From f7a16164657311eb2689ebff0d680510a4d91bee Mon Sep 17 00:00:00 2001
From: morsa4406 <104304449+morsa4406@users.noreply.github.com>
Date: Tue, 27 Jun 2023 16:30:07 +0300
Subject: [PATCH 001/257] CM-24634 - Add dependency paths column on SCA table
output (#127)
---
cycode/cli/printers/sca_table_printer.py | 20 ++++++++++++++++++--
1 file changed, 18 insertions(+), 2 deletions(-)
diff --git a/cycode/cli/printers/sca_table_printer.py b/cycode/cli/printers/sca_table_printer.py
index 34130607..ca441ca6 100644
--- a/cycode/cli/printers/sca_table_printer.py
+++ b/cycode/cli/printers/sca_table_printer.py
@@ -19,7 +19,8 @@
'Ecosystem',
'Dependency Name',
'Direct Dependency',
- 'Development Dependency'
+ 'Development Dependency',
+ 'Dependency Paths',
]
@@ -107,13 +108,28 @@ def set_table_width(headers: List[str], text_table: Texttable) -> None:
def _print_summary_issues(detections: List, title: str) -> None:
click.echo(f'⛔ Found {len(detections)} issues of type: {click.style(title, bold=True)}')
+ @staticmethod
+ def _shortcut_dependency_paths(dependency_paths: str) -> str:
+ dependencies = dependency_paths.split(' -> ')
+
+ if len(dependencies) < 2:
+ return dependencies[0]
+
+ return f'{dependencies[0]} -> ... -> {dependencies[-1]}'
+
def _get_common_detection_fields(self, detection: Detection) -> List[str]:
+ dependency_paths = 'N/A'
+ dependency_paths_raw = detection.detection_details.get('dependency_paths')
+ if dependency_paths_raw:
+ dependency_paths = self._shortcut_dependency_paths(dependency_paths_raw)
+
row = [
detection.detection_details.get('file_name'),
detection.detection_details.get('ecosystem'),
detection.detection_details.get('package_name'),
detection.detection_details.get('is_direct_dependency_str'),
- detection.detection_details.get('is_dev_dependency_str')
+ detection.detection_details.get('is_dev_dependency_str'),
+ dependency_paths,
]
if self._is_git_repository():
From a4b13fb007b7c23ada309feea62a712ba42c3770 Mon Sep 17 00:00:00 2001
From: anna-aleksandrowicz
<135120640+anna-aleksandrowicz@users.noreply.github.com>
Date: Wed, 28 Jun 2023 00:06:34 +0300
Subject: [PATCH 002/257] Improve README (#125)
---
README.md | 34 ++++++++++++++++++----------------
1 file changed, 18 insertions(+), 16 deletions(-)
diff --git a/README.md b/README.md
index 370001e7..f2fbe808 100644
--- a/README.md
+++ b/README.md
@@ -48,14 +48,14 @@ This guide will guide you through both installation and usage.
- The Cycode CLI application requires Python version 3.7 or later.
- Use the [`cycode auth` command](#use-auth-command) to authenticate to Cycode with the CLI
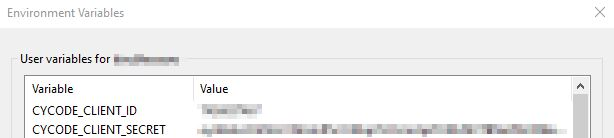
- - Alternatively, a Cycode Client ID and Client Secret Key can be acquired using the steps from the [Service Account Token](https://docs.cycode.com/reference/creating-a-service-account-access-token) and [Personal Access Token](https://docs.cycode.com/reference/creating-a-personal-access-token-1) pages for details on obtaining these values.
+ - Alternatively, you can obtain a Cycode Client ID and Client Secret Key by following the steps detailed in the [Service Account Token](https://docs.cycode.com/reference/creating-a-service-account-access-token) and [Personal Access Token](https://docs.cycode.com/reference/creating-a-personal-access-token-1) pages, which contain details on obtaining these values.
# Installation
-The following installation steps are applicable on both Windows and UNIX / Linux operating systems.
+The following installation steps are applicable to both Windows and UNIX / Linux operating systems.
> :memo: **Note**
-> The following steps assume the use of `python3` and `pip3` for Python-related commands, but some systems may instead use the `python` and `pip` commands, depending on your Python environment’s configuration.
+> The following steps assume the use of `python3` and `pip3` for Python-related commands; however, some systems may instead use the `python` and `pip` commands, depending on your Python environment’s configuration.
## Install Cycode CLI
@@ -75,7 +75,7 @@ To install the Cycode CLI application on your local machine, perform the followi
- [cycode configure](#use-configure-command)
- Add them to your [environment variables](#add-to-environment-variables)
-### Use auth Command
+### Useing the Auth Command
> :memo: **Note**
> This is the **recommended** method for setting up your local machine to authenticate with Cycode CLI.
@@ -88,20 +88,20 @@ To install the Cycode CLI application on your local machine, perform the followi
-3. Enter you login credentials on this page and log in.
+3. Enter your login credentials on this page and log in.
-4. You will eventually be taken to this page, where you will be asked to choose the business group you want to authorize Cycode with (if applicable):
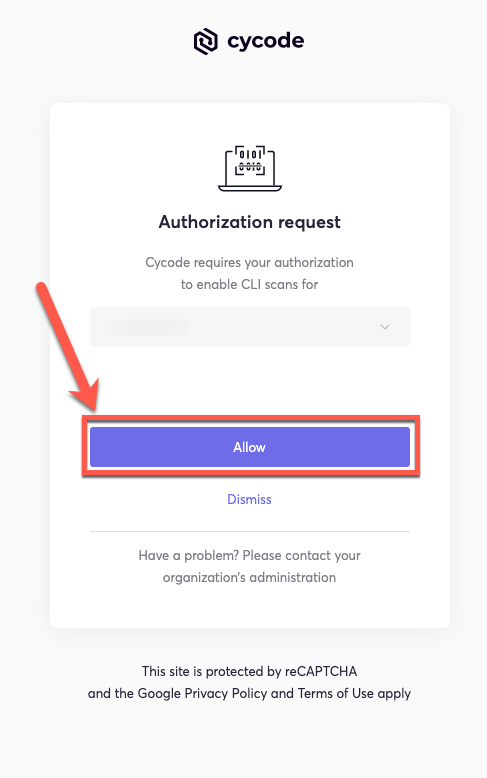
+4. You will eventually be taken to the page below, where you'll be asked to choose the business group you want to authorize Cycode with (if applicable):
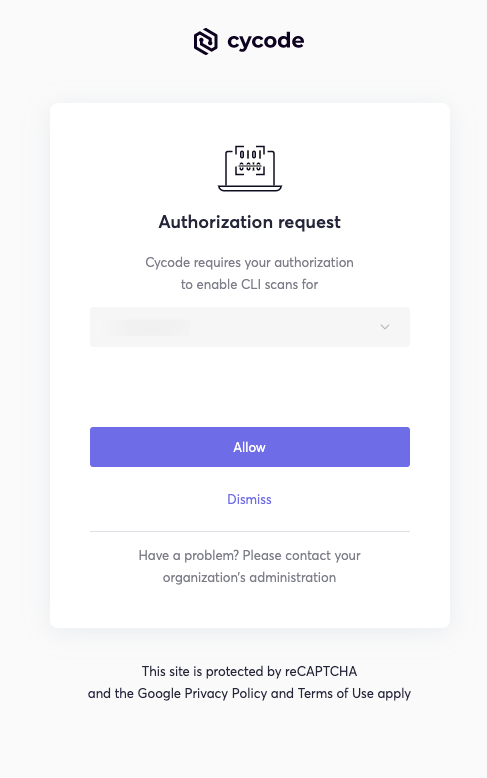
> :memo: **Note**
> This will be the default method for authenticating with the Cycode CLI.
-5. Click the **Allow** button to authorize the Cycode CLI on the chosen business group.
+5. Click the **Allow** button to authorize the Cycode CLI on the selected business group.
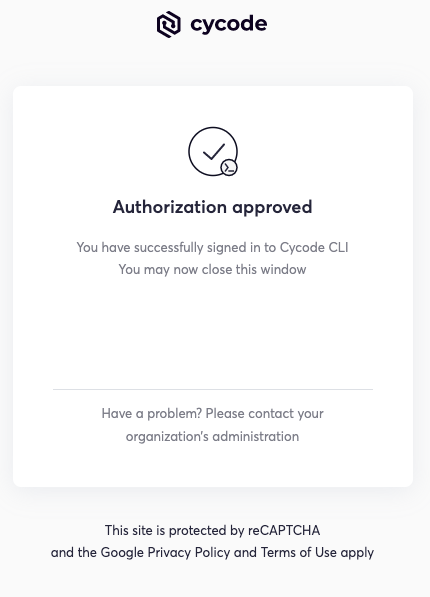
-6. Once done, you will see the following screen, if it was successfully selected:
+6. Once completed, you'll see the following screen, if it was selected successfully:
@@ -111,10 +111,10 @@ To install the Cycode CLI application on your local machine, perform the followi
Successfully logged into cycode
```
-### Use configure Command
+### Using the Configure Command
> :memo: **Note**
-> If you already setup your Cycode client ID and client secret through the Linux or Windows environment variables, those credentials will take precedent over this method
+> If you already set up your Cycode client ID and client secret through the Linux or Windows environment variables, those credentials will take precedent over this method.
1. Type the following command into your terminal/command line window:
@@ -139,13 +139,13 @@ To install the Cycode CLI application on your local machine, perform the followi
cycode client secret []: c1e24929-xxxx-xxxx-xxxx-8b08c1839a2e
```
-4. If the values were entered successfully, you will see the following message:
+4. If the values were entered successfully, you'll see the following message:
```bash
Successfully configured CLI credentials!
```
-If you go into the `.cycode` folder under you user folder, you will find these credentials were created and placed in the `credentials.yaml` file in that folder.
+If you go into the `.cycode` folder under your user folder, you'll find these credentials were created and placed in the `credentials.yaml` file in that folder.
### Add to Environment Variables
@@ -174,9 +174,11 @@ export CYCODE_CLIENT_SECRET={your Cycode Secret Key}
+5. Insert the cycode.exe into the path to complete the installation.
+
## Install Pre-Commit Hook
-Cycode’s pre-commit hook can be set up within your local repository so that the Cycode CLI application will automatically identify any issues with your code before you commit it to your codebase.
+Cycode’s pre-commit hook can be set up within your local repository so that the Cycode CLI application will identify any issues with your code automatically before you commit it to your codebase.
Perform the following steps to install the pre-commit hook:
@@ -204,10 +206,10 @@ repos:
`pre-commit install`
> :memo: **Note**
-> Successful hook installation will result in the message:
+> A successful hook installation will result in the message:
`Pre-commit installed at .git/hooks/pre-commit`
-# Cycode Command
+# Cycode CLI Commands
The following are the options and commands available with the Cycode CLI application:
@@ -251,7 +253,7 @@ The Cycode CLI application offers several types of scans so that you can choose
## Repository Scan
-A repository scan examines an entire local repository for any exposed secrets or insecure misconfigurations. This more holistic scan type looks at everything: the current state of your repository and its commit history. It will look not only for currently exposed secrets within the repository but previously deleted secrets as well.
+A repository scan examines an entire local repository for any exposed secrets or insecure misconfigurations. This more holistic scan type looks at everything: the current state of your repository and its commit history. It will look not only for secrets that are currently exposed within the repository but previously deleted secrets as well.
To execute a full repository scan, execute the following:
From c7f57819eb0196cbfc86ec5ee8d6e923cafdf5d2 Mon Sep 17 00:00:00 2001
From: morsa4406 <104304449+morsa4406@users.noreply.github.com>
Date: Wed, 28 Jun 2023 14:23:08 +0300
Subject: [PATCH 003/257] CM-24707 - Fix dependency paths to add continuation
dependencies sign for the list greater than 2 (#131)
* CM-24707 [SCA-CLI] fixing dependency paths to add continuation dependencies for list greater than 2
* CM-24707 - Fix dependency paths to add continuation dependencies sign for the list greater than 2
* CM-24707 - Fix dependency paths to add continuation dependencies sign for the list greater than 2
* CM-24707 - Fix dependency paths to add continuation dependencies sign for the list greater than 2
* CM-24707 - Fix dependency paths to add continuation dependencies sign for the list greater than 2
---
cycode/cli/consts.py | 5 +++++
cycode/cli/printers/sca_table_printer.py | 14 +++-----------
cycode/cli/utils/string_utils.py | 17 +++++++++++++++++
tests/utils/test_string_utils.py | 7 +++++++
4 files changed, 32 insertions(+), 11 deletions(-)
create mode 100644 tests/utils/test_string_utils.py
diff --git a/cycode/cli/consts.py b/cycode/cli/consts.py
index 3b0aaafe..f37bbdef 100644
--- a/cycode/cli/consts.py
+++ b/cycode/cli/consts.py
@@ -126,3 +126,8 @@
LICENSE_COMPLIANCE_POLICY_ID = '8f681450-49e1-4f7e-85b7-0c8fe84b3a35'
PACKAGE_VULNERABILITY_POLICY_ID = '9369d10a-9ac0-48d3-9921-5de7fe9a37a7'
+
+# Shortcut dependency paths by remove all middle depndencies between direct dependency and influence/vulnerable dependency.
+# Example: A -> B -> C
+# Result: A -> ... -> C
+SCA_SHORTCUT_DEPENDENCY_PATHS = 2
diff --git a/cycode/cli/printers/sca_table_printer.py b/cycode/cli/printers/sca_table_printer.py
index ca441ca6..7feac6b1 100644
--- a/cycode/cli/printers/sca_table_printer.py
+++ b/cycode/cli/printers/sca_table_printer.py
@@ -7,6 +7,7 @@
from cycode.cli.consts import LICENSE_COMPLIANCE_POLICY_ID, PACKAGE_VULNERABILITY_POLICY_ID
from cycode.cli.models import DocumentDetections, Detection
from cycode.cli.printers.base_table_printer import BaseTablePrinter
+from cycode.cli.utils.string_utils import shortcut_dependency_paths
SEVERITY_COLUMN = 'Severity'
LICENSE_COLUMN = 'License'
@@ -108,20 +109,11 @@ def set_table_width(headers: List[str], text_table: Texttable) -> None:
def _print_summary_issues(detections: List, title: str) -> None:
click.echo(f'⛔ Found {len(detections)} issues of type: {click.style(title, bold=True)}')
- @staticmethod
- def _shortcut_dependency_paths(dependency_paths: str) -> str:
- dependencies = dependency_paths.split(' -> ')
-
- if len(dependencies) < 2:
- return dependencies[0]
-
- return f'{dependencies[0]} -> ... -> {dependencies[-1]}'
-
def _get_common_detection_fields(self, detection: Detection) -> List[str]:
dependency_paths = 'N/A'
dependency_paths_raw = detection.detection_details.get('dependency_paths')
if dependency_paths_raw:
- dependency_paths = self._shortcut_dependency_paths(dependency_paths_raw)
+ dependency_paths = shortcut_dependency_paths(dependency_paths_raw)
row = [
detection.detection_details.get('file_name'),
@@ -129,7 +121,7 @@ def _get_common_detection_fields(self, detection: Detection) -> List[str]:
detection.detection_details.get('package_name'),
detection.detection_details.get('is_direct_dependency_str'),
detection.detection_details.get('is_dev_dependency_str'),
- dependency_paths,
+ dependency_paths
]
if self._is_git_repository():
diff --git a/cycode/cli/utils/string_utils.py b/cycode/cli/utils/string_utils.py
index 0e7d0c23..f301f9ac 100644
--- a/cycode/cli/utils/string_utils.py
+++ b/cycode/cli/utils/string_utils.py
@@ -6,6 +6,8 @@
from sys import getsizeof
from binaryornot.check import is_binary_string
+from cycode.cli.consts import SCA_SHORTCUT_DEPENDENCY_PATHS
+
def obfuscate_text(text: str) -> str:
match_len = len(text)
@@ -47,3 +49,18 @@ def generate_random_string(string_len: int):
def get_position_in_line(text: str, position: int) -> int:
return position - text.rfind('\n', 0, position) - 1
+
+
+def shortcut_dependency_paths(dependency_paths_list: str) -> str:
+ separate_dependency_paths_list = dependency_paths_list.split(',')
+ result = ''
+ for dependency_paths in separate_dependency_paths_list:
+ dependency_paths = dependency_paths.strip().rstrip()
+ dependencies = dependency_paths.split(' -> ')
+ if len(dependencies) <= SCA_SHORTCUT_DEPENDENCY_PATHS:
+ result += dependency_paths
+ else:
+ result += f'{dependencies[0]} -> ... -> {dependencies[-1]}'
+ result += '\n\n'
+
+ return result.rstrip().rstrip(',')
diff --git a/tests/utils/test_string_utils.py b/tests/utils/test_string_utils.py
new file mode 100644
index 00000000..7b20fd4c
--- /dev/null
+++ b/tests/utils/test_string_utils.py
@@ -0,0 +1,7 @@
+from cycode.cli.utils.string_utils import shortcut_dependency_paths
+
+
+def test_shortcut_dependency_paths_list_single_dependencies():
+ dependency_paths = "A, A -> B, A -> B -> C"
+ expected_result = "A\n\nA -> B\n\nA -> ... -> C"
+ assert shortcut_dependency_paths(dependency_paths) == expected_result
From 657c7fc2497dccbdfb08981508d9aa450b5a143b Mon Sep 17 00:00:00 2001
From: Ilya Siamionau
Date: Wed, 5 Jul 2023 11:54:50 +0200
Subject: [PATCH 004/257] CM-22718 - Support scan in batches with progress bar
(#129)
---
cycode/cli/auth/auth_command.py | 4 +-
cycode/cli/code_scanner.py | 947 +++++++++++-------
cycode/cli/consts.py | 12 +-
cycode/cli/main.py | 47 +-
cycode/cli/models.py | 11 +-
cycode/cli/printers/base_printer.py | 9 +-
cycode/cli/printers/base_table_printer.py | 22 +-
cycode/cli/printers/console_printer.py | 7 +-
cycode/cli/printers/json_printer.py | 20 +-
cycode/cli/printers/sca_table_printer.py | 28 +-
cycode/cli/printers/table_printer.py | 26 +-
cycode/cli/printers/text_printer.py | 45 +-
cycode/cli/utils/enum_utils.py | 7 +
cycode/cli/utils/path_utils.py | 8 +-
cycode/cli/utils/progress_bar.py | 240 +++++
cycode/cli/utils/scan_batch.py | 73 ++
cycode/cli/utils/scan_utils.py | 10 +-
cycode/cyclient/cycode_client_base.py | 10 +-
cycode/cyclient/cycode_token_based_client.py | 7 +-
cycode/cyclient/scan_client.py | 15 +-
.../scan_config/scan_config_creator.py | 8 +-
poetry.lock | 109 +-
pyproject.toml | 1 -
tests/cli/test_main.py | 6 +-
tests/cyclient/test_scan_client.py | 9 +-
25 files changed, 1131 insertions(+), 550 deletions(-)
create mode 100644 cycode/cli/utils/enum_utils.py
create mode 100644 cycode/cli/utils/progress_bar.py
create mode 100644 cycode/cli/utils/scan_batch.py
diff --git a/cycode/cli/auth/auth_command.py b/cycode/cli/auth/auth_command.py
index f7605965..37b6c3f6 100644
--- a/cycode/cli/auth/auth_command.py
+++ b/cycode/cli/auth/auth_command.py
@@ -48,14 +48,14 @@ def authorization_check(context: click.Context):
return printer.print_result(passed_auth_check_res)
except (NetworkError, HttpUnauthorizedError):
if context.obj['verbose']:
- click.secho(f'Error: {traceback.format_exc()}', fg='red', nl=False)
+ click.secho(f'Error: {traceback.format_exc()}', fg='red')
return printer.print_result(failed_auth_check_res)
def _handle_exception(context: click.Context, e: Exception):
if context.obj['verbose']:
- click.secho(f'Error: {traceback.format_exc()}', fg='red', nl=False)
+ click.secho(f'Error: {traceback.format_exc()}', fg='red')
errors: CliErrors = {
AuthProcessError: CliError(
diff --git a/cycode/cli/code_scanner.py b/cycode/cli/code_scanner.py
index 0c0c996d..f2219716 100644
--- a/cycode/cli/code_scanner.py
+++ b/cycode/cli/code_scanner.py
@@ -7,27 +7,36 @@
import traceback
from platform import platform
from uuid import uuid4, UUID
+from typing import TYPE_CHECKING, Callable, List, Optional, Dict, Tuple
+
from git import Repo, NULL_TREE, InvalidGitRepositoryError
from sys import getsizeof
-from halo import Halo
-
from cycode.cli.printers import ConsolePrinter
-from cycode.cli.models import Document, DocumentDetections, Severity, CliError, CliErrors
+from cycode.cli.models import Document, DocumentDetections, Severity, CliError, CliErrors, LocalScanResult
from cycode.cli.ci_integrations import get_commit_range
-from cycode.cli.consts import *
+from cycode.cli import consts
from cycode.cli.config import configuration_manager
+from cycode.cli.utils.progress_bar import ProgressBarSection
+from cycode.cli.utils.scan_utils import set_issue_detected
from cycode.cli.utils.path_utils import is_sub_path, is_binary_file, get_file_size, get_relevant_files_in_path, \
get_path_by_os, get_file_content
+from cycode.cli.utils.scan_batch import run_parallel_batched_scan
from cycode.cli.utils.string_utils import get_content_size, is_binary_content
from cycode.cli.utils.task_timer import TimeoutAfter
from cycode.cli.utils import scan_utils
from cycode.cli.user_settings.config_file_manager import ConfigFileManager
from cycode.cli.zip_file import InMemoryZip
-from cycode.cli.exceptions.custom_exceptions import *
+from cycode.cli.exceptions import custom_exceptions
from cycode.cli.helpers import sca_code_scanner
from cycode.cyclient import logger
-from cycode.cyclient.models import *
+from cycode.cli.utils.progress_bar import logger as progress_bar_logger
+from cycode.cyclient.models import ZippedFileScanResult, Detection, DetectionsPerFile, DetectionSchema
+
+if TYPE_CHECKING:
+ from cycode.cyclient.scan_client import ScanClient
+ from cycode.cyclient.models import ScanDetailsResponse
+ from cycode.cli.utils.progress_bar import BaseProgressBar
start_scan_time = time.time()
@@ -40,26 +49,40 @@
type=str,
required=False)
@click.pass_context
-def scan_repository(context: click.Context, path, branch):
+def scan_repository(context: click.Context, path: str, branch: str):
""" Scan git repository including its history """
try:
logger.debug('Starting repository scan process, %s', {'path': path, 'branch': branch})
- context.obj["path"] = path
- monitor = context.obj.get("monitor")
- scan_type = context.obj["scan_type"]
- if monitor and scan_type != SCA_SCAN_TYPE:
- raise click.ClickException(f"Monitor flag is currently supported for SCA scan type only")
-
- documents_to_scan = [
- Document(obj.path if monitor else get_path_by_os(os.path.join(path, obj.path)),
- obj.data_stream.read().decode('utf-8', errors='replace'))
- for obj
- in get_git_repository_tree_file_entries(path, branch)]
+
+ scan_type = context.obj['scan_type']
+ monitor = context.obj.get('monitor')
+ if monitor and scan_type != consts.SCA_SCAN_TYPE:
+ raise click.ClickException(f'Monitor flag is currently supported for SCA scan type only')
+
+ progress_bar = context.obj['progress_bar']
+
+ file_entries = list(get_git_repository_tree_file_entries(path, branch))
+ progress_bar.set_section_length(ProgressBarSection.PREPARE_LOCAL_FILES, len(file_entries))
+
+ documents_to_scan = []
+ for file in file_entries:
+ progress_bar.update(ProgressBarSection.PREPARE_LOCAL_FILES)
+
+ if monitor:
+ path = file.path
+ else:
+ path = get_path_by_os(os.path.join(path, file.path))
+
+ documents_to_scan.append(Document(path, file.data_stream.read().decode('UTF-8', errors='replace')))
+
documents_to_scan = exclude_irrelevant_documents_to_scan(context, documents_to_scan)
- perform_pre_scan_documents_actions(context, scan_type, documents_to_scan, False)
+
+ perform_pre_scan_documents_actions(context, scan_type, documents_to_scan, is_git_diff=False)
+
logger.debug('Found all relevant files for scanning %s', {'path': path, 'branch': branch})
- return scan_documents(context, documents_to_scan, is_git_diff=False,
- scan_parameters=get_scan_parameters(context))
+ return scan_documents(
+ context, documents_to_scan, is_git_diff=False, scan_parameters=get_scan_parameters(context, path)
+ )
except Exception as e:
_handle_exception(context, e)
@@ -86,27 +109,32 @@ def scan_repository_commit_history(context: click.Context, path: str, commit_ran
def scan_commit_range(context: click.Context, path: str, commit_range: str, max_commits_count: Optional[int] = None):
- scan_type = context.obj["scan_type"]
- if scan_type not in COMMIT_RANGE_SCAN_SUPPORTED_SCAN_TYPES:
- raise click.ClickException(f"Commit range scanning for {str.upper(scan_type)} is not supported")
+ scan_type = context.obj['scan_type']
+ progress_bar = context.obj['progress_bar']
+
+ if scan_type not in consts.COMMIT_RANGE_SCAN_SUPPORTED_SCAN_TYPES:
+ raise click.ClickException(f'Commit range scanning for {str.upper(scan_type)} is not supported')
- if scan_type == SCA_SCAN_TYPE:
+ if scan_type == consts.SCA_SCAN_TYPE:
return scan_sca_commit_range(context, path, commit_range)
documents_to_scan = []
commit_ids_to_scan = []
repo = Repo(path)
- total_commits_count = repo.git.rev_list('--count', commit_range)
+ total_commits_count = int(repo.git.rev_list('--count', commit_range))
+ logger.debug(f'Calculating diffs for {total_commits_count} commits in the commit range {commit_range}')
+
+ progress_bar.set_section_length(ProgressBarSection.PREPARE_LOCAL_FILES, total_commits_count)
+
scanned_commits_count = 0
- logger.info(f'Calculating diffs for {total_commits_count} commits in the commit range {commit_range}')
for commit in repo.iter_commits(rev=commit_range):
if _does_reach_to_max_commits_to_scan_limit(commit_ids_to_scan, max_commits_count):
- logger.info(f'Reached to max commits to scan count. Going to scan only {max_commits_count} last commits')
+ logger.debug(f'Reached to max commits to scan count. Going to scan only {max_commits_count} last commits')
+ progress_bar.update(ProgressBarSection.PREPARE_LOCAL_FILES, total_commits_count - scanned_commits_count)
break
- if _should_update_progress(scanned_commits_count):
- logger.info(f'Calculated diffs for {scanned_commits_count} out of {total_commits_count} commits')
+ progress_bar.update(ProgressBarSection.PREPARE_LOCAL_FILES)
commit_id = commit.hexsha
commit_ids_to_scan.append(commit_id)
@@ -114,18 +142,29 @@ def scan_commit_range(context: click.Context, path: str, commit_range: str, max_
diff = commit.diff(parent, create_patch=True, R=True)
commit_documents_to_scan = []
for blob in diff:
- doc = Document(get_path_by_os(os.path.join(path, get_diff_file_path(blob))),
- blob.diff.decode('utf-8', errors='replace'), True, unique_id=commit_id)
- commit_documents_to_scan.append(doc)
-
- logger.debug('Found all relevant files in commit %s',
- {'path': path, 'commit_range': commit_range, 'commit_id': commit_id})
- commit_documents_to_scan = exclude_irrelevant_documents_to_scan(context, commit_documents_to_scan)
- documents_to_scan.extend(commit_documents_to_scan)
+ blob_path = get_path_by_os(os.path.join(path, get_diff_file_path(blob)))
+ commit_documents_to_scan.append(Document(
+ path=blob_path,
+ content=blob.diff.decode('UTF-8', errors='replace'),
+ is_git_diff_format=True,
+ unique_id=commit_id
+ ))
+
+ logger.debug(
+ 'Found all relevant files in commit %s',
+ {
+ 'path': path,
+ 'commit_range': commit_range,
+ 'commit_id': commit_id
+ }
+ )
+
+ documents_to_scan.extend(exclude_irrelevant_documents_to_scan(context, commit_documents_to_scan))
scanned_commits_count += 1
logger.debug('List of commit ids to scan, %s', {'commit_ids': commit_ids_to_scan})
- logger.info('Starting to scan commit range (It may take a few minutes)')
+ logger.debug('Starting to scan commit range (It may take a few minutes)')
+
return scan_documents(context, documents_to_scan, is_git_diff=True, is_commit_range=True)
@@ -143,25 +182,32 @@ def scan_ci(context: click.Context):
def scan_path(context: click.Context, path):
""" Scan the files in the path supplied in the command """
logger.debug('Starting path scan process, %s', {'path': path})
- context.obj["path"] = path
files_to_scan = get_relevant_files_in_path(path=path, exclude_patterns=["**/.git/**", "**/.cycode/**"])
files_to_scan = exclude_irrelevant_files(context, files_to_scan)
logger.debug('Found all relevant files for scanning %s', {'path': path, 'file_to_scan_count': len(files_to_scan)})
- return scan_disk_files(context, files_to_scan)
+ return scan_disk_files(context, path, files_to_scan)
@click.command()
-@click.argument("ignored_args", nargs=-1, type=click.UNPROCESSED)
+@click.argument('ignored_args', nargs=-1, type=click.UNPROCESSED)
@click.pass_context
def pre_commit_scan(context: click.Context, ignored_args: List[str]):
""" Use this command to scan the content that was not committed yet """
scan_type = context.obj['scan_type']
- if scan_type == SCA_SCAN_TYPE:
+ progress_bar = context.obj['progress_bar']
+
+ if scan_type == consts.SCA_SCAN_TYPE:
return scan_sca_pre_commit(context)
- diff_files = Repo(os.getcwd()).index.diff("HEAD", create_patch=True, R=True)
- documents_to_scan = [Document(get_path_by_os(get_diff_file_path(file)), get_diff_file_content(file))
- for file in diff_files]
+ diff_files = Repo(os.getcwd()).index.diff('HEAD', create_patch=True, R=True)
+
+ progress_bar.set_section_length(ProgressBarSection.PREPARE_LOCAL_FILES, len(diff_files))
+
+ documents_to_scan = []
+ for file in diff_files:
+ progress_bar.update(ProgressBarSection.PREPARE_LOCAL_FILES)
+ documents_to_scan.append(Document(get_path_by_os(get_diff_file_path(file)), get_diff_file_content(file)))
+
documents_to_scan = exclude_irrelevant_documents_to_scan(context, documents_to_scan)
return scan_documents(context, documents_to_scan, is_git_diff=True)
@@ -170,11 +216,11 @@ def pre_commit_scan(context: click.Context, ignored_args: List[str]):
@click.argument("ignored_args", nargs=-1, type=click.UNPROCESSED)
@click.pass_context
def pre_receive_scan(context: click.Context, ignored_args: List[str]):
- """ Use this command to scan commits on server side before pushing them to the repository """
+ """ Use this command to scan commits on the server side before pushing them to the repository """
try:
scan_type = context.obj['scan_type']
- if scan_type != SECRET_SCAN_TYPE:
- raise click.ClickException(f"Commit range scanning for {str.upper(scan_type)} is not supported")
+ if scan_type != consts.SECRET_SCAN_TYPE:
+ raise click.ClickException(f'Commit range scanning for {scan_type.upper()} is not supported')
if should_skip_pre_receive_scan():
logger.info(
@@ -189,14 +235,16 @@ def pre_receive_scan(context: click.Context, ignored_args: List[str]):
command_scan_type = context.info_name
timeout = configuration_manager.get_pre_receive_command_timeout(command_scan_type)
with TimeoutAfter(timeout):
- if scan_type not in COMMIT_RANGE_SCAN_SUPPORTED_SCAN_TYPES:
- raise click.ClickException(f"Commit range scanning for {str.upper(scan_type)} is not supported")
+ if scan_type not in consts.COMMIT_RANGE_SCAN_SUPPORTED_SCAN_TYPES:
+ raise click.ClickException(f'Commit range scanning for {scan_type.upper()} is not supported')
branch_update_details = parse_pre_receive_input()
commit_range = calculate_pre_receive_commit_range(branch_update_details)
if not commit_range:
- logger.info('No new commits found for pushed branch, %s',
- {'branch_update_details': branch_update_details})
+ logger.info(
+ 'No new commits found for pushed branch, %s',
+ {'branch_update_details': branch_update_details}
+ )
return
max_commits_to_scan = configuration_manager.get_pre_receive_max_commits_to_scan_count(command_scan_type)
@@ -208,7 +256,7 @@ def pre_receive_scan(context: click.Context, ignored_args: List[str]):
def scan_sca_pre_commit(context: click.Context):
scan_parameters = get_default_scan_parameters(context)
- git_head_documents, pre_committed_documents = get_pre_commit_modified_documents()
+ git_head_documents, pre_committed_documents = get_pre_commit_modified_documents(context.obj['progress_bar'])
git_head_documents = exclude_irrelevant_documents_to_scan(context, git_head_documents)
pre_committed_documents = exclude_irrelevant_documents_to_scan(context, pre_committed_documents)
sca_code_scanner.perform_pre_hook_range_scan_actions(git_head_documents, pre_committed_documents)
@@ -218,11 +266,13 @@ def scan_sca_pre_commit(context: click.Context):
def scan_sca_commit_range(context: click.Context, path: str, commit_range: str):
- context.obj["path"] = path
- scan_parameters = get_scan_parameters(context)
+ progress_bar = context.obj['progress_bar']
+
+ scan_parameters = get_scan_parameters(context, path)
from_commit_rev, to_commit_rev = parse_commit_range(commit_range, path)
- from_commit_documents, to_commit_documents = \
- get_commit_range_modified_documents(path, from_commit_rev, to_commit_rev)
+ from_commit_documents, to_commit_documents = get_commit_range_modified_documents(
+ progress_bar, path, from_commit_rev, to_commit_rev
+ )
from_commit_documents = exclude_irrelevant_documents_to_scan(context, from_commit_documents)
to_commit_documents = exclude_irrelevant_documents_to_scan(context, to_commit_documents)
sca_code_scanner.perform_pre_commit_range_scan_actions(path, from_commit_documents, from_commit_rev,
@@ -232,249 +282,401 @@ def scan_sca_commit_range(context: click.Context, path: str, commit_range: str):
scan_parameters=scan_parameters)
-def scan_disk_files(context: click.Context, paths: List[str]):
- scan_parameters = get_scan_parameters(context)
+def scan_disk_files(context: click.Context, path: str, files_to_scan: List[str]):
+ scan_parameters = get_scan_parameters(context, path)
scan_type = context.obj['scan_type']
+ progress_bar = context.obj['progress_bar']
+
is_git_diff = False
+
+ progress_bar.set_section_length(ProgressBarSection.PREPARE_LOCAL_FILES, len(files_to_scan))
+
documents: List[Document] = []
- for path in paths:
- with open(path, "r", encoding="utf-8") as f:
- content = f.read()
- documents.append(Document(path, content, is_git_diff))
+ for file in files_to_scan:
+ progress_bar.update(ProgressBarSection.PREPARE_LOCAL_FILES)
+
+ with open(file, 'r', encoding='UTF-8') as f:
+ try:
+ documents.append(Document(file, f.read(), is_git_diff))
+ except UnicodeDecodeError:
+ continue
perform_pre_scan_documents_actions(context, scan_type, documents, is_git_diff)
return scan_documents(context, documents, is_git_diff=is_git_diff, scan_parameters=scan_parameters)
-def scan_documents(context: click.Context, documents_to_scan: List[Document], is_git_diff: bool = False,
- is_commit_range: bool = False, scan_parameters: dict = None):
- cycode_client = context.obj["client"]
- scan_type = context.obj["scan_type"]
- severity_threshold = context.obj["severity_threshold"]
- command_scan_type = context.info_name
- error_message = None
- all_detections_count = 0
- output_detections_count = 0
- scan_id = _get_scan_id(context)
- zipped_documents = InMemoryZip()
+def set_issue_detected_by_scan_results(context: click.Context, scan_results: List[LocalScanResult]) -> None:
+ set_issue_detected(context, any(scan_result.issue_detected for scan_result in scan_results))
- try:
- logger.debug("Preparing local files")
- zipped_documents = zip_documents_to_scan(scan_type, zipped_documents, documents_to_scan)
- scan_result = perform_scan(context, cycode_client, zipped_documents, scan_type, scan_id, is_git_diff,
- is_commit_range,
- scan_parameters)
+def _get_scan_documents_thread_func(
+ context: click.Context, is_git_diff: bool, is_commit_range: bool, scan_parameters: dict
+) -> Callable[[List[Document]], Tuple[str, CliError, LocalScanResult]]:
+ cycode_client = context.obj['client']
+ scan_type = context.obj['scan_type']
+ severity_threshold = context.obj['severity_threshold']
+ command_scan_type = context.info_name
- all_detections_count, output_detections_count = \
- handle_scan_result(context, scan_result, command_scan_type, scan_type, severity_threshold,
- documents_to_scan)
- scan_completed = True
- except Exception as e:
- _handle_exception(context, e)
- error_message = str(e)
+ def _scan_batch_thread_func(batch: List[Document]) -> Tuple[str, CliError, LocalScanResult]:
+ local_scan_result = error = error_message = None
+ detections_count = relevant_detections_count = zip_file_size = 0
+
+ scan_id = str(_get_scan_id())
scan_completed = False
- zip_file_size = getsizeof(zipped_documents.in_memory_zip)
- logger.debug('Finished scan process, %s',
- {'all_violations_count': all_detections_count, 'relevant_violations_count': output_detections_count,
- 'scan_id': str(scan_id), 'zip_file_size': zip_file_size})
- _report_scan_status(context, scan_type, str(scan_id), scan_completed, output_detections_count,
- all_detections_count, len(documents_to_scan), zip_file_size, command_scan_type, error_message)
+ try:
+ logger.debug('Preparing local files, %s', {'batch_size': len(batch)})
+ zipped_documents = zip_documents_to_scan(scan_type, InMemoryZip(), batch)
+ zip_file_size = getsizeof(zipped_documents.in_memory_zip)
+
+ scan_result = perform_scan(
+ cycode_client, zipped_documents, scan_type, scan_id, is_git_diff, is_commit_range, scan_parameters
+ )
+ local_scan_result = create_local_scan_result(
+ scan_result, batch, command_scan_type, scan_type, severity_threshold
+ )
+
+ scan_completed = True
+ except Exception as e:
+ error = _handle_exception(context, e, return_exception=True)
+ error_message = str(e)
-def scan_commit_range_documents(context: click.Context, from_documents_to_scan: List[Document],
- to_documents_to_scan: List[Document], scan_parameters: dict = None,
- timeout: int = None):
- cycode_client = context.obj["client"]
- scan_type = context.obj["scan_type"]
- severity_threshold = context.obj["severity_threshold"]
+ if local_scan_result:
+ detections_count = local_scan_result.detections_count
+ relevant_detections_count = local_scan_result.relevant_detections_count
+ scan_id = local_scan_result.scan_id
+
+ logger.debug(
+ 'Finished scan process, %s',
+ {
+ 'all_violations_count': detections_count,
+ 'relevant_violations_count': relevant_detections_count,
+ 'scan_id': scan_id,
+ 'zip_file_size': zip_file_size
+ }
+ )
+ _report_scan_status(
+ cycode_client, scan_type, scan_id, scan_completed, relevant_detections_count,
+ detections_count, len(batch), zip_file_size, command_scan_type, error_message
+ )
+
+ return scan_id, error, local_scan_result
+
+ return _scan_batch_thread_func
+
+
+def scan_documents(
+ context: click.Context,
+ documents_to_scan: List[Document],
+ is_git_diff: bool = False,
+ is_commit_range: bool = False,
+ scan_parameters: Optional[dict] = None,
+) -> None:
+ progress_bar = context.obj['progress_bar']
+
+ scan_batch_thread_func = _get_scan_documents_thread_func(context, is_git_diff, is_commit_range, scan_parameters)
+ errors, local_scan_results = run_parallel_batched_scan(
+ scan_batch_thread_func, documents_to_scan, progress_bar=progress_bar
+ )
+
+ progress_bar.set_section_length(ProgressBarSection.GENERATE_REPORT, 1)
+ progress_bar.update(ProgressBarSection.GENERATE_REPORT)
+ progress_bar.stop()
+
+ set_issue_detected_by_scan_results(context, local_scan_results)
+ print_results(context, local_scan_results)
+
+ if not errors:
+ return
+
+ if context.obj['output'] == 'json':
+ # TODO(MarshalX): we can't just print JSON formatted errors here
+ # because we should return only one root json structure per scan
+ # could be added later to "print_results" function if we wish to display detailed errors in UI
+ return
+
+ click.secho(
+ 'Unfortunately, Cycode was unable to complete the full scan. '
+ 'Please note that not all results may be available:',
+ fg='red'
+ )
+ for scan_id, error in errors.items():
+ click.echo(f'- {scan_id}: ', nl=False)
+ ConsolePrinter(context).print_error(error)
+
+
+def scan_commit_range_documents(
+ context: click.Context,
+ from_documents_to_scan: List[Document],
+ to_documents_to_scan: List[Document],
+ scan_parameters: Optional[dict] = None,
+ timeout: Optional[int] = None
+) -> None:
+ cycode_client = context.obj['client']
+ scan_type = context.obj['scan_type']
+ severity_threshold = context.obj['severity_threshold']
scan_command_type = context.info_name
- error_message = None
- all_detections_count = 0
- output_detections_count = 0
- scan_id = _get_scan_id(context)
+ progress_bar = context.obj['progress_bar']
+
+ local_scan_result = error_message = None
+ scan_completed = False
+ scan_id = str(_get_scan_id())
+
from_commit_zipped_documents = InMemoryZip()
to_commit_zipped_documents = InMemoryZip()
try:
- scan_result = init_default_scan_result(str(scan_id))
+ progress_bar.set_section_length(ProgressBarSection.SCAN, 1)
+
+ scan_result = init_default_scan_result(scan_id)
if should_scan_documents(from_documents_to_scan, to_documents_to_scan):
- logger.debug("Preparing from-commit zip")
- from_commit_zipped_documents = zip_documents_to_scan(scan_type, from_commit_zipped_documents,
- from_documents_to_scan)
- logger.debug("Preparing to-commit zip")
- to_commit_zipped_documents = zip_documents_to_scan(scan_type, to_commit_zipped_documents,
- to_documents_to_scan)
- scan_result = perform_commit_range_scan_async(context, cycode_client, from_commit_zipped_documents,
- to_commit_zipped_documents, scan_type, scan_parameters,
- timeout)
- all_detections_count, output_detections_count = \
- handle_scan_result(context, scan_result, scan_command_type, scan_type, severity_threshold,
- to_documents_to_scan)
+ logger.debug('Preparing from-commit zip')
+ from_commit_zipped_documents = zip_documents_to_scan(
+ scan_type, from_commit_zipped_documents, from_documents_to_scan
+ )
+
+ logger.debug('Preparing to-commit zip')
+ to_commit_zipped_documents = zip_documents_to_scan(
+ scan_type, to_commit_zipped_documents, to_documents_to_scan
+ )
+
+ scan_result = perform_commit_range_scan_async(
+ cycode_client, from_commit_zipped_documents, to_commit_zipped_documents,
+ scan_type, scan_parameters, timeout
+ )
+
+ progress_bar.update(ProgressBarSection.SCAN)
+ progress_bar.set_section_length(ProgressBarSection.GENERATE_REPORT, 1)
+
+ local_scan_result = create_local_scan_result(
+ scan_result, to_documents_to_scan, scan_command_type, scan_type, severity_threshold
+ )
+ set_issue_detected_by_scan_results(context, [local_scan_result])
+
+ progress_bar.update(ProgressBarSection.GENERATE_REPORT)
+ progress_bar.stop()
+
+ print_results(context, [local_scan_result])
+
scan_completed = True
except Exception as e:
_handle_exception(context, e)
error_message = str(e)
- scan_completed = False
- zip_file_size = getsizeof(from_commit_zipped_documents.in_memory_zip) + getsizeof(
- to_commit_zipped_documents.in_memory_zip)
- logger.debug('Finished scan process, %s',
- {'all_violations_count': all_detections_count, 'relevant_violations_count': output_detections_count,
- 'scan_id': str(scan_id), 'zip_file_size': zip_file_size})
- _report_scan_status(context, scan_type, str(scan_id), scan_completed, output_detections_count,
- all_detections_count, len(to_documents_to_scan), zip_file_size, scan_command_type,
- error_message)
+ zip_file_size = getsizeof(from_commit_zipped_documents.in_memory_zip) + \
+ getsizeof(to_commit_zipped_documents.in_memory_zip)
+
+ detections_count = relevant_detections_count = 0
+ if local_scan_result:
+ detections_count = local_scan_result.detections_count
+ relevant_detections_count = local_scan_result.relevant_detections_count
+ scan_id = local_scan_result.scan_id
+
+ logger.debug(
+ 'Finished scan process, %s',
+ {
+ 'all_violations_count': detections_count,
+ 'relevant_violations_count': relevant_detections_count,
+ 'scan_id': scan_id,
+ 'zip_file_size': zip_file_size
+ }
+ )
+ _report_scan_status(
+ cycode_client, scan_type, local_scan_result.scan_id, scan_completed,
+ local_scan_result.relevant_detections_count, local_scan_result.detections_count, len(to_documents_to_scan),
+ zip_file_size, scan_command_type, error_message
+ )
def should_scan_documents(from_documents_to_scan: List[Document], to_documents_to_scan: List[Document]) -> bool:
return len(from_documents_to_scan) > 0 or len(to_documents_to_scan) > 0
-def handle_scan_result(context, scan_result, command_scan_type, scan_type, severity_threshold, to_documents_to_scan):
- document_detections_list = enrich_scan_result(scan_result, to_documents_to_scan)
- relevant_document_detections_list = exclude_irrelevant_scan_results(document_detections_list, scan_type,
- command_scan_type, severity_threshold)
- context.obj['report_url'] = scan_result.report_url
- print_results(context, relevant_document_detections_list)
- context.obj['issue_detected'] = len(relevant_document_detections_list) > 0
- all_detections_count = sum(
- [len(document_detections.detections) for document_detections in document_detections_list])
- output_detections_count = sum(
- [len(document_detections.detections) for document_detections in relevant_document_detections_list])
- return all_detections_count, output_detections_count
-
-
-def perform_pre_scan_documents_actions(context: click.Context, scan_type: str, documents_to_scan: List[Document],
- is_git_diff: bool = False):
- if scan_type == SCA_SCAN_TYPE:
- logger.debug(
- f"Perform pre scan document actions")
+def create_local_scan_result(
+ scan_result: ZippedFileScanResult,
+ documents_to_scan: List[Document],
+ command_scan_type: str,
+ scan_type: str,
+ severity_threshold: str,
+) -> LocalScanResult:
+ document_detections = get_document_detections(scan_result, documents_to_scan)
+ relevant_document_detections_list = exclude_irrelevant_document_detections(
+ document_detections, scan_type, command_scan_type, severity_threshold
+ )
+
+ detections_count = sum([len(document_detection.detections) for document_detection in document_detections])
+ relevant_detections_count = sum(
+ [len(document_detections.detections) for document_detections in relevant_document_detections_list]
+ )
+
+ return LocalScanResult(
+ scan_id=scan_result.scan_id,
+ report_url=scan_result.report_url,
+ document_detections=relevant_document_detections_list,
+ issue_detected=len(relevant_document_detections_list) > 0,
+ detections_count=detections_count,
+ relevant_detections_count=relevant_detections_count
+ )
+
+
+def perform_pre_scan_documents_actions(
+ context: click.Context, scan_type: str, documents_to_scan: List[Document], is_git_diff: bool = False
+) -> None:
+ if scan_type == consts.SCA_SCAN_TYPE:
+ logger.debug(f'Perform pre scan document actions')
sca_code_scanner.add_dependencies_tree_document(context, documents_to_scan, is_git_diff)
-def zip_documents_to_scan(scan_type: str, zip: InMemoryZip, documents: List[Document]):
+def zip_documents_to_scan(scan_type: str, zip_file: InMemoryZip, documents: List[Document]) -> InMemoryZip:
start_zip_creation_time = time.time()
for index, document in enumerate(documents):
- zip_file_size = getsizeof(zip.in_memory_zip)
+ zip_file_size = getsizeof(zip_file.in_memory_zip)
validate_zip_file_size(scan_type, zip_file_size)
logger.debug('adding file to zip, %s',
{'index': index, 'filename': document.path, 'unique_id': document.unique_id})
- zip.append(document.path, document.unique_id, document.content)
- zip.close()
+ zip_file.append(document.path, document.unique_id, document.content)
+ zip_file.close()
end_zip_creation_time = time.time()
zip_creation_time = int(end_zip_creation_time - start_zip_creation_time)
logger.debug('finished to create zip file, %s', {'zip_creation_time': zip_creation_time})
- return zip
+ return zip_file
-def validate_zip_file_size(scan_type, zip_file_size):
- if scan_type == SCA_SCAN_TYPE:
- if zip_file_size > SCA_ZIP_MAX_SIZE_LIMIT_IN_BYTES:
- raise ZipTooLargeError(SCA_ZIP_MAX_SIZE_LIMIT_IN_BYTES)
+def validate_zip_file_size(scan_type: str, zip_file_size: int) -> None:
+ if scan_type == consts.SCA_SCAN_TYPE:
+ if zip_file_size > consts.SCA_ZIP_MAX_SIZE_LIMIT_IN_BYTES:
+ raise custom_exceptions.ZipTooLargeError(consts.SCA_ZIP_MAX_SIZE_LIMIT_IN_BYTES)
else:
- if zip_file_size > ZIP_MAX_SIZE_LIMIT_IN_BYTES:
- raise ZipTooLargeError(ZIP_MAX_SIZE_LIMIT_IN_BYTES)
-
-
-def perform_scan(context, cycode_client, zipped_documents: InMemoryZip, scan_type: str, scan_id: UUID,
- is_git_diff: bool,
- is_commit_range: bool, scan_parameters: dict):
- if scan_type == SCA_SCAN_TYPE or scan_type == SAST_SCAN_TYPE:
- return perform_scan_async(context, cycode_client, zipped_documents, scan_type, scan_parameters)
-
- scan_result = cycode_client.commit_range_zipped_file_scan(scan_type, zipped_documents, scan_id) \
- if is_commit_range else cycode_client.zipped_file_scan(scan_type, zipped_documents, scan_id,
- scan_parameters, is_git_diff)
-
- return scan_result
-
-
-def perform_scan_async(context: click.Context, cycode_client, zipped_documents: InMemoryZip, scan_type: str,
- scan_parameters: dict) -> ZippedFileScanResult:
+ if zip_file_size > consts.ZIP_MAX_SIZE_LIMIT_IN_BYTES:
+ raise custom_exceptions.ZipTooLargeError(consts.ZIP_MAX_SIZE_LIMIT_IN_BYTES)
+
+
+def perform_scan(
+ cycode_client: 'ScanClient',
+ zipped_documents: InMemoryZip,
+ scan_type: str,
+ scan_id: str,
+ is_git_diff: bool,
+ is_commit_range: bool,
+ scan_parameters: dict
+) -> ZippedFileScanResult:
+ if scan_type in (consts.SCA_SCAN_TYPE, consts.SAST_SCAN_TYPE):
+ return perform_scan_async(cycode_client, zipped_documents, scan_type, scan_parameters)
+
+ if is_commit_range:
+ return cycode_client.commit_range_zipped_file_scan(scan_type, zipped_documents, scan_id)
+
+ return cycode_client.zipped_file_scan(scan_type, zipped_documents, scan_id, scan_parameters, is_git_diff)
+
+
+def perform_scan_async(
+ cycode_client: 'ScanClient',
+ zipped_documents: InMemoryZip,
+ scan_type: str,
+ scan_parameters: dict
+) -> ZippedFileScanResult:
scan_async_result = cycode_client.zipped_file_scan_async(zipped_documents, scan_type, scan_parameters)
logger.debug("scan request has been triggered successfully, scan id: %s", scan_async_result.scan_id)
- return poll_scan_results(context, cycode_client, scan_async_result.scan_id)
+ return poll_scan_results(cycode_client, scan_async_result.scan_id)
+
+def perform_commit_range_scan_async(
+ cycode_client: 'ScanClient',
+ from_commit_zipped_documents: InMemoryZip,
+ to_commit_zipped_documents: InMemoryZip,
+ scan_type: str,
+ scan_parameters: dict,
+ timeout: int = None
+) -> ZippedFileScanResult:
+ scan_async_result = cycode_client.multiple_zipped_file_scan_async(
+ from_commit_zipped_documents, to_commit_zipped_documents, scan_type, scan_parameters
+ )
-def perform_commit_range_scan_async(context: click.Context, cycode_client, from_commit_zipped_documents: InMemoryZip,
- to_commit_zipped_documents: InMemoryZip, scan_type: str,
- scan_parameters: dict, timeout: int = None) -> ZippedFileScanResult:
- scan_async_result = \
- cycode_client.multiple_zipped_file_scan_async(from_commit_zipped_documents, to_commit_zipped_documents,
- scan_type, scan_parameters)
logger.debug("scan request has been triggered successfully, scan id: %s", scan_async_result.scan_id)
- return poll_scan_results(context, cycode_client, scan_async_result.scan_id, timeout)
+ return poll_scan_results(cycode_client, scan_async_result.scan_id, timeout)
-def poll_scan_results(context: click.Context, cycode_client, scan_id: str, polling_timeout: int = None):
+def poll_scan_results(
+ cycode_client: 'ScanClient', scan_id: str, polling_timeout: Optional[int] = None
+) -> ZippedFileScanResult:
if polling_timeout is None:
polling_timeout = configuration_manager.get_scan_polling_timeout_in_seconds()
last_scan_update_at = None
end_polling_time = time.time() + polling_timeout
- spinner = Halo(spinner='dots')
- spinner.start("Scan in progress")
+
while time.time() < end_polling_time:
scan_details = cycode_client.get_scan_details(scan_id)
+
if scan_details.scan_update_at is not None and scan_details.scan_update_at != last_scan_update_at:
- click.echo()
last_scan_update_at = scan_details.scan_update_at
- print_scan_details(scan_details)
- if scan_details.scan_status == SCAN_STATUS_COMPLETED:
- spinner.succeed()
+ print_debug_scan_details(scan_details)
+
+ if scan_details.scan_status == consts.SCAN_STATUS_COMPLETED:
return _get_scan_result(cycode_client, scan_id, scan_details)
- if scan_details.scan_status == SCAN_STATUS_ERROR:
- spinner.fail()
- raise ScanAsyncError(f'error occurred while trying to scan zip file. {scan_details.message}')
- time.sleep(SCAN_POLLING_WAIT_INTERVAL_IN_SECONDS)
+ elif scan_details.scan_status == consts.SCAN_STATUS_ERROR:
+ raise custom_exceptions.ScanAsyncError(
+ f'Error occurred while trying to scan zip file. {scan_details.message}'
+ )
+
+ time.sleep(consts.SCAN_POLLING_WAIT_INTERVAL_IN_SECONDS)
- spinner.stop_and_persist(symbol="⏰".encode('utf-8'), text='Timeout')
- raise ScanAsyncError(f'Failed to complete scan after {polling_timeout} seconds')
+ raise custom_exceptions.ScanAsyncError(f'Failed to complete scan after {polling_timeout} seconds')
-def print_scan_details(scan_details_response: ScanDetailsResponse):
- logger.info(f"Scan update: (scan_id: {scan_details_response.id})")
- logger.info(f"Scan status: {scan_details_response.scan_status}")
- if scan_details_response.message is not None:
- logger.info(f"Scan message: {scan_details_response.message}")
+def print_debug_scan_details(scan_details_response: 'ScanDetailsResponse') -> None:
+ logger.debug(f'Scan update: (scan_id: {scan_details_response.id})')
+ logger.debug(f'Scan status: {scan_details_response.scan_status}')
+ if scan_details_response.message:
+ logger.debug(f'Scan message: {scan_details_response.message}')
-def print_results(context: click.Context, document_detections_list: List[DocumentDetections]) -> None:
+
+def print_results(context: click.Context, local_scan_results: List[LocalScanResult]) -> None:
printer = ConsolePrinter(context)
- printer.print_scan_results(document_detections_list)
+ printer.print_scan_results(local_scan_results)
-def enrich_scan_result(
+def get_document_detections(
scan_result: ZippedFileScanResult, documents_to_scan: List[Document]
) -> List[DocumentDetections]:
- logger.debug('enriching scan result')
- document_detections_list = []
+ logger.debug('Get document detections')
+
+ document_detections = []
for detections_per_file in scan_result.detections_per_file:
file_name = get_path_by_os(detections_per_file.file_name)
commit_id = detections_per_file.commit_id
- logger.debug("going to find document of violated file, %s", {'file_name': file_name, 'commit_id': commit_id})
+
+ logger.debug('Going to find document of violated file, %s', {'file_name': file_name, 'commit_id': commit_id})
+
document = _get_document_by_file_name(documents_to_scan, file_name, commit_id)
- document_detections_list.append(
- DocumentDetections(document=document, detections=detections_per_file.detections))
+ document_detections.append(
+ DocumentDetections(document=document, detections=detections_per_file.detections)
+ )
- return document_detections_list
+ return document_detections
-def exclude_irrelevant_scan_results(document_detections_list: List[DocumentDetections], scan_type: str,
- command_scan_type: str, severity_threshold: str) -> List[DocumentDetections]:
+def exclude_irrelevant_document_detections(
+ document_detections_list: List[DocumentDetections],
+ scan_type: str,
+ command_scan_type: str,
+ severity_threshold: str
+) -> List[DocumentDetections]:
relevant_document_detections_list = []
for document_detections in document_detections_list:
- relevant_detections = exclude_irrelevant_detections(scan_type, command_scan_type, severity_threshold,
- document_detections.detections)
+ relevant_detections = exclude_irrelevant_detections(
+ document_detections.detections, scan_type, command_scan_type, severity_threshold
+ )
if relevant_detections:
- relevant_document_detections_list.append(DocumentDetections(document=document_detections.document,
- detections=relevant_detections))
+ relevant_document_detections_list.append(
+ DocumentDetections(document=document_detections.document, detections=relevant_detections)
+ )
return relevant_document_detections_list
@@ -492,13 +694,14 @@ def parse_pre_receive_input() -> str:
:return: first branch update details (input's first line)
"""
+ # FIXME(MarshalX): this blocks main thread forever if called outside of pre-receive hook
pre_receive_input = sys.stdin.read().strip()
if not pre_receive_input:
raise ValueError(
"Pre receive input was not found. Make sure that you are using this command only in pre-receive hook")
# each line represents a branch update request, handle the first one only
- # TODO support case of multiple update branch requests
+ # TODO(MichalBor): support case of multiple update branch requests
branch_update_details = pre_receive_input.splitlines()[0]
return branch_update_details
@@ -507,7 +710,7 @@ def calculate_pre_receive_commit_range(branch_update_details: str) -> Optional[s
end_commit = get_end_commit_from_branch_update_details(branch_update_details)
# branch is deleted, no need to perform scan
- if end_commit == EMPTY_COMMIT_SHA:
+ if end_commit == consts.EMPTY_COMMIT_SHA:
return
start_commit = get_oldest_unupdated_commit_for_branch(end_commit)
@@ -543,7 +746,7 @@ def get_diff_file_content(file):
return file.diff.decode('utf-8', errors='replace')
-def should_process_git_object(obj, depth):
+def should_process_git_object(obj, _: int) -> bool:
return obj.type == 'blob' and obj.size > 0
@@ -560,12 +763,12 @@ def get_default_scan_parameters(context: click.Context) -> dict:
}
-def get_scan_parameters(context: click.Context) -> dict:
- path = context.obj["path"]
+def get_scan_parameters(context: click.Context, path: str) -> dict:
scan_parameters = get_default_scan_parameters(context)
remote_url = try_get_git_remote_url(path)
if remote_url:
- context.obj["remote_url"] = remote_url
+ # TODO(MarshalX): remove hardcode
+ context.obj['remote_url'] = remote_url
scan_parameters.update(remote_url)
return scan_parameters
@@ -581,44 +784,68 @@ def try_get_git_remote_url(path: str) -> Optional[dict]:
return None
-def exclude_irrelevant_documents_to_scan(context: click.Context, documents_to_scan: List[Document]) -> \
- List[Document]:
+def exclude_irrelevant_documents_to_scan(
+ context: click.Context, documents_to_scan: List[Document]
+) -> List[Document]:
+ logger.debug('Excluding irrelevant documents to scan')
+
scan_type = context.obj['scan_type']
- logger.debug("excluding irrelevant documents to scan")
- return [document for document in documents_to_scan if
- _is_relevant_document_to_scan(scan_type, document.path, document.content)]
+
+ relevant_documents = []
+ for document in documents_to_scan:
+ if _is_relevant_document_to_scan(scan_type, document.path, document.content):
+ relevant_documents.append(document)
+
+ return relevant_documents
def exclude_irrelevant_files(context: click.Context, filenames: List[str]) -> List[str]:
scan_type = context.obj['scan_type']
- return [filename for filename in filenames if _is_relevant_file_to_scan(scan_type, filename)]
+
+ relevant_files = []
+ for filename in filenames:
+ if _is_relevant_file_to_scan(scan_type, filename):
+ relevant_files.append(filename)
+
+ return relevant_files
-def exclude_irrelevant_detections(scan_type: str, command_scan_type: str, severity_threshold: str, detections) -> List:
- relevant_detections = exclude_detections_by_exclusions_configuration(scan_type, detections)
- relevant_detections = exclude_detections_by_scan_type(scan_type, command_scan_type, relevant_detections)
- relevant_detections = exclude_detections_by_severity(scan_type, severity_threshold, relevant_detections)
+def exclude_irrelevant_detections(
+ detections: List[Detection], scan_type: str, command_scan_type: str, severity_threshold: str
+) -> List[Detection]:
+ relevant_detections = _exclude_detections_by_exclusions_configuration(detections, scan_type)
+ relevant_detections = _exclude_detections_by_scan_type(relevant_detections, scan_type, command_scan_type)
+ relevant_detections = _exclude_detections_by_severity(relevant_detections, scan_type, severity_threshold)
return relevant_detections
-def exclude_detections_by_severity(scan_type: str, severity_threshold: str, detections) -> List:
- if scan_type != SCA_SCAN_TYPE or severity_threshold is None:
+def _exclude_detections_by_severity(
+ detections: List[Detection], scan_type: str, severity_threshold: str
+) -> List[Detection]:
+ if scan_type != consts.SCA_SCAN_TYPE or severity_threshold is None:
return detections
- return [detection for detection in detections if
- _does_severity_match_severity_threshold(detection.detection_details.get('advisory_severity'),
- severity_threshold)]
+ relevant_detections = []
+ for detection in detections:
+ severity = detection.detection_details.get('advisory_severity')
+ if _does_severity_match_severity_threshold(severity, severity_threshold):
+ relevant_detections.append(detection)
+ return relevant_detections
-def exclude_detections_by_scan_type(scan_type: str, command_scan_type: str, detections) -> List:
- if command_scan_type == PRE_COMMIT_COMMAND_SCAN_TYPE:
- return exclude_detections_in_deleted_lines(detections)
- if command_scan_type in COMMIT_RANGE_BASED_COMMAND_SCAN_TYPES \
- and scan_type == SECRET_SCAN_TYPE \
- and configuration_manager.get_should_exclude_detections_in_deleted_lines(command_scan_type):
+def _exclude_detections_by_scan_type(
+ detections: List[Detection], scan_type: str, command_scan_type: str
+) -> List[Detection]:
+ if command_scan_type == consts.PRE_COMMIT_COMMAND_SCAN_TYPE:
return exclude_detections_in_deleted_lines(detections)
+
+ exclude_in_deleted_lines = configuration_manager.get_should_exclude_detections_in_deleted_lines(command_scan_type)
+ if command_scan_type in consts.COMMIT_RANGE_BASED_COMMAND_SCAN_TYPES:
+ if scan_type == consts.SECRET_SCAN_TYPE and exclude_in_deleted_lines:
+ return exclude_detections_in_deleted_lines(detections)
+
return detections
@@ -626,21 +853,25 @@ def exclude_detections_in_deleted_lines(detections) -> List:
return [detection for detection in detections if detection.detection_details.get('line_type') != 'Removed']
-def exclude_detections_by_exclusions_configuration(scan_type: str, detections) -> List:
+def _exclude_detections_by_exclusions_configuration(detections: List[Detection], scan_type: str) -> List[Detection]:
exclusions = configuration_manager.get_exclusions_by_scan_type(scan_type)
return [detection for detection in detections if not _should_exclude_detection(detection, exclusions)]
-def get_pre_commit_modified_documents():
- repo = Repo(os.getcwd())
- diff_files = repo.index.diff(GIT_HEAD_COMMIT_REV, create_patch=True, R=True)
+def get_pre_commit_modified_documents(progress_bar: 'BaseProgressBar') -> Tuple[List[Document], List[Document]]:
git_head_documents = []
pre_committed_documents = []
+
+ repo = Repo(os.getcwd())
+ diff_files = repo.index.diff(consts.GIT_HEAD_COMMIT_REV, create_patch=True, R=True)
+ progress_bar.set_section_length(ProgressBarSection.PREPARE_LOCAL_FILES, len(diff_files))
for file in diff_files:
+ progress_bar.update(ProgressBarSection.PREPARE_LOCAL_FILES)
+
diff_file_path = get_diff_file_path(file)
file_path = get_path_by_os(diff_file_path)
- file_content = sca_code_scanner.get_file_content_from_commit(repo, GIT_HEAD_COMMIT_REV, diff_file_path)
+ file_content = sca_code_scanner.get_file_content_from_commit(repo, consts.GIT_HEAD_COMMIT_REV, diff_file_path)
if file_content is not None:
git_head_documents.append(Document(file_path, file_content))
@@ -651,14 +882,22 @@ def get_pre_commit_modified_documents():
return git_head_documents, pre_committed_documents
-def get_commit_range_modified_documents(path: str, from_commit_rev: str, to_commit_rev: str) -> (
- List[Document], List[Document]):
+def get_commit_range_modified_documents(
+ progress_bar: 'BaseProgressBar', path: str, from_commit_rev: str, to_commit_rev: str
+) -> Tuple[List[Document], List[Document]]:
from_commit_documents = []
to_commit_documents = []
+
repo = Repo(path)
diff = repo.commit(from_commit_rev).diff(to_commit_rev)
- modified_files_diff = [change for change in diff if change.change_type != COMMIT_DIFF_DELETED_FILE_CHANGE_TYPE]
+
+ modified_files_diff = [
+ change for change in diff if change.change_type != consts.COMMIT_DIFF_DELETED_FILE_CHANGE_TYPE
+ ]
+ progress_bar.set_section_length(ProgressBarSection.PREPARE_LOCAL_FILES, len(modified_files_diff))
for blob in modified_files_diff:
+ progress_bar.update(ProgressBarSection.PREPARE_LOCAL_FILES)
+
diff_file_path = get_diff_file_path(blob)
file_path = get_path_by_os(diff_file_path)
@@ -673,20 +912,20 @@ def get_commit_range_modified_documents(path: str, from_commit_rev: str, to_comm
return from_commit_documents, to_commit_documents
-def _should_exclude_detection(detection, exclusions: Dict) -> bool:
- exclusions_by_value = exclusions.get(EXCLUSIONS_BY_VALUE_SECTION_NAME, [])
+def _should_exclude_detection(detection: Detection, exclusions: Dict) -> bool:
+ exclusions_by_value = exclusions.get(consts.EXCLUSIONS_BY_VALUE_SECTION_NAME, [])
if _is_detection_sha_configured_in_exclusions(detection, exclusions_by_value):
logger.debug('Going to ignore violations because is in the values to ignore list, %s',
{'sha': detection.detection_details.get('sha512', '')})
return True
- exclusions_by_sha = exclusions.get(EXCLUSIONS_BY_SHA_SECTION_NAME, [])
+ exclusions_by_sha = exclusions.get(consts.EXCLUSIONS_BY_SHA_SECTION_NAME, [])
if _is_detection_sha_configured_in_exclusions(detection, exclusions_by_sha):
logger.debug('Going to ignore violations because is in the shas to ignore list, %s',
{'sha': detection.detection_details.get('sha512', '')})
return True
- exclusions_by_rule = exclusions.get(EXCLUSIONS_BY_RULE_SECTION_NAME, [])
+ exclusions_by_rule = exclusions.get(consts.EXCLUSIONS_BY_RULE_SECTION_NAME, [])
if exclusions_by_rule:
detection_rule = detection.detection_rule_id
if detection_rule in exclusions_by_rule:
@@ -694,7 +933,7 @@ def _should_exclude_detection(detection, exclusions: Dict) -> bool:
{'detection_rule': detection_rule})
return True
- exclusions_by_package = exclusions.get(EXCLUSIONS_BY_PACKAGE_SECTION_NAME, [])
+ exclusions_by_package = exclusions.get(consts.EXCLUSIONS_BY_PACKAGE_SECTION_NAME, [])
if exclusions_by_package:
package = _get_package_name(detection)
if package in exclusions_by_package:
@@ -711,15 +950,15 @@ def _is_detection_sha_configured_in_exclusions(detection, exclusions: List[str])
def _is_path_configured_in_exclusions(scan_type: str, file_path: str) -> bool:
- exclusions_by_path = configuration_manager.get_exclusions_by_scan_type(scan_type).get(
- EXCLUSIONS_BY_PATH_SECTION_NAME, [])
+ exclusions_by_path = \
+ configuration_manager.get_exclusions_by_scan_type(scan_type).get(consts.EXCLUSIONS_BY_PATH_SECTION_NAME, [])
for exclusion_path in exclusions_by_path:
if is_sub_path(exclusion_path, file_path):
return True
return False
-def _get_package_name(detection) -> str:
+def _get_package_name(detection: Detection) -> str:
package_name = detection.detection_details.get('vulnerable_component', '')
package_version = detection.detection_details.get('vulnerable_component_version', '')
@@ -731,10 +970,13 @@ def _get_package_name(detection) -> str:
def _is_file_relevant_for_sca_scan(filename: str) -> bool:
- if any([sca_excluded_path in filename for sca_excluded_path in SCA_EXCLUDED_PATHS]):
- logger.debug("file is irrelevant because it is from node_modules's inner path, %s",
- {'filename': filename})
+ if any([sca_excluded_path in filename for sca_excluded_path in consts.SCA_EXCLUDED_PATHS]):
+ logger.debug(
+ "file is irrelevant because it is from node_modules's inner path, %s",
+ {'filename': filename}
+ )
return False
+
return True
@@ -759,12 +1001,12 @@ def _is_relevant_file_to_scan(scan_type: str, filename: str) -> bool:
{'filename': filename})
return False
- if scan_type != SCA_SCAN_TYPE and _does_file_exceed_max_size_limit(filename):
+ if scan_type != consts.SCA_SCAN_TYPE and _does_file_exceed_max_size_limit(filename):
logger.debug("file is irrelevant because its exceeded max size limit, %s",
{'filename': filename})
return False
- if scan_type == SCA_SCAN_TYPE and not _is_file_relevant_for_sca_scan(filename):
+ if scan_type == consts.SCA_SCAN_TYPE and not _is_file_relevant_for_sca_scan(filename):
return False
return True
@@ -791,7 +1033,7 @@ def _is_relevant_document_to_scan(scan_type: str, filename: str, content: str) -
{'filename': filename})
return False
- if scan_type != SCA_SCAN_TYPE and _does_document_exceed_max_size_limit(content):
+ if scan_type != consts.SCA_SCAN_TYPE and _does_document_exceed_max_size_limit(content):
logger.debug("document is irrelevant because its exceeded max size limit, %s",
{'filename': filename})
return False
@@ -799,29 +1041,35 @@ def _is_relevant_document_to_scan(scan_type: str, filename: str, content: str) -
def _is_file_extension_supported(scan_type: str, filename: str) -> bool:
- if scan_type == INFRA_CONFIGURATION_SCAN_TYPE:
- return any(filename.lower().endswith(supported_file_extension) for supported_file_extension in
- INFRA_CONFIGURATION_SCAN_SUPPORTED_FILES)
- if scan_type == SCA_SCAN_TYPE:
- return any(filename.lower().endswith(supported_file) for supported_file in
- SCA_CONFIGURATION_SCAN_SUPPORTED_FILES)
- return all(not filename.lower().endswith(file_extension_to_ignore) for file_extension_to_ignore in
- SECRET_SCAN_FILE_EXTENSIONS_TO_IGNORE)
+ filename = filename.lower()
+ if scan_type == consts.INFRA_CONFIGURATION_SCAN_TYPE:
+ return any(filename.endswith(supported_file_extension)
+ for supported_file_extension in consts.INFRA_CONFIGURATION_SCAN_SUPPORTED_FILES)
+ elif scan_type == consts.SCA_SCAN_TYPE:
+ return any(filename.endswith(supported_file)
+ for supported_file in consts.SCA_CONFIGURATION_SCAN_SUPPORTED_FILES)
-def _does_file_exceed_max_size_limit(filename: str) -> bool:
- return FILE_MAX_SIZE_LIMIT_IN_BYTES < get_file_size(filename)
+ return all(not filename.endswith(file_extension_to_ignore)
+ for file_extension_to_ignore in consts.SECRET_SCAN_FILE_EXTENSIONS_TO_IGNORE)
-def _get_document_by_file_name(documents: List[Document], file_name: str, unique_id: Optional[str] = None) \
- -> Optional[Document]:
- return next(
- (document for document in documents if _normalize_file_path(document.path) == _normalize_file_path(file_name)
- and document.unique_id == unique_id), None)
+def _does_file_exceed_max_size_limit(filename: str) -> bool:
+ return consts.FILE_MAX_SIZE_LIMIT_IN_BYTES < get_file_size(filename)
def _does_document_exceed_max_size_limit(content: str) -> bool:
- return FILE_MAX_SIZE_LIMIT_IN_BYTES < get_content_size(content)
+ return consts.FILE_MAX_SIZE_LIMIT_IN_BYTES < get_content_size(content)
+
+
+def _get_document_by_file_name(
+ documents: List[Document], file_name: str, unique_id: Optional[str] = None
+) -> Optional[Document]:
+ for document in documents:
+ if _normalize_file_path(document.path) == _normalize_file_path(file_name) and document.unique_id == unique_id:
+ return document
+
+ return None
def _is_subpath_of_cycode_configuration_folder(filename: str) -> bool:
@@ -830,32 +1078,32 @@ def _is_subpath_of_cycode_configuration_folder(filename: str) -> bool:
or filename.endswith(ConfigFileManager.get_config_file_route())
-def _handle_exception(context: click.Context, e: Exception):
+def _handle_exception(context: click.Context, e: Exception, *, return_exception: bool = False) -> Optional[CliError]:
context.obj['did_fail'] = True
if context.obj['verbose']:
- click.secho(f'Error: {traceback.format_exc()}', fg='red', nl=False)
+ click.secho(f'Error: {traceback.format_exc()}', fg='red')
errors: CliErrors = {
- NetworkError: CliError(
+ custom_exceptions.NetworkError: CliError(
soft_fail=True,
code='cycode_error',
message='Cycode was unable to complete this scan. '
'Please try again by executing the `cycode scan` command'
),
- ScanAsyncError: CliError(
+ custom_exceptions.ScanAsyncError: CliError(
soft_fail=True,
code='scan_error',
message='Cycode was unable to complete this scan. '
'Please try again by executing the `cycode scan` command'
),
- HttpUnauthorizedError: CliError(
+ custom_exceptions.HttpUnauthorizedError: CliError(
soft_fail=True,
code='auth_error',
message='Unable to authenticate to Cycode, your token is either invalid or has expired. '
'Please re-generate your token and reconfigure it by running the `cycode configure` command'
),
- ZipTooLargeError: CliError(
+ custom_exceptions.ZipTooLargeError: CliError(
soft_fail=True,
code='zip_too_large_error',
message='The path you attempted to scan exceeds the current maximum scanning size cap (10MB). '
@@ -876,7 +1124,14 @@ def _handle_exception(context: click.Context, e: Exception):
if error.soft_fail is True:
context.obj['soft_fail'] = True
- return ConsolePrinter(context).print_error(error)
+ if return_exception:
+ return error
+
+ ConsolePrinter(context).print_error(error)
+ return
+
+ if return_exception:
+ return CliError(code='unknown_error', message=str(e))
if isinstance(e, click.ClickException):
raise e
@@ -884,11 +1139,10 @@ def _handle_exception(context: click.Context, e: Exception):
raise click.ClickException(str(e))
-def _report_scan_status(context: click.Context, scan_type: str, scan_id: str, scan_completed: bool,
+def _report_scan_status(cycode_client: 'ScanClient', scan_type: str, scan_id: str, scan_completed: bool,
output_detections_count: int, all_detections_count: int, files_to_scan_count: int,
- zip_size: int, command_scan_type: str, error_message: Optional[str]):
+ zip_size: int, command_scan_type: str, error_message: Optional[str]) -> None:
try:
- cycode_client = context.obj["client"]
end_scan_time = time.time()
scan_status = {
'zip_size': zip_size,
@@ -906,13 +1160,10 @@ def _report_scan_status(context: click.Context, scan_type: str, scan_id: str, sc
cycode_client.report_scan_status(scan_type, scan_id, scan_status)
except Exception as e:
logger.debug('Failed to report scan status, %s', {'exception_message': str(e)})
- pass
-def _get_scan_id(context: click.Context):
- scan_id = uuid4()
- context.obj['scan_id'] = scan_id
- return scan_id
+def _get_scan_id() -> UUID:
+ return uuid4()
def _does_severity_match_severity_threshold(severity: str, severity_threshold: str) -> bool:
@@ -923,51 +1174,69 @@ def _does_severity_match_severity_threshold(severity: str, severity_threshold: s
return detection_severity_value >= Severity.try_get_value(severity_threshold)
-def _get_scan_result(cycode_client, scan_id: str, scan_details: ScanDetailsResponse) -> ZippedFileScanResult:
- scan_result = init_default_scan_result(scan_id, scan_details.metadata)
+def _get_scan_result(
+ cycode_client: 'ScanClient', scan_id: str, scan_details: 'ScanDetailsResponse'
+) -> ZippedFileScanResult:
if not scan_details.detections_count:
- return scan_result
+ return init_default_scan_result(scan_id, scan_details.metadata)
wait_for_detections_creation(cycode_client, scan_id, scan_details.detections_count)
+
scan_detections = cycode_client.get_scan_detections(scan_id)
- scan_result.detections_per_file = _map_detections_per_file(scan_detections)
- scan_result.did_detect = True
- return scan_result
+ return ZippedFileScanResult(
+ did_detect=True,
+ detections_per_file=_map_detections_per_file(scan_detections),
+ scan_id=scan_id,
+ report_url=_try_get_report_url(scan_details.metadata)
+ )
-def init_default_scan_result(scan_id: str, scan_metadata: str = None) -> ZippedFileScanResult:
- return ZippedFileScanResult(did_detect=False, detections_per_file=[],
- scan_id=scan_id,
- report_url=_try_get_report_url(scan_metadata))
+def init_default_scan_result(scan_id: str, scan_metadata: Optional[str] = None) -> ZippedFileScanResult:
+ return ZippedFileScanResult(
+ did_detect=False,
+ detections_per_file=[],
+ scan_id=scan_id,
+ report_url=_try_get_report_url(scan_metadata)
+ )
-def _try_get_report_url(metadata: str) -> Optional[str]:
- if metadata is None:
+def _try_get_report_url(metadata_json: Optional[str]) -> Optional[str]:
+ if metadata_json is None:
return None
+
try:
- metadata = json.loads(metadata)
- return metadata.get('report_url')
- except ValueError:
+ metadata_json = json.loads(metadata_json)
+ return metadata_json.get('report_url')
+ except json.JSONDecodeError:
return None
-def wait_for_detections_creation(cycode_client, scan_id: str, expected_detections_count: int):
- logger.debug("waiting for detections to be created")
+def wait_for_detections_creation(cycode_client: 'ScanClient', scan_id: str, expected_detections_count: int) -> None:
+ logger.debug('Waiting for detections to be created')
+
scan_persisted_detections_count = 0
- end_polling_time = time.time() + DETECTIONS_COUNT_VERIFICATION_TIMEOUT_IN_SECONDS
- spinner = Halo(spinner='dots')
- spinner.start("Please wait until printing scan result...")
+ polling_timeout = consts.DETECTIONS_COUNT_VERIFICATION_TIMEOUT_IN_SECONDS
+ end_polling_time = time.time() + polling_timeout
+
while time.time() < end_polling_time:
scan_persisted_detections_count = cycode_client.get_scan_detections_count(scan_id)
+ logger.debug(
+ f'Excepted {expected_detections_count} detections, got {scan_persisted_detections_count} detections '
+ f'({expected_detections_count - scan_persisted_detections_count} more; '
+ f'{round(end_polling_time - time.time())} seconds left)'
+ )
if scan_persisted_detections_count == expected_detections_count:
- spinner.succeed()
return
- time.sleep(DETECTIONS_COUNT_VERIFICATION_WAIT_INTERVAL_IN_SECONDS)
- spinner.stop_and_persist(symbol="⏰".encode('utf-8'), text='Timeout')
- logger.debug("%i detections has been created", scan_persisted_detections_count)
+
+ time.sleep(consts.DETECTIONS_COUNT_VERIFICATION_WAIT_INTERVAL_IN_SECONDS)
+
+ logger.debug(f'{scan_persisted_detections_count} detections has been created')
+ raise custom_exceptions.ScanAsyncError(
+ f'Failed to wait for detections to be created after {polling_timeout} seconds'
+ )
-def _map_detections_per_file(detections) -> List[DetectionsPerFile]:
+def _map_detections_per_file(detections: List[dict]) -> List[DetectionsPerFile]:
detections_per_files = {}
for detection in detections:
try:
@@ -988,24 +1257,24 @@ def _map_detections_per_file(detections) -> List[DetectionsPerFile]:
for file_name, file_detections in detections_per_files.items()]
-def _get_file_name_from_detection(detection):
- if detection['category'] == "SAST":
+def _get_file_name_from_detection(detection: dict) -> str:
+ if detection['category'] == 'SAST':
return detection['detection_details']['file_path']
return detection['detection_details']['file_name']
-def _does_reach_to_max_commits_to_scan_limit(commit_ids: List, max_commits_count: Optional[int]) -> bool:
- return max_commits_count is not None and len(commit_ids) >= max_commits_count
-
+def _does_reach_to_max_commits_to_scan_limit(commit_ids: List[str], max_commits_count: Optional[int]) -> bool:
+ if max_commits_count is None:
+ return False
-def _should_update_progress(scanned_commits_count: int) -> bool:
- return scanned_commits_count and scanned_commits_count % PROGRESS_UPDATE_COMMITS_INTERVAL == 0
+ return len(commit_ids) >= max_commits_count
-def parse_commit_range(commit_range: str, path: str) -> (str, str):
+def parse_commit_range(commit_range: str, path: str) -> Tuple[str, str]:
from_commit_rev = None
to_commit_rev = None
+
for commit in Repo(path).iter_commits(rev=commit_range):
if not to_commit_rev:
to_commit_rev = commit.hexsha
@@ -1014,33 +1283,35 @@ def parse_commit_range(commit_range: str, path: str) -> (str, str):
return from_commit_rev, to_commit_rev
-def _normalize_file_path(path: str):
- if path.startswith("/"):
+def _normalize_file_path(path: str) -> str:
+ if path.startswith('/'):
return path[1:]
- if path.startswith("./"):
+ if path.startswith('./'):
return path[2:]
return path
-def perform_post_pre_receive_scan_actions(context: click.Context):
+def perform_post_pre_receive_scan_actions(context: click.Context) -> None:
if scan_utils.is_scan_failed(context):
- click.echo(PRE_RECEIVE_REMEDIATION_MESSAGE)
+ click.echo(consts.PRE_RECEIVE_REMEDIATION_MESSAGE)
-def enable_verbose_mode(context: click.Context):
- context.obj["verbose"] = True
+def enable_verbose_mode(context: click.Context) -> None:
+ context.obj['verbose'] = True
+ # TODO(MarshalX): rework setting the log level for loggers
logger.setLevel(logging.DEBUG)
+ progress_bar_logger.setLevel(logging.DEBUG)
def is_verbose_mode_requested_in_pre_receive_scan() -> bool:
- return does_git_push_option_have_value(VERBOSE_SCAN_FLAG)
+ return does_git_push_option_have_value(consts.VERBOSE_SCAN_FLAG)
def should_skip_pre_receive_scan() -> bool:
- return does_git_push_option_have_value(SKIP_SCAN_FLAG)
+ return does_git_push_option_have_value(consts.SKIP_SCAN_FLAG)
def does_git_push_option_have_value(value: str) -> bool:
- option_count_env_value = os.getenv(GIT_PUSH_OPTION_COUNT_ENV_VAR_NAME, '')
+ option_count_env_value = os.getenv(consts.GIT_PUSH_OPTION_COUNT_ENV_VAR_NAME, '')
option_count = int(option_count_env_value) if option_count_env_value.isdigit() else 0
- return any(os.getenv(f'{GIT_PUSH_OPTION_ENV_VAR_PREFIX}{i}') == value for i in range(option_count))
+ return any(os.getenv(f'{consts.GIT_PUSH_OPTION_ENV_VAR_PREFIX}{i}') == value for i in range(option_count))
diff --git a/cycode/cli/consts.py b/cycode/cli/consts.py
index f37bbdef..1959d4ae 100644
--- a/cycode/cli/consts.py
+++ b/cycode/cli/consts.py
@@ -84,6 +84,13 @@
# 200MB in bytes (in binary)
SCA_ZIP_MAX_SIZE_LIMIT_IN_BYTES = 209715200
+# scan in batches
+SCAN_BATCH_MAX_SIZE_IN_BYTES = 9 * 1024 * 1024
+SCAN_BATCH_MAX_FILES_COUNT = 1000
+# if we increase this values, the server doesn't allow connecting (ConnectionError)
+SCAN_BATCH_MAX_PARALLEL_SCANS = 5
+SCAN_BATCH_SCANS_PER_CPU = 1
+
# scan with polling
SCAN_POLLING_WAIT_INTERVAL_IN_SECONDS = 5
DEFAULT_SCAN_POLLING_TIMEOUT_IN_SECONDS = 3600
@@ -93,8 +100,6 @@
DEFAULT_SCA_PRE_COMMIT_TIMEOUT_IN_SECONDS = 600
SCA_PRE_COMMIT_TIMEOUT_IN_SECONDS_ENV_VAR_NAME = 'SCA_PRE_COMMIT_TIMEOUT_IN_SECONDS'
-PROGRESS_UPDATE_COMMITS_INTERVAL = 100
-
# pre receive scan
PRE_RECEIVE_MAX_COMMITS_TO_SCAN_COUNT_ENV_VAR_NAME = 'PRE_RECEIVE_MAX_COMMITS_TO_SCAN_COUNT'
DEFAULT_PRE_RECEIVE_MAX_COMMITS_TO_SCAN_COUNT = 50
@@ -124,6 +129,9 @@
SKIP_SCAN_FLAG = 'skip-cycode-scan'
VERBOSE_SCAN_FLAG = 'verbose'
+ISSUE_DETECTED_STATUS_CODE = 1
+NO_ISSUES_STATUS_CODE = 0
+
LICENSE_COMPLIANCE_POLICY_ID = '8f681450-49e1-4f7e-85b7-0c8fe84b3a35'
PACKAGE_VULNERABILITY_POLICY_ID = '9369d10a-9ac0-48d3-9921-5de7fe9a37a7'
diff --git a/cycode/cli/main.py b/cycode/cli/main.py
index 9eee8343..4e52edb3 100644
--- a/cycode/cli/main.py
+++ b/cycode/cli/main.py
@@ -3,9 +3,10 @@
import click
import sys
-from typing import List, Optional
+from typing import List, Optional, TYPE_CHECKING
from cycode import __version__
+from cycode.cli.consts import NO_ISSUES_STATUS_CODE, ISSUE_DETECTED_STATUS_CODE
from cycode.cli.models import Severity
from cycode.cli.config import config
from cycode.cli import code_scanner
@@ -14,14 +15,17 @@
from cycode.cli.user_settings.user_settings_commands import set_credentials, add_exclusions
from cycode.cli.auth.auth_command import authenticate
from cycode.cli.utils import scan_utils
+from cycode.cli.utils.progress_bar import get_progress_bar
from cycode.cyclient import logger
+from cycode.cli.utils.progress_bar import logger as progress_bar_logger
from cycode.cyclient.cycode_client_base import CycodeClientBase
from cycode.cyclient.models import UserAgentOptionScheme
from cycode.cyclient.scan_config.scan_config_creator import create_scan_client
+if TYPE_CHECKING:
+ from cycode.cyclient.scan_client import ScanClient
+
CONTEXT = dict()
-ISSUE_DETECTED_STATUS_CODE = 1
-NO_ISSUES_STATUS_CODE = 0
@click.group(
@@ -106,25 +110,41 @@ def code_scan(context: click.Context, scan_type, client_id, secret, show_secret,
context.obj["soft_fail"] = config["soft_fail"]
context.obj["scan_type"] = scan_type
+
+ # save backward compatability with old style command
if output is not None:
- # save backward compatability with old style command
context.obj["output"] = output
+ if output == "json":
+ context.obj["no_progress_meter"] = True
+
context.obj["client"] = get_cycode_client(client_id, secret)
context.obj["severity_threshold"] = severity_threshold
context.obj["monitor"] = monitor
context.obj["report"] = report
+
_sca_scan_to_context(context, sca_scan)
+ context.obj["progress_bar"] = get_progress_bar(hidden=context.obj["no_progress_meter"])
+ context.obj["progress_bar"].start()
+
return 1
@code_scan.result_callback()
@click.pass_context
-def finalize(context: click.Context, *args, **kwargs):
- if context.obj["soft_fail"]:
+def finalize(context: click.Context, *_, **__):
+ progress_bar = context.obj.get('progress_bar')
+ if progress_bar:
+ progress_bar.stop()
+
+ if context.obj['soft_fail']:
sys.exit(0)
- sys.exit(ISSUE_DETECTED_STATUS_CODE if _should_fail_scan(context) else NO_ISSUES_STATUS_CODE)
+ exit_code = NO_ISSUES_STATUS_CODE
+ if _should_fail_scan(context):
+ exit_code = ISSUE_DETECTED_STATUS_CODE
+
+ sys.exit(exit_code)
@click.group(
@@ -139,6 +159,9 @@ def finalize(context: click.Context, *args, **kwargs):
@click.option(
"--verbose", "-v", is_flag=True, default=False, help="Show detailed logs",
)
+@click.option(
+ '--no-progress-meter', is_flag=True, default=False, help='Do not show the progress meter',
+)
@click.option(
'--output',
default='text',
@@ -153,23 +176,29 @@ def finalize(context: click.Context, *args, **kwargs):
)
@click.version_option(__version__, prog_name="cycode")
@click.pass_context
-def main_cli(context: click.Context, verbose: bool, output: str, user_agent: Optional[str]):
+def main_cli(context: click.Context, verbose: bool, no_progress_meter: bool, output: str, user_agent: Optional[str]):
context.ensure_object(dict)
configuration_manager = ConfigurationManager()
verbose = verbose or configuration_manager.get_verbose_flag()
context.obj['verbose'] = verbose
+ # TODO(MarshalX): rework setting the log level for loggers
log_level = logging.DEBUG if verbose else logging.INFO
logger.setLevel(log_level)
+ progress_bar_logger.setLevel(log_level)
context.obj['output'] = output
+ if output == 'json':
+ no_progress_meter = True
+
+ context.obj['no_progress_meter'] = no_progress_meter
if user_agent:
user_agent_option = UserAgentOptionScheme().loads(user_agent)
CycodeClientBase.enrich_user_agent(user_agent_option.user_agent_suffix)
-def get_cycode_client(client_id, client_secret):
+def get_cycode_client(client_id: str, client_secret: str) -> 'ScanClient':
if not client_id or not client_secret:
client_id, client_secret = _get_configured_credentials()
if not client_id:
diff --git a/cycode/cli/models.py b/cycode/cli/models.py
index 011ffe4e..94218175 100644
--- a/cycode/cli/models.py
+++ b/cycode/cli/models.py
@@ -1,5 +1,5 @@
from enum import Enum
-from typing import List, NamedTuple, Dict, Type
+from typing import List, NamedTuple, Dict, Type, Optional
from cycode.cyclient.models import Detection
@@ -58,3 +58,12 @@ class CliError(NamedTuple):
class CliResult(NamedTuple):
success: bool
message: str
+
+
+class LocalScanResult(NamedTuple):
+ scan_id: str
+ report_url: Optional[str]
+ document_detections: List[DocumentDetections]
+ issue_detected: bool
+ detections_count: int
+ relevant_detections_count: int
diff --git a/cycode/cli/printers/base_printer.py b/cycode/cli/printers/base_printer.py
index e5450e8f..afd46513 100644
--- a/cycode/cli/printers/base_printer.py
+++ b/cycode/cli/printers/base_printer.py
@@ -1,9 +1,12 @@
from abc import ABC, abstractmethod
-from typing import List
+from typing import List, TYPE_CHECKING
import click
-from cycode.cli.models import DocumentDetections, CliResult, CliError
+from cycode.cli.models import CliResult, CliError
+
+if TYPE_CHECKING:
+ from cycode.cli.models import LocalScanResult
class BasePrinter(ABC):
@@ -15,7 +18,7 @@ def __init__(self, context: click.Context):
self.context = context
@abstractmethod
- def print_scan_results(self, results: List[DocumentDetections]) -> None:
+ def print_scan_results(self, local_scan_results: List['LocalScanResult']) -> None:
pass
@abstractmethod
diff --git a/cycode/cli/printers/base_table_printer.py b/cycode/cli/printers/base_table_printer.py
index 112a1d4a..4a956e66 100644
--- a/cycode/cli/printers/base_table_printer.py
+++ b/cycode/cli/printers/base_table_printer.py
@@ -1,18 +1,20 @@
import abc
-from typing import List
+from typing import List, TYPE_CHECKING
import click
from cycode.cli.printers.text_printer import TextPrinter
-from cycode.cli.models import DocumentDetections, CliError, CliResult
+from cycode.cli.models import CliError, CliResult
from cycode.cli.printers.base_printer import BasePrinter
+if TYPE_CHECKING:
+ from cycode.cli.models import LocalScanResult
+
class BaseTablePrinter(BasePrinter, abc.ABC):
def __init__(self, context: click.Context):
super().__init__(context)
self.context = context
- self.scan_id: str = context.obj.get('scan_id')
self.scan_type: str = context.obj.get('scan_type')
self.show_secret: bool = context.obj.get('show_secret', False)
@@ -22,22 +24,16 @@ def print_result(self, result: CliResult) -> None:
def print_error(self, error: CliError) -> None:
TextPrinter(self.context).print_error(error)
- def print_scan_results(self, results: List[DocumentDetections]):
- click.secho(f'Scan Results: (scan_id: {self.scan_id})')
-
- if not results:
+ def print_scan_results(self, local_scan_results: List['LocalScanResult']):
+ if all(result.issue_detected == 0 for result in local_scan_results):
click.secho('Good job! No issues were found!!! 👏👏👏', fg=self.GREEN_COLOR_NAME)
return
- self._print_results(results)
-
- report_url = self.context.obj.get('report_url')
- if report_url:
- click.secho(f'Report URL: {report_url}')
+ self._print_results(local_scan_results)
def _is_git_repository(self) -> bool:
return self.context.obj.get('remote_url') is not None
@abc.abstractmethod
- def _print_results(self, results: List[DocumentDetections]) -> None:
+ def _print_results(self, local_scan_results: List['LocalScanResult']) -> None:
raise NotImplementedError
diff --git a/cycode/cli/printers/console_printer.py b/cycode/cli/printers/console_printer.py
index 9932e140..06e3ddf7 100644
--- a/cycode/cli/printers/console_printer.py
+++ b/cycode/cli/printers/console_printer.py
@@ -2,13 +2,14 @@
from typing import List, TYPE_CHECKING
from cycode.cli.exceptions.custom_exceptions import CycodeError
-from cycode.cli.models import DocumentDetections, CliResult, CliError
+from cycode.cli.models import CliResult, CliError
from cycode.cli.printers.table_printer import TablePrinter
from cycode.cli.printers.sca_table_printer import SCATablePrinter
from cycode.cli.printers.json_printer import JsonPrinter
from cycode.cli.printers.text_printer import TextPrinter
if TYPE_CHECKING:
+ from cycode.cli.models import LocalScanResult
from cycode.cli.printers.base_printer import BasePrinter
@@ -31,9 +32,9 @@ def __init__(self, context: click.Context):
if self._printer_class is None:
raise CycodeError(f'"{self.output_type}" output type is not supported.')
