN: 978-3-319-07776-5
eBook Packages: EngineeringEngineering (R0)