Abstract
Nowadays, embedded systems can be found everywhere in daily life. In the development of embedded systems, data security is one of the critical factors. Encryption is an effective way to protect data from threats. Among encryption algorithms, chaos-based methods have strong cryptographic properties since chaotic systems are sensitive to initial conditions and parameters. However, most of these algorithms cannot be applied in practice because their encryption speed is not fast enough. In this paper, a fast image encryption algorithm is proposed. Compared with traditional chaos-based image encryption algorithms, the proposed method utilizes mixed-sequence and decorrelation operation to enhance the randomness of chaotic sequence. Moreover, it used minimum length of the sequence which is determined by experiments. Therefore, the proposed scheme spends much less computation time, which is an important advantage for being applied in practice. Testing results have shown that this algorithm has good performance in resisting known attacks, such as known-plaintext attacks, chosen ciphertext attacks, statistical attacks, differential attacks, and various brute-force attacks.









Similar content being viewed by others
References
Alvarez G, Li S (2006) Some basic cryptographic requirements for chaos-based cryp- tosystems. Int J Bifurcation Chaos 16:2129–2151
Chen G, Mao YB, Chui CK (2004) A symmetric image encryption scheme based on 3D chaotic cat maps. Chaos, Solitons Fractals 21(3):749–761
chuan Y, Xijun WANG, GAO Yongke LI, Qingmin TIAN (2015) A new scheme for UAV TT&C and information transmission system. Int Conf Adv Mech Eng Indust Inform (AMEII) 2015(2015):1018–1022
Fridrich J (1998) Symmetric ciphers based on two-dimensional chaotic maps. Int J Bifurcation Chaos 8(6):1259–1284
Galatolo S (2003) Complexity, initial condition sensitivity, dimension and weak chaos in dynamical systems. Nonlinearity 16(4):1219–1238
Reinhard Gerndt, Sören Michalik, Stefan Krupop (2011) Embedded vision system for robotics and industrial automation, 2011 9th IEEE International Conference on Industrial Informatics. 895–899