- def print_scan_results(self, detections_results_list: List[DocumentDetections]) -> None:
+ def print_scan_results(self, local_scan_results: List['LocalScanResult']) -> None:
printer = self._get_scan_printer()
- printer.print_scan_results(detections_results_list)
+ printer.print_scan_results(local_scan_results)
def _get_scan_printer(self) -> 'BasePrinter':
printer_class = self._printer_class
diff --git a/cycode/cli/printers/json_printer.py b/cycode/cli/printers/json_printer.py
index 2e77aba7..c02eff5b 100644
--- a/cycode/cli/printers/json_printer.py
+++ b/cycode/cli/printers/json_printer.py
@@ -1,18 +1,17 @@
import json
-from typing import List
+from typing import List, TYPE_CHECKING
import click
-from cycode.cli.models import DocumentDetections, CliResult, CliError
+from cycode.cli.models import CliResult, CliError
from cycode.cli.printers.base_printer import BasePrinter
from cycode.cyclient.models import DetectionSchema
+if TYPE_CHECKING:
+ from cycode.cli.models import LocalScanResult
-class JsonPrinter(BasePrinter):
- def __init__(self, context: click.Context):
- super().__init__(context)
- self.scan_id = context.obj.get('scan_id')
+class JsonPrinter(BasePrinter):
def print_result(self, result: CliResult) -> None:
result = {
'result': result.success,
@@ -29,10 +28,11 @@ def print_error(self, error: CliError) -> None:
click.secho(self.get_data_json(result))
- def print_scan_results(self, results: List[DocumentDetections]) -> None:
+ def print_scan_results(self, local_scan_results: List['LocalScanResult']) -> None:
detections = []
- for result in results:
- detections.extend(result.detections)
+ for local_scan_result in local_scan_results:
+ for document_detections in local_scan_result.document_detections:
+ detections.extend(document_detections.detections)
detections_dict = DetectionSchema(many=True).dump(detections)
@@ -40,7 +40,7 @@ def print_scan_results(self, results: List[DocumentDetections]) -> None:
def _get_json_scan_result(self, detections: dict) -> str:
result = {
- 'scan_id': str(self.scan_id),
+ 'scan_id': 'DEPRECATED', # FIXME(MarshalX): we need change JSON struct to support multiple scan results
'detections': detections
}
diff --git a/cycode/cli/printers/sca_table_printer.py b/cycode/cli/printers/sca_table_printer.py
index 7feac6b1..051a2e56 100644
--- a/cycode/cli/printers/sca_table_printer.py
+++ b/cycode/cli/printers/sca_table_printer.py
@@ -1,14 +1,17 @@
from collections import defaultdict
-from typing import List, Dict
+from typing import List, Dict, TYPE_CHECKING
import click
from texttable import Texttable
from cycode.cli.consts import LICENSE_COMPLIANCE_POLICY_ID, PACKAGE_VULNERABILITY_POLICY_ID
-from cycode.cli.models import DocumentDetections, Detection
+from cycode.cli.models import Detection
from cycode.cli.printers.base_table_printer import BaseTablePrinter
from cycode.cli.utils.string_utils import shortcut_dependency_paths
+if TYPE_CHECKING:
+ from cycode.cli.models import LocalScanResult
+
SEVERITY_COLUMN = 'Severity'
LICENSE_COLUMN = 'License'
UPGRADE_COLUMN = 'Upgrade'
@@ -26,17 +29,20 @@
class SCATablePrinter(BaseTablePrinter):
- def _print_results(self, results: List[DocumentDetections]) -> None:
- detections_per_detection_type_id = self._extract_detections_per_detection_type_id(results)
+ def _print_results(self, local_scan_results: List['LocalScanResult']) -> None:
+ detections_per_detection_type_id = self._extract_detections_per_detection_type_id(local_scan_results)
self._print_detection_per_detection_type_id(detections_per_detection_type_id)
@staticmethod
- def _extract_detections_per_detection_type_id(results: List[DocumentDetections]) -> Dict[str, List[Detection]]:
+ def _extract_detections_per_detection_type_id(
+ local_scan_results: List['LocalScanResult']
+ ) -> Dict[str, List[Detection]]:
detections_per_detection_type_id = defaultdict(list)
- for document_detection in results:
- for detection in document_detection.detections:
- detections_per_detection_type_id[detection.detection_type_id].append(detection)
+ for local_scan_result in local_scan_results:
+ for document_detection in local_scan_result.document_detections:
+ for detection in document_detection.detections:
+ detections_per_detection_type_id[detection.detection_type_id].append(detection)
return detections_per_detection_type_id
@@ -51,7 +57,7 @@ def _print_detection_per_detection_type_id(
rows = []
if detection_type_id == PACKAGE_VULNERABILITY_POLICY_ID:
- title = "Dependencies Vulnerabilities"
+ title = 'Dependencies Vulnerabilities'
headers = [SEVERITY_COLUMN] + headers
headers.extend(PREVIEW_DETECTIONS_COMMON_HEADERS)
@@ -61,7 +67,7 @@ def _print_detection_per_detection_type_id(
for detection in detections:
rows.append(self._get_upgrade_package_vulnerability(detection))
elif detection_type_id == LICENSE_COMPLIANCE_POLICY_ID:
- title = "License Compliance"
+ title = 'License Compliance'
headers.extend(PREVIEW_DETECTIONS_COMMON_HEADERS)
headers.append(LICENSE_COLUMN)
@@ -138,7 +144,7 @@ def _get_upgrade_package_vulnerability(self, detection: Detection) -> List[str]:
]
upgrade = ''
- if alert.get("first_patched_version"):
+ if alert.get('first_patched_version'):
upgrade = f'{alert.get("vulnerable_requirements")} -> {alert.get("first_patched_version")}'
row.append(upgrade)
diff --git a/cycode/cli/printers/table_printer.py b/cycode/cli/printers/table_printer.py
index 353ce903..12f8f61b 100644
--- a/cycode/cli/printers/table_printer.py
+++ b/cycode/cli/printers/table_printer.py
@@ -1,4 +1,4 @@
-from typing import List
+from typing import List, TYPE_CHECKING
import click
@@ -7,7 +7,10 @@
from cycode.cli.printers.table import Table
from cycode.cli.utils.string_utils import obfuscate_text, get_position_in_line
from cycode.cli.consts import SECRET_SCAN_TYPE, INFRA_CONFIGURATION_SCAN_TYPE, SAST_SCAN_TYPE
-from cycode.cli.models import DocumentDetections, Detection, Document
+from cycode.cli.models import Detection, Document
+
+if TYPE_CHECKING:
+ from cycode.cli.models import LocalScanResult
# Creation must have strict order. Represents the order of the columns in the table (from left to right)
ISSUE_TYPE_COLUMN = ColumnInfoBuilder.build(name='Issue Type')
@@ -19,6 +22,8 @@
COLUMN_NUMBER_COLUMN = ColumnInfoBuilder.build(name='Column Number')
VIOLATION_LENGTH_COLUMN = ColumnInfoBuilder.build(name='Violation Length')
VIOLATION_COLUMN = ColumnInfoBuilder.build(name='Violation')
+SCAN_ID_COLUMN = ColumnInfoBuilder.build(name='Scan ID')
+REPORT_URL_COLUMN = ColumnInfoBuilder.build(name='Report URL')
COLUMN_WIDTHS_CONFIG: ColumnWidthsConfig = {
SECRET_SCAN_TYPE: {
@@ -27,29 +32,36 @@
FILE_PATH_COLUMN: 2,
SECRET_SHA_COLUMN: 2,
VIOLATION_COLUMN: 2,
+ SCAN_ID_COLUMN: 2,
},
INFRA_CONFIGURATION_SCAN_TYPE: {
ISSUE_TYPE_COLUMN: 4,
RULE_ID_COLUMN: 3,
FILE_PATH_COLUMN: 3,
+ SCAN_ID_COLUMN: 2,
},
SAST_SCAN_TYPE: {
ISSUE_TYPE_COLUMN: 7,
RULE_ID_COLUMN: 2,
FILE_PATH_COLUMN: 3,
+ SCAN_ID_COLUMN: 2,
},
}
class TablePrinter(BaseTablePrinter):
- def _print_results(self, results: List[DocumentDetections]) -> None:
+ def _print_results(self, local_scan_results: List['LocalScanResult']) -> None:
table = self._get_table()
if self.scan_type in COLUMN_WIDTHS_CONFIG:
table.set_cols_width(COLUMN_WIDTHS_CONFIG[self.scan_type])
- for result in results:
- for detection in result.detections:
- self._enrich_table_with_values(table, detection, result.document)
+ for local_scan_result in local_scan_results:
+ for document_detections in local_scan_result.document_detections:
+ report_url = local_scan_result.report_url if local_scan_result.report_url else 'N/A'
+ for detection in document_detections.detections:
+ table.set(REPORT_URL_COLUMN, report_url)
+ table.set(SCAN_ID_COLUMN, local_scan_result.scan_id)
+ self._enrich_table_with_values(table, detection, document_detections.document)
click.echo(table.get_table().draw())
@@ -61,6 +73,8 @@ def _get_table(self) -> Table:
table.add(FILE_PATH_COLUMN)
table.add(LINE_NUMBER_COLUMN)
table.add(COLUMN_NUMBER_COLUMN)
+ table.add(SCAN_ID_COLUMN)
+ table.add(REPORT_URL_COLUMN)
if self._is_git_repository():
table.add(COMMIT_SHA_COLUMN)
diff --git a/cycode/cli/printers/text_printer.py b/cycode/cli/printers/text_printer.py
index c3a655d6..2d25af2f 100644
--- a/cycode/cli/printers/text_printer.py
+++ b/cycode/cli/printers/text_printer.py
@@ -1,5 +1,5 @@
import math
-from typing import List, Optional
+from typing import List, Optional, TYPE_CHECKING
import click
@@ -9,11 +9,13 @@
from cycode.cli.consts import SECRET_SCAN_TYPE, COMMIT_RANGE_BASED_COMMAND_SCAN_TYPES
from cycode.cli.utils.string_utils import obfuscate_text, get_position_in_line
+if TYPE_CHECKING:
+ from cycode.cli.models import LocalScanResult
+
class TextPrinter(BasePrinter):
def __init__(self, context: click.Context):
super().__init__(context)
- self.scan_id: str = context.obj.get('scan_id')
self.scan_type: str = context.obj.get('scan_type')
self.command_scan_type: str = context.info_name
self.show_secret: bool = context.obj.get('show_secret', False)
@@ -26,39 +28,46 @@ def print_result(self, result: CliResult) -> None:
click.secho(result.message, fg=color)
def print_error(self, error: CliError) -> None:
- click.secho(error.message, fg=self.RED_COLOR_NAME, nl=False)
-
- def print_scan_results(self, results: List[DocumentDetections]):
- click.secho(f"Scan Results: (scan_id: {self.scan_id})")
+ click.secho(error.message, fg=self.RED_COLOR_NAME)
- if not results:
- click.secho("Good job! No issues were found!!! 👏👏👏", fg=self.GREEN_COLOR_NAME)
+ def print_scan_results(self, local_scan_results: List['LocalScanResult']):
+ if all(result.issue_detected == 0 for result in local_scan_results):
+ click.secho('Good job! No issues were found!!! 👏👏👏', fg=self.GREEN_COLOR_NAME)
return
- for document_detections in results:
- self._print_document_detections(document_detections)
+ for local_scan_result in local_scan_results:
+ for document_detections in local_scan_result.document_detections:
+ self._print_document_detections(
+ document_detections, local_scan_result.scan_id, local_scan_result.report_url
+ )
- report_url = self.context.obj.get('report_url')
- if report_url:
- click.secho(f'Report URL: {report_url}')
-
- def _print_document_detections(self, document_detections: DocumentDetections):
+ def _print_document_detections(
+ self, document_detections: DocumentDetections, scan_id: str, report_url: Optional[str]
+ ):
document = document_detections.document
lines_to_display = self._get_lines_to_display_count()
for detection in document_detections.detections:
- self._print_detection_summary(detection, document.path)
+ self._print_detection_summary(detection, document.path, scan_id, report_url)
self._print_detection_code_segment(detection, document, lines_to_display)
- def _print_detection_summary(self, detection: Detection, document_path: str):
+ def _print_detection_summary(
+ self, detection: Detection, document_path: str, scan_id: str, report_url: Optional[str]
+ ):
detection_name = detection.type if self.scan_type == SECRET_SCAN_TYPE else detection.message
+
detection_sha = detection.detection_details.get('sha512')
detection_sha_message = f'\nSecret SHA: {detection_sha}' if detection_sha else ''
+
+ scan_id_message = f'\nScan ID: {scan_id}'
+ report_url_message = f'\nReport URL: {report_url}' if report_url else ''
+
detection_commit_id = detection.detection_details.get('commit_id')
detection_commit_id_message = f'\nCommit SHA: {detection_commit_id}' if detection_commit_id else ''
+
click.echo(
f'⛔ Found issue of type: {click.style(detection_name, fg="bright_red", bold=True)} '
f'(rule ID: {detection.detection_rule_id}) in file: {click.format_filename(document_path)} '
- f'{detection_sha_message}{detection_commit_id_message} ⛔'
+ f'{detection_sha_message}{scan_id_message}{report_url_message}{detection_commit_id_message} ⛔'
)
def _print_detection_code_segment(self, detection: Detection, document: Document, code_segment_size: int):
diff --git a/cycode/cli/utils/enum_utils.py b/cycode/cli/utils/enum_utils.py
new file mode 100644
index 00000000..54a02ffb
--- /dev/null
+++ b/cycode/cli/utils/enum_utils.py
@@ -0,0 +1,7 @@
+from enum import Enum
+
+
+class AutoCountEnum(Enum):
+ @staticmethod
+ def _generate_next_value_(name, start, count, last_values):
+ return count
diff --git a/cycode/cli/utils/path_utils.py b/cycode/cli/utils/path_utils.py
index d7c4478c..f6bef61b 100644
--- a/cycode/cli/utils/path_utils.py
+++ b/cycode/cli/utils/path_utils.py
@@ -1,4 +1,4 @@
-from typing import Iterable, List, Optional
+from typing import Iterable, List, Optional, AnyStr
import pathspec
import os
from pathlib import Path
@@ -65,10 +65,10 @@ def join_paths(path: str, filename: str) -> str:
return os.path.join(path, filename)
-def get_file_content(file_path: str) -> Optional[str]:
+def get_file_content(file_path: str) -> Optional[AnyStr]:
try:
- with open(file_path, "r", encoding="utf-8") as f:
+ with open(file_path, 'r', encoding='UTF-8') as f:
content = f.read()
return content
- except FileNotFoundError:
+ except (FileNotFoundError, UnicodeDecodeError):
return None
diff --git a/cycode/cli/utils/progress_bar.py b/cycode/cli/utils/progress_bar.py
new file mode 100644
index 00000000..196ca9e9
--- /dev/null
+++ b/cycode/cli/utils/progress_bar.py
@@ -0,0 +1,240 @@
+from abc import ABC, abstractmethod
+from enum import auto
+from typing import NamedTuple, Dict, TYPE_CHECKING, Optional
+
+import click
+
+from cycode.cyclient.config import get_logger
+from cycode.cli.utils.enum_utils import AutoCountEnum
+
+if TYPE_CHECKING:
+ from click._termui_impl import ProgressBar
+
+
+logger = get_logger('progress bar')
+
+
+class ProgressBarSection(AutoCountEnum):
+ PREPARE_LOCAL_FILES = auto()
+ # UPLOAD_FILES = auto()
+ SCAN = auto()
+ GENERATE_REPORT = auto()
+
+ def has_next(self) -> bool:
+ return self.value < len(ProgressBarSection) - 1
+
+ def next(self) -> 'ProgressBarSection':
+ return ProgressBarSection(self.value + 1)
+
+
+class ProgressBarSectionInfo(NamedTuple):
+ section: ProgressBarSection
+ label: str
+ start_percent: int
+ stop_percent: int
+
+
+_PROGRESS_BAR_LENGTH = 100
+
+_PROGRESS_BAR_SECTIONS = {
+ ProgressBarSection.PREPARE_LOCAL_FILES: ProgressBarSectionInfo(
+ ProgressBarSection.PREPARE_LOCAL_FILES, 'Prepare local files', start_percent=0, stop_percent=5
+ ),
+ # TODO(MarshalX): could be added in the future
+ # ProgressBarSection.UPLOAD_FILES: ProgressBarSectionInfo(
+ # ProgressBarSection.UPLOAD_FILES, 'Upload files', start_percent=5, stop_percent=10
+ # ),
+ ProgressBarSection.SCAN: ProgressBarSectionInfo(
+ ProgressBarSection.SCAN, 'Scan in progress', start_percent=5, stop_percent=95
+ ),
+ ProgressBarSection.GENERATE_REPORT: ProgressBarSectionInfo(
+ ProgressBarSection.GENERATE_REPORT, 'Generate report', start_percent=95, stop_percent=100
+ ),
+}
+
+
+def _get_section_length(section: 'ProgressBarSection') -> int:
+ return _PROGRESS_BAR_SECTIONS[section].stop_percent - _PROGRESS_BAR_SECTIONS[section].start_percent
+
+
+class BaseProgressBar(ABC):
+ def __init__(self, *args, **kwargs):
+ pass
+
+ @abstractmethod
+ def __enter__(self) -> 'BaseProgressBar':
+ ...
+
+ @abstractmethod
+ def __exit__(self, *args, **kwargs) -> None:
+ ...
+
+ @abstractmethod
+ def start(self) -> None:
+ ...
+
+ @abstractmethod
+ def stop(self) -> None:
+ ...
+
+ @abstractmethod
+ def set_section_length(self, section: 'ProgressBarSection', length: int) -> None:
+ ...
+
+ @abstractmethod
+ def update(self, section: 'ProgressBarSection') -> None:
+ ...
+
+
+class DummyProgressBar(BaseProgressBar):
+ def __init__(self, *args, **kwargs):
+ super().__init__(*args, **kwargs)
+
+ def __enter__(self) -> 'DummyProgressBar':
+ return self
+
+ def __exit__(self, *args, **kwargs) -> None:
+ pass
+
+ def start(self) -> None:
+ pass
+
+ def stop(self) -> None:
+ pass
+
+ def set_section_length(self, section: 'ProgressBarSection', length: int) -> None:
+ pass
+
+ def update(self, section: 'ProgressBarSection') -> None:
+ pass
+
+
+class CompositeProgressBar(BaseProgressBar):
+ def __init__(self):
+ super().__init__()
+ self._progress_bar_context_manager = click.progressbar(
+ length=_PROGRESS_BAR_LENGTH,
+ item_show_func=self._progress_bar_item_show_func,
+ update_min_steps=0,
+ )
+ self._progress_bar: Optional['ProgressBar'] = None
+ self._run = False
+
+ self._section_lengths: Dict[ProgressBarSection, int] = {}
+ self._section_values: Dict[ProgressBarSection, int] = {}
+
+ self._current_section_value = 0
+ self._current_section: ProgressBarSectionInfo = _PROGRESS_BAR_SECTIONS[ProgressBarSection.PREPARE_LOCAL_FILES]
+
+ def __enter__(self) -> 'CompositeProgressBar':
+ self._progress_bar = self._progress_bar_context_manager.__enter__()
+ self._run = True
+ return self
+
+ def __exit__(self, *args, **kwargs) -> None:
+ self._progress_bar_context_manager.__exit__(*args, **kwargs)
+ self._run = False
+
+ def start(self) -> None:
+ if not self._run:
+ self.__enter__()
+
+ def stop(self) -> None:
+ if self._run:
+ self.__exit__(None, None, None)
+
+ def set_section_length(self, section: 'ProgressBarSection', length: int) -> None:
+ logger.debug(f'set_section_length: {section} {length}')
+ self._section_lengths[section] = length
+
+ if length == 0:
+ self._skip_section(section)
+
+ def _skip_section(self, section: 'ProgressBarSection') -> None:
+ self._progress_bar.update(_get_section_length(section))
+ self._maybe_update_current_section()
+
+ def _increment_section_value(self, section: 'ProgressBarSection', value: int) -> None:
+ self._section_values[section] = self._section_values.get(section, 0) + value
+ logger.debug(
+ f'_increment_section_value: {section} +{value}. '
+ f'{self._section_values[section]}/{self._section_lengths[section]}'
+ )
+
+ def _rerender_progress_bar(self) -> None:
+ """Used to update label right after changing the progress bar section."""
+ self._progress_bar.update(0)
+
+ def _increment_progress(self, section: ProgressBarSection) -> None:
+ increment_value = self._get_increment_progress_value(section)
+
+ self._current_section_value += increment_value
+ self._progress_bar.update(increment_value)
+
+ def _maybe_update_current_section(self) -> None:
+ if not self._current_section.section.has_next():
+ return
+
+ max_val = self._section_lengths.get(self._current_section.section, 0)
+ cur_val = self._section_values.get(self._current_section.section, 0)
+ if cur_val >= max_val:
+ next_section = _PROGRESS_BAR_SECTIONS[self._current_section.section.next()]
+ logger.debug(
+ f'_update_current_section: {self._current_section.section} -> {next_section.section}'
+ )
+
+ self._current_section = next_section
+ self._current_section_value = 0
+ self._rerender_progress_bar()
+
+ def _get_increment_progress_value(self, section: 'ProgressBarSection') -> int:
+ max_val = self._section_lengths[section]
+ cur_val = self._section_values[section]
+
+ expected_value = round(_get_section_length(section) * (cur_val / max_val))
+
+ return expected_value - self._current_section_value
+
+ def _progress_bar_item_show_func(self, _=None) -> str:
+ return self._current_section.label
+
+ def update(self, section: 'ProgressBarSection', value: int = 1) -> None:
+ if not self._progress_bar:
+ raise ValueError('Progress bar is not initialized. Call start() first or use "with" statement.')
+
+ if section not in self._section_lengths:
+ raise ValueError(f'{section} section is not initialized. Call set_section_length() first.')
+ if section is not self._current_section.section:
+ raise ValueError(
+ f'Previous section is not completed yet. Complete {self._current_section.section} section first.'
+ )
+
+ self._increment_section_value(section, value)
+ self._increment_progress(section)
+ self._maybe_update_current_section()
+
+
+def get_progress_bar(*, hidden: bool) -> BaseProgressBar:
+ if hidden:
+ return DummyProgressBar()
+
+ return CompositeProgressBar()
+
+
+if __name__ == '__main__':
+ # TODO(MarshalX): cover with tests and remove this code
+ import time
+ import random
+
+ bar = get_progress_bar(hidden=False)
+ bar.start()
+
+ for bar_section in ProgressBarSection:
+ section_capacity = random.randint(500, 1000)
+ bar.set_section_length(bar_section, section_capacity)
+
+ for i in range(section_capacity):
+ time.sleep(0.01)
+ bar.update(bar_section)
+
+ bar.stop()
diff --git a/cycode/cli/utils/scan_batch.py b/cycode/cli/utils/scan_batch.py
new file mode 100644
index 00000000..5604d562
--- /dev/null
+++ b/cycode/cli/utils/scan_batch.py
@@ -0,0 +1,73 @@
+import os
+from multiprocessing.pool import ThreadPool
+from typing import List, TYPE_CHECKING, Callable, Tuple, Dict
+
+from cycode.cli.consts import SCAN_BATCH_MAX_SIZE_IN_BYTES, SCAN_BATCH_MAX_FILES_COUNT, SCAN_BATCH_SCANS_PER_CPU, \
+ SCAN_BATCH_MAX_PARALLEL_SCANS
+from cycode.cli.models import Document
+from cycode.cli.utils.progress_bar import ProgressBarSection
+
+if TYPE_CHECKING:
+ from cycode.cli.models import LocalScanResult, CliError
+ from cycode.cli.utils.progress_bar import BaseProgressBar
+
+
+def split_documents_into_batches(
+ documents: List[Document],
+ max_size_mb: int = SCAN_BATCH_MAX_SIZE_IN_BYTES,
+ max_files_count: int = SCAN_BATCH_MAX_FILES_COUNT,
+) -> List[List[Document]]:
+ batches = []
+
+ current_size = 0
+ current_batch = []
+ for document in documents:
+ document_size = len(document.content.encode('UTF-8'))
+
+ if (current_size + document_size > max_size_mb) or (len(current_batch) >= max_files_count):
+ batches.append(current_batch)
+
+ current_batch = [document]
+ current_size = document_size
+ else:
+ current_batch.append(document)
+ current_size += document_size
+
+ if current_batch:
+ batches.append(current_batch)
+
+ return batches
+
+
+def _get_threads_count() -> int:
+ return min(os.cpu_count() * SCAN_BATCH_SCANS_PER_CPU, SCAN_BATCH_MAX_PARALLEL_SCANS)
+
+
+def run_parallel_batched_scan(
+ scan_function: Callable[[List[Document]], Tuple[str, 'CliError', 'LocalScanResult']],
+ documents: List[Document],
+ progress_bar: 'BaseProgressBar',
+ max_size_mb: int = SCAN_BATCH_MAX_SIZE_IN_BYTES,
+ max_files_count: int = SCAN_BATCH_MAX_FILES_COUNT,
+) -> Tuple[Dict[str, 'CliError'], List['LocalScanResult']]:
+ batches = split_documents_into_batches(documents, max_size_mb, max_files_count)
+ progress_bar.set_section_length(ProgressBarSection.SCAN, len(batches)) # * 3
+ # TODO(MarshalX): we should multiply the count of batches in SCAN section because each batch has 3 steps:
+ # 1. scan creation
+ # 2. scan completion
+ # 3. detection creation
+ # it's not possible yet because not all scan types moved to polling mechanism
+ # the progress bar could be significant improved (be more dynamic) in the future
+
+ local_scan_results: List['LocalScanResult'] = []
+ cli_errors: Dict[str, 'CliError'] = {}
+ with ThreadPool(processes=_get_threads_count()) as pool:
+ for scan_id, err, result in pool.imap(scan_function, batches):
+ if result:
+ local_scan_results.append(result)
+ if err:
+ cli_errors[scan_id] = err
+
+ progress_bar.update(ProgressBarSection.SCAN)
+
+ return cli_errors, local_scan_results
diff --git a/cycode/cli/utils/scan_utils.py b/cycode/cli/utils/scan_utils.py
index 8541add1..77866c4b 100644
--- a/cycode/cli/utils/scan_utils.py
+++ b/cycode/cli/utils/scan_utils.py
@@ -1,7 +1,11 @@
import click
-def is_scan_failed(context: click.Context):
- did_fail = context.obj.get("did_fail")
- issue_detected = context.obj.get("issue_detected")
+def set_issue_detected(context: click.Context, issue_detected: bool) -> None:
+ context.obj['issue_detected'] = issue_detected
+
+
+def is_scan_failed(context: click.Context) -> bool:
+ did_fail = context.obj.get('did_fail')
+ issue_detected = context.obj.get('issue_detected')
return did_fail or issue_detected
diff --git a/cycode/cyclient/cycode_client_base.py b/cycode/cyclient/cycode_client_base.py
index 1259e250..dc37a258 100644
--- a/cycode/cyclient/cycode_client_base.py
+++ b/cycode/cyclient/cycode_client_base.py
@@ -1,6 +1,7 @@
import platform
from typing import Dict
+from cycode.cyclient import logger
from requests import Response, request, exceptions
from cycode import __version__
@@ -72,21 +73,26 @@ def _execute(
method: str,
endpoint: str,
headers: dict = None,
+ without_auth: bool = False,
**kwargs
) -> Response:
url = self.build_full_url(self.api_url, endpoint)
+ logger.debug(f'Executing {method.upper()} request to {url}')
try:
+ headers = self.get_request_headers(headers, without_auth=without_auth)
response = request(
- method=method, url=url, timeout=self.timeout, headers=self.get_request_headers(headers), **kwargs
+ method=method, url=url, timeout=self.timeout, headers=headers, **kwargs
)
+ logger.debug(f'Response {response.status_code} from {url}. Content: {response.text}')
+
response.raise_for_status()
return response
except Exception as e:
self._handle_exception(e)
- def get_request_headers(self, additional_headers: dict = None) -> dict:
+ def get_request_headers(self, additional_headers: dict = None, **kwargs) -> dict:
if additional_headers is None:
return self.MANDATORY_HEADERS.copy()
return {**self.MANDATORY_HEADERS, **additional_headers}
diff --git a/cycode/cyclient/cycode_token_based_client.py b/cycode/cyclient/cycode_token_based_client.py
index e3da7cc2..f1043c57 100644
--- a/cycode/cyclient/cycode_token_based_client.py
+++ b/cycode/cyclient/cycode_token_based_client.py
@@ -32,17 +32,18 @@ def refresh_api_token_if_needed(self) -> None:
def refresh_api_token(self) -> None:
auth_response = self.post(
url_path=f'api/v1/auth/api-token',
- body={'clientId': self.client_id, 'secret': self.client_secret}
+ body={'clientId': self.client_id, 'secret': self.client_secret},
+ without_auth=True,
)
auth_response_data = auth_response.json()
self._api_token = auth_response_data['token']
self._expires_in = arrow.utcnow().shift(seconds=auth_response_data['expires_in'] * 0.8)
- def get_request_headers(self, additional_headers: dict = None) -> dict:
+ def get_request_headers(self, additional_headers: dict = None, without_auth=False) -> dict:
headers = super().get_request_headers(additional_headers=additional_headers)
- if not self.lock.locked():
+ if not without_auth:
headers = self._add_auth_header(headers)
return headers
diff --git a/cycode/cyclient/scan_client.py b/cycode/cyclient/scan_client.py
index 3eb29cf3..6b754e4a 100644
--- a/cycode/cyclient/scan_client.py
+++ b/cycode/cyclient/scan_client.py
@@ -38,6 +38,7 @@ def zipped_file_scan(self, scan_type: str, zip_file: InMemoryZip, scan_id: str,
data={'scan_id': scan_id, 'is_git_diff': is_git_diff, 'scan_parameters': json.dumps(scan_parameters)},
files=files
)
+
return self.parse_zipped_file_scan_response(response)
def zipped_file_scan_async(self, zip_file: InMemoryZip, scan_type: str, scan_parameters: dict,
@@ -72,14 +73,20 @@ def get_scan_details(self, scan_id: str) -> models.ScanDetailsResponse:
return models.ScanDetailsResponseSchema().load(response.json())
def get_scan_detections(self, scan_id: str) -> List[dict]:
+ url_path = f'{self.scan_config.get_detections_prefix()}/{self.DETECTIONS_SERVICE_CONTROLLER_PATH}'
+ params = {'scan_id': scan_id}
+
+ page_size = 200
+
detections = []
+
page_number = 0
- page_size = 200
last_response_size = 0
-
while page_number == 0 or last_response_size == page_size:
- url_path = f'{self.scan_config.get_detections_prefix()}/{self.DETECTIONS_SERVICE_CONTROLLER_PATH}?scan_id={scan_id}&page_size={page_size}&page_number={page_number}'
- response = self.scan_cycode_client.get(url_path=url_path).json()
+ params['page_size'] = page_size
+ params['page_number'] = page_number
+
+ response = self.scan_cycode_client.get(url_path=url_path, params=params).json()
detections.extend(response)
page_number += 1
diff --git a/cycode/cyclient/scan_config/scan_config_creator.py b/cycode/cyclient/scan_config/scan_config_creator.py
index 5f0b8a7c..ef20ee1e 100644
--- a/cycode/cyclient/scan_config/scan_config_creator.py
+++ b/cycode/cyclient/scan_config/scan_config_creator.py
@@ -1,3 +1,5 @@
+from typing import Tuple
+
from ..config import dev_mode
from ..config_dev import DEV_CYCODE_API_URL
from ..cycode_dev_based_client import CycodeDevBasedClient
@@ -6,7 +8,7 @@
from ..scan_config.scan_config_base import DefaultScanConfig, DevScanConfig
-def create_scan_client(client_id, client_secret):
+def create_scan_client(client_id: str, client_secret: str) -> ScanClient:
if dev_mode:
scan_cycode_client, scan_config = create_scan_for_dev_env()
else:
@@ -16,13 +18,13 @@ def create_scan_client(client_id, client_secret):
scan_config=scan_config)
-def create_scan(client_id, client_secret):
+def create_scan(client_id: str, client_secret: str) -> Tuple[CycodeTokenBasedClient, DefaultScanConfig]:
scan_cycode_client = CycodeTokenBasedClient(client_id, client_secret)
scan_config = DefaultScanConfig()
return scan_cycode_client, scan_config
-def create_scan_for_dev_env():
+def create_scan_for_dev_env() -> Tuple[CycodeDevBasedClient, DevScanConfig]:
scan_cycode_client = CycodeDevBasedClient(DEV_CYCODE_API_URL)
scan_config = DevScanConfig()
return scan_cycode_client, scan_config
diff --git a/poetry.lock b/poetry.lock
index 51b3c7d7..acbcbcd3 100644
--- a/poetry.lock
+++ b/poetry.lock
@@ -1,10 +1,9 @@
-# This file is automatically @generated by Poetry and should not be changed by hand.
+# This file is automatically @generated by Poetry 1.5.1 and should not be changed by hand.
[[package]]
name = "altgraph"
version = "0.17.3"
description = "Python graph (network) package"
-category = "dev"
optional = false
python-versions = "*"
files = [
@@ -16,7 +15,6 @@ files = [
name = "arrow"
version = "0.17.0"
description = "Better dates & times for Python"
-category = "main"
optional = false
python-versions = ">=2.7, !=3.0.*, !=3.1.*, !=3.2.*, !=3.3.*, !=3.4.*"
files = [
@@ -31,7 +29,6 @@ python-dateutil = ">=2.7.0"
name = "binaryornot"
version = "0.4.4"
description = "Ultra-lightweight pure Python package to check if a file is binary or text."
-category = "main"
optional = false
python-versions = "*"
files = [
@@ -46,7 +43,6 @@ chardet = ">=3.0.2"
name = "certifi"
version = "2023.5.7"
description = "Python package for providing Mozilla's CA Bundle."
-category = "main"
optional = false
python-versions = ">=3.6"
files = [
@@ -58,7 +54,6 @@ files = [
name = "chardet"
version = "5.1.0"
description = "Universal encoding detector for Python 3"
-category = "main"
optional = false
python-versions = ">=3.7"
files = [
@@ -70,7 +65,6 @@ files = [
name = "charset-normalizer"
version = "3.1.0"
description = "The Real First Universal Charset Detector. Open, modern and actively maintained alternative to Chardet."
-category = "main"
optional = false
python-versions = ">=3.7.0"
files = [
@@ -155,7 +149,6 @@ files = [
name = "click"
version = "8.1.3"
description = "Composable command line interface toolkit"
-category = "main"
optional = false
python-versions = ">=3.7"
files = [
@@ -171,7 +164,6 @@ importlib-metadata = {version = "*", markers = "python_version < \"3.8\""}
name = "colorama"
version = "0.4.6"
description = "Cross-platform colored terminal text."
-category = "main"
optional = false
python-versions = "!=3.0.*,!=3.1.*,!=3.2.*,!=3.3.*,!=3.4.*,!=3.5.*,!=3.6.*,>=2.7"
files = [
@@ -183,7 +175,6 @@ files = [
name = "coverage"
version = "7.2.5"
description = "Code coverage measurement for Python"
-category = "dev"
optional = false
python-versions = ">=3.7"
files = [
@@ -247,7 +238,6 @@ toml = ["tomli"]
name = "dunamai"
version = "1.16.1"
description = "Dynamic version generation"
-category = "dev"
optional = false
python-versions = ">=3.5,<4.0"
files = [
@@ -263,7 +253,6 @@ packaging = ">=20.9"
name = "exceptiongroup"
version = "1.1.1"
description = "Backport of PEP 654 (exception groups)"
-category = "dev"
optional = false
python-versions = ">=3.7"
files = [
@@ -278,7 +267,6 @@ test = ["pytest (>=6)"]
name = "gitdb"
version = "4.0.10"
description = "Git Object Database"
-category = "main"
optional = false
python-versions = ">=3.7"
files = [
@@ -293,7 +281,6 @@ smmap = ">=3.0.1,<6"
name = "gitpython"
version = "3.1.31"
description = "GitPython is a Python library used to interact with Git repositories"
-category = "main"
optional = false
python-versions = ">=3.7"
files = [
@@ -305,33 +292,10 @@ files = [
gitdb = ">=4.0.1,<5"
typing-extensions = {version = ">=3.7.4.3", markers = "python_version < \"3.8\""}
-[[package]]
-name = "halo"
-version = "0.0.31"
-description = "Beautiful terminal spinners in Python"
-category = "main"
-optional = false
-python-versions = ">=3.4"
-files = [
- {file = "halo-0.0.31-py2-none-any.whl", hash = "sha256:5350488fb7d2aa7c31a1344120cee67a872901ce8858f60da7946cef96c208ab"},
- {file = "halo-0.0.31.tar.gz", hash = "sha256:7b67a3521ee91d53b7152d4ee3452811e1d2a6321975137762eb3d70063cc9d6"},
-]
-
-[package.dependencies]
-colorama = ">=0.3.9"
-log-symbols = ">=0.0.14"
-six = ">=1.12.0"
-spinners = ">=0.0.24"
-termcolor = ">=1.1.0"
-
-[package.extras]
-ipython = ["IPython (==5.7.0)", "ipywidgets (==7.1.0)"]
-
[[package]]
name = "idna"
version = "3.4"
description = "Internationalized Domain Names in Applications (IDNA)"
-category = "main"
optional = false
python-versions = ">=3.5"
files = [
@@ -343,7 +307,6 @@ files = [
name = "importlib-metadata"
version = "6.6.0"
description = "Read metadata from Python packages"
-category = "main"
optional = false
python-versions = ">=3.7"
files = [
@@ -364,7 +327,6 @@ testing = ["flake8 (<5)", "flufl.flake8", "importlib-resources (>=1.3)", "packag
name = "iniconfig"
version = "2.0.0"
description = "brain-dead simple config-ini parsing"
-category = "dev"
optional = false
python-versions = ">=3.7"
files = [
@@ -372,26 +334,10 @@ files = [
{file = "iniconfig-2.0.0.tar.gz", hash = "sha256:2d91e135bf72d31a410b17c16da610a82cb55f6b0477d1a902134b24a455b8b3"},
]
-[[package]]
-name = "log-symbols"
-version = "0.0.14"
-description = "Colored symbols for various log levels for Python"
-category = "main"
-optional = false
-python-versions = "*"
-files = [
- {file = "log_symbols-0.0.14-py3-none-any.whl", hash = "sha256:4952106ff8b605ab7d5081dd2c7e6ca7374584eff7086f499c06edd1ce56dcca"},
- {file = "log_symbols-0.0.14.tar.gz", hash = "sha256:cf0bbc6fe1a8e53f0d174a716bc625c4f87043cc21eb55dd8a740cfe22680556"},
-]
-
-[package.dependencies]
-colorama = ">=0.3.9"
-
[[package]]
name = "macholib"
version = "1.16.2"
description = "Mach-O header analysis and editing"
-category = "dev"
optional = false
python-versions = "*"
files = [
@@ -406,7 +352,6 @@ altgraph = ">=0.17"
name = "marshmallow"
version = "3.8.0"
description = "A lightweight library for converting complex datatypes to and from native Python datatypes."
-category = "main"
optional = false
python-versions = ">=3.5"
files = [
@@ -424,7 +369,6 @@ tests = ["pytest", "pytz", "simplejson"]
name = "mock"
version = "4.0.3"
description = "Rolling backport of unittest.mock for all Pythons"
-category = "dev"
optional = false
python-versions = ">=3.6"
files = [
@@ -441,7 +385,6 @@ test = ["pytest (<5.4)", "pytest-cov"]
name = "packaging"
version = "23.1"
description = "Core utilities for Python packages"
-category = "dev"
optional = false
python-versions = ">=3.7"
files = [
@@ -453,7 +396,6 @@ files = [
name = "pathspec"
version = "0.8.1"
description = "Utility library for gitignore style pattern matching of file paths."
-category = "main"
optional = false
python-versions = ">=2.7, !=3.0.*, !=3.1.*, !=3.2.*, !=3.3.*, !=3.4.*"
files = [
@@ -465,7 +407,6 @@ files = [
name = "pefile"
version = "2023.2.7"
description = "Python PE parsing module"
-category = "dev"
optional = false
python-versions = ">=3.6.0"
files = [
@@ -477,7 +418,6 @@ files = [
name = "pluggy"
version = "1.0.0"
description = "plugin and hook calling mechanisms for python"
-category = "dev"
optional = false
python-versions = ">=3.6"
files = [
@@ -496,7 +436,6 @@ testing = ["pytest", "pytest-benchmark"]
name = "pyinstaller"
version = "5.11.0"
description = "PyInstaller bundles a Python application and all its dependencies into a single package."
-category = "dev"
optional = false
python-versions = "<3.12,>=3.7"
files = [
@@ -531,7 +470,6 @@ hook-testing = ["execnet (>=1.5.0)", "psutil", "pytest (>=2.7.3)"]
name = "pyinstaller-hooks-contrib"
version = "2023.3"
description = "Community maintained hooks for PyInstaller"
-category = "dev"
optional = false
python-versions = ">=3.7"
files = [
@@ -543,7 +481,6 @@ files = [
name = "pytest"
version = "7.3.1"
description = "pytest: simple powerful testing with Python"
-category = "dev"
optional = false
python-versions = ">=3.7"
files = [
@@ -567,7 +504,6 @@ testing = ["argcomplete", "attrs (>=19.2.0)", "hypothesis (>=3.56)", "mock", "no
name = "pytest-mock"
version = "3.10.0"
description = "Thin-wrapper around the mock package for easier use with pytest"
-category = "dev"
optional = false
python-versions = ">=3.7"
files = [
@@ -585,7 +521,6 @@ dev = ["pre-commit", "pytest-asyncio", "tox"]
name = "python-dateutil"
version = "2.8.2"
description = "Extensions to the standard Python datetime module"
-category = "main"
optional = false
python-versions = "!=3.0.*,!=3.1.*,!=3.2.*,>=2.7"
files = [
@@ -600,7 +535,6 @@ six = ">=1.5"
name = "pywin32-ctypes"
version = "0.2.0"
description = ""
-category = "dev"
optional = false
python-versions = "*"
files = [
@@ -612,7 +546,6 @@ files = [
name = "pyyaml"
version = "6.0"
description = "YAML parser and emitter for Python"
-category = "main"
optional = false
python-versions = ">=3.6"
files = [
@@ -662,7 +595,6 @@ files = [
name = "requests"
version = "2.31.0"
description = "Python HTTP for Humans."
-category = "main"
optional = false
python-versions = ">=3.7"
files = [
@@ -684,7 +616,6 @@ use-chardet-on-py3 = ["chardet (>=3.0.2,<6)"]
name = "responses"
version = "0.23.1"
description = "A utility library for mocking out the `requests` Python library."
-category = "dev"
optional = false
python-versions = ">=3.7"
files = [
@@ -706,7 +637,6 @@ tests = ["coverage (>=6.0.0)", "flake8", "mypy", "pytest (>=7.0.0)", "pytest-asy
name = "setuptools"
version = "67.7.2"
description = "Easily download, build, install, upgrade, and uninstall Python packages"
-category = "dev"
optional = false
python-versions = ">=3.7"
files = [
@@ -723,7 +653,6 @@ testing-integration = ["build[virtualenv]", "filelock (>=3.4.0)", "jaraco.envs (
name = "six"
version = "1.16.0"
description = "Python 2 and 3 compatibility utilities"
-category = "main"
optional = false
python-versions = ">=2.7, !=3.0.*, !=3.1.*, !=3.2.*"
files = [
@@ -735,7 +664,6 @@ files = [
name = "smmap"
version = "5.0.0"
description = "A pure Python implementation of a sliding window memory map manager"
-category = "main"
optional = false
python-versions = ">=3.6"
files = [
@@ -743,38 +671,10 @@ files = [
{file = "smmap-5.0.0.tar.gz", hash = "sha256:c840e62059cd3be204b0c9c9f74be2c09d5648eddd4580d9314c3ecde0b30936"},
]
-[[package]]
-name = "spinners"
-version = "0.0.24"
-description = "Spinners for terminals"
-category = "main"
-optional = false
-python-versions = "*"
-files = [
- {file = "spinners-0.0.24-py3-none-any.whl", hash = "sha256:2fa30d0b72c9650ad12bbe031c9943b8d441e41b4f5602b0ec977a19f3290e98"},
- {file = "spinners-0.0.24.tar.gz", hash = "sha256:1eb6aeb4781d72ab42ed8a01dcf20f3002bf50740d7154d12fb8c9769bf9e27f"},
-]
-
-[[package]]
-name = "termcolor"
-version = "2.3.0"
-description = "ANSI color formatting for output in terminal"
-category = "main"
-optional = false
-python-versions = ">=3.7"
-files = [
- {file = "termcolor-2.3.0-py3-none-any.whl", hash = "sha256:3afb05607b89aed0ffe25202399ee0867ad4d3cb4180d98aaf8eefa6a5f7d475"},
- {file = "termcolor-2.3.0.tar.gz", hash = "sha256:b5b08f68937f138fe92f6c089b99f1e2da0ae56c52b78bf7075fd95420fd9a5a"},
-]
-
-[package.extras]
-tests = ["pytest", "pytest-cov"]
-
[[package]]
name = "texttable"
version = "1.6.7"
description = "module to create simple ASCII tables"
-category = "main"
optional = false
python-versions = "*"
files = [
@@ -786,7 +686,6 @@ files = [
name = "tomli"
version = "2.0.1"
description = "A lil' TOML parser"
-category = "dev"
optional = false
python-versions = ">=3.7"
files = [
@@ -798,7 +697,6 @@ files = [
name = "types-pyyaml"
version = "6.0.12.9"
description = "Typing stubs for PyYAML"
-category = "dev"
optional = false
python-versions = "*"
files = [
@@ -810,7 +708,6 @@ files = [
name = "typing-extensions"
version = "4.5.0"
description = "Backported and Experimental Type Hints for Python 3.7+"
-category = "main"
optional = false
python-versions = ">=3.7"
files = [
@@ -822,7 +719,6 @@ files = [
name = "urllib3"
version = "2.0.2"
description = "HTTP library with thread-safe connection pooling, file post, and more."
-category = "main"
optional = false
python-versions = ">=3.7"
files = [
@@ -840,7 +736,6 @@ zstd = ["zstandard (>=0.18.0)"]
name = "zipp"
version = "3.15.0"
description = "Backport of pathlib-compatible object wrapper for zip files"
-category = "main"
optional = false
python-versions = ">=3.7"
files = [
@@ -855,4 +750,4 @@ testing = ["big-O", "flake8 (<5)", "jaraco.functools", "jaraco.itertools", "more
[metadata]
lock-version = "2.0"
python-versions = ">=3.7,<3.12"
-content-hash = "ab665eabb7b281d5fcfef66b81ab5882b511282e822129e2408b1653f5044dd5"
+content-hash = "13ef296063bf977819668451d2ba229a9009e3cee5478f5a9d2c4aef3e5e2b2f"
diff --git a/pyproject.toml b/pyproject.toml
index e95712de..39d01626 100644
--- a/pyproject.toml
+++ b/pyproject.toml
@@ -35,7 +35,6 @@ pathspec = ">=0.8.0,<0.9.0"
gitpython = ">=3.1.30,<3.2.0"
arrow = ">=0.17.0,<0.18.0"
binaryornot = ">=0.4.4,<0.5.0"
-halo = "==0.0.31"
texttable = ">=1.6.7,<1.7.0"
requests = ">=2.24,<3.0"
diff --git a/tests/cli/test_main.py b/tests/cli/test_main.py
index e018819f..f2784626 100644
--- a/tests/cli/test_main.py
+++ b/tests/cli/test_main.py
@@ -34,7 +34,9 @@ def test_passing_output_option(
responses.add(get_zipped_file_scan_response(get_zipped_file_scan_url(scan_type, scan_client)))
responses.add(api_token_response)
- # scan report is not mocked. This raise connection error on attempt to report scan. it doesn't perform real request
+ # Scan report is not mocked.
+ # This raises connection error on the attempt to report scan.
+ # It doesn't perform real request
args = ['scan', '--soft-fail', 'path', str(_PATH_TO_SCAN)]
@@ -58,4 +60,4 @@ def test_passing_output_option(
output = json.loads(result.output)
assert 'scan_id' in output
else:
- assert 'Scan Results' in result.output
+ assert 'Scan ID' in result.output
diff --git a/tests/cyclient/test_scan_client.py b/tests/cyclient/test_scan_client.py
index afbbdabe..d4e11128 100644
--- a/tests/cyclient/test_scan_client.py
+++ b/tests/cyclient/test_scan_client.py
@@ -52,7 +52,7 @@ def get_zipped_file_scan_response(url: str, scan_id: UUID = None) -> responses.R
json_response = {
'did_detect': True,
- 'scan_id': scan_id.hex, # not always as expected due to _get_scan_id and passing scan_id to cxt of CLI
+ 'scan_id': str(scan_id), # not always as expected due to _get_scan_id and passing scan_id to cxt of CLI
'detections_per_file': [
{
'file_name': str(_ZIP_CONTENT_PATH.joinpath('secrets.py')),
@@ -86,7 +86,7 @@ def get_zipped_file_scan_response(url: str, scan_id: UUID = None) -> responses.R
def test_get_service_name(scan_client: ScanClient):
- # TODO(Marshal): get_service_name should be removed from ScanClient? Because it exists in ScanConfig
+ # TODO(MarshalX): get_service_name should be removed from ScanClient? Because it exists in ScanConfig
assert scan_client.get_service_name('secret') == 'secret'
assert scan_client.get_service_name('iac') == 'iac'
assert scan_client.get_service_name('sca') == 'scans'
@@ -102,11 +102,10 @@ def test_zipped_file_scan(scan_type: str, scan_client: ScanClient, api_token_res
responses.add(api_token_response) # mock token based client
responses.add(get_zipped_file_scan_response(url, expected_scan_id))
- # TODO(MarshalX): fix wrong type hint? UUID instead of str
zipped_file_scan_response = scan_client.zipped_file_scan(
- scan_type, zip_file, scan_id=expected_scan_id, scan_parameters={}
+ scan_type, zip_file, scan_id=str(expected_scan_id), scan_parameters={}
)
- assert zipped_file_scan_response.scan_id == expected_scan_id.hex
+ assert zipped_file_scan_response.scan_id == str(expected_scan_id)
@pytest.mark.parametrize('scan_type', config['scans']['supported_scans'])
From ea798720532ba8a17224fb9644ef5317cefb5236 Mon Sep 17 00:00:00 2001
From: Ilya Siamionau
Date: Wed, 5 Jul 2023 13:42:04 +0200
Subject: [PATCH 005/257] CM-24996 - Integrate Black code formatter (#133)
---
.github/workflows/black.yml | 39 ++
cycode/__init__.py | 2 +-
cycode/cli/auth/auth_command.py | 10 +-
cycode/cli/auth/auth_manager.py | 17 +-
cycode/cli/code_scanner.py | 388 ++++++++++--------
cycode/cli/consts.py | 83 +++-
cycode/cli/exceptions/custom_exceptions.py | 6 +-
.../maven/base_restore_maven_dependencies.py | 23 +-
.../maven/restore_gradle_dependencies.py | 3 +-
.../maven/restore_maven_dependencies.py | 40 +-
cycode/cli/helpers/sca_code_scanner.py | 48 ++-
cycode/cli/main.py | 159 ++++---
cycode/cli/models.py | 10 +-
cycode/cli/printers/json_printer.py | 14 +-
cycode/cli/printers/sca_table_printer.py | 12 +-
cycode/cli/printers/table_printer.py | 6 +-
cycode/cli/printers/text_printer.py | 73 ++--
cycode/cli/user_settings/base_file_manager.py | 1 -
.../cli/user_settings/config_file_manager.py | 25 +-
.../user_settings/configuration_manager.py | 27 +-
.../cli/user_settings/credentials_manager.py | 6 +-
.../user_settings/user_settings_commands.py | 103 +++--
cycode/cli/utils/progress_bar.py | 4 +-
cycode/cli/utils/scan_batch.py | 24 +-
cycode/cli/utils/shell_executor.py | 2 +-
cycode/cli/utils/task_timer.py | 14 +-
cycode/cli/zip_file.py | 2 +-
cycode/cyclient/config.py | 5 +-
cycode/cyclient/config_dev.py | 2 +-
cycode/cyclient/cycode_client_base.py | 34 +-
cycode/cyclient/cycode_dev_based_client.py | 1 -
cycode/cyclient/models.py | 67 ++-
cycode/cyclient/scan_client.py | 39 +-
.../cyclient/scan_config/scan_config_base.py | 3 -
.../scan_config/scan_config_creator.py | 3 +-
cycode/cyclient/utils.py | 2 +-
poetry.lock | 145 ++++++-
pyproject.toml | 25 +-
tests/__init__.py | 2 +-
tests/cli/test_code_scanner.py | 20 +-
tests/cli/test_main.py | 2 +-
tests/conftest.py | 9 +-
tests/cyclient/test_auth_client.py | 23 +-
tests/cyclient/test_client_base.py | 6 +-
tests/cyclient/test_dev_based_client.py | 4 +-
tests/cyclient/test_scan_client.py | 20 +-
tests/cyclient/test_token_based_client.py | 4 +-
.../test_configuration_manager.py | 22 +-
.../test_user_settings_commands.py | 46 ++-
49 files changed, 1001 insertions(+), 624 deletions(-)
create mode 100644 .github/workflows/black.yml
diff --git a/.github/workflows/black.yml b/.github/workflows/black.yml
new file mode 100644
index 00000000..05208c66
--- /dev/null
+++ b/.github/workflows/black.yml
@@ -0,0 +1,39 @@
+name: Black (code formatter)
+
+on: [ pull_request, push ]
+
+jobs:
+ black:
+ runs-on: ubuntu-latest
+
+ steps:
+ - name: Run Cimon
+ uses: cycodelabs/cimon-action@v0
+ with:
+ client-id: ${{ secrets.CIMON_CLIENT_ID }}
+ secret: ${{ secrets.CIMON_SECRET }}
+ prevent: true
+ allowed-hosts: >
+ files.pythonhosted.org
+ install.python-poetry.org
+ pypi.org
+
+ - name: Checkout repository
+ uses: actions/checkout@v3
+
+ - name: Setup Python
+ uses: actions/setup-python@v4
+ with:
+ python-version: 3.7
+
+ - name: Setup Poetry
+ uses: snok/install-poetry@v1
+
+ - name: Install dependencies
+ run: poetry install
+
+ - name: Check code style of package
+ run: poetry run black --check cycode
+
+ - name: Check code style of tests
+ run: poetry run black --check tests
diff --git a/cycode/__init__.py b/cycode/__init__.py
index 9d89bffd..4ce71ef1 100644
--- a/cycode/__init__.py
+++ b/cycode/__init__.py
@@ -1 +1 @@
-__version__ = '0.0.0' # DON'T TOUCH. Placeholder. Will be filled automatically on poetry build from Git Tag
+__version__ = '0.0.0' # DON'T TOUCH. Placeholder. Will be filled automatically on poetry build from Git Tag
diff --git a/cycode/cli/auth/auth_command.py b/cycode/cli/auth/auth_command.py
index 37b6c3f6..e19085fb 100644
--- a/cycode/cli/auth/auth_command.py
+++ b/cycode/cli/auth/auth_command.py
@@ -13,7 +13,7 @@
@click.group(invoke_without_command=True)
@click.pass_context
def authenticate(context: click.Context):
- """ Authenticates your machine to associate CLI with your cycode account """
+ """Authenticates your machine to associate CLI with your cycode account"""
if context.invoked_subcommand is not None:
# if it is a subcommand do nothing
return
@@ -33,7 +33,7 @@ def authenticate(context: click.Context):
@authenticate.command(name='check')
@click.pass_context
def authorization_check(context: click.Context):
- """ Check your machine associating CLI with your cycode account """
+ """Check your machine associating CLI with your cycode account"""
printer = ConsolePrinter(context)
passed_auth_check_res = CliResult(success=True, message='You are authorized')
@@ -59,12 +59,10 @@ def _handle_exception(context: click.Context, e: Exception):
errors: CliErrors = {
AuthProcessError: CliError(
- code='auth_error',
- message='Authentication failed. Please try again later using the command `cycode auth`'
+ code='auth_error', message='Authentication failed. Please try again later using the command `cycode auth`'
),
NetworkError: CliError(
- code='cycode_error',
- message='Authentication failed. Please try again later using the command `cycode auth`'
+ code='cycode_error', message='Authentication failed. Please try again later using the command `cycode auth`'
),
}
diff --git a/cycode/cli/auth/auth_manager.py b/cycode/cli/auth/auth_manager.py
index da2ca3b4..d8d018d8 100644
--- a/cycode/cli/auth/auth_manager.py
+++ b/cycode/cli/auth/auth_manager.py
@@ -80,11 +80,7 @@ def save_api_token(self, api_token: ApiToken):
def _build_login_url(self, code_challenge: str, session_id: str):
app_url = self.configuration_manager.get_cycode_app_url()
login_url = f'{app_url}/account/sign-in'
- query_params = {
- 'source': 'cycode_cli',
- 'code_challenge': code_challenge,
- 'session_id': session_id
- }
+ query_params = {'source': 'cycode_cli', 'code_challenge': code_challenge, 'session_id': session_id}
# TODO(MarshalX). Use auth_client instead and don't depend on "requests" lib here
request = Request(url=login_url, params=query_params)
return request.prepare().url
@@ -95,9 +91,12 @@ def _generate_pkce_code_pair(self) -> (str, str):
return code_challenge, code_verifier
def _is_api_token_process_completed(self, api_token_polling_response: ApiTokenGenerationPollingResponse) -> bool:
- return api_token_polling_response is not None \
- and api_token_polling_response.status == self.COMPLETED_POLLING_STATUS
+ return (
+ api_token_polling_response is not None
+ and api_token_polling_response.status == self.COMPLETED_POLLING_STATUS
+ )
def _is_api_token_process_failed(self, api_token_polling_response: ApiTokenGenerationPollingResponse) -> bool:
- return api_token_polling_response is not None \
- and api_token_polling_response.status == self.FAILED_POLLING_STATUS
+ return (
+ api_token_polling_response is not None and api_token_polling_response.status == self.FAILED_POLLING_STATUS
+ )
diff --git a/cycode/cli/code_scanner.py b/cycode/cli/code_scanner.py
index f2219716..47d64ccc 100644
--- a/cycode/cli/code_scanner.py
+++ b/cycode/cli/code_scanner.py
@@ -19,8 +19,14 @@
from cycode.cli.config import configuration_manager
from cycode.cli.utils.progress_bar import ProgressBarSection
from cycode.cli.utils.scan_utils import set_issue_detected
-from cycode.cli.utils.path_utils import is_sub_path, is_binary_file, get_file_size, get_relevant_files_in_path, \
- get_path_by_os, get_file_content
+from cycode.cli.utils.path_utils import (
+ is_sub_path,
+ is_binary_file,
+ get_file_size,
+ get_relevant_files_in_path,
+ get_path_by_os,
+ get_file_content,
+)
from cycode.cli.utils.scan_batch import run_parallel_batched_scan
from cycode.cli.utils.string_utils import get_content_size, is_binary_content
from cycode.cli.utils.task_timer import TimeoutAfter
@@ -43,14 +49,17 @@
@click.command()
@click.argument("path", nargs=1, type=click.STRING, required=True)
-@click.option('--branch', '-b',
- default=None,
- help='Branch to scan, if not set scanning the default branch',
- type=str,
- required=False)
+@click.option(
+ '--branch',
+ '-b',
+ default=None,
+ help='Branch to scan, if not set scanning the default branch',
+ type=str,
+ required=False,
+)
@click.pass_context
def scan_repository(context: click.Context, path: str, branch: str):
- """ Scan git repository including its history """
+ """Scan git repository including its history"""
try:
logger.debug('Starting repository scan process, %s', {'path': path, 'branch': branch})
@@ -88,19 +97,18 @@ def scan_repository(context: click.Context, path: str, branch: str):
@click.command()
-@click.argument("path",
- nargs=1,
- type=click.STRING,
- required=True)
-@click.option("--commit_range", "-r",
- help='Scan a commit range in this git repository, by default cycode scans all '
- 'commit history (example: HEAD~1)',
- type=click.STRING,
- default="--all",
- required=False)
+@click.argument("path", nargs=1, type=click.STRING, required=True)
+@click.option(
+ "--commit_range",
+ "-r",
+ help='Scan a commit range in this git repository, by default cycode scans all ' 'commit history (example: HEAD~1)',
+ type=click.STRING,
+ default="--all",
+ required=False,
+)
@click.pass_context
def scan_repository_commit_history(context: click.Context, path: str, commit_range: str):
- """ Scan all the commits history in this git repository """
+ """Scan all the commits history in this git repository"""
try:
logger.debug('Starting commit history scan process, %s', {'path': path, 'commit_range': commit_range})
return scan_commit_range(context, path=path, commit_range=commit_range)
@@ -143,20 +151,18 @@ def scan_commit_range(context: click.Context, path: str, commit_range: str, max_
commit_documents_to_scan = []
for blob in diff:
blob_path = get_path_by_os(os.path.join(path, get_diff_file_path(blob)))
- commit_documents_to_scan.append(Document(
- path=blob_path,
- content=blob.diff.decode('UTF-8', errors='replace'),
- is_git_diff_format=True,
- unique_id=commit_id
- ))
+ commit_documents_to_scan.append(
+ Document(
+ path=blob_path,
+ content=blob.diff.decode('UTF-8', errors='replace'),
+ is_git_diff_format=True,
+ unique_id=commit_id,
+ )
+ )
logger.debug(
'Found all relevant files in commit %s',
- {
- 'path': path,
- 'commit_range': commit_range,
- 'commit_id': commit_id
- }
+ {'path': path, 'commit_range': commit_range, 'commit_id': commit_id},
)
documents_to_scan.extend(exclude_irrelevant_documents_to_scan(context, commit_documents_to_scan))
@@ -171,8 +177,8 @@ def scan_commit_range(context: click.Context, path: str, commit_range: str, max_
@click.command()
@click.pass_context
def scan_ci(context: click.Context):
- """ Execute scan in a CI environment which relies on the
- CYCODE_TOKEN and CYCODE_REPO_LOCATION environment variables """
+ """Execute scan in a CI environment which relies on the
+ CYCODE_TOKEN and CYCODE_REPO_LOCATION environment variables"""
return scan_commit_range(context, path=os.getcwd(), commit_range=get_commit_range())
@@ -180,7 +186,7 @@ def scan_ci(context: click.Context):
@click.argument("path", nargs=1, type=click.STRING, required=True)
@click.pass_context
def scan_path(context: click.Context, path):
- """ Scan the files in the path supplied in the command """
+ """Scan the files in the path supplied in the command"""
logger.debug('Starting path scan process, %s', {'path': path})
files_to_scan = get_relevant_files_in_path(path=path, exclude_patterns=["**/.git/**", "**/.cycode/**"])
files_to_scan = exclude_irrelevant_files(context, files_to_scan)
@@ -192,7 +198,7 @@ def scan_path(context: click.Context, path):
@click.argument('ignored_args', nargs=-1, type=click.UNPROCESSED)
@click.pass_context
def pre_commit_scan(context: click.Context, ignored_args: List[str]):
- """ Use this command to scan the content that was not committed yet """
+ """Use this command to scan the content that was not committed yet"""
scan_type = context.obj['scan_type']
progress_bar = context.obj['progress_bar']
@@ -216,7 +222,7 @@ def pre_commit_scan(context: click.Context, ignored_args: List[str]):
@click.argument("ignored_args", nargs=-1, type=click.UNPROCESSED)
@click.pass_context
def pre_receive_scan(context: click.Context, ignored_args: List[str]):
- """ Use this command to scan commits on the server side before pushing them to the repository """
+ """Use this command to scan commits on the server side before pushing them to the repository"""
try:
scan_type = context.obj['scan_type']
if scan_type != consts.SECRET_SCAN_TYPE:
@@ -225,7 +231,8 @@ def pre_receive_scan(context: click.Context, ignored_args: List[str]):
if should_skip_pre_receive_scan():
logger.info(
"A scan has been skipped as per your request."
- " Please note that this may leave your system vulnerable to secrets that have not been detected")
+ " Please note that this may leave your system vulnerable to secrets that have not been detected"
+ )
return
if is_verbose_mode_requested_in_pre_receive_scan():
@@ -242,8 +249,7 @@ def pre_receive_scan(context: click.Context, ignored_args: List[str]):
commit_range = calculate_pre_receive_commit_range(branch_update_details)
if not commit_range:
logger.info(
- 'No new commits found for pushed branch, %s',
- {'branch_update_details': branch_update_details}
+ 'No new commits found for pushed branch, %s', {'branch_update_details': branch_update_details}
)
return
@@ -260,9 +266,13 @@ def scan_sca_pre_commit(context: click.Context):
git_head_documents = exclude_irrelevant_documents_to_scan(context, git_head_documents)
pre_committed_documents = exclude_irrelevant_documents_to_scan(context, pre_committed_documents)
sca_code_scanner.perform_pre_hook_range_scan_actions(git_head_documents, pre_committed_documents)
- return scan_commit_range_documents(context, git_head_documents, pre_committed_documents,
- scan_parameters,
- configuration_manager.get_sca_pre_commit_timeout_in_seconds())
+ return scan_commit_range_documents(
+ context,
+ git_head_documents,
+ pre_committed_documents,
+ scan_parameters,
+ configuration_manager.get_sca_pre_commit_timeout_in_seconds(),
+ )
def scan_sca_commit_range(context: click.Context, path: str, commit_range: str):
@@ -275,11 +285,13 @@ def scan_sca_commit_range(context: click.Context, path: str, commit_range: str):
)
from_commit_documents = exclude_irrelevant_documents_to_scan(context, from_commit_documents)
to_commit_documents = exclude_irrelevant_documents_to_scan(context, to_commit_documents)
- sca_code_scanner.perform_pre_commit_range_scan_actions(path, from_commit_documents, from_commit_rev,
- to_commit_documents, to_commit_rev)
+ sca_code_scanner.perform_pre_commit_range_scan_actions(
+ path, from_commit_documents, from_commit_rev, to_commit_documents, to_commit_rev
+ )
- return scan_commit_range_documents(context, from_commit_documents, to_commit_documents,
- scan_parameters=scan_parameters)
+ return scan_commit_range_documents(
+ context, from_commit_documents, to_commit_documents, scan_parameters=scan_parameters
+ )
def scan_disk_files(context: click.Context, path: str, files_to_scan: List[str]):
@@ -310,7 +322,7 @@ def set_issue_detected_by_scan_results(context: click.Context, scan_results: Lis
def _get_scan_documents_thread_func(
- context: click.Context, is_git_diff: bool, is_commit_range: bool, scan_parameters: dict
+ context: click.Context, is_git_diff: bool, is_commit_range: bool, scan_parameters: dict
) -> Callable[[List[Document]], Tuple[str, CliError, LocalScanResult]]:
cycode_client = context.obj['client']
scan_type = context.obj['scan_type']
@@ -353,12 +365,20 @@ def _scan_batch_thread_func(batch: List[Document]) -> Tuple[str, CliError, Local
'all_violations_count': detections_count,
'relevant_violations_count': relevant_detections_count,
'scan_id': scan_id,
- 'zip_file_size': zip_file_size
- }
+ 'zip_file_size': zip_file_size,
+ },
)
_report_scan_status(
- cycode_client, scan_type, scan_id, scan_completed, relevant_detections_count,
- detections_count, len(batch), zip_file_size, command_scan_type, error_message
+ cycode_client,
+ scan_type,
+ scan_id,
+ scan_completed,
+ relevant_detections_count,
+ detections_count,
+ len(batch),
+ zip_file_size,
+ command_scan_type,
+ error_message,
)
return scan_id, error, local_scan_result
@@ -367,11 +387,11 @@ def _scan_batch_thread_func(batch: List[Document]) -> Tuple[str, CliError, Local
def scan_documents(
- context: click.Context,
- documents_to_scan: List[Document],
- is_git_diff: bool = False,
- is_commit_range: bool = False,
- scan_parameters: Optional[dict] = None,
+ context: click.Context,
+ documents_to_scan: List[Document],
+ is_git_diff: bool = False,
+ is_commit_range: bool = False,
+ scan_parameters: Optional[dict] = None,
) -> None:
progress_bar = context.obj['progress_bar']
@@ -399,7 +419,7 @@ def scan_documents(
click.secho(
'Unfortunately, Cycode was unable to complete the full scan. '
'Please note that not all results may be available:',
- fg='red'
+ fg='red',
)
for scan_id, error in errors.items():
click.echo(f'- {scan_id}: ', nl=False)
@@ -407,11 +427,11 @@ def scan_documents(
def scan_commit_range_documents(
- context: click.Context,
- from_documents_to_scan: List[Document],
- to_documents_to_scan: List[Document],
- scan_parameters: Optional[dict] = None,
- timeout: Optional[int] = None
+ context: click.Context,
+ from_documents_to_scan: List[Document],
+ to_documents_to_scan: List[Document],
+ scan_parameters: Optional[dict] = None,
+ timeout: Optional[int] = None,
) -> None:
cycode_client = context.obj['client']
scan_type = context.obj['scan_type']
@@ -442,8 +462,12 @@ def scan_commit_range_documents(
)
scan_result = perform_commit_range_scan_async(
- cycode_client, from_commit_zipped_documents, to_commit_zipped_documents,
- scan_type, scan_parameters, timeout
+ cycode_client,
+ from_commit_zipped_documents,
+ to_commit_zipped_documents,
+ scan_type,
+ scan_parameters,
+ timeout,
)
progress_bar.update(ProgressBarSection.SCAN)
@@ -464,8 +488,9 @@ def scan_commit_range_documents(
_handle_exception(context, e)
error_message = str(e)
- zip_file_size = getsizeof(from_commit_zipped_documents.in_memory_zip) + \
- getsizeof(to_commit_zipped_documents.in_memory_zip)
+ zip_file_size = getsizeof(from_commit_zipped_documents.in_memory_zip) + getsizeof(
+ to_commit_zipped_documents.in_memory_zip
+ )
detections_count = relevant_detections_count = 0
if local_scan_result:
@@ -479,13 +504,20 @@ def scan_commit_range_documents(
'all_violations_count': detections_count,
'relevant_violations_count': relevant_detections_count,
'scan_id': scan_id,
- 'zip_file_size': zip_file_size
- }
+ 'zip_file_size': zip_file_size,
+ },
)
_report_scan_status(
- cycode_client, scan_type, local_scan_result.scan_id, scan_completed,
- local_scan_result.relevant_detections_count, local_scan_result.detections_count, len(to_documents_to_scan),
- zip_file_size, scan_command_type, error_message
+ cycode_client,
+ scan_type,
+ local_scan_result.scan_id,
+ scan_completed,
+ local_scan_result.relevant_detections_count,
+ local_scan_result.detections_count,
+ len(to_documents_to_scan),
+ zip_file_size,
+ scan_command_type,
+ error_message,
)
@@ -494,11 +526,11 @@ def should_scan_documents(from_documents_to_scan: List[Document], to_documents_t
def create_local_scan_result(
- scan_result: ZippedFileScanResult,
- documents_to_scan: List[Document],
- command_scan_type: str,
- scan_type: str,
- severity_threshold: str,
+ scan_result: ZippedFileScanResult,
+ documents_to_scan: List[Document],
+ command_scan_type: str,
+ scan_type: str,
+ severity_threshold: str,
) -> LocalScanResult:
document_detections = get_document_detections(scan_result, documents_to_scan)
relevant_document_detections_list = exclude_irrelevant_document_detections(
@@ -516,12 +548,12 @@ def create_local_scan_result(
document_detections=relevant_document_detections_list,
issue_detected=len(relevant_document_detections_list) > 0,
detections_count=detections_count,
- relevant_detections_count=relevant_detections_count
+ relevant_detections_count=relevant_detections_count,
)
def perform_pre_scan_documents_actions(
- context: click.Context, scan_type: str, documents_to_scan: List[Document], is_git_diff: bool = False
+ context: click.Context, scan_type: str, documents_to_scan: List[Document], is_git_diff: bool = False
) -> None:
if scan_type == consts.SCA_SCAN_TYPE:
logger.debug(f'Perform pre scan document actions')
@@ -535,8 +567,9 @@ def zip_documents_to_scan(scan_type: str, zip_file: InMemoryZip, documents: List
zip_file_size = getsizeof(zip_file.in_memory_zip)
validate_zip_file_size(scan_type, zip_file_size)
- logger.debug('adding file to zip, %s',
- {'index': index, 'filename': document.path, 'unique_id': document.unique_id})
+ logger.debug(
+ 'adding file to zip, %s', {'index': index, 'filename': document.path, 'unique_id': document.unique_id}
+ )
zip_file.append(document.path, document.unique_id, document.content)
zip_file.close()
@@ -556,13 +589,13 @@ def validate_zip_file_size(scan_type: str, zip_file_size: int) -> None:
def perform_scan(
- cycode_client: 'ScanClient',
- zipped_documents: InMemoryZip,
- scan_type: str,
- scan_id: str,
- is_git_diff: bool,
- is_commit_range: bool,
- scan_parameters: dict
+ cycode_client: 'ScanClient',
+ zipped_documents: InMemoryZip,
+ scan_type: str,
+ scan_id: str,
+ is_git_diff: bool,
+ is_commit_range: bool,
+ scan_parameters: dict,
) -> ZippedFileScanResult:
if scan_type in (consts.SCA_SCAN_TYPE, consts.SAST_SCAN_TYPE):
return perform_scan_async(cycode_client, zipped_documents, scan_type, scan_parameters)
@@ -574,10 +607,7 @@ def perform_scan(
def perform_scan_async(
- cycode_client: 'ScanClient',
- zipped_documents: InMemoryZip,
- scan_type: str,
- scan_parameters: dict
+ cycode_client: 'ScanClient', zipped_documents: InMemoryZip, scan_type: str, scan_parameters: dict
) -> ZippedFileScanResult:
scan_async_result = cycode_client.zipped_file_scan_async(zipped_documents, scan_type, scan_parameters)
logger.debug("scan request has been triggered successfully, scan id: %s", scan_async_result.scan_id)
@@ -586,12 +616,12 @@ def perform_scan_async(
def perform_commit_range_scan_async(
- cycode_client: 'ScanClient',
- from_commit_zipped_documents: InMemoryZip,
- to_commit_zipped_documents: InMemoryZip,
- scan_type: str,
- scan_parameters: dict,
- timeout: int = None
+ cycode_client: 'ScanClient',
+ from_commit_zipped_documents: InMemoryZip,
+ to_commit_zipped_documents: InMemoryZip,
+ scan_type: str,
+ scan_parameters: dict,
+ timeout: int = None,
) -> ZippedFileScanResult:
scan_async_result = cycode_client.multiple_zipped_file_scan_async(
from_commit_zipped_documents, to_commit_zipped_documents, scan_type, scan_parameters
@@ -602,7 +632,7 @@ def perform_commit_range_scan_async(
def poll_scan_results(
- cycode_client: 'ScanClient', scan_id: str, polling_timeout: Optional[int] = None
+ cycode_client: 'ScanClient', scan_id: str, polling_timeout: Optional[int] = None
) -> ZippedFileScanResult:
if polling_timeout is None:
polling_timeout = configuration_manager.get_scan_polling_timeout_in_seconds()
@@ -643,7 +673,7 @@ def print_results(context: click.Context, local_scan_results: List[LocalScanResu
def get_document_detections(
- scan_result: ZippedFileScanResult, documents_to_scan: List[Document]
+ scan_result: ZippedFileScanResult, documents_to_scan: List[Document]
) -> List[DocumentDetections]:
logger.debug('Get document detections')
@@ -655,18 +685,13 @@ def get_document_detections(
logger.debug('Going to find document of violated file, %s', {'file_name': file_name, 'commit_id': commit_id})
document = _get_document_by_file_name(documents_to_scan, file_name, commit_id)
- document_detections.append(
- DocumentDetections(document=document, detections=detections_per_file.detections)
- )
+ document_detections.append(DocumentDetections(document=document, detections=detections_per_file.detections))
return document_detections
def exclude_irrelevant_document_detections(
- document_detections_list: List[DocumentDetections],
- scan_type: str,
- command_scan_type: str,
- severity_threshold: str
+ document_detections_list: List[DocumentDetections], scan_type: str, command_scan_type: str, severity_threshold: str
) -> List[DocumentDetections]:
relevant_document_detections_list = []
for document_detections in document_detections_list:
@@ -698,7 +723,8 @@ def parse_pre_receive_input() -> str:
pre_receive_input = sys.stdin.read().strip()
if not pre_receive_input:
raise ValueError(
- "Pre receive input was not found. Make sure that you are using this command only in pre-receive hook")
+ "Pre receive input was not found. Make sure that you are using this command only in pre-receive hook"
+ )
# each line represents a branch update request, handle the first one only
# TODO(MichalBor): support case of multiple update branch requests
@@ -759,7 +785,7 @@ def get_default_scan_parameters(context: click.Context) -> dict:
"monitor": context.obj.get("monitor"),
"report": context.obj.get("report"),
"package_vulnerabilities": context.obj.get("package-vulnerabilities"),
- "license_compliance": context.obj.get("license-compliance")
+ "license_compliance": context.obj.get("license-compliance"),
}
@@ -784,9 +810,7 @@ def try_get_git_remote_url(path: str) -> Optional[dict]:
return None
-def exclude_irrelevant_documents_to_scan(
- context: click.Context, documents_to_scan: List[Document]
-) -> List[Document]:
+def exclude_irrelevant_documents_to_scan(context: click.Context, documents_to_scan: List[Document]) -> List[Document]:
logger.debug('Excluding irrelevant documents to scan')
scan_type = context.obj['scan_type']
@@ -811,7 +835,7 @@ def exclude_irrelevant_files(context: click.Context, filenames: List[str]) -> Li
def exclude_irrelevant_detections(
- detections: List[Detection], scan_type: str, command_scan_type: str, severity_threshold: str
+ detections: List[Detection], scan_type: str, command_scan_type: str, severity_threshold: str
) -> List[Detection]:
relevant_detections = _exclude_detections_by_exclusions_configuration(detections, scan_type)
relevant_detections = _exclude_detections_by_scan_type(relevant_detections, scan_type, command_scan_type)
@@ -821,7 +845,7 @@ def exclude_irrelevant_detections(
def _exclude_detections_by_severity(
- detections: List[Detection], scan_type: str, severity_threshold: str
+ detections: List[Detection], scan_type: str, severity_threshold: str
) -> List[Detection]:
if scan_type != consts.SCA_SCAN_TYPE or severity_threshold is None:
return detections
@@ -836,7 +860,7 @@ def _exclude_detections_by_severity(
def _exclude_detections_by_scan_type(
- detections: List[Detection], scan_type: str, command_scan_type: str
+ detections: List[Detection], scan_type: str, command_scan_type: str
) -> List[Detection]:
if command_scan_type == consts.PRE_COMMIT_COMMAND_SCAN_TYPE:
return exclude_detections_in_deleted_lines(detections)
@@ -883,7 +907,7 @@ def get_pre_commit_modified_documents(progress_bar: 'BaseProgressBar') -> Tuple[
def get_commit_range_modified_documents(
- progress_bar: 'BaseProgressBar', path: str, from_commit_rev: str, to_commit_rev: str
+ progress_bar: 'BaseProgressBar', path: str, from_commit_rev: str, to_commit_rev: str
) -> Tuple[List[Document], List[Document]]:
from_commit_documents = []
to_commit_documents = []
@@ -915,30 +939,37 @@ def get_commit_range_modified_documents(
def _should_exclude_detection(detection: Detection, exclusions: Dict) -> bool:
exclusions_by_value = exclusions.get(consts.EXCLUSIONS_BY_VALUE_SECTION_NAME, [])
if _is_detection_sha_configured_in_exclusions(detection, exclusions_by_value):
- logger.debug('Going to ignore violations because is in the values to ignore list, %s',
- {'sha': detection.detection_details.get('sha512', '')})
+ logger.debug(
+ 'Going to ignore violations because is in the values to ignore list, %s',
+ {'sha': detection.detection_details.get('sha512', '')},
+ )
return True
exclusions_by_sha = exclusions.get(consts.EXCLUSIONS_BY_SHA_SECTION_NAME, [])
if _is_detection_sha_configured_in_exclusions(detection, exclusions_by_sha):
- logger.debug('Going to ignore violations because is in the shas to ignore list, %s',
- {'sha': detection.detection_details.get('sha512', '')})
+ logger.debug(
+ 'Going to ignore violations because is in the shas to ignore list, %s',
+ {'sha': detection.detection_details.get('sha512', '')},
+ )
return True
exclusions_by_rule = exclusions.get(consts.EXCLUSIONS_BY_RULE_SECTION_NAME, [])
if exclusions_by_rule:
detection_rule = detection.detection_rule_id
if detection_rule in exclusions_by_rule:
- logger.debug('Going to ignore violations because is in the shas to ignore list, %s',
- {'detection_rule': detection_rule})
+ logger.debug(
+ 'Going to ignore violations because is in the shas to ignore list, %s',
+ {'detection_rule': detection_rule},
+ )
return True
exclusions_by_package = exclusions.get(consts.EXCLUSIONS_BY_PACKAGE_SECTION_NAME, [])
if exclusions_by_package:
package = _get_package_name(detection)
if package in exclusions_by_package:
- logger.debug('Going to ignore violations because is in the packages to ignore list, %s',
- {'package': package})
+ logger.debug(
+ 'Going to ignore violations because is in the packages to ignore list, %s', {'package': package}
+ )
return True
return False
@@ -950,8 +981,9 @@ def _is_detection_sha_configured_in_exclusions(detection, exclusions: List[str])
def _is_path_configured_in_exclusions(scan_type: str, file_path: str) -> bool:
- exclusions_by_path = \
- configuration_manager.get_exclusions_by_scan_type(scan_type).get(consts.EXCLUSIONS_BY_PATH_SECTION_NAME, [])
+ exclusions_by_path = configuration_manager.get_exclusions_by_scan_type(scan_type).get(
+ consts.EXCLUSIONS_BY_PATH_SECTION_NAME, []
+ )
for exclusion_path in exclusions_by_path:
if is_sub_path(exclusion_path, file_path):
return True
@@ -971,10 +1003,7 @@ def _get_package_name(detection: Detection) -> str:
def _is_file_relevant_for_sca_scan(filename: str) -> bool:
if any([sca_excluded_path in filename for sca_excluded_path in consts.SCA_EXCLUDED_PATHS]):
- logger.debug(
- "file is irrelevant because it is from node_modules's inner path, %s",
- {'filename': filename}
- )
+ logger.debug("file is irrelevant because it is from node_modules's inner path, %s", {'filename': filename})
return False
return True
@@ -982,28 +1011,23 @@ def _is_file_relevant_for_sca_scan(filename: str) -> bool:
def _is_relevant_file_to_scan(scan_type: str, filename: str) -> bool:
if _is_subpath_of_cycode_configuration_folder(filename):
- logger.debug("file is irrelevant because it is in cycode configuration directory, %s",
- {'filename': filename})
+ logger.debug("file is irrelevant because it is in cycode configuration directory, %s", {'filename': filename})
return False
if _is_path_configured_in_exclusions(scan_type, filename):
- logger.debug("file is irrelevant because the file path is in the ignore paths list, %s",
- {'filename': filename})
+ logger.debug("file is irrelevant because the file path is in the ignore paths list, %s", {'filename': filename})
return False
if not _is_file_extension_supported(scan_type, filename):
- logger.debug("file is irrelevant because the file extension is not supported, %s",
- {'filename': filename})
+ logger.debug("file is irrelevant because the file extension is not supported, %s", {'filename': filename})
return False
if is_binary_file(filename):
- logger.debug("file is irrelevant because it is binary file, %s",
- {'filename': filename})
+ logger.debug("file is irrelevant because it is binary file, %s", {'filename': filename})
return False
if scan_type != consts.SCA_SCAN_TYPE and _does_file_exceed_max_size_limit(filename):
- logger.debug("file is irrelevant because its exceeded max size limit, %s",
- {'filename': filename})
+ logger.debug("file is irrelevant because its exceeded max size limit, %s", {'filename': filename})
return False
if scan_type == consts.SCA_SCAN_TYPE and not _is_file_relevant_for_sca_scan(filename):
@@ -1014,28 +1038,27 @@ def _is_relevant_file_to_scan(scan_type: str, filename: str) -> bool:
def _is_relevant_document_to_scan(scan_type: str, filename: str, content: str) -> bool:
if _is_subpath_of_cycode_configuration_folder(filename):
- logger.debug("document is irrelevant because it is in cycode configuration directory, %s",
- {'filename': filename})
+ logger.debug(
+ "document is irrelevant because it is in cycode configuration directory, %s", {'filename': filename}
+ )
return False
if _is_path_configured_in_exclusions(scan_type, filename):
- logger.debug("document is irrelevant because the document path is in the ignore paths list, %s",
- {'filename': filename})
+ logger.debug(
+ "document is irrelevant because the document path is in the ignore paths list, %s", {'filename': filename}
+ )
return False
if not _is_file_extension_supported(scan_type, filename):
- logger.debug("document is irrelevant because the file extension is not supported, %s",
- {'filename': filename})
+ logger.debug("document is irrelevant because the file extension is not supported, %s", {'filename': filename})
return False
if is_binary_content(content):
- logger.debug("document is irrelevant because it is binary, %s",
- {'filename': filename})
+ logger.debug("document is irrelevant because it is binary, %s", {'filename': filename})
return False
if scan_type != consts.SCA_SCAN_TYPE and _does_document_exceed_max_size_limit(content):
- logger.debug("document is irrelevant because its exceeded max size limit, %s",
- {'filename': filename})
+ logger.debug("document is irrelevant because its exceeded max size limit, %s", {'filename': filename})
return False
return True
@@ -1044,14 +1067,19 @@ def _is_file_extension_supported(scan_type: str, filename: str) -> bool:
filename = filename.lower()
if scan_type == consts.INFRA_CONFIGURATION_SCAN_TYPE:
- return any(filename.endswith(supported_file_extension)
- for supported_file_extension in consts.INFRA_CONFIGURATION_SCAN_SUPPORTED_FILES)
+ return any(
+ filename.endswith(supported_file_extension)
+ for supported_file_extension in consts.INFRA_CONFIGURATION_SCAN_SUPPORTED_FILES
+ )
elif scan_type == consts.SCA_SCAN_TYPE:
- return any(filename.endswith(supported_file)
- for supported_file in consts.SCA_CONFIGURATION_SCAN_SUPPORTED_FILES)
+ return any(
+ filename.endswith(supported_file) for supported_file in consts.SCA_CONFIGURATION_SCAN_SUPPORTED_FILES
+ )
- return all(not filename.endswith(file_extension_to_ignore)
- for file_extension_to_ignore in consts.SECRET_SCAN_FILE_EXTENSIONS_TO_IGNORE)
+ return all(
+ not filename.endswith(file_extension_to_ignore)
+ for file_extension_to_ignore in consts.SECRET_SCAN_FILE_EXTENSIONS_TO_IGNORE
+ )
def _does_file_exceed_max_size_limit(filename: str) -> bool:
@@ -1063,7 +1091,7 @@ def _does_document_exceed_max_size_limit(content: str) -> bool:
def _get_document_by_file_name(
- documents: List[Document], file_name: str, unique_id: Optional[str] = None
+ documents: List[Document], file_name: str, unique_id: Optional[str] = None
) -> Optional[Document]:
for document in documents:
if _normalize_file_path(document.path) == _normalize_file_path(file_name) and document.unique_id == unique_id:
@@ -1073,9 +1101,11 @@ def _get_document_by_file_name(
def _is_subpath_of_cycode_configuration_folder(filename: str) -> bool:
- return is_sub_path(configuration_manager.global_config_file_manager.get_config_directory_path(), filename) \
- or is_sub_path(configuration_manager.local_config_file_manager.get_config_directory_path(), filename) \
+ return (
+ is_sub_path(configuration_manager.global_config_file_manager.get_config_directory_path(), filename)
+ or is_sub_path(configuration_manager.local_config_file_manager.get_config_directory_path(), filename)
or filename.endswith(ConfigFileManager.get_config_file_route())
+ )
def _handle_exception(context: click.Context, e: Exception, *, return_exception: bool = False) -> Optional[CliError]:
@@ -1089,32 +1119,32 @@ def _handle_exception(context: click.Context, e: Exception, *, return_exception:
soft_fail=True,
code='cycode_error',
message='Cycode was unable to complete this scan. '
- 'Please try again by executing the `cycode scan` command'
+ 'Please try again by executing the `cycode scan` command',
),
custom_exceptions.ScanAsyncError: CliError(
soft_fail=True,
code='scan_error',
message='Cycode was unable to complete this scan. '
- 'Please try again by executing the `cycode scan` command'
+ 'Please try again by executing the `cycode scan` command',
),
custom_exceptions.HttpUnauthorizedError: CliError(
soft_fail=True,
code='auth_error',
message='Unable to authenticate to Cycode, your token is either invalid or has expired. '
- 'Please re-generate your token and reconfigure it by running the `cycode configure` command'
+ 'Please re-generate your token and reconfigure it by running the `cycode configure` command',
),
custom_exceptions.ZipTooLargeError: CliError(
soft_fail=True,
code='zip_too_large_error',
message='The path you attempted to scan exceeds the current maximum scanning size cap (10MB). '
- 'Please try ignoring irrelevant paths using the ‘cycode ignore --by-path’ command '
- 'and execute the scan again'
+ 'Please try ignoring irrelevant paths using the ‘cycode ignore --by-path’ command '
+ 'and execute the scan again',
),
InvalidGitRepositoryError: CliError(
soft_fail=False,
code='invalid_git_error',
message='The path you supplied does not correlate to a git repository. '
- 'Should you still wish to scan this path, use: ‘cycode scan path ’'
+ 'Should you still wish to scan this path, use: ‘cycode scan path ’',
),
}
@@ -1139,9 +1169,18 @@ def _handle_exception(context: click.Context, e: Exception, *, return_exception:
raise click.ClickException(str(e))
-def _report_scan_status(cycode_client: 'ScanClient', scan_type: str, scan_id: str, scan_completed: bool,
- output_detections_count: int, all_detections_count: int, files_to_scan_count: int,
- zip_size: int, command_scan_type: str, error_message: Optional[str]) -> None:
+def _report_scan_status(
+ cycode_client: 'ScanClient',
+ scan_type: str,
+ scan_id: str,
+ scan_completed: bool,
+ output_detections_count: int,
+ all_detections_count: int,
+ files_to_scan_count: int,
+ zip_size: int,
+ command_scan_type: str,
+ error_message: Optional[str],
+) -> None:
try:
end_scan_time = time.time()
scan_status = {
@@ -1154,7 +1193,7 @@ def _report_scan_status(cycode_client: 'ScanClient', scan_type: str, scan_id: st
'scan_command_type': command_scan_type,
'operation_system': platform(),
'error_message': error_message,
- 'scan_type': scan_type
+ 'scan_type': scan_type,
}
cycode_client.report_scan_status(scan_type, scan_id, scan_status)
@@ -1175,7 +1214,7 @@ def _does_severity_match_severity_threshold(severity: str, severity_threshold: s
def _get_scan_result(
- cycode_client: 'ScanClient', scan_id: str, scan_details: 'ScanDetailsResponse'
+ cycode_client: 'ScanClient', scan_id: str, scan_details: 'ScanDetailsResponse'
) -> ZippedFileScanResult:
if not scan_details.detections_count:
return init_default_scan_result(scan_id, scan_details.metadata)
@@ -1187,16 +1226,13 @@ def _get_scan_result(
did_detect=True,
detections_per_file=_map_detections_per_file(scan_detections),
scan_id=scan_id,
- report_url=_try_get_report_url(scan_details.metadata)
+ report_url=_try_get_report_url(scan_details.metadata),
)
def init_default_scan_result(scan_id: str, scan_metadata: Optional[str] = None) -> ZippedFileScanResult:
return ZippedFileScanResult(
- did_detect=False,
- detections_per_file=[],
- scan_id=scan_id,
- report_url=_try_get_report_url(scan_metadata)
+ did_detect=False, detections_per_file=[], scan_id=scan_id, report_url=_try_get_report_url(scan_metadata)
)
@@ -1253,8 +1289,10 @@ def _map_detections_per_file(detections: List[dict]) -> List[DetectionsPerFile]:
logger.debug("Failed to parse detection: %s", str(e))
continue
- return [DetectionsPerFile(file_name=file_name, detections=file_detections)
- for file_name, file_detections in detections_per_files.items()]
+ return [
+ DetectionsPerFile(file_name=file_name, detections=file_detections)
+ for file_name, file_detections in detections_per_files.items()
+ ]
def _get_file_name_from_detection(detection: dict) -> str:
diff --git a/cycode/cli/consts.py b/cycode/cli/consts.py
index 1959d4ae..f7e4a834 100644
--- a/cycode/cli/consts.py
+++ b/cycode/cli/consts.py
@@ -7,32 +7,75 @@
SCA_SCAN_TYPE = "sca"
SAST_SCAN_TYPE = "sast"
-INFRA_CONFIGURATION_SCAN_SUPPORTED_FILES = [
- '.tf', '.tf.json', '.json', '.yaml', '.yml', 'dockerfile'
-]
+INFRA_CONFIGURATION_SCAN_SUPPORTED_FILES = ['.tf', '.tf.json', '.json', '.yaml', '.yml', 'dockerfile']
SECRET_SCAN_FILE_EXTENSIONS_TO_IGNORE = [
- '.7z', '.bmp', '.bz2', '.dmg', '.exe', '.gif', '.gz', '.ico', '.jar', '.jpg', '.jpeg', '.png', '.rar',
- '.realm', '.s7z', '.svg', '.tar', '.tif', '.tiff', '.webp', '.zi', '.lock', '.css', '.less', '.dll',
- '.enc', '.deb', '.obj', '.model'
+ '.7z',
+ '.bmp',
+ '.bz2',
+ '.dmg',
+ '.exe',
+ '.gif',
+ '.gz',
+ '.ico',
+ '.jar',
+ '.jpg',
+ '.jpeg',
+ '.png',
+ '.rar',
+ '.realm',
+ '.s7z',
+ '.svg',
+ '.tar',
+ '.tif',
+ '.tiff',
+ '.webp',
+ '.zi',
+ '.lock',
+ '.css',
+ '.less',
+ '.dll',
+ '.enc',
+ '.deb',
+ '.obj',
+ '.model',
]
SCA_CONFIGURATION_SCAN_SUPPORTED_FILES = [
- 'cargo.lock', 'cargo.toml',
- 'composer.json', 'composer.lock',
- 'go.sum', 'go.mod', 'gopkg.lock',
- 'pom.xml', 'build.gradle', 'gradle.lockfile', 'build.gradle.kts',
- 'package.json', 'package-lock.json', 'yarn.lock', 'npm-shrinkwrap.json',
- 'packages.config', 'project.assets.json', 'packages.lock.json', 'nuget.config', '.csproj',
- 'gemfile', 'gemfile.lock',
- 'build.sbt', 'build.scala', 'build.sbt.lock',
- 'pyproject.toml', 'poetry.lock',
- 'pipfile', 'pipfile.lock', 'requirements.txt', 'setup.py'
+ 'cargo.lock',
+ 'cargo.toml',
+ 'composer.json',
+ 'composer.lock',
+ 'go.sum',
+ 'go.mod',
+ 'gopkg.lock',
+ 'pom.xml',
+ 'build.gradle',
+ 'gradle.lockfile',
+ 'build.gradle.kts',
+ 'package.json',
+ 'package-lock.json',
+ 'yarn.lock',
+ 'npm-shrinkwrap.json',
+ 'packages.config',
+ 'project.assets.json',
+ 'packages.lock.json',
+ 'nuget.config',
+ '.csproj',
+ 'gemfile',
+ 'gemfile.lock',
+ 'build.sbt',
+ 'build.scala',
+ 'build.sbt.lock',
+ 'pyproject.toml',
+ 'poetry.lock',
+ 'pipfile',
+ 'pipfile.lock',
+ 'requirements.txt',
+ 'setup.py',
]
-SCA_EXCLUDED_PATHS = [
- 'node_modules'
-]
+SCA_EXCLUDED_PATHS = ['node_modules']
PROJECT_FILES_BY_ECOSYSTEM_MAP = {
"crates": ["Cargo.lock", "Cargo.toml"],
@@ -47,7 +90,7 @@
"pypi_poetry": ["pyproject.toml", "poetry.lock"],
"pypi_pipenv": ["Pipfile", "Pipfile.lock"],
"pypi_requirements": ["requirements.txt"],
- "pypi_setup": ["setup.py"]
+ "pypi_setup": ["setup.py"],
}
COMMIT_RANGE_SCAN_SUPPORTED_SCAN_TYPES = [SECRET_SCAN_TYPE, SCA_SCAN_TYPE]
diff --git a/cycode/cli/exceptions/custom_exceptions.py b/cycode/cli/exceptions/custom_exceptions.py
index d80cf26a..8ae2236f 100644
--- a/cycode/cli/exceptions/custom_exceptions.py
+++ b/cycode/cli/exceptions/custom_exceptions.py
@@ -13,8 +13,10 @@ def __init__(self, status_code: int, error_message: str, response: Response):
super().__init__(self.error_message)
def __str__(self):
- return f'error occurred during the request. status code: {self.status_code}, error message: ' \
- f'{self.error_message}'
+ return (
+ f'error occurred during the request. status code: {self.status_code}, error message: '
+ f'{self.error_message}'
+ )
class ScanAsyncError(CycodeError):
diff --git a/cycode/cli/helpers/maven/base_restore_maven_dependencies.py b/cycode/cli/helpers/maven/base_restore_maven_dependencies.py
index 484df810..42bd9cc7 100644
--- a/cycode/cli/helpers/maven/base_restore_maven_dependencies.py
+++ b/cycode/cli/helpers/maven/base_restore_maven_dependencies.py
@@ -17,17 +17,14 @@ def execute_command(command: List[str], file_name: str, command_timeout: int) ->
try:
dependencies = shell(command, command_timeout)
except Exception as e:
- logger.debug('Failed to restore dependencies shell comment. %s',
- {'filename': file_name, 'exception': str(e)})
+ logger.debug('Failed to restore dependencies shell comment. %s', {'filename': file_name, 'exception': str(e)})
return None
return dependencies
class BaseRestoreMavenDependencies(ABC):
-
- def __init__(self, context: click.Context, is_git_diff: bool,
- command_timeout: int):
+ def __init__(self, context: click.Context, is_git_diff: bool, command_timeout: int):
self.context = context
self.is_git_diff = is_git_diff
self.command_timeout = command_timeout
@@ -37,8 +34,11 @@ def restore(self, document: Document) -> Optional[Document]:
return restore_dependencies_document
def get_manifest_file_path(self, document: Document) -> str:
- return join_paths(self.context.params.get('path'), document.path) if self.context.obj.get(
- 'monitor') else document.path
+ return (
+ join_paths(self.context.params.get('path'), document.path)
+ if self.context.obj.get('monitor')
+ else document.path
+ )
@abstractmethod
def is_project(self, document: Document) -> bool:
@@ -54,8 +54,9 @@ def get_lock_file_name(self) -> str:
def try_restore_dependencies(self, document: Document) -> Optional[Document]:
manifest_file_path = self.get_manifest_file_path(document)
- document = Document(build_dep_tree_path(document.path, self.get_lock_file_name()),
- execute_command(self.get_command(manifest_file_path), manifest_file_path,
- self.command_timeout),
- self.is_git_diff)
+ document = Document(
+ build_dep_tree_path(document.path, self.get_lock_file_name()),
+ execute_command(self.get_command(manifest_file_path), manifest_file_path, self.command_timeout),
+ self.is_git_diff,
+ )
return document
diff --git a/cycode/cli/helpers/maven/restore_gradle_dependencies.py b/cycode/cli/helpers/maven/restore_gradle_dependencies.py
index 1e61ee7f..6a60faad 100644
--- a/cycode/cli/helpers/maven/restore_gradle_dependencies.py
+++ b/cycode/cli/helpers/maven/restore_gradle_dependencies.py
@@ -11,8 +11,7 @@
class RestoreGradleDependencies(BaseRestoreMavenDependencies):
- def __init__(self, context: click.Context, is_git_diff: bool,
- command_timeout: int):
+ def __init__(self, context: click.Context, is_git_diff: bool, command_timeout: int):
super().__init__(context, is_git_diff, command_timeout)
def is_project(self, document: Document) -> bool:
diff --git a/cycode/cli/helpers/maven/restore_maven_dependencies.py b/cycode/cli/helpers/maven/restore_maven_dependencies.py
index 8ab21ca3..51e2aa96 100644
--- a/cycode/cli/helpers/maven/restore_maven_dependencies.py
+++ b/cycode/cli/helpers/maven/restore_maven_dependencies.py
@@ -3,8 +3,11 @@
import click
-from cycode.cli.helpers.maven.base_restore_maven_dependencies import BaseRestoreMavenDependencies, build_dep_tree_path, \
- execute_command
+from cycode.cli.helpers.maven.base_restore_maven_dependencies import (
+ BaseRestoreMavenDependencies,
+ build_dep_tree_path,
+ execute_command,
+)
from cycode.cli.models import Document
from cycode.cli.utils.path_utils import get_file_dir, get_file_content, join_paths
@@ -14,8 +17,7 @@
class RestoreMavenDependencies(BaseRestoreMavenDependencies):
- def __init__(self, context: click.Context, is_git_diff: bool,
- command_timeout: int):
+ def __init__(self, context: click.Context, is_git_diff: bool, command_timeout: int):
super().__init__(context, is_git_diff, command_timeout)
def is_project(self, document: Document) -> bool:
@@ -31,24 +33,23 @@ def try_restore_dependencies(self, document: Document) -> Optional[Document]:
restore_dependencies_document = super().try_restore_dependencies(document)
manifest_file_path = self.get_manifest_file_path(document)
if document.content is None:
- restore_dependencies_document = self.restore_from_secondary_command(document, manifest_file_path,
- restore_dependencies_document)
+ restore_dependencies_document = self.restore_from_secondary_command(
+ document, manifest_file_path, restore_dependencies_document
+ )
else:
restore_dependencies_document.content = get_file_content(
- join_paths(get_file_dir(manifest_file_path), self.get_lock_file_name()))
+ join_paths(get_file_dir(manifest_file_path), self.get_lock_file_name())
+ )
return restore_dependencies_document
def restore_from_secondary_command(self, document, manifest_file_path, restore_dependencies_document):
# TODO(MarshalX): does it even work? Missing argument
secondary_restore_command = create_secondary_restore_command(manifest_file_path)
- backup_restore_content = execute_command(
- secondary_restore_command,
- manifest_file_path,
- self.command_timeout)
- restore_dependencies_document = Document(build_dep_tree_path(document.path, MAVEN_DEP_TREE_FILE_NAME),
- backup_restore_content,
- self.is_git_diff)
+ backup_restore_content = execute_command(secondary_restore_command, manifest_file_path, self.command_timeout)
+ restore_dependencies_document = Document(
+ build_dep_tree_path(document.path, MAVEN_DEP_TREE_FILE_NAME), backup_restore_content, self.is_git_diff
+ )
restore_dependencies = None
if restore_dependencies_document.content is not None:
restore_dependencies = restore_dependencies_document
@@ -58,5 +59,12 @@ def restore_from_secondary_command(self, document, manifest_file_path, restore_d
def create_secondary_restore_command(self, manifest_file_path):
- return ['mvn', 'dependency:tree', '-B', '-DoutputType=text', '-f', manifest_file_path,
- f'-DoutputFile={MAVEN_DEP_TREE_FILE_NAME}']
+ return [
+ 'mvn',
+ 'dependency:tree',
+ '-B',
+ '-DoutputType=text',
+ '-f',
+ manifest_file_path,
+ f'-DoutputFile={MAVEN_DEP_TREE_FILE_NAME}',
+ ]
diff --git a/cycode/cli/helpers/sca_code_scanner.py b/cycode/cli/helpers/sca_code_scanner.py
index e12342fd..cbd040c7 100644
--- a/cycode/cli/helpers/sca_code_scanner.py
+++ b/cycode/cli/helpers/sca_code_scanner.py
@@ -17,23 +17,29 @@
BUILD_GRADLE_DEP_TREE_TIMEOUT = 180
-def perform_pre_commit_range_scan_actions(path: str, from_commit_documents: List[Document],
- from_commit_rev: str, to_commit_documents: List[Document],
- to_commit_rev: str) -> None:
+def perform_pre_commit_range_scan_actions(
+ path: str,
+ from_commit_documents: List[Document],
+ from_commit_rev: str,
+ to_commit_documents: List[Document],
+ to_commit_rev: str,
+) -> None:
repo = Repo(path)
add_ecosystem_related_files_if_exists(from_commit_documents, repo, from_commit_rev)
add_ecosystem_related_files_if_exists(to_commit_documents, repo, to_commit_rev)
-def perform_pre_hook_range_scan_actions(git_head_documents: List[Document],
- pre_committed_documents: List[Document]) -> None:
+def perform_pre_hook_range_scan_actions(
+ git_head_documents: List[Document], pre_committed_documents: List[Document]
+) -> None:
repo = Repo(os.getcwd())
add_ecosystem_related_files_if_exists(git_head_documents, repo, GIT_HEAD_COMMIT_REV)
add_ecosystem_related_files_if_exists(pre_committed_documents)
-def add_ecosystem_related_files_if_exists(documents: List[Document], repo: Optional[Repo] = None,
- commit_rev: Optional[str] = None):
+def add_ecosystem_related_files_if_exists(
+ documents: List[Document], repo: Optional[Repo] = None, commit_rev: Optional[str] = None
+):
for doc in documents:
ecosystem = get_project_file_ecosystem(doc)
if ecosystem is None:
@@ -43,14 +49,18 @@ def add_ecosystem_related_files_if_exists(documents: List[Document], repo: Optio
documents.extend(documents_to_add)
-def get_doc_ecosystem_related_project_files(doc: Document, documents: List[Document], ecosystem: str,
- commit_rev: Optional[str], repo: Optional[Repo]) -> List[Document]:
+def get_doc_ecosystem_related_project_files(
+ doc: Document, documents: List[Document], ecosystem: str, commit_rev: Optional[str], repo: Optional[Repo]
+) -> List[Document]:
documents_to_add: List[Document] = []
for ecosystem_project_file in PROJECT_FILES_BY_ECOSYSTEM_MAP.get(ecosystem):
file_to_search = join_paths(get_file_dir(doc.path), ecosystem_project_file)
if not is_project_file_exists_in_documents(documents, file_to_search):
- file_content = get_file_content_from_commit(repo, commit_rev, file_to_search) if repo \
+ file_content = (
+ get_file_content_from_commit(repo, commit_rev, file_to_search)
+ if repo
else get_file_content(file_to_search)
+ )
if file_content is not None:
documents_to_add.append(Document(file_to_search, file_content))
@@ -70,18 +80,17 @@ def get_project_file_ecosystem(document: Document) -> Optional[str]:
return None
-def try_restore_dependencies(context: click.Context, documents_to_add: List[Document], restore_dependencies,
- document: Document):
+def try_restore_dependencies(
+ context: click.Context, documents_to_add: List[Document], restore_dependencies, document: Document
+):
if restore_dependencies.is_project(document):
restore_dependencies_document = restore_dependencies.restore(document)
if restore_dependencies_document is None:
- logger.warning('Error occurred while trying to generate dependencies tree. %s',
- {'filename': document.path})
+ logger.warning('Error occurred while trying to generate dependencies tree. %s', {'filename': document.path})
return
if restore_dependencies_document.content is None:
- logger.warning('Error occurred while trying to generate dependencies tree. %s',
- {'filename': document.path})
+ logger.warning('Error occurred while trying to generate dependencies tree. %s', {'filename': document.path})
restore_dependencies_document.content = ''
else:
is_monitor_action = context.obj.get('monitor')
@@ -95,8 +104,9 @@ def try_restore_dependencies(context: click.Context, documents_to_add: List[Docu
documents_to_add[restore_dependencies_document.path] = restore_dependencies_document
-def add_dependencies_tree_document(context: click.Context, documents_to_scan: List[Document],
- is_git_diff: bool = False) -> None:
+def add_dependencies_tree_document(
+ context: click.Context, documents_to_scan: List[Document], is_git_diff: bool = False
+) -> None:
documents_to_add: Dict[str, Document] = {}
restore_dependencies_list = restore_handlers(context, is_git_diff)
@@ -110,7 +120,7 @@ def add_dependencies_tree_document(context: click.Context, documents_to_scan: Li
def restore_handlers(context, is_git_diff):
return [
RestoreGradleDependencies(context, is_git_diff, BUILD_GRADLE_DEP_TREE_TIMEOUT),
- RestoreMavenDependencies(context, is_git_diff, BUILD_GRADLE_DEP_TREE_TIMEOUT)
+ RestoreMavenDependencies(context, is_git_diff, BUILD_GRADLE_DEP_TREE_TIMEOUT),
]
diff --git a/cycode/cli/main.py b/cycode/cli/main.py
index 4e52edb3..946c1c8b 100644
--- a/cycode/cli/main.py
+++ b/cycode/cli/main.py
@@ -34,71 +34,100 @@
"commit_history": code_scanner.scan_repository_commit_history,
"path": code_scanner.scan_path,
"pre_commit": code_scanner.pre_commit_scan,
- "pre_receive": code_scanner.pre_receive_scan
+ "pre_receive": code_scanner.pre_receive_scan,
},
)
-@click.option('--scan-type', '-t', default="secret",
- help="""
+@click.option(
+ '--scan-type',
+ '-t',
+ default="secret",
+ help="""
\b
Specify the scan you wish to execute (secret/iac/sca),
the default is secret
""",
- type=click.Choice(config['scans']['supported_scans']))
-@click.option('--secret',
- default=None,
- help='Specify a Cycode client secret for this specific scan execution',
- type=str,
- required=False)
-@click.option('--client-id',
- default=None,
- help='Specify a Cycode client ID for this specific scan execution',
- type=str,
- required=False)
-@click.option('--show-secret',
- is_flag=True,
- default=False,
- help='Show secrets in plain text',
- type=bool,
- required=False)
-@click.option('--soft-fail',
- is_flag=True,
- default=False,
- help='Run scan without failing, always return a non-error status code',
- type=bool,
- required=False)
-@click.option('--output', default=None,
- help="""
+ type=click.Choice(config['scans']['supported_scans']),
+)
+@click.option(
+ '--secret',
+ default=None,
+ help='Specify a Cycode client secret for this specific scan execution',
+ type=str,
+ required=False,
+)
+@click.option(
+ '--client-id',
+ default=None,
+ help='Specify a Cycode client ID for this specific scan execution',
+ type=str,
+ required=False,
+)
+@click.option(
+ '--show-secret', is_flag=True, default=False, help='Show secrets in plain text', type=bool, required=False
+)
+@click.option(
+ '--soft-fail',
+ is_flag=True,
+ default=False,
+ help='Run scan without failing, always return a non-error status code',
+ type=bool,
+ required=False,
+)
+@click.option(
+ '--output',
+ default=None,
+ help="""
\b
Specify the results output (text/json/table),
the default is text
""",
- type=click.Choice(['text', 'json', 'table']))
-@click.option('--severity-threshold',
- default=None,
- help='Show only violations at the specified level or higher (supported for SCA scan type only).',
- type=click.Choice([e.name for e in Severity]),
- required=False)
-@click.option('--sca-scan',
- default=None,
- help="Specify the sca scan you wish to execute (package-vulnerabilities/license-compliance), the default is both",
- multiple=True,
- type=click.Choice(config['scans']['supported_sca_scans']))
-@click.option('--monitor',
- is_flag=True,
- default=False,
- help="When specified, the scan results will be recorded in the knowledge graph. Please note that when working in 'monitor' mode, the knowledge graph will not be updated as a result of SCM events (Push, Repo creation).(supported for SCA scan type only).",
- type=bool,
- required=False)
-@click.option('--report',
- is_flag=True,
- default=False,
- help="When specified, a violations report will be generated. A URL link to the report will be printed as an output to the command execution",
- type=bool,
- required=False)
+ type=click.Choice(['text', 'json', 'table']),
+)
+@click.option(
+ '--severity-threshold',
+ default=None,
+ help='Show only violations at the specified level or higher (supported for SCA scan type only).',
+ type=click.Choice([e.name for e in Severity]),
+ required=False,
+)
+@click.option(
+ '--sca-scan',
+ default=None,
+ help="Specify the sca scan you wish to execute (package-vulnerabilities/license-compliance), the default is both",
+ multiple=True,
+ type=click.Choice(config['scans']['supported_sca_scans']),
+)
+@click.option(
+ '--monitor',
+ is_flag=True,
+ default=False,
+ help="When specified, the scan results will be recorded in the knowledge graph. Please note that when working in 'monitor' mode, the knowledge graph will not be updated as a result of SCM events (Push, Repo creation).(supported for SCA scan type only).",
+ type=bool,
+ required=False,
+)
+@click.option(
+ '--report',
+ is_flag=True,
+ default=False,
+ help="When specified, a violations report will be generated. A URL link to the report will be printed as an output to the command execution",
+ type=bool,
+ required=False,
+)
@click.pass_context
-def code_scan(context: click.Context, scan_type, client_id, secret, show_secret, soft_fail, output, severity_threshold,
- sca_scan: List[str], monitor, report):
- """ Scan content for secrets/IaC/sca/SAST violations, You need to specify which scan type: ci/commit_history/path/repository/etc """
+def code_scan(
+ context: click.Context,
+ scan_type,
+ client_id,
+ secret,
+ show_secret,
+ soft_fail,
+ output,
+ severity_threshold,
+ sca_scan: List[str],
+ monitor,
+ report,
+):
+ """Scan content for secrets/IaC/sca/SAST violations, You need to specify which scan type: ci/commit_history/path/repository/etc"""
if show_secret:
context.obj["show_secret"] = show_secret
else:
@@ -148,25 +177,27 @@ def finalize(context: click.Context, *_, **__):
@click.group(
- commands={
- "scan": code_scan,
- "configure": set_credentials,
- "ignore": add_exclusions,
- "auth": authenticate
- },
- context_settings=CONTEXT
+ commands={"scan": code_scan, "configure": set_credentials, "ignore": add_exclusions, "auth": authenticate},
+ context_settings=CONTEXT,
)
@click.option(
- "--verbose", "-v", is_flag=True, default=False, help="Show detailed logs",
+ "--verbose",
+ "-v",
+ is_flag=True,
+ default=False,
+ help="Show detailed logs",
)
@click.option(
- '--no-progress-meter', is_flag=True, default=False, help='Do not show the progress meter',
+ '--no-progress-meter',
+ is_flag=True,
+ default=False,
+ help='Do not show the progress meter',
)
@click.option(
'--output',
default='text',
help='Specify the output (text/json/table), the default is text',
- type=click.Choice(['text', 'json', 'table'])
+ type=click.Choice(['text', 'json', 'table']),
)
@click.option(
'--user-agent',
diff --git a/cycode/cli/models.py b/cycode/cli/models.py
index 94218175..051b2fa7 100644
--- a/cycode/cli/models.py
+++ b/cycode/cli/models.py
@@ -12,10 +12,7 @@ def __init__(self, path: str, content: str, is_git_diff_format: bool = False, un
self.unique_id = unique_id
def __repr__(self) -> str:
- return (
- "path:{0}, "
- "content:{1}".format(self.path, self.content)
- )
+ return "path:{0}, " "content:{1}".format(self.path, self.content)
class DocumentDetections:
@@ -24,10 +21,7 @@ def __init__(self, document: Document, detections: List[Detection]):
self.detections = detections
def __repr__(self) -> str:
- return (
- "document:{0}, "
- "detections:{1}".format(self.document, self.detections)
- )
+ return "document:{0}, " "detections:{1}".format(self.document, self.detections)
class Severity(Enum):
diff --git a/cycode/cli/printers/json_printer.py b/cycode/cli/printers/json_printer.py
index c02eff5b..6469100c 100644
--- a/cycode/cli/printers/json_printer.py
+++ b/cycode/cli/printers/json_printer.py
@@ -13,18 +13,12 @@
class JsonPrinter(BasePrinter):
def print_result(self, result: CliResult) -> None:
- result = {
- 'result': result.success,
- 'message': result.message
- }
+ result = {'result': result.success, 'message': result.message}
click.secho(self.get_data_json(result))
def print_error(self, error: CliError) -> None:
- result = {
- 'error': error.code,
- 'message': error.message
- }
+ result = {'error': error.code, 'message': error.message}
click.secho(self.get_data_json(result))
@@ -40,8 +34,8 @@ def print_scan_results(self, local_scan_results: List['LocalScanResult']) -> Non
def _get_json_scan_result(self, detections: dict) -> str:
result = {
- 'scan_id': 'DEPRECATED', # FIXME(MarshalX): we need change JSON struct to support multiple scan results
- 'detections': detections
+ 'scan_id': 'DEPRECATED', # FIXME(MarshalX): we need change JSON struct to support multiple scan results
+ 'detections': detections,
}
return self.get_data_json(result)
diff --git a/cycode/cli/printers/sca_table_printer.py b/cycode/cli/printers/sca_table_printer.py
index 051a2e56..a8372873 100644
--- a/cycode/cli/printers/sca_table_printer.py
+++ b/cycode/cli/printers/sca_table_printer.py
@@ -35,7 +35,7 @@ def _print_results(self, local_scan_results: List['LocalScanResult']) -> None:
@staticmethod
def _extract_detections_per_detection_type_id(
- local_scan_results: List['LocalScanResult']
+ local_scan_results: List['LocalScanResult'],
) -> Dict[str, List[Detection]]:
detections_per_detection_type_id = defaultdict(list)
@@ -47,7 +47,7 @@ def _extract_detections_per_detection_type_id(
return detections_per_detection_type_id
def _print_detection_per_detection_type_id(
- self, detections_per_detection_type_id: Dict[str, List[Detection]]
+ self, detections_per_detection_type_id: Dict[str, List[Detection]]
) -> None:
for detection_type_id in detections_per_detection_type_id:
detections = detections_per_detection_type_id[detection_type_id]
@@ -84,9 +84,7 @@ def _get_table_headers(self) -> list:
return []
- def _print_table_detections(
- self, detections: List[Detection], headers: List[str], rows, title: str
- ) -> None:
+ def _print_table_detections(self, detections: List[Detection], headers: List[str], rows, title: str) -> None:
self._print_summary_issues(detections, title)
text_table = Texttable()
text_table.header(headers)
@@ -127,7 +125,7 @@ def _get_common_detection_fields(self, detection: Detection) -> List[str]:
detection.detection_details.get('package_name'),
detection.detection_details.get('is_direct_dependency_str'),
detection.detection_details.get('is_dev_dependency_str'),
- dependency_paths
+ dependency_paths,
]
if self._is_git_repository():
@@ -140,7 +138,7 @@ def _get_upgrade_package_vulnerability(self, detection: Detection) -> List[str]:
row = [
detection.detection_details.get('advisory_severity'),
*self._get_common_detection_fields(detection),
- detection.detection_details.get('vulnerability_id')
+ detection.detection_details.get('vulnerability_id'),
]
upgrade = ''
diff --git a/cycode/cli/printers/table_printer.py b/cycode/cli/printers/table_printer.py
index 12f8f61b..3e5e6d49 100644
--- a/cycode/cli/printers/table_printer.py
+++ b/cycode/cli/printers/table_printer.py
@@ -91,7 +91,7 @@ def _enrich_table_with_values(self, table: Table, detection: Detection, document
self._enrich_table_with_detection_code_segment_values(table, detection, document)
def _enrich_table_with_detection_summary_values(
- self, table: Table, detection: Detection, document: Document
+ self, table: Table, detection: Detection, document: Document
) -> None:
issue_type = detection.message
if self.scan_type == SECRET_SCAN_TYPE:
@@ -104,7 +104,7 @@ def _enrich_table_with_detection_summary_values(
table.set(COMMIT_SHA_COLUMN, detection.detection_details.get('commit_id', ''))
def _enrich_table_with_detection_code_segment_values(
- self, table: Table, detection: Detection, document: Document
+ self, table: Table, detection: Detection, document: Document
) -> None:
detection_details = detection.detection_details
@@ -119,7 +119,7 @@ def _enrich_table_with_detection_code_segment_values(
file_content_lines = document.content.splitlines()
if detection_line < len(file_content_lines):
line = file_content_lines[detection_line]
- violation = line[detection_column: detection_column + violation_length]
+ violation = line[detection_column : detection_column + violation_length]
if not self.show_secret:
violation = obfuscate_text(violation)
diff --git a/cycode/cli/printers/text_printer.py b/cycode/cli/printers/text_printer.py
index 2d25af2f..de71371d 100644
--- a/cycode/cli/printers/text_printer.py
+++ b/cycode/cli/printers/text_printer.py
@@ -42,7 +42,7 @@ def print_scan_results(self, local_scan_results: List['LocalScanResult']):
)
def _print_document_detections(
- self, document_detections: DocumentDetections, scan_id: str, report_url: Optional[str]
+ self, document_detections: DocumentDetections, scan_id: str, report_url: Optional[str]
):
document = document_detections.document
lines_to_display = self._get_lines_to_display_count()
@@ -51,7 +51,7 @@ def _print_document_detections(
self._print_detection_code_segment(detection, document, lines_to_display)
def _print_detection_summary(
- self, detection: Detection, document_path: str, scan_id: str, report_url: Optional[str]
+ self, detection: Detection, document_path: str, scan_id: str, report_url: Optional[str]
):
detection_name = detection.type if self.scan_type == SECRET_SCAN_TYPE else detection.message
@@ -81,15 +81,23 @@ def _get_code_segment_start_line(self, detection_line: int, code_segment_size: i
start_line = detection_line - math.ceil(code_segment_size / 2)
return 0 if start_line < 0 else start_line
- def _print_line_of_code_segment(self, document: Document, line: str, line_number: int,
- detection_position_in_line: int, violation_length: int, is_detection_line: bool):
+ def _print_line_of_code_segment(
+ self,
+ document: Document,
+ line: str,
+ line_number: int,
+ detection_position_in_line: int,
+ violation_length: int,
+ is_detection_line: bool,
+ ):
if is_detection_line:
self._print_detection_line(document, line, line_number, detection_position_in_line, violation_length)
else:
self._print_line(document, line, line_number)
- def _print_detection_line(self, document: Document, line: str, line_number: int, detection_position_in_line: int,
- violation_length: int) -> None:
+ def _print_detection_line(
+ self, document: Document, line: str, line_number: int, detection_position_in_line: int, violation_length: int
+ ) -> None:
click.echo(
f'{self._get_line_number_style(line_number)} '
f'{self._get_detection_line_style(line, document.is_git_diff_format, detection_position_in_line, violation_length)}'
@@ -106,19 +114,21 @@ def _get_detection_line_style(self, line: str, is_git_diff: bool, start_position
if self.scan_type != SECRET_SCAN_TYPE or start_position < 0 or length < 0:
return self._get_line_style(line, is_git_diff, line_color)
- violation = line[start_position: start_position + length]
+ violation = line[start_position : start_position + length]
if not self.show_secret:
violation = obfuscate_text(violation)
- line_to_violation = line[0: start_position]
- line_from_violation = line[start_position + length:]
+ line_to_violation = line[0:start_position]
+ line_from_violation = line[start_position + length :]
- return f'{self._get_line_style(line_to_violation, is_git_diff, line_color)}' \
- f'{self._get_line_style(violation, is_git_diff, line_color, underline=True)}' \
- f'{self._get_line_style(line_from_violation, is_git_diff, line_color)}'
+ return (
+ f'{self._get_line_style(line_to_violation, is_git_diff, line_color)}'
+ f'{self._get_line_style(violation, is_git_diff, line_color, underline=True)}'
+ f'{self._get_line_style(line_from_violation, is_git_diff, line_color)}'
+ )
def _get_line_style(
- self, line: str, is_git_diff: bool, color: Optional[str] = None, underline: bool = False
+ self, line: str, is_git_diff: bool, color: Optional[str] = None, underline: bool = False
) -> str:
if color is None:
color = self._get_line_color(line, is_git_diff)
@@ -138,13 +148,16 @@ def _get_line_color(self, line: str, is_git_diff: bool) -> str:
return self.WHITE_COLOR_NAME
def _get_line_number_style(self, line_number: int):
- return f'{click.style(str(line_number), fg=self.WHITE_COLOR_NAME, bold=False)} ' \
- f'{click.style("|", fg=self.RED_COLOR_NAME, bold=False)}'
+ return (
+ f'{click.style(str(line_number), fg=self.WHITE_COLOR_NAME, bold=False)} '
+ f'{click.style("|", fg=self.RED_COLOR_NAME, bold=False)}'
+ )
def _get_lines_to_display_count(self) -> int:
result_printer_configuration = config.get('result_printer')
- lines_to_display_of_scan = result_printer_configuration.get(self.scan_type, {}) \
- .get(self.command_scan_type, {}).get('lines_to_display')
+ lines_to_display_of_scan = (
+ result_printer_configuration.get(self.scan_type, {}).get(self.command_scan_type, {}).get('lines_to_display')
+ )
if lines_to_display_of_scan:
return lines_to_display_of_scan
@@ -152,8 +165,11 @@ def _get_lines_to_display_count(self) -> int:
def _print_detection_from_file(self, detection: Detection, document: Document, code_segment_size: int):
detection_details = detection.detection_details
- detection_line = detection_details.get('line', -1) if self.scan_type == SECRET_SCAN_TYPE else \
- detection_details.get('line_in_file', -1)
+ detection_line = (
+ detection_details.get('line', -1)
+ if self.scan_type == SECRET_SCAN_TYPE
+ else detection_details.get('line_in_file', -1)
+ )
detection_position = detection_details.get('start_position', -1)
violation_length = detection_details.get('length', -1)
@@ -170,8 +186,14 @@ def _print_detection_from_file(self, detection: Detection, document: Document, c
current_line = file_lines[current_line_index]
is_detection_line = current_line_index == detection_line
- self._print_line_of_code_segment(document, current_line, current_line_index + 1, detection_position_in_line,
- violation_length, is_detection_line)
+ self._print_line_of_code_segment(
+ document,
+ current_line,
+ current_line_index + 1,
+ detection_position_in_line,
+ violation_length,
+ is_detection_line,
+ )
click.echo()
def _print_detection_from_git_diff(self, detection: Detection, document: Document):
@@ -187,8 +209,13 @@ def _print_detection_from_git_diff(self, detection: Detection, document: Documen
detection_position_in_line = get_position_in_line(git_diff_content, detection_position)
click.echo()
- self._print_detection_line(document, detection_line, detection_line_number_in_original_file,
- detection_position_in_line, violation_length)
+ self._print_detection_line(
+ document,
+ detection_line,
+ detection_line_number_in_original_file,
+ detection_position_in_line,
+ violation_length,
+ )
click.echo()
def _is_git_diff_based_scan(self):
diff --git a/cycode/cli/user_settings/base_file_manager.py b/cycode/cli/user_settings/base_file_manager.py
index 22c4fffc..ec7c4813 100644
--- a/cycode/cli/user_settings/base_file_manager.py
+++ b/cycode/cli/user_settings/base_file_manager.py
@@ -4,7 +4,6 @@
class BaseFileManager(ABC):
-
@abstractmethod
def get_filename(self):
pass
diff --git a/cycode/cli/user_settings/config_file_manager.py b/cycode/cli/user_settings/config_file_manager.py
index 7c99f033..876f85f1 100644
--- a/cycode/cli/user_settings/config_file_manager.py
+++ b/cycode/cli/user_settings/config_file_manager.py
@@ -46,26 +46,19 @@ def get_command_timeout(self, command_scan_type) -> Optional[int]:
return self._get_value_from_command_scan_type_configuration(command_scan_type, self.COMMAND_TIMEOUT_FIELD_NAME)
def get_exclude_detections_in_deleted_lines(self, command_scan_type) -> Optional[bool]:
- return self._get_value_from_command_scan_type_configuration(command_scan_type,
- self.EXCLUDE_DETECTIONS_IN_DELETED_LINES)
+ return self._get_value_from_command_scan_type_configuration(
+ command_scan_type, self.EXCLUDE_DETECTIONS_IN_DELETED_LINES
+ )
def update_base_url(self, base_url: str):
- update_data = {
- self.ENVIRONMENT_SECTION_NAME: {
- self.API_URL_FIELD_NAME: base_url
- }
- }
+ update_data = {self.ENVIRONMENT_SECTION_NAME: {self.API_URL_FIELD_NAME: base_url}}
self.write_content_to_file(update_data)
def get_installation_id(self) -> Optional[str]:
return self._get_value_from_environment_section(self.INSTALLATION_ID_FIELD_NAME)
def update_installation_id(self, installation_id: str) -> None:
- update_data = {
- self.ENVIRONMENT_SECTION_NAME: {
- self.INSTALLATION_ID_FIELD_NAME: installation_id
- }
- }
+ update_data = {self.ENVIRONMENT_SECTION_NAME: {self.INSTALLATION_ID_FIELD_NAME: installation_id}}
self.write_content_to_file(update_data)
def add_exclusion(self, scan_type, exclusion_type, new_exclusion):
@@ -75,13 +68,7 @@ def add_exclusion(self, scan_type, exclusion_type, new_exclusion):
exclusions.append(new_exclusion)
- update_data = {
- self.EXCLUSIONS_SECTION_NAME: {
- scan_type: {
- exclusion_type: exclusions
- }
- }
- }
+ update_data = {self.EXCLUSIONS_SECTION_NAME: {scan_type: {exclusion_type: exclusions}}}
self.write_content_to_file(update_data)
def get_config_directory_path(self) -> str:
diff --git a/cycode/cli/user_settings/configuration_manager.py b/cycode/cli/user_settings/configuration_manager.py
index 3769a77f..fa11c87a 100644
--- a/cycode/cli/user_settings/configuration_manager.py
+++ b/cycode/cli/user_settings/configuration_manager.py
@@ -95,12 +95,18 @@ def get_config_file_manager(self, scope: Optional[str] = None) -> ConfigFileMana
return self.global_config_file_manager
def get_scan_polling_timeout_in_seconds(self) -> int:
- return int(self._get_value_from_environment_variables(SCAN_POLLING_TIMEOUT_IN_SECONDS_ENV_VAR_NAME,
- DEFAULT_SCAN_POLLING_TIMEOUT_IN_SECONDS))
+ return int(
+ self._get_value_from_environment_variables(
+ SCAN_POLLING_TIMEOUT_IN_SECONDS_ENV_VAR_NAME, DEFAULT_SCAN_POLLING_TIMEOUT_IN_SECONDS
+ )
+ )
def get_sca_pre_commit_timeout_in_seconds(self) -> int:
- return int(self._get_value_from_environment_variables(SCA_PRE_COMMIT_TIMEOUT_IN_SECONDS_ENV_VAR_NAME,
- DEFAULT_SCA_PRE_COMMIT_TIMEOUT_IN_SECONDS))
+ return int(
+ self._get_value_from_environment_variables(
+ SCA_PRE_COMMIT_TIMEOUT_IN_SECONDS_ENV_VAR_NAME, DEFAULT_SCA_PRE_COMMIT_TIMEOUT_IN_SECONDS
+ )
+ )
def get_pre_receive_max_commits_to_scan_count(self, command_scan_type: str) -> int:
max_commits = self._get_value_from_environment_variables(PRE_RECEIVE_MAX_COMMITS_TO_SCAN_COUNT_ENV_VAR_NAME)
@@ -134,17 +140,20 @@ def get_pre_receive_command_timeout(self, command_scan_type: str) -> int:
def get_should_exclude_detections_in_deleted_lines(self, command_scan_type: str) -> bool:
exclude_detections_in_deleted_lines = self._get_value_from_environment_variables(
- EXCLUDE_DETECTIONS_IN_DELETED_LINES_ENV_VAR_NAME)
+ EXCLUDE_DETECTIONS_IN_DELETED_LINES_ENV_VAR_NAME
+ )
if exclude_detections_in_deleted_lines is not None:
return exclude_detections_in_deleted_lines.lower() in ('true', '1')
- exclude_detections_in_deleted_lines = self.local_config_file_manager \
- .get_exclude_detections_in_deleted_lines(command_scan_type)
+ exclude_detections_in_deleted_lines = self.local_config_file_manager.get_exclude_detections_in_deleted_lines(
+ command_scan_type
+ )
if exclude_detections_in_deleted_lines is not None:
return exclude_detections_in_deleted_lines
- exclude_detections_in_deleted_lines = self.global_config_file_manager\
- .get_exclude_detections_in_deleted_lines(command_scan_type)
+ exclude_detections_in_deleted_lines = self.global_config_file_manager.get_exclude_detections_in_deleted_lines(
+ command_scan_type
+ )
if exclude_detections_in_deleted_lines is not None:
return exclude_detections_in_deleted_lines
diff --git a/cycode/cli/user_settings/credentials_manager.py b/cycode/cli/user_settings/credentials_manager.py
index 67d31275..675deae2 100644
--- a/cycode/cli/user_settings/credentials_manager.py
+++ b/cycode/cli/user_settings/credentials_manager.py
@@ -7,7 +7,6 @@
class CredentialsManager(BaseFileManager):
-
HOME_PATH: str = Path.home()
CYCODE_HIDDEN_DIRECTORY: str = '.cycode'
FILE_NAME: str = 'credentials.yaml'
@@ -38,10 +37,7 @@ def get_credentials_from_file(self) -> (str, str):
return client_id, client_secret
def update_credentials_file(self, client_id: str, client_secret: str):
- credentials = {
- self.CLIENT_ID_FIELD_NAME: client_id,
- self.CLIENT_SECRET_FIELD_NAME: client_secret
- }
+ credentials = {self.CLIENT_ID_FIELD_NAME: client_id, self.CLIENT_SECRET_FIELD_NAME: client_secret}
filename = self.get_filename()
self.write_content_to_file(credentials)
diff --git a/cycode/cli/user_settings/user_settings_commands.py b/cycode/cli/user_settings/user_settings_commands.py
index 24ebb0e9..a7863671 100644
--- a/cycode/cli/user_settings/user_settings_commands.py
+++ b/cycode/cli/user_settings/user_settings_commands.py
@@ -12,16 +12,18 @@
from cycode.cyclient import logger
CREDENTIALS_UPDATED_SUCCESSFULLY_MESSAGE = 'Successfully configured CLI credentials!'
-CREDENTIALS_ARE_SET_IN_ENVIRONMENT_VARIABLES_MESSAGE = 'Note that the credentials that already exist in environment' \
- ' variables (CYCODE_CLIENT_ID and CYCODE_CLIENT_SECRET) take' \
- ' precedent over these credentials; either update or remove ' \
- 'the environment variables.'
+CREDENTIALS_ARE_SET_IN_ENVIRONMENT_VARIABLES_MESSAGE = (
+ 'Note that the credentials that already exist in environment'
+ ' variables (CYCODE_CLIENT_ID and CYCODE_CLIENT_SECRET) take'
+ ' precedent over these credentials; either update or remove '
+ 'the environment variables.'
+)
credentials_manager = CredentialsManager()
@click.command()
def set_credentials():
- """ Initial command to authenticate your CLI client with Cycode using client ID and client secret """
+ """Initial command to authenticate your CLI client with Cycode using client ID and client secret"""
click.echo(f'Update credentials in file ({credentials_manager.get_filename()})')
current_client_id, current_client_secret = credentials_manager.get_credentials_from_file()
client_id = _get_client_id_input(current_client_id)
@@ -35,28 +37,55 @@ def set_credentials():
@click.command()
-@click.option("--by-value", type=click.STRING, required=False,
- help="Ignore a specific value while scanning for secrets")
-@click.option("--by-sha", type=click.STRING, required=False,
- help='Ignore a specific SHA512 representation of a string while scanning for secrets')
-@click.option("--by-path", type=click.STRING, required=False,
- help='Avoid scanning a specific path. Need to specify scan type ')
-@click.option("--by-rule", type=click.STRING, required=False,
- help='Ignore scanning a specific secret rule ID/IaC rule ID. Need to specify scan type.')
-@click.option("--by-package", type=click.STRING, required=False,
- help='Ignore scanning a specific package version while running SCA scan. expected pattern - name@version')
-@click.option('--scan-type', '-t', default='secret',
- help="""
+@click.option(
+ "--by-value", type=click.STRING, required=False, help="Ignore a specific value while scanning for secrets"
+)
+@click.option(
+ "--by-sha",
+ type=click.STRING,
+ required=False,
+ help='Ignore a specific SHA512 representation of a string while scanning for secrets',
+)
+@click.option(
+ "--by-path", type=click.STRING, required=False, help='Avoid scanning a specific path. Need to specify scan type '
+)
+@click.option(
+ "--by-rule",
+ type=click.STRING,
+ required=False,
+ help='Ignore scanning a specific secret rule ID/IaC rule ID. Need to specify scan type.',
+)
+@click.option(
+ "--by-package",
+ type=click.STRING,
+ required=False,
+ help='Ignore scanning a specific package version while running SCA scan. expected pattern - name@version',
+)
+@click.option(
+ '--scan-type',
+ '-t',
+ default='secret',
+ help="""
\b
Specify the scan you wish to execute (secrets/iac),
the default is secrets
""",
- type=click.Choice(config['scans']['supported_scans']), required=False)
-@click.option('--global', '-g', 'is_global', is_flag=True, default=False, required=False,
- help='Add an ignore rule and update it in the global .cycode config file')
-def add_exclusions(by_value: str, by_sha: str, by_path: str, by_rule: str, by_package: str, scan_type: str,
- is_global: bool):
- """ Ignore a specific value, path or rule ID """
+ type=click.Choice(config['scans']['supported_scans']),
+ required=False,
+)
+@click.option(
+ '--global',
+ '-g',
+ 'is_global',
+ is_flag=True,
+ default=False,
+ required=False,
+ help='Add an ignore rule and update it in the global .cycode config file',
+)
+def add_exclusions(
+ by_value: str, by_sha: str, by_path: str, by_rule: str, by_package: str, scan_type: str, is_global: bool
+):
+ """Ignore a specific value, path or rule ID"""
if not by_value and not by_sha and not by_path and not by_rule and not by_package:
raise click.ClickException("ignore by type is missing")
@@ -88,24 +117,29 @@ def add_exclusions(by_value: str, by_sha: str, by_path: str, by_rule: str, by_pa
exclusion_value = by_rule
configuration_scope = 'global' if is_global else 'local'
- logger.debug('Adding ignore rule, %s',
- {'configuration_scope': configuration_scope, 'exclusion_type': exclusion_type,
- 'exclusion_value': exclusion_value})
+ logger.debug(
+ 'Adding ignore rule, %s',
+ {
+ 'configuration_scope': configuration_scope,
+ 'exclusion_type': exclusion_type,
+ 'exclusion_value': exclusion_value,
+ },
+ )
configuration_manager.add_exclusion(configuration_scope, scan_type, exclusion_type, exclusion_value)
def _get_client_id_input(current_client_id: str) -> str:
- new_client_id = click.prompt(f'cycode client id [{_obfuscate_credential(current_client_id)}]',
- default='',
- show_default=False)
+ new_client_id = click.prompt(
+ f'cycode client id [{_obfuscate_credential(current_client_id)}]', default='', show_default=False
+ )
return current_client_id if not new_client_id else new_client_id
def _get_client_secret_input(current_client_secret: str) -> str:
- new_client_secret = click.prompt(f'cycode client secret [{_obfuscate_credential(current_client_secret)}]',
- default='',
- show_default=False)
+ new_client_secret = click.prompt(
+ f'cycode client secret [{_obfuscate_credential(current_client_secret)}]', default='', show_default=False
+ )
return current_client_secret if not new_client_secret else new_client_secret
@@ -121,8 +155,9 @@ def _are_credentials_exist_in_environment_variables():
return client_id is not None or client_secret is not None
-def _should_update_credentials(current_client_id: str, current_client_secret: str, new_client_id: str,
- new_client_secret: str) -> bool:
+def _should_update_credentials(
+ current_client_id: str, current_client_secret: str, new_client_id: str, new_client_secret: str
+) -> bool:
return current_client_id != new_client_id or current_client_secret != new_client_secret
diff --git a/cycode/cli/utils/progress_bar.py b/cycode/cli/utils/progress_bar.py
index 196ca9e9..010405ef 100644
--- a/cycode/cli/utils/progress_bar.py
+++ b/cycode/cli/utils/progress_bar.py
@@ -179,9 +179,7 @@ def _maybe_update_current_section(self) -> None:
cur_val = self._section_values.get(self._current_section.section, 0)
if cur_val >= max_val:
next_section = _PROGRESS_BAR_SECTIONS[self._current_section.section.next()]
- logger.debug(
- f'_update_current_section: {self._current_section.section} -> {next_section.section}'
- )
+ logger.debug(f'_update_current_section: {self._current_section.section} -> {next_section.section}')
self._current_section = next_section
self._current_section_value = 0
diff --git a/cycode/cli/utils/scan_batch.py b/cycode/cli/utils/scan_batch.py
index 5604d562..b5f1c5d2 100644
--- a/cycode/cli/utils/scan_batch.py
+++ b/cycode/cli/utils/scan_batch.py
@@ -2,8 +2,12 @@
from multiprocessing.pool import ThreadPool
from typing import List, TYPE_CHECKING, Callable, Tuple, Dict
-from cycode.cli.consts import SCAN_BATCH_MAX_SIZE_IN_BYTES, SCAN_BATCH_MAX_FILES_COUNT, SCAN_BATCH_SCANS_PER_CPU, \
- SCAN_BATCH_MAX_PARALLEL_SCANS
+from cycode.cli.consts import (
+ SCAN_BATCH_MAX_SIZE_IN_BYTES,
+ SCAN_BATCH_MAX_FILES_COUNT,
+ SCAN_BATCH_SCANS_PER_CPU,
+ SCAN_BATCH_MAX_PARALLEL_SCANS,
+)
from cycode.cli.models import Document
from cycode.cli.utils.progress_bar import ProgressBarSection
@@ -13,9 +17,9 @@
def split_documents_into_batches(
- documents: List[Document],
- max_size_mb: int = SCAN_BATCH_MAX_SIZE_IN_BYTES,
- max_files_count: int = SCAN_BATCH_MAX_FILES_COUNT,
+ documents: List[Document],
+ max_size_mb: int = SCAN_BATCH_MAX_SIZE_IN_BYTES,
+ max_files_count: int = SCAN_BATCH_MAX_FILES_COUNT,
) -> List[List[Document]]:
batches = []
@@ -44,11 +48,11 @@ def _get_threads_count() -> int:
def run_parallel_batched_scan(
- scan_function: Callable[[List[Document]], Tuple[str, 'CliError', 'LocalScanResult']],
- documents: List[Document],
- progress_bar: 'BaseProgressBar',
- max_size_mb: int = SCAN_BATCH_MAX_SIZE_IN_BYTES,
- max_files_count: int = SCAN_BATCH_MAX_FILES_COUNT,
+ scan_function: Callable[[List[Document]], Tuple[str, 'CliError', 'LocalScanResult']],
+ documents: List[Document],
+ progress_bar: 'BaseProgressBar',
+ max_size_mb: int = SCAN_BATCH_MAX_SIZE_IN_BYTES,
+ max_files_count: int = SCAN_BATCH_MAX_FILES_COUNT,
) -> Tuple[Dict[str, 'CliError'], List['LocalScanResult']]:
batches = split_documents_into_batches(documents, max_size_mb, max_files_count)
progress_bar.set_section_length(ProgressBarSection.SCAN, len(batches)) # * 3
diff --git a/cycode/cli/utils/shell_executor.py b/cycode/cli/utils/shell_executor.py
index ca2e8caa..512d7432 100644
--- a/cycode/cli/utils/shell_executor.py
+++ b/cycode/cli/utils/shell_executor.py
@@ -9,7 +9,7 @@
def shell(
- command: Union[str, List[str]], timeout: int = _SUBPROCESS_DEFAULT_TIMEOUT_SEC, execute_in_shell=False
+ command: Union[str, List[str]], timeout: int = _SUBPROCESS_DEFAULT_TIMEOUT_SEC, execute_in_shell=False
) -> Optional[str]:
logger.debug(f'Executing shell command: {command}')
diff --git a/cycode/cli/utils/task_timer.py b/cycode/cli/utils/task_timer.py
index dadc0aea..7d8efd9e 100644
--- a/cycode/cli/utils/task_timer.py
+++ b/cycode/cli/utils/task_timer.py
@@ -5,7 +5,6 @@
class FunctionContext:
-
def __init__(self, function: Callable, args: List = None, kwargs: Dict = None):
self.function = function
self.args = args or []
@@ -20,8 +19,8 @@ class TimerThread(Thread):
timeout - the amount of time to count until timeout in seconds
quit_function (Mandatory) - function to perform when reaching to timeout
"""
- def __init__(self, timeout: int,
- quit_function: FunctionContext):
+
+ def __init__(self, timeout: int, quit_function: FunctionContext):
Thread.__init__(self)
self._timeout = timeout
self._quit_function = quit_function
@@ -56,8 +55,8 @@ class TimeoutAfter:
quit_function (Optional) - function to perform when reaching to timeout,
the default option is to interrupt main thread
"""
- def __init__(self, timeout: int,
- quit_function: Optional[FunctionContext] = None):
+
+ def __init__(self, timeout: int, quit_function: Optional[FunctionContext] = None):
self.timeout = timeout
self._quit_function = quit_function or FunctionContext(function=self.timeout_function)
self.timer = TimerThread(timeout, quit_function=self._quit_function)
@@ -66,8 +65,9 @@ def __enter__(self) -> None:
if self.timeout:
self.timer.start()
- def __exit__(self, exc_type: Optional[Type[BaseException]], exc_val: Optional[BaseException],
- exc_tb: Optional[TracebackType]) -> None:
+ def __exit__(
+ self, exc_type: Optional[Type[BaseException]], exc_val: Optional[BaseException], exc_tb: Optional[TracebackType]
+ ) -> None:
if self.timeout:
self.timer.stop()
diff --git a/cycode/cli/zip_file.py b/cycode/cli/zip_file.py
index 3a23f9a2..a177b6b7 100644
--- a/cycode/cli/zip_file.py
+++ b/cycode/cli/zip_file.py
@@ -28,6 +28,6 @@ def read(self) -> bytes:
def concat_unique_id(filename: str, unique_id: str) -> str:
if filename.startswith(os.sep):
# remove leading slash to join path correctly
- filename = filename[len(os.sep):]
+ filename = filename[len(os.sep) :]
return os.path.join(unique_id, filename)
diff --git a/cycode/cyclient/config.py b/cycode/cyclient/config.py
index 5946265c..a73fc9d7 100644
--- a/cycode/cyclient/config.py
+++ b/cycode/cyclient/config.py
@@ -5,6 +5,7 @@
from cycode.cli.consts import *
from cycode.cli.user_settings.configuration_manager import ConfigurationManager
+
# set io encoding (for windows)
from .config_dev import DEV_MODE_ENV_VAR_NAME, DEV_TENANT_ID_ENV_VAR_NAME
@@ -16,7 +17,7 @@
stream=sys.stdout,
level=logging.DEBUG,
format="%(asctime)s [%(name)s] %(levelname)s: %(message)s",
- datefmt="%Y-%m-%d %H:%M:%S"
+ datefmt="%Y-%m-%d %H:%M:%S",
)
logging.getLogger("urllib3").setLevel(logging.WARNING)
logging.getLogger("werkzeug").setLevel(logging.WARNING)
@@ -32,7 +33,7 @@
TIMEOUT_ENV_VAR_NAME: 300,
LOGGING_LEVEL_ENV_VAR_NAME: logging.INFO,
DEV_MODE_ENV_VAR_NAME: 'False',
- BATCH_SIZE_ENV_VAR_NAME: 20
+ BATCH_SIZE_ENV_VAR_NAME: 20,
}
configuration = dict(DEFAULT_CONFIGURATION, **os.environ)
diff --git a/cycode/cyclient/config_dev.py b/cycode/cyclient/config_dev.py
index 1033c7e7..5913bb16 100644
--- a/cycode/cyclient/config_dev.py
+++ b/cycode/cyclient/config_dev.py
@@ -1,3 +1,3 @@
DEV_CYCODE_API_URL = "http://localhost"
DEV_MODE_ENV_VAR_NAME = "DEV_MODE"
-DEV_TENANT_ID_ENV_VAR_NAME = "DEV_TENANT_ID"
\ No newline at end of file
+DEV_TENANT_ID_ENV_VAR_NAME = "DEV_TENANT_ID"
diff --git a/cycode/cyclient/cycode_client_base.py b/cycode/cyclient/cycode_client_base.py
index dc37a258..e6220ac2 100644
--- a/cycode/cyclient/cycode_client_base.py
+++ b/cycode/cyclient/cycode_client_base.py
@@ -42,48 +42,24 @@ def reset_user_agent() -> None:
def enrich_user_agent(user_agent_suffix: str) -> None:
CycodeClientBase.MANDATORY_HEADERS['User-Agent'] += f' {user_agent_suffix}'
- def post(
- self,
- url_path: str,
- body: dict = None,
- headers: dict = None,
- **kwargs
- ) -> Response:
+ def post(self, url_path: str, body: dict = None, headers: dict = None, **kwargs) -> Response:
return self._execute(method='post', endpoint=url_path, json=body, headers=headers, **kwargs)
- def put(
- self,
- url_path: str,
- body: dict = None,
- headers: dict = None,
- **kwargs
- ) -> Response:
+ def put(self, url_path: str, body: dict = None, headers: dict = None, **kwargs) -> Response:
return self._execute(method='put', endpoint=url_path, json=body, headers=headers, **kwargs)
- def get(
- self,
- url_path: str,
- headers: dict = None,
- **kwargs
- ) -> Response:
+ def get(self, url_path: str, headers: dict = None, **kwargs) -> Response:
return self._execute(method='get', endpoint=url_path, headers=headers, **kwargs)
def _execute(
- self,
- method: str,
- endpoint: str,
- headers: dict = None,
- without_auth: bool = False,
- **kwargs
+ self, method: str, endpoint: str, headers: dict = None, without_auth: bool = False, **kwargs
) -> Response:
url = self.build_full_url(self.api_url, endpoint)
logger.debug(f'Executing {method.upper()} request to {url}')
try:
headers = self.get_request_headers(headers, without_auth=without_auth)
- response = request(
- method=method, url=url, timeout=self.timeout, headers=headers, **kwargs
- )
+ response = request(method=method, url=url, timeout=self.timeout, headers=headers, **kwargs)
logger.debug(f'Response {response.status_code} from {url}. Content: {response.text}')
diff --git a/cycode/cyclient/cycode_dev_based_client.py b/cycode/cyclient/cycode_dev_based_client.py
index 651e0db4..31f182bf 100644
--- a/cycode/cyclient/cycode_dev_based_client.py
+++ b/cycode/cyclient/cycode_dev_based_client.py
@@ -7,7 +7,6 @@
class CycodeDevBasedClient(CycodeClientBase):
-
def __init__(self, api_url):
super().__init__(api_url)
diff --git a/cycode/cyclient/models.py b/cycode/cyclient/models.py
index 9885896e..330fd2d9 100644
--- a/cycode/cyclient/models.py
+++ b/cycode/cyclient/models.py
@@ -4,8 +4,15 @@
class Detection(Schema):
- def __init__(self, detection_type_id: str, type: str, message: str, detection_details: dict,
- detection_rule_id: str, severity: Optional[str] = None):
+ def __init__(
+ self,
+ detection_type_id: str,
+ type: str,
+ message: str,
+ detection_details: dict,
+ detection_rule_id: str,
+ severity: Optional[str] = None,
+ ):
super().__init__()
self.message = message
self.type = type
@@ -15,11 +22,13 @@ def __init__(self, detection_type_id: str, type: str, message: str, detection_de
self.detection_rule_id = detection_rule_id
def __repr__(self) -> str:
- return f'type:{self.type}, ' \
- f'severity:{self.severity}, ' \
- f'message:{self.message}, ' \
- f'detection_details:{repr(self.detection_details)}, ' \
- f'detection_rule_id:{self.detection_rule_id}'
+ return (
+ f'type:{self.type}, '
+ f'severity:{self.severity}, '
+ f'message:{self.message}, '
+ f'detection_details:{repr(self.detection_details)}, '
+ f'detection_rule_id:{self.detection_rule_id}'
+ )
class DetectionSchema(Schema):
@@ -61,8 +70,14 @@ def build_dto(self, data, **kwargs):
class ZippedFileScanResult(Schema):
- def __init__(self, did_detect: bool, detections_per_file: List[DetectionsPerFile], report_url: Optional[str] = None,
- scan_id: str = None, err: str = None):
+ def __init__(
+ self,
+ did_detect: bool,
+ detections_per_file: List[DetectionsPerFile],
+ report_url: Optional[str] = None,
+ scan_id: str = None,
+ err: str = None,
+ ):
super().__init__()
self.did_detect = did_detect
self.detections_per_file = detections_per_file
@@ -78,8 +93,7 @@ class Meta:
did_detect = fields.Boolean()
scan_id = fields.String()
report_url = fields.String(allow_none=True)
- detections_per_file = fields.List(
- fields.Nested(DetectionsPerFileSchema))
+ detections_per_file = fields.List(fields.Nested(DetectionsPerFileSchema))
err = fields.String()
@post_load
@@ -102,8 +116,7 @@ class Meta:
did_detect = fields.Boolean()
scan_id = fields.String()
- detections = fields.List(
- fields.Nested(DetectionSchema), required=False, allow_none=True)
+ detections = fields.List(fields.Nested(DetectionSchema), required=False, allow_none=True)
err = fields.String()
@post_load
@@ -131,8 +144,16 @@ def build_dto(self, data, **kwargs):
class ScanDetailsResponse(Schema):
- def __init__(self, id: str = None, scan_status: str = None, results_count: int = None, metadata: str = None, message: str = None,
- scan_update_at: str = None, err: str = None):
+ def __init__(
+ self,
+ id: str = None,
+ scan_status: str = None,
+ results_count: int = None,
+ metadata: str = None,
+ message: str = None,
+ scan_update_at: str = None,
+ err: str = None,
+ ):
super().__init__()
self.id = id
self.scan_status = scan_status
@@ -287,9 +308,9 @@ def build_dto(self, data, **kwargs):
class UserAgentOptionScheme(Schema):
app_name = fields.String(required=True) # ex. vscode_extension
- app_version = fields.String(required=True) # ex. 0.2.3
+ app_version = fields.String(required=True) # ex. 0.2.3
env_name = fields.String(required=True) # ex.: Visual Studio Code
- env_version = fields.String(required=True) # ex. 1.78.2
+ env_version = fields.String(required=True) # ex. 1.78.2
@post_load
def build_dto(self, data: dict, **_) -> 'UserAgentOption':
@@ -309,8 +330,10 @@ def user_agent_suffix(self) -> str:
Example: vscode_extension (AppVersion: 0.1.2; EnvName: vscode; EnvVersion: 1.78.2)
"""
- return f'{self.app_name} ' \
- f'(' \
- f'AppVersion: {self.app_version}; ' \
- f'EnvName: {self.env_name}; EnvVersion: {self.env_version}' \
- f')'
+ return (
+ f'{self.app_name} '
+ f'('
+ f'AppVersion: {self.app_version}; '
+ f'EnvName: {self.env_name}; EnvVersion: {self.env_version}'
+ f')'
+ )
diff --git a/cycode/cyclient/scan_client.py b/cycode/cyclient/scan_client.py
index 6b754e4a..e6a46a3b 100644
--- a/cycode/cyclient/scan_client.py
+++ b/cycode/cyclient/scan_client.py
@@ -28,42 +28,51 @@ def file_scan(self, scan_type: str, path: str) -> models.ScanResult:
response = self.scan_cycode_client.post(url_path=url_path, files=files)
return self.parse_scan_response(response)
- def zipped_file_scan(self, scan_type: str, zip_file: InMemoryZip, scan_id: str, scan_parameters: dict,
- is_git_diff: bool = False) -> models.ZippedFileScanResult:
+ def zipped_file_scan(
+ self, scan_type: str, zip_file: InMemoryZip, scan_id: str, scan_parameters: dict, is_git_diff: bool = False
+ ) -> models.ZippedFileScanResult:
url_path = f'{self.scan_config.get_service_name(scan_type)}/{self.SCAN_CONTROLLER_PATH}/zipped-file'
files = {'file': ('multiple_files_scan.zip', zip_file.read())}
response = self.scan_cycode_client.post(
url_path=url_path,
data={'scan_id': scan_id, 'is_git_diff': is_git_diff, 'scan_parameters': json.dumps(scan_parameters)},
- files=files
+ files=files,
)
return self.parse_zipped_file_scan_response(response)
- def zipped_file_scan_async(self, zip_file: InMemoryZip, scan_type: str, scan_parameters: dict,
- is_git_diff: bool = False) -> models.ScanInitializationResponse:
+ def zipped_file_scan_async(
+ self, zip_file: InMemoryZip, scan_type: str, scan_parameters: dict, is_git_diff: bool = False
+ ) -> models.ScanInitializationResponse:
url_path = f'{self.scan_config.get_scans_prefix()}/{self.SCAN_CONTROLLER_PATH}/{scan_type}/repository'
files = {'file': ('multiple_files_scan.zip', zip_file.read())}
response = self.scan_cycode_client.post(
url_path=url_path,
data={'is_git_diff': is_git_diff, 'scan_parameters': json.dumps(scan_parameters)},
- files=files
+ files=files,
)
return models.ScanInitializationResponseSchema().load(response.json())
- def multiple_zipped_file_scan_async(self, from_commit_zip_file: InMemoryZip, to_commit_zip_file: InMemoryZip,
- scan_type: str, scan_parameters: dict,
- is_git_diff: bool = False) -> models.ScanInitializationResponse:
- url_path = f'{self.scan_config.get_scans_prefix()}/{self.SCAN_CONTROLLER_PATH}/{scan_type}/repository/commit-range'
+ def multiple_zipped_file_scan_async(
+ self,
+ from_commit_zip_file: InMemoryZip,
+ to_commit_zip_file: InMemoryZip,
+ scan_type: str,
+ scan_parameters: dict,
+ is_git_diff: bool = False,
+ ) -> models.ScanInitializationResponse:
+ url_path = (
+ f'{self.scan_config.get_scans_prefix()}/{self.SCAN_CONTROLLER_PATH}/{scan_type}/repository/commit-range'
+ )
files = {
'file_from_commit': ('multiple_files_scan.zip', from_commit_zip_file.read()),
- 'file_to_commit': ('multiple_files_scan.zip', to_commit_zip_file.read())
+ 'file_to_commit': ('multiple_files_scan.zip', to_commit_zip_file.read()),
}
response = self.scan_cycode_client.post(
url_path=url_path,
data={'is_git_diff': is_git_diff, 'scan_parameters': json.dumps(scan_parameters)},
- files=files
+ files=files,
)
return models.ScanInitializationResponseSchema().load(response.json())
@@ -100,9 +109,11 @@ def get_scan_detections_count(self, scan_id: str) -> int:
return response.json().get('count', 0)
def commit_range_zipped_file_scan(
- self, scan_type: str, zip_file: InMemoryZip, scan_id: str
+ self, scan_type: str, zip_file: InMemoryZip, scan_id: str
) -> models.ZippedFileScanResult:
- url_path = f'{self.scan_config.get_service_name(scan_type)}/{self.SCAN_CONTROLLER_PATH}/commit-range-zipped-file'
+ url_path = (
+ f'{self.scan_config.get_service_name(scan_type)}/{self.SCAN_CONTROLLER_PATH}/commit-range-zipped-file'
+ )
files = {'file': ('multiple_files_scan.zip', zip_file.read())}
response = self.scan_cycode_client.post(url_path=url_path, data={'scan_id': scan_id}, files=files)
return self.parse_zipped_file_scan_response(response)
diff --git a/cycode/cyclient/scan_config/scan_config_base.py b/cycode/cyclient/scan_config/scan_config_base.py
index 957923d4..81fec2a6 100644
--- a/cycode/cyclient/scan_config/scan_config_base.py
+++ b/cycode/cyclient/scan_config/scan_config_base.py
@@ -2,7 +2,6 @@
class ScanConfigBase(ABC):
-
@abstractmethod
def get_service_name(self, scan_type):
pass
@@ -17,7 +16,6 @@ def get_detections_prefix(self):
class DevScanConfig(ScanConfigBase):
-
def get_service_name(self, scan_type):
if scan_type == 'secret':
return '5025'
@@ -34,7 +32,6 @@ def get_detections_prefix(self):
class DefaultScanConfig(ScanConfigBase):
-
def get_service_name(self, scan_type):
if scan_type == 'secret':
return 'secret'
diff --git a/cycode/cyclient/scan_config/scan_config_creator.py b/cycode/cyclient/scan_config/scan_config_creator.py
index ef20ee1e..adcaf1d9 100644
--- a/cycode/cyclient/scan_config/scan_config_creator.py
+++ b/cycode/cyclient/scan_config/scan_config_creator.py
@@ -14,8 +14,7 @@ def create_scan_client(client_id: str, client_secret: str) -> ScanClient:
else:
scan_cycode_client, scan_config = create_scan(client_id, client_secret)
- return ScanClient(scan_cycode_client=scan_cycode_client,
- scan_config=scan_config)
+ return ScanClient(scan_cycode_client=scan_cycode_client, scan_config=scan_config)
def create_scan(client_id: str, client_secret: str) -> Tuple[CycodeTokenBasedClient, DefaultScanConfig]:
diff --git a/cycode/cyclient/utils.py b/cycode/cyclient/utils.py
index b8be58dc..4b6c1d1c 100644
--- a/cycode/cyclient/utils.py
+++ b/cycode/cyclient/utils.py
@@ -3,7 +3,7 @@
def split_list(input_list, batch_size):
for i in range(0, len(input_list), batch_size):
- yield input_list[i:i + batch_size]
+ yield input_list[i : i + batch_size]
def cpu_count():
diff --git a/poetry.lock b/poetry.lock
index acbcbcd3..93240772 100644
--- a/poetry.lock
+++ b/poetry.lock
@@ -39,6 +39,56 @@ files = [
[package.dependencies]
chardet = ">=3.0.2"
+[[package]]
+name = "black"
+version = "23.3.0"
+description = "The uncompromising code formatter."
+optional = false
+python-versions = ">=3.7"
+files = [
+ {file = "black-23.3.0-cp310-cp310-macosx_10_16_arm64.whl", hash = "sha256:0945e13506be58bf7db93ee5853243eb368ace1c08a24c65ce108986eac65915"},
+ {file = "black-23.3.0-cp310-cp310-macosx_10_16_universal2.whl", hash = "sha256:67de8d0c209eb5b330cce2469503de11bca4085880d62f1628bd9972cc3366b9"},
+ {file = "black-23.3.0-cp310-cp310-macosx_10_16_x86_64.whl", hash = "sha256:7c3eb7cea23904399866c55826b31c1f55bbcd3890ce22ff70466b907b6775c2"},
+ {file = "black-23.3.0-cp310-cp310-manylinux_2_17_x86_64.manylinux2014_x86_64.whl", hash = "sha256:32daa9783106c28815d05b724238e30718f34155653d4d6e125dc7daec8e260c"},
+ {file = "black-23.3.0-cp310-cp310-win_amd64.whl", hash = "sha256:35d1381d7a22cc5b2be2f72c7dfdae4072a3336060635718cc7e1ede24221d6c"},
+ {file = "black-23.3.0-cp311-cp311-macosx_10_16_arm64.whl", hash = "sha256:a8a968125d0a6a404842fa1bf0b349a568634f856aa08ffaff40ae0dfa52e7c6"},
+ {file = "black-23.3.0-cp311-cp311-macosx_10_16_universal2.whl", hash = "sha256:c7ab5790333c448903c4b721b59c0d80b11fe5e9803d8703e84dcb8da56fec1b"},
+ {file = "black-23.3.0-cp311-cp311-macosx_10_16_x86_64.whl", hash = "sha256:a6f6886c9869d4daae2d1715ce34a19bbc4b95006d20ed785ca00fa03cba312d"},
+ {file = "black-23.3.0-cp311-cp311-manylinux_2_17_x86_64.manylinux2014_x86_64.whl", hash = "sha256:6f3c333ea1dd6771b2d3777482429864f8e258899f6ff05826c3a4fcc5ce3f70"},
+ {file = "black-23.3.0-cp311-cp311-win_amd64.whl", hash = "sha256:11c410f71b876f961d1de77b9699ad19f939094c3a677323f43d7a29855fe326"},
+ {file = "black-23.3.0-cp37-cp37m-macosx_10_16_x86_64.whl", hash = "sha256:1d06691f1eb8de91cd1b322f21e3bfc9efe0c7ca1f0e1eb1db44ea367dff656b"},
+ {file = "black-23.3.0-cp37-cp37m-manylinux_2_17_x86_64.manylinux2014_x86_64.whl", hash = "sha256:50cb33cac881766a5cd9913e10ff75b1e8eb71babf4c7104f2e9c52da1fb7de2"},
+ {file = "black-23.3.0-cp37-cp37m-win_amd64.whl", hash = "sha256:e114420bf26b90d4b9daa597351337762b63039752bdf72bf361364c1aa05925"},
+ {file = "black-23.3.0-cp38-cp38-macosx_10_16_arm64.whl", hash = "sha256:48f9d345675bb7fbc3dd85821b12487e1b9a75242028adad0333ce36ed2a6d27"},
+ {file = "black-23.3.0-cp38-cp38-macosx_10_16_universal2.whl", hash = "sha256:714290490c18fb0126baa0fca0a54ee795f7502b44177e1ce7624ba1c00f2331"},
+ {file = "black-23.3.0-cp38-cp38-macosx_10_16_x86_64.whl", hash = "sha256:064101748afa12ad2291c2b91c960be28b817c0c7eaa35bec09cc63aa56493c5"},
+ {file = "black-23.3.0-cp38-cp38-manylinux_2_17_x86_64.manylinux2014_x86_64.whl", hash = "sha256:562bd3a70495facf56814293149e51aa1be9931567474993c7942ff7d3533961"},
+ {file = "black-23.3.0-cp38-cp38-win_amd64.whl", hash = "sha256:e198cf27888ad6f4ff331ca1c48ffc038848ea9f031a3b40ba36aced7e22f2c8"},
+ {file = "black-23.3.0-cp39-cp39-macosx_10_16_arm64.whl", hash = "sha256:3238f2aacf827d18d26db07524e44741233ae09a584273aa059066d644ca7b30"},
+ {file = "black-23.3.0-cp39-cp39-macosx_10_16_universal2.whl", hash = "sha256:f0bd2f4a58d6666500542b26354978218a9babcdc972722f4bf90779524515f3"},
+ {file = "black-23.3.0-cp39-cp39-macosx_10_16_x86_64.whl", hash = "sha256:92c543f6854c28a3c7f39f4d9b7694f9a6eb9d3c5e2ece488c327b6e7ea9b266"},
+ {file = "black-23.3.0-cp39-cp39-manylinux_2_17_x86_64.manylinux2014_x86_64.whl", hash = "sha256:3a150542a204124ed00683f0db1f5cf1c2aaaa9cc3495b7a3b5976fb136090ab"},
+ {file = "black-23.3.0-cp39-cp39-win_amd64.whl", hash = "sha256:6b39abdfb402002b8a7d030ccc85cf5afff64ee90fa4c5aebc531e3ad0175ddb"},
+ {file = "black-23.3.0-py3-none-any.whl", hash = "sha256:ec751418022185b0c1bb7d7736e6933d40bbb14c14a0abcf9123d1b159f98dd4"},
+ {file = "black-23.3.0.tar.gz", hash = "sha256:1c7b8d606e728a41ea1ccbd7264677e494e87cf630e399262ced92d4a8dac940"},
+]
+
+[package.dependencies]
+click = ">=8.0.0"
+mypy-extensions = ">=0.4.3"
+packaging = ">=22.0"
+pathspec = ">=0.9.0"
+platformdirs = ">=2"
+tomli = {version = ">=1.1.0", markers = "python_version < \"3.11\""}
+typed-ast = {version = ">=1.4.2", markers = "python_version < \"3.8\" and implementation_name == \"cpython\""}
+typing-extensions = {version = ">=3.10.0.0", markers = "python_version < \"3.10\""}
+
+[package.extras]
+colorama = ["colorama (>=0.4.3)"]
+d = ["aiohttp (>=3.7.4)"]
+jupyter = ["ipython (>=7.8.0)", "tokenize-rt (>=3.2.0)"]
+uvloop = ["uvloop (>=0.15.2)"]
+
[[package]]
name = "certifi"
version = "2023.5.7"
@@ -381,6 +431,17 @@ build = ["blurb", "twine", "wheel"]
docs = ["sphinx"]
test = ["pytest (<5.4)", "pytest-cov"]
+[[package]]
+name = "mypy-extensions"
+version = "1.0.0"
+description = "Type system extensions for programs checked with the mypy type checker."
+optional = false
+python-versions = ">=3.5"
+files = [
+ {file = "mypy_extensions-1.0.0-py3-none-any.whl", hash = "sha256:4392f6c0eb8a5668a69e23d168ffa70f0be9ccfd32b5cc2d26a34ae5b844552d"},
+ {file = "mypy_extensions-1.0.0.tar.gz", hash = "sha256:75dbf8955dc00442a438fc4d0666508a9a97b6bd41aa2f0ffe9d2f2725af0782"},
+]
+
[[package]]
name = "packaging"
version = "23.1"
@@ -394,13 +455,13 @@ files = [
[[package]]
name = "pathspec"
-version = "0.8.1"
+version = "0.11.1"
description = "Utility library for gitignore style pattern matching of file paths."
optional = false
-python-versions = ">=2.7, !=3.0.*, !=3.1.*, !=3.2.*, !=3.3.*, !=3.4.*"
+python-versions = ">=3.7"
files = [
- {file = "pathspec-0.8.1-py2.py3-none-any.whl", hash = "sha256:aa0cb481c4041bf52ffa7b0d8fa6cd3e88a2ca4879c533c9153882ee2556790d"},
- {file = "pathspec-0.8.1.tar.gz", hash = "sha256:86379d6b86d75816baba717e64b1a3a3469deb93bb76d613c9ce79edc5cb68fd"},
+ {file = "pathspec-0.11.1-py3-none-any.whl", hash = "sha256:d8af70af76652554bd134c22b3e8a1cc46ed7d91edcdd721ef1a0c51a84a5293"},
+ {file = "pathspec-0.11.1.tar.gz", hash = "sha256:2798de800fa92780e33acca925945e9a19a133b715067cf165b8866c15a31687"},
]
[[package]]
@@ -414,6 +475,24 @@ files = [
{file = "pefile-2023.2.7.tar.gz", hash = "sha256:82e6114004b3d6911c77c3953e3838654b04511b8b66e8583db70c65998017dc"},
]
+[[package]]
+name = "platformdirs"
+version = "3.8.0"
+description = "A small Python package for determining appropriate platform-specific dirs, e.g. a \"user data dir\"."