Guo W, Zhao J, Ye R (2014) A Chaos-based pseudorandom permutation and bilateral diffusion scheme for image encryption, international journal of image. Graph Sign Proc 6(11):50–61
Hamza R, Titouna F (2016) A novel sensitive image encryption algorithm based on the Zaslavsky chaotic map. Inform Sec J A Glob Perspect 25(4–6):162–179
Li Y, Wang YL (2015) Customizing dynamic libraries of Qt based on the embedded Linux. Appl Mech Mater 740:782–785
Liu Y, Nie L, Han L, Zhang L, David S (2015) Rosenblum, Action2Activity: recognizing complex activities from sensor data. Proc Twenty-Fourth Int Joint Conf Artificial Intel (IJCAI) 2015:1617–1623
Liu Y, Zhang L, Nie L, Yan Y, Rosenblum DS (2016) Fortune teller: predicting your career path. Proc Thirtieth AAAI Conf Artific Intel (AAAI-16):201–207
Liu Y, Nie L, Liu L, Rosenblum DS (2016) From action to activity: sensor-based activity recognition. Neurocomputing 181:108–115
Liu J, Ma Y, Li S, Lian J, Xinguo Zhang A (2018) New simple chaotic system and its application in medical image encryption. Multimed Tools Appl 4:1–22
Liu J, Sprott JC, Wang S, Ma Y (2018) Simplest chaotic system with a hyperbolic sine and its applications in DCSK scheme. IET Commun
Malinowski A, Yu H (2011) Comparison of embedded system Design for Industrial Applications. IEEE Trans Indust Inform 7(2):244–254
Murillo-Escobar MA, Cruz-Hernández C, Abundiz-Pérez F, López-Gutiérrez RM (2016) Implementation of an improved chaotic encryption algorithm for real-time embedded systems by using a 32-bit microcontroller. Microprocess Microsyst 45:297–309
Mykhatsky OYu , KuzmenkoNS , Savchenko OV (2013) Experimental UAV flight data structuring transmission and visualization by narrowband telemetry transmission, 2013 IEEE 2nd International Conference Actual Problems of Unmanned Air Vehicles Developments Proceedings (APUAVD). 118–121
Pareek NK, Vinod Patidar KKS (2006) Image encryption using chaotic logistic map. Image Vis Comput 24:926–934
Song R, Lang WC, Pan SW (2009) Development of embedded system GUI based on Qt/embedded. Appl Mech Mater 109:586–590
Talarposhti KM, Jamei MK (2016) A secure image encryption method based on dynamic harmony search (DHS) combined with chaotic map. Opt Lasers Eng 81:21–34