+optional = false
+python-versions = ">=3.7"
+files = [
+ {file = "platformdirs-3.8.0-py3-none-any.whl", hash = "sha256:ca9ed98ce73076ba72e092b23d3c93ea6c4e186b3f1c3dad6edd98ff6ffcca2e"},
+ {file = "platformdirs-3.8.0.tar.gz", hash = "sha256:b0cabcb11063d21a0b261d557acb0a9d2126350e63b70cdf7db6347baea456dc"},
+]
+
+[package.dependencies]
+typing-extensions = {version = ">=4.6.3", markers = "python_version < \"3.8\""}
+
+[package.extras]
+docs = ["furo (>=2023.5.20)", "proselint (>=0.13)", "sphinx (>=7.0.1)", "sphinx-autodoc-typehints (>=1.23,!=1.23.4)"]
+test = ["appdirs (==1.4.4)", "covdefaults (>=2.3)", "pytest (>=7.3.1)", "pytest-cov (>=4.1)", "pytest-mock (>=3.10)"]
+
[[package]]
name = "pluggy"
version = "1.0.0"
@@ -693,6 +772,56 @@ files = [
{file = "tomli-2.0.1.tar.gz", hash = "sha256:de526c12914f0c550d15924c62d72abc48d6fe7364aa87328337a31007fe8a4f"},
]
+[[package]]
+name = "typed-ast"
+version = "1.5.5"
+description = "a fork of Python 2 and 3 ast modules with type comment support"
+optional = false
+python-versions = ">=3.6"
+files = [
+ {file = "typed_ast-1.5.5-cp310-cp310-macosx_10_9_x86_64.whl", hash = "sha256:4bc1efe0ce3ffb74784e06460f01a223ac1f6ab31c6bc0376a21184bf5aabe3b"},
+ {file = "typed_ast-1.5.5-cp310-cp310-macosx_11_0_arm64.whl", hash = "sha256:5f7a8c46a8b333f71abd61d7ab9255440d4a588f34a21f126bbfc95f6049e686"},
+ {file = "typed_ast-1.5.5-cp310-cp310-manylinux_2_17_aarch64.manylinux2014_aarch64.whl", hash = "sha256:597fc66b4162f959ee6a96b978c0435bd63791e31e4f410622d19f1686d5e769"},
+ {file = "typed_ast-1.5.5-cp310-cp310-manylinux_2_17_x86_64.manylinux2014_x86_64.whl", hash = "sha256:d41b7a686ce653e06c2609075d397ebd5b969d821b9797d029fccd71fdec8e04"},
+ {file = "typed_ast-1.5.5-cp310-cp310-musllinux_1_1_aarch64.whl", hash = "sha256:5fe83a9a44c4ce67c796a1b466c270c1272e176603d5e06f6afbc101a572859d"},
+ {file = "typed_ast-1.5.5-cp310-cp310-musllinux_1_1_x86_64.whl", hash = "sha256:d5c0c112a74c0e5db2c75882a0adf3133adedcdbfd8cf7c9d6ed77365ab90a1d"},
+ {file = "typed_ast-1.5.5-cp310-cp310-win_amd64.whl", hash = "sha256:e1a976ed4cc2d71bb073e1b2a250892a6e968ff02aa14c1f40eba4f365ffec02"},
+ {file = "typed_ast-1.5.5-cp311-cp311-macosx_10_9_x86_64.whl", hash = "sha256:c631da9710271cb67b08bd3f3813b7af7f4c69c319b75475436fcab8c3d21bee"},
+ {file = "typed_ast-1.5.5-cp311-cp311-macosx_11_0_arm64.whl", hash = "sha256:b445c2abfecab89a932b20bd8261488d574591173d07827c1eda32c457358b18"},
+ {file = "typed_ast-1.5.5-cp311-cp311-manylinux_2_17_aarch64.manylinux2014_aarch64.whl", hash = "sha256:cc95ffaaab2be3b25eb938779e43f513e0e538a84dd14a5d844b8f2932593d88"},
+ {file = "typed_ast-1.5.5-cp311-cp311-manylinux_2_17_x86_64.manylinux2014_x86_64.whl", hash = "sha256:61443214d9b4c660dcf4b5307f15c12cb30bdfe9588ce6158f4a005baeb167b2"},
+ {file = "typed_ast-1.5.5-cp311-cp311-musllinux_1_1_aarch64.whl", hash = "sha256:6eb936d107e4d474940469e8ec5b380c9b329b5f08b78282d46baeebd3692dc9"},
+ {file = "typed_ast-1.5.5-cp311-cp311-musllinux_1_1_x86_64.whl", hash = "sha256:e48bf27022897577d8479eaed64701ecaf0467182448bd95759883300ca818c8"},
+ {file = "typed_ast-1.5.5-cp311-cp311-win_amd64.whl", hash = "sha256:83509f9324011c9a39faaef0922c6f720f9623afe3fe220b6d0b15638247206b"},
+ {file = "typed_ast-1.5.5-cp36-cp36m-macosx_10_9_x86_64.whl", hash = "sha256:44f214394fc1af23ca6d4e9e744804d890045d1643dd7e8229951e0ef39429b5"},
+ {file = "typed_ast-1.5.5-cp36-cp36m-manylinux_2_17_aarch64.manylinux2014_aarch64.whl", hash = "sha256:118c1ce46ce58fda78503eae14b7664163aa735b620b64b5b725453696f2a35c"},
+ {file = "typed_ast-1.5.5-cp36-cp36m-manylinux_2_17_x86_64.manylinux2014_x86_64.whl", hash = "sha256:be4919b808efa61101456e87f2d4c75b228f4e52618621c77f1ddcaae15904fa"},
+ {file = "typed_ast-1.5.5-cp36-cp36m-musllinux_1_1_aarch64.whl", hash = "sha256:fc2b8c4e1bc5cd96c1a823a885e6b158f8451cf6f5530e1829390b4d27d0807f"},
+ {file = "typed_ast-1.5.5-cp36-cp36m-musllinux_1_1_x86_64.whl", hash = "sha256:16f7313e0a08c7de57f2998c85e2a69a642e97cb32f87eb65fbfe88381a5e44d"},
+ {file = "typed_ast-1.5.5-cp36-cp36m-win_amd64.whl", hash = "sha256:2b946ef8c04f77230489f75b4b5a4a6f24c078be4aed241cfabe9cbf4156e7e5"},
+ {file = "typed_ast-1.5.5-cp37-cp37m-macosx_10_9_x86_64.whl", hash = "sha256:2188bc33d85951ea4ddad55d2b35598b2709d122c11c75cffd529fbc9965508e"},
+ {file = "typed_ast-1.5.5-cp37-cp37m-manylinux_2_17_aarch64.manylinux2014_aarch64.whl", hash = "sha256:0635900d16ae133cab3b26c607586131269f88266954eb04ec31535c9a12ef1e"},
+ {file = "typed_ast-1.5.5-cp37-cp37m-manylinux_2_17_x86_64.manylinux2014_x86_64.whl", hash = "sha256:57bfc3cf35a0f2fdf0a88a3044aafaec1d2f24d8ae8cd87c4f58d615fb5b6311"},
+ {file = "typed_ast-1.5.5-cp37-cp37m-musllinux_1_1_aarch64.whl", hash = "sha256:fe58ef6a764de7b4b36edfc8592641f56e69b7163bba9f9c8089838ee596bfb2"},
+ {file = "typed_ast-1.5.5-cp37-cp37m-musllinux_1_1_x86_64.whl", hash = "sha256:d09d930c2d1d621f717bb217bf1fe2584616febb5138d9b3e8cdd26506c3f6d4"},
+ {file = "typed_ast-1.5.5-cp37-cp37m-win_amd64.whl", hash = "sha256:d40c10326893ecab8a80a53039164a224984339b2c32a6baf55ecbd5b1df6431"},
+ {file = "typed_ast-1.5.5-cp38-cp38-macosx_10_9_x86_64.whl", hash = "sha256:fd946abf3c31fb50eee07451a6aedbfff912fcd13cf357363f5b4e834cc5e71a"},
+ {file = "typed_ast-1.5.5-cp38-cp38-macosx_11_0_arm64.whl", hash = "sha256:ed4a1a42df8a3dfb6b40c3d2de109e935949f2f66b19703eafade03173f8f437"},
+ {file = "typed_ast-1.5.5-cp38-cp38-manylinux_2_17_aarch64.manylinux2014_aarch64.whl", hash = "sha256:045f9930a1550d9352464e5149710d56a2aed23a2ffe78946478f7b5416f1ede"},
+ {file = "typed_ast-1.5.5-cp38-cp38-manylinux_2_17_x86_64.manylinux2014_x86_64.whl", hash = "sha256:381eed9c95484ceef5ced626355fdc0765ab51d8553fec08661dce654a935db4"},
+ {file = "typed_ast-1.5.5-cp38-cp38-musllinux_1_1_aarch64.whl", hash = "sha256:bfd39a41c0ef6f31684daff53befddae608f9daf6957140228a08e51f312d7e6"},
+ {file = "typed_ast-1.5.5-cp38-cp38-musllinux_1_1_x86_64.whl", hash = "sha256:8c524eb3024edcc04e288db9541fe1f438f82d281e591c548903d5b77ad1ddd4"},
+ {file = "typed_ast-1.5.5-cp38-cp38-win_amd64.whl", hash = "sha256:7f58fabdde8dcbe764cef5e1a7fcb440f2463c1bbbec1cf2a86ca7bc1f95184b"},
+ {file = "typed_ast-1.5.5-cp39-cp39-macosx_10_9_x86_64.whl", hash = "sha256:042eb665ff6bf020dd2243307d11ed626306b82812aba21836096d229fdc6a10"},
+ {file = "typed_ast-1.5.5-cp39-cp39-macosx_11_0_arm64.whl", hash = "sha256:622e4a006472b05cf6ef7f9f2636edc51bda670b7bbffa18d26b255269d3d814"},
+ {file = "typed_ast-1.5.5-cp39-cp39-manylinux_2_17_aarch64.manylinux2014_aarch64.whl", hash = "sha256:1efebbbf4604ad1283e963e8915daa240cb4bf5067053cf2f0baadc4d4fb51b8"},
+ {file = "typed_ast-1.5.5-cp39-cp39-manylinux_2_17_x86_64.manylinux2014_x86_64.whl", hash = "sha256:f0aefdd66f1784c58f65b502b6cf8b121544680456d1cebbd300c2c813899274"},
+ {file = "typed_ast-1.5.5-cp39-cp39-musllinux_1_1_aarch64.whl", hash = "sha256:48074261a842acf825af1968cd912f6f21357316080ebaca5f19abbb11690c8a"},
+ {file = "typed_ast-1.5.5-cp39-cp39-musllinux_1_1_x86_64.whl", hash = "sha256:429ae404f69dc94b9361bb62291885894b7c6fb4640d561179548c849f8492ba"},
+ {file = "typed_ast-1.5.5-cp39-cp39-win_amd64.whl", hash = "sha256:335f22ccb244da2b5c296e6f96b06ee9bed46526db0de38d2f0e5a6597b81155"},
+ {file = "typed_ast-1.5.5.tar.gz", hash = "sha256:94282f7a354f36ef5dbce0ef3467ebf6a258e370ab33d5b40c249fa996e590dd"},
+]
+
[[package]]
name = "types-pyyaml"
version = "6.0.12.9"
@@ -706,13 +835,13 @@ files = [
[[package]]
name = "typing-extensions"
-version = "4.5.0"
+version = "4.7.1"
description = "Backported and Experimental Type Hints for Python 3.7+"
optional = false
python-versions = ">=3.7"
files = [
- {file = "typing_extensions-4.5.0-py3-none-any.whl", hash = "sha256:fb33085c39dd998ac16d1431ebc293a8b3eedd00fd4a32de0ff79002c19511b4"},
- {file = "typing_extensions-4.5.0.tar.gz", hash = "sha256:5cb5f4a79139d699607b3ef622a1dedafa84e115ab0024e0d9c044a9479ca7cb"},
+ {file = "typing_extensions-4.7.1-py3-none-any.whl", hash = "sha256:440d5dd3af93b060174bf433bccd69b0babc3b15b1a8dca43789fd7f61514b36"},
+ {file = "typing_extensions-4.7.1.tar.gz", hash = "sha256:b75ddc264f0ba5615db7ba217daeb99701ad295353c45f9e95963337ceeeffb2"},
]
[[package]]
@@ -750,4 +879,4 @@ testing = ["big-O", "flake8 (<5)", "jaraco.functools", "jaraco.itertools", "more
[metadata]
lock-version = "2.0"
python-versions = ">=3.7,<3.12"
-content-hash = "13ef296063bf977819668451d2ba229a9009e3cee5478f5a9d2c4aef3e5e2b2f"
+content-hash = "833e8a506d7c9c0ef2585dc822d37d9b665d51cd0ef4c49b3d6c3397bdd8ecea"
diff --git a/pyproject.toml b/pyproject.toml
index 39d01626..69232760 100644
--- a/pyproject.toml
+++ b/pyproject.toml
@@ -31,7 +31,7 @@ click = ">=8.1.0,<8.2.0"
colorama = ">=0.4.3,<0.5.0"
pyyaml = ">=6.0,<7.0"
marshmallow = ">=3.8.0,<3.9.0"
-pathspec = ">=0.8.0,<0.9.0"
+pathspec = ">=0.11.1,<0.12.0"
gitpython = ">=3.1.30,<3.2.0"
arrow = ">=0.17.0,<0.18.0"
binaryornot = ">=0.4.4,<0.5.0"
@@ -49,6 +49,9 @@ responses = ">=0.23.1,<0.24.0"
pyinstaller = ">=5.11.0,<5.12.0"
dunamai = ">=1.16.1,<1.17.0"
+[tool.poetry.group.dev.dependencies]
+black = ">=23.3.0,<23.4.0"
+
[tool.pytest.ini_options]
log_cli = true
@@ -61,6 +64,26 @@ metadata = false
vcs = "git"
style = "pep440"
+[tool.black]
+line-length = 120
+skip-string-normalization=true
+target-version = ['py37']
+include = '\.pyi?$'
+exclude = '''
+(
+ /(
+ \.git
+ | \.mypy_cache
+ | .idea
+ | .pytest_cache
+ | venv
+ | htmlcov
+ | build
+ | dist
+ )/
+)
+'''
+
[build-system]
requires = ["poetry-core>=1.0.0", "poetry-dynamic-versioning"]
build-backend = "poetry_dynamic_versioning.backend"
diff --git a/tests/__init__.py b/tests/__init__.py
index b475f6f5..421a461f 100644
--- a/tests/__init__.py
+++ b/tests/__init__.py
@@ -23,7 +23,7 @@
"kind": "Deployment",
"name": "nginx-deployment",
}
- ]
+ ],
}
}
diff --git a/tests/cli/test_code_scanner.py b/tests/cli/test_code_scanner.py
index ee4e19bb..c4c23e2a 100644
--- a/tests/cli/test_code_scanner.py
+++ b/tests/cli/test_code_scanner.py
@@ -15,15 +15,19 @@ def ctx():
return click.Context(click.Command('path'), obj={'verbose': False, 'output': 'text'})
-@pytest.mark.parametrize('exception, expected_soft_fail', [
- (custom_exceptions.NetworkError(400, 'msg', Response()), True),
- (custom_exceptions.ScanAsyncError('msg'), True),
- (custom_exceptions.HttpUnauthorizedError('msg', Response()), True),
- (custom_exceptions.ZipTooLargeError(1000), True),
- (InvalidGitRepositoryError(), None),
-])
+@pytest.mark.parametrize(
+ 'exception, expected_soft_fail',
+ [
+ (custom_exceptions.NetworkError(400, 'msg', Response()), True),
+ (custom_exceptions.ScanAsyncError('msg'), True),
+ (custom_exceptions.HttpUnauthorizedError('msg', Response()), True),
+ (custom_exceptions.ZipTooLargeError(1000), True),
+ (InvalidGitRepositoryError(), None),
+ ],
+)
def test_handle_exception_soft_fail(
- ctx: click.Context, exception: custom_exceptions.CycodeError, expected_soft_fail: bool):
+ ctx: click.Context, exception: custom_exceptions.CycodeError, expected_soft_fail: bool
+):
with ctx:
_handle_exception(ctx, exception)
diff --git a/tests/cli/test_main.py b/tests/cli/test_main.py
index f2784626..92ec2e58 100644
--- a/tests/cli/test_main.py
+++ b/tests/cli/test_main.py
@@ -28,7 +28,7 @@ def _is_json(plain: str) -> bool:
@pytest.mark.parametrize('output', ['text', 'json'])
@pytest.mark.parametrize('option_space', ['scan', 'global'])
def test_passing_output_option(
- output: str, option_space: str, scan_client: 'ScanClient', api_token_response: responses.Response
+ output: str, option_space: str, scan_client: 'ScanClient', api_token_response: responses.Response
):
scan_type = 'secret'
diff --git a/tests/conftest.py b/tests/conftest.py
index 3af4b303..72860e70 100644
--- a/tests/conftest.py
+++ b/tests/conftest.py
@@ -12,10 +12,7 @@
_CLIENT_ID = 'b1234568-0eaa-1234-beb8-6f0c12345678'
_CLIENT_SECRET = 'a12345a-42b2-1234-3bdd-c0130123456'
-CLI_ENV_VARS = {
- 'CYCODE_CLIENT_ID': _CLIENT_ID,
- 'CYCODE_CLIENT_SECRET': _CLIENT_SECRET
-}
+CLI_ENV_VARS = {'CYCODE_CLIENT_ID': _CLIENT_ID, 'CYCODE_CLIENT_SECRET': _CLIENT_SECRET}
TEST_FILES_PATH = Path(__file__).parent.joinpath('test_files').absolute()
@@ -43,9 +40,9 @@ def api_token_response(api_token_url) -> responses.Response:
json={
'token': _EXPECTED_API_TOKEN,
'refresh_token': '12345678-0c68-1234-91ba-a13123456789',
- 'expires_in': 86400
+ 'expires_in': 86400,
},
- status=200
+ status=200,
)
diff --git a/tests/cyclient/test_auth_client.py b/tests/cyclient/test_auth_client.py
index a74b2ec7..d6647b27 100644
--- a/tests/cyclient/test_auth_client.py
+++ b/tests/cyclient/test_auth_client.py
@@ -4,14 +4,18 @@
from requests import Timeout
from cycode.cyclient.auth_client import AuthClient
-from cycode.cyclient.models import AuthenticationSession, ApiTokenGenerationPollingResponse, \
- ApiTokenGenerationPollingResponseSchema
+from cycode.cyclient.models import (
+ AuthenticationSession,
+ ApiTokenGenerationPollingResponse,
+ ApiTokenGenerationPollingResponseSchema,
+)
from cycode.cli.exceptions.custom_exceptions import CycodeError
@pytest.fixture(scope='module')
def code_challenge() -> str:
from cycode.cli.auth.auth_manager import AuthManager
+
code_challenge, _ = AuthManager()._generate_pkce_code_pair()
return code_challenge
@@ -19,6 +23,7 @@ def code_challenge() -> str:
@pytest.fixture(scope='module')
def code_verifier() -> str:
from cycode.cli.auth.auth_manager import AuthManager
+
_, code_verifier = AuthManager()._generate_pkce_code_pair()
return code_verifier
@@ -31,18 +36,12 @@ def auth_client() -> AuthClient:
@pytest.fixture(scope='module', name='start_url')
def auth_start_url(client: AuthClient) -> str:
# TODO(MarshalX): create database of constants of endpoints. remove hardcoded paths
- return client.cycode_client.build_full_url(
- client.cycode_client.api_url,
- f'{client.AUTH_CONTROLLER_PATH}/start'
- )
+ return client.cycode_client.build_full_url(client.cycode_client.api_url, f'{client.AUTH_CONTROLLER_PATH}/start')
@pytest.fixture(scope='module', name='token_url')
def auth_token_url(client: AuthClient) -> str:
- return client.cycode_client.build_full_url(
- client.cycode_client.api_url,
- f'{client.AUTH_CONTROLLER_PATH}/token'
- )
+ return client.cycode_client.build_full_url(client.cycode_client.api_url, f'{client.AUTH_CONTROLLER_PATH}/token')
_SESSION_ID = '4cff1234-a209-47ed-ab2f-85676912345c'
@@ -121,8 +120,8 @@ def test_get_api_token_success_completed(client: AuthClient, token_url: str, cod
'secret': 'a123450a-42b2-4ad5-8bdd-c0130123456',
'description': 'cycode cli api token',
'createdByUserId': None,
- 'createdAt': '2023-04-26T11:38:54+00:00'
- }
+ 'createdAt': '2023-04-26T11:38:54+00:00',
+ },
}
expected_response = ApiTokenGenerationPollingResponseSchema().load(expected_json)
diff --git a/tests/cyclient/test_client_base.py b/tests/cyclient/test_client_base.py
index 744ba097..dff25c52 100644
--- a/tests/cyclient/test_client_base.py
+++ b/tests/cyclient/test_client_base.py
@@ -8,7 +8,7 @@ def test_mandatory_headers():
}
client = CycodeClientBase(config.cycode_api_url)
-
+
assert client.MANDATORY_HEADERS == expected_headers
@@ -21,9 +21,7 @@ def test_get_request_headers():
def test_get_request_headers_with_additional():
client = CycodeClientBase(config.cycode_api_url)
- additional_headers = {
- 'Authorize': 'Token test'
- }
+ additional_headers = {'Authorize': 'Token test'}
expected_headers = {**client.MANDATORY_HEADERS, **additional_headers}
assert client.get_request_headers(additional_headers) == expected_headers
diff --git a/tests/cyclient/test_dev_based_client.py b/tests/cyclient/test_dev_based_client.py
index 6ce9f3be..e5fcfecd 100644
--- a/tests/cyclient/test_dev_based_client.py
+++ b/tests/cyclient/test_dev_based_client.py
@@ -5,9 +5,7 @@
def test_get_request_headers():
client = CycodeDevBasedClient(config.cycode_api_url)
- dev_based_headers = {
- 'X-Tenant-Id': config.dev_tenant_id
- }
+ dev_based_headers = {'X-Tenant-Id': config.dev_tenant_id}
expected_headers = {**client.MANDATORY_HEADERS, **dev_based_headers}
assert client.get_request_headers() == expected_headers
diff --git a/tests/cyclient/test_scan_client.py b/tests/cyclient/test_scan_client.py
index d4e11128..41c15a71 100644
--- a/tests/cyclient/test_scan_client.py
+++ b/tests/cyclient/test_scan_client.py
@@ -52,7 +52,7 @@ def get_zipped_file_scan_response(url: str, scan_id: UUID = None) -> responses.R
json_response = {
'did_detect': True,
- 'scan_id': str(scan_id), # not always as expected due to _get_scan_id and passing scan_id to cxt of CLI
+ 'scan_id': str(scan_id), # not always as expected due to _get_scan_id and passing scan_id to cxt of CLI
'detections_per_file': [
{
'file_name': str(_ZIP_CONTENT_PATH.joinpath('secrets.py')),
@@ -73,13 +73,13 @@ def get_zipped_file_scan_response(url: str, scan_id: UUID = None) -> responses.R
'file_path': str(_ZIP_CONTENT_PATH),
'file_name': 'secrets.py',
'file_extension': '.py',
- 'should_resolve_upon_branch_deletion': False
- }
+ 'should_resolve_upon_branch_deletion': False,
+ },
}
- ]
+ ],
}
],
- 'report_url': None
+ 'report_url': None,
}
return responses.Response(method=responses.POST, url=url, json=json_response, status=200)
@@ -99,7 +99,7 @@ def test_zipped_file_scan(scan_type: str, scan_client: ScanClient, api_token_res
url, zip_file = zip_scan_resources(scan_type, scan_client)
expected_scan_id = uuid4()
- responses.add(api_token_response) # mock token based client
+ responses.add(api_token_response) # mock token based client
responses.add(get_zipped_file_scan_response(url, expected_scan_id))
zipped_file_scan_response = scan_client.zipped_file_scan(
@@ -114,7 +114,7 @@ def test_zipped_file_scan_unauthorized_error(scan_type: str, scan_client: ScanCl
url, zip_file = zip_scan_resources(scan_type, scan_client)
expected_scan_id = uuid4().hex
- responses.add(api_token_response) # mock token based client
+ responses.add(api_token_response) # mock token based client
responses.add(method=responses.POST, url=url, status=401)
with pytest.raises(HttpUnauthorizedError) as e_info:
@@ -132,7 +132,7 @@ def test_zipped_file_scan_bad_request_error(scan_type: str, scan_client: ScanCli
expected_status_code = 400
expected_response_text = 'Bad Request'
- responses.add(api_token_response) # mock token based client
+ responses.add(api_token_response) # mock token based client
responses.add(method=responses.POST, url=url, status=expected_status_code, body=expected_response_text)
with pytest.raises(CycodeError) as e_info:
@@ -159,7 +159,7 @@ def test_zipped_file_scan_timeout_error(scan_type: str, scan_client: ScanClient,
timeout_error = Timeout()
timeout_error.response = timeout_response
- responses.add(api_token_response) # mock token based client
+ responses.add(api_token_response) # mock token based client
responses.add(method=responses.POST, url=scan_url, body=timeout_error, status=504)
with pytest.raises(CycodeError) as e_info:
@@ -175,7 +175,7 @@ def test_zipped_file_scan_connection_error(scan_type: str, scan_client: ScanClie
url, zip_file = zip_scan_resources(scan_type, scan_client)
expected_scan_id = uuid4().hex
- responses.add(api_token_response) # mock token based client
+ responses.add(api_token_response) # mock token based client
responses.add(method=responses.POST, url=url, body=ProxyError())
with pytest.raises(CycodeError) as e_info:
diff --git a/tests/cyclient/test_token_based_client.py b/tests/cyclient/test_token_based_client.py
index 1ffa8948..b906a976 100644
--- a/tests/cyclient/test_token_based_client.py
+++ b/tests/cyclient/test_token_based_client.py
@@ -31,9 +31,7 @@ def test_api_token_expired(token_based_client: CycodeTokenBasedClient, api_token
def test_get_request_headers(token_based_client: CycodeTokenBasedClient, api_token: str):
- token_based_headers = {
- 'Authorization': f'Bearer {_EXPECTED_API_TOKEN}'
- }
+ token_based_headers = {'Authorization': f'Bearer {_EXPECTED_API_TOKEN}'}
expected_headers = {**token_based_client.MANDATORY_HEADERS, **token_based_headers}
assert token_based_client.get_request_headers() == expected_headers
diff --git a/tests/user_settings/test_configuration_manager.py b/tests/user_settings/test_configuration_manager.py
index 18c9cb9f..8f4e01f1 100644
--- a/tests/user_settings/test_configuration_manager.py
+++ b/tests/user_settings/test_configuration_manager.py
@@ -16,8 +16,9 @@
def test_get_base_url_from_environment_variable(mocker):
# Arrange
- configuration_manager = _configure_mocks(mocker, ENV_VARS_BASE_URL_VALUE, LOCAL_CONFIG_FILE_BASE_URL_VALUE,
- GLOBAL_CONFIG_BASE_URL_VALUE)
+ configuration_manager = _configure_mocks(
+ mocker, ENV_VARS_BASE_URL_VALUE, LOCAL_CONFIG_FILE_BASE_URL_VALUE, GLOBAL_CONFIG_BASE_URL_VALUE
+ )
# Act
result = configuration_manager.get_cycode_api_url()
@@ -28,8 +29,9 @@ def test_get_base_url_from_environment_variable(mocker):
def test_get_base_url_from_local_config(mocker):
# Arrange
- configuration_manager = _configure_mocks(mocker, None, LOCAL_CONFIG_FILE_BASE_URL_VALUE,
- GLOBAL_CONFIG_BASE_URL_VALUE)
+ configuration_manager = _configure_mocks(
+ mocker, None, LOCAL_CONFIG_FILE_BASE_URL_VALUE, GLOBAL_CONFIG_BASE_URL_VALUE
+ )
# Act
result = configuration_manager.get_cycode_api_url()
@@ -60,12 +62,12 @@ def test_get_base_url_not_configured(mocker):
assert result == DEFAULT_CYCODE_API_URL
-def _configure_mocks(mocker,
- expected_env_var_base_url,
- expected_local_config_file_base_url,
- expected_global_config_file_base_url):
- mocker.patch.object(ConfigurationManager, 'get_api_url_from_environment_variables',
- return_value=expected_env_var_base_url)
+def _configure_mocks(
+ mocker, expected_env_var_base_url, expected_local_config_file_base_url, expected_global_config_file_base_url
+):
+ mocker.patch.object(
+ ConfigurationManager, 'get_api_url_from_environment_variables', return_value=expected_env_var_base_url
+ )
configuration_manager = ConfigurationManager()
configuration_manager.local_config_file_manager = Mock()
configuration_manager.local_config_file_manager.get_api_url.return_value = expected_local_config_file_base_url
diff --git a/tests/user_settings/test_user_settings_commands.py b/tests/user_settings/test_user_settings_commands.py
index 600284d5..cd5e5974 100644
--- a/tests/user_settings/test_user_settings_commands.py
+++ b/tests/user_settings/test_user_settings_commands.py
@@ -7,13 +7,16 @@ def test_set_credentials_no_exist_credentials_in_file(mocker):
# Arrange
client_id_user_input = "new client id"
client_secret_user_input = "new client secret"
- mocker.patch('cycode.cli.user_settings.credentials_manager.CredentialsManager.get_credentials_from_file',
- return_value=(None, None))
+ mocker.patch(
+ 'cycode.cli.user_settings.credentials_manager.CredentialsManager.get_credentials_from_file',
+ return_value=(None, None),
+ )
# side effect - multiple return values, each item in the list represent return of a call
mocker.patch('click.prompt', side_effect=[client_id_user_input, client_secret_user_input])
mocked_update_credentials = mocker.patch(
- 'cycode.cli.user_settings.credentials_manager.CredentialsManager.update_credentials_file')
+ 'cycode.cli.user_settings.credentials_manager.CredentialsManager.update_credentials_file'
+ )
click = CliRunner()
# Act
@@ -27,13 +30,16 @@ def test_set_credentials_update_current_credentials_in_file(mocker):
# Arrange
client_id_user_input = "new client id"
client_secret_user_input = "new client secret"
- mocker.patch('cycode.cli.user_settings.credentials_manager.CredentialsManager.get_credentials_from_file',
- return_value=('client id file', 'client secret file'))
+ mocker.patch(
+ 'cycode.cli.user_settings.credentials_manager.CredentialsManager.get_credentials_from_file',
+ return_value=('client id file', 'client secret file'),
+ )
# side effect - multiple return values, each item in the list represent return of a call
mocker.patch('click.prompt', side_effect=[client_id_user_input, client_secret_user_input])
mocked_update_credentials = mocker.patch(
- 'cycode.cli.user_settings.credentials_manager.CredentialsManager.update_credentials_file')
+ 'cycode.cli.user_settings.credentials_manager.CredentialsManager.update_credentials_file'
+ )
click = CliRunner()
# Act
@@ -47,13 +53,16 @@ def test_set_credentials_update_only_client_id(mocker):
# Arrange
client_id_user_input = "new client id"
current_client_id = 'client secret file'
- mocker.patch('cycode.cli.user_settings.credentials_manager.CredentialsManager.get_credentials_from_file',
- return_value=('client id file', 'client secret file'))
+ mocker.patch(
+ 'cycode.cli.user_settings.credentials_manager.CredentialsManager.get_credentials_from_file',
+ return_value=('client id file', 'client secret file'),
+ )
# side effect - multiple return values, each item in the list represent return of a call
mocker.patch('click.prompt', side_effect=[client_id_user_input, ''])
mocked_update_credentials = mocker.patch(
- 'cycode.cli.user_settings.credentials_manager.CredentialsManager.update_credentials_file')
+ 'cycode.cli.user_settings.credentials_manager.CredentialsManager.update_credentials_file'
+ )
click = CliRunner()
# Act
@@ -67,13 +76,16 @@ def test_set_credentials_update_only_client_secret(mocker):
# Arrange
client_secret_user_input = "new client secret"
current_client_id = 'client secret file'
- mocker.patch('cycode.cli.user_settings.credentials_manager.CredentialsManager.get_credentials_from_file',
- return_value=(current_client_id, 'client secret file'))
+ mocker.patch(
+ 'cycode.cli.user_settings.credentials_manager.CredentialsManager.get_credentials_from_file',
+ return_value=(current_client_id, 'client secret file'),
+ )
# side effect - multiple return values, each item in the list represent return of a call
mocker.patch('click.prompt', side_effect=['', client_secret_user_input])
mocked_update_credentials = mocker.patch(
- 'cycode.cli.user_settings.credentials_manager.CredentialsManager.update_credentials_file')
+ 'cycode.cli.user_settings.credentials_manager.CredentialsManager.update_credentials_file'
+ )
click = CliRunner()
# Act
@@ -87,13 +99,16 @@ def test_set_credentials_should_not_update_file(mocker):
# Arrange
client_id_user_input = ""
client_secret_user_input = ""
- mocker.patch('cycode.cli.user_settings.credentials_manager.CredentialsManager.get_credentials_from_file',
- return_value=('client id file', 'client secret file'))
+ mocker.patch(
+ 'cycode.cli.user_settings.credentials_manager.CredentialsManager.get_credentials_from_file',
+ return_value=('client id file', 'client secret file'),
+ )
# side effect - multiple return values, each item in the list represent return of a call
mocker.patch('click.prompt', side_effect=[client_id_user_input, client_secret_user_input])
mocked_update_credentials = mocker.patch(
- 'cycode.cli.user_settings.credentials_manager.CredentialsManager.update_credentials_file')
+ 'cycode.cli.user_settings.credentials_manager.CredentialsManager.update_credentials_file'
+ )
click = CliRunner()
# Act
@@ -101,4 +116,3 @@ def test_set_credentials_should_not_update_file(mocker):
# Assert
assert not mocked_update_credentials.called
-
From 67f0900571980e94cca31b6d2c99e95948227d5c Mon Sep 17 00:00:00 2001
From: Ilya Siamionau
Date: Wed, 5 Jul 2023 16:25:31 +0200
Subject: [PATCH 006/257] CM-24997 - Integrate Ruff linter (#134)
also, fix truncated help text of commands
---
.github/workflows/ruff.yml | 36 ++++
cycode/cli/auth/auth_command.py | 16 +-
cycode/cli/auth/auth_manager.py | 13 +-
cycode/cli/ci_integrations.py | 53 +++--
cycode/cli/code_scanner.py | 182 +++++++++---------
cycode/cli/config.py | 5 +-
cycode/cli/consts.py | 55 +++---
.../maven/base_restore_maven_dependencies.py | 10 +-
.../maven/restore_maven_dependencies.py | 2 +-
cycode/cli/helpers/sca_code_scanner.py | 20 +-
cycode/cli/main.py | 91 ++++-----
cycode/cli/models.py | 10 +-
cycode/cli/printers/base_printer.py | 4 +-
cycode/cli/printers/base_table_printer.py | 4 +-
cycode/cli/printers/console_printer.py | 11 +-
cycode/cli/printers/json_printer.py | 4 +-
cycode/cli/printers/sca_table_printer.py | 6 +-
cycode/cli/printers/table.py | 9 +-
cycode/cli/printers/table_models.py | 2 +-
cycode/cli/printers/table_printer.py | 10 +-
cycode/cli/printers/text_printer.py | 17 +-
cycode/cli/user_settings/base_file_manager.py | 3 +-
.../cli/user_settings/config_file_manager.py | 13 +-
.../user_settings/configuration_manager.py | 32 +--
.../cli/user_settings/credentials_manager.py | 4 +-
.../user_settings/user_settings_commands.py | 60 +++---
cycode/cli/utils/path_utils.py | 10 +-
cycode/cli/utils/progress_bar.py | 13 +-
cycode/cli/utils/scan_batch.py | 8 +-
cycode/cli/utils/shell_executor.py | 8 +-
cycode/cli/utils/string_utils.py | 11 +-
cycode/cli/utils/task_timer.py | 8 +-
cycode/cli/utils/yaml_utils.py | 9 +-
cycode/cli/zip_file.py | 4 +-
cycode/cyclient/__init__.py | 3 +-
cycode/cyclient/auth_client.py | 5 +-
cycode/cyclient/config.py | 49 ++---
cycode/cyclient/config_dev.py | 6 +-
cycode/cyclient/cycode_client_base.py | 26 +--
cycode/cyclient/cycode_dev_based_client.py | 6 +-
cycode/cyclient/cycode_token_based_client.py | 5 +-
cycode/cyclient/models.py | 37 ++--
cycode/cyclient/scan_client.py | 17 +-
.../cyclient/scan_config/scan_config_base.py | 14 +-
.../scan_config/scan_config_creator.py | 12 +-
poetry.lock | 28 ++-
pyproject.toml | 43 +++++
tests/__init__.py | 10 +-
tests/cli/test_code_scanner.py | 25 ++-
tests/cli/test_main.py | 5 +-
tests/cyclient/test_auth_client.py | 4 +-
tests/cyclient/test_client_base.py | 2 +-
tests/cyclient/test_scan_client.py | 17 +-
tests/cyclient/test_token_based_client.py | 4 +-
tests/test_files/zip_content/__init__.py | 0
tests/test_files/zip_content/sast.py | 3 +-
tests/test_files/zip_content/secrets.py | 2 +-
tests/test_models.py | 10 +-
.../test_configuration_manager.py | 2 +-
.../test_user_settings_commands.py | 16 +-
tests/utils/test_string_utils.py | 4 +-
61 files changed, 609 insertions(+), 489 deletions(-)
create mode 100644 .github/workflows/ruff.yml
create mode 100644 tests/test_files/zip_content/__init__.py
diff --git a/.github/workflows/ruff.yml b/.github/workflows/ruff.yml
new file mode 100644
index 00000000..0fc3ddb5
--- /dev/null
+++ b/.github/workflows/ruff.yml
@@ -0,0 +1,36 @@
+name: Ruff (linter)
+
+on: [ pull_request, push ]
+
+jobs:
+ ruff:
+ runs-on: ubuntu-latest
+
+ steps:
+ - name: Run Cimon
+ uses: cycodelabs/cimon-action@v0
+ with:
+ client-id: ${{ secrets.CIMON_CLIENT_ID }}
+ secret: ${{ secrets.CIMON_SECRET }}
+ prevent: true
+ allowed-hosts: >
+ files.pythonhosted.org
+ install.python-poetry.org
+ pypi.org
+
+ - name: Checkout repository
+ uses: actions/checkout@v3
+
+ - name: Setup Python
+ uses: actions/setup-python@v4
+ with:
+ python-version: 3.7
+
+ - name: Setup Poetry
+ uses: snok/install-poetry@v1
+
+ - name: Install dependencies
+ run: poetry install
+
+ - name: Run linter check
+ run: poetry run ruff check .
diff --git a/cycode/cli/auth/auth_command.py b/cycode/cli/auth/auth_command.py
index e19085fb..63384276 100644
--- a/cycode/cli/auth/auth_command.py
+++ b/cycode/cli/auth/auth_command.py
@@ -1,21 +1,23 @@
-import click
import traceback
-from cycode.cli.models import CliResult, CliErrors, CliError
-from cycode.cli.printers import ConsolePrinter
+import click
+
from cycode.cli.auth.auth_manager import AuthManager
+from cycode.cli.exceptions.custom_exceptions import AuthProcessError, HttpUnauthorizedError, NetworkError
+from cycode.cli.models import CliError, CliErrors, CliResult
+from cycode.cli.printers import ConsolePrinter
from cycode.cli.user_settings.credentials_manager import CredentialsManager
-from cycode.cli.exceptions.custom_exceptions import AuthProcessError, NetworkError, HttpUnauthorizedError
from cycode.cyclient import logger
from cycode.cyclient.cycode_token_based_client import CycodeTokenBasedClient
-@click.group(invoke_without_command=True)
+@click.group(
+ invoke_without_command=True, short_help='Authenticates your machine to associate CLI with your cycode account'
+)
@click.pass_context
def authenticate(context: click.Context):
- """Authenticates your machine to associate CLI with your cycode account"""
if context.invoked_subcommand is not None:
- # if it is a subcommand do nothing
+ # if it is a subcommand, do nothing
return
try:
diff --git a/cycode/cli/auth/auth_manager.py b/cycode/cli/auth/auth_manager.py
index d8d018d8..3a177467 100644
--- a/cycode/cli/auth/auth_manager.py
+++ b/cycode/cli/auth/auth_manager.py
@@ -1,23 +1,24 @@
import time
import webbrowser
-from requests import Request
from typing import Optional
+from requests import Request
+
from cycode.cli.exceptions.custom_exceptions import AuthProcessError
-from cycode.cli.utils.string_utils import generate_random_string, hash_string_to_sha256
from cycode.cli.user_settings.configuration_manager import ConfigurationManager
from cycode.cli.user_settings.credentials_manager import CredentialsManager
+from cycode.cli.utils.string_utils import generate_random_string, hash_string_to_sha256
+from cycode.cyclient import logger
from cycode.cyclient.auth_client import AuthClient
from cycode.cyclient.models import ApiToken, ApiTokenGenerationPollingResponse
-from cycode.cyclient import logger
class AuthManager:
CODE_VERIFIER_LENGTH = 101
POLLING_WAIT_INTERVAL_IN_SECONDS = 3
POLLING_TIMEOUT_IN_SECONDS = 180
- FAILED_POLLING_STATUS = "Error"
- COMPLETED_POLLING_STATUS = "Completed"
+ FAILED_POLLING_STATUS = 'Error'
+ COMPLETED_POLLING_STATUS = 'Completed'
configuration_manager: ConfigurationManager
credentials_manager: CredentialsManager
@@ -56,7 +57,7 @@ def redirect_to_login_page(self, code_challenge: str, session_id: str):
def get_api_token(self, session_id: str, code_verifier: str) -> Optional[ApiToken]:
api_token = self.get_api_token_polling(session_id, code_verifier)
if api_token is None:
- raise AuthProcessError("getting api token is completed, but the token is missing")
+ raise AuthProcessError('getting api token is completed, but the token is missing')
return api_token
def get_api_token_polling(self, session_id: str, code_verifier: str) -> Optional[ApiToken]:
diff --git a/cycode/cli/ci_integrations.py b/cycode/cli/ci_integrations.py
index a98abf4d..5ea93e38 100644
--- a/cycode/cli/ci_integrations.py
+++ b/cycode/cli/ci_integrations.py
@@ -1,61 +1,60 @@
import os
+
import click
def github_action_range():
- before_sha = os.getenv("BEFORE_SHA")
- push_base_sha = os.getenv("BASE_SHA")
- pr_base_sha = os.getenv("PR_BASE_SHA")
- default_branch = os.getenv("DEFAULT_BRANCH")
- head_sha = os.getenv("GITHUB_SHA")
- ref = os.getenv("GITHUB_REF")
-
- click.echo(f"{before_sha}, {push_base_sha}, {pr_base_sha}, {default_branch}, {head_sha}, {ref}")
+ before_sha = os.getenv('BEFORE_SHA')
+ push_base_sha = os.getenv('BASE_SHA')
+ pr_base_sha = os.getenv('PR_BASE_SHA')
+ default_branch = os.getenv('DEFAULT_BRANCH')
+ head_sha = os.getenv('GITHUB_SHA')
+ ref = os.getenv('GITHUB_REF')
+
+ click.echo(f'{before_sha}, {push_base_sha}, {pr_base_sha}, {default_branch}, {head_sha}, {ref}')
if before_sha and before_sha != NO_COMMITS:
- return f"{before_sha}..."
+ return f'{before_sha}...'
- return "..."
+ return '...'
# if pr_base_sha and pr_base_sha != FIRST_COMMIT:
- # return f"{pr_base_sha}..."
#
# if push_base_sha and push_base_sha != "null":
- # return f"{push_base_sha}..."
def circleci_range():
- before_sha = os.getenv("BEFORE_SHA")
- current_sha = os.getenv("CURRENT_SHA")
- commit_range = f"{before_sha}...{current_sha}"
- click.echo(f"commit range: {commit_range}")
+ before_sha = os.getenv('BEFORE_SHA')
+ current_sha = os.getenv('CURRENT_SHA')
+ commit_range = f'{before_sha}...{current_sha}'
+ click.echo(f'commit range: {commit_range}')
if not commit_range.startswith('...'):
return commit_range
- commit_sha = os.getenv("CIRCLE_SHA1", "HEAD")
+ commit_sha = os.getenv('CIRCLE_SHA1', 'HEAD')
return f'{commit_sha}~1...'
def gitlab_range():
- before_sha = os.getenv("CI_COMMIT_BEFORE_SHA")
- commit_sha = os.getenv("CI_COMMIT_SHA", "HEAD")
+ before_sha = os.getenv('CI_COMMIT_BEFORE_SHA')
+ commit_sha = os.getenv('CI_COMMIT_SHA', 'HEAD')
if before_sha and before_sha != NO_COMMITS:
- return f"{before_sha}..."
+ return f'{before_sha}...'
- return f"{commit_sha}"
+ return f'{commit_sha}'
def get_commit_range():
- if os.getenv("GITHUB_ACTIONS"):
+ if os.getenv('GITHUB_ACTIONS'):
return github_action_range()
- elif os.getenv("CIRCLECI"):
+ if os.getenv('CIRCLECI'):
return circleci_range()
- elif os.getenv("GITLAB_CI"):
+ if os.getenv('GITLAB_CI'):
return gitlab_range()
- else:
- raise click.ClickException("CI framework is not supported")
+
+ raise click.ClickException('CI framework is not supported')
-NO_COMMITS = "0000000000000000000000000000000000000000"
+NO_COMMITS = '0000000000000000000000000000000000000000'
diff --git a/cycode/cli/code_scanner.py b/cycode/cli/code_scanner.py
index 47d64ccc..bd72ebd9 100644
--- a/cycode/cli/code_scanner.py
+++ b/cycode/cli/code_scanner.py
@@ -1,4 +1,3 @@
-import click
import json
import logging
import os
@@ -6,49 +5,50 @@
import time
import traceback
from platform import platform
-from uuid import uuid4, UUID
-from typing import TYPE_CHECKING, Callable, List, Optional, Dict, Tuple
-
-from git import Repo, NULL_TREE, InvalidGitRepositoryError
from sys import getsizeof
+from typing import TYPE_CHECKING, Callable, Dict, List, Optional, Tuple
+from uuid import UUID, uuid4
+
+import click
+from git import NULL_TREE, InvalidGitRepositoryError, Repo
-from cycode.cli.printers import ConsolePrinter
-from cycode.cli.models import Document, DocumentDetections, Severity, CliError, CliErrors, LocalScanResult
-from cycode.cli.ci_integrations import get_commit_range
from cycode.cli import consts
+from cycode.cli.ci_integrations import get_commit_range
from cycode.cli.config import configuration_manager
-from cycode.cli.utils.progress_bar import ProgressBarSection
-from cycode.cli.utils.scan_utils import set_issue_detected
+from cycode.cli.exceptions import custom_exceptions
+from cycode.cli.helpers import sca_code_scanner
+from cycode.cli.models import CliError, CliErrors, Document, DocumentDetections, LocalScanResult, Severity
+from cycode.cli.printers import ConsolePrinter
+from cycode.cli.user_settings.config_file_manager import ConfigFileManager
+from cycode.cli.utils import scan_utils
from cycode.cli.utils.path_utils import (
- is_sub_path,
- is_binary_file,
+ get_file_content,
get_file_size,
- get_relevant_files_in_path,
get_path_by_os,
- get_file_content,
+ get_relevant_files_in_path,
+ is_binary_file,
+ is_sub_path,
)
+from cycode.cli.utils.progress_bar import ProgressBarSection
+from cycode.cli.utils.progress_bar import logger as progress_bar_logger
from cycode.cli.utils.scan_batch import run_parallel_batched_scan
+from cycode.cli.utils.scan_utils import set_issue_detected
from cycode.cli.utils.string_utils import get_content_size, is_binary_content
from cycode.cli.utils.task_timer import TimeoutAfter
-from cycode.cli.utils import scan_utils
-from cycode.cli.user_settings.config_file_manager import ConfigFileManager
from cycode.cli.zip_file import InMemoryZip
-from cycode.cli.exceptions import custom_exceptions
-from cycode.cli.helpers import sca_code_scanner
from cycode.cyclient import logger
-from cycode.cli.utils.progress_bar import logger as progress_bar_logger
-from cycode.cyclient.models import ZippedFileScanResult, Detection, DetectionsPerFile, DetectionSchema
+from cycode.cyclient.models import Detection, DetectionSchema, DetectionsPerFile, ZippedFileScanResult
if TYPE_CHECKING:
- from cycode.cyclient.scan_client import ScanClient
- from cycode.cyclient.models import ScanDetailsResponse
from cycode.cli.utils.progress_bar import BaseProgressBar
+ from cycode.cyclient.models import ScanDetailsResponse
+ from cycode.cyclient.scan_client import ScanClient
start_scan_time = time.time()
-@click.command()
-@click.argument("path", nargs=1, type=click.STRING, required=True)
+@click.command(short_help='Scan git repository including its history')
+@click.argument('path', nargs=1, type=click.STRING, required=True)
@click.option(
'--branch',
'-b',
@@ -59,14 +59,13 @@
)
@click.pass_context
def scan_repository(context: click.Context, path: str, branch: str):
- """Scan git repository including its history"""
try:
logger.debug('Starting repository scan process, %s', {'path': path, 'branch': branch})
scan_type = context.obj['scan_type']
monitor = context.obj.get('monitor')
if monitor and scan_type != consts.SCA_SCAN_TYPE:
- raise click.ClickException(f'Monitor flag is currently supported for SCA scan type only')
+ raise click.ClickException('Monitor flag is currently supported for SCA scan type only')
progress_bar = context.obj['progress_bar']
@@ -77,10 +76,7 @@ def scan_repository(context: click.Context, path: str, branch: str):
for file in file_entries:
progress_bar.update(ProgressBarSection.PREPARE_LOCAL_FILES)
- if monitor:
- path = file.path
- else:
- path = get_path_by_os(os.path.join(path, file.path))
+ path = file.path if monitor else get_path_by_os(os.path.join(path, file.path))
documents_to_scan.append(Document(path, file.data_stream.read().decode('UTF-8', errors='replace')))
@@ -96,19 +92,18 @@ def scan_repository(context: click.Context, path: str, branch: str):
_handle_exception(context, e)
-@click.command()
-@click.argument("path", nargs=1, type=click.STRING, required=True)
+@click.command(short_help='Scan all the commits history in this git repository')
+@click.argument('path', nargs=1, type=click.STRING, required=True)
@click.option(
- "--commit_range",
- "-r",
- help='Scan a commit range in this git repository, by default cycode scans all ' 'commit history (example: HEAD~1)',
+ '--commit_range',
+ '-r',
+ help='Scan a commit range in this git repository, by default cycode scans all commit history (example: HEAD~1)',
type=click.STRING,
- default="--all",
+ default='--all',
required=False,
)
@click.pass_context
def scan_repository_commit_history(context: click.Context, path: str, commit_range: str):
- """Scan all the commits history in this git repository"""
try:
logger.debug('Starting commit history scan process, %s', {'path': path, 'commit_range': commit_range})
return scan_commit_range(context, path=path, commit_range=commit_range)
@@ -174,31 +169,30 @@ def scan_commit_range(context: click.Context, path: str, commit_range: str, max_
return scan_documents(context, documents_to_scan, is_git_diff=True, is_commit_range=True)
-@click.command()
+@click.command(
+ short_help='Execute scan in a CI environment which relies on the '
+ 'CYCODE_TOKEN and CYCODE_REPO_LOCATION environment variables'
+)
@click.pass_context
def scan_ci(context: click.Context):
- """Execute scan in a CI environment which relies on the
- CYCODE_TOKEN and CYCODE_REPO_LOCATION environment variables"""
return scan_commit_range(context, path=os.getcwd(), commit_range=get_commit_range())
-@click.command()
-@click.argument("path", nargs=1, type=click.STRING, required=True)
+@click.command(short_help='Scan the files in the path supplied in the command')
+@click.argument('path', nargs=1, type=click.STRING, required=True)
@click.pass_context
def scan_path(context: click.Context, path):
- """Scan the files in the path supplied in the command"""
logger.debug('Starting path scan process, %s', {'path': path})
- files_to_scan = get_relevant_files_in_path(path=path, exclude_patterns=["**/.git/**", "**/.cycode/**"])
+ files_to_scan = get_relevant_files_in_path(path=path, exclude_patterns=['**/.git/**', '**/.cycode/**'])
files_to_scan = exclude_irrelevant_files(context, files_to_scan)
logger.debug('Found all relevant files for scanning %s', {'path': path, 'file_to_scan_count': len(files_to_scan)})
return scan_disk_files(context, path, files_to_scan)
-@click.command()
+@click.command(short_help='Use this command to scan the content that was not committed yet')
@click.argument('ignored_args', nargs=-1, type=click.UNPROCESSED)
@click.pass_context
def pre_commit_scan(context: click.Context, ignored_args: List[str]):
- """Use this command to scan the content that was not committed yet"""
scan_type = context.obj['scan_type']
progress_bar = context.obj['progress_bar']
@@ -218,11 +212,10 @@ def pre_commit_scan(context: click.Context, ignored_args: List[str]):
return scan_documents(context, documents_to_scan, is_git_diff=True)
-@click.command()
-@click.argument("ignored_args", nargs=-1, type=click.UNPROCESSED)
+@click.command(short_help='Use this command to scan commits on the server side before pushing them to the repository')
+@click.argument('ignored_args', nargs=-1, type=click.UNPROCESSED)
@click.pass_context
def pre_receive_scan(context: click.Context, ignored_args: List[str]):
- """Use this command to scan commits on the server side before pushing them to the repository"""
try:
scan_type = context.obj['scan_type']
if scan_type != consts.SECRET_SCAN_TYPE:
@@ -230,8 +223,8 @@ def pre_receive_scan(context: click.Context, ignored_args: List[str]):
if should_skip_pre_receive_scan():
logger.info(
- "A scan has been skipped as per your request."
- " Please note that this may leave your system vulnerable to secrets that have not been detected"
+ 'A scan has been skipped as per your request.'
+ ' Please note that this may leave your system vulnerable to secrets that have not been detected'
)
return
@@ -556,7 +549,7 @@ def perform_pre_scan_documents_actions(
context: click.Context, scan_type: str, documents_to_scan: List[Document], is_git_diff: bool = False
) -> None:
if scan_type == consts.SCA_SCAN_TYPE:
- logger.debug(f'Perform pre scan document actions')
+ logger.debug('Perform pre scan document actions')
sca_code_scanner.add_dependencies_tree_document(context, documents_to_scan, is_git_diff)
@@ -610,7 +603,7 @@ def perform_scan_async(
cycode_client: 'ScanClient', zipped_documents: InMemoryZip, scan_type: str, scan_parameters: dict
) -> ZippedFileScanResult:
scan_async_result = cycode_client.zipped_file_scan_async(zipped_documents, scan_type, scan_parameters)
- logger.debug("scan request has been triggered successfully, scan id: %s", scan_async_result.scan_id)
+ logger.debug('scan request has been triggered successfully, scan id: %s', scan_async_result.scan_id)
return poll_scan_results(cycode_client, scan_async_result.scan_id)
@@ -621,13 +614,13 @@ def perform_commit_range_scan_async(
to_commit_zipped_documents: InMemoryZip,
scan_type: str,
scan_parameters: dict,
- timeout: int = None,
+ timeout: Optional[int] = None,
) -> ZippedFileScanResult:
scan_async_result = cycode_client.multiple_zipped_file_scan_async(
from_commit_zipped_documents, to_commit_zipped_documents, scan_type, scan_parameters
)
- logger.debug("scan request has been triggered successfully, scan id: %s", scan_async_result.scan_id)
+ logger.debug('scan request has been triggered successfully, scan id: %s', scan_async_result.scan_id)
return poll_scan_results(cycode_client, scan_async_result.scan_id, timeout)
@@ -649,7 +642,8 @@ def poll_scan_results(
if scan_details.scan_status == consts.SCAN_STATUS_COMPLETED:
return _get_scan_result(cycode_client, scan_id, scan_details)
- elif scan_details.scan_status == consts.SCAN_STATUS_ERROR:
+
+ if scan_details.scan_status == consts.SCAN_STATUS_ERROR:
raise custom_exceptions.ScanAsyncError(
f'Error occurred while trying to scan zip file. {scan_details.message}'
)
@@ -723,13 +717,12 @@ def parse_pre_receive_input() -> str:
pre_receive_input = sys.stdin.read().strip()
if not pre_receive_input:
raise ValueError(
- "Pre receive input was not found. Make sure that you are using this command only in pre-receive hook"
+ 'Pre receive input was not found. Make sure that you are using this command only in pre-receive hook'
)
# each line represents a branch update request, handle the first one only
# TODO(MichalBor): support case of multiple update branch requests
- branch_update_details = pre_receive_input.splitlines()[0]
- return branch_update_details
+ return pre_receive_input.splitlines()[0]
def calculate_pre_receive_commit_range(branch_update_details: str) -> Optional[str]:
@@ -737,13 +730,13 @@ def calculate_pre_receive_commit_range(branch_update_details: str) -> Optional[s
# branch is deleted, no need to perform scan
if end_commit == consts.EMPTY_COMMIT_SHA:
- return
+ return None
start_commit = get_oldest_unupdated_commit_for_branch(end_commit)
# no new commit to update found
if not start_commit:
- return
+ return None
return f'{start_commit}~1...{end_commit}'
@@ -769,7 +762,7 @@ def get_diff_file_path(file):
def get_diff_file_content(file):
- return file.diff.decode('utf-8', errors='replace')
+ return file.diff.decode('UTF-8', errors='replace')
def should_process_git_object(obj, _: int) -> bool:
@@ -782,10 +775,10 @@ def get_git_repository_tree_file_entries(path: str, branch: str):
def get_default_scan_parameters(context: click.Context) -> dict:
return {
- "monitor": context.obj.get("monitor"),
- "report": context.obj.get("report"),
- "package_vulnerabilities": context.obj.get("package-vulnerabilities"),
- "license_compliance": context.obj.get("license-compliance"),
+ 'monitor': context.obj.get('monitor'),
+ 'report': context.obj.get('report'),
+ 'package_vulnerabilities': context.obj.get('package-vulnerabilities'),
+ 'license_compliance': context.obj.get('license-compliance'),
}
@@ -839,9 +832,7 @@ def exclude_irrelevant_detections(
) -> List[Detection]:
relevant_detections = _exclude_detections_by_exclusions_configuration(detections, scan_type)
relevant_detections = _exclude_detections_by_scan_type(relevant_detections, scan_type, command_scan_type)
- relevant_detections = _exclude_detections_by_severity(relevant_detections, scan_type, severity_threshold)
-
- return relevant_detections
+ return _exclude_detections_by_severity(relevant_detections, scan_type, severity_threshold)
def _exclude_detections_by_severity(
@@ -866,9 +857,12 @@ def _exclude_detections_by_scan_type(
return exclude_detections_in_deleted_lines(detections)
exclude_in_deleted_lines = configuration_manager.get_should_exclude_detections_in_deleted_lines(command_scan_type)
- if command_scan_type in consts.COMMIT_RANGE_BASED_COMMAND_SCAN_TYPES:
- if scan_type == consts.SECRET_SCAN_TYPE and exclude_in_deleted_lines:
- return exclude_detections_in_deleted_lines(detections)
+ if (
+ command_scan_type in consts.COMMIT_RANGE_BASED_COMMAND_SCAN_TYPES
+ and scan_type == consts.SECRET_SCAN_TYPE
+ and exclude_in_deleted_lines
+ ):
+ return exclude_detections_in_deleted_lines(detections)
return detections
@@ -984,10 +978,7 @@ def _is_path_configured_in_exclusions(scan_type: str, file_path: str) -> bool:
exclusions_by_path = configuration_manager.get_exclusions_by_scan_type(scan_type).get(
consts.EXCLUSIONS_BY_PATH_SECTION_NAME, []
)
- for exclusion_path in exclusions_by_path:
- if is_sub_path(exclusion_path, file_path):
- return True
- return False
+ return any(is_sub_path(exclusion_path, file_path) for exclusion_path in exclusions_by_path)
def _get_package_name(detection: Detection) -> str:
@@ -1002,7 +993,7 @@ def _get_package_name(detection: Detection) -> str:
def _is_file_relevant_for_sca_scan(filename: str) -> bool:
- if any([sca_excluded_path in filename for sca_excluded_path in consts.SCA_EXCLUDED_PATHS]):
+ if any(sca_excluded_path in filename for sca_excluded_path in consts.SCA_EXCLUDED_PATHS):
logger.debug("file is irrelevant because it is from node_modules's inner path, %s", {'filename': filename})
return False
@@ -1011,23 +1002,23 @@ def _is_file_relevant_for_sca_scan(filename: str) -> bool:
def _is_relevant_file_to_scan(scan_type: str, filename: str) -> bool:
if _is_subpath_of_cycode_configuration_folder(filename):
- logger.debug("file is irrelevant because it is in cycode configuration directory, %s", {'filename': filename})
+ logger.debug('file is irrelevant because it is in cycode configuration directory, %s', {'filename': filename})
return False
if _is_path_configured_in_exclusions(scan_type, filename):
- logger.debug("file is irrelevant because the file path is in the ignore paths list, %s", {'filename': filename})
+ logger.debug('file is irrelevant because the file path is in the ignore paths list, %s', {'filename': filename})
return False
if not _is_file_extension_supported(scan_type, filename):
- logger.debug("file is irrelevant because the file extension is not supported, %s", {'filename': filename})
+ logger.debug('file is irrelevant because the file extension is not supported, %s', {'filename': filename})
return False
if is_binary_file(filename):
- logger.debug("file is irrelevant because it is binary file, %s", {'filename': filename})
+ logger.debug('file is irrelevant because it is binary file, %s', {'filename': filename})
return False
if scan_type != consts.SCA_SCAN_TYPE and _does_file_exceed_max_size_limit(filename):
- logger.debug("file is irrelevant because its exceeded max size limit, %s", {'filename': filename})
+ logger.debug('file is irrelevant because its exceeded max size limit, %s', {'filename': filename})
return False
if scan_type == consts.SCA_SCAN_TYPE and not _is_file_relevant_for_sca_scan(filename):
@@ -1039,26 +1030,26 @@ def _is_relevant_file_to_scan(scan_type: str, filename: str) -> bool:
def _is_relevant_document_to_scan(scan_type: str, filename: str, content: str) -> bool:
if _is_subpath_of_cycode_configuration_folder(filename):
logger.debug(
- "document is irrelevant because it is in cycode configuration directory, %s", {'filename': filename}
+ 'document is irrelevant because it is in cycode configuration directory, %s', {'filename': filename}
)
return False
if _is_path_configured_in_exclusions(scan_type, filename):
logger.debug(
- "document is irrelevant because the document path is in the ignore paths list, %s", {'filename': filename}
+ 'document is irrelevant because the document path is in the ignore paths list, %s', {'filename': filename}
)
return False
if not _is_file_extension_supported(scan_type, filename):
- logger.debug("document is irrelevant because the file extension is not supported, %s", {'filename': filename})
+ logger.debug('document is irrelevant because the file extension is not supported, %s', {'filename': filename})
return False
if is_binary_content(content):
- logger.debug("document is irrelevant because it is binary, %s", {'filename': filename})
+ logger.debug('document is irrelevant because it is binary, %s', {'filename': filename})
return False
if scan_type != consts.SCA_SCAN_TYPE and _does_document_exceed_max_size_limit(content):
- logger.debug("document is irrelevant because its exceeded max size limit, %s", {'filename': filename})
+ logger.debug('document is irrelevant because its exceeded max size limit, %s', {'filename': filename})
return False
return True
@@ -1071,7 +1062,8 @@ def _is_file_extension_supported(scan_type: str, filename: str) -> bool:
filename.endswith(supported_file_extension)
for supported_file_extension in consts.INFRA_CONFIGURATION_SCAN_SUPPORTED_FILES
)
- elif scan_type == consts.SCA_SCAN_TYPE:
+
+ if scan_type == consts.SCA_SCAN_TYPE:
return any(
filename.endswith(supported_file) for supported_file in consts.SCA_CONFIGURATION_SCAN_SUPPORTED_FILES
)
@@ -1083,11 +1075,11 @@ def _is_file_extension_supported(scan_type: str, filename: str) -> bool:
def _does_file_exceed_max_size_limit(filename: str) -> bool:
- return consts.FILE_MAX_SIZE_LIMIT_IN_BYTES < get_file_size(filename)
+ return get_file_size(filename) > consts.FILE_MAX_SIZE_LIMIT_IN_BYTES
def _does_document_exceed_max_size_limit(content: str) -> bool:
- return consts.FILE_MAX_SIZE_LIMIT_IN_BYTES < get_content_size(content)
+ return get_content_size(content) > consts.FILE_MAX_SIZE_LIMIT_IN_BYTES
def _get_document_by_file_name(
@@ -1137,14 +1129,14 @@ def _handle_exception(context: click.Context, e: Exception, *, return_exception:
soft_fail=True,
code='zip_too_large_error',
message='The path you attempted to scan exceeds the current maximum scanning size cap (10MB). '
- 'Please try ignoring irrelevant paths using the ‘cycode ignore --by-path’ command '
+ 'Please try ignoring irrelevant paths using the `cycode ignore --by-path` command '
'and execute the scan again',
),
InvalidGitRepositoryError: CliError(
soft_fail=False,
code='invalid_git_error',
message='The path you supplied does not correlate to a git repository. '
- 'Should you still wish to scan this path, use: ‘cycode scan path ’',
+ 'Should you still wish to scan this path, use: `cycode scan path `',
),
}
@@ -1158,7 +1150,7 @@ def _handle_exception(context: click.Context, e: Exception, *, return_exception:
return error
ConsolePrinter(context).print_error(error)
- return
+ return None
if return_exception:
return CliError(code='unknown_error', message=str(e))
@@ -1279,14 +1271,14 @@ def _map_detections_per_file(detections: List[dict]) -> List[DetectionsPerFile]:
detection['message'] = detection['correlation_message']
file_name = _get_file_name_from_detection(detection)
if file_name is None:
- logger.debug("file name is missing from detection with id %s", detection.get('id'))
+ logger.debug('file name is missing from detection with id %s', detection.get('id'))
continue
if detections_per_files.get(file_name) is None:
detections_per_files[file_name] = [DetectionSchema().load(detection)]
else:
detections_per_files[file_name].append(DetectionSchema().load(detection))
except Exception as e:
- logger.debug("Failed to parse detection: %s", str(e))
+ logger.debug('Failed to parse detection: %s', str(e))
continue
return [
diff --git a/cycode/cli/config.py b/cycode/cli/config.py
index 9e023bfa..71f354ad 100644
--- a/cycode/cli/config.py
+++ b/cycode/cli/config.py
@@ -1,8 +1,7 @@
import os
-from cycode.cli.utils.yaml_utils import read_file
from cycode.cli.user_settings.configuration_manager import ConfigurationManager
-
+from cycode.cli.utils.yaml_utils import read_file
relative_path = os.path.dirname(__file__)
config_file_path = os.path.join(relative_path, 'config.yaml')
@@ -11,4 +10,4 @@
# env vars
CYCODE_CLIENT_ID_ENV_VAR_NAME = 'CYCODE_CLIENT_ID'
-CYCODE_CLIENT_SECRET_ENV_VAR_NAME = 'CYCODE_CLIENT_SECRET'
+CYCODE_CLIENT_SECRET_ENV_VAR_NAME = 'CYCODE_CLIENT_SECRET' # noqa: S105
diff --git a/cycode/cli/consts.py b/cycode/cli/consts.py
index f7e4a834..eb3f2c00 100644
--- a/cycode/cli/consts.py
+++ b/cycode/cli/consts.py
@@ -2,10 +2,10 @@
PRE_RECEIVE_COMMAND_SCAN_TYPE = 'pre_receive'
COMMIT_HISTORY_COMMAND_SCAN_TYPE = 'commit_history'
-SECRET_SCAN_TYPE = 'secret'
+SECRET_SCAN_TYPE = 'secret' # noqa: S105
INFRA_CONFIGURATION_SCAN_TYPE = 'iac'
-SCA_SCAN_TYPE = "sca"
-SAST_SCAN_TYPE = "sast"
+SCA_SCAN_TYPE = 'sca'
+SAST_SCAN_TYPE = 'sast'
INFRA_CONFIGURATION_SCAN_SUPPORTED_FILES = ['.tf', '.tf.json', '.json', '.yaml', '.yml', 'dockerfile']
@@ -78,37 +78,37 @@
SCA_EXCLUDED_PATHS = ['node_modules']
PROJECT_FILES_BY_ECOSYSTEM_MAP = {
- "crates": ["Cargo.lock", "Cargo.toml"],
- "composer": ["composer.json", "composer.lock"],
- "go": ["go.sum", "go.mod", "Gopkg.lock"],
- "maven_pom": ["pom.xml"],
- "maven_gradle": ["build.gradle", "build.gradle.kts", "gradle.lockfile"],
- "npm": ["package.json", "package-lock.json", "yarn.lock", "npm-shrinkwrap.json", ".npmrc"],
- "nuget": ["packages.config", "project.assets.json", "packages.lock.json", "nuget.config"],
- "ruby_gems": ["Gemfile", "Gemfile.lock"],
- "sbt": ["build.sbt", "build.scala", "build.sbt.lock"],
- "pypi_poetry": ["pyproject.toml", "poetry.lock"],
- "pypi_pipenv": ["Pipfile", "Pipfile.lock"],
- "pypi_requirements": ["requirements.txt"],
- "pypi_setup": ["setup.py"],
+ 'crates': ['Cargo.lock', 'Cargo.toml'],
+ 'composer': ['composer.json', 'composer.lock'],
+ 'go': ['go.sum', 'go.mod', 'Gopkg.lock'],
+ 'maven_pom': ['pom.xml'],
+ 'maven_gradle': ['build.gradle', 'build.gradle.kts', 'gradle.lockfile'],
+ 'npm': ['package.json', 'package-lock.json', 'yarn.lock', 'npm-shrinkwrap.json', '.npmrc'],
+ 'nuget': ['packages.config', 'project.assets.json', 'packages.lock.json', 'nuget.config'],
+ 'ruby_gems': ['Gemfile', 'Gemfile.lock'],
+ 'sbt': ['build.sbt', 'build.scala', 'build.sbt.lock'],
+ 'pypi_poetry': ['pyproject.toml', 'poetry.lock'],
+ 'pypi_pipenv': ['Pipfile', 'Pipfile.lock'],
+ 'pypi_requirements': ['requirements.txt'],
+ 'pypi_setup': ['setup.py'],
}
COMMIT_RANGE_SCAN_SUPPORTED_SCAN_TYPES = [SECRET_SCAN_TYPE, SCA_SCAN_TYPE]
COMMIT_RANGE_BASED_COMMAND_SCAN_TYPES = [PRE_RECEIVE_COMMAND_SCAN_TYPE, COMMIT_HISTORY_COMMAND_SCAN_TYPE]
-DEFAULT_CYCODE_API_URL = "https://api.cycode.com"
-DEFAULT_CYCODE_APP_URL = "https://app.cycode.com"
+DEFAULT_CYCODE_API_URL = 'https://api.cycode.com'
+DEFAULT_CYCODE_APP_URL = 'https://app.cycode.com'
# env var names
-CYCODE_API_URL_ENV_VAR_NAME = "CYCODE_API_URL"
-CYCODE_APP_URL_ENV_VAR_NAME = "CYCODE_APP_URL"
-TIMEOUT_ENV_VAR_NAME = "TIMEOUT"
-CYCODE_CLI_REQUEST_TIMEOUT_ENV_VAR_NAME = "CYCODE_CLI_REQUEST_TIMEOUT"
-LOGGING_LEVEL_ENV_VAR_NAME = "LOGGING_LEVEL"
+CYCODE_API_URL_ENV_VAR_NAME = 'CYCODE_API_URL'
+CYCODE_APP_URL_ENV_VAR_NAME = 'CYCODE_APP_URL'
+TIMEOUT_ENV_VAR_NAME = 'TIMEOUT'
+CYCODE_CLI_REQUEST_TIMEOUT_ENV_VAR_NAME = 'CYCODE_CLI_REQUEST_TIMEOUT'
+LOGGING_LEVEL_ENV_VAR_NAME = 'LOGGING_LEVEL'
# use only for dev envs locally
-BATCH_SIZE_ENV_VAR_NAME = "BATCH_SIZE"
-VERBOSE_ENV_VAR_NAME = "CYCODE_CLI_VERBOSE"
+BATCH_SIZE_ENV_VAR_NAME = 'BATCH_SIZE'
+VERBOSE_ENV_VAR_NAME = 'CYCODE_CLI_VERBOSE'
CYCODE_CONFIGURATION_DIRECTORY: str = '.cycode'
@@ -152,7 +152,7 @@
Cycode Secrets Push Protection
------------------------------------------------------------------------------
Resolve the following secrets by rewriting your local commit history before pushing again.
-Learn how to: https://cycode.com/dont-let-hardcoded-secrets-compromise-your-security-4-effective-remediation-techniques
+Learn how to: https://cycode.com/dont-let-hardcoded-secrets-compromise-your-security-4-effective-remediation-techniques
"""
EXCLUDE_DETECTIONS_IN_DELETED_LINES_ENV_VAR_NAME = 'EXCLUDE_DETECTIONS_IN_DELETED_LINES'
@@ -178,7 +178,8 @@
LICENSE_COMPLIANCE_POLICY_ID = '8f681450-49e1-4f7e-85b7-0c8fe84b3a35'
PACKAGE_VULNERABILITY_POLICY_ID = '9369d10a-9ac0-48d3-9921-5de7fe9a37a7'
-# Shortcut dependency paths by remove all middle depndencies between direct dependency and influence/vulnerable dependency.
+# Shortcut dependency paths by remove all middle dependencies
+# between direct dependency and influence/vulnerable dependency.
# Example: A -> B -> C
# Result: A -> ... -> C
SCA_SHORTCUT_DEPENDENCY_PATHS = 2
diff --git a/cycode/cli/helpers/maven/base_restore_maven_dependencies.py b/cycode/cli/helpers/maven/base_restore_maven_dependencies.py
index 42bd9cc7..b3c55008 100644
--- a/cycode/cli/helpers/maven/base_restore_maven_dependencies.py
+++ b/cycode/cli/helpers/maven/base_restore_maven_dependencies.py
@@ -1,10 +1,10 @@
from abc import ABC, abstractmethod
-from typing import List, Optional, Dict
+from typing import Dict, List, Optional
import click
from cycode.cli.models import Document
-from cycode.cli.utils.path_utils import join_paths, get_file_dir
+from cycode.cli.utils.path_utils import get_file_dir, join_paths
from cycode.cli.utils.shell_executor import shell
from cycode.cyclient import logger
@@ -30,8 +30,7 @@ def __init__(self, context: click.Context, is_git_diff: bool, command_timeout: i
self.command_timeout = command_timeout
def restore(self, document: Document) -> Optional[Document]:
- restore_dependencies_document = self.try_restore_dependencies(document)
- return restore_dependencies_document
+ return self.try_restore_dependencies(document)
def get_manifest_file_path(self, document: Document) -> str:
return (
@@ -54,9 +53,8 @@ def get_lock_file_name(self) -> str:
def try_restore_dependencies(self, document: Document) -> Optional[Document]:
manifest_file_path = self.get_manifest_file_path(document)
- document = Document(
+ return Document(
build_dep_tree_path(document.path, self.get_lock_file_name()),
execute_command(self.get_command(manifest_file_path), manifest_file_path, self.command_timeout),
self.is_git_diff,
)
- return document
diff --git a/cycode/cli/helpers/maven/restore_maven_dependencies.py b/cycode/cli/helpers/maven/restore_maven_dependencies.py
index 51e2aa96..bef8a1b1 100644
--- a/cycode/cli/helpers/maven/restore_maven_dependencies.py
+++ b/cycode/cli/helpers/maven/restore_maven_dependencies.py
@@ -9,7 +9,7 @@
execute_command,
)
from cycode.cli.models import Document
-from cycode.cli.utils.path_utils import get_file_dir, get_file_content, join_paths
+from cycode.cli.utils.path_utils import get_file_content, get_file_dir, join_paths
BUILD_MAVEN_FILE_NAME = 'pom.xml'
MAVEN_CYCLONE_DEP_TREE_FILE_NAME = 'bom.json'
diff --git a/cycode/cli/helpers/sca_code_scanner.py b/cycode/cli/helpers/sca_code_scanner.py
index cbd040c7..87e301e3 100644
--- a/cycode/cli/helpers/sca_code_scanner.py
+++ b/cycode/cli/helpers/sca_code_scanner.py
@@ -1,14 +1,14 @@
import os
-from typing import List, Optional, Dict
+from typing import Dict, List, Optional
import click
-from git import Repo, GitCommandError
+from git import GitCommandError, Repo
-from cycode.cli.consts import *
+from cycode.cli import consts
from cycode.cli.helpers.maven.restore_gradle_dependencies import RestoreGradleDependencies
from cycode.cli.helpers.maven.restore_maven_dependencies import RestoreMavenDependencies
from cycode.cli.models import Document
-from cycode.cli.utils.path_utils import get_file_dir, join_paths, get_file_content
+from cycode.cli.utils.path_utils import get_file_content, get_file_dir, join_paths
from cycode.cyclient import logger
BUILD_GRADLE_FILE_NAME = 'build.gradle'
@@ -33,7 +33,7 @@ def perform_pre_hook_range_scan_actions(
git_head_documents: List[Document], pre_committed_documents: List[Document]
) -> None:
repo = Repo(os.getcwd())
- add_ecosystem_related_files_if_exists(git_head_documents, repo, GIT_HEAD_COMMIT_REV)
+ add_ecosystem_related_files_if_exists(git_head_documents, repo, consts.GIT_HEAD_COMMIT_REV)
add_ecosystem_related_files_if_exists(pre_committed_documents)
@@ -43,7 +43,7 @@ def add_ecosystem_related_files_if_exists(
for doc in documents:
ecosystem = get_project_file_ecosystem(doc)
if ecosystem is None:
- logger.debug("failed to resolve project file ecosystem: %s", doc.path)
+ logger.debug('failed to resolve project file ecosystem: %s', doc.path)
continue
documents_to_add = get_doc_ecosystem_related_project_files(doc, documents, ecosystem, commit_rev, repo)
documents.extend(documents_to_add)
@@ -53,7 +53,7 @@ def get_doc_ecosystem_related_project_files(
doc: Document, documents: List[Document], ecosystem: str, commit_rev: Optional[str], repo: Optional[Repo]
) -> List[Document]:
documents_to_add: List[Document] = []
- for ecosystem_project_file in PROJECT_FILES_BY_ECOSYSTEM_MAP.get(ecosystem):
+ for ecosystem_project_file in consts.PROJECT_FILES_BY_ECOSYSTEM_MAP.get(ecosystem):
file_to_search = join_paths(get_file_dir(doc.path), ecosystem_project_file)
if not is_project_file_exists_in_documents(documents, file_to_search):
file_content = (
@@ -73,7 +73,7 @@ def is_project_file_exists_in_documents(documents: List[Document], file: str) ->
def get_project_file_ecosystem(document: Document) -> Optional[str]:
- for ecosystem, project_files in PROJECT_FILES_BY_ECOSYSTEM_MAP.items():
+ for ecosystem, project_files in consts.PROJECT_FILES_BY_ECOSYSTEM_MAP.items():
for project_file in project_files:
if document.path.endswith(project_file):
return ecosystem
@@ -96,10 +96,10 @@ def try_restore_dependencies(
is_monitor_action = context.obj.get('monitor')
project_path = context.params.get('path')
manifest_file_path = get_manifest_file_path(document, is_monitor_action, project_path)
- logger.debug(f"Succeeded to generate dependencies tree on path: {manifest_file_path}")
+ logger.debug(f'Succeeded to generate dependencies tree on path: {manifest_file_path}')
if restore_dependencies_document.path in documents_to_add:
- logger.debug(f"Duplicate document on restore for path: {restore_dependencies_document.path}")
+ logger.debug(f'Duplicate document on restore for path: {restore_dependencies_document.path}')
else:
documents_to_add[restore_dependencies_document.path] = restore_dependencies_document
diff --git a/cycode/cli/main.py b/cycode/cli/main.py
index 946c1c8b..cb741ad7 100644
--- a/cycode/cli/main.py
+++ b/cycode/cli/main.py
@@ -1,23 +1,22 @@
import logging
-
-import click
import sys
+from typing import TYPE_CHECKING, List, Optional
-from typing import List, Optional, TYPE_CHECKING
+import click
from cycode import __version__
-from cycode.cli.consts import NO_ISSUES_STATUS_CODE, ISSUE_DETECTED_STATUS_CODE
-from cycode.cli.models import Severity
-from cycode.cli.config import config
from cycode.cli import code_scanner
-from cycode.cli.user_settings.credentials_manager import CredentialsManager
-from cycode.cli.user_settings.configuration_manager import ConfigurationManager
-from cycode.cli.user_settings.user_settings_commands import set_credentials, add_exclusions
from cycode.cli.auth.auth_command import authenticate
+from cycode.cli.config import config
+from cycode.cli.consts import ISSUE_DETECTED_STATUS_CODE, NO_ISSUES_STATUS_CODE
+from cycode.cli.models import Severity
+from cycode.cli.user_settings.configuration_manager import ConfigurationManager
+from cycode.cli.user_settings.credentials_manager import CredentialsManager
+from cycode.cli.user_settings.user_settings_commands import add_exclusions, set_credentials
from cycode.cli.utils import scan_utils
from cycode.cli.utils.progress_bar import get_progress_bar
-from cycode.cyclient import logger
from cycode.cli.utils.progress_bar import logger as progress_bar_logger
+from cycode.cyclient import logger
from cycode.cyclient.cycode_client_base import CycodeClientBase
from cycode.cyclient.models import UserAgentOptionScheme
from cycode.cyclient.scan_config.scan_config_creator import create_scan_client
@@ -25,25 +24,27 @@
if TYPE_CHECKING:
from cycode.cyclient.scan_client import ScanClient
-CONTEXT = dict()
+CONTEXT = {}
@click.group(
commands={
- "repository": code_scanner.scan_repository,
- "commit_history": code_scanner.scan_repository_commit_history,
- "path": code_scanner.scan_path,
- "pre_commit": code_scanner.pre_commit_scan,
- "pre_receive": code_scanner.pre_receive_scan,
+ 'repository': code_scanner.scan_repository,
+ 'commit_history': code_scanner.scan_repository_commit_history,
+ 'path': code_scanner.scan_path,
+ 'pre_commit': code_scanner.pre_commit_scan,
+ 'pre_receive': code_scanner.pre_receive_scan,
},
+ short_help='Scan content for secrets/IaC/sca/SAST violations. '
+ 'You need to specify which scan type: ci/commit_history/path/repository/etc',
)
@click.option(
'--scan-type',
'-t',
- default="secret",
+ default='secret',
help="""
\b
- Specify the scan you wish to execute (secret/iac/sca),
+ Specify the scan you wish to execute (secret/iac/sca),
the default is secret
""",
type=click.Choice(config['scans']['supported_scans']),
@@ -78,7 +79,7 @@
default=None,
help="""
\b
- Specify the results output (text/json/table),
+ Specify the results output (text/json/table),
the default is text
""",
type=click.Choice(['text', 'json', 'table']),
@@ -93,7 +94,7 @@
@click.option(
'--sca-scan',
default=None,
- help="Specify the sca scan you wish to execute (package-vulnerabilities/license-compliance), the default is both",
+ help='Specify the sca scan you wish to execute (package-vulnerabilities/license-compliance), the default is both',
multiple=True,
type=click.Choice(config['scans']['supported_sca_scans']),
)
@@ -101,7 +102,9 @@
'--monitor',
is_flag=True,
default=False,
- help="When specified, the scan results will be recorded in the knowledge graph. Please note that when working in 'monitor' mode, the knowledge graph will not be updated as a result of SCM events (Push, Repo creation).(supported for SCA scan type only).",
+ help="When specified, the scan results will be recorded in the knowledge graph. "
+ "Please note that when working in 'monitor' mode, the knowledge graph "
+ "will not be updated as a result of SCM events (Push, Repo creation).(supported for SCA scan type only).",
type=bool,
required=False,
)
@@ -109,7 +112,8 @@
'--report',
is_flag=True,
default=False,
- help="When specified, a violations report will be generated. A URL link to the report will be printed as an output to the command execution",
+ help='When specified, a violations report will be generated. '
+ 'A URL link to the report will be printed as an output to the command execution',
type=bool,
required=False,
)
@@ -127,34 +131,33 @@ def code_scan(
monitor,
report,
):
- """Scan content for secrets/IaC/sca/SAST violations, You need to specify which scan type: ci/commit_history/path/repository/etc"""
if show_secret:
- context.obj["show_secret"] = show_secret
+ context.obj['show_secret'] = show_secret
else:
- context.obj["show_secret"] = config["result_printer"]["default"]["show_secret"]
+ context.obj['show_secret'] = config['result_printer']['default']['show_secret']
if soft_fail:
- context.obj["soft_fail"] = soft_fail
+ context.obj['soft_fail'] = soft_fail
else:
- context.obj["soft_fail"] = config["soft_fail"]
+ context.obj['soft_fail'] = config['soft_fail']
- context.obj["scan_type"] = scan_type
+ context.obj['scan_type'] = scan_type
# save backward compatability with old style command
if output is not None:
- context.obj["output"] = output
- if output == "json":
- context.obj["no_progress_meter"] = True
+ context.obj['output'] = output
+ if output == 'json':
+ context.obj['no_progress_meter'] = True
- context.obj["client"] = get_cycode_client(client_id, secret)
- context.obj["severity_threshold"] = severity_threshold
- context.obj["monitor"] = monitor
- context.obj["report"] = report
+ context.obj['client'] = get_cycode_client(client_id, secret)
+ context.obj['severity_threshold'] = severity_threshold
+ context.obj['monitor'] = monitor
+ context.obj['report'] = report
_sca_scan_to_context(context, sca_scan)
- context.obj["progress_bar"] = get_progress_bar(hidden=context.obj["no_progress_meter"])
- context.obj["progress_bar"].start()
+ context.obj['progress_bar'] = get_progress_bar(hidden=context.obj['no_progress_meter'])
+ context.obj['progress_bar'].start()
return 1
@@ -177,15 +180,15 @@ def finalize(context: click.Context, *_, **__):
@click.group(
- commands={"scan": code_scan, "configure": set_credentials, "ignore": add_exclusions, "auth": authenticate},
+ commands={'scan': code_scan, 'configure': set_credentials, 'ignore': add_exclusions, 'auth': authenticate},
context_settings=CONTEXT,
)
@click.option(
- "--verbose",
- "-v",
+ '--verbose',
+ '-v',
is_flag=True,
default=False,
- help="Show detailed logs",
+ help='Show detailed logs',
)
@click.option(
'--no-progress-meter',
@@ -205,7 +208,7 @@ def finalize(context: click.Context, *_, **__):
help='Characteristic JSON object that lets servers identify the application',
type=str,
)
-@click.version_option(__version__, prog_name="cycode")
+@click.version_option(__version__, prog_name='cycode')
@click.pass_context
def main_cli(context: click.Context, verbose: bool, no_progress_meter: bool, output: str, user_agent: Optional[str]):
context.ensure_object(dict)
@@ -233,9 +236,9 @@ def get_cycode_client(client_id: str, client_secret: str) -> 'ScanClient':
if not client_id or not client_secret:
client_id, client_secret = _get_configured_credentials()
if not client_id:
- raise click.ClickException("Cycode client id needed.")
+ raise click.ClickException('Cycode client id needed.')
if not client_secret:
- raise click.ClickException("Cycode client secret is needed.")
+ raise click.ClickException('Cycode client secret is needed.')
return create_scan_client(client_id, client_secret)
diff --git a/cycode/cli/models.py b/cycode/cli/models.py
index 051b2fa7..67453b8c 100644
--- a/cycode/cli/models.py
+++ b/cycode/cli/models.py
@@ -1,18 +1,18 @@
from enum import Enum
-from typing import List, NamedTuple, Dict, Type, Optional
+from typing import Dict, List, NamedTuple, Optional, Type
from cycode.cyclient.models import Detection
class Document:
- def __init__(self, path: str, content: str, is_git_diff_format: bool = False, unique_id: str = None):
+ def __init__(self, path: str, content: str, is_git_diff_format: bool = False, unique_id: Optional[str] = None):
self.path = path
self.content = content
self.is_git_diff_format = is_git_diff_format
self.unique_id = unique_id
def __repr__(self) -> str:
- return "path:{0}, " "content:{1}".format(self.path, self.content)
+ return 'path:{0}, content:{1}'.format(self.path, self.content)
class DocumentDetections:
@@ -21,14 +21,14 @@ def __init__(self, document: Document, detections: List[Detection]):
self.detections = detections
def __repr__(self) -> str:
- return "document:{0}, " "detections:{1}".format(self.document, self.detections)
+ return 'document:{0}, detections:{1}'.format(self.document, self.detections)
class Severity(Enum):
INFO = -1
LOW = 0
MEDIUM = 1
- MODERATE = 1
+ MODERATE = 1 # noqa: PIE796. TODO(MarshalX): rework. should not be Enum
HIGH = 2
CRITICAL = 3
diff --git a/cycode/cli/printers/base_printer.py b/cycode/cli/printers/base_printer.py
index afd46513..7b094c65 100644
--- a/cycode/cli/printers/base_printer.py
+++ b/cycode/cli/printers/base_printer.py
@@ -1,9 +1,9 @@
from abc import ABC, abstractmethod
-from typing import List, TYPE_CHECKING
+from typing import TYPE_CHECKING, List
import click
-from cycode.cli.models import CliResult, CliError
+from cycode.cli.models import CliError, CliResult
if TYPE_CHECKING:
from cycode.cli.models import LocalScanResult
diff --git a/cycode/cli/printers/base_table_printer.py b/cycode/cli/printers/base_table_printer.py
index 4a956e66..56a1a552 100644
--- a/cycode/cli/printers/base_table_printer.py
+++ b/cycode/cli/printers/base_table_printer.py
@@ -1,11 +1,11 @@
import abc
-from typing import List, TYPE_CHECKING
+from typing import TYPE_CHECKING, List
import click
-from cycode.cli.printers.text_printer import TextPrinter
from cycode.cli.models import CliError, CliResult
from cycode.cli.printers.base_printer import BasePrinter
+from cycode.cli.printers.text_printer import TextPrinter
if TYPE_CHECKING:
from cycode.cli.models import LocalScanResult
diff --git a/cycode/cli/printers/console_printer.py b/cycode/cli/printers/console_printer.py
index 06e3ddf7..2321f089 100644
--- a/cycode/cli/printers/console_printer.py
+++ b/cycode/cli/printers/console_printer.py
@@ -1,11 +1,12 @@
+from typing import TYPE_CHECKING, ClassVar, Dict, List
+
import click
-from typing import List, TYPE_CHECKING
from cycode.cli.exceptions.custom_exceptions import CycodeError
-from cycode.cli.models import CliResult, CliError
-from cycode.cli.printers.table_printer import TablePrinter
-from cycode.cli.printers.sca_table_printer import SCATablePrinter
+from cycode.cli.models import CliError, CliResult
from cycode.cli.printers.json_printer import JsonPrinter
+from cycode.cli.printers.sca_table_printer import SCATablePrinter
+from cycode.cli.printers.table_printer import TablePrinter
from cycode.cli.printers.text_printer import TextPrinter
if TYPE_CHECKING:
@@ -14,7 +15,7 @@
class ConsolePrinter:
- _AVAILABLE_PRINTERS = {
+ _AVAILABLE_PRINTERS: ClassVar[Dict[str, 'BasePrinter']] = {
'text': TextPrinter,
'json': JsonPrinter,
'table': TablePrinter,
diff --git a/cycode/cli/printers/json_printer.py b/cycode/cli/printers/json_printer.py
index 6469100c..52df39ea 100644
--- a/cycode/cli/printers/json_printer.py
+++ b/cycode/cli/printers/json_printer.py
@@ -1,9 +1,9 @@
import json
-from typing import List, TYPE_CHECKING
+from typing import TYPE_CHECKING, List
import click
-from cycode.cli.models import CliResult, CliError
+from cycode.cli.models import CliError, CliResult
from cycode.cli.printers.base_printer import BasePrinter
from cycode.cyclient.models import DetectionSchema
diff --git a/cycode/cli/printers/sca_table_printer.py b/cycode/cli/printers/sca_table_printer.py
index a8372873..b3b03567 100644
--- a/cycode/cli/printers/sca_table_printer.py
+++ b/cycode/cli/printers/sca_table_printer.py
@@ -1,5 +1,5 @@
from collections import defaultdict
-from typing import List, Dict, TYPE_CHECKING
+from typing import TYPE_CHECKING, Dict, List
import click
from texttable import Texttable
@@ -59,7 +59,7 @@ def _print_detection_per_detection_type_id(
if detection_type_id == PACKAGE_VULNERABILITY_POLICY_ID:
title = 'Dependencies Vulnerabilities'
- headers = [SEVERITY_COLUMN] + headers
+ headers = [SEVERITY_COLUMN, *headers]
headers.extend(PREVIEW_DETECTIONS_COMMON_HEADERS)
headers.append(CVE_COLUMN)
headers.append(UPGRADE_COLUMN)
@@ -129,7 +129,7 @@ def _get_common_detection_fields(self, detection: Detection) -> List[str]:
]
if self._is_git_repository():
- row = [detection.detection_details.get('repository_name')] + row
+ row = [detection.detection_details.get('repository_name'), *row]
return row
diff --git a/cycode/cli/printers/table.py b/cycode/cli/printers/table.py
index 3677ec05..d2847399 100644
--- a/cycode/cli/printers/table.py
+++ b/cycode/cli/printers/table.py
@@ -1,4 +1,5 @@
-from typing import List, Dict, Optional, TYPE_CHECKING
+from typing import TYPE_CHECKING, Dict, List, Optional
+
from texttable import Texttable
if TYPE_CHECKING:
@@ -11,12 +12,12 @@ class Table:
def __init__(self, column_infos: Optional[List['ColumnInfo']] = None):
self._column_widths = None
- self._columns: Dict['ColumnInfo', List[str]] = dict()
+ self._columns: Dict['ColumnInfo', List[str]] = {}
if column_infos:
- self._columns: Dict['ColumnInfo', List[str]] = {columns: list() for columns in column_infos}
+ self._columns: Dict['ColumnInfo', List[str]] = {columns: [] for columns in column_infos}
def add(self, column: 'ColumnInfo') -> None:
- self._columns[column] = list()
+ self._columns[column] = []
def set(self, column: 'ColumnInfo', value: str) -> None:
# we push values only for existing columns what were added before
diff --git a/cycode/cli/printers/table_models.py b/cycode/cli/printers/table_models.py
index 34859e06..e3dc195d 100644
--- a/cycode/cli/printers/table_models.py
+++ b/cycode/cli/printers/table_models.py
@@ -1,4 +1,4 @@
-from typing import NamedTuple, Dict
+from typing import Dict, NamedTuple
class ColumnInfoBuilder:
diff --git a/cycode/cli/printers/table_printer.py b/cycode/cli/printers/table_printer.py
index 3e5e6d49..c5a01201 100644
--- a/cycode/cli/printers/table_printer.py
+++ b/cycode/cli/printers/table_printer.py
@@ -1,13 +1,13 @@
-from typing import List, TYPE_CHECKING
+from typing import TYPE_CHECKING, List
import click
+from cycode.cli.consts import INFRA_CONFIGURATION_SCAN_TYPE, SAST_SCAN_TYPE, SECRET_SCAN_TYPE
+from cycode.cli.models import Detection, Document
from cycode.cli.printers.base_table_printer import BaseTablePrinter
-from cycode.cli.printers.table_models import ColumnInfoBuilder, ColumnWidthsConfig
from cycode.cli.printers.table import Table
-from cycode.cli.utils.string_utils import obfuscate_text, get_position_in_line
-from cycode.cli.consts import SECRET_SCAN_TYPE, INFRA_CONFIGURATION_SCAN_TYPE, SAST_SCAN_TYPE
-from cycode.cli.models import Detection, Document
+from cycode.cli.printers.table_models import ColumnInfoBuilder, ColumnWidthsConfig
+from cycode.cli.utils.string_utils import get_position_in_line, obfuscate_text
if TYPE_CHECKING:
from cycode.cli.models import LocalScanResult
diff --git a/cycode/cli/printers/text_printer.py b/cycode/cli/printers/text_printer.py
index de71371d..4555225d 100644
--- a/cycode/cli/printers/text_printer.py
+++ b/cycode/cli/printers/text_printer.py
@@ -1,13 +1,13 @@
import math
-from typing import List, Optional, TYPE_CHECKING
+from typing import TYPE_CHECKING, List, Optional
import click
-from cycode.cli.printers.base_printer import BasePrinter
-from cycode.cli.models import DocumentDetections, Detection, Document, CliResult, CliError
from cycode.cli.config import config
-from cycode.cli.consts import SECRET_SCAN_TYPE, COMMIT_RANGE_BASED_COMMAND_SCAN_TYPES
-from cycode.cli.utils.string_utils import obfuscate_text, get_position_in_line
+from cycode.cli.consts import COMMIT_RANGE_BASED_COMMAND_SCAN_TYPES, SECRET_SCAN_TYPE
+from cycode.cli.models import CliError, CliResult, Detection, Document, DocumentDetections
+from cycode.cli.printers.base_printer import BasePrinter
+from cycode.cli.utils.string_utils import get_position_in_line, obfuscate_text
if TYPE_CHECKING:
from cycode.cli.models import LocalScanResult
@@ -98,11 +98,12 @@ def _print_line_of_code_segment(
def _print_detection_line(
self, document: Document, line: str, line_number: int, detection_position_in_line: int, violation_length: int
) -> None:
- click.echo(
- f'{self._get_line_number_style(line_number)} '
- f'{self._get_detection_line_style(line, document.is_git_diff_format, detection_position_in_line, violation_length)}'
+ detection_line = self._get_detection_line_style(
+ line, document.is_git_diff_format, detection_position_in_line, violation_length
)
+ click.echo(f'{self._get_line_number_style(line_number)} {detection_line}')
+
def _print_line(self, document: Document, line: str, line_number: int):
line_no = self._get_line_number_style(line_number)
line = self._get_line_style(line, document.is_git_diff_format)
diff --git a/cycode/cli/user_settings/base_file_manager.py b/cycode/cli/user_settings/base_file_manager.py
index ec7c4813..a640d8fa 100644
--- a/cycode/cli/user_settings/base_file_manager.py
+++ b/cycode/cli/user_settings/base_file_manager.py
@@ -1,6 +1,7 @@
import os
from abc import ABC, abstractmethod
-from cycode.cli.utils.yaml_utils import update_file, read_file
+
+from cycode.cli.utils.yaml_utils import read_file, update_file
class BaseFileManager(ABC):
diff --git a/cycode/cli/user_settings/config_file_manager.py b/cycode/cli/user_settings/config_file_manager.py
index 876f85f1..5d2e3016 100644
--- a/cycode/cli/user_settings/config_file_manager.py
+++ b/cycode/cli/user_settings/config_file_manager.py
@@ -1,8 +1,8 @@
import os
-from typing import Optional, List, Dict
+from typing import Dict, List, Optional
-from cycode.cli.user_settings.base_file_manager import BaseFileManager
from cycode.cli.consts import CYCODE_CONFIGURATION_DIRECTORY
+from cycode.cli.user_settings.base_file_manager import BaseFileManager
class ConfigFileManager(BaseFileManager):
@@ -36,8 +36,7 @@ def get_verbose_flag(self) -> Optional[bool]:
def get_exclusions_by_scan_type(self, scan_type) -> Dict:
exclusions_section = self._get_section(self.EXCLUSIONS_SECTION_NAME)
- scan_type_exclusions = exclusions_section.get(scan_type, {})
- return scan_type_exclusions
+ return exclusions_section.get(scan_type, {})
def get_max_commits(self, command_scan_type) -> Optional[int]:
return self._get_value_from_command_scan_type_configuration(command_scan_type, self.MAX_COMMITS_FIELD_NAME)
@@ -87,8 +86,7 @@ def _get_exclusions_by_exclusion_type(self, scan_type, exclusion_type) -> List:
def _get_value_from_environment_section(self, field_name: str):
environment_section = self._get_section(self.ENVIRONMENT_SECTION_NAME)
- value = environment_section.get(field_name)
- return value
+ return environment_section.get(field_name)
def _get_scan_configuration_by_scan_type(self, command_scan_type: str) -> Dict:
scan_section = self._get_section(self.SCAN_SECTION_NAME)
@@ -96,8 +94,7 @@ def _get_scan_configuration_by_scan_type(self, command_scan_type: str) -> Dict:
def _get_value_from_command_scan_type_configuration(self, command_scan_type: str, field_name: str):
command_scan_type_configuration = self._get_scan_configuration_by_scan_type(command_scan_type)
- value = command_scan_type_configuration.get(field_name)
- return value
+ return command_scan_type_configuration.get(field_name)
def _get_section(self, section_name: str) -> Dict:
file_content = self.read_file()
diff --git a/cycode/cli/user_settings/configuration_manager.py b/cycode/cli/user_settings/configuration_manager.py
index fa11c87a..f93759c9 100644
--- a/cycode/cli/user_settings/configuration_manager.py
+++ b/cycode/cli/user_settings/configuration_manager.py
@@ -1,10 +1,10 @@
import os
from pathlib import Path
-from typing import Optional, Dict
+from typing import Dict, Optional
from uuid import uuid4
+from cycode.cli import consts
from cycode.cli.user_settings.config_file_manager import ConfigFileManager
-from cycode.cli.consts import *
class ConfigurationManager:
@@ -28,7 +28,7 @@ def get_cycode_api_url(self) -> str:
if api_url is not None:
return api_url
- return DEFAULT_CYCODE_API_URL
+ return consts.DEFAULT_CYCODE_API_URL
def get_cycode_app_url(self) -> str:
app_url = self.get_app_url_from_environment_variables()
@@ -43,7 +43,7 @@ def get_cycode_app_url(self) -> str:
if app_url is not None:
return app_url
- return DEFAULT_CYCODE_APP_URL
+ return consts.DEFAULT_CYCODE_APP_URL
def get_verbose_flag(self) -> bool:
verbose_flag_env_var = self.get_verbose_flag_from_environment_variables()
@@ -52,13 +52,13 @@ def get_verbose_flag(self) -> bool:
return verbose_flag_env_var or verbose_flag_local_config or verbose_flag_global_config
def get_api_url_from_environment_variables(self) -> Optional[str]:
- return self._get_value_from_environment_variables(CYCODE_API_URL_ENV_VAR_NAME)
+ return self._get_value_from_environment_variables(consts.CYCODE_API_URL_ENV_VAR_NAME)
def get_app_url_from_environment_variables(self) -> Optional[str]:
- return self._get_value_from_environment_variables(CYCODE_APP_URL_ENV_VAR_NAME)
+ return self._get_value_from_environment_variables(consts.CYCODE_APP_URL_ENV_VAR_NAME)
def get_verbose_flag_from_environment_variables(self) -> bool:
- value = self._get_value_from_environment_variables(VERBOSE_ENV_VAR_NAME, '')
+ value = self._get_value_from_environment_variables(consts.VERBOSE_ENV_VAR_NAME, '')
return value.lower() in ('true', '1')
def get_exclusions_by_scan_type(self, scan_type) -> Dict:
@@ -97,19 +97,21 @@ def get_config_file_manager(self, scope: Optional[str] = None) -> ConfigFileMana
def get_scan_polling_timeout_in_seconds(self) -> int:
return int(
self._get_value_from_environment_variables(
- SCAN_POLLING_TIMEOUT_IN_SECONDS_ENV_VAR_NAME, DEFAULT_SCAN_POLLING_TIMEOUT_IN_SECONDS
+ consts.SCAN_POLLING_TIMEOUT_IN_SECONDS_ENV_VAR_NAME, consts.DEFAULT_SCAN_POLLING_TIMEOUT_IN_SECONDS
)
)
def get_sca_pre_commit_timeout_in_seconds(self) -> int:
return int(
self._get_value_from_environment_variables(
- SCA_PRE_COMMIT_TIMEOUT_IN_SECONDS_ENV_VAR_NAME, DEFAULT_SCA_PRE_COMMIT_TIMEOUT_IN_SECONDS
+ consts.SCA_PRE_COMMIT_TIMEOUT_IN_SECONDS_ENV_VAR_NAME, consts.DEFAULT_SCA_PRE_COMMIT_TIMEOUT_IN_SECONDS
)
)
def get_pre_receive_max_commits_to_scan_count(self, command_scan_type: str) -> int:
- max_commits = self._get_value_from_environment_variables(PRE_RECEIVE_MAX_COMMITS_TO_SCAN_COUNT_ENV_VAR_NAME)
+ max_commits = self._get_value_from_environment_variables(
+ consts.PRE_RECEIVE_MAX_COMMITS_TO_SCAN_COUNT_ENV_VAR_NAME
+ )
if max_commits is not None:
return int(max_commits)
@@ -121,10 +123,10 @@ def get_pre_receive_max_commits_to_scan_count(self, command_scan_type: str) -> i
if max_commits is not None:
return max_commits
- return DEFAULT_PRE_RECEIVE_MAX_COMMITS_TO_SCAN_COUNT
+ return consts.DEFAULT_PRE_RECEIVE_MAX_COMMITS_TO_SCAN_COUNT
def get_pre_receive_command_timeout(self, command_scan_type: str) -> int:
- command_timeout = self._get_value_from_environment_variables(PRE_RECEIVE_COMMAND_TIMEOUT_ENV_VAR_NAME)
+ command_timeout = self._get_value_from_environment_variables(consts.PRE_RECEIVE_COMMAND_TIMEOUT_ENV_VAR_NAME)
if command_timeout is not None:
return int(command_timeout)
@@ -136,11 +138,11 @@ def get_pre_receive_command_timeout(self, command_scan_type: str) -> int:
if command_timeout is not None:
return command_timeout
- return DEFAULT_PRE_RECEIVE_COMMAND_TIMEOUT_IN_SECONDS
+ return consts.DEFAULT_PRE_RECEIVE_COMMAND_TIMEOUT_IN_SECONDS
def get_should_exclude_detections_in_deleted_lines(self, command_scan_type: str) -> bool:
exclude_detections_in_deleted_lines = self._get_value_from_environment_variables(
- EXCLUDE_DETECTIONS_IN_DELETED_LINES_ENV_VAR_NAME
+ consts.EXCLUDE_DETECTIONS_IN_DELETED_LINES_ENV_VAR_NAME
)
if exclude_detections_in_deleted_lines is not None:
return exclude_detections_in_deleted_lines.lower() in ('true', '1')
@@ -157,7 +159,7 @@ def get_should_exclude_detections_in_deleted_lines(self, command_scan_type: str)
if exclude_detections_in_deleted_lines is not None:
return exclude_detections_in_deleted_lines
- return DEFAULT_EXCLUDE_DETECTIONS_IN_DELETED_LINES
+ return consts.DEFAULT_EXCLUDE_DETECTIONS_IN_DELETED_LINES
@staticmethod
def _get_value_from_environment_variables(env_var_name, default=None):
diff --git a/cycode/cli/user_settings/credentials_manager.py b/cycode/cli/user_settings/credentials_manager.py
index 675deae2..0ec0e6e8 100644
--- a/cycode/cli/user_settings/credentials_manager.py
+++ b/cycode/cli/user_settings/credentials_manager.py
@@ -1,9 +1,9 @@
import os
from pathlib import Path
-from cycode.cli.utils.yaml_utils import read_file
from cycode.cli.config import CYCODE_CLIENT_ID_ENV_VAR_NAME, CYCODE_CLIENT_SECRET_ENV_VAR_NAME
from cycode.cli.user_settings.base_file_manager import BaseFileManager
+from cycode.cli.utils.yaml_utils import read_file
class CredentialsManager(BaseFileManager):
@@ -39,7 +39,7 @@ def get_credentials_from_file(self) -> (str, str):
def update_credentials_file(self, client_id: str, client_secret: str):
credentials = {self.CLIENT_ID_FIELD_NAME: client_id, self.CLIENT_SECRET_FIELD_NAME: client_secret}
- filename = self.get_filename()
+ self.get_filename()
self.write_content_to_file(credentials)
def get_filename(self) -> str:
diff --git a/cycode/cli/user_settings/user_settings_commands.py b/cycode/cli/user_settings/user_settings_commands.py
index a7863671..f4fb5bee 100644
--- a/cycode/cli/user_settings/user_settings_commands.py
+++ b/cycode/cli/user_settings/user_settings_commands.py
@@ -1,14 +1,14 @@
-import re
import os.path
+import re
from typing import Optional
import click
-from cycode.cli.utils.string_utils import obfuscate_text, hash_string_to_sha256
-from cycode.cli.utils.path_utils import get_absolute_path
+from cycode.cli import consts
+from cycode.cli.config import config, configuration_manager
from cycode.cli.user_settings.credentials_manager import CredentialsManager
-from cycode.cli.config import configuration_manager, config
-from cycode.cli.consts import *
+from cycode.cli.utils.path_utils import get_absolute_path
+from cycode.cli.utils.string_utils import hash_string_to_sha256, obfuscate_text
from cycode.cyclient import logger
CREDENTIALS_UPDATED_SUCCESSFULLY_MESSAGE = 'Successfully configured CLI credentials!'
@@ -21,9 +21,10 @@
credentials_manager = CredentialsManager()
-@click.command()
+@click.command(
+ short_help='Initial command to authenticate your CLI client with Cycode using client ID and client secret'
+)
def set_credentials():
- """Initial command to authenticate your CLI client with Cycode using client ID and client secret"""
click.echo(f'Update credentials in file ({credentials_manager.get_filename()})')
current_client_id, current_client_secret = credentials_manager.get_credentials_from_file()
client_id = _get_client_id_input(current_client_id)
@@ -38,25 +39,25 @@ def set_credentials():
@click.command()
@click.option(
- "--by-value", type=click.STRING, required=False, help="Ignore a specific value while scanning for secrets"
+ '--by-value', type=click.STRING, required=False, help='Ignore a specific value while scanning for secrets'
)
@click.option(
- "--by-sha",
+ '--by-sha',
type=click.STRING,
required=False,
help='Ignore a specific SHA512 representation of a string while scanning for secrets',
)
@click.option(
- "--by-path", type=click.STRING, required=False, help='Avoid scanning a specific path. Need to specify scan type '
+ '--by-path', type=click.STRING, required=False, help='Avoid scanning a specific path. Need to specify scan type '
)
@click.option(
- "--by-rule",
+ '--by-rule',
type=click.STRING,
required=False,
help='Ignore scanning a specific secret rule ID/IaC rule ID. Need to specify scan type.',
)
@click.option(
- "--by-package",
+ '--by-package',
type=click.STRING,
required=False,
help='Ignore scanning a specific package version while running SCA scan. expected pattern - name@version',
@@ -67,7 +68,7 @@ def set_credentials():
default='secret',
help="""
\b
- Specify the scan you wish to execute (secrets/iac),
+ Specify the scan you wish to execute (secrets/iac),
the default is secrets
""",
type=click.Choice(config['scans']['supported_scans']),
@@ -87,33 +88,32 @@ def add_exclusions(
):
"""Ignore a specific value, path or rule ID"""
if not by_value and not by_sha and not by_path and not by_rule and not by_package:
- raise click.ClickException("ignore by type is missing")
+ raise click.ClickException('ignore by type is missing')
+
+ if any(by is not None for by in [by_value, by_sha]) and scan_type != consts.SECRET_SCAN_TYPE:
+ raise click.ClickException('this exclude is supported only for secret scan type')
if by_value is not None:
- if scan_type != SECRET_SCAN_TYPE:
- raise click.ClickException("exclude by value is supported only for secret scan type")
- exclusion_type = EXCLUSIONS_BY_VALUE_SECTION_NAME
+ exclusion_type = consts.EXCLUSIONS_BY_VALUE_SECTION_NAME
exclusion_value = hash_string_to_sha256(by_value)
elif by_sha is not None:
- if scan_type != SECRET_SCAN_TYPE:
- raise click.ClickException("exclude by sha is supported only for secret scan type")
- exclusion_type = EXCLUSIONS_BY_SHA_SECTION_NAME
+ exclusion_type = consts.EXCLUSIONS_BY_SHA_SECTION_NAME
exclusion_value = by_sha
elif by_path is not None:
absolute_path = get_absolute_path(by_path)
if not _is_path_to_ignore_exists(absolute_path):
- raise click.ClickException("the provided path to ignore by is not exist")
- exclusion_type = EXCLUSIONS_BY_PATH_SECTION_NAME
+ raise click.ClickException('the provided path to ignore by is not exist')
+ exclusion_type = consts.EXCLUSIONS_BY_PATH_SECTION_NAME
exclusion_value = get_absolute_path(absolute_path)
elif by_package is not None:
- if scan_type != SCA_SCAN_TYPE:
- raise click.ClickException("exclude by package is supported only for sca scan type")
+ if scan_type != consts.SCA_SCAN_TYPE:
+ raise click.ClickException('exclude by package is supported only for sca scan type')
if not _is_package_pattern_valid(by_package):
- raise click.ClickException("wrong package pattern. should be name@version.")
- exclusion_type = EXCLUSIONS_BY_PACKAGE_SECTION_NAME
+ raise click.ClickException('wrong package pattern. should be name@version.')
+ exclusion_type = consts.EXCLUSIONS_BY_PACKAGE_SECTION_NAME
exclusion_value = by_package
else:
- exclusion_type = EXCLUSIONS_BY_RULE_SECTION_NAME
+ exclusion_type = consts.EXCLUSIONS_BY_RULE_SECTION_NAME
exclusion_value = by_rule
configuration_scope = 'global' if is_global else 'local'
@@ -133,14 +133,14 @@ def _get_client_id_input(current_client_id: str) -> str:
f'cycode client id [{_obfuscate_credential(current_client_id)}]', default='', show_default=False
)
- return current_client_id if not new_client_id else new_client_id
+ return new_client_id if new_client_id else current_client_id
def _get_client_secret_input(current_client_secret: str) -> str:
new_client_secret = click.prompt(
f'cycode client secret [{_obfuscate_credential(current_client_secret)}]', default='', show_default=False
)
- return current_client_secret if not new_client_secret else new_client_secret
+ return new_client_secret if new_client_secret else current_client_secret
def _get_credentials_update_result_message():
@@ -170,4 +170,4 @@ def _is_path_to_ignore_exists(path: str) -> bool:
def _is_package_pattern_valid(package: str) -> bool:
- return re.search("^[^@]+@[^@]+$", package) is not None
+ return re.search('^[^@]+@[^@]+$', package) is not None
diff --git a/cycode/cli/utils/path_utils.py b/cycode/cli/utils/path_utils.py
index f6bef61b..3522807a 100644
--- a/cycode/cli/utils/path_utils.py
+++ b/cycode/cli/utils/path_utils.py
@@ -1,7 +1,8 @@
-from typing import Iterable, List, Optional, AnyStr
-import pathspec
import os
from pathlib import Path
+from typing import AnyStr, Iterable, List, Optional
+
+import pathspec
from binaryornot.check import is_binary
@@ -50,7 +51,7 @@ def get_path_by_os(filename: str) -> str:
def _get_all_existing_files_in_directory(path: str):
directory = Path(path)
- return directory.rglob(r"*")
+ return directory.rglob(r'*')
def is_path_exists(path: str):
@@ -68,7 +69,6 @@ def join_paths(path: str, filename: str) -> str:
def get_file_content(file_path: str) -> Optional[AnyStr]:
try:
with open(file_path, 'r', encoding='UTF-8') as f:
- content = f.read()
- return content
+ return f.read()
except (FileNotFoundError, UnicodeDecodeError):
return None
diff --git a/cycode/cli/utils/progress_bar.py b/cycode/cli/utils/progress_bar.py
index 010405ef..38e00984 100644
--- a/cycode/cli/utils/progress_bar.py
+++ b/cycode/cli/utils/progress_bar.py
@@ -1,11 +1,11 @@
from abc import ABC, abstractmethod
from enum import auto
-from typing import NamedTuple, Dict, TYPE_CHECKING, Optional
+from typing import TYPE_CHECKING, Dict, NamedTuple, Optional
import click
-from cycode.cyclient.config import get_logger
from cycode.cli.utils.enum_utils import AutoCountEnum
+from cycode.cyclient.config import get_logger
if TYPE_CHECKING:
from click._termui_impl import ProgressBar
@@ -16,7 +16,6 @@
class ProgressBarSection(AutoCountEnum):
PREPARE_LOCAL_FILES = auto()
- # UPLOAD_FILES = auto()
SCAN = auto()
GENERATE_REPORT = auto()
@@ -42,7 +41,6 @@ class ProgressBarSectionInfo(NamedTuple):
),
# TODO(MarshalX): could be added in the future
# ProgressBarSection.UPLOAD_FILES: ProgressBarSectionInfo(
- # ProgressBarSection.UPLOAD_FILES, 'Upload files', start_percent=5, stop_percent=10
# ),
ProgressBarSection.SCAN: ProgressBarSectionInfo(
ProgressBarSection.SCAN, 'Scan in progress', start_percent=5, stop_percent=95
@@ -58,6 +56,7 @@ def _get_section_length(section: 'ProgressBarSection') -> int:
class BaseProgressBar(ABC):
+ @abstractmethod
def __init__(self, *args, **kwargs):
pass
@@ -221,17 +220,17 @@ def get_progress_bar(*, hidden: bool) -> BaseProgressBar:
if __name__ == '__main__':
# TODO(MarshalX): cover with tests and remove this code
- import time
import random
+ import time
bar = get_progress_bar(hidden=False)
bar.start()
for bar_section in ProgressBarSection:
- section_capacity = random.randint(500, 1000)
+ section_capacity = random.randint(500, 1000) # noqa: S311
bar.set_section_length(bar_section, section_capacity)
- for i in range(section_capacity):
+ for _i in range(section_capacity):
time.sleep(0.01)
bar.update(bar_section)
diff --git a/cycode/cli/utils/scan_batch.py b/cycode/cli/utils/scan_batch.py
index b5f1c5d2..0f47c30c 100644
--- a/cycode/cli/utils/scan_batch.py
+++ b/cycode/cli/utils/scan_batch.py
@@ -1,18 +1,18 @@
import os
from multiprocessing.pool import ThreadPool
-from typing import List, TYPE_CHECKING, Callable, Tuple, Dict
+from typing import TYPE_CHECKING, Callable, Dict, List, Tuple
from cycode.cli.consts import (
- SCAN_BATCH_MAX_SIZE_IN_BYTES,
SCAN_BATCH_MAX_FILES_COUNT,
- SCAN_BATCH_SCANS_PER_CPU,
SCAN_BATCH_MAX_PARALLEL_SCANS,
+ SCAN_BATCH_MAX_SIZE_IN_BYTES,
+ SCAN_BATCH_SCANS_PER_CPU,
)
from cycode.cli.models import Document
from cycode.cli.utils.progress_bar import ProgressBarSection
if TYPE_CHECKING:
- from cycode.cli.models import LocalScanResult, CliError
+ from cycode.cli.models import CliError, LocalScanResult
from cycode.cli.utils.progress_bar import BaseProgressBar
diff --git a/cycode/cli/utils/shell_executor.py b/cycode/cli/utils/shell_executor.py
index 512d7432..6b992738 100644
--- a/cycode/cli/utils/shell_executor.py
+++ b/cycode/cli/utils/shell_executor.py
@@ -17,7 +17,7 @@ def shell(
result = subprocess.run(
command,
timeout=timeout,
- shell=execute_in_shell,
+ shell=execute_in_shell, # noqa: S603
check=True,
capture_output=True,
)
@@ -25,9 +25,9 @@ def shell(
return result.stdout.decode('UTF-8').strip()
except subprocess.CalledProcessError as e:
logger.debug(f'Error occurred while running shell command. Exception: {e.stderr}')
- except subprocess.TimeoutExpired:
- raise click.Abort(f'Command "{command}" timed out')
+ except subprocess.TimeoutExpired as e:
+ raise click.Abort(f'Command "{command}" timed out') from e
except Exception as e:
- raise click.ClickException(f'Unhandled exception: {e}')
+ raise click.ClickException(f'Unhandled exception: {e}') from e
return None
diff --git a/cycode/cli/utils/string_utils.py b/cycode/cli/utils/string_utils.py
index f301f9ac..790f65b2 100644
--- a/cycode/cli/utils/string_utils.py
+++ b/cycode/cli/utils/string_utils.py
@@ -1,9 +1,10 @@
import hashlib
import math
-import re
import random
+import re
import string
from sys import getsizeof
+
from binaryornot.check import is_binary_string
from cycode.cli.consts import SCA_SHORTCUT_DEPENDENCY_PATHS
@@ -14,12 +15,12 @@ def obfuscate_text(text: str) -> str:
start_reveled_len = math.ceil(match_len / 8)
end_reveled_len = match_len - (math.ceil(match_len / 8))
- obfuscated = obfuscate_regex.sub("*", text)
+ obfuscated = obfuscate_regex.sub('*', text)
return f'{text[:start_reveled_len]}{obfuscated[start_reveled_len:end_reveled_len]}{text[end_reveled_len:]}'
-obfuscate_regex = re.compile(r"[^+\-\s]")
+obfuscate_regex = re.compile(r'[^+\-\s]')
def is_binary_content(content: str) -> bool:
@@ -34,7 +35,7 @@ def get_content_size(content: str):
def convert_string_to_bytes(content: str):
- return bytes(content, 'utf-8')
+ return bytes(content, 'UTF-8')
def hash_string_to_sha256(content: str):
@@ -44,7 +45,7 @@ def hash_string_to_sha256(content: str):
def generate_random_string(string_len: int):
# letters, digits, and symbols
characters = string.ascii_letters + string.digits + string.punctuation
- return ''.join(random.choice(characters) for _ in range(string_len))
+ return ''.join(random.choice(characters) for _ in range(string_len)) # noqa: S311
def get_position_in_line(text: str, position: int) -> int:
diff --git a/cycode/cli/utils/task_timer.py b/cycode/cli/utils/task_timer.py
index 7d8efd9e..d6399ba7 100644
--- a/cycode/cli/utils/task_timer.py
+++ b/cycode/cli/utils/task_timer.py
@@ -1,11 +1,11 @@
-from threading import Thread, Event
from _thread import interrupt_main
-from typing import Optional, Callable, List, Dict, Type
+from threading import Event, Thread
from types import TracebackType
+from typing import Callable, Dict, List, Optional, Type
class FunctionContext:
- def __init__(self, function: Callable, args: List = None, kwargs: Dict = None):
+ def __init__(self, function: Callable, args: Optional[List] = None, kwargs: Optional[Dict] = None):
self.function = function
self.args = args or []
self.kwargs = kwargs or {}
@@ -74,7 +74,7 @@ def __exit__(
# catch the exception of interrupt_main before exiting
# the with statement and throw timeout error instead
if exc_type == KeyboardInterrupt:
- raise TimeoutError(f"Task timed out after {self.timeout} seconds")
+ raise TimeoutError(f'Task timed out after {self.timeout} seconds')
def timeout_function(self):
interrupt_main()
diff --git a/cycode/cli/utils/yaml_utils.py b/cycode/cli/utils/yaml_utils.py
index e1732ef8..b9e9f408 100644
--- a/cycode/cli/utils/yaml_utils.py
+++ b/cycode/cli/utils/yaml_utils.py
@@ -1,20 +1,21 @@
-import yaml
from typing import Dict
+import yaml
+
def read_file(filename: str) -> Dict:
- with open(filename, 'r', encoding="utf-8") as file:
+ with open(filename, 'r', encoding='UTF-8') as file:
return yaml.safe_load(file)
def update_file(filename: str, content: Dict):
try:
- with open(filename, 'r', encoding="utf-8") as file:
+ with open(filename, 'r', encoding='UTF-8') as file:
file_content = yaml.safe_load(file)
except FileNotFoundError:
file_content = {}
- with open(filename, 'w', encoding="utf-8") as file:
+ with open(filename, 'w', encoding='UTF-8') as file:
file_content = _deep_update(file_content, content)
yaml.safe_dump(file_content, file)
diff --git a/cycode/cli/zip_file.py b/cycode/cli/zip_file.py
index a177b6b7..d4c5c3fc 100644
--- a/cycode/cli/zip_file.py
+++ b/cycode/cli/zip_file.py
@@ -1,13 +1,13 @@
import os.path
-from zipfile import ZipFile, ZIP_DEFLATED
from io import BytesIO
+from zipfile import ZIP_DEFLATED, ZipFile
class InMemoryZip(object):
def __init__(self):
# Create the in-memory file-like object
self.in_memory_zip = BytesIO()
- self.zip = ZipFile(self.in_memory_zip, "a", ZIP_DEFLATED, False)
+ self.zip = ZipFile(self.in_memory_zip, 'a', ZIP_DEFLATED, False)
def append(self, filename, unique_id, content):
# Write the file to the in-memory zip
diff --git a/cycode/cyclient/__init__.py b/cycode/cyclient/__init__.py
index f33d4b71..7018a231 100644
--- a/cycode/cyclient/__init__.py
+++ b/cycode/cyclient/__init__.py
@@ -1,6 +1,5 @@
from .config import logger
-
__all__ = [
- "logger",
+ 'logger',
]
diff --git a/cycode/cyclient/auth_client.py b/cycode/cyclient/auth_client.py
index 379e9bf1..5717c583 100644
--- a/cycode/cyclient/auth_client.py
+++ b/cycode/cyclient/auth_client.py
@@ -2,9 +2,10 @@
from requests import Response
-from .cycode_client import CycodeClient
+from cycode.cli.exceptions.custom_exceptions import HttpUnauthorizedError, NetworkError
+
from . import models
-from cycode.cli.exceptions.custom_exceptions import NetworkError, HttpUnauthorizedError
+from .cycode_client import CycodeClient
class AuthClient:
diff --git a/cycode/cyclient/config.py b/cycode/cyclient/config.py
index a73fc9d7..c6ed6432 100644
--- a/cycode/cyclient/config.py
+++ b/cycode/cyclient/config.py
@@ -3,37 +3,37 @@
import sys
from urllib.parse import urlparse
-from cycode.cli.consts import *
+from cycode.cli import consts
from cycode.cli.user_settings.configuration_manager import ConfigurationManager
# set io encoding (for windows)
from .config_dev import DEV_MODE_ENV_VAR_NAME, DEV_TENANT_ID_ENV_VAR_NAME
-sys.stdout.reconfigure(encoding='utf-8')
-sys.stderr.reconfigure(encoding='utf-8')
+sys.stdout.reconfigure(encoding='UTF-8')
+sys.stderr.reconfigure(encoding='UTF-8')
# logs
logging.basicConfig(
stream=sys.stdout,
level=logging.DEBUG,
- format="%(asctime)s [%(name)s] %(levelname)s: %(message)s",
- datefmt="%Y-%m-%d %H:%M:%S",
+ format='%(asctime)s [%(name)s] %(levelname)s: %(message)s',
+ datefmt='%Y-%m-%d %H:%M:%S',
)
-logging.getLogger("urllib3").setLevel(logging.WARNING)
-logging.getLogger("werkzeug").setLevel(logging.WARNING)
-logging.getLogger("schedule").setLevel(logging.WARNING)
-logging.getLogger("kubernetes").setLevel(logging.WARNING)
-logging.getLogger("binaryornot").setLevel(logging.WARNING)
-logging.getLogger("chardet").setLevel(logging.WARNING)
-logging.getLogger("git.cmd").setLevel(logging.WARNING)
-logging.getLogger("git.util").setLevel(logging.WARNING)
+logging.getLogger('urllib3').setLevel(logging.WARNING)
+logging.getLogger('werkzeug').setLevel(logging.WARNING)
+logging.getLogger('schedule').setLevel(logging.WARNING)
+logging.getLogger('kubernetes').setLevel(logging.WARNING)
+logging.getLogger('binaryornot').setLevel(logging.WARNING)
+logging.getLogger('chardet').setLevel(logging.WARNING)
+logging.getLogger('git.cmd').setLevel(logging.WARNING)
+logging.getLogger('git.util').setLevel(logging.WARNING)
# configs
DEFAULT_CONFIGURATION = {
- TIMEOUT_ENV_VAR_NAME: 300,
- LOGGING_LEVEL_ENV_VAR_NAME: logging.INFO,
+ consts.TIMEOUT_ENV_VAR_NAME: 300,
+ consts.LOGGING_LEVEL_ENV_VAR_NAME: logging.INFO,
DEV_MODE_ENV_VAR_NAME: 'False',
- BATCH_SIZE_ENV_VAR_NAME: 20,
+ consts.BATCH_SIZE_ENV_VAR_NAME: 20,
}
configuration = dict(DEFAULT_CONFIGURATION, **os.environ)
@@ -41,8 +41,8 @@
def get_logger(logger_name=None):
logger = logging.getLogger(logger_name)
- level = _get_val_as_string(LOGGING_LEVEL_ENV_VAR_NAME)
- level = level if level in logging._nameToLevel.keys() else int(level)
+ level = _get_val_as_string(consts.LOGGING_LEVEL_ENV_VAR_NAME)
+ level = level if level in logging._nameToLevel else int(level)
logger.setLevel(level)
return logger
@@ -62,7 +62,7 @@ def _get_val_as_int(key):
return int(val) if val is not None else None
-logger = get_logger("cycode cli")
+logger = get_logger('cycode cli')
configuration_manager = ConfigurationManager()
@@ -71,10 +71,13 @@ def _get_val_as_int(key):
urlparse(cycode_api_url)
except ValueError as e:
logger.warning(f'Invalid cycode api url: {cycode_api_url}, using default value', e)
- cycode_api_url = DEFAULT_CYCODE_API_URL
+ cycode_api_url = consts.DEFAULT_CYCODE_API_URL
+
+timeout = _get_val_as_int(consts.CYCODE_CLI_REQUEST_TIMEOUT_ENV_VAR_NAME)
+if not timeout:
+ timeout = _get_val_as_int(consts.TIMEOUT_ENV_VAR_NAME)
-timeout = _get_val_as_int(CYCODE_CLI_REQUEST_TIMEOUT_ENV_VAR_NAME) or _get_val_as_int(TIMEOUT_ENV_VAR_NAME)
dev_mode = _get_val_as_bool(DEV_MODE_ENV_VAR_NAME)
dev_tenant_id = _get_val_as_string(DEV_TENANT_ID_ENV_VAR_NAME)
-batch_size = _get_val_as_int(BATCH_SIZE_ENV_VAR_NAME)
-verbose = _get_val_as_bool(VERBOSE_ENV_VAR_NAME)
+batch_size = _get_val_as_int(consts.BATCH_SIZE_ENV_VAR_NAME)
+verbose = _get_val_as_bool(consts.VERBOSE_ENV_VAR_NAME)
diff --git a/cycode/cyclient/config_dev.py b/cycode/cyclient/config_dev.py
index 5913bb16..6345c8f8 100644
--- a/cycode/cyclient/config_dev.py
+++ b/cycode/cyclient/config_dev.py
@@ -1,3 +1,3 @@
-DEV_CYCODE_API_URL = "http://localhost"
-DEV_MODE_ENV_VAR_NAME = "DEV_MODE"
-DEV_TENANT_ID_ENV_VAR_NAME = "DEV_TENANT_ID"
+DEV_CYCODE_API_URL = 'http://localhost'
+DEV_MODE_ENV_VAR_NAME = 'DEV_MODE'
+DEV_TENANT_ID_ENV_VAR_NAME = 'DEV_TENANT_ID'
diff --git a/cycode/cyclient/cycode_client_base.py b/cycode/cyclient/cycode_client_base.py
index e6220ac2..d4c27c0e 100644
--- a/cycode/cyclient/cycode_client_base.py
+++ b/cycode/cyclient/cycode_client_base.py
@@ -1,13 +1,14 @@
import platform
-from typing import Dict
+from typing import ClassVar, Dict, Optional
-from cycode.cyclient import logger
-from requests import Response, request, exceptions
+from requests import Response, exceptions, request
from cycode import __version__
+from cycode.cli.exceptions.custom_exceptions import HttpUnauthorizedError, NetworkError
+from cycode.cli.user_settings.configuration_manager import ConfigurationManager
+from cycode.cyclient import logger
+
from . import config
-from ..cli.exceptions.custom_exceptions import NetworkError, HttpUnauthorizedError
-from ..cli.user_settings.configuration_manager import ConfigurationManager
def get_cli_user_agent() -> str:
@@ -28,7 +29,7 @@ def get_cli_user_agent() -> str:
class CycodeClientBase:
- MANDATORY_HEADERS: Dict[str, str] = {'User-Agent': get_cli_user_agent()}
+ MANDATORY_HEADERS: ClassVar[Dict[str, str]] = {'User-Agent': get_cli_user_agent()}
def __init__(self, api_url: str):
self.timeout = config.timeout
@@ -42,17 +43,17 @@ def reset_user_agent() -> None:
def enrich_user_agent(user_agent_suffix: str) -> None:
CycodeClientBase.MANDATORY_HEADERS['User-Agent'] += f' {user_agent_suffix}'
- def post(self, url_path: str, body: dict = None, headers: dict = None, **kwargs) -> Response:
+ def post(self, url_path: str, body: Optional[dict] = None, headers: Optional[dict] = None, **kwargs) -> Response:
return self._execute(method='post', endpoint=url_path, json=body, headers=headers, **kwargs)
- def put(self, url_path: str, body: dict = None, headers: dict = None, **kwargs) -> Response:
+ def put(self, url_path: str, body: Optional[dict] = None, headers: Optional[dict] = None, **kwargs) -> Response:
return self._execute(method='put', endpoint=url_path, json=body, headers=headers, **kwargs)
- def get(self, url_path: str, headers: dict = None, **kwargs) -> Response:
+ def get(self, url_path: str, headers: Optional[dict] = None, **kwargs) -> Response:
return self._execute(method='get', endpoint=url_path, headers=headers, **kwargs)
def _execute(
- self, method: str, endpoint: str, headers: dict = None, without_auth: bool = False, **kwargs
+ self, method: str, endpoint: str, headers: Optional[dict] = None, without_auth: bool = False, **kwargs
) -> Response:
url = self.build_full_url(self.api_url, endpoint)
logger.debug(f'Executing {method.upper()} request to {url}')
@@ -68,7 +69,7 @@ def _execute(
except Exception as e:
self._handle_exception(e)
- def get_request_headers(self, additional_headers: dict = None, **kwargs) -> dict:
+ def get_request_headers(self, additional_headers: Optional[dict] = None, **kwargs) -> dict:
if additional_headers is None:
return self.MANDATORY_HEADERS.copy()
return {**self.MANDATORY_HEADERS, **additional_headers}
@@ -79,7 +80,8 @@ def build_full_url(self, url: str, endpoint: str) -> str:
def _handle_exception(self, e: Exception):
if isinstance(e, exceptions.Timeout):
raise NetworkError(504, 'Timeout Error', e.response)
- elif isinstance(e, exceptions.HTTPError):
+
+ if isinstance(e, exceptions.HTTPError):
self._handle_http_exception(e)
elif isinstance(e, exceptions.ConnectionError):
raise NetworkError(502, 'Connection Error', e.response)
diff --git a/cycode/cyclient/cycode_dev_based_client.py b/cycode/cyclient/cycode_dev_based_client.py
index 31f182bf..bb647acf 100644
--- a/cycode/cyclient/cycode_dev_based_client.py
+++ b/cycode/cyclient/cycode_dev_based_client.py
@@ -1,3 +1,5 @@
+from typing import Optional
+
from .config import dev_tenant_id
from .cycode_client_base import CycodeClientBase
@@ -10,11 +12,11 @@ class CycodeDevBasedClient(CycodeClientBase):
def __init__(self, api_url):
super().__init__(api_url)
- def get_request_headers(self, additional_headers: dict = None):
+ def get_request_headers(self, additional_headers: Optional[dict] = None):
headers = super().get_request_headers(additional_headers=additional_headers)
headers['X-Tenant-Id'] = dev_tenant_id
return headers
def build_full_url(self, url, endpoint):
- return f"{url}:{endpoint}"
+ return f'{url}:{endpoint}'
diff --git a/cycode/cyclient/cycode_token_based_client.py b/cycode/cyclient/cycode_token_based_client.py
index f1043c57..b8898a41 100644
--- a/cycode/cyclient/cycode_token_based_client.py
+++ b/cycode/cyclient/cycode_token_based_client.py
@@ -1,4 +1,5 @@
from threading import Lock
+from typing import Optional
import arrow
@@ -31,7 +32,7 @@ def refresh_api_token_if_needed(self) -> None:
def refresh_api_token(self) -> None:
auth_response = self.post(
- url_path=f'api/v1/auth/api-token',
+ url_path='api/v1/auth/api-token',
body={'clientId': self.client_id, 'secret': self.client_secret},
without_auth=True,
)
@@ -40,7 +41,7 @@ def refresh_api_token(self) -> None:
self._api_token = auth_response_data['token']
self._expires_in = arrow.utcnow().shift(seconds=auth_response_data['expires_in'] * 0.8)
- def get_request_headers(self, additional_headers: dict = None, without_auth=False) -> dict:
+ def get_request_headers(self, additional_headers: Optional[dict] = None, without_auth=False) -> dict:
headers = super().get_request_headers(additional_headers=additional_headers)
if not without_auth:
diff --git a/cycode/cyclient/models.py b/cycode/cyclient/models.py
index 330fd2d9..89e39b11 100644
--- a/cycode/cyclient/models.py
+++ b/cycode/cyclient/models.py
@@ -1,6 +1,7 @@
from dataclasses import dataclass
-from typing import List, Dict, Optional
-from marshmallow import Schema, fields, EXCLUDE, post_load
+from typing import Dict, List, Optional
+
+from marshmallow import EXCLUDE, Schema, fields, post_load
class Detection(Schema):
@@ -26,7 +27,7 @@ def __repr__(self) -> str:
f'type:{self.type}, '
f'severity:{self.severity}, '
f'message:{self.message}, '
- f'detection_details:{repr(self.detection_details)}, '
+ f'detection_details:{self.detection_details!r}, '
f'detection_rule_id:{self.detection_rule_id}'
)
@@ -75,8 +76,8 @@ def __init__(
did_detect: bool,
detections_per_file: List[DetectionsPerFile],
report_url: Optional[str] = None,
- scan_id: str = None,
- err: str = None,
+ scan_id: Optional[str] = None,
+ err: Optional[str] = None,
):
super().__init__()
self.did_detect = did_detect
@@ -102,7 +103,13 @@ def build_dto(self, data, **kwargs):
class ScanResult(Schema):
- def __init__(self, did_detect: bool, scan_id: str = None, detections: List[Detection] = None, err: str = None):
+ def __init__(
+ self,
+ did_detect: bool,
+ scan_id: Optional[str] = None,
+ detections: Optional[List[Detection]] = None,
+ err: Optional[str] = None,
+ ):
super().__init__()
self.did_detect = did_detect
self.scan_id = scan_id
@@ -125,7 +132,7 @@ def build_dto(self, data, **kwargs):
class ScanInitializationResponse(Schema):
- def __init__(self, scan_id: str = None, err: str = None):
+ def __init__(self, scan_id: Optional[str] = None, err: Optional[str] = None):
super().__init__()
self.scan_id = scan_id
self.err = err
@@ -146,13 +153,13 @@ def build_dto(self, data, **kwargs):
class ScanDetailsResponse(Schema):
def __init__(
self,
- id: str = None,
- scan_status: str = None,
- results_count: int = None,
- metadata: str = None,
- message: str = None,
- scan_update_at: str = None,
- err: str = None,
+ id: Optional[str] = None,
+ scan_status: Optional[str] = None,
+ results_count: Optional[int] = None,
+ metadata: Optional[str] = None,
+ message: Optional[str] = None,
+ scan_update_at: Optional[str] = None,
+ err: Optional[str] = None,
):
super().__init__()
self.id = id
@@ -246,7 +253,7 @@ def __init__(self, name: str, kind: str):
self.kind = kind
def __str__(self):
- return "Name: {0}, Kind: {1}".format(self.name, self.kind)
+ return 'Name: {0}, Kind: {1}'.format(self.name, self.kind)
class AuthenticationSession(Schema):
diff --git a/cycode/cyclient/scan_client.py b/cycode/cyclient/scan_client.py
index e6a46a3b..03844da1 100644
--- a/cycode/cyclient/scan_client.py
+++ b/cycode/cyclient/scan_client.py
@@ -1,9 +1,10 @@
import json
-from typing import List
+from typing import List, Optional
from requests import Response
from cycode.cli.zip_file import InMemoryZip
+
from . import models
from .cycode_client_base import CycodeClientBase
from .scan_config.scan_config_base import ScanConfigBase
@@ -24,7 +25,7 @@ def content_scan(self, scan_type: str, file_name: str, content: str, is_git_diff
def file_scan(self, scan_type: str, path: str) -> models.ScanResult:
url_path = f'{self.scan_config.get_service_name(scan_type)}/{self.SCAN_CONTROLLER_PATH}'
- files = {'file': open(path, 'rb')}
+ files = {'file': open(path, 'rb')} # noqa: SIM115 requests lib should care about closing
response = self.scan_cycode_client.post(url_path=url_path, files=files)
return self.parse_scan_response(response)
@@ -104,8 +105,8 @@ def get_scan_detections(self, scan_id: str) -> List[dict]:
return detections
def get_scan_detections_count(self, scan_id: str) -> int:
- url_path = f'{self.scan_config.get_detections_prefix()}/{self.DETECTIONS_SERVICE_CONTROLLER_PATH}/count?scan_id={scan_id}'
- response = self.scan_cycode_client.get(url_path=url_path)
+ url_path = f'{self.scan_config.get_detections_prefix()}/{self.DETECTIONS_SERVICE_CONTROLLER_PATH}/count'
+ response = self.scan_cycode_client.get(url_path=url_path, params={'scan_id': scan_id})
return response.json().get('count', 0)
def commit_range_zipped_file_scan(
@@ -131,10 +132,12 @@ def parse_zipped_file_scan_response(response: Response) -> models.ZippedFileScan
return models.ZippedFileScanResultSchema().load(response.json())
@staticmethod
- def get_service_name(scan_type: str) -> str:
+ def get_service_name(scan_type: str) -> Optional[str]:
if scan_type == 'secret':
return 'secret'
- elif scan_type == 'iac':
+ if scan_type == 'iac':
return 'iac'
- elif scan_type == 'sca' or scan_type == 'sast':
+ if scan_type == 'sca' or scan_type == 'sast':
return 'scans'
+
+ return None
diff --git a/cycode/cyclient/scan_config/scan_config_base.py b/cycode/cyclient/scan_config/scan_config_base.py
index 81fec2a6..b4e0cb53 100644
--- a/cycode/cyclient/scan_config/scan_config_base.py
+++ b/cycode/cyclient/scan_config/scan_config_base.py
@@ -1,4 +1,5 @@
from abc import ABC, abstractmethod
+from typing import Optional
class ScanConfigBase(ABC):
@@ -19,10 +20,11 @@ class DevScanConfig(ScanConfigBase):
def get_service_name(self, scan_type):
if scan_type == 'secret':
return '5025'
- elif scan_type == 'iac':
+ if scan_type == 'iac':
return '5026'
- elif scan_type == 'sca' or scan_type == 'sast':
+ if scan_type == 'sca' or scan_type == 'sast':
return '5004'
+ return None
def get_scans_prefix(self):
return '5004'
@@ -32,14 +34,16 @@ def get_detections_prefix(self):
class DefaultScanConfig(ScanConfigBase):
- def get_service_name(self, scan_type):
+ def get_service_name(self, scan_type) -> Optional[str]:
if scan_type == 'secret':
return 'secret'
- elif scan_type == 'iac':
+ if scan_type == 'iac':
return 'iac'
- elif scan_type == 'sca' or scan_type == 'sast':
+ if scan_type == 'sca' or scan_type == 'sast':
return 'scans'
+ return None
+
def get_scans_prefix(self):
return 'scans'
diff --git a/cycode/cyclient/scan_config/scan_config_creator.py b/cycode/cyclient/scan_config/scan_config_creator.py
index adcaf1d9..c138565f 100644
--- a/cycode/cyclient/scan_config/scan_config_creator.py
+++ b/cycode/cyclient/scan_config/scan_config_creator.py
@@ -1,11 +1,11 @@
from typing import Tuple
-from ..config import dev_mode
-from ..config_dev import DEV_CYCODE_API_URL
-from ..cycode_dev_based_client import CycodeDevBasedClient
-from ..cycode_token_based_client import CycodeTokenBasedClient
-from ..scan_client import ScanClient
-from ..scan_config.scan_config_base import DefaultScanConfig, DevScanConfig
+from cycode.cyclient.config import dev_mode
+from cycode.cyclient.config_dev import DEV_CYCODE_API_URL
+from cycode.cyclient.cycode_dev_based_client import CycodeDevBasedClient
+from cycode.cyclient.cycode_token_based_client import CycodeTokenBasedClient
+from cycode.cyclient.scan_client import ScanClient
+from cycode.cyclient.scan_config.scan_config_base import DefaultScanConfig, DevScanConfig
def create_scan_client(client_id: str, client_secret: str) -> ScanClient:
diff --git a/poetry.lock b/poetry.lock
index 93240772..b5584637 100644
--- a/poetry.lock
+++ b/poetry.lock
@@ -712,6 +712,32 @@ urllib3 = ">=1.25.10"
[package.extras]
tests = ["coverage (>=6.0.0)", "flake8", "mypy", "pytest (>=7.0.0)", "pytest-asyncio", "pytest-cov", "pytest-httpserver", "tomli", "tomli-w", "types-requests"]
+[[package]]
+name = "ruff"
+version = "0.0.277"
+description = "An extremely fast Python linter, written in Rust."
+optional = false
+python-versions = ">=3.7"
+files = [
+ {file = "ruff-0.0.277-py3-none-macosx_10_7_x86_64.whl", hash = "sha256:3250b24333ef419b7a232080d9724ccc4d2da1dbbe4ce85c4caa2290d83200f8"},
+ {file = "ruff-0.0.277-py3-none-macosx_10_9_x86_64.macosx_11_0_arm64.macosx_10_9_universal2.whl", hash = "sha256:3e60605e07482183ba1c1b7237eca827bd6cbd3535fe8a4ede28cbe2a323cb97"},
+ {file = "ruff-0.0.277-py3-none-manylinux_2_17_aarch64.manylinux2014_aarch64.whl", hash = "sha256:7baa97c3d7186e5ed4d5d4f6834d759a27e56cf7d5874b98c507335f0ad5aadb"},
+ {file = "ruff-0.0.277-py3-none-manylinux_2_17_armv7l.manylinux2014_armv7l.whl", hash = "sha256:74e4b206cb24f2e98a615f87dbe0bde18105217cbcc8eb785bb05a644855ba50"},
+ {file = "ruff-0.0.277-py3-none-manylinux_2_17_i686.manylinux2014_i686.whl", hash = "sha256:479864a3ccd8a6a20a37a6e7577bdc2406868ee80b1e65605478ad3b8eb2ba0b"},
+ {file = "ruff-0.0.277-py3-none-manylinux_2_17_ppc64.manylinux2014_ppc64.whl", hash = "sha256:468bfb0a7567443cec3d03cf408d6f562b52f30c3c29df19927f1e0e13a40cd7"},
+ {file = "ruff-0.0.277-py3-none-manylinux_2_17_ppc64le.manylinux2014_ppc64le.whl", hash = "sha256:f32ec416c24542ca2f9cc8c8b65b84560530d338aaf247a4a78e74b99cd476b4"},
+ {file = "ruff-0.0.277-py3-none-manylinux_2_17_s390x.manylinux2014_s390x.whl", hash = "sha256:14a7b2f00f149c5a295f188a643ac25226ff8a4d08f7a62b1d4b0a1dc9f9b85c"},
+ {file = "ruff-0.0.277-py3-none-manylinux_2_17_x86_64.manylinux2014_x86_64.whl", hash = "sha256:a9879f59f763cc5628aa01c31ad256a0f4dc61a29355c7315b83c2a5aac932b5"},
+ {file = "ruff-0.0.277-py3-none-musllinux_1_2_aarch64.whl", hash = "sha256:f612e0a14b3d145d90eb6ead990064e22f6f27281d847237560b4e10bf2251f3"},
+ {file = "ruff-0.0.277-py3-none-musllinux_1_2_armv7l.whl", hash = "sha256:323b674c98078be9aaded5b8b51c0d9c424486566fb6ec18439b496ce79e5998"},
+ {file = "ruff-0.0.277-py3-none-musllinux_1_2_i686.whl", hash = "sha256:3a43fbe026ca1a2a8c45aa0d600a0116bec4dfa6f8bf0c3b871ecda51ef2b5dd"},
+ {file = "ruff-0.0.277-py3-none-musllinux_1_2_x86_64.whl", hash = "sha256:734165ea8feb81b0d53e3bf523adc2413fdb76f1264cde99555161dd5a725522"},
+ {file = "ruff-0.0.277-py3-none-win32.whl", hash = "sha256:88d0f2afb2e0c26ac1120e7061ddda2a566196ec4007bd66d558f13b374b9efc"},
+ {file = "ruff-0.0.277-py3-none-win_amd64.whl", hash = "sha256:6fe81732f788894a00f6ade1fe69e996cc9e485b7c35b0f53fb00284397284b2"},
+ {file = "ruff-0.0.277-py3-none-win_arm64.whl", hash = "sha256:2d4444c60f2e705c14cd802b55cd2b561d25bf4311702c463a002392d3116b22"},
+ {file = "ruff-0.0.277.tar.gz", hash = "sha256:2dab13cdedbf3af6d4427c07f47143746b6b95d9e4a254ac369a0edb9280a0d2"},
+]
+
[[package]]
name = "setuptools"
version = "67.7.2"
@@ -879,4 +905,4 @@ testing = ["big-O", "flake8 (<5)", "jaraco.functools", "jaraco.itertools", "more
[metadata]
lock-version = "2.0"
python-versions = ">=3.7,<3.12"
-content-hash = "833e8a506d7c9c0ef2585dc822d37d9b665d51cd0ef4c49b3d6c3397bdd8ecea"
+content-hash = "5cb535c853d7233ac226c8ea2e50ca05ee7243bfb81ce72f76e93be3f56d1e7f"
diff --git a/pyproject.toml b/pyproject.toml
index 69232760..fa51f398 100644
--- a/pyproject.toml
+++ b/pyproject.toml
@@ -51,6 +51,7 @@ dunamai = ">=1.16.1,<1.17.0"
[tool.poetry.group.dev.dependencies]
black = ">=23.3.0,<23.4.0"
+ruff = "0.0.277"
[tool.pytest.ini_options]
log_cli = true
@@ -84,6 +85,48 @@ exclude = '''
)
'''
+[tool.ruff]
+extend-select = [
+ "E", # pycodestyle errors
+ "W", # pycodestyle warnings
+ "F", # Pyflakes
+ "I", # isort
+ "C90", # flake8-comprehensions
+ "B", # flake8-bugbear
+ "Q", # flake8-quotes
+ "S", # flake8-bandit
+ "ASYNC", # flake8-async
+ # "ANN", # flake8-annotations. Enable later
+ "C",
+ "BLE",
+ "ERA",
+ "ICN",
+ "INP",
+ "ISC",
+ "NPY",
+ "PGH",
+ "PIE",
+ "RET",
+ "RSE",
+ "RUF",
+ "SIM",
+ "T20",
+ # "TCH", # it can't be autofixed yet
+ "TID",
+ "YTT",
+]
+line-length = 120
+target-version = "py37"
+
+[tool.ruff.flake8-quotes]
+docstring-quotes = "double"
+multiline-quotes = "double"
+inline-quotes = "single"
+
+[tool.ruff.per-file-ignores]
+"tests/*.py" = ["S101", "S105"]
+"cycode/*.py" = ["BLE001"]
+
[build-system]
requires = ["poetry-core>=1.0.0", "poetry-dynamic-versioning"]
build-backend = "poetry_dynamic_versioning.backend"
diff --git a/tests/__init__.py b/tests/__init__.py
index 421a461f..80fbb2d8 100644
--- a/tests/__init__.py
+++ b/tests/__init__.py
@@ -16,12 +16,12 @@
POD_MOCK = {
'metadata': {
- "name": "pod-template-123xyz",
- "namespace": "default",
+ 'name': 'pod-template-123xyz',
+ 'namespace': 'default',
'ownerReferences': [
{
- "kind": "Deployment",
- "name": "nginx-deployment",
+ 'kind': 'Deployment',
+ 'name': 'nginx-deployment',
}
],
}
@@ -31,4 +31,4 @@
def list_to_str(values):
- return ",".join([str(val) for val in values])
+ return ','.join([str(val) for val in values])
diff --git a/tests/cli/test_code_scanner.py b/tests/cli/test_code_scanner.py
index c4c23e2a..041dac49 100644
--- a/tests/cli/test_code_scanner.py
+++ b/tests/cli/test_code_scanner.py
@@ -6,7 +6,7 @@
from git import InvalidGitRepositoryError
from requests import Response
-from cycode.cli.code_scanner import _handle_exception, _is_file_relevant_for_sca_scan, exclude_irrelevant_files # noqa
+from cycode.cli.code_scanner import _handle_exception, _is_file_relevant_for_sca_scan
from cycode.cli.exceptions import custom_exceptions
@@ -36,21 +36,19 @@ def test_handle_exception_soft_fail(
def test_handle_exception_unhandled_error(ctx: click.Context):
- with ctx:
- with pytest.raises(ClickException):
- _handle_exception(ctx, ValueError('test'))
+ with ctx, pytest.raises(ClickException):
+ _handle_exception(ctx, ValueError('test'))
- assert ctx.obj.get('did_fail') is True
- assert ctx.obj.get('soft_fail') is None
+ assert ctx.obj.get('did_fail') is True
+ assert ctx.obj.get('soft_fail') is None
def test_handle_exception_click_error(ctx: click.Context):
- with ctx:
- with pytest.raises(ClickException):
- _handle_exception(ctx, click.ClickException('test'))
+ with ctx, pytest.raises(ClickException):
+ _handle_exception(ctx, click.ClickException('test'))
- assert ctx.obj.get('did_fail') is True
- assert ctx.obj.get('soft_fail') is None
+ assert ctx.obj.get('did_fail') is True
+ assert ctx.obj.get('soft_fail') is None
def test_handle_exception_verbose(monkeypatch):
@@ -61,9 +59,8 @@ def mock_secho(msg, *_, **__):
monkeypatch.setattr(click, 'secho', mock_secho)
- with ctx:
- with pytest.raises(ClickException):
- _handle_exception(ctx, ValueError('test'))
+ with ctx, pytest.raises(ClickException):
+ _handle_exception(ctx, ValueError('test'))
def test_is_file_relevant_for_sca_scan():
diff --git a/tests/cli/test_main.py b/tests/cli/test_main.py
index 92ec2e58..2996c0d4 100644
--- a/tests/cli/test_main.py
+++ b/tests/cli/test_main.py
@@ -1,13 +1,12 @@
import json
-
-import pytest
from typing import TYPE_CHECKING
+import pytest
import responses
from click.testing import CliRunner
from cycode.cli.main import main_cli
-from tests.conftest import TEST_FILES_PATH, CLI_ENV_VARS
+from tests.conftest import CLI_ENV_VARS, TEST_FILES_PATH
from tests.cyclient.test_scan_client import get_zipped_file_scan_response, get_zipped_file_scan_url
_PATH_TO_SCAN = TEST_FILES_PATH.joinpath('zip_content').absolute()
diff --git a/tests/cyclient/test_auth_client.py b/tests/cyclient/test_auth_client.py
index d6647b27..b3898fd3 100644
--- a/tests/cyclient/test_auth_client.py
+++ b/tests/cyclient/test_auth_client.py
@@ -3,13 +3,13 @@
import responses
from requests import Timeout
+from cycode.cli.exceptions.custom_exceptions import CycodeError
from cycode.cyclient.auth_client import AuthClient
from cycode.cyclient.models import (
- AuthenticationSession,
ApiTokenGenerationPollingResponse,
ApiTokenGenerationPollingResponseSchema,
+ AuthenticationSession,
)
-from cycode.cli.exceptions.custom_exceptions import CycodeError
@pytest.fixture(scope='module')
diff --git a/tests/cyclient/test_client_base.py b/tests/cyclient/test_client_base.py
index dff25c52..5a7810a8 100644
--- a/tests/cyclient/test_client_base.py
+++ b/tests/cyclient/test_client_base.py
@@ -9,7 +9,7 @@ def test_mandatory_headers():
client = CycodeClientBase(config.cycode_api_url)
- assert client.MANDATORY_HEADERS == expected_headers
+ assert expected_headers == client.MANDATORY_HEADERS
def test_get_request_headers():
diff --git a/tests/cyclient/test_scan_client.py b/tests/cyclient/test_scan_client.py
index 41c15a71..fecbaed2 100644
--- a/tests/cyclient/test_scan_client.py
+++ b/tests/cyclient/test_scan_client.py
@@ -1,23 +1,21 @@
import os
-from uuid import uuid4, UUID
+from typing import List, Optional
+from uuid import UUID, uuid4
import pytest
import requests
import responses
-from typing import List
-
from requests import Timeout
from requests.exceptions import ProxyError
+from cycode.cli.code_scanner import zip_documents_to_scan
from cycode.cli.config import config
-from cycode.cli.zip_file import InMemoryZip
+from cycode.cli.exceptions.custom_exceptions import CycodeError, HttpUnauthorizedError
from cycode.cli.models import Document
-from cycode.cli.code_scanner import zip_documents_to_scan
-from cycode.cli.exceptions.custom_exceptions import HttpUnauthorizedError, CycodeError
+from cycode.cli.zip_file import InMemoryZip
from cycode.cyclient.scan_client import ScanClient
from tests.conftest import TEST_FILES_PATH
-
_ZIP_CONTENT_PATH = TEST_FILES_PATH.joinpath('zip_content').absolute()
@@ -31,7 +29,8 @@ def zip_scan_resources(scan_type: str, scan_client: ScanClient):
def get_zipped_file_scan_url(scan_type: str, scan_client: ScanClient) -> str:
api_url = scan_client.scan_cycode_client.api_url
# TODO(MarshalX): create method in the scan client to build this url
- return f'{api_url}/{scan_client.scan_config.get_service_name(scan_type)}/{scan_client.SCAN_CONTROLLER_PATH}/zipped-file'
+ service_url = f'{api_url}/{scan_client.scan_config.get_service_name(scan_type)}'
+ return f'{service_url}/{scan_client.SCAN_CONTROLLER_PATH}/zipped-file'
def get_test_zip_file(scan_type: str) -> InMemoryZip:
@@ -46,7 +45,7 @@ def get_test_zip_file(scan_type: str) -> InMemoryZip:
return zip_documents_to_scan(scan_type, InMemoryZip(), test_documents)
-def get_zipped_file_scan_response(url: str, scan_id: UUID = None) -> responses.Response:
+def get_zipped_file_scan_response(url: str, scan_id: Optional[UUID] = None) -> responses.Response:
if not scan_id:
scan_id = uuid4()
diff --git a/tests/cyclient/test_token_based_client.py b/tests/cyclient/test_token_based_client.py
index b906a976..ebc672fb 100644
--- a/tests/cyclient/test_token_based_client.py
+++ b/tests/cyclient/test_token_based_client.py
@@ -2,7 +2,7 @@
import responses
from cycode.cyclient.cycode_token_based_client import CycodeTokenBasedClient
-from ..conftest import _EXPECTED_API_TOKEN
+from tests.conftest import _EXPECTED_API_TOKEN
@responses.activate
@@ -19,7 +19,7 @@ def test_api_token_expired(token_based_client: CycodeTokenBasedClient, api_token
responses.add(api_token_response)
# this property performs HTTP req to refresh the token. IDE doesn't know it
- token_based_client.api_token
+ token_based_client.api_token # noqa: B018
# mark token as expired
token_based_client._expires_in = arrow.utcnow().shift(hours=-1)
diff --git a/tests/test_files/zip_content/__init__.py b/tests/test_files/zip_content/__init__.py
new file mode 100644
index 00000000..e69de29b
diff --git a/tests/test_files/zip_content/sast.py b/tests/test_files/zip_content/sast.py
index aa6df96e..2de8a5ca 100644
--- a/tests/test_files/zip_content/sast.py
+++ b/tests/test_files/zip_content/sast.py
@@ -1,4 +1,3 @@
import requests
-
-requests.get('https://slack.com/api/conversations.list', verify=False)
+requests.get('https://slack.com/api/conversations.list', verify=False) # noqa: S113, S501
diff --git a/tests/test_files/zip_content/secrets.py b/tests/test_files/zip_content/secrets.py
index a8c7d82a..627ee470 100644
--- a/tests/test_files/zip_content/secrets.py
+++ b/tests/test_files/zip_content/secrets.py
@@ -1 +1 @@
-slack_bot_token = "xoxb-1234518014707-1234518014707-M14123412341234Fra15WS"
+slack_bot_token = 'xoxb-1234518014707-1234518014707-M14123412341234Fra15WS'
diff --git a/tests/test_models.py b/tests/test_models.py
index 270b9780..bb583b8e 100644
--- a/tests/test_models.py
+++ b/tests/test_models.py
@@ -1,14 +1,14 @@
-from cycode.cyclient.models import ResourcesCollection, InternalMetadata, K8SResource
+from cycode.cyclient.models import InternalMetadata, K8SResource, ResourcesCollection
from tests import PODS_MOCK
def test_batch_resources_to_json():
batch = ResourcesCollection('pod', 'default', PODS_MOCK, 77777)
json_dict = batch.to_json()
- assert 'resources' in json_dict.keys()
- assert 'namespace' in json_dict.keys()
- assert 'total_count' in json_dict.keys()
- assert 'type' in json_dict.keys()
+ assert 'resources' in json_dict
+ assert 'namespace' in json_dict
+ assert 'total_count' in json_dict
+ assert 'type' in json_dict
assert json_dict['total_count'] == 77777
assert json_dict['type'] == 'pod'
assert json_dict['namespace'] == 'default'
diff --git a/tests/user_settings/test_configuration_manager.py b/tests/user_settings/test_configuration_manager.py
index 8f4e01f1..1da4a346 100644
--- a/tests/user_settings/test_configuration_manager.py
+++ b/tests/user_settings/test_configuration_manager.py
@@ -1,7 +1,7 @@
from mock import Mock
-from cycode.cli.user_settings.configuration_manager import ConfigurationManager
from cycode.cli.consts import DEFAULT_CYCODE_API_URL
+from cycode.cli.user_settings.configuration_manager import ConfigurationManager
"""
we check for base url in the three places, in the following order:
diff --git a/tests/user_settings/test_user_settings_commands.py b/tests/user_settings/test_user_settings_commands.py
index cd5e5974..b63c1e5c 100644
--- a/tests/user_settings/test_user_settings_commands.py
+++ b/tests/user_settings/test_user_settings_commands.py
@@ -5,8 +5,8 @@
def test_set_credentials_no_exist_credentials_in_file(mocker):
# Arrange
- client_id_user_input = "new client id"
- client_secret_user_input = "new client secret"
+ client_id_user_input = 'new client id'
+ client_secret_user_input = 'new client secret'
mocker.patch(
'cycode.cli.user_settings.credentials_manager.CredentialsManager.get_credentials_from_file',
return_value=(None, None),
@@ -28,8 +28,8 @@ def test_set_credentials_no_exist_credentials_in_file(mocker):
def test_set_credentials_update_current_credentials_in_file(mocker):
# Arrange
- client_id_user_input = "new client id"
- client_secret_user_input = "new client secret"
+ client_id_user_input = 'new client id'
+ client_secret_user_input = 'new client secret'
mocker.patch(
'cycode.cli.user_settings.credentials_manager.CredentialsManager.get_credentials_from_file',
return_value=('client id file', 'client secret file'),
@@ -51,7 +51,7 @@ def test_set_credentials_update_current_credentials_in_file(mocker):
def test_set_credentials_update_only_client_id(mocker):
# Arrange
- client_id_user_input = "new client id"
+ client_id_user_input = 'new client id'
current_client_id = 'client secret file'
mocker.patch(
'cycode.cli.user_settings.credentials_manager.CredentialsManager.get_credentials_from_file',
@@ -74,7 +74,7 @@ def test_set_credentials_update_only_client_id(mocker):
def test_set_credentials_update_only_client_secret(mocker):
# Arrange
- client_secret_user_input = "new client secret"
+ client_secret_user_input = 'new client secret'
current_client_id = 'client secret file'
mocker.patch(
'cycode.cli.user_settings.credentials_manager.CredentialsManager.get_credentials_from_file',
@@ -97,8 +97,8 @@ def test_set_credentials_update_only_client_secret(mocker):
def test_set_credentials_should_not_update_file(mocker):
# Arrange
- client_id_user_input = ""
- client_secret_user_input = ""
+ client_id_user_input = ''
+ client_secret_user_input = ''
mocker.patch(
'cycode.cli.user_settings.credentials_manager.CredentialsManager.get_credentials_from_file',
return_value=('client id file', 'client secret file'),
diff --git a/tests/utils/test_string_utils.py b/tests/utils/test_string_utils.py
index 7b20fd4c..2a78b9f6 100644
--- a/tests/utils/test_string_utils.py
+++ b/tests/utils/test_string_utils.py
@@ -2,6 +2,6 @@
def test_shortcut_dependency_paths_list_single_dependencies():
- dependency_paths = "A, A -> B, A -> B -> C"
- expected_result = "A\n\nA -> B\n\nA -> ... -> C"
+ dependency_paths = 'A, A -> B, A -> B -> C'
+ expected_result = 'A\n\nA -> B\n\nA -> ... -> C'
assert shortcut_dependency_paths(dependency_paths) == expected_result
From 2368b5a0357eb306a00be27e264d79b9a8941a3b Mon Sep 17 00:00:00 2001
From: Ilya Siamionau
Date: Thu, 6 Jul 2023 10:21:04 +0200
Subject: [PATCH 007/257] CM-24619 - CLI pre-commit hook can't be installed
properly (#135)
---
.gitignore | 1 +
.pre-commit-hooks.yaml | 6 ++++--
cycode/__init__.py | 14 ++++++++++++++
cycode/pre-commit-hook-version | 1 +
pyproject.toml | 2 +-
5 files changed, 21 insertions(+), 3 deletions(-)
create mode 100644 cycode/pre-commit-hook-version
diff --git a/.gitignore b/.gitignore
index 1de92d03..9b17b29b 100644
--- a/.gitignore
+++ b/.gitignore
@@ -1,3 +1,4 @@
+.DS_Store
.idea
*.iml
.env
diff --git a/.pre-commit-hooks.yaml b/.pre-commit-hooks.yaml
index d3b55ce6..44b0dd1c 100644
--- a/.pre-commit-hooks.yaml
+++ b/.pre-commit-hooks.yaml
@@ -1,10 +1,12 @@
- id: cycode
name: Cycode pre commit defender
language: python
+ language_version: python3
entry: cycode
- args: [ 'scan', 'pre_commit' ]
+ args: [ '--no-progress-meter', 'scan', 'pre_commit' ]
- id: cycode-sca
name: Cycode SCA pre commit defender
language: python
+ language_version: python3
entry: cycode
- args: [ 'scan', '--scan-type', 'sca', 'pre_commit' ]
\ No newline at end of file
+ args: [ '--no-progress-meter', 'scan', '--scan-type', 'sca', 'pre_commit' ]
diff --git a/cycode/__init__.py b/cycode/__init__.py
index 4ce71ef1..2b478887 100644
--- a/cycode/__init__.py
+++ b/cycode/__init__.py
@@ -1 +1,15 @@
__version__ = '0.0.0' # DON'T TOUCH. Placeholder. Will be filled automatically on poetry build from Git Tag
+
+if __version__ == '0.0.1.dev1':
+ # If CLI was installed from shallow clone, __version__ will be 0.0.1.dev1 due to non-strict versioning.
+ # This happens when installing CLI as pre-commit hook.
+ # We are not able to provide the version based on Git Tag in this case.
+ # This fallback version is maintained manually.
+
+ # One benefit of it is that we could pass the version with a special suffix to mark pre-commit hook usage.
+
+ import os
+
+ version_filepath = os.path.join(os.path.dirname(__file__), 'pre-commit-hook-version')
+ with open(version_filepath, 'r', encoding='UTF-8') as f:
+ __version__ = f.read().strip()
diff --git a/cycode/pre-commit-hook-version b/cycode/pre-commit-hook-version
new file mode 100644
index 00000000..d1e8df28
--- /dev/null
+++ b/cycode/pre-commit-hook-version
@@ -0,0 +1 @@
+0.2.5-pre-commit
\ No newline at end of file
diff --git a/pyproject.toml b/pyproject.toml
index fa51f398..dd3c8e04 100644
--- a/pyproject.toml
+++ b/pyproject.toml
@@ -59,7 +59,7 @@ log_cli = true
[tool.poetry-dynamic-versioning]
# poetry self add "poetry-dynamic-versioning[plugin]"
enable = true
-strict = true
+strict = false
bump = true
metadata = false
vcs = "git"
From 8cb7da4138f2c7d62f0775c7e8b8cd93965a8fb1 Mon Sep 17 00:00:00 2001
From: Ilya Siamionau
Date: Thu, 6 Jul 2023 14:06:32 +0200
Subject: [PATCH 008/257] CM-25040 - Improve type annotations (#137)
---
cycode/cli/auth/auth_command.py | 18 +++--
cycode/cli/auth/auth_manager.py | 29 ++++----
cycode/cli/ci_integrations.py | 8 +--
cycode/cli/code_scanner.py | 70 +++++++++++--------
cycode/cli/exceptions/custom_exceptions.py | 20 +++---
.../maven/base_restore_maven_dependencies.py | 6 +-
.../maven/restore_gradle_dependencies.py | 2 +-
.../maven/restore_maven_dependencies.py | 10 +--
cycode/cli/helpers/sca_code_scanner.py | 16 +++--
cycode/cli/main.py | 34 ++++-----
cycode/cli/models.py | 6 +-
cycode/cli/printers/base_printer.py | 2 +-
cycode/cli/printers/base_table_printer.py | 4 +-
cycode/cli/printers/console_printer.py | 2 +-
cycode/cli/printers/sca_table_printer.py | 4 +-
cycode/cli/printers/table.py | 2 +-
cycode/cli/printers/text_printer.py | 25 +++----
cycode/cli/user_settings/base_file_manager.py | 9 +--
.../cli/user_settings/config_file_manager.py | 35 +++++-----
.../user_settings/configuration_manager.py | 12 ++--
.../cli/user_settings/credentials_manager.py | 10 +--
.../user_settings/user_settings_commands.py | 8 +--
cycode/cli/utils/enum_utils.py | 3 +-
cycode/cli/utils/path_utils.py | 6 +-
cycode/cli/utils/progress_bar.py | 9 +--
cycode/cli/utils/scan_batch.py | 3 +-
cycode/cli/utils/shell_executor.py | 2 +-
cycode/cli/utils/string_utils.py | 8 +--
cycode/cli/utils/task_timer.py | 16 ++---
cycode/cli/utils/yaml_utils.py | 8 +--
cycode/cli/zip_file.py | 9 +--
cycode/cyclient/auth_client.py | 2 +-
cycode/cyclient/config.py | 14 ++--
cycode/cyclient/cycode_client.py | 2 +-
cycode/cyclient/cycode_client_base.py | 8 +--
cycode/cyclient/cycode_dev_based_client.py | 8 +--
cycode/cyclient/cycode_token_based_client.py | 4 +-
cycode/cyclient/models.py | 56 +++++++--------
cycode/cyclient/scan_client.py | 4 +-
.../cyclient/scan_config/scan_config_base.py | 36 +++++-----
cycode/cyclient/utils.py | 10 ---
pyproject.toml | 10 ++-
tests/__init__.py | 4 --
tests/cli/test_code_scanner.py | 18 +++--
tests/cli/test_main.py | 2 +-
tests/conftest.py | 2 +-
.../scan_config/test_default_scan_config.py | 6 +-
.../scan_config/test_dev_scan_config.py | 6 +-
tests/cyclient/test_auth_client.py | 16 ++---
tests/cyclient/test_client.py | 2 +-
tests/cyclient/test_client_base.py | 8 +--
tests/cyclient/test_dev_based_client.py | 4 +-
tests/cyclient/test_scan_client.py | 24 ++++---
tests/cyclient/test_token_based_client.py | 6 +-
tests/test_code_scanner.py | 2 +-
tests/test_models.py | 4 +-
tests/test_zip_file.py | 4 +-
.../test_configuration_manager.py | 20 ++++--
.../test_user_settings_commands.py | 17 +++--
tests/utils/test_path_utils.py | 10 +--
tests/utils/test_string_utils.py | 2 +-
61 files changed, 381 insertions(+), 326 deletions(-)
delete mode 100644 cycode/cyclient/utils.py
diff --git a/cycode/cli/auth/auth_command.py b/cycode/cli/auth/auth_command.py
index 63384276..3fe037bf 100644
--- a/cycode/cli/auth/auth_command.py
+++ b/cycode/cli/auth/auth_command.py
@@ -15,7 +15,7 @@
invoke_without_command=True, short_help='Authenticates your machine to associate CLI with your cycode account'
)
@click.pass_context
-def authenticate(context: click.Context):
+def authenticate(context: click.Context) -> None:
if context.invoked_subcommand is not None:
# if it is a subcommand, do nothing
return
@@ -34,7 +34,7 @@ def authenticate(context: click.Context):
@authenticate.command(name='check')
@click.pass_context
-def authorization_check(context: click.Context):
+def authorization_check(context: click.Context) -> None:
"""Check your machine associating CLI with your cycode account"""
printer = ConsolePrinter(context)
@@ -43,19 +43,22 @@ def authorization_check(context: click.Context):
client_id, client_secret = CredentialsManager().get_credentials()
if not client_id or not client_secret:
- return printer.print_result(failed_auth_check_res)
+ printer.print_result(failed_auth_check_res)
+ return
try:
if CycodeTokenBasedClient(client_id, client_secret).api_token:
- return printer.print_result(passed_auth_check_res)
+ printer.print_result(passed_auth_check_res)
+ return
except (NetworkError, HttpUnauthorizedError):
if context.obj['verbose']:
click.secho(f'Error: {traceback.format_exc()}', fg='red')
- return printer.print_result(failed_auth_check_res)
+ printer.print_result(failed_auth_check_res)
+ return
-def _handle_exception(context: click.Context, e: Exception):
+def _handle_exception(context: click.Context, e: Exception) -> None:
if context.obj['verbose']:
click.secho(f'Error: {traceback.format_exc()}', fg='red')
@@ -70,7 +73,8 @@ def _handle_exception(context: click.Context, e: Exception):
error = errors.get(type(e))
if error:
- return ConsolePrinter(context).print_error(error)
+ ConsolePrinter(context).print_error(error)
+ return
if isinstance(e, click.ClickException):
raise e
diff --git a/cycode/cli/auth/auth_manager.py b/cycode/cli/auth/auth_manager.py
index 3a177467..11fbf751 100644
--- a/cycode/cli/auth/auth_manager.py
+++ b/cycode/cli/auth/auth_manager.py
@@ -1,6 +1,6 @@
import time
import webbrowser
-from typing import Optional
+from typing import TYPE_CHECKING, Tuple
from requests import Request
@@ -10,7 +10,10 @@
from cycode.cli.utils.string_utils import generate_random_string, hash_string_to_sha256
from cycode.cyclient import logger
from cycode.cyclient.auth_client import AuthClient
-from cycode.cyclient.models import ApiToken, ApiTokenGenerationPollingResponse
+from cycode.cyclient.models import ApiTokenGenerationPollingResponse
+
+if TYPE_CHECKING:
+ from cycode.cyclient.models import ApiToken
class AuthManager:
@@ -20,16 +23,12 @@ class AuthManager:
FAILED_POLLING_STATUS = 'Error'
COMPLETED_POLLING_STATUS = 'Completed'
- configuration_manager: ConfigurationManager
- credentials_manager: CredentialsManager
- auth_client: AuthClient
-
- def __init__(self):
+ def __init__(self) -> None:
self.configuration_manager = ConfigurationManager()
self.credentials_manager = CredentialsManager()
self.auth_client = AuthClient()
- def authenticate(self):
+ def authenticate(self) -> None:
logger.debug('generating pkce code pair')
code_challenge, code_verifier = self._generate_pkce_code_pair()
@@ -46,21 +45,21 @@ def authenticate(self):
logger.debug('saving get api token')
self.save_api_token(api_token)
- def start_session(self, code_challenge: str):
+ def start_session(self, code_challenge: str) -> str:
auth_session = self.auth_client.start_session(code_challenge)
return auth_session.session_id
- def redirect_to_login_page(self, code_challenge: str, session_id: str):
+ def redirect_to_login_page(self, code_challenge: str, session_id: str) -> None:
login_url = self._build_login_url(code_challenge, session_id)
webbrowser.open(login_url)
- def get_api_token(self, session_id: str, code_verifier: str) -> Optional[ApiToken]:
+ def get_api_token(self, session_id: str, code_verifier: str) -> 'ApiToken':
api_token = self.get_api_token_polling(session_id, code_verifier)
if api_token is None:
raise AuthProcessError('getting api token is completed, but the token is missing')
return api_token
- def get_api_token_polling(self, session_id: str, code_verifier: str) -> Optional[ApiToken]:
+ def get_api_token_polling(self, session_id: str, code_verifier: str) -> 'ApiToken':
end_polling_time = time.time() + self.POLLING_TIMEOUT_IN_SECONDS
while time.time() < end_polling_time:
logger.debug('trying to get api token...')
@@ -75,10 +74,10 @@ def get_api_token_polling(self, session_id: str, code_verifier: str) -> Optional
raise AuthProcessError('session expired')
- def save_api_token(self, api_token: ApiToken):
+ def save_api_token(self, api_token: 'ApiToken') -> None:
self.credentials_manager.update_credentials_file(api_token.client_id, api_token.secret)
- def _build_login_url(self, code_challenge: str, session_id: str):
+ def _build_login_url(self, code_challenge: str, session_id: str) -> str:
app_url = self.configuration_manager.get_cycode_app_url()
login_url = f'{app_url}/account/sign-in'
query_params = {'source': 'cycode_cli', 'code_challenge': code_challenge, 'session_id': session_id}
@@ -86,7 +85,7 @@ def _build_login_url(self, code_challenge: str, session_id: str):
request = Request(url=login_url, params=query_params)
return request.prepare().url
- def _generate_pkce_code_pair(self) -> (str, str):
+ def _generate_pkce_code_pair(self) -> Tuple[str, str]:
code_verifier = generate_random_string(self.CODE_VERIFIER_LENGTH)
code_challenge = hash_string_to_sha256(code_verifier)
return code_challenge, code_verifier
diff --git a/cycode/cli/ci_integrations.py b/cycode/cli/ci_integrations.py
index 5ea93e38..f2869b2f 100644
--- a/cycode/cli/ci_integrations.py
+++ b/cycode/cli/ci_integrations.py
@@ -3,7 +3,7 @@
import click
-def github_action_range():
+def github_action_range() -> str:
before_sha = os.getenv('BEFORE_SHA')
push_base_sha = os.getenv('BASE_SHA')
pr_base_sha = os.getenv('PR_BASE_SHA')
@@ -22,7 +22,7 @@ def github_action_range():
# if push_base_sha and push_base_sha != "null":
-def circleci_range():
+def circleci_range() -> str:
before_sha = os.getenv('BEFORE_SHA')
current_sha = os.getenv('CURRENT_SHA')
commit_range = f'{before_sha}...{current_sha}'
@@ -36,7 +36,7 @@ def circleci_range():
return f'{commit_sha}~1...'
-def gitlab_range():
+def gitlab_range() -> str:
before_sha = os.getenv('CI_COMMIT_BEFORE_SHA')
commit_sha = os.getenv('CI_COMMIT_SHA', 'HEAD')
@@ -46,7 +46,7 @@ def gitlab_range():
return f'{commit_sha}'
-def get_commit_range():
+def get_commit_range() -> str:
if os.getenv('GITHUB_ACTIONS'):
return github_action_range()
if os.getenv('CIRCLECI'):
diff --git a/cycode/cli/code_scanner.py b/cycode/cli/code_scanner.py
index bd72ebd9..65230537 100644
--- a/cycode/cli/code_scanner.py
+++ b/cycode/cli/code_scanner.py
@@ -6,7 +6,7 @@
import traceback
from platform import platform
from sys import getsizeof
-from typing import TYPE_CHECKING, Callable, Dict, List, Optional, Tuple
+from typing import TYPE_CHECKING, Callable, Dict, Iterator, List, Optional, Tuple, Union
from uuid import UUID, uuid4
import click
@@ -40,6 +40,10 @@
from cycode.cyclient.models import Detection, DetectionSchema, DetectionsPerFile, ZippedFileScanResult
if TYPE_CHECKING:
+ from git import Blob, Diff
+ from git.objects.base import IndexObjUnion
+ from git.objects.tree import TraversedTreeTup
+
from cycode.cli.utils.progress_bar import BaseProgressBar
from cycode.cyclient.models import ScanDetailsResponse
from cycode.cyclient.scan_client import ScanClient
@@ -58,7 +62,7 @@
required=False,
)
@click.pass_context
-def scan_repository(context: click.Context, path: str, branch: str):
+def scan_repository(context: click.Context, path: str, branch: str) -> None:
try:
logger.debug('Starting repository scan process, %s', {'path': path, 'branch': branch})
@@ -74,11 +78,11 @@ def scan_repository(context: click.Context, path: str, branch: str):
documents_to_scan = []
for file in file_entries:
+ # FIXME(MarshalX): probably file could be tree or submodule too. we expect blob only
progress_bar.update(ProgressBarSection.PREPARE_LOCAL_FILES)
- path = file.path if monitor else get_path_by_os(os.path.join(path, file.path))
-
- documents_to_scan.append(Document(path, file.data_stream.read().decode('UTF-8', errors='replace')))
+ file_path = file.path if monitor else get_path_by_os(os.path.join(path, file.path))
+ documents_to_scan.append(Document(file_path, file.data_stream.read().decode('UTF-8', errors='replace')))
documents_to_scan = exclude_irrelevant_documents_to_scan(context, documents_to_scan)
@@ -103,15 +107,17 @@ def scan_repository(context: click.Context, path: str, branch: str):
required=False,
)
@click.pass_context
-def scan_repository_commit_history(context: click.Context, path: str, commit_range: str):
+def scan_repository_commit_history(context: click.Context, path: str, commit_range: str) -> None:
try:
logger.debug('Starting commit history scan process, %s', {'path': path, 'commit_range': commit_range})
- return scan_commit_range(context, path=path, commit_range=commit_range)
+ scan_commit_range(context, path=path, commit_range=commit_range)
except Exception as e:
_handle_exception(context, e)
-def scan_commit_range(context: click.Context, path: str, commit_range: str, max_commits_count: Optional[int] = None):
+def scan_commit_range(
+ context: click.Context, path: str, commit_range: str, max_commits_count: Optional[int] = None
+) -> None:
scan_type = context.obj['scan_type']
progress_bar = context.obj['progress_bar']
@@ -166,7 +172,8 @@ def scan_commit_range(context: click.Context, path: str, commit_range: str, max_
logger.debug('List of commit ids to scan, %s', {'commit_ids': commit_ids_to_scan})
logger.debug('Starting to scan commit range (It may take a few minutes)')
- return scan_documents(context, documents_to_scan, is_git_diff=True, is_commit_range=True)
+ scan_documents(context, documents_to_scan, is_git_diff=True, is_commit_range=True)
+ return None
@click.command(
@@ -174,30 +181,31 @@ def scan_commit_range(context: click.Context, path: str, commit_range: str, max_
'CYCODE_TOKEN and CYCODE_REPO_LOCATION environment variables'
)
@click.pass_context
-def scan_ci(context: click.Context):
- return scan_commit_range(context, path=os.getcwd(), commit_range=get_commit_range())
+def scan_ci(context: click.Context) -> None:
+ scan_commit_range(context, path=os.getcwd(), commit_range=get_commit_range())
@click.command(short_help='Scan the files in the path supplied in the command')
@click.argument('path', nargs=1, type=click.STRING, required=True)
@click.pass_context
-def scan_path(context: click.Context, path):
+def scan_path(context: click.Context, path: str) -> None:
logger.debug('Starting path scan process, %s', {'path': path})
files_to_scan = get_relevant_files_in_path(path=path, exclude_patterns=['**/.git/**', '**/.cycode/**'])
files_to_scan = exclude_irrelevant_files(context, files_to_scan)
logger.debug('Found all relevant files for scanning %s', {'path': path, 'file_to_scan_count': len(files_to_scan)})
- return scan_disk_files(context, path, files_to_scan)
+ scan_disk_files(context, path, files_to_scan)
@click.command(short_help='Use this command to scan the content that was not committed yet')
@click.argument('ignored_args', nargs=-1, type=click.UNPROCESSED)
@click.pass_context
-def pre_commit_scan(context: click.Context, ignored_args: List[str]):
+def pre_commit_scan(context: click.Context, ignored_args: List[str]) -> None:
scan_type = context.obj['scan_type']
progress_bar = context.obj['progress_bar']
if scan_type == consts.SCA_SCAN_TYPE:
- return scan_sca_pre_commit(context)
+ scan_sca_pre_commit(context)
+ return
diff_files = Repo(os.getcwd()).index.diff('HEAD', create_patch=True, R=True)
@@ -209,13 +217,13 @@ def pre_commit_scan(context: click.Context, ignored_args: List[str]):
documents_to_scan.append(Document(get_path_by_os(get_diff_file_path(file)), get_diff_file_content(file)))
documents_to_scan = exclude_irrelevant_documents_to_scan(context, documents_to_scan)
- return scan_documents(context, documents_to_scan, is_git_diff=True)
+ scan_documents(context, documents_to_scan, is_git_diff=True)
@click.command(short_help='Use this command to scan commits on the server side before pushing them to the repository')
@click.argument('ignored_args', nargs=-1, type=click.UNPROCESSED)
@click.pass_context
-def pre_receive_scan(context: click.Context, ignored_args: List[str]):
+def pre_receive_scan(context: click.Context, ignored_args: List[str]) -> None:
try:
scan_type = context.obj['scan_type']
if scan_type != consts.SECRET_SCAN_TYPE:
@@ -253,13 +261,13 @@ def pre_receive_scan(context: click.Context, ignored_args: List[str]):
_handle_exception(context, e)
-def scan_sca_pre_commit(context: click.Context):
+def scan_sca_pre_commit(context: click.Context) -> None:
scan_parameters = get_default_scan_parameters(context)
git_head_documents, pre_committed_documents = get_pre_commit_modified_documents(context.obj['progress_bar'])
git_head_documents = exclude_irrelevant_documents_to_scan(context, git_head_documents)
pre_committed_documents = exclude_irrelevant_documents_to_scan(context, pre_committed_documents)
sca_code_scanner.perform_pre_hook_range_scan_actions(git_head_documents, pre_committed_documents)
- return scan_commit_range_documents(
+ scan_commit_range_documents(
context,
git_head_documents,
pre_committed_documents,
@@ -268,7 +276,7 @@ def scan_sca_pre_commit(context: click.Context):
)
-def scan_sca_commit_range(context: click.Context, path: str, commit_range: str):
+def scan_sca_commit_range(context: click.Context, path: str, commit_range: str) -> None:
progress_bar = context.obj['progress_bar']
scan_parameters = get_scan_parameters(context, path)
@@ -282,12 +290,10 @@ def scan_sca_commit_range(context: click.Context, path: str, commit_range: str):
path, from_commit_documents, from_commit_rev, to_commit_documents, to_commit_rev
)
- return scan_commit_range_documents(
- context, from_commit_documents, to_commit_documents, scan_parameters=scan_parameters
- )
+ scan_commit_range_documents(context, from_commit_documents, to_commit_documents, scan_parameters=scan_parameters)
-def scan_disk_files(context: click.Context, path: str, files_to_scan: List[str]):
+def scan_disk_files(context: click.Context, path: str, files_to_scan: List[str]) -> None:
scan_parameters = get_scan_parameters(context, path)
scan_type = context.obj['scan_type']
progress_bar = context.obj['progress_bar']
@@ -307,7 +313,7 @@ def scan_disk_files(context: click.Context, path: str, files_to_scan: List[str])
continue
perform_pre_scan_documents_actions(context, scan_type, documents, is_git_diff)
- return scan_documents(context, documents, is_git_diff=is_git_diff, scan_parameters=scan_parameters)
+ scan_documents(context, documents, is_git_diff=is_git_diff, scan_parameters=scan_parameters)
def set_issue_detected_by_scan_results(context: click.Context, scan_results: List[LocalScanResult]) -> None:
@@ -757,19 +763,21 @@ def get_oldest_unupdated_commit_for_branch(commit: str) -> Optional[str]:
return commits[0]
-def get_diff_file_path(file):
+def get_diff_file_path(file: 'Diff') -> Optional[str]:
return file.b_path if file.b_path else file.a_path
-def get_diff_file_content(file):
+def get_diff_file_content(file: 'Diff') -> str:
return file.diff.decode('UTF-8', errors='replace')
-def should_process_git_object(obj, _: int) -> bool:
+def should_process_git_object(obj: 'Blob', _: int) -> bool:
return obj.type == 'blob' and obj.size > 0
-def get_git_repository_tree_file_entries(path: str, branch: str):
+def get_git_repository_tree_file_entries(
+ path: str, branch: str
+) -> Union[Iterator['IndexObjUnion'], Iterator['TraversedTreeTup']]:
return Repo(path).tree(branch).traverse(predicate=should_process_git_object)
@@ -867,7 +875,7 @@ def _exclude_detections_by_scan_type(
return detections
-def exclude_detections_in_deleted_lines(detections) -> List:
+def exclude_detections_in_deleted_lines(detections: List[Detection]) -> List[Detection]:
return [detection for detection in detections if detection.detection_details.get('line_type') != 'Removed']
@@ -969,7 +977,7 @@ def _should_exclude_detection(detection: Detection, exclusions: Dict) -> bool:
return False
-def _is_detection_sha_configured_in_exclusions(detection, exclusions: List[str]) -> bool:
+def _is_detection_sha_configured_in_exclusions(detection: Detection, exclusions: List[str]) -> bool:
detection_sha = detection.detection_details.get('sha512', '')
return detection_sha in exclusions
diff --git a/cycode/cli/exceptions/custom_exceptions.py b/cycode/cli/exceptions/custom_exceptions.py
index 8ae2236f..4806e17c 100644
--- a/cycode/cli/exceptions/custom_exceptions.py
+++ b/cycode/cli/exceptions/custom_exceptions.py
@@ -6,13 +6,13 @@ class CycodeError(Exception):
class NetworkError(CycodeError):
- def __init__(self, status_code: int, error_message: str, response: Response):
+ def __init__(self, status_code: int, error_message: str, response: Response) -> None:
self.status_code = status_code
self.error_message = error_message
self.response = response
super().__init__(self.error_message)
- def __str__(self):
+ def __str__(self) -> str:
return (
f'error occurred during the request. status code: {self.status_code}, error message: '
f'{self.error_message}'
@@ -20,38 +20,38 @@ def __str__(self):
class ScanAsyncError(CycodeError):
- def __init__(self, error_message: str):
+ def __init__(self, error_message: str) -> None:
self.error_message = error_message
super().__init__(self.error_message)
- def __str__(self):
+ def __str__(self) -> str:
return f'error occurred during the scan. error message: {self.error_message}'
class HttpUnauthorizedError(CycodeError):
- def __init__(self, error_message: str, response: Response):
+ def __init__(self, error_message: str, response: Response) -> None:
self.status_code = 401
self.error_message = error_message
self.response = response
super().__init__(self.error_message)
- def __str__(self):
+ def __str__(self) -> str:
return 'Http Unauthorized Error'
class ZipTooLargeError(CycodeError):
- def __init__(self, size_limit: int):
+ def __init__(self, size_limit: int) -> None:
self.size_limit = size_limit
super().__init__()
- def __str__(self):
+ def __str__(self) -> str:
return f'The size of zip to scan is too large, size limit: {self.size_limit}'
class AuthProcessError(CycodeError):
- def __init__(self, error_message: str):
+ def __init__(self, error_message: str) -> None:
self.error_message = error_message
super().__init__()
- def __str__(self):
+ def __str__(self) -> str:
return f'Something went wrong during the authentication process, error message: {self.error_message}'
diff --git a/cycode/cli/helpers/maven/base_restore_maven_dependencies.py b/cycode/cli/helpers/maven/base_restore_maven_dependencies.py
index b3c55008..064b9eeb 100644
--- a/cycode/cli/helpers/maven/base_restore_maven_dependencies.py
+++ b/cycode/cli/helpers/maven/base_restore_maven_dependencies.py
@@ -1,5 +1,5 @@
from abc import ABC, abstractmethod
-from typing import Dict, List, Optional
+from typing import List, Optional
import click
@@ -13,7 +13,7 @@ def build_dep_tree_path(path: str, generated_file_name: str) -> str:
return join_paths(get_file_dir(path), generated_file_name)
-def execute_command(command: List[str], file_name: str, command_timeout: int) -> Optional[Dict]:
+def execute_command(command: List[str], file_name: str, command_timeout: int) -> Optional[str]:
try:
dependencies = shell(command, command_timeout)
except Exception as e:
@@ -24,7 +24,7 @@ def execute_command(command: List[str], file_name: str, command_timeout: int) ->
class BaseRestoreMavenDependencies(ABC):
- def __init__(self, context: click.Context, is_git_diff: bool, command_timeout: int):
+ def __init__(self, context: click.Context, is_git_diff: bool, command_timeout: int) -> None:
self.context = context
self.is_git_diff = is_git_diff
self.command_timeout = command_timeout
diff --git a/cycode/cli/helpers/maven/restore_gradle_dependencies.py b/cycode/cli/helpers/maven/restore_gradle_dependencies.py
index 6a60faad..f8cd2fec 100644
--- a/cycode/cli/helpers/maven/restore_gradle_dependencies.py
+++ b/cycode/cli/helpers/maven/restore_gradle_dependencies.py
@@ -11,7 +11,7 @@
class RestoreGradleDependencies(BaseRestoreMavenDependencies):
- def __init__(self, context: click.Context, is_git_diff: bool, command_timeout: int):
+ def __init__(self, context: click.Context, is_git_diff: bool, command_timeout: int) -> None:
super().__init__(context, is_git_diff, command_timeout)
def is_project(self, document: Document) -> bool:
diff --git a/cycode/cli/helpers/maven/restore_maven_dependencies.py b/cycode/cli/helpers/maven/restore_maven_dependencies.py
index bef8a1b1..d8e6675f 100644
--- a/cycode/cli/helpers/maven/restore_maven_dependencies.py
+++ b/cycode/cli/helpers/maven/restore_maven_dependencies.py
@@ -17,7 +17,7 @@
class RestoreMavenDependencies(BaseRestoreMavenDependencies):
- def __init__(self, context: click.Context, is_git_diff: bool, command_timeout: int):
+ def __init__(self, context: click.Context, is_git_diff: bool, command_timeout: int) -> None:
super().__init__(context, is_git_diff, command_timeout)
def is_project(self, document: Document) -> bool:
@@ -43,8 +43,10 @@ def try_restore_dependencies(self, document: Document) -> Optional[Document]:
return restore_dependencies_document
- def restore_from_secondary_command(self, document, manifest_file_path, restore_dependencies_document):
- # TODO(MarshalX): does it even work? Missing argument
+ def restore_from_secondary_command(
+ self, document: Document, manifest_file_path: str, restore_dependencies_document: Optional[Document]
+ ) -> Optional[Document]:
+ # TODO(MarshalX): does it even work? Ignored restore_dependencies_document arg
secondary_restore_command = create_secondary_restore_command(manifest_file_path)
backup_restore_content = execute_command(secondary_restore_command, manifest_file_path, self.command_timeout)
restore_dependencies_document = Document(
@@ -58,7 +60,7 @@ def restore_from_secondary_command(self, document, manifest_file_path, restore_d
return restore_dependencies
-def create_secondary_restore_command(self, manifest_file_path):
+def create_secondary_restore_command(manifest_file_path: str) -> List[str]:
return [
'mvn',
'dependency:tree',
diff --git a/cycode/cli/helpers/sca_code_scanner.py b/cycode/cli/helpers/sca_code_scanner.py
index 87e301e3..ccff11b0 100644
--- a/cycode/cli/helpers/sca_code_scanner.py
+++ b/cycode/cli/helpers/sca_code_scanner.py
@@ -1,5 +1,5 @@
import os
-from typing import Dict, List, Optional
+from typing import TYPE_CHECKING, Dict, List, Optional
import click
from git import GitCommandError, Repo
@@ -11,6 +11,9 @@
from cycode.cli.utils.path_utils import get_file_content, get_file_dir, join_paths
from cycode.cyclient import logger
+if TYPE_CHECKING:
+ from cycode.cli.helpers.maven.base_restore_maven_dependencies import BaseRestoreMavenDependencies
+
BUILD_GRADLE_FILE_NAME = 'build.gradle'
BUILD_GRADLE_KTS_FILE_NAME = 'build.gradle.kts'
BUILD_GRADLE_DEP_TREE_FILE_NAME = 'gradle-dependencies-generated.txt'
@@ -39,7 +42,7 @@ def perform_pre_hook_range_scan_actions(
def add_ecosystem_related_files_if_exists(
documents: List[Document], repo: Optional[Repo] = None, commit_rev: Optional[str] = None
-):
+) -> None:
for doc in documents:
ecosystem = get_project_file_ecosystem(doc)
if ecosystem is None:
@@ -81,8 +84,11 @@ def get_project_file_ecosystem(document: Document) -> Optional[str]:
def try_restore_dependencies(
- context: click.Context, documents_to_add: List[Document], restore_dependencies, document: Document
-):
+ context: click.Context,
+ documents_to_add: Dict[str, Document],
+ restore_dependencies: 'BaseRestoreMavenDependencies',
+ document: Document,
+) -> None:
if restore_dependencies.is_project(document):
restore_dependencies_document = restore_dependencies.restore(document)
if restore_dependencies_document is None:
@@ -117,7 +123,7 @@ def add_dependencies_tree_document(
documents_to_scan.extend(list(documents_to_add.values()))
-def restore_handlers(context, is_git_diff):
+def restore_handlers(context: click.Context, is_git_diff: bool) -> List[RestoreGradleDependencies]:
return [
RestoreGradleDependencies(context, is_git_diff, BUILD_GRADLE_DEP_TREE_TIMEOUT),
RestoreMavenDependencies(context, is_git_diff, BUILD_GRADLE_DEP_TREE_TIMEOUT),
diff --git a/cycode/cli/main.py b/cycode/cli/main.py
index cb741ad7..0086534e 100644
--- a/cycode/cli/main.py
+++ b/cycode/cli/main.py
@@ -1,6 +1,6 @@
import logging
import sys
-from typing import TYPE_CHECKING, List, Optional
+from typing import TYPE_CHECKING, List, Optional, Tuple
import click
@@ -120,17 +120,17 @@
@click.pass_context
def code_scan(
context: click.Context,
- scan_type,
- client_id,
- secret,
- show_secret,
- soft_fail,
- output,
- severity_threshold,
+ scan_type: str,
+ secret: str,
+ client_id: str,
+ show_secret: bool,
+ soft_fail: bool,
+ output: str,
+ severity_threshold: str,
sca_scan: List[str],
- monitor,
- report,
-):
+ monitor: bool,
+ report: bool,
+) -> int:
if show_secret:
context.obj['show_secret'] = show_secret
else:
@@ -164,7 +164,7 @@ def code_scan(
@code_scan.result_callback()
@click.pass_context
-def finalize(context: click.Context, *_, **__):
+def finalize(context: click.Context, *_, **__) -> None:
progress_bar = context.obj.get('progress_bar')
if progress_bar:
progress_bar.stop()
@@ -210,7 +210,9 @@ def finalize(context: click.Context, *_, **__):
)
@click.version_option(__version__, prog_name='cycode')
@click.pass_context
-def main_cli(context: click.Context, verbose: bool, no_progress_meter: bool, output: str, user_agent: Optional[str]):
+def main_cli(
+ context: click.Context, verbose: bool, no_progress_meter: bool, output: str, user_agent: Optional[str]
+) -> None:
context.ensure_object(dict)
configuration_manager = ConfigurationManager()
@@ -243,16 +245,16 @@ def get_cycode_client(client_id: str, client_secret: str) -> 'ScanClient':
return create_scan_client(client_id, client_secret)
-def _get_configured_credentials():
+def _get_configured_credentials() -> Tuple[str, str]:
credentials_manager = CredentialsManager()
return credentials_manager.get_credentials()
-def _should_fail_scan(context: click.Context):
+def _should_fail_scan(context: click.Context) -> bool:
return scan_utils.is_scan_failed(context)
-def _sca_scan_to_context(context: click.Context, sca_scan_user_selected: List[str]):
+def _sca_scan_to_context(context: click.Context, sca_scan_user_selected: List[str]) -> None:
for sca_scan_option_selected in sca_scan_user_selected:
context.obj[sca_scan_option_selected] = True
diff --git a/cycode/cli/models.py b/cycode/cli/models.py
index 67453b8c..05713934 100644
--- a/cycode/cli/models.py
+++ b/cycode/cli/models.py
@@ -5,7 +5,9 @@
class Document:
- def __init__(self, path: str, content: str, is_git_diff_format: bool = False, unique_id: Optional[str] = None):
+ def __init__(
+ self, path: str, content: str, is_git_diff_format: bool = False, unique_id: Optional[str] = None
+ ) -> None:
self.path = path
self.content = content
self.is_git_diff_format = is_git_diff_format
@@ -16,7 +18,7 @@ def __repr__(self) -> str:
class DocumentDetections:
- def __init__(self, document: Document, detections: List[Detection]):
+ def __init__(self, document: Document, detections: List[Detection]) -> None:
self.document = document
self.detections = detections
diff --git a/cycode/cli/printers/base_printer.py b/cycode/cli/printers/base_printer.py
index 7b094c65..ceb430ab 100644
--- a/cycode/cli/printers/base_printer.py
+++ b/cycode/cli/printers/base_printer.py
@@ -14,7 +14,7 @@ class BasePrinter(ABC):
WHITE_COLOR_NAME = 'white'
GREEN_COLOR_NAME = 'green'
- def __init__(self, context: click.Context):
+ def __init__(self, context: click.Context) -> None:
self.context = context
@abstractmethod
diff --git a/cycode/cli/printers/base_table_printer.py b/cycode/cli/printers/base_table_printer.py
index 56a1a552..f304f967 100644
--- a/cycode/cli/printers/base_table_printer.py
+++ b/cycode/cli/printers/base_table_printer.py
@@ -12,7 +12,7 @@
class BaseTablePrinter(BasePrinter, abc.ABC):
- def __init__(self, context: click.Context):
+ def __init__(self, context: click.Context) -> None:
super().__init__(context)
self.context = context
self.scan_type: str = context.obj.get('scan_type')
@@ -24,7 +24,7 @@ def print_result(self, result: CliResult) -> None:
def print_error(self, error: CliError) -> None:
TextPrinter(self.context).print_error(error)
- def print_scan_results(self, local_scan_results: List['LocalScanResult']):
+ def print_scan_results(self, local_scan_results: List['LocalScanResult']) -> None:
if all(result.issue_detected == 0 for result in local_scan_results):
click.secho('Good job! No issues were found!!! 👏👏👏', fg=self.GREEN_COLOR_NAME)
return
diff --git a/cycode/cli/printers/console_printer.py b/cycode/cli/printers/console_printer.py
index 2321f089..533ed321 100644
--- a/cycode/cli/printers/console_printer.py
+++ b/cycode/cli/printers/console_printer.py
@@ -24,7 +24,7 @@ class ConsolePrinter:
'text_sca': SCATablePrinter,
}
- def __init__(self, context: click.Context):
+ def __init__(self, context: click.Context) -> None:
self.context = context
self.scan_type = self.context.obj.get('scan_type')
self.output_type = self.context.obj.get('output')
diff --git a/cycode/cli/printers/sca_table_printer.py b/cycode/cli/printers/sca_table_printer.py
index b3b03567..80d2da4f 100644
--- a/cycode/cli/printers/sca_table_printer.py
+++ b/cycode/cli/printers/sca_table_printer.py
@@ -84,7 +84,9 @@ def _get_table_headers(self) -> list:
return []
- def _print_table_detections(self, detections: List[Detection], headers: List[str], rows, title: str) -> None:
+ def _print_table_detections(
+ self, detections: List[Detection], headers: List[str], rows: List[List[str]], title: str
+ ) -> None:
self._print_summary_issues(detections, title)
text_table = Texttable()
text_table.header(headers)
diff --git a/cycode/cli/printers/table.py b/cycode/cli/printers/table.py
index d2847399..9c90c940 100644
--- a/cycode/cli/printers/table.py
+++ b/cycode/cli/printers/table.py
@@ -9,7 +9,7 @@
class Table:
"""Helper class to manage columns and their values in the right order and only if the column should be presented."""
- def __init__(self, column_infos: Optional[List['ColumnInfo']] = None):
+ def __init__(self, column_infos: Optional[List['ColumnInfo']] = None) -> None:
self._column_widths = None
self._columns: Dict['ColumnInfo', List[str]] = {}
diff --git a/cycode/cli/printers/text_printer.py b/cycode/cli/printers/text_printer.py
index 4555225d..d06021a3 100644
--- a/cycode/cli/printers/text_printer.py
+++ b/cycode/cli/printers/text_printer.py
@@ -14,7 +14,7 @@
class TextPrinter(BasePrinter):
- def __init__(self, context: click.Context):
+ def __init__(self, context: click.Context) -> None:
super().__init__(context)
self.scan_type: str = context.obj.get('scan_type')
self.command_scan_type: str = context.info_name
@@ -30,7 +30,7 @@ def print_result(self, result: CliResult) -> None:
def print_error(self, error: CliError) -> None:
click.secho(error.message, fg=self.RED_COLOR_NAME)
- def print_scan_results(self, local_scan_results: List['LocalScanResult']):
+ def print_scan_results(self, local_scan_results: List['LocalScanResult']) -> None:
if all(result.issue_detected == 0 for result in local_scan_results):
click.secho('Good job! No issues were found!!! 👏👏👏', fg=self.GREEN_COLOR_NAME)
return
@@ -43,7 +43,7 @@ def print_scan_results(self, local_scan_results: List['LocalScanResult']):
def _print_document_detections(
self, document_detections: DocumentDetections, scan_id: str, report_url: Optional[str]
- ):
+ ) -> None:
document = document_detections.document
lines_to_display = self._get_lines_to_display_count()
for detection in document_detections.detections:
@@ -52,7 +52,7 @@ def _print_document_detections(
def _print_detection_summary(
self, detection: Detection, document_path: str, scan_id: str, report_url: Optional[str]
- ):
+ ) -> None:
detection_name = detection.type if self.scan_type == SECRET_SCAN_TYPE else detection.message
detection_sha = detection.detection_details.get('sha512')
@@ -70,14 +70,15 @@ def _print_detection_summary(
f'{detection_sha_message}{scan_id_message}{report_url_message}{detection_commit_id_message} ⛔'
)
- def _print_detection_code_segment(self, detection: Detection, document: Document, code_segment_size: int):
+ def _print_detection_code_segment(self, detection: Detection, document: Document, code_segment_size: int) -> None:
if self._is_git_diff_based_scan():
self._print_detection_from_git_diff(detection, document)
return
self._print_detection_from_file(detection, document, code_segment_size)
- def _get_code_segment_start_line(self, detection_line: int, code_segment_size: int):
+ @staticmethod
+ def _get_code_segment_start_line(detection_line: int, code_segment_size: int) -> int:
start_line = detection_line - math.ceil(code_segment_size / 2)
return 0 if start_line < 0 else start_line
@@ -89,7 +90,7 @@ def _print_line_of_code_segment(
detection_position_in_line: int,
violation_length: int,
is_detection_line: bool,
- ):
+ ) -> None:
if is_detection_line:
self._print_detection_line(document, line, line_number, detection_position_in_line, violation_length)
else:
@@ -104,7 +105,7 @@ def _print_detection_line(
click.echo(f'{self._get_line_number_style(line_number)} {detection_line}')
- def _print_line(self, document: Document, line: str, line_number: int):
+ def _print_line(self, document: Document, line: str, line_number: int) -> None:
line_no = self._get_line_number_style(line_number)
line = self._get_line_style(line, document.is_git_diff_format)
@@ -148,7 +149,7 @@ def _get_line_color(self, line: str, is_git_diff: bool) -> str:
return self.WHITE_COLOR_NAME
- def _get_line_number_style(self, line_number: int):
+ def _get_line_number_style(self, line_number: int) -> str:
return (
f'{click.style(str(line_number), fg=self.WHITE_COLOR_NAME, bold=False)} '
f'{click.style("|", fg=self.RED_COLOR_NAME, bold=False)}'
@@ -164,7 +165,7 @@ def _get_lines_to_display_count(self) -> int:
return result_printer_configuration.get('default').get('lines_to_display')
- def _print_detection_from_file(self, detection: Detection, document: Document, code_segment_size: int):
+ def _print_detection_from_file(self, detection: Detection, document: Document, code_segment_size: int) -> None:
detection_details = detection.detection_details
detection_line = (
detection_details.get('line', -1)
@@ -197,7 +198,7 @@ def _print_detection_from_file(self, detection: Detection, document: Document, c
)
click.echo()
- def _print_detection_from_git_diff(self, detection: Detection, document: Document):
+ def _print_detection_from_git_diff(self, detection: Detection, document: Document) -> None:
detection_details = detection.detection_details
detection_line_number = detection_details.get('line', -1)
detection_line_number_in_original_file = detection_details.get('line_in_file', -1)
@@ -219,5 +220,5 @@ def _print_detection_from_git_diff(self, detection: Detection, document: Documen
)
click.echo()
- def _is_git_diff_based_scan(self):
+ def _is_git_diff_based_scan(self) -> bool:
return self.command_scan_type in COMMIT_RANGE_BASED_COMMAND_SCAN_TYPES and self.scan_type == SECRET_SCAN_TYPE
diff --git a/cycode/cli/user_settings/base_file_manager.py b/cycode/cli/user_settings/base_file_manager.py
index a640d8fa..37c9b0de 100644
--- a/cycode/cli/user_settings/base_file_manager.py
+++ b/cycode/cli/user_settings/base_file_manager.py
@@ -1,21 +1,22 @@
import os
from abc import ABC, abstractmethod
+from typing import Any, Dict, Hashable
from cycode.cli.utils.yaml_utils import read_file, update_file
class BaseFileManager(ABC):
@abstractmethod
- def get_filename(self):
- pass
+ def get_filename(self) -> str:
+ ...