Wong KW, Kwok SH, Law WS (2008) A fast image encryption scheme based on chaotic standard map. Phys Lett A 372(15):2645–2652
Xu Z, Wu L, Gerke M, Wang R, Yang H (2016) Skeletal camera network embedded structure-from-motion for 3D scene reconstruction from UAV images. ISPRS J Photogramm Remote Sens 121:113–127
Xu H, Tong X, Meng X (2016) An efficient chaos pseudo-random number generator applied to video encryption. Optik - Int J Light Electron Optics 127(20):9305–9319
Yao Y, Zhang W, Yu N (2017) Inter-frame distortion drift analysis for reversible data hiding in encrypted H.264/AVC video bitstreams. Signal Process 132:19–28
YAOBIN MAO, GUANRONG CHEN, SHIGUO LIAN (2004) A novel fast image encryption scheme based on the 3D chaotic baker map. Int J Bifurcat Chaos 14(10):3613–3624
Yin SJ, Xia DC, Ma J (2014) Application of machine vision in ARM based on OpenCV and Qt. Adv Mater Res 1049-1050(1):1938–1941
Zhang G, Liu Q (2011) A novel image encryption method based on total shuffling scheme. Opt Commun 284(12):2775–2780
Zhang YQ, Wang XY (2014) A symmetric image encryption algorithm based on mixed linear–nonlinear coupled map lattice. Inf Sci 273(8):329–351
Acknowledgements
Thanks for the useful suggestions provided by Yide Ma and Jizhao Liu. This study was supported by the Fundamental Research Funds for the Central Universities (No.lzujbky-2016-238). National Natural Science Foundation of China (No.61175012). 2017 s batch of innovation base and innovative talents (Small and medium enterprises innovation fund 17CX2JA018).
Author information
Authors and Affiliations
Corresponding author
Additional information
Publisher’s note
Springer Nature remains neutral with regard to jurisdictional claims in published maps and institutional affiliations.
Appendices
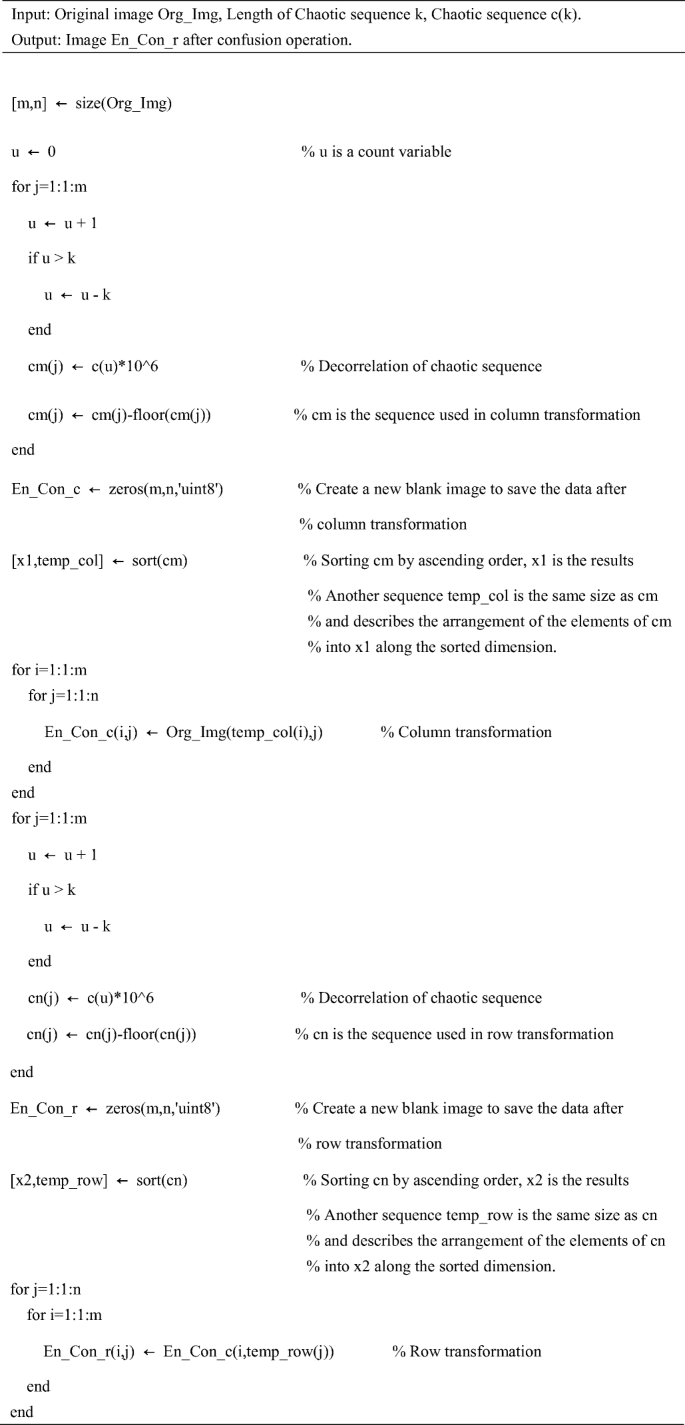
Appendix A Process of confusion
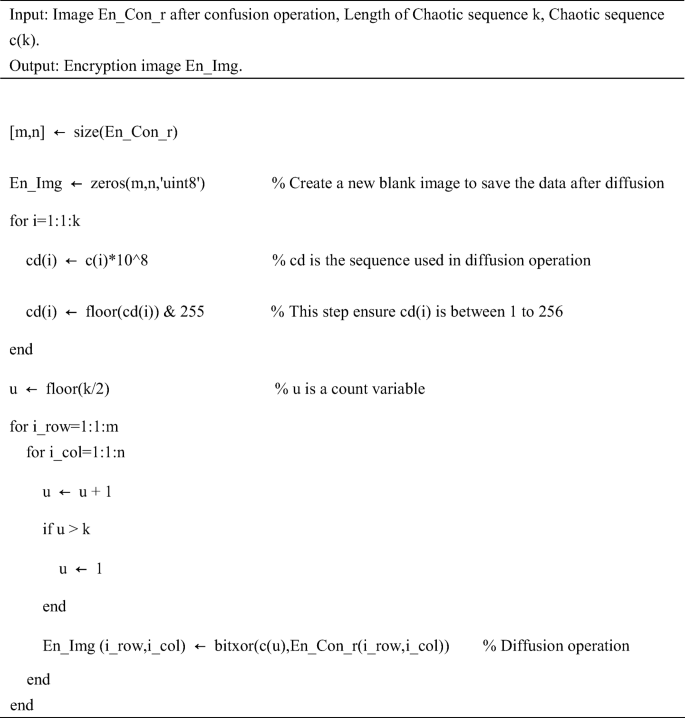
Appendix B process of diffusion
Rights and permissions
About this article
Cite this article
Lin, Z., Liu, J., Lian, J. et al. A novel fast image encryption algorithm for embedded systems. Multimed Tools Appl 78, 20511–20531 (2019). https://doi.org/10.1007/s11042-018-6824-5
Received:
Revised:
Accepted:
Published:
Issue Date:
DOI: https://doi.org/10.1007/s11042-018-6824-5