- def read_file(self):
+ def read_file(self) -> Dict[Hashable, Any]:
try:
return read_file(self.get_filename())
except FileNotFoundError:
return {}
- def write_content_to_file(self, content):
+ def write_content_to_file(self, content: Dict[Hashable, Any]) -> None:
filename = self.get_filename()
os.makedirs(os.path.dirname(filename), exist_ok=True)
update_file(filename, content)
diff --git a/cycode/cli/user_settings/config_file_manager.py b/cycode/cli/user_settings/config_file_manager.py
index 5d2e3016..acec4d17 100644
--- a/cycode/cli/user_settings/config_file_manager.py
+++ b/cycode/cli/user_settings/config_file_manager.py
@@ -1,9 +1,12 @@
import os
-from typing import Dict, List, Optional
+from typing import TYPE_CHECKING, Any, Dict, Hashable, List, Optional, Union
from cycode.cli.consts import CYCODE_CONFIGURATION_DIRECTORY
from cycode.cli.user_settings.base_file_manager import BaseFileManager
+if TYPE_CHECKING:
+ from pathlib import Path
+
class ConfigFileManager(BaseFileManager):
CYCODE_HIDDEN_DIRECTORY: str = CYCODE_CONFIGURATION_DIRECTORY
@@ -22,34 +25,34 @@ class ConfigFileManager(BaseFileManager):
COMMAND_TIMEOUT_FIELD_NAME: str = 'command_timeout'
EXCLUDE_DETECTIONS_IN_DELETED_LINES: str = 'exclude_detections_in_deleted_lines'
- def __init__(self, path):
+ def __init__(self, path: Union['Path', str]) -> None:
self.path = path
- def get_api_url(self) -> Optional[str]:
+ def get_api_url(self) -> Optional[Any]:
return self._get_value_from_environment_section(self.API_URL_FIELD_NAME)
- def get_app_url(self) -> Optional[str]:
+ def get_app_url(self) -> Optional[Any]:
return self._get_value_from_environment_section(self.APP_URL_FIELD_NAME)
- def get_verbose_flag(self) -> Optional[bool]:
+ def get_verbose_flag(self) -> Optional[Any]:
return self._get_value_from_environment_section(self.VERBOSE_FIELD_NAME)
- def get_exclusions_by_scan_type(self, scan_type) -> Dict:
+ def get_exclusions_by_scan_type(self, scan_type: str) -> Dict[Hashable, Any]:
exclusions_section = self._get_section(self.EXCLUSIONS_SECTION_NAME)
return exclusions_section.get(scan_type, {})
- def get_max_commits(self, command_scan_type) -> Optional[int]:
+ def get_max_commits(self, command_scan_type: str) -> Optional[Any]:
return self._get_value_from_command_scan_type_configuration(command_scan_type, self.MAX_COMMITS_FIELD_NAME)
- def get_command_timeout(self, command_scan_type) -> Optional[int]:
+ def get_command_timeout(self, command_scan_type: str) -> Optional[Any]:
return self._get_value_from_command_scan_type_configuration(command_scan_type, self.COMMAND_TIMEOUT_FIELD_NAME)
- def get_exclude_detections_in_deleted_lines(self, command_scan_type) -> Optional[bool]:
+ def get_exclude_detections_in_deleted_lines(self, command_scan_type: str) -> Optional[Any]:
return self._get_value_from_command_scan_type_configuration(
command_scan_type, self.EXCLUDE_DETECTIONS_IN_DELETED_LINES
)
- def update_base_url(self, base_url: str):
+ def update_base_url(self, base_url: str) -> None:
update_data = {self.ENVIRONMENT_SECTION_NAME: {self.API_URL_FIELD_NAME: base_url}}
self.write_content_to_file(update_data)
@@ -60,7 +63,7 @@ def update_installation_id(self, installation_id: str) -> None:
update_data = {self.ENVIRONMENT_SECTION_NAME: {self.INSTALLATION_ID_FIELD_NAME: installation_id}}
self.write_content_to_file(update_data)
- def add_exclusion(self, scan_type, exclusion_type, new_exclusion):
+ def add_exclusion(self, scan_type: str, exclusion_type: str, new_exclusion: str) -> None:
exclusions = self._get_exclusions_by_exclusion_type(scan_type, exclusion_type)
if new_exclusion in exclusions:
return
@@ -80,22 +83,22 @@ def get_filename(self) -> str:
def get_config_file_route() -> str:
return os.path.join(ConfigFileManager.CYCODE_HIDDEN_DIRECTORY, ConfigFileManager.FILE_NAME)
- def _get_exclusions_by_exclusion_type(self, scan_type, exclusion_type) -> List:
+ def _get_exclusions_by_exclusion_type(self, scan_type: str, exclusion_type: str) -> List[Any]:
scan_type_exclusions = self.get_exclusions_by_scan_type(scan_type)
return scan_type_exclusions.get(exclusion_type, [])
- def _get_value_from_environment_section(self, field_name: str):
+ def _get_value_from_environment_section(self, field_name: str) -> Optional[Any]:
environment_section = self._get_section(self.ENVIRONMENT_SECTION_NAME)
return environment_section.get(field_name)
- def _get_scan_configuration_by_scan_type(self, command_scan_type: str) -> Dict:
+ def _get_scan_configuration_by_scan_type(self, command_scan_type: str) -> Dict[Hashable, Any]:
scan_section = self._get_section(self.SCAN_SECTION_NAME)
return scan_section.get(command_scan_type, {})
- def _get_value_from_command_scan_type_configuration(self, command_scan_type: str, field_name: str):
+ def _get_value_from_command_scan_type_configuration(self, command_scan_type: str, field_name: str) -> Optional[Any]:
command_scan_type_configuration = self._get_scan_configuration_by_scan_type(command_scan_type)
return command_scan_type_configuration.get(field_name)
- def _get_section(self, section_name: str) -> Dict:
+ def _get_section(self, section_name: str) -> Dict[Hashable, Any]:
file_content = self.read_file()
return file_content.get(section_name, {})
diff --git a/cycode/cli/user_settings/configuration_manager.py b/cycode/cli/user_settings/configuration_manager.py
index f93759c9..947781da 100644
--- a/cycode/cli/user_settings/configuration_manager.py
+++ b/cycode/cli/user_settings/configuration_manager.py
@@ -1,6 +1,6 @@
import os
from pathlib import Path
-from typing import Dict, Optional
+from typing import Any, Dict, Optional
from uuid import uuid4
from cycode.cli import consts
@@ -11,7 +11,7 @@ class ConfigurationManager:
global_config_file_manager: ConfigFileManager
local_config_file_manager: ConfigFileManager
- def __init__(self):
+ def __init__(self) -> None:
self.global_config_file_manager = ConfigFileManager(Path.home())
self.local_config_file_manager = ConfigFileManager(os.getcwd())
@@ -61,12 +61,12 @@ def get_verbose_flag_from_environment_variables(self) -> bool:
value = self._get_value_from_environment_variables(consts.VERBOSE_ENV_VAR_NAME, '')
return value.lower() in ('true', '1')
- def get_exclusions_by_scan_type(self, scan_type) -> Dict:
+ def get_exclusions_by_scan_type(self, scan_type: str) -> Dict:
local_exclusions = self.local_config_file_manager.get_exclusions_by_scan_type(scan_type)
global_exclusions = self.global_config_file_manager.get_exclusions_by_scan_type(scan_type)
return self._merge_exclusions(local_exclusions, global_exclusions)
- def add_exclusion(self, scope: str, scan_type: str, exclusion_type: str, value: str):
+ def add_exclusion(self, scope: str, scan_type: str, exclusion_type: str, value: str) -> None:
config_file_manager = self.get_config_file_manager(scope)
config_file_manager.add_exclusion(scan_type, exclusion_type, value)
@@ -74,7 +74,7 @@ def _merge_exclusions(self, local_exclusions: Dict, global_exclusions: Dict) ->
keys = set(list(local_exclusions.keys()) + list(global_exclusions.keys()))
return {key: local_exclusions.get(key, []) + global_exclusions.get(key, []) for key in keys}
- def update_base_url(self, base_url: str, scope: str = 'local'):
+ def update_base_url(self, base_url: str, scope: str = 'local') -> None:
config_file_manager = self.get_config_file_manager(scope)
config_file_manager.update_base_url(base_url)
@@ -162,5 +162,5 @@ def get_should_exclude_detections_in_deleted_lines(self, command_scan_type: str)
return consts.DEFAULT_EXCLUDE_DETECTIONS_IN_DELETED_LINES
@staticmethod
- def _get_value_from_environment_variables(env_var_name, default=None):
+ def _get_value_from_environment_variables(env_var_name: str, default: Optional[Any] = None) -> Optional[Any]:
return os.getenv(env_var_name, default)
diff --git a/cycode/cli/user_settings/credentials_manager.py b/cycode/cli/user_settings/credentials_manager.py
index 0ec0e6e8..02653f6d 100644
--- a/cycode/cli/user_settings/credentials_manager.py
+++ b/cycode/cli/user_settings/credentials_manager.py
@@ -1,5 +1,6 @@
import os
from pathlib import Path
+from typing import Optional, Tuple
from cycode.cli.config import CYCODE_CLIENT_ID_ENV_VAR_NAME, CYCODE_CLIENT_SECRET_ENV_VAR_NAME
from cycode.cli.user_settings.base_file_manager import BaseFileManager
@@ -13,19 +14,20 @@ class CredentialsManager(BaseFileManager):
CLIENT_ID_FIELD_NAME: str = 'cycode_client_id'
CLIENT_SECRET_FIELD_NAME: str = 'cycode_client_secret'
- def get_credentials(self) -> (str, str):
+ def get_credentials(self) -> Tuple[str, str]:
client_id, client_secret = self.get_credentials_from_environment_variables()
if client_id is not None and client_secret is not None:
return client_id, client_secret
return self.get_credentials_from_file()
- def get_credentials_from_environment_variables(self) -> (str, str):
+ @staticmethod
+ def get_credentials_from_environment_variables() -> Tuple[str, str]:
client_id = os.getenv(CYCODE_CLIENT_ID_ENV_VAR_NAME)
client_secret = os.getenv(CYCODE_CLIENT_SECRET_ENV_VAR_NAME)
return client_id, client_secret
- def get_credentials_from_file(self) -> (str, str):
+ def get_credentials_from_file(self) -> Tuple[Optional[str], Optional[str]]:
credentials_filename = self.get_filename()
try:
file_content = read_file(credentials_filename)
@@ -36,7 +38,7 @@ def get_credentials_from_file(self) -> (str, str):
client_secret = file_content.get(self.CLIENT_SECRET_FIELD_NAME)
return client_id, client_secret
- def update_credentials_file(self, client_id: str, client_secret: str):
+ def update_credentials_file(self, client_id: str, client_secret: str) -> None:
credentials = {self.CLIENT_ID_FIELD_NAME: client_id, self.CLIENT_SECRET_FIELD_NAME: client_secret}
self.get_filename()
diff --git a/cycode/cli/user_settings/user_settings_commands.py b/cycode/cli/user_settings/user_settings_commands.py
index f4fb5bee..500b13db 100644
--- a/cycode/cli/user_settings/user_settings_commands.py
+++ b/cycode/cli/user_settings/user_settings_commands.py
@@ -24,7 +24,7 @@
@click.command(
short_help='Initial command to authenticate your CLI client with Cycode using client ID and client secret'
)
-def set_credentials():
+def set_credentials() -> None:
click.echo(f'Update credentials in file ({credentials_manager.get_filename()})')
current_client_id, current_client_secret = credentials_manager.get_credentials_from_file()
client_id = _get_client_id_input(current_client_id)
@@ -85,7 +85,7 @@ def set_credentials():
)
def add_exclusions(
by_value: str, by_sha: str, by_path: str, by_rule: str, by_package: str, scan_type: str, is_global: bool
-):
+) -> None:
"""Ignore a specific value, path or rule ID"""
if not by_value and not by_sha and not by_path and not by_rule and not by_package:
raise click.ClickException('ignore by type is missing')
@@ -143,14 +143,14 @@ def _get_client_secret_input(current_client_secret: str) -> str:
return new_client_secret if new_client_secret else current_client_secret
-def _get_credentials_update_result_message():
+def _get_credentials_update_result_message() -> str:
if not _are_credentials_exist_in_environment_variables():
return CREDENTIALS_UPDATED_SUCCESSFULLY_MESSAGE
return CREDENTIALS_UPDATED_SUCCESSFULLY_MESSAGE + ' ' + CREDENTIALS_ARE_SET_IN_ENVIRONMENT_VARIABLES_MESSAGE
-def _are_credentials_exist_in_environment_variables():
+def _are_credentials_exist_in_environment_variables() -> bool:
client_id, client_secret = credentials_manager.get_credentials_from_environment_variables()
return client_id is not None or client_secret is not None
diff --git a/cycode/cli/utils/enum_utils.py b/cycode/cli/utils/enum_utils.py
index 54a02ffb..6ea9ef72 100644
--- a/cycode/cli/utils/enum_utils.py
+++ b/cycode/cli/utils/enum_utils.py
@@ -1,7 +1,8 @@
from enum import Enum
+from typing import List
class AutoCountEnum(Enum):
@staticmethod
- def _generate_next_value_(name, start, count, last_values):
+ def _generate_next_value_(name: str, start: int, count: int, last_values: List[int]) -> int:
return count
diff --git a/cycode/cli/utils/path_utils.py b/cycode/cli/utils/path_utils.py
index 3522807a..e25daede 100644
--- a/cycode/cli/utils/path_utils.py
+++ b/cycode/cli/utils/path_utils.py
@@ -1,6 +1,6 @@
import os
from pathlib import Path
-from typing import AnyStr, Iterable, List, Optional
+from typing import AnyStr, Generator, Iterable, List, Optional
import pathspec
from binaryornot.check import is_binary
@@ -49,12 +49,12 @@ def get_path_by_os(filename: str) -> str:
return filename.replace('/', os.sep)
-def _get_all_existing_files_in_directory(path: str):
+def _get_all_existing_files_in_directory(path: str) -> Generator[Path, None, None]:
directory = Path(path)
return directory.rglob(r'*')
-def is_path_exists(path: str):
+def is_path_exists(path: str) -> bool:
return os.path.exists(path)
diff --git a/cycode/cli/utils/progress_bar.py b/cycode/cli/utils/progress_bar.py
index 38e00984..e340fb92 100644
--- a/cycode/cli/utils/progress_bar.py
+++ b/cycode/cli/utils/progress_bar.py
@@ -9,6 +9,7 @@
if TYPE_CHECKING:
from click._termui_impl import ProgressBar
+ from click.termui import V as ProgressBarValue
logger = get_logger('progress bar')
@@ -57,7 +58,7 @@ def _get_section_length(section: 'ProgressBarSection') -> int:
class BaseProgressBar(ABC):
@abstractmethod
- def __init__(self, *args, **kwargs):
+ def __init__(self, *args, **kwargs) -> None:
pass
@abstractmethod
@@ -86,7 +87,7 @@ def update(self, section: 'ProgressBarSection') -> None:
class DummyProgressBar(BaseProgressBar):
- def __init__(self, *args, **kwargs):
+ def __init__(self, *args, **kwargs) -> None:
super().__init__(*args, **kwargs)
def __enter__(self) -> 'DummyProgressBar':
@@ -109,7 +110,7 @@ def update(self, section: 'ProgressBarSection') -> None:
class CompositeProgressBar(BaseProgressBar):
- def __init__(self):
+ def __init__(self) -> None:
super().__init__()
self._progress_bar_context_manager = click.progressbar(
length=_PROGRESS_BAR_LENGTH,
@@ -192,7 +193,7 @@ def _get_increment_progress_value(self, section: 'ProgressBarSection') -> int:
return expected_value - self._current_section_value
- def _progress_bar_item_show_func(self, _=None) -> str:
+ def _progress_bar_item_show_func(self, _: Optional['ProgressBarValue'] = None) -> str:
return self._current_section.label
def update(self, section: 'ProgressBarSection', value: int = 1) -> None:
diff --git a/cycode/cli/utils/scan_batch.py b/cycode/cli/utils/scan_batch.py
index 0f47c30c..4c839440 100644
--- a/cycode/cli/utils/scan_batch.py
+++ b/cycode/cli/utils/scan_batch.py
@@ -44,7 +44,8 @@ def split_documents_into_batches(
def _get_threads_count() -> int:
- return min(os.cpu_count() * SCAN_BATCH_SCANS_PER_CPU, SCAN_BATCH_MAX_PARALLEL_SCANS)
+ cpu_count = os.cpu_count() or 1
+ return min(cpu_count * SCAN_BATCH_SCANS_PER_CPU, SCAN_BATCH_MAX_PARALLEL_SCANS)
def run_parallel_batched_scan(
diff --git a/cycode/cli/utils/shell_executor.py b/cycode/cli/utils/shell_executor.py
index 6b992738..a4ed889a 100644
--- a/cycode/cli/utils/shell_executor.py
+++ b/cycode/cli/utils/shell_executor.py
@@ -9,7 +9,7 @@
def shell(
- command: Union[str, List[str]], timeout: int = _SUBPROCESS_DEFAULT_TIMEOUT_SEC, execute_in_shell=False
+ command: Union[str, List[str]], timeout: int = _SUBPROCESS_DEFAULT_TIMEOUT_SEC, execute_in_shell: bool = False
) -> Optional[str]:
logger.debug(f'Executing shell command: {command}')
diff --git a/cycode/cli/utils/string_utils.py b/cycode/cli/utils/string_utils.py
index 790f65b2..9dce0026 100644
--- a/cycode/cli/utils/string_utils.py
+++ b/cycode/cli/utils/string_utils.py
@@ -30,19 +30,19 @@ def is_binary_content(content: str) -> bool:
return is_binary_string(chunk_bytes)
-def get_content_size(content: str):
+def get_content_size(content: str) -> int:
return getsizeof(content)
-def convert_string_to_bytes(content: str):
+def convert_string_to_bytes(content: str) -> bytes:
return bytes(content, 'UTF-8')
-def hash_string_to_sha256(content: str):
+def hash_string_to_sha256(content: str) -> str:
return hashlib.sha256(content.encode()).hexdigest()
-def generate_random_string(string_len: int):
+def generate_random_string(string_len: int) -> str:
# letters, digits, and symbols
characters = string.ascii_letters + string.digits + string.punctuation
return ''.join(random.choice(characters) for _ in range(string_len)) # noqa: S311
diff --git a/cycode/cli/utils/task_timer.py b/cycode/cli/utils/task_timer.py
index d6399ba7..0179179d 100644
--- a/cycode/cli/utils/task_timer.py
+++ b/cycode/cli/utils/task_timer.py
@@ -5,7 +5,7 @@
class FunctionContext:
- def __init__(self, function: Callable, args: Optional[List] = None, kwargs: Optional[Dict] = None):
+ def __init__(self, function: Callable, args: Optional[List] = None, kwargs: Optional[Dict] = None) -> None:
self.function = function
self.args = args or []
self.kwargs = kwargs or {}
@@ -20,25 +20,25 @@ class TimerThread(Thread):
quit_function (Mandatory) - function to perform when reaching to timeout
"""
- def __init__(self, timeout: int, quit_function: FunctionContext):
+ def __init__(self, timeout: int, quit_function: FunctionContext) -> None:
Thread.__init__(self)
self._timeout = timeout
self._quit_function = quit_function
self.event = Event()
- def run(self):
+ def run(self) -> None:
self._run_quit_function_on_timeout()
- def stop(self):
+ def stop(self) -> None:
self.event.set()
- def _run_quit_function_on_timeout(self):
+ def _run_quit_function_on_timeout(self) -> None:
self.event.wait(self._timeout)
if not self.event.is_set():
self._call_quit_function()
self.stop()
- def _call_quit_function(self):
+ def _call_quit_function(self) -> None:
self._quit_function.function(*self._quit_function.args, **self._quit_function.kwargs)
@@ -56,7 +56,7 @@ class TimeoutAfter:
the default option is to interrupt main thread
"""
- def __init__(self, timeout: int, quit_function: Optional[FunctionContext] = None):
+ def __init__(self, timeout: int, quit_function: Optional[FunctionContext] = None) -> None:
self.timeout = timeout
self._quit_function = quit_function or FunctionContext(function=self.timeout_function)
self.timer = TimerThread(timeout, quit_function=self._quit_function)
@@ -76,5 +76,5 @@ def __exit__(
if exc_type == KeyboardInterrupt:
raise TimeoutError(f'Task timed out after {self.timeout} seconds')
- def timeout_function(self):
+ def timeout_function(self) -> None:
interrupt_main()
diff --git a/cycode/cli/utils/yaml_utils.py b/cycode/cli/utils/yaml_utils.py
index b9e9f408..3f910537 100644
--- a/cycode/cli/utils/yaml_utils.py
+++ b/cycode/cli/utils/yaml_utils.py
@@ -1,14 +1,14 @@
-from typing import Dict
+from typing import Any, Dict, Hashable
import yaml
-def read_file(filename: str) -> Dict:
+def read_file(filename: str) -> Dict[Hashable, Any]:
with open(filename, 'r', encoding='UTF-8') as file:
return yaml.safe_load(file)
-def update_file(filename: str, content: Dict):
+def update_file(filename: str, content: Dict[Hashable, Any]) -> None:
try:
with open(filename, 'r', encoding='UTF-8') as file:
file_content = yaml.safe_load(file)
@@ -20,7 +20,7 @@ def update_file(filename: str, content: Dict):
yaml.safe_dump(file_content, file)
-def _deep_update(source, overrides):
+def _deep_update(source: Dict[Hashable, Any], overrides: Dict[Hashable, Any]) -> Dict[Hashable, Any]:
for key, value in overrides.items():
if isinstance(value, dict) and value:
source[key] = _deep_update(source.get(key, {}), value)
diff --git a/cycode/cli/zip_file.py b/cycode/cli/zip_file.py
index d4c5c3fc..7d659c8e 100644
--- a/cycode/cli/zip_file.py
+++ b/cycode/cli/zip_file.py
@@ -1,22 +1,23 @@
import os.path
from io import BytesIO
+from typing import Optional
from zipfile import ZIP_DEFLATED, ZipFile
class InMemoryZip(object):
- def __init__(self):
+ def __init__(self) -> None:
# Create the in-memory file-like object
self.in_memory_zip = BytesIO()
self.zip = ZipFile(self.in_memory_zip, 'a', ZIP_DEFLATED, False)
- def append(self, filename, unique_id, content):
+ def append(self, filename: str, unique_id: Optional[str], content: str) -> None:
# Write the file to the in-memory zip
if unique_id:
filename = concat_unique_id(filename, unique_id)
self.zip.writestr(filename, content)
- def close(self):
+ def close(self) -> None:
self.zip.close()
# to bytes
@@ -27,7 +28,7 @@ def read(self) -> bytes:
def concat_unique_id(filename: str, unique_id: str) -> str:
if filename.startswith(os.sep):
- # remove leading slash to join path correctly
+ # remove leading slash to join the path correctly
filename = filename[len(os.sep) :]
return os.path.join(unique_id, filename)
diff --git a/cycode/cyclient/auth_client.py b/cycode/cyclient/auth_client.py
index 5717c583..9cd35f34 100644
--- a/cycode/cyclient/auth_client.py
+++ b/cycode/cyclient/auth_client.py
@@ -11,7 +11,7 @@
class AuthClient:
AUTH_CONTROLLER_PATH = 'api/v1/device-auth'
- def __init__(self):
+ def __init__(self) -> None:
self.cycode_client = CycodeClient()
def start_session(self, code_challenge: str) -> models.AuthenticationSession:
diff --git a/cycode/cyclient/config.py b/cycode/cyclient/config.py
index c6ed6432..2c2f3c00 100644
--- a/cycode/cyclient/config.py
+++ b/cycode/cyclient/config.py
@@ -1,6 +1,7 @@
import logging
import os
import sys
+from typing import Optional
from urllib.parse import urlparse
from cycode.cli import consts
@@ -39,7 +40,7 @@
configuration = dict(DEFAULT_CONFIGURATION, **os.environ)
-def get_logger(logger_name=None):
+def get_logger(logger_name: Optional[str] = None) -> logging.Logger:
logger = logging.getLogger(logger_name)
level = _get_val_as_string(consts.LOGGING_LEVEL_ENV_VAR_NAME)
level = level if level in logging._nameToLevel else int(level)
@@ -48,18 +49,21 @@ def get_logger(logger_name=None):
return logger
-def _get_val_as_string(key):
+def _get_val_as_string(key: str) -> str:
return configuration.get(key)
-def _get_val_as_bool(key, default=''):
+def _get_val_as_bool(key: str, default: str = '') -> bool:
val = configuration.get(key, default)
return val.lower() in ('true', '1')
-def _get_val_as_int(key):
+def _get_val_as_int(key: str) -> Optional[int]:
val = configuration.get(key)
- return int(val) if val is not None else None
+ if val:
+ return int(val)
+
+ return None
logger = get_logger('cycode cli')
diff --git a/cycode/cyclient/cycode_client.py b/cycode/cyclient/cycode_client.py
index ed3781f7..dfbd2269 100644
--- a/cycode/cyclient/cycode_client.py
+++ b/cycode/cyclient/cycode_client.py
@@ -3,6 +3,6 @@
class CycodeClient(CycodeClientBase):
- def __init__(self):
+ def __init__(self) -> None:
super().__init__(config.cycode_api_url)
self.timeout = config.timeout
diff --git a/cycode/cyclient/cycode_client_base.py b/cycode/cyclient/cycode_client_base.py
index d4c27c0e..031d184b 100644
--- a/cycode/cyclient/cycode_client_base.py
+++ b/cycode/cyclient/cycode_client_base.py
@@ -31,7 +31,7 @@ def get_cli_user_agent() -> str:
class CycodeClientBase:
MANDATORY_HEADERS: ClassVar[Dict[str, str]] = {'User-Agent': get_cli_user_agent()}
- def __init__(self, api_url: str):
+ def __init__(self, api_url: str) -> None:
self.timeout = config.timeout
self.api_url = api_url
@@ -69,7 +69,7 @@ def _execute(
except Exception as e:
self._handle_exception(e)
- def get_request_headers(self, additional_headers: Optional[dict] = None, **kwargs) -> dict:
+ def get_request_headers(self, additional_headers: Optional[dict] = None, **kwargs) -> Dict[str, str]:
if additional_headers is None:
return self.MANDATORY_HEADERS.copy()
return {**self.MANDATORY_HEADERS, **additional_headers}
@@ -77,7 +77,7 @@ def get_request_headers(self, additional_headers: Optional[dict] = None, **kwarg
def build_full_url(self, url: str, endpoint: str) -> str:
return f'{url}/{endpoint}'
- def _handle_exception(self, e: Exception):
+ def _handle_exception(self, e: Exception) -> None:
if isinstance(e, exceptions.Timeout):
raise NetworkError(504, 'Timeout Error', e.response)
@@ -89,7 +89,7 @@ def _handle_exception(self, e: Exception):
raise e
@staticmethod
- def _handle_http_exception(e: exceptions.HTTPError):
+ def _handle_http_exception(e: exceptions.HTTPError) -> None:
if e.response.status_code == 401:
raise HttpUnauthorizedError(e.response.text, e.response)
diff --git a/cycode/cyclient/cycode_dev_based_client.py b/cycode/cyclient/cycode_dev_based_client.py
index bb647acf..f325bd6e 100644
--- a/cycode/cyclient/cycode_dev_based_client.py
+++ b/cycode/cyclient/cycode_dev_based_client.py
@@ -1,4 +1,4 @@
-from typing import Optional
+from typing import Dict, Optional
from .config import dev_tenant_id
from .cycode_client_base import CycodeClientBase
@@ -9,14 +9,14 @@
class CycodeDevBasedClient(CycodeClientBase):
- def __init__(self, api_url):
+ def __init__(self, api_url: str) -> None:
super().__init__(api_url)
- def get_request_headers(self, additional_headers: Optional[dict] = None):
+ def get_request_headers(self, additional_headers: Optional[dict] = None, **_) -> Dict[str, str]:
headers = super().get_request_headers(additional_headers=additional_headers)
headers['X-Tenant-Id'] = dev_tenant_id
return headers
- def build_full_url(self, url, endpoint):
+ def build_full_url(self, url: str, endpoint: str) -> str:
return f'{url}:{endpoint}'
diff --git a/cycode/cyclient/cycode_token_based_client.py b/cycode/cyclient/cycode_token_based_client.py
index b8898a41..59287c80 100644
--- a/cycode/cyclient/cycode_token_based_client.py
+++ b/cycode/cyclient/cycode_token_based_client.py
@@ -9,7 +9,7 @@
class CycodeTokenBasedClient(CycodeClient):
"""Send requests with api token"""
- def __init__(self, client_id: str, client_secret: str):
+ def __init__(self, client_id: str, client_secret: str) -> None:
super().__init__()
self.client_secret = client_secret
self.client_id = client_id
@@ -41,7 +41,7 @@ def refresh_api_token(self) -> None:
self._api_token = auth_response_data['token']
self._expires_in = arrow.utcnow().shift(seconds=auth_response_data['expires_in'] * 0.8)
- def get_request_headers(self, additional_headers: Optional[dict] = None, without_auth=False) -> dict:
+ def get_request_headers(self, additional_headers: Optional[dict] = None, without_auth: bool = False) -> dict:
headers = super().get_request_headers(additional_headers=additional_headers)
if not without_auth:
diff --git a/cycode/cyclient/models.py b/cycode/cyclient/models.py
index 89e39b11..f5983083 100644
--- a/cycode/cyclient/models.py
+++ b/cycode/cyclient/models.py
@@ -1,5 +1,5 @@
from dataclasses import dataclass
-from typing import Dict, List, Optional
+from typing import Any, Dict, List, Optional
from marshmallow import EXCLUDE, Schema, fields, post_load
@@ -13,7 +13,7 @@ def __init__(
detection_details: dict,
detection_rule_id: str,
severity: Optional[str] = None,
- ):
+ ) -> None:
super().__init__()
self.message = message
self.type = type
@@ -45,12 +45,12 @@ class Meta:
detection_rule_id = fields.String()
@post_load
- def build_dto(self, data, **kwargs):
+ def build_dto(self, data: Dict[str, Any], **_) -> Detection:
return Detection(**data)
class DetectionsPerFile(Schema):
- def __init__(self, file_name: str, detections: List[Detection], commit_id: Optional[str] = None):
+ def __init__(self, file_name: str, detections: List[Detection], commit_id: Optional[str] = None) -> None:
super().__init__()
self.file_name = file_name
self.detections = detections
@@ -66,7 +66,7 @@ class Meta:
commit_id = fields.String(allow_none=True)
@post_load
- def build_dto(self, data, **kwargs):
+ def build_dto(self, data: Dict[str, Any], **_) -> 'DetectionsPerFile':
return DetectionsPerFile(**data)
@@ -78,7 +78,7 @@ def __init__(
report_url: Optional[str] = None,
scan_id: Optional[str] = None,
err: Optional[str] = None,
- ):
+ ) -> None:
super().__init__()
self.did_detect = did_detect
self.detections_per_file = detections_per_file
@@ -98,7 +98,7 @@ class Meta:
err = fields.String()
@post_load
- def build_dto(self, data, **kwargs):
+ def build_dto(self, data: Dict[str, Any], **_) -> 'ZippedFileScanResult':
return ZippedFileScanResult(**data)
@@ -109,7 +109,7 @@ def __init__(
scan_id: Optional[str] = None,
detections: Optional[List[Detection]] = None,
err: Optional[str] = None,
- ):
+ ) -> None:
super().__init__()
self.did_detect = did_detect
self.scan_id = scan_id
@@ -127,12 +127,12 @@ class Meta:
err = fields.String()
@post_load
- def build_dto(self, data, **kwargs):
+ def build_dto(self, data: Dict[str, Any], **_) -> 'ScanResult':
return ScanResult(**data)
class ScanInitializationResponse(Schema):
- def __init__(self, scan_id: Optional[str] = None, err: Optional[str] = None):
+ def __init__(self, scan_id: Optional[str] = None, err: Optional[str] = None) -> None:
super().__init__()
self.scan_id = scan_id
self.err = err
@@ -146,7 +146,7 @@ class Meta:
err = fields.String()
@post_load
- def build_dto(self, data, **kwargs):
+ def build_dto(self, data: Dict[str, Any], **_) -> 'ScanInitializationResponse':
return ScanInitializationResponse(**data)
@@ -160,7 +160,7 @@ def __init__(
message: Optional[str] = None,
scan_update_at: Optional[str] = None,
err: Optional[str] = None,
- ):
+ ) -> None:
super().__init__()
self.id = id
self.scan_status = scan_status
@@ -184,12 +184,12 @@ class Meta:
err = fields.String()
@post_load
- def build_dto(self, data, **kwargs):
+ def build_dto(self, data: Dict[str, Any], **_) -> 'ScanDetailsResponse':
return ScanDetailsResponse(**data)
class K8SResource:
- def __init__(self, name: str, resource_type: str, namespace: str, content: Dict):
+ def __init__(self, name: str, resource_type: str, namespace: str, content: Dict) -> None:
super().__init__()
self.name = name
self.type = resource_type
@@ -198,23 +198,23 @@ def __init__(self, name: str, resource_type: str, namespace: str, content: Dict)
self.internal_metadata = None
self.schema = K8SResourceSchema()
- def to_json(self):
+ def to_json(self) -> dict: # FIXME(MarshalX): rename to to_dict?
return self.schema.dump(self)
class InternalMetadata:
- def __init__(self, root_entity_name: str, root_entity_type: str):
+ def __init__(self, root_entity_name: str, root_entity_type: str) -> None:
super().__init__()
self.root_entity_name = root_entity_name
self.root_entity_type = root_entity_type
self.schema = InternalMetadataSchema()
- def to_json(self):
+ def to_json(self) -> dict: # FIXME(MarshalX): rename to to_dict?
return self.schema.dump(self)
class ResourcesCollection:
- def __init__(self, resource_type: str, namespace: str, resources: List[K8SResource], total_count: int):
+ def __init__(self, resource_type: str, namespace: str, resources: List[K8SResource], total_count: int) -> None:
super().__init__()
self.type = resource_type
self.namespace = namespace
@@ -222,7 +222,7 @@ def __init__(self, resource_type: str, namespace: str, resources: List[K8SResour
self.total_count = total_count
self.schema = ResourcesCollectionSchema()
- def to_json(self):
+ def to_json(self) -> dict: # FIXME(MarshalX): rename to to_dict?
return self.schema.dump(self)
@@ -247,17 +247,17 @@ class ResourcesCollectionSchema(Schema):
class OwnerReference:
- def __init__(self, name: str, kind: str):
+ def __init__(self, name: str, kind: str) -> None:
super().__init__()
self.name = name
self.kind = kind
- def __str__(self):
+ def __str__(self) -> str:
return 'Name: {0}, Kind: {1}'.format(self.name, self.kind)
class AuthenticationSession(Schema):
- def __init__(self, session_id: str):
+ def __init__(self, session_id: str) -> None:
super().__init__()
self.session_id = session_id
@@ -269,12 +269,12 @@ class Meta:
session_id = fields.String()
@post_load
- def build_dto(self, data, **kwargs):
+ def build_dto(self, data: Dict[str, Any], **_) -> 'AuthenticationSession':
return AuthenticationSession(**data)
class ApiToken(Schema):
- def __init__(self, client_id: str, secret: str, description: str):
+ def __init__(self, client_id: str, secret: str, description: str) -> None:
super().__init__()
self.client_id = client_id
self.secret = secret
@@ -290,12 +290,12 @@ class Meta:
description = fields.String()
@post_load
- def build_dto(self, data, **kwargs):
+ def build_dto(self, data: Dict[str, Any], **_) -> 'ApiToken':
return ApiToken(**data)
class ApiTokenGenerationPollingResponse(Schema):
- def __init__(self, status: str, api_token):
+ def __init__(self, status: str, api_token: 'ApiToken') -> None:
super().__init__()
self.status = status
self.api_token = api_token
@@ -309,7 +309,7 @@ class Meta:
api_token = fields.Nested(ApiTokenSchema, allow_none=True)
@post_load
- def build_dto(self, data, **kwargs):
+ def build_dto(self, data: Dict[str, Any], **_) -> 'ApiTokenGenerationPollingResponse':
return ApiTokenGenerationPollingResponse(**data)
@@ -320,7 +320,7 @@ class UserAgentOptionScheme(Schema):
env_version = fields.String(required=True) # ex. 1.78.2
@post_load
- def build_dto(self, data: dict, **_) -> 'UserAgentOption':
+ def build_dto(self, data: Dict[str, Any], **_) -> 'UserAgentOption':
return UserAgentOption(**data)
diff --git a/cycode/cyclient/scan_client.py b/cycode/cyclient/scan_client.py
index 03844da1..3eb3b310 100644
--- a/cycode/cyclient/scan_client.py
+++ b/cycode/cyclient/scan_client.py
@@ -11,7 +11,7 @@
class ScanClient:
- def __init__(self, scan_cycode_client: CycodeClientBase, scan_config: ScanConfigBase):
+ def __init__(self, scan_cycode_client: CycodeClientBase, scan_config: ScanConfigBase) -> None:
self.scan_cycode_client = scan_cycode_client
self.scan_config = scan_config
self.SCAN_CONTROLLER_PATH = 'api/v1/scan'
@@ -119,7 +119,7 @@ def commit_range_zipped_file_scan(
response = self.scan_cycode_client.post(url_path=url_path, data={'scan_id': scan_id}, files=files)
return self.parse_zipped_file_scan_response(response)
- def report_scan_status(self, scan_type: str, scan_id: str, scan_status: dict):
+ def report_scan_status(self, scan_type: str, scan_id: str, scan_status: dict) -> None:
url_path = f'{self.scan_config.get_service_name(scan_type)}/{self.SCAN_CONTROLLER_PATH}/{scan_id}/status'
self.scan_cycode_client.post(url_path=url_path, body=scan_status)
diff --git a/cycode/cyclient/scan_config/scan_config_base.py b/cycode/cyclient/scan_config/scan_config_base.py
index b4e0cb53..976008bb 100644
--- a/cycode/cyclient/scan_config/scan_config_base.py
+++ b/cycode/cyclient/scan_config/scan_config_base.py
@@ -1,51 +1,49 @@
from abc import ABC, abstractmethod
-from typing import Optional
class ScanConfigBase(ABC):
@abstractmethod
- def get_service_name(self, scan_type):
- pass
+ def get_service_name(self, scan_type: str) -> str:
+ ...
@abstractmethod
- def get_scans_prefix(self):
- pass
+ def get_scans_prefix(self) -> str:
+ ...
@abstractmethod
- def get_detections_prefix(self):
- pass
+ def get_detections_prefix(self) -> str:
+ ...
class DevScanConfig(ScanConfigBase):
- def get_service_name(self, scan_type):
+ def get_service_name(self, scan_type: str) -> str:
if scan_type == 'secret':
return '5025'
if scan_type == 'iac':
return '5026'
- if scan_type == 'sca' or scan_type == 'sast':
- return '5004'
- return None
- def get_scans_prefix(self):
+ # sca and sast
return '5004'
- def get_detections_prefix(self):
+ def get_scans_prefix(self) -> str:
+ return '5004'
+
+ def get_detections_prefix(self) -> str:
return '5016'
class DefaultScanConfig(ScanConfigBase):
- def get_service_name(self, scan_type) -> Optional[str]:
+ def get_service_name(self, scan_type: str) -> str:
if scan_type == 'secret':
return 'secret'
if scan_type == 'iac':
return 'iac'
- if scan_type == 'sca' or scan_type == 'sast':
- return 'scans'
- return None
+ # sca and sast
+ return 'scans'
- def get_scans_prefix(self):
+ def get_scans_prefix(self) -> str:
return 'scans'
- def get_detections_prefix(self):
+ def get_detections_prefix(self) -> str:
return 'detections'
diff --git a/cycode/cyclient/utils.py b/cycode/cyclient/utils.py
deleted file mode 100644
index 4b6c1d1c..00000000
--- a/cycode/cyclient/utils.py
+++ /dev/null
@@ -1,10 +0,0 @@
-import os
-
-
-def split_list(input_list, batch_size):
- for i in range(0, len(input_list), batch_size):
- yield input_list[i : i + batch_size]
-
-
-def cpu_count():
- return os.cpu_count() or 1
diff --git a/pyproject.toml b/pyproject.toml
index dd3c8e04..292e53d8 100644
--- a/pyproject.toml
+++ b/pyproject.toml
@@ -96,7 +96,7 @@ extend-select = [
"Q", # flake8-quotes
"S", # flake8-bandit
"ASYNC", # flake8-async
- # "ANN", # flake8-annotations. Enable later
+ "ANN", # flake8-annotations
"C",
"BLE",
"ERA",
@@ -111,12 +111,18 @@ extend-select = [
"RUF",
"SIM",
"T20",
- # "TCH", # it can't be autofixed yet
+ "TCH",
"TID",
"YTT",
]
line-length = 120
target-version = "py37"
+ignore = [
+ "ANN002", # Missing type annotation for `*args`
+ "ANN003", # Missing type annotation for `**kwargs`
+ "ANN101", # Missing type annotation for `self` in method
+ "ANN102", # Missing type annotation for `cls` in classmethod
+]
[tool.ruff.flake8-quotes]
docstring-quotes = "double"
diff --git a/tests/__init__.py b/tests/__init__.py
index 80fbb2d8..617049bb 100644
--- a/tests/__init__.py
+++ b/tests/__init__.py
@@ -28,7 +28,3 @@
}
K8S_POD_MOCK = K8SResource('pod-template-123xyz', 'pod', 'default', POD_MOCK)
-
-
-def list_to_str(values):
- return ','.join([str(val) for val in values])
diff --git a/tests/cli/test_code_scanner.py b/tests/cli/test_code_scanner.py
index 041dac49..0bd02845 100644
--- a/tests/cli/test_code_scanner.py
+++ b/tests/cli/test_code_scanner.py
@@ -1,4 +1,5 @@
import os
+from typing import TYPE_CHECKING
import click
import pytest
@@ -9,9 +10,12 @@
from cycode.cli.code_scanner import _handle_exception, _is_file_relevant_for_sca_scan
from cycode.cli.exceptions import custom_exceptions
+if TYPE_CHECKING:
+ from _pytest.monkeypatch import MonkeyPatch
+
@pytest.fixture()
-def ctx():
+def ctx() -> click.Context:
return click.Context(click.Command('path'), obj={'verbose': False, 'output': 'text'})
@@ -27,7 +31,7 @@ def ctx():
)
def test_handle_exception_soft_fail(
ctx: click.Context, exception: custom_exceptions.CycodeError, expected_soft_fail: bool
-):
+) -> None:
with ctx:
_handle_exception(ctx, exception)
@@ -35,7 +39,7 @@ def test_handle_exception_soft_fail(
assert ctx.obj.get('soft_fail') is expected_soft_fail
-def test_handle_exception_unhandled_error(ctx: click.Context):
+def test_handle_exception_unhandled_error(ctx: click.Context) -> None:
with ctx, pytest.raises(ClickException):
_handle_exception(ctx, ValueError('test'))
@@ -43,7 +47,7 @@ def test_handle_exception_unhandled_error(ctx: click.Context):
assert ctx.obj.get('soft_fail') is None
-def test_handle_exception_click_error(ctx: click.Context):
+def test_handle_exception_click_error(ctx: click.Context) -> None:
with ctx, pytest.raises(ClickException):
_handle_exception(ctx, click.ClickException('test'))
@@ -51,10 +55,10 @@ def test_handle_exception_click_error(ctx: click.Context):
assert ctx.obj.get('soft_fail') is None
-def test_handle_exception_verbose(monkeypatch):
+def test_handle_exception_verbose(monkeypatch: 'MonkeyPatch') -> None:
ctx = click.Context(click.Command('path'), obj={'verbose': True, 'output': 'text'})
- def mock_secho(msg, *_, **__):
+ def mock_secho(msg: str, *_, **__) -> None:
assert 'Error:' in msg
monkeypatch.setattr(click, 'secho', mock_secho)
@@ -63,7 +67,7 @@ def mock_secho(msg, *_, **__):
_handle_exception(ctx, ValueError('test'))
-def test_is_file_relevant_for_sca_scan():
+def test_is_file_relevant_for_sca_scan() -> None:
path = os.path.join('some_package', 'node_modules', 'package.json')
assert _is_file_relevant_for_sca_scan(path) is False
path = os.path.join('some_package', 'node_modules', 'package.lock')
diff --git a/tests/cli/test_main.py b/tests/cli/test_main.py
index 2996c0d4..77375920 100644
--- a/tests/cli/test_main.py
+++ b/tests/cli/test_main.py
@@ -28,7 +28,7 @@ def _is_json(plain: str) -> bool:
@pytest.mark.parametrize('option_space', ['scan', 'global'])
def test_passing_output_option(
output: str, option_space: str, scan_client: 'ScanClient', api_token_response: responses.Response
-):
+) -> None:
scan_type = 'secret'
responses.add(get_zipped_file_scan_response(get_zipped_file_scan_url(scan_type, scan_client)))
diff --git a/tests/conftest.py b/tests/conftest.py
index 72860e70..ae7d4cd4 100644
--- a/tests/conftest.py
+++ b/tests/conftest.py
@@ -33,7 +33,7 @@ def api_token_url(token_based_client: CycodeTokenBasedClient) -> str:
@pytest.fixture(scope='session')
-def api_token_response(api_token_url) -> responses.Response:
+def api_token_response(api_token_url: str) -> responses.Response:
return responses.Response(
method=responses.POST,
url=api_token_url,
diff --git a/tests/cyclient/scan_config/test_default_scan_config.py b/tests/cyclient/scan_config/test_default_scan_config.py
index 1043f505..0945402b 100644
--- a/tests/cyclient/scan_config/test_default_scan_config.py
+++ b/tests/cyclient/scan_config/test_default_scan_config.py
@@ -1,7 +1,7 @@
from cycode.cyclient.scan_config.scan_config_creator import DefaultScanConfig
-def test_get_service_name():
+def test_get_service_name() -> None:
default_scan_config = DefaultScanConfig()
assert default_scan_config.get_service_name('secret') == 'secret'
@@ -10,13 +10,13 @@ def test_get_service_name():
assert default_scan_config.get_service_name('sast') == 'scans'
-def test_get_scans_prefix():
+def test_get_scans_prefix() -> None:
default_scan_config = DefaultScanConfig()
assert default_scan_config.get_scans_prefix() == 'scans'
-def test_get_detections_prefix():
+def test_get_detections_prefix() -> None:
default_scan_config = DefaultScanConfig()
assert default_scan_config.get_detections_prefix() == 'detections'
diff --git a/tests/cyclient/scan_config/test_dev_scan_config.py b/tests/cyclient/scan_config/test_dev_scan_config.py
index 28f42c63..0673d601 100644
--- a/tests/cyclient/scan_config/test_dev_scan_config.py
+++ b/tests/cyclient/scan_config/test_dev_scan_config.py
@@ -1,7 +1,7 @@
from cycode.cyclient.scan_config.scan_config_creator import DevScanConfig
-def test_get_service_name():
+def test_get_service_name() -> None:
dev_scan_config = DevScanConfig()
assert dev_scan_config.get_service_name('secret') == '5025'
@@ -10,13 +10,13 @@ def test_get_service_name():
assert dev_scan_config.get_service_name('sast') == '5004'
-def test_get_scans_prefix():
+def test_get_scans_prefix() -> None:
dev_scan_config = DevScanConfig()
assert dev_scan_config.get_scans_prefix() == '5004'
-def test_get_detections_prefix():
+def test_get_detections_prefix() -> None:
dev_scan_config = DevScanConfig()
assert dev_scan_config.get_detections_prefix() == '5016'
diff --git a/tests/cyclient/test_auth_client.py b/tests/cyclient/test_auth_client.py
index b3898fd3..0a34d3b2 100644
--- a/tests/cyclient/test_auth_client.py
+++ b/tests/cyclient/test_auth_client.py
@@ -48,7 +48,7 @@ def auth_token_url(client: AuthClient) -> str:
@responses.activate
-def test_start_session_success(client: AuthClient, start_url: str, code_challenge: str):
+def test_start_session_success(client: AuthClient, start_url: str, code_challenge: str) -> None:
responses.add(
responses.POST,
start_url,
@@ -62,7 +62,7 @@ def test_start_session_success(client: AuthClient, start_url: str, code_challeng
@responses.activate
-def test_start_session_timeout(client: AuthClient, start_url: str, code_challenge: str):
+def test_start_session_timeout(client: AuthClient, start_url: str, code_challenge: str) -> None:
responses.add(responses.POST, start_url, status=504)
timeout_response = requests.post(start_url, timeout=5)
@@ -83,7 +83,7 @@ def test_start_session_timeout(client: AuthClient, start_url: str, code_challeng
@responses.activate
-def test_start_session_http_error(client: AuthClient, start_url: str, code_challenge: str):
+def test_start_session_http_error(client: AuthClient, start_url: str, code_challenge: str) -> None:
responses.add(responses.POST, start_url, status=401)
with pytest.raises(CycodeError) as e_info:
@@ -93,7 +93,7 @@ def test_start_session_http_error(client: AuthClient, start_url: str, code_chall
@responses.activate
-def test_get_api_token_success_pending(client: AuthClient, token_url: str, code_verifier: str):
+def test_get_api_token_success_pending(client: AuthClient, token_url: str, code_verifier: str) -> None:
expected_status = 'Pending'
expected_api_token = None
@@ -111,7 +111,7 @@ def test_get_api_token_success_pending(client: AuthClient, token_url: str, code_
@responses.activate
-def test_get_api_token_success_completed(client: AuthClient, token_url: str, code_verifier: str):
+def test_get_api_token_success_completed(client: AuthClient, token_url: str, code_verifier: str) -> None:
expected_status = 'Completed'
expected_json = {
'status': expected_status,
@@ -141,7 +141,7 @@ def test_get_api_token_success_completed(client: AuthClient, token_url: str, cod
@responses.activate
-def test_get_api_token_http_error_valid_response(client: AuthClient, token_url: str, code_verifier: str):
+def test_get_api_token_http_error_valid_response(client: AuthClient, token_url: str, code_verifier: str) -> None:
expected_status = 'Pending'
expected_api_token = None
@@ -159,7 +159,7 @@ def test_get_api_token_http_error_valid_response(client: AuthClient, token_url:
@responses.activate
-def test_get_api_token_http_error_invalid_response(client: AuthClient, token_url: str, code_verifier: str):
+def test_get_api_token_http_error_invalid_response(client: AuthClient, token_url: str, code_verifier: str) -> None:
responses.add(
responses.POST,
token_url,
@@ -172,7 +172,7 @@ def test_get_api_token_http_error_invalid_response(client: AuthClient, token_url
@responses.activate
-def test_get_api_token_not_excepted_exception(client: AuthClient, token_url: str, code_verifier: str):
+def test_get_api_token_not_excepted_exception(client: AuthClient, token_url: str, code_verifier: str) -> None:
responses.add(responses.POST, token_url, body=Timeout())
api_token_polling_response = client.get_api_token(_SESSION_ID, code_verifier)
diff --git a/tests/cyclient/test_client.py b/tests/cyclient/test_client.py
index 623877a4..9c68cacf 100644
--- a/tests/cyclient/test_client.py
+++ b/tests/cyclient/test_client.py
@@ -2,7 +2,7 @@
from cycode.cyclient.cycode_client import CycodeClient
-def test_init_values_from_config():
+def test_init_values_from_config() -> None:
client = CycodeClient()
assert client.api_url == config.cycode_api_url
diff --git a/tests/cyclient/test_client_base.py b/tests/cyclient/test_client_base.py
index 5a7810a8..d0b00563 100644
--- a/tests/cyclient/test_client_base.py
+++ b/tests/cyclient/test_client_base.py
@@ -2,7 +2,7 @@
from cycode.cyclient.cycode_client_base import CycodeClientBase, get_cli_user_agent
-def test_mandatory_headers():
+def test_mandatory_headers() -> None:
expected_headers = {
'User-Agent': get_cli_user_agent(),
}
@@ -12,13 +12,13 @@ def test_mandatory_headers():
assert expected_headers == client.MANDATORY_HEADERS
-def test_get_request_headers():
+def test_get_request_headers() -> None:
client = CycodeClientBase(config.cycode_api_url)
assert client.get_request_headers() == client.MANDATORY_HEADERS
-def test_get_request_headers_with_additional():
+def test_get_request_headers_with_additional() -> None:
client = CycodeClientBase(config.cycode_api_url)
additional_headers = {'Authorize': 'Token test'}
@@ -27,7 +27,7 @@ def test_get_request_headers_with_additional():
assert client.get_request_headers(additional_headers) == expected_headers
-def test_build_full_url():
+def test_build_full_url() -> None:
url = config.cycode_api_url
client = CycodeClientBase(url)
diff --git a/tests/cyclient/test_dev_based_client.py b/tests/cyclient/test_dev_based_client.py
index e5fcfecd..f270761f 100644
--- a/tests/cyclient/test_dev_based_client.py
+++ b/tests/cyclient/test_dev_based_client.py
@@ -2,7 +2,7 @@
from cycode.cyclient.cycode_dev_based_client import CycodeDevBasedClient
-def test_get_request_headers():
+def test_get_request_headers() -> None:
client = CycodeDevBasedClient(config.cycode_api_url)
dev_based_headers = {'X-Tenant-Id': config.dev_tenant_id}
@@ -11,7 +11,7 @@ def test_get_request_headers():
assert client.get_request_headers() == expected_headers
-def test_build_full_url():
+def test_build_full_url() -> None:
url = config.cycode_api_url
client = CycodeDevBasedClient(url)
diff --git a/tests/cyclient/test_scan_client.py b/tests/cyclient/test_scan_client.py
index fecbaed2..db867a9f 100644
--- a/tests/cyclient/test_scan_client.py
+++ b/tests/cyclient/test_scan_client.py
@@ -1,5 +1,5 @@
import os
-from typing import List, Optional
+from typing import List, Optional, Tuple
from uuid import UUID, uuid4
import pytest
@@ -19,7 +19,7 @@
_ZIP_CONTENT_PATH = TEST_FILES_PATH.joinpath('zip_content').absolute()
-def zip_scan_resources(scan_type: str, scan_client: ScanClient):
+def zip_scan_resources(scan_type: str, scan_client: ScanClient) -> Tuple[str, InMemoryZip]:
url = get_zipped_file_scan_url(scan_type, scan_client)
zip_file = get_test_zip_file(scan_type)
@@ -84,7 +84,7 @@ def get_zipped_file_scan_response(url: str, scan_id: Optional[UUID] = None) -> r
return responses.Response(method=responses.POST, url=url, json=json_response, status=200)
-def test_get_service_name(scan_client: ScanClient):
+def test_get_service_name(scan_client: ScanClient) -> None:
# TODO(MarshalX): get_service_name should be removed from ScanClient? Because it exists in ScanConfig
assert scan_client.get_service_name('secret') == 'secret'
assert scan_client.get_service_name('iac') == 'iac'
@@ -94,7 +94,7 @@ def test_get_service_name(scan_client: ScanClient):
@pytest.mark.parametrize('scan_type', config['scans']['supported_scans'])
@responses.activate
-def test_zipped_file_scan(scan_type: str, scan_client: ScanClient, api_token_response):
+def test_zipped_file_scan(scan_type: str, scan_client: ScanClient, api_token_response: responses.Response) -> None:
url, zip_file = zip_scan_resources(scan_type, scan_client)
expected_scan_id = uuid4()
@@ -109,7 +109,9 @@ def test_zipped_file_scan(scan_type: str, scan_client: ScanClient, api_token_res
@pytest.mark.parametrize('scan_type', config['scans']['supported_scans'])
@responses.activate
-def test_zipped_file_scan_unauthorized_error(scan_type: str, scan_client: ScanClient, api_token_response):
+def test_zipped_file_scan_unauthorized_error(
+ scan_type: str, scan_client: ScanClient, api_token_response: responses.Response
+) -> None:
url, zip_file = zip_scan_resources(scan_type, scan_client)
expected_scan_id = uuid4().hex
@@ -124,7 +126,9 @@ def test_zipped_file_scan_unauthorized_error(scan_type: str, scan_client: ScanCl
@pytest.mark.parametrize('scan_type', config['scans']['supported_scans'])
@responses.activate
-def test_zipped_file_scan_bad_request_error(scan_type: str, scan_client: ScanClient, api_token_response):
+def test_zipped_file_scan_bad_request_error(
+ scan_type: str, scan_client: ScanClient, api_token_response: responses.Response
+) -> None:
url, zip_file = zip_scan_resources(scan_type, scan_client)
expected_scan_id = uuid4().hex
@@ -143,7 +147,9 @@ def test_zipped_file_scan_bad_request_error(scan_type: str, scan_client: ScanCli
@pytest.mark.parametrize('scan_type', config['scans']['supported_scans'])
@responses.activate
-def test_zipped_file_scan_timeout_error(scan_type: str, scan_client: ScanClient, api_token_response):
+def test_zipped_file_scan_timeout_error(
+ scan_type: str, scan_client: ScanClient, api_token_response: responses.Response
+) -> None:
scan_url, zip_file = zip_scan_resources(scan_type, scan_client)
expected_scan_id = uuid4().hex
@@ -170,7 +176,9 @@ def test_zipped_file_scan_timeout_error(scan_type: str, scan_client: ScanClient,
@pytest.mark.parametrize('scan_type', config['scans']['supported_scans'])
@responses.activate
-def test_zipped_file_scan_connection_error(scan_type: str, scan_client: ScanClient, api_token_response):
+def test_zipped_file_scan_connection_error(
+ scan_type: str, scan_client: ScanClient, api_token_response: responses.Response
+) -> None:
url, zip_file = zip_scan_resources(scan_type, scan_client)
expected_scan_id = uuid4().hex
diff --git a/tests/cyclient/test_token_based_client.py b/tests/cyclient/test_token_based_client.py
index ebc672fb..b5d824f4 100644
--- a/tests/cyclient/test_token_based_client.py
+++ b/tests/cyclient/test_token_based_client.py
@@ -6,7 +6,7 @@
@responses.activate
-def test_api_token_new(token_based_client: CycodeTokenBasedClient, api_token_response: responses.Response):
+def test_api_token_new(token_based_client: CycodeTokenBasedClient, api_token_response: responses.Response) -> None:
responses.add(api_token_response)
api_token = token_based_client.api_token
@@ -15,7 +15,7 @@ def test_api_token_new(token_based_client: CycodeTokenBasedClient, api_token_res
@responses.activate
-def test_api_token_expired(token_based_client: CycodeTokenBasedClient, api_token_response: responses.Response):
+def test_api_token_expired(token_based_client: CycodeTokenBasedClient, api_token_response: responses.Response) -> None:
responses.add(api_token_response)
# this property performs HTTP req to refresh the token. IDE doesn't know it
@@ -30,7 +30,7 @@ def test_api_token_expired(token_based_client: CycodeTokenBasedClient, api_token
assert api_token_refreshed == _EXPECTED_API_TOKEN
-def test_get_request_headers(token_based_client: CycodeTokenBasedClient, api_token: str):
+def test_get_request_headers(token_based_client: CycodeTokenBasedClient, api_token: str) -> None:
token_based_headers = {'Authorization': f'Bearer {_EXPECTED_API_TOKEN}'}
expected_headers = {**token_based_client.MANDATORY_HEADERS, **token_based_headers}
diff --git a/tests/test_code_scanner.py b/tests/test_code_scanner.py
index 9e17a0c5..b1f7e163 100644
--- a/tests/test_code_scanner.py
+++ b/tests/test_code_scanner.py
@@ -4,6 +4,6 @@
from tests.conftest import TEST_FILES_PATH
-def test_is_relevant_file_to_scan_sca():
+def test_is_relevant_file_to_scan_sca() -> None:
path = os.path.join(TEST_FILES_PATH, 'package.json')
assert code_scanner._is_relevant_file_to_scan('sca', path) is True
diff --git a/tests/test_models.py b/tests/test_models.py
index bb583b8e..38998250 100644
--- a/tests/test_models.py
+++ b/tests/test_models.py
@@ -2,7 +2,7 @@
from tests import PODS_MOCK
-def test_batch_resources_to_json():
+def test_batch_resources_to_json() -> None:
batch = ResourcesCollection('pod', 'default', PODS_MOCK, 77777)
json_dict = batch.to_json()
assert 'resources' in json_dict
@@ -15,7 +15,7 @@ def test_batch_resources_to_json():
assert json_dict['resources'][0]['name'] == 'pod_name_1'
-def test_internal_metadata_to_json():
+def test_internal_metadata_to_json() -> None:
resource = K8SResource('nginx-template-123-456', 'pod', 'cycode', {})
resource.internal_metadata = InternalMetadata('nginx-template', 'deployment')
batch = ResourcesCollection('pod', 'cycode', [resource], 1)
diff --git a/tests/test_zip_file.py b/tests/test_zip_file.py
index c05089f5..f73514c8 100644
--- a/tests/test_zip_file.py
+++ b/tests/test_zip_file.py
@@ -3,7 +3,7 @@
from cycode.cli import zip_file
-def test_concat_unique_id_to_file_with_leading_slash():
+def test_concat_unique_id_to_file_with_leading_slash() -> None:
filename = os.path.join('path', 'to', 'file') # we should care about slash characters in tests
unique_id = 'unique_id'
@@ -13,7 +13,7 @@ def test_concat_unique_id_to_file_with_leading_slash():
assert zip_file.concat_unique_id(filename, unique_id) == expected_path
-def test_concat_unique_id_to_file_without_leading_slash():
+def test_concat_unique_id_to_file_without_leading_slash() -> None:
filename = os.path.join('path', 'to', 'file') # we should care about slash characters in tests
unique_id = 'unique_id'
diff --git a/tests/user_settings/test_configuration_manager.py b/tests/user_settings/test_configuration_manager.py
index 1da4a346..50251340 100644
--- a/tests/user_settings/test_configuration_manager.py
+++ b/tests/user_settings/test_configuration_manager.py
@@ -1,8 +1,13 @@
+from typing import TYPE_CHECKING, Optional
+
from mock import Mock
from cycode.cli.consts import DEFAULT_CYCODE_API_URL
from cycode.cli.user_settings.configuration_manager import ConfigurationManager
+if TYPE_CHECKING:
+ from pytest_mock import MockerFixture
+
"""
we check for base url in the three places, in the following order:
1. environment vars
@@ -14,7 +19,7 @@
GLOBAL_CONFIG_BASE_URL_VALUE = 'url_from_global_config_file'
-def test_get_base_url_from_environment_variable(mocker):
+def test_get_base_url_from_environment_variable(mocker: 'MockerFixture') -> None:
# Arrange
configuration_manager = _configure_mocks(
mocker, ENV_VARS_BASE_URL_VALUE, LOCAL_CONFIG_FILE_BASE_URL_VALUE, GLOBAL_CONFIG_BASE_URL_VALUE
@@ -27,7 +32,7 @@ def test_get_base_url_from_environment_variable(mocker):
assert result == ENV_VARS_BASE_URL_VALUE
-def test_get_base_url_from_local_config(mocker):
+def test_get_base_url_from_local_config(mocker: 'MockerFixture') -> None:
# Arrange
configuration_manager = _configure_mocks(
mocker, None, LOCAL_CONFIG_FILE_BASE_URL_VALUE, GLOBAL_CONFIG_BASE_URL_VALUE
@@ -40,7 +45,7 @@ def test_get_base_url_from_local_config(mocker):
assert result == LOCAL_CONFIG_FILE_BASE_URL_VALUE
-def test_get_base_url_from_global_config(mocker):
+def test_get_base_url_from_global_config(mocker: 'MockerFixture') -> None:
# Arrange
configuration_manager = _configure_mocks(mocker, None, None, GLOBAL_CONFIG_BASE_URL_VALUE)
@@ -51,7 +56,7 @@ def test_get_base_url_from_global_config(mocker):
assert result == GLOBAL_CONFIG_BASE_URL_VALUE
-def test_get_base_url_not_configured(mocker):
+def test_get_base_url_not_configured(mocker: 'MockerFixture') -> None:
# Arrange
configuration_manager = _configure_mocks(mocker, None, None, None)
@@ -63,8 +68,11 @@ def test_get_base_url_not_configured(mocker):
def _configure_mocks(
- mocker, expected_env_var_base_url, expected_local_config_file_base_url, expected_global_config_file_base_url
-):
+ mocker: 'MockerFixture',
+ expected_env_var_base_url: Optional[str],
+ expected_local_config_file_base_url: Optional[str],
+ expected_global_config_file_base_url: Optional[str],
+) -> ConfigurationManager:
mocker.patch.object(
ConfigurationManager, 'get_api_url_from_environment_variables', return_value=expected_env_var_base_url
)
diff --git a/tests/user_settings/test_user_settings_commands.py b/tests/user_settings/test_user_settings_commands.py
index b63c1e5c..6ef0cf2e 100644
--- a/tests/user_settings/test_user_settings_commands.py
+++ b/tests/user_settings/test_user_settings_commands.py
@@ -1,9 +1,14 @@
+from typing import TYPE_CHECKING
+
from click.testing import CliRunner
from cycode.cli.user_settings.user_settings_commands import set_credentials
+if TYPE_CHECKING:
+ from pytest_mock import MockerFixture
+
-def test_set_credentials_no_exist_credentials_in_file(mocker):
+def test_set_credentials_no_exist_credentials_in_file(mocker: 'MockerFixture') -> None:
# Arrange
client_id_user_input = 'new client id'
client_secret_user_input = 'new client secret'
@@ -26,7 +31,7 @@ def test_set_credentials_no_exist_credentials_in_file(mocker):
mocked_update_credentials.assert_called_once_with(client_id_user_input, client_secret_user_input)
-def test_set_credentials_update_current_credentials_in_file(mocker):
+def test_set_credentials_update_current_credentials_in_file(mocker: 'MockerFixture') -> None:
# Arrange
client_id_user_input = 'new client id'
client_secret_user_input = 'new client secret'
@@ -35,7 +40,7 @@ def test_set_credentials_update_current_credentials_in_file(mocker):
return_value=('client id file', 'client secret file'),
)
- # side effect - multiple return values, each item in the list represent return of a call
+ # side effect - multiple return values, each item in the list represents return of a call
mocker.patch('click.prompt', side_effect=[client_id_user_input, client_secret_user_input])
mocked_update_credentials = mocker.patch(
'cycode.cli.user_settings.credentials_manager.CredentialsManager.update_credentials_file'
@@ -49,7 +54,7 @@ def test_set_credentials_update_current_credentials_in_file(mocker):
mocked_update_credentials.assert_called_once_with(client_id_user_input, client_secret_user_input)
-def test_set_credentials_update_only_client_id(mocker):
+def test_set_credentials_update_only_client_id(mocker: 'MockerFixture') -> None:
# Arrange
client_id_user_input = 'new client id'
current_client_id = 'client secret file'
@@ -72,7 +77,7 @@ def test_set_credentials_update_only_client_id(mocker):
mocked_update_credentials.assert_called_once_with(client_id_user_input, current_client_id)
-def test_set_credentials_update_only_client_secret(mocker):
+def test_set_credentials_update_only_client_secret(mocker: 'MockerFixture') -> None:
# Arrange
client_secret_user_input = 'new client secret'
current_client_id = 'client secret file'
@@ -95,7 +100,7 @@ def test_set_credentials_update_only_client_secret(mocker):
mocked_update_credentials.assert_called_once_with(current_client_id, client_secret_user_input)
-def test_set_credentials_should_not_update_file(mocker):
+def test_set_credentials_should_not_update_file(mocker: 'MockerFixture') -> None:
# Arrange
client_id_user_input = ''
client_secret_user_input = ''
diff --git a/tests/utils/test_path_utils.py b/tests/utils/test_path_utils.py
index d5c9e3ae..eaf67f65 100644
--- a/tests/utils/test_path_utils.py
+++ b/tests/utils/test_path_utils.py
@@ -4,31 +4,31 @@
from tests.conftest import TEST_FILES_PATH
-def test_is_sub_path_both_paths_are_same():
+def test_is_sub_path_both_paths_are_same() -> None:
path = os.path.join(TEST_FILES_PATH, 'hello')
sub_path = os.path.join(TEST_FILES_PATH, 'hello')
assert is_sub_path(path, sub_path) is True
-def test_is_sub_path_path_is_not_subpath():
+def test_is_sub_path_path_is_not_subpath() -> None:
path = os.path.join(TEST_FILES_PATH, 'hello')
sub_path = os.path.join(TEST_FILES_PATH, 'hello.txt')
assert is_sub_path(path, sub_path) is False
-def test_is_sub_path_path_is_subpath():
+def test_is_sub_path_path_is_subpath() -> None:
path = os.path.join(TEST_FILES_PATH, 'hello')
sub_path = os.path.join(TEST_FILES_PATH, 'hello', 'random.txt')
assert is_sub_path(path, sub_path) is True
-def test_is_sub_path_path_not_exists():
+def test_is_sub_path_path_not_exists() -> None:
path = os.path.join(TEST_FILES_PATH, 'goodbye')
sub_path = os.path.join(TEST_FILES_PATH, 'hello', 'random.txt')
assert is_sub_path(path, sub_path) is False
-def test_is_sub_path_subpath_not_exists():
+def test_is_sub_path_subpath_not_exists() -> None:
path = os.path.join(TEST_FILES_PATH, 'hello', 'random.txt')
sub_path = os.path.join(TEST_FILES_PATH, 'goodbye')
assert is_sub_path(path, sub_path) is False
diff --git a/tests/utils/test_string_utils.py b/tests/utils/test_string_utils.py
index 2a78b9f6..60d10efa 100644
--- a/tests/utils/test_string_utils.py
+++ b/tests/utils/test_string_utils.py
@@ -1,7 +1,7 @@
from cycode.cli.utils.string_utils import shortcut_dependency_paths
-def test_shortcut_dependency_paths_list_single_dependencies():
+def test_shortcut_dependency_paths_list_single_dependencies() -> None:
dependency_paths = 'A, A -> B, A -> B -> C'
expected_result = 'A\n\nA -> B\n\nA -> ... -> C'
assert shortcut_dependency_paths(dependency_paths) == expected_result
From 40d686ff73f4683db97a768c5a4364137a48de09 Mon Sep 17 00:00:00 2001
From: Ilya Siamionau
Date: Thu, 6 Jul 2023 16:55:16 +0200
Subject: [PATCH 009/257] CM-25061 - Hide sensitive API responses from debug
logs (#138)
---
cycode/cli/main.py | 6 ++---
cycode/cyclient/auth_client.py | 2 +-
cycode/cyclient/cycode_client_base.py | 11 ++++++--
cycode/cyclient/cycode_token_based_client.py | 1 +
cycode/cyclient/scan_client.py | 26 ++++++++++++-------
.../scan_config/scan_config_creator.py | 4 +--
tests/conftest.py | 2 +-
7 files changed, 33 insertions(+), 19 deletions(-)
diff --git a/cycode/cli/main.py b/cycode/cli/main.py
index 0086534e..823701d5 100644
--- a/cycode/cli/main.py
+++ b/cycode/cli/main.py
@@ -149,7 +149,7 @@ def code_scan(
if output == 'json':
context.obj['no_progress_meter'] = True
- context.obj['client'] = get_cycode_client(client_id, secret)
+ context.obj['client'] = get_cycode_client(client_id, secret, not context.obj['show_secret'])
context.obj['severity_threshold'] = severity_threshold
context.obj['monitor'] = monitor
context.obj['report'] = report
@@ -234,7 +234,7 @@ def main_cli(
CycodeClientBase.enrich_user_agent(user_agent_option.user_agent_suffix)
-def get_cycode_client(client_id: str, client_secret: str) -> 'ScanClient':
+def get_cycode_client(client_id: str, client_secret: str, hide_response_log: bool) -> 'ScanClient':
if not client_id or not client_secret:
client_id, client_secret = _get_configured_credentials()
if not client_id:
@@ -242,7 +242,7 @@ def get_cycode_client(client_id: str, client_secret: str) -> 'ScanClient':
if not client_secret:
raise click.ClickException('Cycode client secret is needed.')
- return create_scan_client(client_id, client_secret)
+ return create_scan_client(client_id, client_secret, hide_response_log)
def _get_configured_credentials() -> Tuple[str, str]:
diff --git a/cycode/cyclient/auth_client.py b/cycode/cyclient/auth_client.py
index 9cd35f34..626d4ff9 100644
--- a/cycode/cyclient/auth_client.py
+++ b/cycode/cyclient/auth_client.py
@@ -24,7 +24,7 @@ def get_api_token(self, session_id: str, code_verifier: str) -> Optional[models.
path = f'{self.AUTH_CONTROLLER_PATH}/token'
body = {'session_id': session_id, 'code_verifier': code_verifier}
try:
- response = self.cycode_client.post(url_path=path, body=body)
+ response = self.cycode_client.post(url_path=path, body=body, hide_response_content_log=True)
return self.parse_api_token_polling_response(response)
except (NetworkError, HttpUnauthorizedError) as e:
return self.parse_api_token_polling_response(e.response)
diff --git a/cycode/cyclient/cycode_client_base.py b/cycode/cyclient/cycode_client_base.py
index 031d184b..d804b8cb 100644
--- a/cycode/cyclient/cycode_client_base.py
+++ b/cycode/cyclient/cycode_client_base.py
@@ -53,7 +53,13 @@ def get(self, url_path: str, headers: Optional[dict] = None, **kwargs) -> Respon
return self._execute(method='get', endpoint=url_path, headers=headers, **kwargs)
def _execute(
- self, method: str, endpoint: str, headers: Optional[dict] = None, without_auth: bool = False, **kwargs
+ self,
+ method: str,
+ endpoint: str,
+ headers: Optional[dict] = None,
+ without_auth: bool = False,
+ hide_response_content_log: bool = False,
+ **kwargs,
) -> Response:
url = self.build_full_url(self.api_url, endpoint)
logger.debug(f'Executing {method.upper()} request to {url}')
@@ -62,7 +68,8 @@ def _execute(
headers = self.get_request_headers(headers, without_auth=without_auth)
response = request(method=method, url=url, timeout=self.timeout, headers=headers, **kwargs)
- logger.debug(f'Response {response.status_code} from {url}. Content: {response.text}')
+ content = 'HIDDEN' if hide_response_content_log else response.text
+ logger.debug(f'Response {response.status_code} from {url}. Content: {content}')
response.raise_for_status()
return response
diff --git a/cycode/cyclient/cycode_token_based_client.py b/cycode/cyclient/cycode_token_based_client.py
index 59287c80..c73999fb 100644
--- a/cycode/cyclient/cycode_token_based_client.py
+++ b/cycode/cyclient/cycode_token_based_client.py
@@ -35,6 +35,7 @@ def refresh_api_token(self) -> None:
url_path='api/v1/auth/api-token',
body={'clientId': self.client_id, 'secret': self.client_secret},
without_auth=True,
+ hide_response_content_log=True,
)
auth_response_data = auth_response.json()
diff --git a/cycode/cyclient/scan_client.py b/cycode/cyclient/scan_client.py
index 3eb3b310..f09a96ef 100644
--- a/cycode/cyclient/scan_client.py
+++ b/cycode/cyclient/scan_client.py
@@ -11,22 +11,23 @@
class ScanClient:
- def __init__(self, scan_cycode_client: CycodeClientBase, scan_config: ScanConfigBase) -> None:
+ def __init__(
+ self, scan_cycode_client: CycodeClientBase, scan_config: ScanConfigBase, hide_response_log: bool = True
+ ) -> None:
self.scan_cycode_client = scan_cycode_client
self.scan_config = scan_config
+
self.SCAN_CONTROLLER_PATH = 'api/v1/scan'
self.DETECTIONS_SERVICE_CONTROLLER_PATH = 'api/v1/detections'
+ self._hide_response_log = hide_response_log
+
def content_scan(self, scan_type: str, file_name: str, content: str, is_git_diff: bool = True) -> models.ScanResult:
path = f'{self.scan_config.get_service_name(scan_type)}/{self.SCAN_CONTROLLER_PATH}/content'
body = {'name': file_name, 'content': content, 'is_git_diff': is_git_diff}
- response = self.scan_cycode_client.post(url_path=path, body=body)
- return self.parse_scan_response(response)
-
- def file_scan(self, scan_type: str, path: str) -> models.ScanResult:
- url_path = f'{self.scan_config.get_service_name(scan_type)}/{self.SCAN_CONTROLLER_PATH}'
- files = {'file': open(path, 'rb')} # noqa: SIM115 requests lib should care about closing
- response = self.scan_cycode_client.post(url_path=url_path, files=files)
+ response = self.scan_cycode_client.post(
+ url_path=path, body=body, hide_response_content_log=self._hide_response_log
+ )
return self.parse_scan_response(response)
def zipped_file_scan(
@@ -39,6 +40,7 @@ def zipped_file_scan(
url_path=url_path,
data={'scan_id': scan_id, 'is_git_diff': is_git_diff, 'scan_parameters': json.dumps(scan_parameters)},
files=files,
+ hide_response_content_log=self._hide_response_log,
)
return self.parse_zipped_file_scan_response(response)
@@ -96,7 +98,9 @@ def get_scan_detections(self, scan_id: str) -> List[dict]:
params['page_size'] = page_size
params['page_number'] = page_number
- response = self.scan_cycode_client.get(url_path=url_path, params=params).json()
+ response = self.scan_cycode_client.get(
+ url_path=url_path, params=params, hide_response_content_log=self._hide_response_log
+ ).json()
detections.extend(response)
page_number += 1
@@ -116,7 +120,9 @@ def commit_range_zipped_file_scan(
f'{self.scan_config.get_service_name(scan_type)}/{self.SCAN_CONTROLLER_PATH}/commit-range-zipped-file'
)
files = {'file': ('multiple_files_scan.zip', zip_file.read())}
- response = self.scan_cycode_client.post(url_path=url_path, data={'scan_id': scan_id}, files=files)
+ response = self.scan_cycode_client.post(
+ url_path=url_path, data={'scan_id': scan_id}, files=files, hide_response_content_log=self._hide_response_log
+ )
return self.parse_zipped_file_scan_response(response)
def report_scan_status(self, scan_type: str, scan_id: str, scan_status: dict) -> None:
diff --git a/cycode/cyclient/scan_config/scan_config_creator.py b/cycode/cyclient/scan_config/scan_config_creator.py
index c138565f..f17be424 100644
--- a/cycode/cyclient/scan_config/scan_config_creator.py
+++ b/cycode/cyclient/scan_config/scan_config_creator.py
@@ -8,13 +8,13 @@
from cycode.cyclient.scan_config.scan_config_base import DefaultScanConfig, DevScanConfig
-def create_scan_client(client_id: str, client_secret: str) -> ScanClient:
+def create_scan_client(client_id: str, client_secret: str, hide_response_log: bool) -> ScanClient:
if dev_mode:
scan_cycode_client, scan_config = create_scan_for_dev_env()
else:
scan_cycode_client, scan_config = create_scan(client_id, client_secret)
- return ScanClient(scan_cycode_client=scan_cycode_client, scan_config=scan_config)
+ return ScanClient(scan_cycode_client, scan_config, hide_response_log)
def create_scan(client_id: str, client_secret: str) -> Tuple[CycodeTokenBasedClient, DefaultScanConfig]:
diff --git a/tests/conftest.py b/tests/conftest.py
index ae7d4cd4..e500395a 100644
--- a/tests/conftest.py
+++ b/tests/conftest.py
@@ -19,7 +19,7 @@
@pytest.fixture(scope='session')
def scan_client() -> ScanClient:
- return create_scan_client(_CLIENT_ID, _CLIENT_SECRET)
+ return create_scan_client(_CLIENT_ID, _CLIENT_SECRET, hide_response_log=False)
@pytest.fixture(scope='session')
From 32616a8a1ee8e35216092cd419ccec9837523aea Mon Sep 17 00:00:00 2001
From: Ilya Siamionau
Date: Mon, 10 Jul 2023 14:32:31 +0200
Subject: [PATCH 010/257] CM-25167 - Update package description (#139)
---
pyproject.toml | 2 +-
1 file changed, 1 insertion(+), 1 deletion(-)
diff --git a/pyproject.toml b/pyproject.toml
index 292e53d8..14e1e605 100644
--- a/pyproject.toml
+++ b/pyproject.toml
@@ -1,7 +1,7 @@
[tool.poetry]
name = "cycode"
version = "0.0.0" # DON'T TOUCH. Placeholder. Will be filled automatically on poetry build from Git Tag
-description = "Perform secrets/iac scans for your sources using Cycode's engine"
+description = "Boost security in your dev lifecycle via SAST, SCA, Secrets & IaC scanning."
keywords=["secret-scan", "cycode", "devops", "token", "secret", "security", "cycode", "code"]
authors = ["Cycode "]
license = "MIT"
From be3a884ecad882ca0e13a010919f99e872423516 Mon Sep 17 00:00:00 2001
From: Ilya Siamionau
Date: Mon, 10 Jul 2023 14:53:51 +0200
Subject: [PATCH 011/257] CM-25168 - Add short alias for the output option
(#140)
---
.gitignore | 1 +
README.md | 12 ++++++------
cycode/cli/main.py | 2 ++
3 files changed, 9 insertions(+), 6 deletions(-)
diff --git a/.gitignore b/.gitignore
index 9b17b29b..7f27180f 100644
--- a/.gitignore
+++ b/.gitignore
@@ -2,6 +2,7 @@
.idea
*.iml
.env
+.ruff_cache/
# Byte-compiled / optimized / DLL files
__pycache__/
diff --git a/README.md b/README.md
index f2fbe808..5ea2bdc6 100644
--- a/README.md
+++ b/README.md
@@ -213,12 +213,12 @@ repos:
The following are the options and commands available with the Cycode CLI application:
-| Option | Description |
-|--------------------------------|-------------------------------------------------------------------|
-| `--output [text\|json\|table]` | Specify the output (`text`/`json`/`table`). The default is `text` |
-| `-v`, `--verbose` | Show detailed logs |
-| `--version` | Show the version and exit. |
-| `--help` | Show options for given command. |
+| Option | Description |
+|--------------------------------------|-------------------------------------------------------------------|
+| `-o`, `--output [text\|json\|table]` | Specify the output (`text`/`json`/`table`). The default is `text` |
+| `-v`, `--verbose` | Show detailed logs |
+| `--version` | Show the version and exit. |
+| `--help` | Show options for given command. |
| Command | Description |
|-------------------------------------|-------------|
diff --git a/cycode/cli/main.py b/cycode/cli/main.py
index 823701d5..a8020e54 100644
--- a/cycode/cli/main.py
+++ b/cycode/cli/main.py
@@ -76,6 +76,7 @@
)
@click.option(
'--output',
+ '-o',
default=None,
help="""
\b
@@ -198,6 +199,7 @@ def finalize(context: click.Context, *_, **__) -> None:
)
@click.option(
'--output',
+ '-o',
default='text',
help='Specify the output (text/json/table), the default is text',
type=click.Choice(['text', 'json', 'table']),
From 9d91ff44713efb78e174f0288d55d121888d49ea Mon Sep 17 00:00:00 2001
From: Ilya Siamionau
Date: Wed, 12 Jul 2023 17:58:06 +0200
Subject: [PATCH 012/257] CM-25249 - Optimize the local files collection and
improve the progress bar stage (#141)
---
cycode/cli/code_scanner.py | 60 +++++++-----
cycode/cli/consts.py | 12 +--
.../user_settings/configuration_manager.py | 2 +
cycode/cli/utils/path_utils.py | 31 +++---
cycode/cli/utils/progress_bar.py | 3 -
tests/conftest.py | 5 +
tests/test_files/.test_env | 1 +
tests/test_performance_get_all_files.py | 94 +++++++++++++++++++
8 files changed, 166 insertions(+), 42 deletions(-)
create mode 100644 tests/test_files/.test_env
create mode 100644 tests/test_performance_get_all_files.py
diff --git a/cycode/cli/code_scanner.py b/cycode/cli/code_scanner.py
index 65230537..15313d45 100644
--- a/cycode/cli/code_scanner.py
+++ b/cycode/cli/code_scanner.py
@@ -190,10 +190,32 @@ def scan_ci(context: click.Context) -> None:
@click.pass_context
def scan_path(context: click.Context, path: str) -> None:
logger.debug('Starting path scan process, %s', {'path': path})
- files_to_scan = get_relevant_files_in_path(path=path, exclude_patterns=['**/.git/**', '**/.cycode/**'])
- files_to_scan = exclude_irrelevant_files(context, files_to_scan)
- logger.debug('Found all relevant files for scanning %s', {'path': path, 'file_to_scan_count': len(files_to_scan)})
- scan_disk_files(context, path, files_to_scan)
+
+ progress_bar = context.obj['progress_bar']
+
+ all_files_to_scan = get_relevant_files_in_path(path=path, exclude_patterns=['**/.git/**', '**/.cycode/**'])
+
+ # we are double the progress bar section length because we are going to process the files twice
+ # first time to get the file list with respect of excluded patterns (excluding takes seconds to execute)
+ # second time to get the files content
+ progress_bar_section_len = len(all_files_to_scan) * 2
+ progress_bar.set_section_length(ProgressBarSection.PREPARE_LOCAL_FILES, progress_bar_section_len)
+
+ relevant_files_to_scan = exclude_irrelevant_files(context, all_files_to_scan)
+
+ # after finishing the first processing (excluding),
+ # we must update the progress bar stage with respect of excluded files.
+ # now it's possible that we will not process x2 of the files count
+ # because some of them were excluded, we should subtract the excluded files count
+ # from the progress bar section length
+ excluded_files_count = len(all_files_to_scan) - len(relevant_files_to_scan)
+ progress_bar_section_len = progress_bar_section_len - excluded_files_count
+ progress_bar.set_section_length(ProgressBarSection.PREPARE_LOCAL_FILES, progress_bar_section_len)
+
+ logger.debug(
+ 'Found all relevant files for scanning %s', {'path': path, 'file_to_scan_count': len(relevant_files_to_scan)}
+ )
+ scan_disk_files(context, path, relevant_files_to_scan)
@click.command(short_help='Use this command to scan the content that was not committed yet')
@@ -300,17 +322,15 @@ def scan_disk_files(context: click.Context, path: str, files_to_scan: List[str])
is_git_diff = False
- progress_bar.set_section_length(ProgressBarSection.PREPARE_LOCAL_FILES, len(files_to_scan))
-
documents: List[Document] = []
for file in files_to_scan:
progress_bar.update(ProgressBarSection.PREPARE_LOCAL_FILES)
- with open(file, 'r', encoding='UTF-8') as f:
- try:
- documents.append(Document(file, f.read(), is_git_diff))
- except UnicodeDecodeError:
- continue
+ content = get_file_content(file)
+ if not content:
+ continue
+
+ documents.append(Document(file, content, is_git_diff))
perform_pre_scan_documents_actions(context, scan_type, documents, is_git_diff)
scan_documents(context, documents, is_git_diff=is_git_diff, scan_parameters=scan_parameters)
@@ -826,12 +846,16 @@ def exclude_irrelevant_documents_to_scan(context: click.Context, documents_to_sc
def exclude_irrelevant_files(context: click.Context, filenames: List[str]) -> List[str]:
scan_type = context.obj['scan_type']
+ progress_bar = context.obj['progress_bar']
relevant_files = []
for filename in filenames:
+ progress_bar.update(ProgressBarSection.PREPARE_LOCAL_FILES)
if _is_relevant_file_to_scan(scan_type, filename):
relevant_files.append(filename)
+ is_sub_path.cache_clear() # free up memory
+
return relevant_files
@@ -1066,20 +1090,12 @@ def _is_file_extension_supported(scan_type: str, filename: str) -> bool:
filename = filename.lower()
if scan_type == consts.INFRA_CONFIGURATION_SCAN_TYPE:
- return any(
- filename.endswith(supported_file_extension)
- for supported_file_extension in consts.INFRA_CONFIGURATION_SCAN_SUPPORTED_FILES
- )
+ return filename.endswith(consts.INFRA_CONFIGURATION_SCAN_SUPPORTED_FILES)
if scan_type == consts.SCA_SCAN_TYPE:
- return any(
- filename.endswith(supported_file) for supported_file in consts.SCA_CONFIGURATION_SCAN_SUPPORTED_FILES
- )
+ return filename.endswith(consts.SCA_CONFIGURATION_SCAN_SUPPORTED_FILES)
- return all(
- not filename.endswith(file_extension_to_ignore)
- for file_extension_to_ignore in consts.SECRET_SCAN_FILE_EXTENSIONS_TO_IGNORE
- )
+ return not filename.endswith(consts.SECRET_SCAN_FILE_EXTENSIONS_TO_IGNORE)
def _does_file_exceed_max_size_limit(filename: str) -> bool:
diff --git a/cycode/cli/consts.py b/cycode/cli/consts.py
index eb3f2c00..71dcedf0 100644
--- a/cycode/cli/consts.py
+++ b/cycode/cli/consts.py
@@ -7,9 +7,9 @@
SCA_SCAN_TYPE = 'sca'
SAST_SCAN_TYPE = 'sast'
-INFRA_CONFIGURATION_SCAN_SUPPORTED_FILES = ['.tf', '.tf.json', '.json', '.yaml', '.yml', 'dockerfile']
+INFRA_CONFIGURATION_SCAN_SUPPORTED_FILES = ('.tf', '.tf.json', '.json', '.yaml', '.yml', 'dockerfile')
-SECRET_SCAN_FILE_EXTENSIONS_TO_IGNORE = [
+SECRET_SCAN_FILE_EXTENSIONS_TO_IGNORE = (
'.7z',
'.bmp',
'.bz2',
@@ -39,9 +39,9 @@
'.deb',
'.obj',
'.model',
-]
+)
-SCA_CONFIGURATION_SCAN_SUPPORTED_FILES = [
+SCA_CONFIGURATION_SCAN_SUPPORTED_FILES = (
'cargo.lock',
'cargo.toml',
'composer.json',
@@ -73,9 +73,9 @@
'pipfile.lock',
'requirements.txt',
'setup.py',
-]
+)
-SCA_EXCLUDED_PATHS = ['node_modules']
+SCA_EXCLUDED_PATHS = ('node_modules',)
PROJECT_FILES_BY_ECOSYSTEM_MAP = {
'crates': ['Cargo.lock', 'Cargo.toml'],
diff --git a/cycode/cli/user_settings/configuration_manager.py b/cycode/cli/user_settings/configuration_manager.py
index 947781da..98e62e07 100644
--- a/cycode/cli/user_settings/configuration_manager.py
+++ b/cycode/cli/user_settings/configuration_manager.py
@@ -1,4 +1,5 @@
import os
+from functools import lru_cache
from pathlib import Path
from typing import Any, Dict, Optional
from uuid import uuid4
@@ -61,6 +62,7 @@ def get_verbose_flag_from_environment_variables(self) -> bool:
value = self._get_value_from_environment_variables(consts.VERBOSE_ENV_VAR_NAME, '')
return value.lower() in ('true', '1')
+ @lru_cache(maxsize=None) # noqa: B019
def get_exclusions_by_scan_type(self, scan_type: str) -> Dict:
local_exclusions = self.local_config_file_manager.get_exclusions_by_scan_type(scan_type)
global_exclusions = self.global_config_file_manager.get_exclusions_by_scan_type(scan_type)
diff --git a/cycode/cli/utils/path_utils.py b/cycode/cli/utils/path_utils.py
index e25daede..ef758fed 100644
--- a/cycode/cli/utils/path_utils.py
+++ b/cycode/cli/utils/path_utils.py
@@ -1,6 +1,6 @@
import os
-from pathlib import Path
-from typing import AnyStr, Generator, Iterable, List, Optional
+from functools import lru_cache
+from typing import AnyStr, Iterable, List, Optional
import pathspec
from binaryornot.check import is_binary
@@ -8,20 +8,24 @@
def get_relevant_files_in_path(path: str, exclude_patterns: Iterable[str]) -> List[str]:
absolute_path = get_absolute_path(path)
+
if not os.path.isfile(absolute_path) and not os.path.isdir(absolute_path):
- raise FileNotFoundError(f'the specified path was not found, path: {path}')
+ raise FileNotFoundError(f'the specified path was not found, path: {absolute_path}')
if os.path.isfile(absolute_path):
return [absolute_path]
- directory_files_paths = _get_all_existing_files_in_directory(absolute_path)
- file_paths = set({str(file_path) for file_path in directory_files_paths})
- spec = pathspec.PathSpec.from_lines(pathspec.patterns.GitWildMatchPattern, exclude_patterns)
- exclude_file_paths = set(spec.match_files(file_paths))
+ all_file_paths = set(_get_all_existing_files_in_directory(absolute_path))
+
+ path_spec = pathspec.PathSpec.from_lines(pathspec.patterns.GitWildMatchPattern, exclude_patterns)
+ excluded_file_paths = set(path_spec.match_files(all_file_paths))
+
+ relevant_file_paths = all_file_paths - excluded_file_paths
- return [file_path for file_path in (file_paths - exclude_file_paths) if os.path.isfile(file_path)]
+ return [file_path for file_path in relevant_file_paths if os.path.isfile(file_path)]
+@lru_cache(maxsize=None)
def is_sub_path(path: str, sub_path: str) -> bool:
try:
common_path = os.path.commonpath([get_absolute_path(path), get_absolute_path(sub_path)])
@@ -49,9 +53,14 @@ def get_path_by_os(filename: str) -> str:
return filename.replace('/', os.sep)
-def _get_all_existing_files_in_directory(path: str) -> Generator[Path, None, None]:
- directory = Path(path)
- return directory.rglob(r'*')
+def _get_all_existing_files_in_directory(path: str) -> List[str]:
+ files: List[str] = []
+
+ for root, _, filenames in os.walk(path):
+ for filename in filenames:
+ files.append(os.path.join(root, filename))
+
+ return files
def is_path_exists(path: str) -> bool:
diff --git a/cycode/cli/utils/progress_bar.py b/cycode/cli/utils/progress_bar.py
index e340fb92..d22abf84 100644
--- a/cycode/cli/utils/progress_bar.py
+++ b/cycode/cli/utils/progress_bar.py
@@ -40,9 +40,6 @@ class ProgressBarSectionInfo(NamedTuple):
ProgressBarSection.PREPARE_LOCAL_FILES: ProgressBarSectionInfo(
ProgressBarSection.PREPARE_LOCAL_FILES, 'Prepare local files', start_percent=0, stop_percent=5
),
- # TODO(MarshalX): could be added in the future
- # ProgressBarSection.UPLOAD_FILES: ProgressBarSectionInfo(
- # ),
ProgressBarSection.SCAN: ProgressBarSectionInfo(
ProgressBarSection.SCAN, 'Scan in progress', start_percent=5, stop_percent=95
),
diff --git a/tests/conftest.py b/tests/conftest.py
index e500395a..a763f6bb 100644
--- a/tests/conftest.py
+++ b/tests/conftest.py
@@ -17,6 +17,11 @@
TEST_FILES_PATH = Path(__file__).parent.joinpath('test_files').absolute()
+@pytest.fixture(scope='session')
+def test_files_path() -> Path:
+ return TEST_FILES_PATH
+
+
@pytest.fixture(scope='session')
def scan_client() -> ScanClient:
return create_scan_client(_CLIENT_ID, _CLIENT_SECRET, hide_response_log=False)
diff --git a/tests/test_files/.test_env b/tests/test_files/.test_env
new file mode 100644
index 00000000..3e58295a
--- /dev/null
+++ b/tests/test_files/.test_env
@@ -0,0 +1 @@
+TELEGRAM_BOT_TOKEN=923445010:AAGWKwWTNx_6RAuRdcp2kWax5_JltwkF2Lw
diff --git a/tests/test_performance_get_all_files.py b/tests/test_performance_get_all_files.py
new file mode 100644
index 00000000..b10b86e7
--- /dev/null
+++ b/tests/test_performance_get_all_files.py
@@ -0,0 +1,94 @@
+import glob
+import logging
+import os
+import timeit
+from pathlib import Path
+from typing import Dict, List, Tuple, Union
+
+logger = logging.getLogger(__name__)
+logging.basicConfig(level=logging.INFO)
+
+
+def filter_files(paths: List[Union[Path, str]]) -> List[str]:
+ return [str(path) for path in paths if os.path.isfile(path)]
+
+
+def get_all_files_glob(path: Union[Path, str]) -> List[str]:
+ # DOESN'T RETURN HIDDEN FILES. CAN'T BE USED
+ # and doesn't show the best performance
+ if not str(path).endswith(os.sep):
+ path = f'{path}{os.sep}'
+
+ return filter_files(glob.glob(f'{path}**', recursive=True))
+
+
+def get_all_files_walk(path: str) -> List[str]:
+ files = []
+
+ for root, _, filenames in os.walk(path):
+ for filename in filenames:
+ files.append(os.path.join(root, filename))
+
+ return files
+
+
+def get_all_files_listdir(path: str) -> List[str]:
+ files = []
+
+ def _(sub_path: str) -> None:
+ items = os.listdir(sub_path)
+
+ for item in items:
+ item_path = os.path.join(sub_path, item)
+
+ if os.path.isfile(item_path):
+ files.append(item_path)
+ elif os.path.isdir(item_path):
+ _(item_path)
+
+ _(path)
+ return files
+
+
+def get_all_files_rglob(path: str) -> List[str]:
+ return filter_files(list(Path(path).rglob(r'*')))
+
+
+def test_get_all_files_performance(test_files_path: str) -> None:
+ results: Dict[str, Tuple[int, float]] = {}
+ for func in {
+ get_all_files_rglob,
+ get_all_files_listdir,
+ get_all_files_walk,
+ }:
+ name = func.__name__
+ start_time = timeit.default_timer()
+
+ files_count = len(func(test_files_path))
+
+ executed_time = timeit.default_timer() - start_time
+ results[name] = (files_count, executed_time)
+
+ logger.info(f'Time result {name}: {executed_time}')
+ logger.info(f'Files count {name}: {files_count}')
+
+ files_counts = [result[0] for result in results.values()]
+ assert len(set(files_counts)) == 1 # all should be equal
+
+ logger.info(f'Benchmark TOP with ({files_counts[0]}) files:')
+ for func_name, result in sorted(results.items(), key=lambda x: x[1][1]):
+ logger.info(f'- {func_name}: {result[1]}')
+
+ # according to my (MarshalX) local tests, the fastest is get_all_files_walk
+
+
+if __name__ == '__main__':
+ # provide a path with thousands of files
+ huge_dir_path = '/Users/ilyasiamionau/projects/cycode/'
+ test_get_all_files_performance(huge_dir_path)
+
+ # Output:
+ # INFO:__main__:Benchmark TOP with (94882) files:
+ # INFO:__main__:- get_all_files_walk: 0.717258458
+ # INFO:__main__:- get_all_files_listdir: 1.4648628330000002
+ # INFO:__main__:- get_all_files_rglob: 2.368291458
From db748c49a54eb839031a17990cd68f749f27f8ea Mon Sep 17 00:00:00 2001
From: Ilya Siamionau
Date: Tue, 18 Jul 2023 17:22:15 +0200
Subject: [PATCH 013/257] CM-25361 - Add version command that supports TEXT and
JSON output formats (#142)
---
cycode/cli/consts.py | 2 ++
cycode/cli/main.py | 29 ++++++++++++++++++++++++++---
2 files changed, 28 insertions(+), 3 deletions(-)
diff --git a/cycode/cli/consts.py b/cycode/cli/consts.py
index 71dcedf0..6d710b1b 100644
--- a/cycode/cli/consts.py
+++ b/cycode/cli/consts.py
@@ -1,3 +1,5 @@
+PROGRAM_NAME = 'cycode'
+
PRE_COMMIT_COMMAND_SCAN_TYPE = 'pre_commit'
PRE_RECEIVE_COMMAND_SCAN_TYPE = 'pre_receive'
COMMIT_HISTORY_COMMAND_SCAN_TYPE = 'commit_history'
diff --git a/cycode/cli/main.py b/cycode/cli/main.py
index a8020e54..3fd99f7f 100644
--- a/cycode/cli/main.py
+++ b/cycode/cli/main.py
@@ -1,3 +1,4 @@
+import json
import logging
import sys
from typing import TYPE_CHECKING, List, Optional, Tuple
@@ -8,7 +9,7 @@
from cycode.cli import code_scanner
from cycode.cli.auth.auth_command import authenticate
from cycode.cli.config import config
-from cycode.cli.consts import ISSUE_DETECTED_STATUS_CODE, NO_ISSUES_STATUS_CODE
+from cycode.cli.consts import ISSUE_DETECTED_STATUS_CODE, NO_ISSUES_STATUS_CODE, PROGRAM_NAME
from cycode.cli.models import Severity
from cycode.cli.user_settings.configuration_manager import ConfigurationManager
from cycode.cli.user_settings.credentials_manager import CredentialsManager
@@ -180,8 +181,30 @@ def finalize(context: click.Context, *_, **__) -> None:
sys.exit(exit_code)
+@click.command(short_help='Show the version and exit')
+@click.pass_context
+def version(context: click.Context) -> None:
+ output = context.obj['output']
+
+ prog = PROGRAM_NAME
+ ver = __version__
+
+ message = f'{prog}, version {ver}'
+ if output == 'json':
+ message = json.dumps({'name': prog, 'version': ver})
+
+ click.echo(message, color=context.color)
+ context.exit()
+
+
@click.group(
- commands={'scan': code_scan, 'configure': set_credentials, 'ignore': add_exclusions, 'auth': authenticate},
+ commands={
+ 'scan': code_scan,
+ 'configure': set_credentials,
+ 'ignore': add_exclusions,
+ 'auth': authenticate,
+ 'version': version,
+ },
context_settings=CONTEXT,
)
@click.option(
@@ -210,7 +233,7 @@ def finalize(context: click.Context, *_, **__) -> None:
help='Characteristic JSON object that lets servers identify the application',
type=str,
)
-@click.version_option(__version__, prog_name='cycode')
+@click.version_option(__version__, prog_name=PROGRAM_NAME)
@click.pass_context
def main_cli(
context: click.Context, verbose: bool, no_progress_meter: bool, output: str, user_agent: Optional[str]
From 4b7bc8c3d25b0d9498712b31d2c62ae6158f687b Mon Sep 17 00:00:00 2001
From: Ilya Siamionau
Date: Tue, 18 Jul 2023 17:59:16 +0200
Subject: [PATCH 014/257] CM-25340 - Fix list modification while in a for loop
(#143)
---
cycode/cli/helpers/sca_code_scanner.py | 16 +++++++++-------
1 file changed, 9 insertions(+), 7 deletions(-)
diff --git a/cycode/cli/helpers/sca_code_scanner.py b/cycode/cli/helpers/sca_code_scanner.py
index ccff11b0..227b553e 100644
--- a/cycode/cli/helpers/sca_code_scanner.py
+++ b/cycode/cli/helpers/sca_code_scanner.py
@@ -43,13 +43,16 @@ def perform_pre_hook_range_scan_actions(
def add_ecosystem_related_files_if_exists(
documents: List[Document], repo: Optional[Repo] = None, commit_rev: Optional[str] = None
) -> None:
+ documents_to_add: List[Document] = []
for doc in documents:
ecosystem = get_project_file_ecosystem(doc)
if ecosystem is None:
logger.debug('failed to resolve project file ecosystem: %s', doc.path)
continue
- documents_to_add = get_doc_ecosystem_related_project_files(doc, documents, ecosystem, commit_rev, repo)
- documents.extend(documents_to_add)
+
+ documents_to_add.extend(get_doc_ecosystem_related_project_files(doc, documents, ecosystem, commit_rev, repo))
+
+ documents.extend(documents_to_add)
def get_doc_ecosystem_related_project_files(
@@ -59,11 +62,10 @@ def get_doc_ecosystem_related_project_files(
for ecosystem_project_file in consts.PROJECT_FILES_BY_ECOSYSTEM_MAP.get(ecosystem):
file_to_search = join_paths(get_file_dir(doc.path), ecosystem_project_file)
if not is_project_file_exists_in_documents(documents, file_to_search):
- file_content = (
- get_file_content_from_commit(repo, commit_rev, file_to_search)
- if repo
- else get_file_content(file_to_search)
- )
+ if repo:
+ file_content = get_file_content_from_commit(repo, commit_rev, file_to_search)
+ else:
+ file_content = get_file_content(file_to_search)
if file_content is not None:
documents_to_add.append(Document(file_to_search, file_content))
From 4937adcb556799044d4dbfab448a468aaf6322dd Mon Sep 17 00:00:00 2001
From: Ilya Siamionau
Date: Tue, 18 Jul 2023 18:19:57 +0200
Subject: [PATCH 015/257] CM-25271 - Improve version managing of pre-commit
hook (#144)
Fix shallow repository
---
cycode/__init__.py | 14 --------------
cycode/pre-commit-hook-version | 1 -
pyproject.toml | 5 +++--
3 files changed, 3 insertions(+), 17 deletions(-)
delete mode 100644 cycode/pre-commit-hook-version
diff --git a/cycode/__init__.py b/cycode/__init__.py
index 2b478887..4ce71ef1 100644
--- a/cycode/__init__.py
+++ b/cycode/__init__.py
@@ -1,15 +1 @@
__version__ = '0.0.0' # DON'T TOUCH. Placeholder. Will be filled automatically on poetry build from Git Tag
-
-if __version__ == '0.0.1.dev1':
- # If CLI was installed from shallow clone, __version__ will be 0.0.1.dev1 due to non-strict versioning.
- # This happens when installing CLI as pre-commit hook.
- # We are not able to provide the version based on Git Tag in this case.
- # This fallback version is maintained manually.
-
- # One benefit of it is that we could pass the version with a special suffix to mark pre-commit hook usage.
-
- import os
-
- version_filepath = os.path.join(os.path.dirname(__file__), 'pre-commit-hook-version')
- with open(version_filepath, 'r', encoding='UTF-8') as f:
- __version__ = f.read().strip()
diff --git a/cycode/pre-commit-hook-version b/cycode/pre-commit-hook-version
deleted file mode 100644
index d1e8df28..00000000
--- a/cycode/pre-commit-hook-version
+++ /dev/null
@@ -1 +0,0 @@
-0.2.5-pre-commit
\ No newline at end of file
diff --git a/pyproject.toml b/pyproject.toml
index 14e1e605..4c093047 100644
--- a/pyproject.toml
+++ b/pyproject.toml
@@ -59,9 +59,10 @@ log_cli = true
[tool.poetry-dynamic-versioning]
# poetry self add "poetry-dynamic-versioning[plugin]"
enable = true
-strict = false
+strict = true
bump = true
metadata = false
+fix-shallow-repository=true
vcs = "git"
style = "pep440"
@@ -134,5 +135,5 @@ inline-quotes = "single"
"cycode/*.py" = ["BLE001"]
[build-system]
-requires = ["poetry-core>=1.0.0", "poetry-dynamic-versioning"]
+requires = ["poetry-core>=1.0.0", "poetry-dynamic-versioning>=0.25.0"]
build-backend = "poetry_dynamic_versioning.backend"
From 7d52a5a33521a30d60fd8b91023f909c5892c45b Mon Sep 17 00:00:00 2001
From: Ilya Siamionau
Date: Tue, 18 Jul 2023 19:02:46 +0200
Subject: [PATCH 016/257] CM-25171 - Add Poetry installation cache (#145)
---
.github/workflows/black.yml | 11 +++++++++++
.github/workflows/build_executable.yml | 11 +++++++++++
.github/workflows/pre_release.yml | 11 +++++++++++
.github/workflows/release.yml | 11 +++++++++++
.github/workflows/ruff.yml | 11 +++++++++++
.github/workflows/tests.yml | 11 +++++++++++
.github/workflows/tests_full.yml | 11 +++++++++++
7 files changed, 77 insertions(+)
diff --git a/.github/workflows/black.yml b/.github/workflows/black.yml
index 05208c66..917994f5 100644
--- a/.github/workflows/black.yml
+++ b/.github/workflows/black.yml
@@ -26,9 +26,20 @@ jobs:
with:
python-version: 3.7
+ - name: Load cached Poetry setup
+ id: cached-poetry
+ uses: actions/cache@v3
+ with:
+ path: ~/.local
+ key: poetry-ubuntu-0 # increment to reset cache
+
- name: Setup Poetry
+ if: steps.cached-poetry.outputs.cache-hit != 'true'
uses: snok/install-poetry@v1
+ - name: Add Poetry to PATH
+ run: echo "$HOME/.local/bin" >> $GITHUB_PATH
+
- name: Install dependencies
run: poetry install
diff --git a/.github/workflows/build_executable.yml b/.github/workflows/build_executable.yml
index ed522efd..4f0417a8 100644
--- a/.github/workflows/build_executable.yml
+++ b/.github/workflows/build_executable.yml
@@ -41,9 +41,20 @@ jobs:
with:
python-version: '3.7'
+ - name: Load cached Poetry setup
+ id: cached-poetry
+ uses: actions/cache@v3
+ with:
+ path: ~/.local
+ key: poetry-${{ matrix.os }}-0 # increment to reset cache
+
- name: Setup Poetry
+ if: steps.cached-poetry.outputs.cache-hit != 'true'
uses: snok/install-poetry@v1
+ - name: Add Poetry to PATH
+ run: echo "$HOME/.local/bin" >> $GITHUB_PATH
+
- name: Install dependencies
run: poetry install
diff --git a/.github/workflows/pre_release.yml b/.github/workflows/pre_release.yml
index 13ae474b..a2734ca4 100644
--- a/.github/workflows/pre_release.yml
+++ b/.github/workflows/pre_release.yml
@@ -36,9 +36,20 @@ jobs:
with:
python-version: '3.7'
+ - name: Load cached Poetry setup
+ id: cached-poetry
+ uses: actions/cache@v3
+ with:
+ path: ~/.local
+ key: poetry-ubuntu-0 # increment to reset cache
+
- name: Setup Poetry
+ if: steps.cached-poetry.outputs.cache-hit != 'true'
uses: snok/install-poetry@v1
+ - name: Add Poetry to PATH
+ run: echo "$HOME/.local/bin" >> $GITHUB_PATH
+
- name: Install Poetry Plugin
run: poetry self add "poetry-dynamic-versioning[plugin]"
diff --git a/.github/workflows/release.yml b/.github/workflows/release.yml
index 70a60c33..91eeb315 100644
--- a/.github/workflows/release.yml
+++ b/.github/workflows/release.yml
@@ -35,9 +35,20 @@ jobs:
with:
python-version: '3.7'
+ - name: Load cached Poetry setup
+ id: cached-poetry
+ uses: actions/cache@v3
+ with:
+ path: ~/.local
+ key: poetry-ubuntu-0 # increment to reset cache
+
- name: Setup Poetry
+ if: steps.cached-poetry.outputs.cache-hit != 'true'
uses: snok/install-poetry@v1
+ - name: Add Poetry to PATH
+ run: echo "$HOME/.local/bin" >> $GITHUB_PATH
+
- name: Install Poetry Plugin
run: poetry self add "poetry-dynamic-versioning[plugin]"
diff --git a/.github/workflows/ruff.yml b/.github/workflows/ruff.yml
index 0fc3ddb5..6ef7cefd 100644
--- a/.github/workflows/ruff.yml
+++ b/.github/workflows/ruff.yml
@@ -26,9 +26,20 @@ jobs:
with:
python-version: 3.7
+ - name: Load cached Poetry setup
+ id: cached-poetry
+ uses: actions/cache@v3
+ with:
+ path: ~/.local
+ key: poetry-ubuntu-0 # increment to reset cache
+
- name: Setup Poetry
+ if: steps.cached-poetry.outputs.cache-hit != 'true'
uses: snok/install-poetry@v1
+ - name: Add Poetry to PATH
+ run: echo "$HOME/.local/bin" >> $GITHUB_PATH
+
- name: Install dependencies
run: poetry install
diff --git a/.github/workflows/tests.yml b/.github/workflows/tests.yml
index 27450b71..5b6db7c7 100644
--- a/.github/workflows/tests.yml
+++ b/.github/workflows/tests.yml
@@ -29,9 +29,20 @@ jobs:
with:
python-version: '3.7'
+ - name: Load cached Poetry setup
+ id: cached-poetry
+ uses: actions/cache@v3
+ with:
+ path: ~/.local
+ key: poetry-ubuntu-0 # increment to reset cache
+
- name: Setup Poetry
+ if: steps.cached-poetry.outputs.cache-hit != 'true'
uses: snok/install-poetry@v1
+ - name: Add Poetry to PATH
+ run: echo "$HOME/.local/bin" >> $GITHUB_PATH
+
- name: Install dependencies
run: poetry install
diff --git a/.github/workflows/tests_full.yml b/.github/workflows/tests_full.yml
index bdcc49d4..461e1231 100644
--- a/.github/workflows/tests_full.yml
+++ b/.github/workflows/tests_full.yml
@@ -42,9 +42,20 @@ jobs:
with:
python-version: ${{ matrix.python-version }}
+ - name: Load cached Poetry setup
+ id: cached-poetry
+ uses: actions/cache@v3
+ with:
+ path: ~/.local
+ key: poetry-${{ matrix.os }}-0 # increment to reset cache
+
- name: Setup Poetry
+ if: steps.cached-poetry.outputs.cache-hit != 'true'
uses: snok/install-poetry@v1
+ - name: Add Poetry to PATH
+ run: echo "$HOME/.local/bin" >> $GITHUB_PATH
+
- name: Install dependencies
run: poetry install
From b17d9b2bcf8be9d716f07bf9846fab08618980e6 Mon Sep 17 00:00:00 2001
From: Ilya Siamionau
Date: Mon, 24 Jul 2023 14:57:47 +0400
Subject: [PATCH 017/257] CM-24116 - Migrate SCA tables to the new table
management system (#146)
---
cycode/cli/printers/console_printer.py | 14 +-
cycode/cli/printers/json_printer.py | 4 +-
.../{base_printer.py => printer_base.py} | 2 +-
cycode/cli/printers/sca_table_printer.py | 156 ------------------
cycode/cli/printers/tables/__init__.py | 0
.../cli/printers/tables/sca_table_printer.py | 143 ++++++++++++++++
cycode/cli/printers/{ => tables}/table.py | 2 +-
.../cli/printers/{ => tables}/table_models.py | 10 +-
.../printers/{ => tables}/table_printer.py | 40 +++--
.../table_printer_base.py} | 10 +-
cycode/cli/printers/text_printer.py | 4 +-
11 files changed, 190 insertions(+), 195 deletions(-)
rename cycode/cli/printers/{base_printer.py => printer_base.py} (96%)
delete mode 100644 cycode/cli/printers/sca_table_printer.py
create mode 100644 cycode/cli/printers/tables/__init__.py
create mode 100644 cycode/cli/printers/tables/sca_table_printer.py
rename cycode/cli/printers/{ => tables}/table.py (96%)
rename cycode/cli/printers/{ => tables}/table_models.py (62%)
rename cycode/cli/printers/{ => tables}/table_printer.py (79%)
rename cycode/cli/printers/{base_table_printer.py => tables/table_printer_base.py} (82%)
diff --git a/cycode/cli/printers/console_printer.py b/cycode/cli/printers/console_printer.py
index 533ed321..f0bccadf 100644
--- a/cycode/cli/printers/console_printer.py
+++ b/cycode/cli/printers/console_printer.py
@@ -5,23 +5,23 @@
from cycode.cli.exceptions.custom_exceptions import CycodeError
from cycode.cli.models import CliError, CliResult
from cycode.cli.printers.json_printer import JsonPrinter
-from cycode.cli.printers.sca_table_printer import SCATablePrinter
-from cycode.cli.printers.table_printer import TablePrinter
+from cycode.cli.printers.tables.sca_table_printer import ScaTablePrinter
+from cycode.cli.printers.tables.table_printer import TablePrinter
from cycode.cli.printers.text_printer import TextPrinter
if TYPE_CHECKING:
from cycode.cli.models import LocalScanResult
- from cycode.cli.printers.base_printer import BasePrinter
+ from cycode.cli.printers.tables.table_printer_base import PrinterBase
class ConsolePrinter:
- _AVAILABLE_PRINTERS: ClassVar[Dict[str, 'BasePrinter']] = {
+ _AVAILABLE_PRINTERS: ClassVar[Dict[str, 'PrinterBase']] = {
'text': TextPrinter,
'json': JsonPrinter,
'table': TablePrinter,
# overrides
- 'table_sca': SCATablePrinter,
- 'text_sca': SCATablePrinter,
+ 'table_sca': ScaTablePrinter,
+ 'text_sca': ScaTablePrinter,
}
def __init__(self, context: click.Context) -> None:
@@ -37,7 +37,7 @@ def print_scan_results(self, local_scan_results: List['LocalScanResult']) -> Non
printer = self._get_scan_printer()
printer.print_scan_results(local_scan_results)
- def _get_scan_printer(self) -> 'BasePrinter':
+ def _get_scan_printer(self) -> 'PrinterBase':
printer_class = self._printer_class
composite_printer = self._AVAILABLE_PRINTERS.get(f'{self.output_type}_{self.scan_type}')
diff --git a/cycode/cli/printers/json_printer.py b/cycode/cli/printers/json_printer.py
index 52df39ea..2f048ae7 100644
--- a/cycode/cli/printers/json_printer.py
+++ b/cycode/cli/printers/json_printer.py
@@ -4,14 +4,14 @@
import click
from cycode.cli.models import CliError, CliResult
-from cycode.cli.printers.base_printer import BasePrinter
+from cycode.cli.printers.printer_base import PrinterBase
from cycode.cyclient.models import DetectionSchema
if TYPE_CHECKING:
from cycode.cli.models import LocalScanResult
-class JsonPrinter(BasePrinter):
+class JsonPrinter(PrinterBase):
def print_result(self, result: CliResult) -> None:
result = {'result': result.success, 'message': result.message}
diff --git a/cycode/cli/printers/base_printer.py b/cycode/cli/printers/printer_base.py
similarity index 96%
rename from cycode/cli/printers/base_printer.py
rename to cycode/cli/printers/printer_base.py
index ceb430ab..69802e54 100644
--- a/cycode/cli/printers/base_printer.py
+++ b/cycode/cli/printers/printer_base.py
@@ -9,7 +9,7 @@
from cycode.cli.models import LocalScanResult
-class BasePrinter(ABC):
+class PrinterBase(ABC):
RED_COLOR_NAME = 'red'
WHITE_COLOR_NAME = 'white'
GREEN_COLOR_NAME = 'green'
diff --git a/cycode/cli/printers/sca_table_printer.py b/cycode/cli/printers/sca_table_printer.py
deleted file mode 100644
index 80d2da4f..00000000
--- a/cycode/cli/printers/sca_table_printer.py
+++ /dev/null
@@ -1,156 +0,0 @@
-from collections import defaultdict
-from typing import TYPE_CHECKING, Dict, List
-
-import click
-from texttable import Texttable
-
-from cycode.cli.consts import LICENSE_COMPLIANCE_POLICY_ID, PACKAGE_VULNERABILITY_POLICY_ID
-from cycode.cli.models import Detection
-from cycode.cli.printers.base_table_printer import BaseTablePrinter
-from cycode.cli.utils.string_utils import shortcut_dependency_paths
-
-if TYPE_CHECKING:
- from cycode.cli.models import LocalScanResult
-
-SEVERITY_COLUMN = 'Severity'
-LICENSE_COLUMN = 'License'
-UPGRADE_COLUMN = 'Upgrade'
-REPOSITORY_COLUMN = 'Repository'
-CVE_COLUMN = 'CVE'
-
-PREVIEW_DETECTIONS_COMMON_HEADERS = [
- 'File Path',
- 'Ecosystem',
- 'Dependency Name',
- 'Direct Dependency',
- 'Development Dependency',
- 'Dependency Paths',
-]
-
-
-class SCATablePrinter(BaseTablePrinter):
- def _print_results(self, local_scan_results: List['LocalScanResult']) -> None:
- detections_per_detection_type_id = self._extract_detections_per_detection_type_id(local_scan_results)
- self._print_detection_per_detection_type_id(detections_per_detection_type_id)
-
- @staticmethod
- def _extract_detections_per_detection_type_id(
- local_scan_results: List['LocalScanResult'],
- ) -> Dict[str, List[Detection]]:
- detections_per_detection_type_id = defaultdict(list)
-
- for local_scan_result in local_scan_results:
- for document_detection in local_scan_result.document_detections:
- for detection in document_detection.detections:
- detections_per_detection_type_id[detection.detection_type_id].append(detection)
-
- return detections_per_detection_type_id
-
- def _print_detection_per_detection_type_id(
- self, detections_per_detection_type_id: Dict[str, List[Detection]]
- ) -> None:
- for detection_type_id in detections_per_detection_type_id:
- detections = detections_per_detection_type_id[detection_type_id]
- headers = self._get_table_headers()
-
- title = None
- rows = []
-
- if detection_type_id == PACKAGE_VULNERABILITY_POLICY_ID:
- title = 'Dependencies Vulnerabilities'
-
- headers = [SEVERITY_COLUMN, *headers]
- headers.extend(PREVIEW_DETECTIONS_COMMON_HEADERS)
- headers.append(CVE_COLUMN)
- headers.append(UPGRADE_COLUMN)
-
- for detection in detections:
- rows.append(self._get_upgrade_package_vulnerability(detection))
- elif detection_type_id == LICENSE_COMPLIANCE_POLICY_ID:
- title = 'License Compliance'
-
- headers.extend(PREVIEW_DETECTIONS_COMMON_HEADERS)
- headers.append(LICENSE_COLUMN)
-
- for detection in detections:
- rows.append(self._get_license(detection))
-
- if rows:
- self._print_table_detections(detections, headers, rows, title)
-
- def _get_table_headers(self) -> list:
- if self._is_git_repository():
- return [REPOSITORY_COLUMN]
-
- return []
-
- def _print_table_detections(
- self, detections: List[Detection], headers: List[str], rows: List[List[str]], title: str
- ) -> None:
- self._print_summary_issues(detections, title)
- text_table = Texttable()
- text_table.header(headers)
-
- self.set_table_width(headers, text_table)
-
- for row in rows:
- text_table.add_row(row)
-
- click.echo(text_table.draw())
-
- @staticmethod
- def set_table_width(headers: List[str], text_table: Texttable) -> None:
- header_width_size_cols = []
- for header in headers:
- header_len = len(header)
- if header == CVE_COLUMN:
- header_width_size_cols.append(header_len * 5)
- elif header == UPGRADE_COLUMN:
- header_width_size_cols.append(header_len * 2)
- else:
- header_width_size_cols.append(header_len)
- text_table.set_cols_width(header_width_size_cols)
-
- @staticmethod
- def _print_summary_issues(detections: List, title: str) -> None:
- click.echo(f'⛔ Found {len(detections)} issues of type: {click.style(title, bold=True)}')
-
- def _get_common_detection_fields(self, detection: Detection) -> List[str]:
- dependency_paths = 'N/A'
- dependency_paths_raw = detection.detection_details.get('dependency_paths')
- if dependency_paths_raw:
- dependency_paths = shortcut_dependency_paths(dependency_paths_raw)
-
- row = [
- detection.detection_details.get('file_name'),
- detection.detection_details.get('ecosystem'),
- detection.detection_details.get('package_name'),
- detection.detection_details.get('is_direct_dependency_str'),
- detection.detection_details.get('is_dev_dependency_str'),
- dependency_paths,
- ]
-
- if self._is_git_repository():
- row = [detection.detection_details.get('repository_name'), *row]
-
- return row
-
- def _get_upgrade_package_vulnerability(self, detection: Detection) -> List[str]:
- alert = detection.detection_details.get('alert')
- row = [
- detection.detection_details.get('advisory_severity'),
- *self._get_common_detection_fields(detection),
- detection.detection_details.get('vulnerability_id'),
- ]
-
- upgrade = ''
- if alert.get('first_patched_version'):
- upgrade = f'{alert.get("vulnerable_requirements")} -> {alert.get("first_patched_version")}'
- row.append(upgrade)
-
- return row
-
- def _get_license(self, detection: Detection) -> List[str]:
- row = self._get_common_detection_fields(detection)
- row.append(f'{detection.detection_details.get("license")}')
- return row
diff --git a/cycode/cli/printers/tables/__init__.py b/cycode/cli/printers/tables/__init__.py
new file mode 100644
index 00000000..e69de29b
diff --git a/cycode/cli/printers/tables/sca_table_printer.py b/cycode/cli/printers/tables/sca_table_printer.py
new file mode 100644
index 00000000..da0ac8ac
--- /dev/null
+++ b/cycode/cli/printers/tables/sca_table_printer.py
@@ -0,0 +1,143 @@
+from collections import defaultdict
+from typing import TYPE_CHECKING, Dict, List
+
+import click
+
+from cycode.cli.consts import LICENSE_COMPLIANCE_POLICY_ID, PACKAGE_VULNERABILITY_POLICY_ID
+from cycode.cli.models import Detection
+from cycode.cli.printers.tables.table import Table
+from cycode.cli.printers.tables.table_models import ColumnInfoBuilder, ColumnWidths
+from cycode.cli.printers.tables.table_printer_base import TablePrinterBase
+from cycode.cli.utils.string_utils import shortcut_dependency_paths
+
+if TYPE_CHECKING:
+ from cycode.cli.models import LocalScanResult
+
+
+column_builder = ColumnInfoBuilder()
+
+# Building must have strict order. Represents the order of the columns in the table (from left to right)
+SEVERITY_COLUMN = column_builder.build(name='Severity')
+REPOSITORY_COLUMN = column_builder.build(name='Repository')
+
+FILE_PATH_COLUMN = column_builder.build(name='File Path')
+ECOSYSTEM_COLUMN = column_builder.build(name='Ecosystem')
+DEPENDENCY_NAME_COLUMN = column_builder.build(name='Dependency Name')
+DIRECT_DEPENDENCY_COLUMN = column_builder.build(name='Direct Dependency')
+DEVELOPMENT_DEPENDENCY_COLUMN = column_builder.build(name='Development Dependency')
+DEPENDENCY_PATHS_COLUMN = column_builder.build(name='Dependency Paths')
+
+CVE_COLUMNS = column_builder.build(name='CVE')
+UPGRADE_COLUMN = column_builder.build(name='Upgrade')
+LICENSE_COLUMN = column_builder.build(name='License')
+
+COLUMN_WIDTHS_CONFIG: ColumnWidths = {
+ REPOSITORY_COLUMN: 2,
+ FILE_PATH_COLUMN: 3,
+ CVE_COLUMNS: 5,
+ UPGRADE_COLUMN: 3,
+ LICENSE_COLUMN: 2,
+}
+
+
+class ScaTablePrinter(TablePrinterBase):
+ def _print_results(self, local_scan_results: List['LocalScanResult']) -> None:
+ detections_per_policy_id = self._extract_detections_per_policy_id(local_scan_results)
+ for policy_id, detections in detections_per_policy_id.items():
+ table = self._get_table(policy_id)
+ table.set_cols_width(COLUMN_WIDTHS_CONFIG)
+
+ for detection in detections:
+ self._enrich_table_with_values(table, detection)
+
+ self._print_summary_issues(len(detections), self._get_title(policy_id))
+ self._print_table(table)
+
+ self._print_report_urls(local_scan_results)
+
+ @staticmethod
+ def _get_title(policy_id: str) -> str:
+ if policy_id == PACKAGE_VULNERABILITY_POLICY_ID:
+ return 'Dependencies Vulnerabilities'
+ if policy_id == LICENSE_COMPLIANCE_POLICY_ID:
+ return 'License Compliance'
+
+ return 'Unknown'
+
+ def _get_table(self, policy_id: str) -> Table:
+ table = Table()
+
+ if policy_id == PACKAGE_VULNERABILITY_POLICY_ID:
+ table.add(SEVERITY_COLUMN)
+ table.add(CVE_COLUMNS)
+ table.add(UPGRADE_COLUMN)
+ elif policy_id == LICENSE_COMPLIANCE_POLICY_ID:
+ table.add(LICENSE_COLUMN)
+
+ if self._is_git_repository():
+ table.add(REPOSITORY_COLUMN)
+
+ table.add(FILE_PATH_COLUMN)
+ table.add(ECOSYSTEM_COLUMN)
+ table.add(DEPENDENCY_NAME_COLUMN)
+ table.add(DIRECT_DEPENDENCY_COLUMN)
+ table.add(DEVELOPMENT_DEPENDENCY_COLUMN)
+ table.add(DEPENDENCY_PATHS_COLUMN)
+
+ return table
+
+ @staticmethod
+ def _enrich_table_with_values(table: Table, detection: Detection) -> None:
+ detection_details = detection.detection_details
+
+ table.set(SEVERITY_COLUMN, detection_details.get('advisory_severity'))
+ table.set(REPOSITORY_COLUMN, detection_details.get('repository_name'))
+
+ table.set(FILE_PATH_COLUMN, detection_details.get('file_name'))
+ table.set(ECOSYSTEM_COLUMN, detection_details.get('ecosystem'))
+ table.set(DEPENDENCY_NAME_COLUMN, detection_details.get('package_name'))
+ table.set(DIRECT_DEPENDENCY_COLUMN, detection_details.get('is_direct_dependency_str'))
+ table.set(DEVELOPMENT_DEPENDENCY_COLUMN, detection_details.get('is_dev_dependency_str'))
+
+ dependency_paths = 'N/A'
+ dependency_paths_raw = detection_details.get('dependency_paths')
+ if dependency_paths_raw:
+ dependency_paths = shortcut_dependency_paths(dependency_paths_raw)
+ table.set(DEPENDENCY_PATHS_COLUMN, dependency_paths)
+
+ upgrade = ''
+ alert = detection_details.get('alert')
+ if alert and alert.get('first_patched_version'):
+ upgrade = f'{alert.get("vulnerable_requirements")} -> {alert.get("first_patched_version")}'
+ table.set(UPGRADE_COLUMN, upgrade)
+
+ table.set(CVE_COLUMNS, detection_details.get('vulnerability_id'))
+ table.set(LICENSE_COLUMN, detection_details.get('license'))
+
+ @staticmethod
+ def _print_report_urls(local_scan_results: List['LocalScanResult']) -> None:
+ report_urls = [scan_result.report_url for scan_result in local_scan_results if scan_result.report_url]
+ if not report_urls:
+ return
+
+ click.echo('Report URLs:')
+ for report_url in report_urls:
+ click.echo(f'- {report_url}')
+
+ @staticmethod
+ def _print_summary_issues(detections_count: int, title: str) -> None:
+ click.echo(f'⛔ Found {detections_count} issues of type: {click.style(title, bold=True)}')
+
+ @staticmethod
+ def _extract_detections_per_policy_id(
+ local_scan_results: List['LocalScanResult'],
+ ) -> Dict[str, List[Detection]]:
+ detections_to_policy_id = defaultdict(list)
+
+ for local_scan_result in local_scan_results:
+ for document_detection in local_scan_result.document_detections:
+ for detection in document_detection.detections:
+ detections_to_policy_id[detection.detection_type_id].append(detection)
+
+ # sort dict by keys (policy id) to make persist output order
+ return dict(sorted(detections_to_policy_id.items(), reverse=True))
diff --git a/cycode/cli/printers/table.py b/cycode/cli/printers/tables/table.py
similarity index 96%
rename from cycode/cli/printers/table.py
rename to cycode/cli/printers/tables/table.py
index 9c90c940..2017b9c8 100644
--- a/cycode/cli/printers/table.py
+++ b/cycode/cli/printers/tables/table.py
@@ -3,7 +3,7 @@
from texttable import Texttable
if TYPE_CHECKING:
- from cycode.cli.printers.table_models import ColumnInfo, ColumnWidths
+ from cycode.cli.printers.tables.table_models import ColumnInfo, ColumnWidths
class Table:
diff --git a/cycode/cli/printers/table_models.py b/cycode/cli/printers/tables/table_models.py
similarity index 62%
rename from cycode/cli/printers/table_models.py
rename to cycode/cli/printers/tables/table_models.py
index e3dc195d..c162a8ce 100644
--- a/cycode/cli/printers/table_models.py
+++ b/cycode/cli/printers/tables/table_models.py
@@ -2,12 +2,12 @@
class ColumnInfoBuilder:
- _index = 0
+ def __init__(self) -> None:
+ self._index = 0
- @staticmethod
- def build(name: str) -> 'ColumnInfo':
- column_info = ColumnInfo(name, ColumnInfoBuilder._index)
- ColumnInfoBuilder._index += 1
+ def build(self, name: str) -> 'ColumnInfo':
+ column_info = ColumnInfo(name, self._index)
+ self._index += 1
return column_info
diff --git a/cycode/cli/printers/table_printer.py b/cycode/cli/printers/tables/table_printer.py
similarity index 79%
rename from cycode/cli/printers/table_printer.py
rename to cycode/cli/printers/tables/table_printer.py
index c5a01201..2aa2ca4e 100644
--- a/cycode/cli/printers/table_printer.py
+++ b/cycode/cli/printers/tables/table_printer.py
@@ -4,26 +4,28 @@
from cycode.cli.consts import INFRA_CONFIGURATION_SCAN_TYPE, SAST_SCAN_TYPE, SECRET_SCAN_TYPE
from cycode.cli.models import Detection, Document
-from cycode.cli.printers.base_table_printer import BaseTablePrinter
-from cycode.cli.printers.table import Table
-from cycode.cli.printers.table_models import ColumnInfoBuilder, ColumnWidthsConfig
+from cycode.cli.printers.tables.table import Table
+from cycode.cli.printers.tables.table_models import ColumnInfoBuilder, ColumnWidthsConfig
+from cycode.cli.printers.tables.table_printer_base import TablePrinterBase
from cycode.cli.utils.string_utils import get_position_in_line, obfuscate_text
if TYPE_CHECKING:
from cycode.cli.models import LocalScanResult
-# Creation must have strict order. Represents the order of the columns in the table (from left to right)
-ISSUE_TYPE_COLUMN = ColumnInfoBuilder.build(name='Issue Type')
-RULE_ID_COLUMN = ColumnInfoBuilder.build(name='Rule ID')
-FILE_PATH_COLUMN = ColumnInfoBuilder.build(name='File Path')
-SECRET_SHA_COLUMN = ColumnInfoBuilder.build(name='Secret SHA')
-COMMIT_SHA_COLUMN = ColumnInfoBuilder.build(name='Commit SHA')
-LINE_NUMBER_COLUMN = ColumnInfoBuilder.build(name='Line Number')
-COLUMN_NUMBER_COLUMN = ColumnInfoBuilder.build(name='Column Number')
-VIOLATION_LENGTH_COLUMN = ColumnInfoBuilder.build(name='Violation Length')
-VIOLATION_COLUMN = ColumnInfoBuilder.build(name='Violation')
-SCAN_ID_COLUMN = ColumnInfoBuilder.build(name='Scan ID')
-REPORT_URL_COLUMN = ColumnInfoBuilder.build(name='Report URL')
+column_builder = ColumnInfoBuilder()
+
+# Building must have strict order. Represents the order of the columns in the table (from left to right)
+ISSUE_TYPE_COLUMN = column_builder.build(name='Issue Type')
+RULE_ID_COLUMN = column_builder.build(name='Rule ID')
+FILE_PATH_COLUMN = column_builder.build(name='File Path')
+SECRET_SHA_COLUMN = column_builder.build(name='Secret SHA')
+COMMIT_SHA_COLUMN = column_builder.build(name='Commit SHA')
+LINE_NUMBER_COLUMN = column_builder.build(name='Line Number')
+COLUMN_NUMBER_COLUMN = column_builder.build(name='Column Number')
+VIOLATION_LENGTH_COLUMN = column_builder.build(name='Violation Length')
+VIOLATION_COLUMN = column_builder.build(name='Violation')
+SCAN_ID_COLUMN = column_builder.build(name='Scan ID')
+REPORT_URL_COLUMN = column_builder.build(name='Report URL')
COLUMN_WIDTHS_CONFIG: ColumnWidthsConfig = {
SECRET_SCAN_TYPE: {
@@ -49,7 +51,7 @@
}
-class TablePrinter(BaseTablePrinter):
+class TablePrinter(TablePrinterBase):
def _print_results(self, local_scan_results: List['LocalScanResult']) -> None:
table = self._get_table()
if self.scan_type in COLUMN_WIDTHS_CONFIG:
@@ -63,7 +65,7 @@ def _print_results(self, local_scan_results: List['LocalScanResult']) -> None:
table.set(SCAN_ID_COLUMN, local_scan_result.scan_id)
self._enrich_table_with_values(table, detection, document_detections.document)
- click.echo(table.get_table().draw())
+ self._print_table(table)
def _get_table(self) -> Table:
table = Table()
@@ -74,7 +76,6 @@ def _get_table(self) -> Table:
table.add(LINE_NUMBER_COLUMN)
table.add(COLUMN_NUMBER_COLUMN)
table.add(SCAN_ID_COLUMN)
- table.add(REPORT_URL_COLUMN)
if self._is_git_repository():
table.add(COMMIT_SHA_COLUMN)
@@ -84,6 +85,9 @@ def _get_table(self) -> Table:
table.add(VIOLATION_LENGTH_COLUMN)
table.add(VIOLATION_COLUMN)
+ if self.context.obj.get('report'):
+ table.add(REPORT_URL_COLUMN)
+
return table
def _enrich_table_with_values(self, table: Table, detection: Detection, document: Document) -> None:
diff --git a/cycode/cli/printers/base_table_printer.py b/cycode/cli/printers/tables/table_printer_base.py
similarity index 82%
rename from cycode/cli/printers/base_table_printer.py
rename to cycode/cli/printers/tables/table_printer_base.py
index f304f967..ab444c58 100644
--- a/cycode/cli/printers/base_table_printer.py
+++ b/cycode/cli/printers/tables/table_printer_base.py
@@ -4,17 +4,17 @@
import click
from cycode.cli.models import CliError, CliResult
-from cycode.cli.printers.base_printer import BasePrinter
+from cycode.cli.printers.printer_base import PrinterBase
from cycode.cli.printers.text_printer import TextPrinter
if TYPE_CHECKING:
from cycode.cli.models import LocalScanResult
+ from cycode.cli.printers.tables.table import Table
-class BaseTablePrinter(BasePrinter, abc.ABC):
+class TablePrinterBase(PrinterBase, abc.ABC):
def __init__(self, context: click.Context) -> None:
super().__init__(context)
- self.context = context
self.scan_type: str = context.obj.get('scan_type')
self.show_secret: bool = context.obj.get('show_secret', False)
@@ -37,3 +37,7 @@ def _is_git_repository(self) -> bool:
@abc.abstractmethod
def _print_results(self, local_scan_results: List['LocalScanResult']) -> None:
raise NotImplementedError
+
+ @staticmethod
+ def _print_table(table: 'Table') -> None:
+ click.echo(table.get_table().draw())
diff --git a/cycode/cli/printers/text_printer.py b/cycode/cli/printers/text_printer.py
index d06021a3..0390210a 100644
--- a/cycode/cli/printers/text_printer.py
+++ b/cycode/cli/printers/text_printer.py
@@ -6,14 +6,14 @@
from cycode.cli.config import config
from cycode.cli.consts import COMMIT_RANGE_BASED_COMMAND_SCAN_TYPES, SECRET_SCAN_TYPE
from cycode.cli.models import CliError, CliResult, Detection, Document, DocumentDetections
-from cycode.cli.printers.base_printer import BasePrinter
+from cycode.cli.printers.printer_base import PrinterBase
from cycode.cli.utils.string_utils import get_position_in_line, obfuscate_text
if TYPE_CHECKING:
from cycode.cli.models import LocalScanResult
-class TextPrinter(BasePrinter):
+class TextPrinter(PrinterBase):
def __init__(self, context: click.Context) -> None:
super().__init__(context)
self.scan_type: str = context.obj.get('scan_type')
From 6feeb0803e7d115cd045e8d07a29e4fd8028bbeb Mon Sep 17 00:00:00 2001
From: Ilya Siamionau
Date: Mon, 24 Jul 2023 15:43:11 +0400
Subject: [PATCH 018/257] CM-25594 - Drop support of the old position of
--output option (#148)
---
cycode/cli/main.py | 21 +--------------------
tests/cli/test_main.py | 18 ++----------------
2 files changed, 3 insertions(+), 36 deletions(-)
diff --git a/cycode/cli/main.py b/cycode/cli/main.py
index 3fd99f7f..2f5c5b04 100644
--- a/cycode/cli/main.py
+++ b/cycode/cli/main.py
@@ -75,17 +75,6 @@
type=bool,
required=False,
)
-@click.option(
- '--output',
- '-o',
- default=None,
- help="""
- \b
- Specify the results output (text/json/table),
- the default is text
- """,
- type=click.Choice(['text', 'json', 'table']),
-)
@click.option(
'--severity-threshold',
default=None,
@@ -127,7 +116,6 @@ def code_scan(
client_id: str,
show_secret: bool,
soft_fail: bool,
- output: str,
severity_threshold: str,
sca_scan: List[str],
monitor: bool,
@@ -143,15 +131,8 @@ def code_scan(
else:
context.obj['soft_fail'] = config['soft_fail']
- context.obj['scan_type'] = scan_type
-
- # save backward compatability with old style command
- if output is not None:
- context.obj['output'] = output
- if output == 'json':
- context.obj['no_progress_meter'] = True
-
context.obj['client'] = get_cycode_client(client_id, secret, not context.obj['show_secret'])
+ context.obj['scan_type'] = scan_type
context.obj['severity_threshold'] = severity_threshold
context.obj['monitor'] = monitor
context.obj['report'] = report
diff --git a/tests/cli/test_main.py b/tests/cli/test_main.py
index 77375920..8c3c6246 100644
--- a/tests/cli/test_main.py
+++ b/tests/cli/test_main.py
@@ -25,10 +25,7 @@ def _is_json(plain: str) -> bool:
@responses.activate
@pytest.mark.parametrize('output', ['text', 'json'])
-@pytest.mark.parametrize('option_space', ['scan', 'global'])
-def test_passing_output_option(
- output: str, option_space: str, scan_client: 'ScanClient', api_token_response: responses.Response
-) -> None:
+def test_passing_output_option(output: str, scan_client: 'ScanClient', api_token_response: responses.Response) -> None:
scan_type = 'secret'
responses.add(get_zipped_file_scan_response(get_zipped_file_scan_url(scan_type, scan_client)))
@@ -37,18 +34,7 @@ def test_passing_output_option(
# This raises connection error on the attempt to report scan.
# It doesn't perform real request
- args = ['scan', '--soft-fail', 'path', str(_PATH_TO_SCAN)]
-
- if option_space == 'global':
- global_args = ['--output', output]
- global_args.extend(args)
-
- args = global_args
- elif option_space == 'scan':
- # test backward compatability with old style command
- args.insert(2, '--output')
- args.insert(3, output)
-
+ args = ['--output', output, 'scan', '--soft-fail', 'path', str(_PATH_TO_SCAN)]
result = CliRunner().invoke(main_cli, args, env=CLI_ENV_VARS)
except_json = output == 'json'
From f8149a5c31ea0aab8a8bece13ae794dfeb7847c2 Mon Sep 17 00:00:00 2001
From: Ilya Siamionau
Date: Mon, 24 Jul 2023 15:53:16 +0400
Subject: [PATCH 019/257] CM-25595 - Drop support of --version option (#147)
---
.github/workflows/build_executable.yml | 4 ++--
README.md | 27 +++++++++++++-------------
cycode/cli/main.py | 1 -
3 files changed, 16 insertions(+), 16 deletions(-)
diff --git a/.github/workflows/build_executable.yml b/.github/workflows/build_executable.yml
index 4f0417a8..f3690f11 100644
--- a/.github/workflows/build_executable.yml
+++ b/.github/workflows/build_executable.yml
@@ -62,7 +62,7 @@ jobs:
run: poetry run pyinstaller pyinstaller.spec
- name: Test executable
- run: ./dist/cycode --version
+ run: ./dist/cycode version
- name: Sign macOS executable
if: ${{ startsWith(matrix.os, 'macos') }}
@@ -110,7 +110,7 @@ jobs:
- name: Test signed executable
if: ${{ startsWith(matrix.os, 'macos') }}
- run: ./dist/cycode --version
+ run: ./dist/cycode version
- uses: actions/upload-artifact@v3
with:
diff --git a/README.md b/README.md
index 5ea2bdc6..71b885e1 100644
--- a/README.md
+++ b/README.md
@@ -213,19 +213,19 @@ repos:
The following are the options and commands available with the Cycode CLI application:
-| Option | Description |
-|--------------------------------------|-------------------------------------------------------------------|
-| `-o`, `--output [text\|json\|table]` | Specify the output (`text`/`json`/`table`). The default is `text` |
-| `-v`, `--verbose` | Show detailed logs |
-| `--version` | Show the version and exit. |
-| `--help` | Show options for given command. |
-
-| Command | Description |
-|-------------------------------------|-------------|
-| [auth](#use-auth-command) | Authenticates your machine to associate CLI with your Cycode account. |
-| [configure](#use-configure-command) | Initial command to authenticate your CLI client with Cycode using client ID and client secret. |
-| [ignore](#ingoring-scan-results) | Ignore a specific value, path or rule ID |
-| [scan](#running-a-scan) | Scan content for secrets/IaC/SCA/SAST violations. You need to specify which scan type: `ci`/`commit_history`/`path`/`repository`/etc |
+| Option | Description |
+|--------------------------------------|--------------------------------------------------------------------|
+| `-o`, `--output [text\|json\|table]` | Specify the output (`text`/`json`/`table`). The default is `text`. |
+| `-v`, `--verbose` | Show detailed logs. |
+| `--help` | Show options for given command. |
+
+| Command | Description |
+|-------------------------------------|---------------------------------------------------------------------------------------------------------------------------------------|
+| [auth](#use-auth-command) | Authenticates your machine to associate CLI with your Cycode account. |
+| [configure](#use-configure-command) | Initial command to authenticate your CLI client with Cycode using client ID and client secret. |
+| [ignore](#ingoring-scan-results) | Ignore a specific value, path or rule ID. |
+| [scan](#running-a-scan) | Scan content for secrets/IaC/SCA/SAST violations. You need to specify which scan type: `ci`/`commit_history`/`path`/`repository`/etc. |
+| version | Show the version and exit. |
# Running a Scan
@@ -555,6 +555,7 @@ Ignore rules can be added to ignore specific secret values, specific SHA512 valu
> :warning: **Warning**
> Adding values to be ignored should be done with careful consideration of the values, paths, and policies to ensure that the scans will pick up true positives.
+
The following are the options available for the `cycode ignore` command:
| Option | Description |
diff --git a/cycode/cli/main.py b/cycode/cli/main.py
index 2f5c5b04..4263ff02 100644
--- a/cycode/cli/main.py
+++ b/cycode/cli/main.py
@@ -214,7 +214,6 @@ def version(context: click.Context) -> None:
help='Characteristic JSON object that lets servers identify the application',
type=str,
)
-@click.version_option(__version__, prog_name=PROGRAM_NAME)
@click.pass_context
def main_cli(
context: click.Context, verbose: bool, no_progress_meter: bool, output: str, user_agent: Optional[str]
From 62b49071756b4fd2461097f8890859969d97efe7 Mon Sep 17 00:00:00 2001
From: Ilya Siamionau
Date: Wed, 26 Jul 2023 17:49:22 +0400
Subject: [PATCH 020/257] CM-25653 - Improve text messages (#149)
---
cycode/cli/auth/auth_command.py | 13 +++--
cycode/cli/code_scanner.py | 22 +++++---
cycode/cli/consts.py | 4 ++
cycode/cli/main.py | 51 ++++++++-----------
.../cli/printers/tables/sca_table_printer.py | 2 +-
.../user_settings/user_settings_commands.py | 28 +++++-----
6 files changed, 61 insertions(+), 59 deletions(-)
diff --git a/cycode/cli/auth/auth_command.py b/cycode/cli/auth/auth_command.py
index 3fe037bf..c7853068 100644
--- a/cycode/cli/auth/auth_command.py
+++ b/cycode/cli/auth/auth_command.py
@@ -12,10 +12,11 @@
@click.group(
- invoke_without_command=True, short_help='Authenticates your machine to associate CLI with your cycode account'
+ invoke_without_command=True, short_help='Authenticate your machine to associate the CLI with your Cycode account.'
)
@click.pass_context
def authenticate(context: click.Context) -> None:
+ """Authenticates your machine."""
if context.invoked_subcommand is not None:
# if it is a subcommand, do nothing
return
@@ -32,14 +33,16 @@ def authenticate(context: click.Context) -> None:
_handle_exception(context, e)
-@authenticate.command(name='check')
+@authenticate.command(
+ name='check', short_help='Checks that your machine is associating the CLI with your Cycode account.'
+)
@click.pass_context
def authorization_check(context: click.Context) -> None:
- """Check your machine associating CLI with your cycode account"""
+ """Validates that your Cycode account has permission to work with the CLI."""
printer = ConsolePrinter(context)
- passed_auth_check_res = CliResult(success=True, message='You are authorized')
- failed_auth_check_res = CliResult(success=False, message='You are not authorized')
+ passed_auth_check_res = CliResult(success=True, message='Cycode authentication verified')
+ failed_auth_check_res = CliResult(success=False, message='Cycode authentication failed')
client_id, client_secret = CredentialsManager().get_credentials()
if not client_id or not client_secret:
diff --git a/cycode/cli/code_scanner.py b/cycode/cli/code_scanner.py
index 15313d45..a7588172 100644
--- a/cycode/cli/code_scanner.py
+++ b/cycode/cli/code_scanner.py
@@ -51,7 +51,7 @@
start_scan_time = time.time()
-@click.command(short_help='Scan git repository including its history')
+@click.command(short_help='Scan the git repository including its history.')
@click.argument('path', nargs=1, type=click.STRING, required=True)
@click.option(
'--branch',
@@ -72,6 +72,7 @@ def scan_repository(context: click.Context, path: str, branch: str) -> None:
raise click.ClickException('Monitor flag is currently supported for SCA scan type only')
progress_bar = context.obj['progress_bar']
+ progress_bar.start()
file_entries = list(get_git_repository_tree_file_entries(path, branch))
progress_bar.set_section_length(ProgressBarSection.PREPARE_LOCAL_FILES, len(file_entries))
@@ -96,7 +97,7 @@ def scan_repository(context: click.Context, path: str, branch: str) -> None:
_handle_exception(context, e)
-@click.command(short_help='Scan all the commits history in this git repository')
+@click.command(short_help='Scan all the commits history in this git repository.')
@click.argument('path', nargs=1, type=click.STRING, required=True)
@click.option(
'--commit_range',
@@ -119,7 +120,9 @@ def scan_commit_range(
context: click.Context, path: str, commit_range: str, max_commits_count: Optional[int] = None
) -> None:
scan_type = context.obj['scan_type']
+
progress_bar = context.obj['progress_bar']
+ progress_bar.start()
if scan_type not in consts.COMMIT_RANGE_SCAN_SUPPORTED_SCAN_TYPES:
raise click.ClickException(f'Commit range scanning for {str.upper(scan_type)} is not supported')
@@ -185,13 +188,14 @@ def scan_ci(context: click.Context) -> None:
scan_commit_range(context, path=os.getcwd(), commit_range=get_commit_range())
-@click.command(short_help='Scan the files in the path supplied in the command')
+@click.command(short_help='Scan the files in the path provided in the command.')
@click.argument('path', nargs=1, type=click.STRING, required=True)
@click.pass_context
def scan_path(context: click.Context, path: str) -> None:
- logger.debug('Starting path scan process, %s', {'path': path})
-
progress_bar = context.obj['progress_bar']
+ progress_bar.start()
+
+ logger.debug('Starting path scan process, %s', {'path': path})
all_files_to_scan = get_relevant_files_in_path(path=path, exclude_patterns=['**/.git/**', '**/.cycode/**'])
@@ -218,12 +222,14 @@ def scan_path(context: click.Context, path: str) -> None:
scan_disk_files(context, path, relevant_files_to_scan)
-@click.command(short_help='Use this command to scan the content that was not committed yet')
+@click.command(short_help='Use this command to scan any content that was not committed yet.')
@click.argument('ignored_args', nargs=-1, type=click.UNPROCESSED)
@click.pass_context
def pre_commit_scan(context: click.Context, ignored_args: List[str]) -> None:
scan_type = context.obj['scan_type']
+
progress_bar = context.obj['progress_bar']
+ progress_bar.start()
if scan_type == consts.SCA_SCAN_TYPE:
scan_sca_pre_commit(context)
@@ -242,7 +248,7 @@ def pre_commit_scan(context: click.Context, ignored_args: List[str]) -> None:
scan_documents(context, documents_to_scan, is_git_diff=True)
-@click.command(short_help='Use this command to scan commits on the server side before pushing them to the repository')
+@click.command(short_help='Use this command to scan commits on the server side before pushing them to the repository.')
@click.argument('ignored_args', nargs=-1, type=click.UNPROCESSED)
@click.pass_context
def pre_receive_scan(context: click.Context, ignored_args: List[str]) -> None:
@@ -1160,7 +1166,7 @@ def _handle_exception(context: click.Context, e: Exception, *, return_exception:
soft_fail=False,
code='invalid_git_error',
message='The path you supplied does not correlate to a git repository. '
- 'Should you still wish to scan this path, use: `cycode scan path `',
+ 'If you still wish to scan this path, use: `cycode scan path `',
),
}
diff --git a/cycode/cli/consts.py b/cycode/cli/consts.py
index 6d710b1b..76570fde 100644
--- a/cycode/cli/consts.py
+++ b/cycode/cli/consts.py
@@ -1,4 +1,8 @@
PROGRAM_NAME = 'cycode'
+CLI_CONTEXT_SETTINGS = {
+ 'terminal_width': 10**9,
+ 'max_content_width': 10**9,
+}
PRE_COMMIT_COMMAND_SCAN_TYPE = 'pre_commit'
PRE_RECEIVE_COMMAND_SCAN_TYPE = 'pre_receive'
diff --git a/cycode/cli/main.py b/cycode/cli/main.py
index 4263ff02..821251ad 100644
--- a/cycode/cli/main.py
+++ b/cycode/cli/main.py
@@ -9,7 +9,7 @@
from cycode.cli import code_scanner
from cycode.cli.auth.auth_command import authenticate
from cycode.cli.config import config
-from cycode.cli.consts import ISSUE_DETECTED_STATUS_CODE, NO_ISSUES_STATUS_CODE, PROGRAM_NAME
+from cycode.cli.consts import CLI_CONTEXT_SETTINGS, ISSUE_DETECTED_STATUS_CODE, NO_ISSUES_STATUS_CODE, PROGRAM_NAME
from cycode.cli.models import Severity
from cycode.cli.user_settings.configuration_manager import ConfigurationManager
from cycode.cli.user_settings.credentials_manager import CredentialsManager
@@ -25,8 +25,6 @@
if TYPE_CHECKING:
from cycode.cyclient.scan_client import ScanClient
-CONTEXT = {}
-
@click.group(
commands={
@@ -36,56 +34,52 @@
'pre_commit': code_scanner.pre_commit_scan,
'pre_receive': code_scanner.pre_receive_scan,
},
- short_help='Scan content for secrets/IaC/sca/SAST violations. '
- 'You need to specify which scan type: ci/commit_history/path/repository/etc',
+ short_help='Scan the content for Secrets/IaC/SCA/SAST violations. '
+ 'You`ll need to specify which scan type to perform: ci/commit_history/path/repository/etc.',
)
@click.option(
'--scan-type',
'-t',
default='secret',
- help="""
- \b
- Specify the scan you wish to execute (secret/iac/sca),
- the default is secret
- """,
+ help='Specify the type of scan you wish to execute (the default is Secrets)',
type=click.Choice(config['scans']['supported_scans']),
)
@click.option(
'--secret',
default=None,
- help='Specify a Cycode client secret for this specific scan execution',
+ help='Specify a Cycode client secret for this specific scan execution.',
type=str,
required=False,
)
@click.option(
'--client-id',
default=None,
- help='Specify a Cycode client ID for this specific scan execution',
+ help='Specify a Cycode client ID for this specific scan execution.',
type=str,
required=False,
)
@click.option(
- '--show-secret', is_flag=True, default=False, help='Show secrets in plain text', type=bool, required=False
+ '--show-secret', is_flag=True, default=False, help='Show Secrets in plain text.', type=bool, required=False
)
@click.option(
'--soft-fail',
is_flag=True,
default=False,
- help='Run scan without failing, always return a non-error status code',
+ help='Run the scan without failing; always return a non-error status code.',
type=bool,
required=False,
)
@click.option(
'--severity-threshold',
default=None,
- help='Show only violations at the specified level or higher (supported for SCA scan type only).',
+ help='Show violations only for the specified level or higher (supported for SCA scan types only).',
type=click.Choice([e.name for e in Severity]),
required=False,
)
@click.option(
'--sca-scan',
default=None,
- help='Specify the sca scan you wish to execute (package-vulnerabilities/license-compliance), the default is both',
+ help='Specify the type of SCA scan you wish to execute (the default is both).',
multiple=True,
type=click.Choice(config['scans']['supported_sca_scans']),
)
@@ -93,9 +87,7 @@
'--monitor',
is_flag=True,
default=False,
- help="When specified, the scan results will be recorded in the knowledge graph. "
- "Please note that when working in 'monitor' mode, the knowledge graph "
- "will not be updated as a result of SCM events (Push, Repo creation).(supported for SCA scan type only).",
+ help='Used for SCA scan types only; when specified, the scan results are recorded in the Discovery module.',
type=bool,
required=False,
)
@@ -103,8 +95,7 @@
'--report',
is_flag=True,
default=False,
- help='When specified, a violations report will be generated. '
- 'A URL link to the report will be printed as an output to the command execution',
+ help='When specified, generates a violations report. A link to the report will be displayed in the console output.',
type=bool,
required=False,
)
@@ -121,6 +112,7 @@ def code_scan(
monitor: bool,
report: bool,
) -> int:
+ """Scans for Secrets, IaC, SCA or SAST violations."""
if show_secret:
context.obj['show_secret'] = show_secret
else:
@@ -139,9 +131,6 @@ def code_scan(
_sca_scan_to_context(context, sca_scan)
- context.obj['progress_bar'] = get_progress_bar(hidden=context.obj['no_progress_meter'])
- context.obj['progress_bar'].start()
-
return 1
@@ -162,7 +151,7 @@ def finalize(context: click.Context, *_, **__) -> None:
sys.exit(exit_code)
-@click.command(short_help='Show the version and exit')
+@click.command(short_help='Show the CLI version and exit.')
@click.pass_context
def version(context: click.Context) -> None:
output = context.obj['output']
@@ -186,32 +175,32 @@ def version(context: click.Context) -> None:
'auth': authenticate,
'version': version,
},
- context_settings=CONTEXT,
+ context_settings=CLI_CONTEXT_SETTINGS,
)
@click.option(
'--verbose',
'-v',
is_flag=True,
default=False,
- help='Show detailed logs',
+ help='Show detailed logs.',
)
@click.option(
'--no-progress-meter',
is_flag=True,
default=False,
- help='Do not show the progress meter',
+ help='Do not show the progress meter.',
)
@click.option(
'--output',
'-o',
default='text',
- help='Specify the output (text/json/table), the default is text',
+ help='Specify the output type (the default is text).',
type=click.Choice(['text', 'json', 'table']),
)
@click.option(
'--user-agent',
default=None,
- help='Characteristic JSON object that lets servers identify the application',
+ help='Characteristic JSON object that lets servers identify the application.',
type=str,
)
@click.pass_context
@@ -232,7 +221,7 @@ def main_cli(
if output == 'json':
no_progress_meter = True
- context.obj['no_progress_meter'] = no_progress_meter
+ context.obj['progress_bar'] = get_progress_bar(hidden=no_progress_meter)
if user_agent:
user_agent_option = UserAgentOptionScheme().loads(user_agent)
diff --git a/cycode/cli/printers/tables/sca_table_printer.py b/cycode/cli/printers/tables/sca_table_printer.py
index da0ac8ac..92247d41 100644
--- a/cycode/cli/printers/tables/sca_table_printer.py
+++ b/cycode/cli/printers/tables/sca_table_printer.py
@@ -58,7 +58,7 @@ def _print_results(self, local_scan_results: List['LocalScanResult']) -> None:
@staticmethod
def _get_title(policy_id: str) -> str:
if policy_id == PACKAGE_VULNERABILITY_POLICY_ID:
- return 'Dependencies Vulnerabilities'
+ return 'Dependency Vulnerabilities'
if policy_id == LICENSE_COMPLIANCE_POLICY_ID:
return 'License Compliance'
diff --git a/cycode/cli/user_settings/user_settings_commands.py b/cycode/cli/user_settings/user_settings_commands.py
index 500b13db..9629de1e 100644
--- a/cycode/cli/user_settings/user_settings_commands.py
+++ b/cycode/cli/user_settings/user_settings_commands.py
@@ -22,9 +22,10 @@
@click.command(
- short_help='Initial command to authenticate your CLI client with Cycode using client ID and client secret'
+ short_help='Initial command to authenticate your CLI client with Cycode using a client ID and client secret.'
)
def set_credentials() -> None:
+ """Authenticates your CLI client with Cycode manually by using a client ID and client secret."""
click.echo(f'Update credentials in file ({credentials_manager.get_filename()})')
current_client_id, current_client_secret = credentials_manager.get_credentials_from_file()
client_id = _get_client_id_input(current_client_id)
@@ -37,40 +38,39 @@ def set_credentials() -> None:
click.echo(_get_credentials_update_result_message())
-@click.command()
+@click.command(short_help='Ignores a specific value, path or rule ID.')
@click.option(
- '--by-value', type=click.STRING, required=False, help='Ignore a specific value while scanning for secrets'
+ '--by-value', type=click.STRING, required=False, help='Ignore a specific value while scanning for Secrets.'
)
@click.option(
'--by-sha',
type=click.STRING,
required=False,
- help='Ignore a specific SHA512 representation of a string while scanning for secrets',
+ help='Ignore a specific SHA512 representation of a string while scanning for Secrets.',
)
@click.option(
- '--by-path', type=click.STRING, required=False, help='Avoid scanning a specific path. Need to specify scan type '
+ '--by-path',
+ type=click.STRING,
+ required=False,
+ help='Avoid scanning a specific path. You`ll need to specify the scan type.',
)
@click.option(
'--by-rule',
type=click.STRING,
required=False,
- help='Ignore scanning a specific secret rule ID/IaC rule ID. Need to specify scan type.',
+ help='Ignore scanning a specific secret rule ID or IaC rule ID. You`ll to specify the scan type.',
)
@click.option(
'--by-package',
type=click.STRING,
required=False,
- help='Ignore scanning a specific package version while running SCA scan. expected pattern - name@version',
+ help='Ignore scanning a specific package version while running an SCA scan. Expected pattern: name@version.',
)
@click.option(
'--scan-type',
'-t',
default='secret',
- help="""
- \b
- Specify the scan you wish to execute (secrets/iac),
- the default is secrets
- """,
+ help='Specify the type of scan you wish to execute (the default is Secrets).',
type=click.Choice(config['scans']['supported_scans']),
required=False,
)
@@ -81,12 +81,12 @@ def set_credentials() -> None:
is_flag=True,
default=False,
required=False,
- help='Add an ignore rule and update it in the global .cycode config file',
+ help='Add an ignore rule to the global CLI config.',
)
def add_exclusions(
by_value: str, by_sha: str, by_path: str, by_rule: str, by_package: str, scan_type: str, is_global: bool
) -> None:
- """Ignore a specific value, path or rule ID"""
+ """Ignores a specific value, path or rule ID."""
if not by_value and not by_sha and not by_path and not by_rule and not by_package:
raise click.ClickException('ignore by type is missing')
From d03b42f3f61f603b9e433fe79ca9069d1c328e1e Mon Sep 17 00:00:00 2001
From: Ilya Siamionau
Date: Thu, 27 Jul 2023 14:16:54 +0400
Subject: [PATCH 021/257] CM-25728 - Fix relative paths; fix validations of
paths (#150)
---
cycode/cli/code_scanner.py | 6 +++---
1 file changed, 3 insertions(+), 3 deletions(-)
diff --git a/cycode/cli/code_scanner.py b/cycode/cli/code_scanner.py
index a7588172..3d55b21f 100644
--- a/cycode/cli/code_scanner.py
+++ b/cycode/cli/code_scanner.py
@@ -52,7 +52,7 @@
@click.command(short_help='Scan the git repository including its history.')
-@click.argument('path', nargs=1, type=click.STRING, required=True)
+@click.argument('path', nargs=1, type=click.Path(exists=True, resolve_path=True), required=True)
@click.option(
'--branch',
'-b',
@@ -98,7 +98,7 @@ def scan_repository(context: click.Context, path: str, branch: str) -> None:
@click.command(short_help='Scan all the commits history in this git repository.')
-@click.argument('path', nargs=1, type=click.STRING, required=True)
+@click.argument('path', nargs=1, type=click.Path(exists=True, resolve_path=True), required=True)
@click.option(
'--commit_range',
'-r',
@@ -189,7 +189,7 @@ def scan_ci(context: click.Context) -> None:
@click.command(short_help='Scan the files in the path provided in the command.')
-@click.argument('path', nargs=1, type=click.STRING, required=True)
+@click.argument('path', nargs=1, type=click.Path(exists=True, resolve_path=True), required=True)
@click.pass_context
def scan_path(context: click.Context, path: str) -> None:
progress_bar = context.obj['progress_bar']
From d0b46d515415307694b9b170e37d65796e911786 Mon Sep 17 00:00:00 2001
From: Ilya Siamionau
Date: Fri, 28 Jul 2023 21:20:04 +0400
Subject: [PATCH 022/257] CM-25543 - Implement proper handling of errors in
printers (#151)
---
cycode/cli/code_scanner.py | 39 ++++++++-----------
cycode/cli/printers/console_printer.py | 8 ++--
cycode/cli/printers/json_printer.py | 20 +++++++---
cycode/cli/printers/printer_base.py | 6 ++-
.../cli/printers/tables/table_printer_base.py | 23 +++++++++--
cycode/cli/printers/text_printer.py | 20 ++++++++--
cycode/cli/utils/progress_bar.py | 2 +
7 files changed, 78 insertions(+), 40 deletions(-)
diff --git a/cycode/cli/code_scanner.py b/cycode/cli/code_scanner.py
index 3d55b21f..7c8e1987 100644
--- a/cycode/cli/code_scanner.py
+++ b/cycode/cli/code_scanner.py
@@ -90,7 +90,7 @@ def scan_repository(context: click.Context, path: str, branch: str) -> None:
perform_pre_scan_documents_actions(context, scan_type, documents_to_scan, is_git_diff=False)
logger.debug('Found all relevant files for scanning %s', {'path': path, 'branch': branch})
- return scan_documents(
+ scan_documents(
context, documents_to_scan, is_git_diff=False, scan_parameters=get_scan_parameters(context, path)
)
except Exception as e:
@@ -420,6 +420,16 @@ def scan_documents(
) -> None:
progress_bar = context.obj['progress_bar']
+ if not documents_to_scan:
+ progress_bar.stop()
+ ConsolePrinter(context).print_error(
+ CliError(
+ code='no_relevant_files',
+ message='Error: The scan could not be completed - relevant files to scan are not found.',
+ )
+ )
+ return
+
scan_batch_thread_func = _get_scan_documents_thread_func(context, is_git_diff, is_commit_range, scan_parameters)
errors, local_scan_results = run_parallel_batched_scan(
scan_batch_thread_func, documents_to_scan, progress_bar=progress_bar
@@ -430,25 +440,7 @@ def scan_documents(
progress_bar.stop()
set_issue_detected_by_scan_results(context, local_scan_results)
- print_results(context, local_scan_results)
-
- if not errors:
- return
-
- if context.obj['output'] == 'json':
- # TODO(MarshalX): we can't just print JSON formatted errors here
- # because we should return only one root json structure per scan
- # could be added later to "print_results" function if we wish to display detailed errors in UI
- return
-
- click.secho(
- 'Unfortunately, Cycode was unable to complete the full scan. '
- 'Please note that not all results may be available:',
- fg='red',
- )
- for scan_id, error in errors.items():
- click.echo(f'- {scan_id}: ', nl=False)
- ConsolePrinter(context).print_error(error)
+ print_results(context, local_scan_results, errors)
def scan_commit_range_documents(
@@ -506,6 +498,7 @@ def scan_commit_range_documents(
progress_bar.update(ProgressBarSection.GENERATE_REPORT)
progress_bar.stop()
+ # errors will be handled with try-except block; printing will not occur on errors
print_results(context, [local_scan_result])
scan_completed = True
@@ -693,9 +686,11 @@ def print_debug_scan_details(scan_details_response: 'ScanDetailsResponse') -> No
logger.debug(f'Scan message: {scan_details_response.message}')
-def print_results(context: click.Context, local_scan_results: List[LocalScanResult]) -> None:
+def print_results(
+ context: click.Context, local_scan_results: List[LocalScanResult], errors: Optional[Dict[str, 'CliError']] = None
+) -> None:
printer = ConsolePrinter(context)
- printer.print_scan_results(local_scan_results)
+ printer.print_scan_results(local_scan_results, errors)
def get_document_detections(
diff --git a/cycode/cli/printers/console_printer.py b/cycode/cli/printers/console_printer.py
index f0bccadf..d9ae56df 100644
--- a/cycode/cli/printers/console_printer.py
+++ b/cycode/cli/printers/console_printer.py
@@ -1,4 +1,4 @@
-from typing import TYPE_CHECKING, ClassVar, Dict, List
+from typing import TYPE_CHECKING, ClassVar, Dict, List, Optional
import click
@@ -33,9 +33,11 @@ def __init__(self, context: click.Context) -> None:
if self._printer_class is None:
raise CycodeError(f'"{self.output_type}" output type is not supported.')
- def print_scan_results(self, local_scan_results: List['LocalScanResult']) -> None:
+ def print_scan_results(
+ self, local_scan_results: List['LocalScanResult'], errors: Optional[Dict[str, 'CliError']] = None
+ ) -> None:
printer = self._get_scan_printer()
- printer.print_scan_results(local_scan_results)
+ printer.print_scan_results(local_scan_results, errors)
def _get_scan_printer(self) -> 'PrinterBase':
printer_class = self._printer_class
diff --git a/cycode/cli/printers/json_printer.py b/cycode/cli/printers/json_printer.py
index 2f048ae7..89b903ad 100644
--- a/cycode/cli/printers/json_printer.py
+++ b/cycode/cli/printers/json_printer.py
@@ -1,5 +1,5 @@
import json
-from typing import TYPE_CHECKING, List
+from typing import TYPE_CHECKING, Dict, List, Optional
import click
@@ -15,14 +15,16 @@ class JsonPrinter(PrinterBase):
def print_result(self, result: CliResult) -> None:
result = {'result': result.success, 'message': result.message}
- click.secho(self.get_data_json(result))
+ click.echo(self.get_data_json(result))
def print_error(self, error: CliError) -> None:
result = {'error': error.code, 'message': error.message}
- click.secho(self.get_data_json(result))
+ click.echo(self.get_data_json(result))
- def print_scan_results(self, local_scan_results: List['LocalScanResult']) -> None:
+ def print_scan_results(
+ self, local_scan_results: List['LocalScanResult'], errors: Optional[Dict[str, 'CliError']] = None
+ ) -> None:
detections = []
for local_scan_result in local_scan_results:
for document_detections in local_scan_result.document_detections:
@@ -30,12 +32,18 @@ def print_scan_results(self, local_scan_results: List['LocalScanResult']) -> Non
detections_dict = DetectionSchema(many=True).dump(detections)
- click.secho(self._get_json_scan_result(detections_dict))
+ inlined_errors = []
+ if errors:
+ # FIXME(MarshalX): we don't care about scan IDs in JSON output due to clumsy JSON root structure
+ inlined_errors = [err._asdict() for err in errors.values()]
- def _get_json_scan_result(self, detections: dict) -> str:
+ click.echo(self._get_json_scan_result(detections_dict, inlined_errors))
+
+ def _get_json_scan_result(self, detections: dict, errors: List[dict]) -> str:
result = {
'scan_id': 'DEPRECATED', # FIXME(MarshalX): we need change JSON struct to support multiple scan results
'detections': detections,
+ 'errors': errors,
}
return self.get_data_json(result)
diff --git a/cycode/cli/printers/printer_base.py b/cycode/cli/printers/printer_base.py
index 69802e54..e1fbfa51 100644
--- a/cycode/cli/printers/printer_base.py
+++ b/cycode/cli/printers/printer_base.py
@@ -1,5 +1,5 @@
from abc import ABC, abstractmethod
-from typing import TYPE_CHECKING, List
+from typing import TYPE_CHECKING, Dict, List, Optional
import click
@@ -18,7 +18,9 @@ def __init__(self, context: click.Context) -> None:
self.context = context
@abstractmethod
- def print_scan_results(self, local_scan_results: List['LocalScanResult']) -> None:
+ def print_scan_results(
+ self, local_scan_results: List['LocalScanResult'], errors: Optional[Dict[str, 'CliError']] = None
+ ) -> None:
pass
@abstractmethod
diff --git a/cycode/cli/printers/tables/table_printer_base.py b/cycode/cli/printers/tables/table_printer_base.py
index ab444c58..10a94e55 100644
--- a/cycode/cli/printers/tables/table_printer_base.py
+++ b/cycode/cli/printers/tables/table_printer_base.py
@@ -1,5 +1,5 @@
import abc
-from typing import TYPE_CHECKING, List
+from typing import TYPE_CHECKING, Dict, List, Optional
import click
@@ -24,13 +24,27 @@ def print_result(self, result: CliResult) -> None:
def print_error(self, error: CliError) -> None:
TextPrinter(self.context).print_error(error)
- def print_scan_results(self, local_scan_results: List['LocalScanResult']) -> None:
- if all(result.issue_detected == 0 for result in local_scan_results):
+ def print_scan_results(
+ self, local_scan_results: List['LocalScanResult'], errors: Optional[Dict[str, 'CliError']] = None
+ ) -> None:
+ if not errors and all(result.issue_detected == 0 for result in local_scan_results):
click.secho('Good job! No issues were found!!! 👏👏👏', fg=self.GREEN_COLOR_NAME)
return
self._print_results(local_scan_results)
+ if not errors:
+ return
+
+ click.secho(
+ 'Unfortunately, Cycode was unable to complete the full scan. '
+ 'Please note that not all results may be available:',
+ fg='red',
+ )
+ for scan_id, error in errors.items():
+ click.echo(f'- {scan_id}: ', nl=False)
+ self.print_error(error)
+
def _is_git_repository(self) -> bool:
return self.context.obj.get('remote_url') is not None
@@ -40,4 +54,5 @@ def _print_results(self, local_scan_results: List['LocalScanResult']) -> None:
@staticmethod
def _print_table(table: 'Table') -> None:
- click.echo(table.get_table().draw())
+ if table.get_rows():
+ click.echo(table.get_table().draw())
diff --git a/cycode/cli/printers/text_printer.py b/cycode/cli/printers/text_printer.py
index 0390210a..821e755f 100644
--- a/cycode/cli/printers/text_printer.py
+++ b/cycode/cli/printers/text_printer.py
@@ -1,5 +1,5 @@
import math
-from typing import TYPE_CHECKING, List, Optional
+from typing import TYPE_CHECKING, Dict, List, Optional
import click
@@ -30,8 +30,10 @@ def print_result(self, result: CliResult) -> None:
def print_error(self, error: CliError) -> None:
click.secho(error.message, fg=self.RED_COLOR_NAME)
- def print_scan_results(self, local_scan_results: List['LocalScanResult']) -> None:
- if all(result.issue_detected == 0 for result in local_scan_results):
+ def print_scan_results(
+ self, local_scan_results: List['LocalScanResult'], errors: Optional[Dict[str, 'CliError']] = None
+ ) -> None:
+ if not errors and all(result.issue_detected == 0 for result in local_scan_results):
click.secho('Good job! No issues were found!!! 👏👏👏', fg=self.GREEN_COLOR_NAME)
return
@@ -41,6 +43,18 @@ def print_scan_results(self, local_scan_results: List['LocalScanResult']) -> Non
document_detections, local_scan_result.scan_id, local_scan_result.report_url
)
+ if not errors:
+ return
+
+ click.secho(
+ 'Unfortunately, Cycode was unable to complete the full scan. '
+ 'Please note that not all results may be available:',
+ fg='red',
+ )
+ for scan_id, error in errors.items():
+ click.echo(f'- {scan_id}: ', nl=False)
+ self.print_error(error)
+
def _print_document_detections(
self, document_detections: DocumentDetections, scan_id: str, report_url: Optional[str]
) -> None:
diff --git a/cycode/cli/utils/progress_bar.py b/cycode/cli/utils/progress_bar.py
index d22abf84..083d0715 100644
--- a/cycode/cli/utils/progress_bar.py
+++ b/cycode/cli/utils/progress_bar.py
@@ -146,6 +146,8 @@ def set_section_length(self, section: 'ProgressBarSection', length: int) -> None
if length == 0:
self._skip_section(section)
+ else:
+ self._maybe_update_current_section()
def _skip_section(self, section: 'ProgressBarSection') -> None:
self._progress_bar.update(_get_section_length(section))
From 78e8763a2e508798a557744e53b70bf7ecb568f0 Mon Sep 17 00:00:00 2001
From: Ilya Siamionau
Date: Fri, 28 Jul 2023 22:06:57 +0400
Subject: [PATCH 023/257] CM-24629 - Lock urllib3 v1 (#152)
update certifi to fix CVE-2023-37920
---
poetry.lock | 23 +++++++++++------------
pyproject.toml | 1 +
2 files changed, 12 insertions(+), 12 deletions(-)
diff --git a/poetry.lock b/poetry.lock
index b5584637..e4137a58 100644
--- a/poetry.lock
+++ b/poetry.lock
@@ -91,13 +91,13 @@ uvloop = ["uvloop (>=0.15.2)"]
[[package]]
name = "certifi"
-version = "2023.5.7"
+version = "2023.7.22"
description = "Python package for providing Mozilla's CA Bundle."
optional = false
python-versions = ">=3.6"
files = [
- {file = "certifi-2023.5.7-py3-none-any.whl", hash = "sha256:c6c2e98f5c7869efca1f8916fed228dd91539f9f1b444c314c06eef02980c716"},
- {file = "certifi-2023.5.7.tar.gz", hash = "sha256:0f0d56dc5a6ad56fd4ba36484d6cc34451e1c6548c61daad8c320169f91eddc7"},
+ {file = "certifi-2023.7.22-py3-none-any.whl", hash = "sha256:92d6037539857d8206b8f6ae472e8b77db8058fec5937a1ef3f54304089edbb9"},
+ {file = "certifi-2023.7.22.tar.gz", hash = "sha256:539cc1d13202e33ca466e88b2807e29f4c13049d6d87031a3c110744495cb082"},
]
[[package]]
@@ -872,20 +872,19 @@ files = [
[[package]]
name = "urllib3"
-version = "2.0.2"
+version = "1.26.16"
description = "HTTP library with thread-safe connection pooling, file post, and more."
optional = false
-python-versions = ">=3.7"
+python-versions = ">=2.7, !=3.0.*, !=3.1.*, !=3.2.*, !=3.3.*, !=3.4.*, !=3.5.*"
files = [
- {file = "urllib3-2.0.2-py3-none-any.whl", hash = "sha256:d055c2f9d38dc53c808f6fdc8eab7360b6fdbbde02340ed25cfbcd817c62469e"},
- {file = "urllib3-2.0.2.tar.gz", hash = "sha256:61717a1095d7e155cdb737ac7bb2f4324a858a1e2e6466f6d03ff630ca68d3cc"},
+ {file = "urllib3-1.26.16-py2.py3-none-any.whl", hash = "sha256:8d36afa7616d8ab714608411b4a3b13e58f463aee519024578e062e141dce20f"},
+ {file = "urllib3-1.26.16.tar.gz", hash = "sha256:8f135f6502756bde6b2a9b28989df5fbe87c9970cecaa69041edcce7f0589b14"},
]
[package.extras]
-brotli = ["brotli (>=1.0.9)", "brotlicffi (>=0.8.0)"]
-secure = ["certifi", "cryptography (>=1.9)", "idna (>=2.0.0)", "pyopenssl (>=17.1.0)", "urllib3-secure-extra"]
-socks = ["pysocks (>=1.5.6,!=1.5.7,<2.0)"]
-zstd = ["zstandard (>=0.18.0)"]
+brotli = ["brotli (>=1.0.9)", "brotlicffi (>=0.8.0)", "brotlipy (>=0.6.0)"]
+secure = ["certifi", "cryptography (>=1.3.4)", "idna (>=2.0.0)", "ipaddress", "pyOpenSSL (>=0.14)", "urllib3-secure-extra"]
+socks = ["PySocks (>=1.5.6,!=1.5.7,<2.0)"]
[[package]]
name = "zipp"
@@ -905,4 +904,4 @@ testing = ["big-O", "flake8 (<5)", "jaraco.functools", "jaraco.itertools", "more
[metadata]
lock-version = "2.0"
python-versions = ">=3.7,<3.12"
-content-hash = "5cb535c853d7233ac226c8ea2e50ca05ee7243bfb81ce72f76e93be3f56d1e7f"
+content-hash = "ca732947ba4a2d16d4697a43b8c81c77cf2f9b73892ba7f8fa80c43703ec8b0b"
diff --git a/pyproject.toml b/pyproject.toml
index 4c093047..93fa2516 100644
--- a/pyproject.toml
+++ b/pyproject.toml
@@ -37,6 +37,7 @@ arrow = ">=0.17.0,<0.18.0"
binaryornot = ">=0.4.4,<0.5.0"
texttable = ">=1.6.7,<1.7.0"
requests = ">=2.24,<3.0"
+urllib3 = "1.26.16" # lock v1 to avoid issues with openssl and old Python versions (<3.9.11) on macOS
[tool.poetry.group.test.dependencies]
mock = ">=4.0.3,<4.1.0"
From 4c04a32df27573f6c791f7b8f627e88c3776016b Mon Sep 17 00:00:00 2001
From: EfratIsrael <139685962+EfratIsrael@users.noreply.github.com>
Date: Mon, 7 Aug 2023 13:19:49 +0300
Subject: [PATCH 024/257] CM-25773 - Support TF Plan scans (#153)
* CM-25773- initial commit
* lint fix
* remove new line
* add try-except
* change list to List
* key error exception handler
parser test
* prettier
* encoding
* fix path
* lint
* review fixing
* renaming + typo fixing
* remove redundant json load check
* change soft fail
* add json.loads wrapper
* lint
* remove constructor
* refactor iac parsing
* handle null after + add test
* Fix error handling
* Fix replacement of files
* fix iac doc manipulation
* revert iac manipultaion outside pre scan doc
* adding tests for different plans +
handle delete action list +
update readme
* fix readme
* fix readme
* fixing
* pr fixing
* pr fixing
* lint
* test fix
* add test for generate document
* lint
* update test
* typo fix
* move \n
---------
Co-authored-by: Ilya Siamionau
---
README.md | 31 +
cycode/cli/code_scanner.py | 67 +-
cycode/cli/exceptions/custom_exceptions.py | 9 +
cycode/cli/helpers/tf_content_generator.py | 49 +
cycode/cli/models.py | 12 +
cycode/cli/utils/path_utils.py | 17 +
tests/cli/helpers/__init__.py | 0
.../cli/helpers/test_tf_content_generator.py | 16 +
tests/cli/test_code_scanner.py | 62 +-
.../tfplan-create-example/tf_content.txt | 113 ++
.../tfplan-create-example/tfplan.json | 1072 +++++++++++
.../tfplan-destroy-example/tf_content.txt | 0
.../tfplan-destroy-example/tfplan.json | 1082 +++++++++++
.../tfplan-false-var/tf_content.txt | 14 +
.../tfplan-false-var/tfplan.json | 218 +++
.../tfplan-no-op-example/tf_content.txt | 122 ++
.../tfplan-no-op-example/tfplan.json | 1634 +++++++++++++++++
.../tfplan-null-example/tf_content.txt | 4 +
.../tfplan-null-example/tfplan.json | 75 +
.../tfplan-update-example/tf_content.txt | 34 +
.../tfplan-update-example/tfplan.json | 736 ++++++++
21 files changed, 5355 insertions(+), 12 deletions(-)
create mode 100644 cycode/cli/helpers/tf_content_generator.py
create mode 100644 tests/cli/helpers/__init__.py
create mode 100644 tests/cli/helpers/test_tf_content_generator.py
create mode 100644 tests/test_files/tf_content_generator_files/tfplan-create-example/tf_content.txt
create mode 100644 tests/test_files/tf_content_generator_files/tfplan-create-example/tfplan.json
create mode 100644 tests/test_files/tf_content_generator_files/tfplan-destroy-example/tf_content.txt
create mode 100644 tests/test_files/tf_content_generator_files/tfplan-destroy-example/tfplan.json
create mode 100644 tests/test_files/tf_content_generator_files/tfplan-false-var/tf_content.txt
create mode 100644 tests/test_files/tf_content_generator_files/tfplan-false-var/tfplan.json
create mode 100644 tests/test_files/tf_content_generator_files/tfplan-no-op-example/tf_content.txt
create mode 100644 tests/test_files/tf_content_generator_files/tfplan-no-op-example/tfplan.json
create mode 100644 tests/test_files/tf_content_generator_files/tfplan-null-example/tf_content.txt
create mode 100644 tests/test_files/tf_content_generator_files/tfplan-null-example/tfplan.json
create mode 100644 tests/test_files/tf_content_generator_files/tfplan-update-example/tf_content.txt
create mode 100644 tests/test_files/tf_content_generator_files/tfplan-update-example/tfplan.json
diff --git a/README.md b/README.md
index 71b885e1..4e3da50a 100644
--- a/README.md
+++ b/README.md
@@ -25,6 +25,7 @@ This guide will guide you through both installation and usage.
1. [License Compliance Option](#license-compliance-option)
2. [Severity Threshold](#severity-threshold)
5. [Path Scan](#path-scan)
+ 1. [Terraform Plan Scan](#terraform-plan-scan)
6. [Commit History Scan](#commit-history-scan)
1. [Commit Range Option](#commit-range-option)
7. [Pre-Commit Scan](#pre-commit-scan)
@@ -421,6 +422,36 @@ For example, consider a scenario in which you want to scan the directory located
`cycode scan path ~/home/git/codebase`
+
+### Terraform Plan Scan
+
+Cycode CLI supports Terraform plan scanning (supporting Terraform 0.12 and later)
+
+Terraform plan file must be in JSON format (having `.json` extension)
+
+
+_How to generate a Terraform plan from Terraform configuration file?_
+
+1. Initialize a working directory that contains Terraform configuration file:
+
+ `terraform init`
+
+
+2. Create Terraform execution plan and save the binary output:
+
+ `terraform plan -out={tfplan_output}`
+
+
+3. Convert the binary output file into readable JSON:
+
+ `terraform show -json {tfplan_output} > {tfplan}.json`
+
+
+4. Scan your `{tfplan}.json` with Cycode CLI:
+
+ `cycode scan -t iac path ~/PATH/TO/YOUR/{tfplan}.json`
+
+
## Commit History Scan
A commit history scan is limited to a local repository’s previous commits, focused on finding any secrets within the commit history, instead of examining the repository’s current state.
diff --git a/cycode/cli/code_scanner.py b/cycode/cli/code_scanner.py
index 7c8e1987..978b4240 100644
--- a/cycode/cli/code_scanner.py
+++ b/cycode/cli/code_scanner.py
@@ -16,18 +16,20 @@
from cycode.cli.ci_integrations import get_commit_range
from cycode.cli.config import configuration_manager
from cycode.cli.exceptions import custom_exceptions
-from cycode.cli.helpers import sca_code_scanner
+from cycode.cli.helpers import sca_code_scanner, tf_content_generator
from cycode.cli.models import CliError, CliErrors, Document, DocumentDetections, LocalScanResult, Severity
from cycode.cli.printers import ConsolePrinter
from cycode.cli.user_settings.config_file_manager import ConfigFileManager
from cycode.cli.utils import scan_utils
from cycode.cli.utils.path_utils import (
+ change_filename_extension,
get_file_content,
get_file_size,
get_path_by_os,
get_relevant_files_in_path,
is_binary_file,
is_sub_path,
+ load_json,
)
from cycode.cli.utils.progress_bar import ProgressBarSection
from cycode.cli.utils.progress_bar import logger as progress_bar_logger
@@ -328,18 +330,22 @@ def scan_disk_files(context: click.Context, path: str, files_to_scan: List[str])
is_git_diff = False
- documents: List[Document] = []
- for file in files_to_scan:
- progress_bar.update(ProgressBarSection.PREPARE_LOCAL_FILES)
+ try:
+ documents: List[Document] = []
+ for file in files_to_scan:
+ progress_bar.update(ProgressBarSection.PREPARE_LOCAL_FILES)
- content = get_file_content(file)
- if not content:
- continue
+ content = get_file_content(file)
+ if not content:
+ continue
+
+ documents.append(_generate_document(file, scan_type, content, is_git_diff))
- documents.append(Document(file, content, is_git_diff))
+ perform_pre_scan_documents_actions(context, scan_type, documents, is_git_diff)
+ scan_documents(context, documents, is_git_diff=is_git_diff, scan_parameters=scan_parameters)
- perform_pre_scan_documents_actions(context, scan_type, documents, is_git_diff)
- scan_documents(context, documents, is_git_diff=is_git_diff, scan_parameters=scan_parameters)
+ except Exception as e:
+ _handle_exception(context, e)
def set_issue_detected_by_scan_results(context: click.Context, scan_results: List[LocalScanResult]) -> None:
@@ -574,7 +580,7 @@ def perform_pre_scan_documents_actions(
context: click.Context, scan_type: str, documents_to_scan: List[Document], is_git_diff: bool = False
) -> None:
if scan_type == consts.SCA_SCAN_TYPE:
- logger.debug('Perform pre scan document actions')
+ logger.debug('Perform pre scan document add_dependencies_tree_document action')
sca_code_scanner.add_dependencies_tree_document(context, documents_to_scan, is_git_diff)
@@ -1099,6 +1105,37 @@ def _is_file_extension_supported(scan_type: str, filename: str) -> bool:
return not filename.endswith(consts.SECRET_SCAN_FILE_EXTENSIONS_TO_IGNORE)
+def _generate_document(file: str, scan_type: str, content: str, is_git_diff: bool) -> Document:
+ if _is_iac(scan_type) and _is_tfplan_file(file, content):
+ return _handle_tfplan_file(file, content, is_git_diff)
+ return Document(file, content, is_git_diff)
+
+
+def _handle_tfplan_file(file: str, content: str, is_git_diff: bool) -> Document:
+ document_name = _generate_tfplan_document_name(file)
+ tf_content = tf_content_generator.generate_tf_content_from_tfplan(file, content)
+ return Document(document_name, tf_content, is_git_diff)
+
+
+def _generate_tfplan_document_name(path: str) -> str:
+ document_name = change_filename_extension(path, 'tf')
+ timestamp = int(time.time())
+ return f'{timestamp}-{document_name}'
+
+
+def _is_iac(scan_type: str) -> bool:
+ return scan_type == consts.INFRA_CONFIGURATION_SCAN_TYPE
+
+
+def _is_tfplan_file(file: str, content: str) -> bool:
+ if not file.endswith('.json'):
+ return False
+ tf_plan = load_json(content)
+ if not isinstance(tf_plan, dict):
+ return False
+ return 'resource_changes' in tf_plan
+
+
def _does_file_exceed_max_size_limit(filename: str) -> bool:
return get_file_size(filename) > consts.FILE_MAX_SIZE_LIMIT_IN_BYTES
@@ -1157,6 +1194,14 @@ def _handle_exception(context: click.Context, e: Exception, *, return_exception:
'Please try ignoring irrelevant paths using the `cycode ignore --by-path` command '
'and execute the scan again',
),
+ custom_exceptions.TfplanKeyError: CliError(
+ soft_fail=True,
+ code='key_error',
+ message=f'\n{e!s}\n'
+ 'A crucial field is missing in your terraform plan file. '
+ 'Please make sure that your file is well formed '
+ 'and execute the scan again',
+ ),
InvalidGitRepositoryError: CliError(
soft_fail=False,
code='invalid_git_error',
diff --git a/cycode/cli/exceptions/custom_exceptions.py b/cycode/cli/exceptions/custom_exceptions.py
index 4806e17c..ea98a0aa 100644
--- a/cycode/cli/exceptions/custom_exceptions.py
+++ b/cycode/cli/exceptions/custom_exceptions.py
@@ -55,3 +55,12 @@ def __init__(self, error_message: str) -> None:
def __str__(self) -> str:
return f'Something went wrong during the authentication process, error message: {self.error_message}'
+
+
+class TfplanKeyError(CycodeError):
+ def __init__(self, file_path: str) -> None:
+ self.file_path = file_path
+ super().__init__()
+
+ def __str__(self) -> str:
+ return f'Error occurred while parsing terraform plan file. Path: {self.file_path}'
diff --git a/cycode/cli/helpers/tf_content_generator.py b/cycode/cli/helpers/tf_content_generator.py
new file mode 100644
index 00000000..7594a96f
--- /dev/null
+++ b/cycode/cli/helpers/tf_content_generator.py
@@ -0,0 +1,49 @@
+import json
+from typing import List
+
+from cycode.cli.exceptions.custom_exceptions import TfplanKeyError
+from cycode.cli.models import ResourceChange
+from cycode.cli.utils.path_utils import load_json
+
+ACTIONS_TO_OMIT_RESOURCE = ['delete']
+
+
+def generate_tf_content_from_tfplan(filename: str, tfplan: str) -> str:
+ planned_resources = _extract_resources(tfplan, filename)
+ return _generate_tf_content(planned_resources)
+
+
+def _generate_tf_content(resource_changes: List[ResourceChange]) -> str:
+ tf_content = ''
+ for resource_change in resource_changes:
+ if not any(item in resource_change.actions for item in ACTIONS_TO_OMIT_RESOURCE):
+ tf_content += _generate_resource_content(resource_change)
+ return tf_content
+
+
+def _generate_resource_content(resource_change: ResourceChange) -> str:
+ resource_content = f'resource "{resource_change.resource_type}" "{resource_change.name}" {{\n'
+ if resource_change.values is not None:
+ for key, value in resource_change.values.items():
+ resource_content += f' {key} = {json.dumps(value)}\n'
+ resource_content += '}\n\n'
+ return resource_content
+
+
+def _extract_resources(tfplan: str, filename: str) -> List[ResourceChange]:
+ tfplan_json = load_json(tfplan)
+ resources: List[ResourceChange] = []
+ try:
+ resource_changes = tfplan_json['resource_changes']
+ for resource_change in resource_changes:
+ resources.append(
+ ResourceChange(
+ resource_type=resource_change['type'],
+ name=resource_change['name'],
+ actions=resource_change['change']['actions'],
+ values=resource_change['change']['after'],
+ )
+ )
+ except (KeyError, TypeError) as e:
+ raise TfplanKeyError(filename) from e
+ return resources
diff --git a/cycode/cli/models.py b/cycode/cli/models.py
index 05713934..d60801df 100644
--- a/cycode/cli/models.py
+++ b/cycode/cli/models.py
@@ -1,3 +1,4 @@
+from dataclasses import dataclass
from enum import Enum
from typing import Dict, List, NamedTuple, Optional, Type
@@ -63,3 +64,14 @@ class LocalScanResult(NamedTuple):
issue_detected: bool
detections_count: int
relevant_detections_count: int
+
+
+@dataclass
+class ResourceChange:
+ resource_type: str
+ name: str
+ actions: List[str]
+ values: Dict[str, str]
+
+ def __repr__(self) -> str:
+ return f'resource_type: {self.resource_type}, name: {self.name}'
diff --git a/cycode/cli/utils/path_utils.py b/cycode/cli/utils/path_utils.py
index ef758fed..ad5ce94e 100644
--- a/cycode/cli/utils/path_utils.py
+++ b/cycode/cli/utils/path_utils.py
@@ -1,3 +1,4 @@
+import json
import os
from functools import lru_cache
from typing import AnyStr, Iterable, List, Optional
@@ -71,6 +72,10 @@ def get_file_dir(path: str) -> str:
return os.path.dirname(path)
+def get_immediate_subdirectories(path: str) -> List[str]:
+ return [f.name for f in os.scandir(path) if f.is_dir()]
+
+
def join_paths(path: str, filename: str) -> str:
return os.path.join(path, filename)
@@ -81,3 +86,15 @@ def get_file_content(file_path: str) -> Optional[AnyStr]:
return f.read()
except (FileNotFoundError, UnicodeDecodeError):
return None
+
+
+def load_json(txt: str) -> Optional[dict]:
+ try:
+ return json.loads(txt)
+ except json.JSONDecodeError:
+ return None
+
+
+def change_filename_extension(filename: str, extension: str) -> str:
+ base_name, _ = os.path.splitext(filename)
+ return f'{base_name}.{extension}'
diff --git a/tests/cli/helpers/__init__.py b/tests/cli/helpers/__init__.py
new file mode 100644
index 00000000..e69de29b
diff --git a/tests/cli/helpers/test_tf_content_generator.py b/tests/cli/helpers/test_tf_content_generator.py
new file mode 100644
index 00000000..ae19b2f6
--- /dev/null
+++ b/tests/cli/helpers/test_tf_content_generator.py
@@ -0,0 +1,16 @@
+import os
+
+from cycode.cli.helpers import tf_content_generator
+from cycode.cli.utils.path_utils import get_file_content, get_immediate_subdirectories
+from tests.conftest import TEST_FILES_PATH
+
+_PATH_TO_EXAMPLES = os.path.join(TEST_FILES_PATH, 'tf_content_generator_files')
+
+
+def test_generate_tf_content_from_tfplan() -> None:
+ examples_directories = get_immediate_subdirectories(_PATH_TO_EXAMPLES)
+ for example in examples_directories:
+ tfplan_content = get_file_content(os.path.join(_PATH_TO_EXAMPLES, example, 'tfplan.json'))
+ tf_expected_content = get_file_content(os.path.join(_PATH_TO_EXAMPLES, example, 'tf_content.txt'))
+ tf_content = tf_content_generator.generate_tf_content_from_tfplan(example, tfplan_content)
+ assert tf_content == tf_expected_content
diff --git a/tests/cli/test_code_scanner.py b/tests/cli/test_code_scanner.py
index 0bd02845..b715e9c6 100644
--- a/tests/cli/test_code_scanner.py
+++ b/tests/cli/test_code_scanner.py
@@ -7,8 +7,10 @@
from git import InvalidGitRepositoryError
from requests import Response
-from cycode.cli.code_scanner import _handle_exception, _is_file_relevant_for_sca_scan
+from cycode.cli import consts
+from cycode.cli.code_scanner import _generate_document, _handle_exception, _is_file_relevant_for_sca_scan
from cycode.cli.exceptions import custom_exceptions
+from cycode.cli.models import Document
if TYPE_CHECKING:
from _pytest.monkeypatch import MonkeyPatch
@@ -26,6 +28,7 @@ def ctx() -> click.Context:
(custom_exceptions.ScanAsyncError('msg'), True),
(custom_exceptions.HttpUnauthorizedError('msg', Response()), True),
(custom_exceptions.ZipTooLargeError(1000), True),
+ (custom_exceptions.TfplanKeyError('msg'), True),
(InvalidGitRepositoryError(), None),
],
)
@@ -76,3 +79,60 @@ def test_is_file_relevant_for_sca_scan() -> None:
assert _is_file_relevant_for_sca_scan(path) is True
path = os.path.join('some_package', 'package.lock')
assert _is_file_relevant_for_sca_scan(path) is True
+
+
+def test_generate_document() -> None:
+ is_git_diff = False
+
+ path = 'path/to/nowhere.txt'
+ content = 'nothing important here'
+
+ non_iac_document = Document(path, content, is_git_diff)
+ generated_document = _generate_document(path, consts.SCA_SCAN_TYPE, content, is_git_diff)
+
+ assert non_iac_document.path == generated_document.path
+ assert non_iac_document.content == generated_document.content
+ assert non_iac_document.is_git_diff_format == generated_document.is_git_diff_format
+
+ path = 'path/to/nowhere.tf'
+ content = """provider "aws" {
+ profile = "chili"
+ region = "us-east-1"
+ }
+
+ resource "aws_s3_bucket" "chili-env-var-test" {
+ bucket = "chili-env-var-test"
+ }"""
+
+ iac_document = Document(path, content, is_git_diff)
+ generated_document = _generate_document(path, consts.INFRA_CONFIGURATION_SCAN_TYPE, content, is_git_diff)
+ assert iac_document.path == generated_document.path
+ assert iac_document.content == generated_document.content
+ assert iac_document.is_git_diff_format == generated_document.is_git_diff_format
+
+ content = """
+ {
+ "resource_changes":[
+ {
+ "type":"aws_s3_bucket_public_access_block",
+ "name":"efrat-env-var-test",
+ "change":{
+ "actions":[
+ "create"
+ ],
+ "after":{
+ "block_public_acls":false,
+ "block_public_policy":true,
+ "ignore_public_acls":false,
+ "restrict_public_buckets":true
+ }
+ }
+ ]
+ }
+ """
+
+ generated_tfplan_document = _generate_document(path, consts.INFRA_CONFIGURATION_SCAN_TYPE, content, is_git_diff)
+
+ assert type(generated_tfplan_document) == Document
+ assert generated_tfplan_document.path.endswith('.tf')
+ assert generated_tfplan_document.is_git_diff_format == is_git_diff
diff --git a/tests/test_files/tf_content_generator_files/tfplan-create-example/tf_content.txt b/tests/test_files/tf_content_generator_files/tfplan-create-example/tf_content.txt
new file mode 100644
index 00000000..4021097e
--- /dev/null
+++ b/tests/test_files/tf_content_generator_files/tfplan-create-example/tf_content.txt
@@ -0,0 +1,113 @@
+resource "aws_codebuild_project" "terra_ci" {
+ artifacts = [{"artifact_identifier": null, "encryption_disabled": false, "location": "terra-ci-artifacts-eu-west-1-000002", "name": null, "namespace_type": null, "override_artifact_name": false, "packaging": null, "path": null, "type": "S3"}]
+ badge_enabled = false
+ build_timeout = 10
+ cache = []
+ description = "Deploy environment configuration"
+ environment = [{"certificate": null, "compute_type": "BUILD_GENERAL1_SMALL", "environment_variable": [], "image": "aws/codebuild/amazonlinux2-x86_64-standard:2.0", "image_pull_credentials_type": "CODEBUILD", "privileged_mode": false, "registry_credential": [], "type": "LINUX_CONTAINER"}]
+ logs_config = [{"cloudwatch_logs": [{"group_name": null, "status": "ENABLED", "stream_name": null}], "s3_logs": [{"encryption_disabled": false, "location": null, "status": "DISABLED"}]}]
+ name = "terra-ci-runner"
+ queued_timeout = 480
+ secondary_artifacts = []
+ secondary_sources = []
+ source = [{"auth": [], "buildspec": "version: 0.2\nphases:\n install:\n commands:\n - make install_tools\n build:\n commands:\n - make plan_local resource=$TERRA_CI_RESOURCE\nartifacts:\n files:\n - ./tfplan\n name: $TERRA_CI_BUILD_NAME\n\n", "git_clone_depth": 1, "git_submodules_config": [], "insecure_ssl": false, "location": "https://github.com/p0tr3c-terraform/terra-ci-single-account.git", "report_build_status": false, "type": "GITHUB"}]
+ source_version = null
+ tags = null
+ vpc_config = []
+}
+
+resource "aws_iam_role" "terra_ci_job" {
+ assume_role_policy = "{\n \"Version\": \"2012-10-17\",\n \"Statement\": [\n {\n \"Effect\": \"Allow\",\n \"Principal\": {\n \"Service\": \"codebuild.amazonaws.com\"\n },\n \"Action\": \"sts:AssumeRole\"\n }\n ]\n}\n"
+ description = null
+ force_detach_policies = false
+ max_session_duration = 3600
+ name = "terra_ci_job"
+ name_prefix = null
+ path = "/"
+ permissions_boundary = null
+ tags = null
+}
+
+resource "aws_iam_role" "terra_ci_runner" {
+ assume_role_policy = "{\n \"Version\": \"2012-10-17\",\n \"Statement\": [\n {\n \"Effect\": \"Allow\",\n \"Principal\": {\n \"Service\": \"states.amazonaws.com\"\n },\n \"Action\": \"sts:AssumeRole\"\n }\n ]\n}\n"
+ description = null
+ force_detach_policies = false
+ max_session_duration = 3600
+ name = "terra_ci_runner"
+ name_prefix = null
+ path = "/"
+ permissions_boundary = null
+ tags = null
+}
+
+resource "aws_iam_role_policy" "terra_ci_job" {
+ name_prefix = null
+ role = "terra_ci_job"
+}
+
+resource "aws_iam_role_policy" "terra_ci_runner" {
+ name_prefix = null
+ role = "terra_ci_runner"
+}
+
+resource "aws_iam_role_policy_attachment" "terra_ci_job_ecr_access" {
+ policy_arn = "arn:aws:iam::aws:policy/AmazonEC2ContainerRegistryPowerUser"
+ role = "terra_ci_job"
+}
+
+resource "aws_s3_bucket" "terra_ci" {
+ acl = "private"
+ bucket = "terra-ci-artifacts-eu-west-1-000002"
+ bucket_prefix = null
+ cors_rule = []
+ force_destroy = false
+ grant = []
+ lifecycle_rule = []
+ logging = []
+ object_lock_configuration = []
+ policy = null
+ replication_configuration = []
+ server_side_encryption_configuration = [{"rule": [{"apply_server_side_encryption_by_default": [{"kms_master_key_id": null, "sse_algorithm": "aws:kms"}], "bucket_key_enabled": false}]}]
+ tags = null
+ website = []
+}
+
+resource "aws_sfn_state_machine" "terra_ci_runner" {
+ definition = "{\n \"Comment\": \"Run Terragrunt Jobs\",\n \"StartAt\": \"OnBranch?\",\n \"States\": {\n \"OnBranch?\": {\n \"Type\": \"Choice\",\n \"Choices\": [\n {\n \"Variable\": \"$.build.sourceversion\",\n \"IsPresent\": true,\n \"Next\": \"PlanBranch\"\n }\n ],\n \"Default\": \"Plan\"\n },\n \"Plan\": {\n \"Type\": \"Task\",\n \"Resource\": \"arn:aws:states:::codebuild:startBuild.sync\",\n \"Parameters\": {\n \"ProjectName\": \"terra-ci-runner\",\n \"EnvironmentVariablesOverride\": [\n {\n \"Name\": \"TERRA_CI_BUILD_NAME\",\n \"Value.$\": \"$$.Execution.Name\"\n },\n {\n \"Name\": \"TERRA_CI_RESOURCE\",\n \"Value.$\": \"$.build.environment.terra_ci_resource\"\n }\n ]\n },\n \"End\": true\n },\n \"PlanBranch\": {\n \"Type\": \"Task\",\n \"Resource\": \"arn:aws:states:::codebuild:startBuild.sync\",\n \"Parameters\": {\n \"ProjectName\": \"terra-ci-runner\",\n \"SourceVersion.$\": \"$.build.sourceversion\",\n \"EnvironmentVariablesOverride\": [\n {\n \"Name\": \"TERRA_CI_RESOURCE\",\n \"Value.$\": \"$.build.environment.terra_ci_resource\"\n }\n ]\n },\n \"End\": true\n }\n }\n}\n"
+ name = "terra-ci-runner"
+ tags = null
+ type = "STANDARD"
+}
+
+resource "aws_route" "private" {
+ carrier_gateway_id = null
+ destination_cidr_block = "172.25.16.0/20"
+ destination_ipv6_cidr_block = null
+ destination_prefix_list_id = null
+ egress_only_gateway_id = null
+ gateway_id = null
+ local_gateway_id = null
+ nat_gateway_id = null
+ route_table_id = "rtb-00cf8381520103cfb"
+ timeouts = null
+ transit_gateway_id = "tgw-0f68a4f2c58772c51"
+ vpc_endpoint_id = null
+ vpc_peering_connection_id = null
+}
+
+resource "aws_route" "private" {
+ carrier_gateway_id = null
+ destination_cidr_block = "172.25.16.0/20"
+ destination_ipv6_cidr_block = null
+ destination_prefix_list_id = null
+ egress_only_gateway_id = null
+ gateway_id = null
+ local_gateway_id = null
+ nat_gateway_id = null
+ route_table_id = "rtb-00cf8381520103cfb"
+ timeouts = null
+ transit_gateway_id = "tgw-0f68a4f2c58772c51"
+ vpc_endpoint_id = null
+ vpc_peering_connection_id = null
+}
+
diff --git a/tests/test_files/tf_content_generator_files/tfplan-create-example/tfplan.json b/tests/test_files/tf_content_generator_files/tfplan-create-example/tfplan.json
new file mode 100644
index 00000000..0b3a9296
--- /dev/null
+++ b/tests/test_files/tf_content_generator_files/tfplan-create-example/tfplan.json
@@ -0,0 +1,1072 @@
+{
+ "comment-for-reader": "THIS TERRAFORM FILE REPRESENTS A REAL TF-PLAN OUTPUT FOR NEWLY CREATED INFRASTRUCTRE",
+ "format_version": "0.1",
+ "terraform_version": "0.15.0",
+ "variables": {
+ "aws_region": {
+ "value": "eu-west-1"
+ },
+ "repo_url": {
+ "value": "https://github.com/p0tr3c-terraform/terra-ci-single-account.git"
+ },
+ "serial_number": {
+ "value": "000002"
+ }
+ },
+ "planned_values": {
+ "root_module": {
+ "resources": [
+ {
+ "address": "aws_codebuild_project.terra_ci",
+ "mode": "managed",
+ "type": "aws_codebuild_project",
+ "name": "terra_ci",
+ "provider_name": "registry.terraform.io/hashicorp/aws",
+ "schema_version": 0,
+ "values": {
+ "artifacts": [
+ {
+ "artifact_identifier": null,
+ "encryption_disabled": false,
+ "location": "terra-ci-artifacts-eu-west-1-000002",
+ "name": null,
+ "namespace_type": null,
+ "override_artifact_name": false,
+ "packaging": null,
+ "path": null,
+ "type": "S3"
+ }
+ ],
+ "badge_enabled": false,
+ "build_timeout": 10,
+ "cache": [],
+ "description": "Deploy environment configuration",
+ "environment": [
+ {
+ "certificate": null,
+ "compute_type": "BUILD_GENERAL1_SMALL",
+ "environment_variable": [],
+ "image": "aws/codebuild/amazonlinux2-x86_64-standard:2.0",
+ "image_pull_credentials_type": "CODEBUILD",
+ "privileged_mode": false,
+ "registry_credential": [],
+ "type": "LINUX_CONTAINER"
+ }
+ ],
+ "logs_config": [
+ {
+ "cloudwatch_logs": [
+ {
+ "group_name": null,
+ "status": "ENABLED",
+ "stream_name": null
+ }
+ ],
+ "s3_logs": [
+ {
+ "encryption_disabled": false,
+ "location": null,
+ "status": "DISABLED"
+ }
+ ]
+ }
+ ],
+ "name": "terra-ci-runner",
+ "queued_timeout": 480,
+ "secondary_artifacts": [],
+ "secondary_sources": [],
+ "source": [
+ {
+ "auth": [],
+ "buildspec": "version: 0.2\nphases:\n install:\n commands:\n - make install_tools\n build:\n commands:\n - make plan_local resource=$TERRA_CI_RESOURCE\nartifacts:\n files:\n - ./tfplan\n name: $TERRA_CI_BUILD_NAME\n\n",
+ "git_clone_depth": 1,
+ "git_submodules_config": [],
+ "insecure_ssl": false,
+ "location": "https://github.com/p0tr3c-terraform/terra-ci-single-account.git",
+ "report_build_status": false,
+ "type": "GITHUB"
+ }
+ ],
+ "source_version": null,
+ "tags": null,
+ "vpc_config": []
+ }
+ },
+ {
+ "address": "aws_iam_role.terra_ci_job",
+ "mode": "managed",
+ "type": "aws_iam_role",
+ "name": "terra_ci_job",
+ "provider_name": "registry.terraform.io/hashicorp/aws",
+ "schema_version": 0,
+ "values": {
+ "assume_role_policy": "{\n \"Version\": \"2012-10-17\",\n \"Statement\": [\n {\n \"Effect\": \"Allow\",\n \"Principal\": {\n \"Service\": \"codebuild.amazonaws.com\"\n },\n \"Action\": \"sts:AssumeRole\"\n }\n ]\n}\n",
+ "description": null,
+ "force_detach_policies": false,
+ "max_session_duration": 3600,
+ "name": "terra_ci_job",
+ "name_prefix": null,
+ "path": "/",
+ "permissions_boundary": null,
+ "tags": null
+ }
+ },
+ {
+ "address": "aws_iam_role.terra_ci_runner",
+ "mode": "managed",
+ "type": "aws_iam_role",
+ "name": "terra_ci_runner",
+ "provider_name": "registry.terraform.io/hashicorp/aws",
+ "schema_version": 0,
+ "values": {
+ "assume_role_policy": "{\n \"Version\": \"2012-10-17\",\n \"Statement\": [\n {\n \"Effect\": \"Allow\",\n \"Principal\": {\n \"Service\": \"states.amazonaws.com\"\n },\n \"Action\": \"sts:AssumeRole\"\n }\n ]\n}\n",
+ "description": null,
+ "force_detach_policies": false,
+ "max_session_duration": 3600,
+ "name": "terra_ci_runner",
+ "name_prefix": null,
+ "path": "/",
+ "permissions_boundary": null,
+ "tags": null
+ }
+ },
+ {
+ "address": "aws_iam_role_policy.terra_ci_job",
+ "mode": "managed",
+ "type": "aws_iam_role_policy",
+ "name": "terra_ci_job",
+ "provider_name": "registry.terraform.io/hashicorp/aws",
+ "schema_version": 0,
+ "values": {
+ "name_prefix": null,
+ "role": "terra_ci_job"
+ }
+ },
+ {
+ "address": "aws_iam_role_policy.terra_ci_runner",
+ "mode": "managed",
+ "type": "aws_iam_role_policy",
+ "name": "terra_ci_runner",
+ "provider_name": "registry.terraform.io/hashicorp/aws",
+ "schema_version": 0,
+ "values": {
+ "name_prefix": null,
+ "role": "terra_ci_runner"
+ }
+ },
+ {
+ "address": "aws_iam_role_policy_attachment.terra_ci_job_ecr_access",
+ "mode": "managed",
+ "type": "aws_iam_role_policy_attachment",
+ "name": "terra_ci_job_ecr_access",
+ "provider_name": "registry.terraform.io/hashicorp/aws",
+ "schema_version": 0,
+ "values": {
+ "policy_arn": "arn:aws:iam::aws:policy/AmazonEC2ContainerRegistryPowerUser",
+ "role": "terra_ci_job"
+ }
+ },
+ {
+ "address": "aws_s3_bucket.terra_ci",
+ "mode": "managed",
+ "type": "aws_s3_bucket",
+ "name": "terra_ci",
+ "provider_name": "registry.terraform.io/hashicorp/aws",
+ "schema_version": 0,
+ "values": {
+ "acl": "private",
+ "bucket": "terra-ci-artifacts-eu-west-1-000002",
+ "bucket_prefix": null,
+ "cors_rule": [],
+ "force_destroy": false,
+ "grant": [],
+ "lifecycle_rule": [],
+ "logging": [],
+ "object_lock_configuration": [],
+ "policy": null,
+ "replication_configuration": [],
+ "server_side_encryption_configuration": [
+ {
+ "rule": [
+ {
+ "apply_server_side_encryption_by_default": [
+ {
+ "kms_master_key_id": null,
+ "sse_algorithm": "aws:kms"
+ }
+ ],
+ "bucket_key_enabled": false
+ }
+ ]
+ }
+ ],
+ "tags": null,
+ "website": []
+ }
+ },
+ {
+ "address": "aws_sfn_state_machine.terra_ci_runner",
+ "mode": "managed",
+ "type": "aws_sfn_state_machine",
+ "name": "terra_ci_runner",
+ "provider_name": "registry.terraform.io/hashicorp/aws",
+ "schema_version": 0,
+ "values": {
+ "definition": "{\n \"Comment\": \"Run Terragrunt Jobs\",\n \"StartAt\": \"OnBranch?\",\n \"States\": {\n \"OnBranch?\": {\n \"Type\": \"Choice\",\n \"Choices\": [\n {\n \"Variable\": \"$.build.sourceversion\",\n \"IsPresent\": true,\n \"Next\": \"PlanBranch\"\n }\n ],\n \"Default\": \"Plan\"\n },\n \"Plan\": {\n \"Type\": \"Task\",\n \"Resource\": \"arn:aws:states:::codebuild:startBuild.sync\",\n \"Parameters\": {\n \"ProjectName\": \"terra-ci-runner\",\n \"EnvironmentVariablesOverride\": [\n {\n \"Name\": \"TERRA_CI_BUILD_NAME\",\n \"Value.$\": \"$$.Execution.Name\"\n },\n {\n \"Name\": \"TERRA_CI_RESOURCE\",\n \"Value.$\": \"$.build.environment.terra_ci_resource\"\n }\n ]\n },\n \"End\": true\n },\n \"PlanBranch\": {\n \"Type\": \"Task\",\n \"Resource\": \"arn:aws:states:::codebuild:startBuild.sync\",\n \"Parameters\": {\n \"ProjectName\": \"terra-ci-runner\",\n \"SourceVersion.$\": \"$.build.sourceversion\",\n \"EnvironmentVariablesOverride\": [\n {\n \"Name\": \"TERRA_CI_RESOURCE\",\n \"Value.$\": \"$.build.environment.terra_ci_resource\"\n }\n ]\n },\n \"End\": true\n }\n }\n}\n",
+ "name": "terra-ci-runner",
+ "tags": null,
+ "type": "STANDARD"
+ }
+ }
+ ]
+ }
+ },
+ "resource_changes": [
+ {
+ "address": "aws_codebuild_project.terra_ci",
+ "mode": "managed",
+ "type": "aws_codebuild_project",
+ "name": "terra_ci",
+ "provider_name": "registry.terraform.io/hashicorp/aws",
+ "change": {
+ "actions": [
+ "create"
+ ],
+ "before": null,
+ "after": {
+ "artifacts": [
+ {
+ "artifact_identifier": null,
+ "encryption_disabled": false,
+ "location": "terra-ci-artifacts-eu-west-1-000002",
+ "name": null,
+ "namespace_type": null,
+ "override_artifact_name": false,
+ "packaging": null,
+ "path": null,
+ "type": "S3"
+ }
+ ],
+ "badge_enabled": false,
+ "build_timeout": 10,
+ "cache": [],
+ "description": "Deploy environment configuration",
+ "environment": [
+ {
+ "certificate": null,
+ "compute_type": "BUILD_GENERAL1_SMALL",
+ "environment_variable": [],
+ "image": "aws/codebuild/amazonlinux2-x86_64-standard:2.0",
+ "image_pull_credentials_type": "CODEBUILD",
+ "privileged_mode": false,
+ "registry_credential": [],
+ "type": "LINUX_CONTAINER"
+ }
+ ],
+ "logs_config": [
+ {
+ "cloudwatch_logs": [
+ {
+ "group_name": null,
+ "status": "ENABLED",
+ "stream_name": null
+ }
+ ],
+ "s3_logs": [
+ {
+ "encryption_disabled": false,
+ "location": null,
+ "status": "DISABLED"
+ }
+ ]
+ }
+ ],
+ "name": "terra-ci-runner",
+ "queued_timeout": 480,
+ "secondary_artifacts": [],
+ "secondary_sources": [],
+ "source": [
+ {
+ "auth": [],
+ "buildspec": "version: 0.2\nphases:\n install:\n commands:\n - make install_tools\n build:\n commands:\n - make plan_local resource=$TERRA_CI_RESOURCE\nartifacts:\n files:\n - ./tfplan\n name: $TERRA_CI_BUILD_NAME\n\n",
+ "git_clone_depth": 1,
+ "git_submodules_config": [],
+ "insecure_ssl": false,
+ "location": "https://github.com/p0tr3c-terraform/terra-ci-single-account.git",
+ "report_build_status": false,
+ "type": "GITHUB"
+ }
+ ],
+ "source_version": null,
+ "tags": null,
+ "vpc_config": []
+ },
+ "after_unknown": {
+ "arn": true,
+ "artifacts": [
+ {}
+ ],
+ "badge_url": true,
+ "cache": [],
+ "encryption_key": true,
+ "environment": [
+ {
+ "environment_variable": [],
+ "registry_credential": []
+ }
+ ],
+ "id": true,
+ "logs_config": [
+ {
+ "cloudwatch_logs": [
+ {}
+ ],
+ "s3_logs": [
+ {}
+ ]
+ }
+ ],
+ "secondary_artifacts": [],
+ "secondary_sources": [],
+ "service_role": true,
+ "source": [
+ {
+ "auth": [],
+ "git_submodules_config": []
+ }
+ ],
+ "vpc_config": []
+ },
+ "before_sensitive": false,
+ "after_sensitive": {
+ "artifacts": [
+ {}
+ ],
+ "cache": [],
+ "environment": [
+ {
+ "environment_variable": [],
+ "registry_credential": []
+ }
+ ],
+ "logs_config": [
+ {
+ "cloudwatch_logs": [
+ {}
+ ],
+ "s3_logs": [
+ {}
+ ]
+ }
+ ],
+ "secondary_artifacts": [],
+ "secondary_sources": [],
+ "source": [
+ {
+ "auth": [],
+ "git_submodules_config": []
+ }
+ ],
+ "vpc_config": []
+ }
+ }
+ },
+ {
+ "address": "aws_iam_role.terra_ci_job",
+ "mode": "managed",
+ "type": "aws_iam_role",
+ "name": "terra_ci_job",
+ "provider_name": "registry.terraform.io/hashicorp/aws",
+ "change": {
+ "actions": [
+ "create"
+ ],
+ "before": null,
+ "after": {
+ "assume_role_policy": "{\n \"Version\": \"2012-10-17\",\n \"Statement\": [\n {\n \"Effect\": \"Allow\",\n \"Principal\": {\n \"Service\": \"codebuild.amazonaws.com\"\n },\n \"Action\": \"sts:AssumeRole\"\n }\n ]\n}\n",
+ "description": null,
+ "force_detach_policies": false,
+ "max_session_duration": 3600,
+ "name": "terra_ci_job",
+ "name_prefix": null,
+ "path": "/",
+ "permissions_boundary": null,
+ "tags": null
+ },
+ "after_unknown": {
+ "arn": true,
+ "create_date": true,
+ "id": true,
+ "inline_policy": true,
+ "managed_policy_arns": true,
+ "unique_id": true
+ },
+ "before_sensitive": false,
+ "after_sensitive": {
+ "inline_policy": [],
+ "managed_policy_arns": []
+ }
+ }
+ },
+ {
+ "address": "aws_iam_role.terra_ci_runner",
+ "mode": "managed",
+ "type": "aws_iam_role",
+ "name": "terra_ci_runner",
+ "provider_name": "registry.terraform.io/hashicorp/aws",
+ "change": {
+ "actions": [
+ "create"
+ ],
+ "before": null,
+ "after": {
+ "assume_role_policy": "{\n \"Version\": \"2012-10-17\",\n \"Statement\": [\n {\n \"Effect\": \"Allow\",\n \"Principal\": {\n \"Service\": \"states.amazonaws.com\"\n },\n \"Action\": \"sts:AssumeRole\"\n }\n ]\n}\n",
+ "description": null,
+ "force_detach_policies": false,
+ "max_session_duration": 3600,
+ "name": "terra_ci_runner",
+ "name_prefix": null,
+ "path": "/",
+ "permissions_boundary": null,
+ "tags": null
+ },
+ "after_unknown": {
+ "arn": true,
+ "create_date": true,
+ "id": true,
+ "inline_policy": true,
+ "managed_policy_arns": true,
+ "unique_id": true
+ },
+ "before_sensitive": false,
+ "after_sensitive": {
+ "inline_policy": [],
+ "managed_policy_arns": []
+ }
+ }
+ },
+ {
+ "address": "aws_iam_role_policy.terra_ci_job",
+ "mode": "managed",
+ "type": "aws_iam_role_policy",
+ "name": "terra_ci_job",
+ "provider_name": "registry.terraform.io/hashicorp/aws",
+ "change": {
+ "actions": [
+ "create"
+ ],
+ "before": null,
+ "after": {
+ "name_prefix": null,
+ "role": "terra_ci_job"
+ },
+ "after_unknown": {
+ "id": true,
+ "name": true,
+ "policy": true
+ },
+ "before_sensitive": false,
+ "after_sensitive": {}
+ }
+ },
+ {
+ "address": "aws_iam_role_policy.terra_ci_runner",
+ "mode": "managed",
+ "type": "aws_iam_role_policy",
+ "name": "terra_ci_runner",
+ "provider_name": "registry.terraform.io/hashicorp/aws",
+ "change": {
+ "actions": [
+ "create"
+ ],
+ "before": null,
+ "after": {
+ "name_prefix": null,
+ "role": "terra_ci_runner"
+ },
+ "after_unknown": {
+ "id": true,
+ "name": true,
+ "policy": true
+ },
+ "before_sensitive": false,
+ "after_sensitive": {}
+ }
+ },
+ {
+ "address": "aws_iam_role_policy_attachment.terra_ci_job_ecr_access",
+ "mode": "managed",
+ "type": "aws_iam_role_policy_attachment",
+ "name": "terra_ci_job_ecr_access",
+ "provider_name": "registry.terraform.io/hashicorp/aws",
+ "change": {
+ "actions": [
+ "create"
+ ],
+ "before": null,
+ "after": {
+ "policy_arn": "arn:aws:iam::aws:policy/AmazonEC2ContainerRegistryPowerUser",
+ "role": "terra_ci_job"
+ },
+ "after_unknown": {
+ "id": true
+ },
+ "before_sensitive": false,
+ "after_sensitive": {}
+ }
+ },
+ {
+ "address": "aws_s3_bucket.terra_ci",
+ "mode": "managed",
+ "type": "aws_s3_bucket",
+ "name": "terra_ci",
+ "provider_name": "registry.terraform.io/hashicorp/aws",
+ "change": {
+ "actions": [
+ "create"
+ ],
+ "before": null,
+ "after": {
+ "acl": "private",
+ "bucket": "terra-ci-artifacts-eu-west-1-000002",
+ "bucket_prefix": null,
+ "cors_rule": [],
+ "force_destroy": false,
+ "grant": [],
+ "lifecycle_rule": [],
+ "logging": [],
+ "object_lock_configuration": [],
+ "policy": null,
+ "replication_configuration": [],
+ "server_side_encryption_configuration": [
+ {
+ "rule": [
+ {
+ "apply_server_side_encryption_by_default": [
+ {
+ "kms_master_key_id": null,
+ "sse_algorithm": "aws:kms"
+ }
+ ],
+ "bucket_key_enabled": false
+ }
+ ]
+ }
+ ],
+ "tags": null,
+ "website": []
+ },
+ "after_unknown": {
+ "acceleration_status": true,
+ "arn": true,
+ "bucket_domain_name": true,
+ "bucket_regional_domain_name": true,
+ "cors_rule": [],
+ "grant": [],
+ "hosted_zone_id": true,
+ "id": true,
+ "lifecycle_rule": [],
+ "logging": [],
+ "object_lock_configuration": [],
+ "region": true,
+ "replication_configuration": [],
+ "request_payer": true,
+ "server_side_encryption_configuration": [
+ {
+ "rule": [
+ {
+ "apply_server_side_encryption_by_default": [
+ {}
+ ]
+ }
+ ]
+ }
+ ],
+ "versioning": true,
+ "website": [],
+ "website_domain": true,
+ "website_endpoint": true
+ },
+ "before_sensitive": false,
+ "after_sensitive": {
+ "cors_rule": [],
+ "grant": [],
+ "lifecycle_rule": [],
+ "logging": [],
+ "object_lock_configuration": [],
+ "replication_configuration": [],
+ "server_side_encryption_configuration": [
+ {
+ "rule": [
+ {
+ "apply_server_side_encryption_by_default": [
+ {}
+ ]
+ }
+ ]
+ }
+ ],
+ "versioning": [],
+ "website": []
+ }
+ }
+ },
+ {
+ "address": "aws_sfn_state_machine.terra_ci_runner",
+ "mode": "managed",
+ "type": "aws_sfn_state_machine",
+ "name": "terra_ci_runner",
+ "provider_name": "registry.terraform.io/hashicorp/aws",
+ "change": {
+ "actions": [
+ "create"
+ ],
+ "before": null,
+ "after": {
+ "definition": "{\n \"Comment\": \"Run Terragrunt Jobs\",\n \"StartAt\": \"OnBranch?\",\n \"States\": {\n \"OnBranch?\": {\n \"Type\": \"Choice\",\n \"Choices\": [\n {\n \"Variable\": \"$.build.sourceversion\",\n \"IsPresent\": true,\n \"Next\": \"PlanBranch\"\n }\n ],\n \"Default\": \"Plan\"\n },\n \"Plan\": {\n \"Type\": \"Task\",\n \"Resource\": \"arn:aws:states:::codebuild:startBuild.sync\",\n \"Parameters\": {\n \"ProjectName\": \"terra-ci-runner\",\n \"EnvironmentVariablesOverride\": [\n {\n \"Name\": \"TERRA_CI_BUILD_NAME\",\n \"Value.$\": \"$$.Execution.Name\"\n },\n {\n \"Name\": \"TERRA_CI_RESOURCE\",\n \"Value.$\": \"$.build.environment.terra_ci_resource\"\n }\n ]\n },\n \"End\": true\n },\n \"PlanBranch\": {\n \"Type\": \"Task\",\n \"Resource\": \"arn:aws:states:::codebuild:startBuild.sync\",\n \"Parameters\": {\n \"ProjectName\": \"terra-ci-runner\",\n \"SourceVersion.$\": \"$.build.sourceversion\",\n \"EnvironmentVariablesOverride\": [\n {\n \"Name\": \"TERRA_CI_RESOURCE\",\n \"Value.$\": \"$.build.environment.terra_ci_resource\"\n }\n ]\n },\n \"End\": true\n }\n }\n}\n",
+ "name": "terra-ci-runner",
+ "tags": null,
+ "type": "STANDARD"
+ },
+ "after_unknown": {
+ "arn": true,
+ "creation_date": true,
+ "id": true,
+ "logging_configuration": true,
+ "role_arn": true,
+ "status": true
+ },
+ "before_sensitive": false,
+ "after_sensitive": {
+ "logging_configuration": []
+ }
+ }
+ },
+ {
+ "address": "aws_route.private[\"1\"]",
+ "mode": "managed",
+ "type": "aws_route",
+ "name": "private",
+ "index": 1,
+ "provider_name": "registry.terraform.io/hashicorp/aws",
+ "change": {
+ "actions": [
+ "create"
+ ],
+ "before": null,
+ "after": {
+ "carrier_gateway_id": null,
+ "destination_cidr_block": "172.25.16.0/20",
+ "destination_ipv6_cidr_block": null,
+ "destination_prefix_list_id": null,
+ "egress_only_gateway_id": null,
+ "gateway_id": null,
+ "local_gateway_id": null,
+ "nat_gateway_id": null,
+ "route_table_id": "rtb-00cf8381520103cfb",
+ "timeouts": null,
+ "transit_gateway_id": "tgw-0f68a4f2c58772c51",
+ "vpc_endpoint_id": null,
+ "vpc_peering_connection_id": null
+ },
+ "after_unknown": {
+ "id": true,
+ "instance_id": true,
+ "instance_owner_id": true,
+ "network_interface_id": true,
+ "origin": true,
+ "state": true
+ },
+ "before_sensitive": false,
+ "after_sensitive": {}
+ }
+ },
+ {
+ "address": "aws_route.private[\"rtb-00cf8381520103cfb\"]",
+ "mode": "managed",
+ "type": "aws_route",
+ "name": "private",
+ "index": "rtb-00cf8381520103cfb",
+ "provider_name": "registry.terraform.io/hashicorp/aws",
+ "change": {
+ "actions": [
+ "create"
+ ],
+ "before": null,
+ "after": {
+ "carrier_gateway_id": null,
+ "destination_cidr_block": "172.25.16.0/20",
+ "destination_ipv6_cidr_block": null,
+ "destination_prefix_list_id": null,
+ "egress_only_gateway_id": null,
+ "gateway_id": null,
+ "local_gateway_id": null,
+ "nat_gateway_id": null,
+ "route_table_id": "rtb-00cf8381520103cfb",
+ "timeouts": null,
+ "transit_gateway_id": "tgw-0f68a4f2c58772c51",
+ "vpc_endpoint_id": null,
+ "vpc_peering_connection_id": null
+ },
+ "after_unknown": {
+ "id": true,
+ "instance_id": true,
+ "instance_owner_id": true,
+ "network_interface_id": true,
+ "origin": true,
+ "state": true
+ },
+ "before_sensitive": false,
+ "after_sensitive": {}
+ }
+ }
+ ],
+ "prior_state": {
+ "format_version": "0.1",
+ "terraform_version": "0.15.0",
+ "values": {
+ "root_module": {
+ "resources": [
+ {
+ "address": "data.aws_caller_identity.current",
+ "mode": "data",
+ "type": "aws_caller_identity",
+ "name": "current",
+ "provider_name": "registry.terraform.io/hashicorp/aws",
+ "schema_version": 0,
+ "values": {
+ "account_id": "719261439472",
+ "arn": "arn:aws:sts::719261439472:assumed-role/ci/1620222847597477484",
+ "id": "719261439472",
+ "user_id": "AROA2O52SSXYLVFYURBIV:1620222847597477484"
+ }
+ },
+ {
+ "address": "data.template_file.terra_ci",
+ "mode": "data",
+ "type": "template_file",
+ "name": "terra_ci",
+ "provider_name": "registry.terraform.io/hashicorp/template",
+ "schema_version": 0,
+ "values": {
+ "filename": null,
+ "id": "64e36ed71e7270140dde96fec9c89d1d55ae5a6e91f7c0be15170200dcf9481b",
+ "rendered": "version: 0.2\nphases:\n install:\n commands:\n - make install_tools\n build:\n commands:\n - make plan_local resource=$TERRA_CI_RESOURCE\nartifacts:\n files:\n - ./tfplan\n name: $TERRA_CI_BUILD_NAME\n\n",
+ "template": "version: 0.2\nphases:\n install:\n commands:\n - make install_tools\n build:\n commands:\n - make plan_local resource=$TERRA_CI_RESOURCE\nartifacts:\n files:\n - ./tfplan\n name: $TERRA_CI_BUILD_NAME\n\n",
+ "vars": null
+ }
+ }
+ ]
+ }
+ }
+ },
+ "configuration": {
+ "provider_config": {
+ "aws": {
+ "name": "aws",
+ "expressions": {
+ "allowed_account_ids": {
+ "constant_value": [
+ "719261439472"
+ ]
+ },
+ "assume_role": [
+ {
+ "role_arn": {
+ "constant_value": "arn:aws:iam::719261439472:role/ci"
+ }
+ }
+ ],
+ "region": {
+ "constant_value": "eu-west-1"
+ }
+ }
+ }
+ },
+ "root_module": {
+ "resources": [
+ {
+ "address": "aws_codebuild_project.terra_ci",
+ "mode": "managed",
+ "type": "aws_codebuild_project",
+ "name": "terra_ci",
+ "provider_config_key": "aws",
+ "expressions": {
+ "artifacts": [
+ {
+ "location": {
+ "references": [
+ "aws_s3_bucket.terra_ci"
+ ]
+ },
+ "type": {
+ "constant_value": "S3"
+ }
+ }
+ ],
+ "build_timeout": {
+ "constant_value": "10"
+ },
+ "description": {
+ "constant_value": "Deploy environment configuration"
+ },
+ "environment": [
+ {
+ "compute_type": {
+ "constant_value": "BUILD_GENERAL1_SMALL"
+ },
+ "image": {
+ "constant_value": "aws/codebuild/amazonlinux2-x86_64-standard:2.0"
+ },
+ "image_pull_credentials_type": {
+ "constant_value": "CODEBUILD"
+ },
+ "privileged_mode": {
+ "constant_value": false
+ },
+ "type": {
+ "constant_value": "LINUX_CONTAINER"
+ }
+ }
+ ],
+ "logs_config": [
+ {
+ "cloudwatch_logs": [
+ {
+ "status": {
+ "constant_value": "ENABLED"
+ }
+ }
+ ],
+ "s3_logs": [
+ {
+ "encryption_disabled": {
+ "constant_value": false
+ },
+ "status": {
+ "constant_value": "DISABLED"
+ }
+ }
+ ]
+ }
+ ],
+ "name": {
+ "constant_value": "terra-ci-runner"
+ },
+ "service_role": {
+ "references": [
+ "aws_iam_role.terra_ci_job"
+ ]
+ },
+ "source": [
+ {
+ "buildspec": {
+ "references": [
+ "data.template_file.terra_ci"
+ ]
+ },
+ "git_clone_depth": {
+ "constant_value": 1
+ },
+ "insecure_ssl": {
+ "constant_value": false
+ },
+ "location": {
+ "references": [
+ "var.repo_url"
+ ]
+ },
+ "report_build_status": {
+ "constant_value": false
+ },
+ "type": {
+ "constant_value": "GITHUB"
+ }
+ }
+ ]
+ },
+ "schema_version": 0
+ },
+ {
+ "address": "aws_iam_role.terra_ci_job",
+ "mode": "managed",
+ "type": "aws_iam_role",
+ "name": "terra_ci_job",
+ "provider_config_key": "aws",
+ "expressions": {
+ "assume_role_policy": {
+ "constant_value": "{\n \"Version\": \"2012-10-17\",\n \"Statement\": [\n {\n \"Effect\": \"Allow\",\n \"Principal\": {\n \"Service\": \"codebuild.amazonaws.com\"\n },\n \"Action\": \"sts:AssumeRole\"\n }\n ]\n}\n"
+ },
+ "name": {
+ "constant_value": "terra_ci_job"
+ }
+ },
+ "schema_version": 0
+ },
+ {
+ "address": "aws_iam_role.terra_ci_runner",
+ "mode": "managed",
+ "type": "aws_iam_role",
+ "name": "terra_ci_runner",
+ "provider_config_key": "aws",
+ "expressions": {
+ "assume_role_policy": {
+ "constant_value": "{\n \"Version\": \"2012-10-17\",\n \"Statement\": [\n {\n \"Effect\": \"Allow\",\n \"Principal\": {\n \"Service\": \"states.amazonaws.com\"\n },\n \"Action\": \"sts:AssumeRole\"\n }\n ]\n}\n"
+ },
+ "name": {
+ "constant_value": "terra_ci_runner"
+ }
+ },
+ "schema_version": 0
+ },
+ {
+ "address": "aws_iam_role_policy.terra_ci_job",
+ "mode": "managed",
+ "type": "aws_iam_role_policy",
+ "name": "terra_ci_job",
+ "provider_config_key": "aws",
+ "expressions": {
+ "policy": {
+ "references": [
+ "data.aws_caller_identity.current",
+ "aws_s3_bucket.terra_ci",
+ "aws_s3_bucket.terra_ci"
+ ]
+ },
+ "role": {
+ "references": [
+ "aws_iam_role.terra_ci_job"
+ ]
+ }
+ },
+ "schema_version": 0
+ },
+ {
+ "address": "aws_iam_role_policy.terra_ci_runner",
+ "mode": "managed",
+ "type": "aws_iam_role_policy",
+ "name": "terra_ci_runner",
+ "provider_config_key": "aws",
+ "expressions": {
+ "policy": {
+ "references": [
+ "aws_codebuild_project.terra_ci",
+ "var.aws_region",
+ "data.aws_caller_identity.current"
+ ]
+ },
+ "role": {
+ "references": [
+ "aws_iam_role.terra_ci_runner"
+ ]
+ }
+ },
+ "schema_version": 0
+ },
+ {
+ "address": "aws_iam_role_policy_attachment.terra_ci_job_ecr_access",
+ "mode": "managed",
+ "type": "aws_iam_role_policy_attachment",
+ "name": "terra_ci_job_ecr_access",
+ "provider_config_key": "aws",
+ "expressions": {
+ "policy_arn": {
+ "constant_value": "arn:aws:iam::aws:policy/AmazonEC2ContainerRegistryPowerUser"
+ },
+ "role": {
+ "references": [
+ "aws_iam_role.terra_ci_job"
+ ]
+ }
+ },
+ "schema_version": 0
+ },
+ {
+ "address": "aws_s3_bucket.terra_ci",
+ "mode": "managed",
+ "type": "aws_s3_bucket",
+ "name": "terra_ci",
+ "provider_config_key": "aws",
+ "expressions": {
+ "acl": {
+ "constant_value": "private"
+ },
+ "bucket": {
+ "references": [
+ "var.aws_region",
+ "var.serial_number"
+ ]
+ },
+ "server_side_encryption_configuration": [
+ {
+ "rule": [
+ {
+ "apply_server_side_encryption_by_default": [
+ {
+ "sse_algorithm": {
+ "constant_value": "aws:kms"
+ }
+ }
+ ],
+ "bucket_key_enabled": {
+ "constant_value": false
+ }
+ }
+ ]
+ }
+ ]
+ },
+ "schema_version": 0
+ },
+ {
+ "address": "aws_sfn_state_machine.terra_ci_runner",
+ "mode": "managed",
+ "type": "aws_sfn_state_machine",
+ "name": "terra_ci_runner",
+ "provider_config_key": "aws",
+ "expressions": {
+ "definition": {
+ "references": [
+ "aws_codebuild_project.terra_ci",
+ "aws_codebuild_project.terra_ci"
+ ]
+ },
+ "name": {
+ "constant_value": "terra-ci-runner"
+ },
+ "role_arn": {
+ "references": [
+ "aws_iam_role.terra_ci_runner"
+ ]
+ }
+ },
+ "schema_version": 0
+ },
+ {
+ "address": "data.aws_caller_identity.current",
+ "mode": "data",
+ "type": "aws_caller_identity",
+ "name": "current",
+ "provider_config_key": "aws",
+ "schema_version": 0
+ },
+ {
+ "address": "data.template_file.terra_ci",
+ "mode": "data",
+ "type": "template_file",
+ "name": "terra_ci",
+ "provider_config_key": "template",
+ "expressions": {
+ "template": {}
+ },
+ "schema_version": 0
+ }
+ ],
+ "variables": {
+ "aws_region": {},
+ "repo_url": {},
+ "serial_number": {}
+ }
+ }
+ }
+ }
diff --git a/tests/test_files/tf_content_generator_files/tfplan-destroy-example/tf_content.txt b/tests/test_files/tf_content_generator_files/tfplan-destroy-example/tf_content.txt
new file mode 100644
index 00000000..e69de29b
diff --git a/tests/test_files/tf_content_generator_files/tfplan-destroy-example/tfplan.json b/tests/test_files/tf_content_generator_files/tfplan-destroy-example/tfplan.json
new file mode 100644
index 00000000..88176ec9
--- /dev/null
+++ b/tests/test_files/tf_content_generator_files/tfplan-destroy-example/tfplan.json
@@ -0,0 +1,1082 @@
+{
+ "comment-for-reader": "THIS TERRAFORM FILE REPRESENTS A REAL TF-PLAN OUTPUT FOR DELETED INFRASTRUCTRE",
+ "format_version": "0.1",
+ "terraform_version": "0.15.0",
+ "variables": {
+ "aws_region": {
+ "value": "eu-west-1"
+ },
+ "repo_url": {
+ "value": "https://github.com/p0tr3c-terraform/terra-ci-single-account.git"
+ },
+ "serial_number": {
+ "value": "000002"
+ }
+ },
+ "planned_values": {
+ "root_module": {}
+ },
+ "resource_changes": [
+ {
+ "address": "aws_codebuild_project.terra_ci",
+ "mode": "managed",
+ "type": "aws_codebuild_project",
+ "name": "terra_ci",
+ "provider_name": "registry.terraform.io/hashicorp/aws",
+ "change": {
+ "actions": [
+ "delete"
+ ],
+ "before": {
+ "arn": "arn:aws:codebuild:eu-west-1:719261439472:project/terra-ci-runner",
+ "artifacts": [
+ {
+ "artifact_identifier": "",
+ "encryption_disabled": false,
+ "location": "terra-ci-artifacts-eu-west-1-000002",
+ "name": "terra-ci-runner",
+ "namespace_type": "NONE",
+ "override_artifact_name": false,
+ "packaging": "NONE",
+ "path": "",
+ "type": "S3"
+ }
+ ],
+ "badge_enabled": false,
+ "badge_url": "",
+ "build_timeout": 10,
+ "cache": [
+ {
+ "location": "",
+ "modes": [],
+ "type": "NO_CACHE"
+ }
+ ],
+ "description": "Deploy environment configuration",
+ "encryption_key": "arn:aws:kms:eu-west-1:719261439472:alias/aws/s3",
+ "environment": [
+ {
+ "certificate": "",
+ "compute_type": "BUILD_GENERAL1_SMALL",
+ "environment_variable": [],
+ "image": "aws/codebuild/amazonlinux2-x86_64-standard:2.0",
+ "image_pull_credentials_type": "CODEBUILD",
+ "privileged_mode": false,
+ "registry_credential": [],
+ "type": "LINUX_CONTAINER"
+ }
+ ],
+ "id": "arn:aws:codebuild:eu-west-1:719261439472:project/terra-ci-runner",
+ "logs_config": [
+ {
+ "cloudwatch_logs": [
+ {
+ "group_name": "",
+ "status": "ENABLED",
+ "stream_name": ""
+ }
+ ],
+ "s3_logs": [
+ {
+ "encryption_disabled": false,
+ "location": "",
+ "status": "DISABLED"
+ }
+ ]
+ }
+ ],
+ "name": "terra-ci-runner",
+ "queued_timeout": 480,
+ "secondary_artifacts": [],
+ "secondary_sources": [],
+ "service_role": "arn:aws:iam::719261439472:role/terra_ci_job",
+ "source": [
+ {
+ "auth": [],
+ "buildspec": "version: 0.2\nphases:\n install:\n commands:\n - make install_tools\n build:\n commands:\n - make plan_local resource=$TERRA_CI_RESOURCE\nartifacts:\n files:\n - ./tfplan\n name: $TERRA_CI_BUILD_NAME\n\n",
+ "git_clone_depth": 1,
+ "git_submodules_config": [],
+ "insecure_ssl": false,
+ "location": "https://github.com/p0tr3c-terraform/terra-ci-single-account.git",
+ "report_build_status": false,
+ "type": "GITHUB"
+ }
+ ],
+ "source_version": "",
+ "tags": {},
+ "vpc_config": []
+ },
+ "after": null,
+ "after_unknown": {},
+ "before_sensitive": {
+ "artifacts": [
+ {}
+ ],
+ "cache": [
+ {
+ "modes": []
+ }
+ ],
+ "environment": [
+ {
+ "environment_variable": [],
+ "registry_credential": []
+ }
+ ],
+ "logs_config": [
+ {
+ "cloudwatch_logs": [
+ {}
+ ],
+ "s3_logs": [
+ {}
+ ]
+ }
+ ],
+ "secondary_artifacts": [],
+ "secondary_sources": [],
+ "source": [
+ {
+ "auth": [],
+ "git_submodules_config": []
+ }
+ ],
+ "tags": {},
+ "vpc_config": []
+ },
+ "after_sensitive": false
+ }
+ },
+ {
+ "address": "aws_iam_role.terra_ci_job",
+ "mode": "managed",
+ "type": "aws_iam_role",
+ "name": "terra_ci_job",
+ "provider_name": "registry.terraform.io/hashicorp/aws",
+ "change": {
+ "actions": [
+ "delete"
+ ],
+ "before": {
+ "arn": "arn:aws:iam::719261439472:role/terra_ci_job",
+ "assume_role_policy": "{\"Version\":\"2012-10-17\",\"Statement\":[{\"Effect\":\"Allow\",\"Principal\":{\"Service\":\"codebuild.amazonaws.com\"},\"Action\":\"sts:AssumeRole\"}]}",
+ "create_date": "2021-05-05T13:59:07Z",
+ "description": "",
+ "force_detach_policies": false,
+ "id": "terra_ci_job",
+ "inline_policy": [
+ {
+ "name": "terraform-20210505135914255500000001",
+ "policy": "{\n \"Version\": \"2012-10-17\",\n \"Statement\": [\n {\n \"Effect\": \"Allow\",\n \"Action\": \"sts:AssumeRole\",\n \"Resource\": \"arn:aws:iam::719261439472:role/ci\"\n },\n {\n \"Effect\": \"Allow\",\n \"Resource\": [\n \"*\"\n ],\n \"Action\": [\n \"logs:CreateLogGroup\",\n \"logs:CreateLogStream\",\n \"logs:PutLogEvents\"\n ]\n },\n {\n \"Effect\": \"Allow\",\n \"Resource\": [\n \"arn:aws:s3:::terra-ci-artifacts-eu-west-1-000002\",\n \"arn:aws:s3:::terra-ci-artifacts-eu-west-1-000002/*\"\n ],\n \"Action\": [\n \"s3:ListBucket\",\n \"s3:*Object\"\n ]\n }\n ]\n}\n"
+ }
+ ],
+ "managed_policy_arns": [
+ "arn:aws:iam::aws:policy/AmazonEC2ContainerRegistryPowerUser"
+ ],
+ "max_session_duration": 3600,
+ "name": "terra_ci_job",
+ "name_prefix": null,
+ "path": "/",
+ "permissions_boundary": null,
+ "tags": {},
+ "unique_id": "AROA2O52SSXYMEA4VGINT"
+ },
+ "after": null,
+ "after_unknown": {},
+ "before_sensitive": {
+ "inline_policy": [
+ {}
+ ],
+ "managed_policy_arns": [
+ false
+ ],
+ "tags": {}
+ },
+ "after_sensitive": false
+ }
+ },
+ {
+ "address": "aws_iam_role.terra_ci_runner",
+ "mode": "managed",
+ "type": "aws_iam_role",
+ "name": "terra_ci_runner",
+ "provider_name": "registry.terraform.io/hashicorp/aws",
+ "change": {
+ "actions": [
+ "delete"
+ ],
+ "before": {
+ "arn": "arn:aws:iam::719261439472:role/terra_ci_runner",
+ "assume_role_policy": "{\"Version\":\"2012-10-17\",\"Statement\":[{\"Effect\":\"Allow\",\"Principal\":{\"Service\":\"states.amazonaws.com\"},\"Action\":\"sts:AssumeRole\"}]}",
+ "create_date": "2021-05-05T13:59:07Z",
+ "description": "",
+ "force_detach_policies": false,
+ "id": "terra_ci_runner",
+ "inline_policy": [
+ {
+ "name": "terraform-20210505135918902900000003",
+ "policy": "{\n \"Version\": \"2012-10-17\",\n \"Statement\": [\n {\n \"Effect\": \"Allow\",\n \"Action\": [\n \"codebuild:StartBuild\",\n \"codebuild:StopBuild\",\n \"codebuild:BatchGetBuilds\"\n ],\n \"Resource\": [\n \"arn:aws:codebuild:eu-west-1:719261439472:project/terra-ci-runner\"\n ]\n },\n {\n \"Effect\": \"Allow\",\n \"Action\": [\n \"events:PutTargets\",\n \"events:PutRule\",\n \"events:DescribeRule\"\n ],\n \"Resource\": [\n \"arn:aws:events:eu-west-1:719261439472:rule/StepFunctionsGetEventForCodeBuildStartBuildRule\"\n ]\n }\n ]\n}\n"
+ }
+ ],
+ "managed_policy_arns": [],
+ "max_session_duration": 3600,
+ "name": "terra_ci_runner",
+ "name_prefix": null,
+ "path": "/",
+ "permissions_boundary": null,
+ "tags": {},
+ "unique_id": "AROA2O52SSXYPQLY6HIHV"
+ },
+ "after": null,
+ "after_unknown": {},
+ "before_sensitive": {
+ "inline_policy": [
+ {}
+ ],
+ "managed_policy_arns": [],
+ "tags": {}
+ },
+ "after_sensitive": false
+ }
+ },
+ {
+ "address": "aws_iam_role_policy.terra_ci_job",
+ "mode": "managed",
+ "type": "aws_iam_role_policy",
+ "name": "terra_ci_job",
+ "provider_name": "registry.terraform.io/hashicorp/aws",
+ "change": {
+ "actions": [
+ "delete"
+ ],
+ "before": {
+ "id": "terra_ci_job:terraform-20210505135914255500000001",
+ "name": "terraform-20210505135914255500000001",
+ "name_prefix": null,
+ "policy": "{\n \"Version\": \"2012-10-17\",\n \"Statement\": [\n {\n \"Effect\": \"Allow\",\n \"Action\": \"sts:AssumeRole\",\n \"Resource\": \"arn:aws:iam::719261439472:role/ci\"\n },\n {\n \"Effect\": \"Allow\",\n \"Resource\": [\n \"*\"\n ],\n \"Action\": [\n \"logs:CreateLogGroup\",\n \"logs:CreateLogStream\",\n \"logs:PutLogEvents\"\n ]\n },\n {\n \"Effect\": \"Allow\",\n \"Resource\": [\n \"arn:aws:s3:::terra-ci-artifacts-eu-west-1-000002\",\n \"arn:aws:s3:::terra-ci-artifacts-eu-west-1-000002/*\"\n ],\n \"Action\": [\n \"s3:ListBucket\",\n \"s3:*Object\"\n ]\n }\n ]\n}\n",
+ "role": "terra_ci_job"
+ },
+ "after": null,
+ "after_unknown": {},
+ "before_sensitive": {},
+ "after_sensitive": false
+ }
+ },
+ {
+ "address": "aws_iam_role_policy.terra_ci_runner",
+ "mode": "managed",
+ "type": "aws_iam_role_policy",
+ "name": "terra_ci_runner",
+ "provider_name": "registry.terraform.io/hashicorp/aws",
+ "change": {
+ "actions": [
+ "delete"
+ ],
+ "before": {
+ "id": "terra_ci_runner:terraform-20210505135918902900000003",
+ "name": "terraform-20210505135918902900000003",
+ "name_prefix": null,
+ "policy": "{\n \"Version\": \"2012-10-17\",\n \"Statement\": [\n {\n \"Effect\": \"Allow\",\n \"Action\": [\n \"codebuild:StartBuild\",\n \"codebuild:StopBuild\",\n \"codebuild:BatchGetBuilds\"\n ],\n \"Resource\": [\n \"arn:aws:codebuild:eu-west-1:719261439472:project/terra-ci-runner\"\n ]\n },\n {\n \"Effect\": \"Allow\",\n \"Action\": [\n \"events:PutTargets\",\n \"events:PutRule\",\n \"events:DescribeRule\"\n ],\n \"Resource\": [\n \"arn:aws:events:eu-west-1:719261439472:rule/StepFunctionsGetEventForCodeBuildStartBuildRule\"\n ]\n }\n ]\n}\n",
+ "role": "terra_ci_runner"
+ },
+ "after": null,
+ "after_unknown": {},
+ "before_sensitive": {},
+ "after_sensitive": false
+ }
+ },
+ {
+ "address": "aws_iam_role_policy_attachment.terra_ci_job_ecr_access",
+ "mode": "managed",
+ "type": "aws_iam_role_policy_attachment",
+ "name": "terra_ci_job_ecr_access",
+ "provider_name": "registry.terraform.io/hashicorp/aws",
+ "change": {
+ "actions": [
+ "delete"
+ ],
+ "before": {
+ "id": "terra_ci_job-20210505135914799900000002",
+ "policy_arn": "arn:aws:iam::aws:policy/AmazonEC2ContainerRegistryPowerUser",
+ "role": "terra_ci_job"
+ },
+ "after": null,
+ "after_unknown": {},
+ "before_sensitive": {},
+ "after_sensitive": false
+ }
+ },
+ {
+ "address": "aws_s3_bucket.terra_ci",
+ "mode": "managed",
+ "type": "aws_s3_bucket",
+ "name": "terra_ci",
+ "provider_name": "registry.terraform.io/hashicorp/aws",
+ "change": {
+ "actions": [
+ "delete"
+ ],
+ "before": {
+ "acceleration_status": "",
+ "acl": "private",
+ "arn": "arn:aws:s3:::terra-ci-artifacts-eu-west-1-000002",
+ "bucket": "terra-ci-artifacts-eu-west-1-000002",
+ "bucket_domain_name": "terra-ci-artifacts-eu-west-1-000002.s3.amazonaws.com",
+ "bucket_prefix": null,
+ "bucket_regional_domain_name": "terra-ci-artifacts-eu-west-1-000002.s3.eu-west-1.amazonaws.com",
+ "cors_rule": [],
+ "force_destroy": false,
+ "grant": [],
+ "hosted_zone_id": "Z1BKCTXD74EZPE",
+ "id": "terra-ci-artifacts-eu-west-1-000002",
+ "lifecycle_rule": [],
+ "logging": [],
+ "object_lock_configuration": [],
+ "policy": null,
+ "region": "eu-west-1",
+ "replication_configuration": [],
+ "request_payer": "BucketOwner",
+ "server_side_encryption_configuration": [
+ {
+ "rule": [
+ {
+ "apply_server_side_encryption_by_default": [
+ {
+ "kms_master_key_id": "",
+ "sse_algorithm": "aws:kms"
+ }
+ ],
+ "bucket_key_enabled": false
+ }
+ ]
+ }
+ ],
+ "tags": {},
+ "versioning": [
+ {
+ "enabled": false,
+ "mfa_delete": false
+ }
+ ],
+ "website": [],
+ "website_domain": null,
+ "website_endpoint": null
+ },
+ "after": null,
+ "after_unknown": {},
+ "before_sensitive": {
+ "cors_rule": [],
+ "grant": [],
+ "lifecycle_rule": [],
+ "logging": [],
+ "object_lock_configuration": [],
+ "replication_configuration": [],
+ "server_side_encryption_configuration": [
+ {
+ "rule": [
+ {
+ "apply_server_side_encryption_by_default": [
+ {}
+ ]
+ }
+ ]
+ }
+ ],
+ "tags": {},
+ "versioning": [
+ {}
+ ],
+ "website": []
+ },
+ "after_sensitive": false
+ }
+ },
+ {
+ "address": "aws_sfn_state_machine.terra_ci_runner",
+ "mode": "managed",
+ "type": "aws_sfn_state_machine",
+ "name": "terra_ci_runner",
+ "provider_name": "registry.terraform.io/hashicorp/aws",
+ "change": {
+ "actions": [
+ "delete"
+ ],
+ "before": {
+ "arn": "arn:aws:states:eu-west-1:719261439472:stateMachine:terra-ci-runner",
+ "creation_date": "2021-05-05T13:59:28Z",
+ "definition": "{\n \"Comment\": \"Run Terragrunt Jobs\",\n \"StartAt\": \"OnBranch?\",\n \"States\": {\n \"OnBranch?\": {\n \"Type\": \"Choice\",\n \"Choices\": [\n {\n \"Variable\": \"$.build.sourceversion\",\n \"IsPresent\": true,\n \"Next\": \"PlanBranch\"\n }\n ],\n \"Default\": \"Plan\"\n },\n \"Plan\": {\n \"Type\": \"Task\",\n \"Resource\": \"arn:aws:states:::codebuild:startBuild.sync\",\n \"Parameters\": {\n \"ProjectName\": \"terra-ci-runner\",\n \"EnvironmentVariablesOverride\": [\n {\n \"Name\": \"TERRA_CI_BUILD_NAME\",\n \"Value.$\": \"$$.Execution.Name\"\n },\n {\n \"Name\": \"TERRA_CI_RESOURCE\",\n \"Value.$\": \"$.build.environment.terra_ci_resource\"\n }\n ]\n },\n \"End\": true\n },\n \"PlanBranch\": {\n \"Type\": \"Task\",\n \"Resource\": \"arn:aws:states:::codebuild:startBuild.sync\",\n \"Parameters\": {\n \"ProjectName\": \"terra-ci-runner\",\n \"SourceVersion.$\": \"$.build.sourceversion\",\n \"EnvironmentVariablesOverride\": [\n {\n \"Name\": \"TERRA_CI_RESOURCE\",\n \"Value.$\": \"$.build.environment.terra_ci_resource\"\n }\n ]\n },\n \"End\": true\n }\n }\n}\n",
+ "id": "arn:aws:states:eu-west-1:719261439472:stateMachine:terra-ci-runner",
+ "logging_configuration": [
+ {
+ "include_execution_data": false,
+ "level": "OFF",
+ "log_destination": ""
+ }
+ ],
+ "name": "terra-ci-runner",
+ "role_arn": "arn:aws:iam::719261439472:role/terra_ci_runner",
+ "status": "ACTIVE",
+ "tags": {},
+ "type": "STANDARD"
+ },
+ "after": null,
+ "after_unknown": {},
+ "before_sensitive": {
+ "logging_configuration": [
+ {}
+ ],
+ "tags": {}
+ },
+ "after_sensitive": false
+ }
+ }
+ ],
+ "prior_state": {
+ "format_version": "0.1",
+ "terraform_version": "0.15.0",
+ "values": {
+ "root_module": {
+ "resources": [
+ {
+ "address": "aws_codebuild_project.terra_ci",
+ "mode": "managed",
+ "type": "aws_codebuild_project",
+ "name": "terra_ci",
+ "provider_name": "registry.terraform.io/hashicorp/aws",
+ "schema_version": 0,
+ "values": {
+ "arn": "arn:aws:codebuild:eu-west-1:719261439472:project/terra-ci-runner",
+ "artifacts": [
+ {
+ "artifact_identifier": "",
+ "encryption_disabled": false,
+ "location": "terra-ci-artifacts-eu-west-1-000002",
+ "name": "terra-ci-runner",
+ "namespace_type": "NONE",
+ "override_artifact_name": false,
+ "packaging": "NONE",
+ "path": "",
+ "type": "S3"
+ }
+ ],
+ "badge_enabled": false,
+ "badge_url": "",
+ "build_timeout": 10,
+ "cache": [
+ {
+ "location": "",
+ "modes": [],
+ "type": "NO_CACHE"
+ }
+ ],
+ "description": "Deploy environment configuration",
+ "encryption_key": "arn:aws:kms:eu-west-1:719261439472:alias/aws/s3",
+ "environment": [
+ {
+ "certificate": "",
+ "compute_type": "BUILD_GENERAL1_SMALL",
+ "environment_variable": [],
+ "image": "aws/codebuild/amazonlinux2-x86_64-standard:2.0",
+ "image_pull_credentials_type": "CODEBUILD",
+ "privileged_mode": false,
+ "registry_credential": [],
+ "type": "LINUX_CONTAINER"
+ }
+ ],
+ "id": "arn:aws:codebuild:eu-west-1:719261439472:project/terra-ci-runner",
+ "logs_config": [
+ {
+ "cloudwatch_logs": [
+ {
+ "group_name": "",
+ "status": "ENABLED",
+ "stream_name": ""
+ }
+ ],
+ "s3_logs": [
+ {
+ "encryption_disabled": false,
+ "location": "",
+ "status": "DISABLED"
+ }
+ ]
+ }
+ ],
+ "name": "terra-ci-runner",
+ "queued_timeout": 480,
+ "secondary_artifacts": [],
+ "secondary_sources": [],
+ "service_role": "arn:aws:iam::719261439472:role/terra_ci_job",
+ "source": [
+ {
+ "auth": [],
+ "buildspec": "version: 0.2\nphases:\n install:\n commands:\n - make install_tools\n build:\n commands:\n - make plan_local resource=$TERRA_CI_RESOURCE\nartifacts:\n files:\n - ./tfplan\n name: $TERRA_CI_BUILD_NAME\n\n",
+ "git_clone_depth": 1,
+ "git_submodules_config": [],
+ "insecure_ssl": false,
+ "location": "https://github.com/p0tr3c-terraform/terra-ci-single-account.git",
+ "report_build_status": false,
+ "type": "GITHUB"
+ }
+ ],
+ "source_version": "",
+ "tags": {},
+ "vpc_config": []
+ },
+ "depends_on": [
+ "aws_iam_role.terra_ci_job",
+ "aws_s3_bucket.terra_ci",
+ "data.template_file.terra_ci"
+ ]
+ },
+ {
+ "address": "aws_iam_role.terra_ci_job",
+ "mode": "managed",
+ "type": "aws_iam_role",
+ "name": "terra_ci_job",
+ "provider_name": "registry.terraform.io/hashicorp/aws",
+ "schema_version": 0,
+ "values": {
+ "arn": "arn:aws:iam::719261439472:role/terra_ci_job",
+ "assume_role_policy": "{\"Version\":\"2012-10-17\",\"Statement\":[{\"Effect\":\"Allow\",\"Principal\":{\"Service\":\"codebuild.amazonaws.com\"},\"Action\":\"sts:AssumeRole\"}]}",
+ "create_date": "2021-05-05T13:59:07Z",
+ "description": "",
+ "force_detach_policies": false,
+ "id": "terra_ci_job",
+ "inline_policy": [
+ {
+ "name": "terraform-20210505135914255500000001",
+ "policy": "{\n \"Version\": \"2012-10-17\",\n \"Statement\": [\n {\n \"Effect\": \"Allow\",\n \"Action\": \"sts:AssumeRole\",\n \"Resource\": \"arn:aws:iam::719261439472:role/ci\"\n },\n {\n \"Effect\": \"Allow\",\n \"Resource\": [\n \"*\"\n ],\n \"Action\": [\n \"logs:CreateLogGroup\",\n \"logs:CreateLogStream\",\n \"logs:PutLogEvents\"\n ]\n },\n {\n \"Effect\": \"Allow\",\n \"Resource\": [\n \"arn:aws:s3:::terra-ci-artifacts-eu-west-1-000002\",\n \"arn:aws:s3:::terra-ci-artifacts-eu-west-1-000002/*\"\n ],\n \"Action\": [\n \"s3:ListBucket\",\n \"s3:*Object\"\n ]\n }\n ]\n}\n"
+ }
+ ],
+ "managed_policy_arns": [
+ "arn:aws:iam::aws:policy/AmazonEC2ContainerRegistryPowerUser"
+ ],
+ "max_session_duration": 3600,
+ "name": "terra_ci_job",
+ "name_prefix": null,
+ "path": "/",
+ "permissions_boundary": null,
+ "tags": {},
+ "unique_id": "AROA2O52SSXYMEA4VGINT"
+ }
+ },
+ {
+ "address": "aws_iam_role.terra_ci_runner",
+ "mode": "managed",
+ "type": "aws_iam_role",
+ "name": "terra_ci_runner",
+ "provider_name": "registry.terraform.io/hashicorp/aws",
+ "schema_version": 0,
+ "values": {
+ "arn": "arn:aws:iam::719261439472:role/terra_ci_runner",
+ "assume_role_policy": "{\"Version\":\"2012-10-17\",\"Statement\":[{\"Effect\":\"Allow\",\"Principal\":{\"Service\":\"states.amazonaws.com\"},\"Action\":\"sts:AssumeRole\"}]}",
+ "create_date": "2021-05-05T13:59:07Z",
+ "description": "",
+ "force_detach_policies": false,
+ "id": "terra_ci_runner",
+ "inline_policy": [
+ {
+ "name": "terraform-20210505135918902900000003",
+ "policy": "{\n \"Version\": \"2012-10-17\",\n \"Statement\": [\n {\n \"Effect\": \"Allow\",\n \"Action\": [\n \"codebuild:StartBuild\",\n \"codebuild:StopBuild\",\n \"codebuild:BatchGetBuilds\"\n ],\n \"Resource\": [\n \"arn:aws:codebuild:eu-west-1:719261439472:project/terra-ci-runner\"\n ]\n },\n {\n \"Effect\": \"Allow\",\n \"Action\": [\n \"events:PutTargets\",\n \"events:PutRule\",\n \"events:DescribeRule\"\n ],\n \"Resource\": [\n \"arn:aws:events:eu-west-1:719261439472:rule/StepFunctionsGetEventForCodeBuildStartBuildRule\"\n ]\n }\n ]\n}\n"
+ }
+ ],
+ "managed_policy_arns": [],
+ "max_session_duration": 3600,
+ "name": "terra_ci_runner",
+ "name_prefix": null,
+ "path": "/",
+ "permissions_boundary": null,
+ "tags": {},
+ "unique_id": "AROA2O52SSXYPQLY6HIHV"
+ }
+ },
+ {
+ "address": "aws_iam_role_policy.terra_ci_job",
+ "mode": "managed",
+ "type": "aws_iam_role_policy",
+ "name": "terra_ci_job",
+ "provider_name": "registry.terraform.io/hashicorp/aws",
+ "schema_version": 0,
+ "values": {
+ "id": "terra_ci_job:terraform-20210505135914255500000001",
+ "name": "terraform-20210505135914255500000001",
+ "name_prefix": null,
+ "policy": "{\n \"Version\": \"2012-10-17\",\n \"Statement\": [\n {\n \"Effect\": \"Allow\",\n \"Action\": \"sts:AssumeRole\",\n \"Resource\": \"arn:aws:iam::719261439472:role/ci\"\n },\n {\n \"Effect\": \"Allow\",\n \"Resource\": [\n \"*\"\n ],\n \"Action\": [\n \"logs:CreateLogGroup\",\n \"logs:CreateLogStream\",\n \"logs:PutLogEvents\"\n ]\n },\n {\n \"Effect\": \"Allow\",\n \"Resource\": [\n \"arn:aws:s3:::terra-ci-artifacts-eu-west-1-000002\",\n \"arn:aws:s3:::terra-ci-artifacts-eu-west-1-000002/*\"\n ],\n \"Action\": [\n \"s3:ListBucket\",\n \"s3:*Object\"\n ]\n }\n ]\n}\n",
+ "role": "terra_ci_job"
+ },
+ "depends_on": [
+ "aws_iam_role.terra_ci_job",
+ "aws_s3_bucket.terra_ci",
+ "data.aws_caller_identity.current"
+ ]
+ },
+ {
+ "address": "aws_iam_role_policy.terra_ci_runner",
+ "mode": "managed",
+ "type": "aws_iam_role_policy",
+ "name": "terra_ci_runner",
+ "provider_name": "registry.terraform.io/hashicorp/aws",
+ "schema_version": 0,
+ "values": {
+ "id": "terra_ci_runner:terraform-20210505135918902900000003",
+ "name": "terraform-20210505135918902900000003",
+ "name_prefix": null,
+ "policy": "{\n \"Version\": \"2012-10-17\",\n \"Statement\": [\n {\n \"Effect\": \"Allow\",\n \"Action\": [\n \"codebuild:StartBuild\",\n \"codebuild:StopBuild\",\n \"codebuild:BatchGetBuilds\"\n ],\n \"Resource\": [\n \"arn:aws:codebuild:eu-west-1:719261439472:project/terra-ci-runner\"\n ]\n },\n {\n \"Effect\": \"Allow\",\n \"Action\": [\n \"events:PutTargets\",\n \"events:PutRule\",\n \"events:DescribeRule\"\n ],\n \"Resource\": [\n \"arn:aws:events:eu-west-1:719261439472:rule/StepFunctionsGetEventForCodeBuildStartBuildRule\"\n ]\n }\n ]\n}\n",
+ "role": "terra_ci_runner"
+ },
+ "depends_on": [
+ "aws_codebuild_project.terra_ci",
+ "aws_iam_role.terra_ci_job",
+ "aws_iam_role.terra_ci_runner",
+ "aws_s3_bucket.terra_ci",
+ "data.aws_caller_identity.current",
+ "data.template_file.terra_ci"
+ ]
+ },
+ {
+ "address": "aws_iam_role_policy_attachment.terra_ci_job_ecr_access",
+ "mode": "managed",
+ "type": "aws_iam_role_policy_attachment",
+ "name": "terra_ci_job_ecr_access",
+ "provider_name": "registry.terraform.io/hashicorp/aws",
+ "schema_version": 0,
+ "values": {
+ "id": "terra_ci_job-20210505135914799900000002",
+ "policy_arn": "arn:aws:iam::aws:policy/AmazonEC2ContainerRegistryPowerUser",
+ "role": "terra_ci_job"
+ },
+ "depends_on": [
+ "aws_iam_role.terra_ci_job"
+ ]
+ },
+ {
+ "address": "aws_s3_bucket.terra_ci",
+ "mode": "managed",
+ "type": "aws_s3_bucket",
+ "name": "terra_ci",
+ "provider_name": "registry.terraform.io/hashicorp/aws",
+ "schema_version": 0,
+ "values": {
+ "acceleration_status": "",
+ "acl": "private",
+ "arn": "arn:aws:s3:::terra-ci-artifacts-eu-west-1-000002",
+ "bucket": "terra-ci-artifacts-eu-west-1-000002",
+ "bucket_domain_name": "terra-ci-artifacts-eu-west-1-000002.s3.amazonaws.com",
+ "bucket_prefix": null,
+ "bucket_regional_domain_name": "terra-ci-artifacts-eu-west-1-000002.s3.eu-west-1.amazonaws.com",
+ "cors_rule": [],
+ "force_destroy": false,
+ "grant": [],
+ "hosted_zone_id": "Z1BKCTXD74EZPE",
+ "id": "terra-ci-artifacts-eu-west-1-000002",
+ "lifecycle_rule": [],
+ "logging": [],
+ "object_lock_configuration": [],
+ "policy": null,
+ "region": "eu-west-1",
+ "replication_configuration": [],
+ "request_payer": "BucketOwner",
+ "server_side_encryption_configuration": [
+ {
+ "rule": [
+ {
+ "apply_server_side_encryption_by_default": [
+ {
+ "kms_master_key_id": "",
+ "sse_algorithm": "aws:kms"
+ }
+ ],
+ "bucket_key_enabled": false
+ }
+ ]
+ }
+ ],
+ "tags": {},
+ "versioning": [
+ {
+ "enabled": false,
+ "mfa_delete": false
+ }
+ ],
+ "website": [],
+ "website_domain": null,
+ "website_endpoint": null
+ }
+ },
+ {
+ "address": "aws_sfn_state_machine.terra_ci_runner",
+ "mode": "managed",
+ "type": "aws_sfn_state_machine",
+ "name": "terra_ci_runner",
+ "provider_name": "registry.terraform.io/hashicorp/aws",
+ "schema_version": 0,
+ "values": {
+ "arn": "arn:aws:states:eu-west-1:719261439472:stateMachine:terra-ci-runner",
+ "creation_date": "2021-05-05T13:59:28Z",
+ "definition": "{\n \"Comment\": \"Run Terragrunt Jobs\",\n \"StartAt\": \"OnBranch?\",\n \"States\": {\n \"OnBranch?\": {\n \"Type\": \"Choice\",\n \"Choices\": [\n {\n \"Variable\": \"$.build.sourceversion\",\n \"IsPresent\": true,\n \"Next\": \"PlanBranch\"\n }\n ],\n \"Default\": \"Plan\"\n },\n \"Plan\": {\n \"Type\": \"Task\",\n \"Resource\": \"arn:aws:states:::codebuild:startBuild.sync\",\n \"Parameters\": {\n \"ProjectName\": \"terra-ci-runner\",\n \"EnvironmentVariablesOverride\": [\n {\n \"Name\": \"TERRA_CI_BUILD_NAME\",\n \"Value.$\": \"$$.Execution.Name\"\n },\n {\n \"Name\": \"TERRA_CI_RESOURCE\",\n \"Value.$\": \"$.build.environment.terra_ci_resource\"\n }\n ]\n },\n \"End\": true\n },\n \"PlanBranch\": {\n \"Type\": \"Task\",\n \"Resource\": \"arn:aws:states:::codebuild:startBuild.sync\",\n \"Parameters\": {\n \"ProjectName\": \"terra-ci-runner\",\n \"SourceVersion.$\": \"$.build.sourceversion\",\n \"EnvironmentVariablesOverride\": [\n {\n \"Name\": \"TERRA_CI_RESOURCE\",\n \"Value.$\": \"$.build.environment.terra_ci_resource\"\n }\n ]\n },\n \"End\": true\n }\n }\n}\n",
+ "id": "arn:aws:states:eu-west-1:719261439472:stateMachine:terra-ci-runner",
+ "logging_configuration": [
+ {
+ "include_execution_data": false,
+ "level": "OFF",
+ "log_destination": ""
+ }
+ ],
+ "name": "terra-ci-runner",
+ "role_arn": "arn:aws:iam::719261439472:role/terra_ci_runner",
+ "status": "ACTIVE",
+ "tags": {},
+ "type": "STANDARD"
+ },
+ "depends_on": [
+ "aws_iam_role.terra_ci_job",
+ "aws_iam_role.terra_ci_runner",
+ "aws_s3_bucket.terra_ci",
+ "data.template_file.terra_ci",
+ "aws_codebuild_project.terra_ci"
+ ]
+ },
+ {
+ "address": "data.aws_caller_identity.current",
+ "mode": "data",
+ "type": "aws_caller_identity",
+ "name": "current",
+ "provider_name": "registry.terraform.io/hashicorp/aws",
+ "schema_version": 0,
+ "values": {
+ "account_id": "719261439472",
+ "arn": "arn:aws:sts::719261439472:assumed-role/ci/1620223184813487213",
+ "id": "719261439472",
+ "user_id": "AROA2O52SSXYLVFYURBIV:1620223184813487213"
+ }
+ },
+ {
+ "address": "data.template_file.terra_ci",
+ "mode": "data",
+ "type": "template_file",
+ "name": "terra_ci",
+ "provider_name": "registry.terraform.io/hashicorp/template",
+ "schema_version": 0,
+ "values": {
+ "filename": null,
+ "id": "64e36ed71e7270140dde96fec9c89d1d55ae5a6e91f7c0be15170200dcf9481b",
+ "rendered": "version: 0.2\nphases:\n install:\n commands:\n - make install_tools\n build:\n commands:\n - make plan_local resource=$TERRA_CI_RESOURCE\nartifacts:\n files:\n - ./tfplan\n name: $TERRA_CI_BUILD_NAME\n\n",
+ "template": "version: 0.2\nphases:\n install:\n commands:\n - make install_tools\n build:\n commands:\n - make plan_local resource=$TERRA_CI_RESOURCE\nartifacts:\n files:\n - ./tfplan\n name: $TERRA_CI_BUILD_NAME\n\n",
+ "vars": null
+ }
+ }
+ ]
+ }
+ }
+ },
+ "configuration": {
+ "provider_config": {
+ "aws": {
+ "name": "aws",
+ "expressions": {
+ "allowed_account_ids": {
+ "constant_value": [
+ "719261439472"
+ ]
+ },
+ "assume_role": [
+ {
+ "role_arn": {
+ "constant_value": "arn:aws:iam::719261439472:role/ci"
+ }
+ }
+ ],
+ "region": {
+ "constant_value": "eu-west-1"
+ }
+ }
+ }
+ },
+ "root_module": {
+ "resources": [
+ {
+ "address": "aws_codebuild_project.terra_ci",
+ "mode": "managed",
+ "type": "aws_codebuild_project",
+ "name": "terra_ci",
+ "provider_config_key": "aws",
+ "expressions": {
+ "artifacts": [
+ {
+ "location": {
+ "references": [
+ "aws_s3_bucket.terra_ci"
+ ]
+ },
+ "type": {
+ "constant_value": "S3"
+ }
+ }
+ ],
+ "build_timeout": {
+ "constant_value": "10"
+ },
+ "description": {
+ "constant_value": "Deploy environment configuration"
+ },
+ "environment": [
+ {
+ "compute_type": {
+ "constant_value": "BUILD_GENERAL1_SMALL"
+ },
+ "image": {
+ "constant_value": "aws/codebuild/amazonlinux2-x86_64-standard:2.0"
+ },
+ "image_pull_credentials_type": {
+ "constant_value": "CODEBUILD"
+ },
+ "privileged_mode": {
+ "constant_value": false
+ },
+ "type": {
+ "constant_value": "LINUX_CONTAINER"
+ }
+ }
+ ],
+ "logs_config": [
+ {
+ "cloudwatch_logs": [
+ {
+ "status": {
+ "constant_value": "ENABLED"
+ }
+ }
+ ],
+ "s3_logs": [
+ {
+ "encryption_disabled": {
+ "constant_value": false
+ },
+ "status": {
+ "constant_value": "DISABLED"
+ }
+ }
+ ]
+ }
+ ],
+ "name": {
+ "constant_value": "terra-ci-runner"
+ },
+ "service_role": {
+ "references": [
+ "aws_iam_role.terra_ci_job"
+ ]
+ },
+ "source": [
+ {
+ "buildspec": {
+ "references": [
+ "data.template_file.terra_ci"
+ ]
+ },
+ "git_clone_depth": {
+ "constant_value": 1
+ },
+ "insecure_ssl": {
+ "constant_value": false
+ },
+ "location": {
+ "references": [
+ "var.repo_url"
+ ]
+ },
+ "report_build_status": {
+ "constant_value": false
+ },
+ "type": {
+ "constant_value": "GITHUB"
+ }
+ }
+ ]
+ },
+ "schema_version": 0
+ },
+ {
+ "address": "aws_iam_role.terra_ci_job",
+ "mode": "managed",
+ "type": "aws_iam_role",
+ "name": "terra_ci_job",
+ "provider_config_key": "aws",
+ "expressions": {
+ "assume_role_policy": {
+ "constant_value": "{\n \"Version\": \"2012-10-17\",\n \"Statement\": [\n {\n \"Effect\": \"Allow\",\n \"Principal\": {\n \"Service\": \"codebuild.amazonaws.com\"\n },\n \"Action\": \"sts:AssumeRole\"\n }\n ]\n}\n"
+ },
+ "name": {
+ "constant_value": "terra_ci_job"
+ }
+ },
+ "schema_version": 0
+ },
+ {
+ "address": "aws_iam_role.terra_ci_runner",
+ "mode": "managed",
+ "type": "aws_iam_role",
+ "name": "terra_ci_runner",
+ "provider_config_key": "aws",
+ "expressions": {
+ "assume_role_policy": {
+ "constant_value": "{\n \"Version\": \"2012-10-17\",\n \"Statement\": [\n {\n \"Effect\": \"Allow\",\n \"Principal\": {\n \"Service\": \"states.amazonaws.com\"\n },\n \"Action\": \"sts:AssumeRole\"\n }\n ]\n}\n"
+ },
+ "name": {
+ "constant_value": "terra_ci_runner"
+ }
+ },
+ "schema_version": 0
+ },
+ {
+ "address": "aws_iam_role_policy.terra_ci_job",
+ "mode": "managed",
+ "type": "aws_iam_role_policy",
+ "name": "terra_ci_job",
+ "provider_config_key": "aws",
+ "expressions": {
+ "policy": {
+ "references": [
+ "data.aws_caller_identity.current",
+ "aws_s3_bucket.terra_ci",
+ "aws_s3_bucket.terra_ci"
+ ]
+ },
+ "role": {
+ "references": [
+ "aws_iam_role.terra_ci_job"
+ ]
+ }
+ },
+ "schema_version": 0
+ },
+ {
+ "address": "aws_iam_role_policy.terra_ci_runner",
+ "mode": "managed",
+ "type": "aws_iam_role_policy",
+ "name": "terra_ci_runner",
+ "provider_config_key": "aws",
+ "expressions": {
+ "policy": {
+ "references": [
+ "aws_codebuild_project.terra_ci",
+ "var.aws_region",
+ "data.aws_caller_identity.current"
+ ]
+ },
+ "role": {
+ "references": [
+ "aws_iam_role.terra_ci_runner"
+ ]
+ }
+ },
+ "schema_version": 0
+ },
+ {
+ "address": "aws_iam_role_policy_attachment.terra_ci_job_ecr_access",
+ "mode": "managed",
+ "type": "aws_iam_role_policy_attachment",
+ "name": "terra_ci_job_ecr_access",
+ "provider_config_key": "aws",
+ "expressions": {
+ "policy_arn": {
+ "constant_value": "arn:aws:iam::aws:policy/AmazonEC2ContainerRegistryPowerUser"
+ },
+ "role": {
+ "references": [
+ "aws_iam_role.terra_ci_job"
+ ]
+ }
+ },
+ "schema_version": 0
+ },
+ {
+ "address": "aws_s3_bucket.terra_ci",
+ "mode": "managed",
+ "type": "aws_s3_bucket",
+ "name": "terra_ci",
+ "provider_config_key": "aws",
+ "expressions": {
+ "acl": {
+ "constant_value": "private"
+ },
+ "bucket": {
+ "references": [
+ "var.aws_region",
+ "var.serial_number"
+ ]
+ },
+ "server_side_encryption_configuration": [
+ {
+ "rule": [
+ {
+ "apply_server_side_encryption_by_default": [
+ {
+ "sse_algorithm": {
+ "constant_value": "aws:kms"
+ }
+ }
+ ],
+ "bucket_key_enabled": {
+ "constant_value": false
+ }
+ }
+ ]
+ }
+ ]
+ },
+ "schema_version": 0
+ },
+ {
+ "address": "aws_sfn_state_machine.terra_ci_runner",
+ "mode": "managed",
+ "type": "aws_sfn_state_machine",
+ "name": "terra_ci_runner",
+ "provider_config_key": "aws",
+ "expressions": {
+ "definition": {
+ "references": [
+ "aws_codebuild_project.terra_ci",
+ "aws_codebuild_project.terra_ci"
+ ]
+ },
+ "name": {
+ "constant_value": "terra-ci-runner"
+ },
+ "role_arn": {
+ "references": [
+ "aws_iam_role.terra_ci_runner"
+ ]
+ }
+ },
+ "schema_version": 0
+ },
+ {
+ "address": "data.aws_caller_identity.current",
+ "mode": "data",
+ "type": "aws_caller_identity",
+ "name": "current",
+ "provider_config_key": "aws",
+ "schema_version": 0
+ },
+ {
+ "address": "data.template_file.terra_ci",
+ "mode": "data",
+ "type": "template_file",
+ "name": "terra_ci",
+ "provider_config_key": "template",
+ "expressions": {
+ "template": {}
+ },
+ "schema_version": 0
+ }
+ ],
+ "variables": {
+ "aws_region": {},
+ "repo_url": {},
+ "serial_number": {}
+ }
+ }
+ }
+ }
diff --git a/tests/test_files/tf_content_generator_files/tfplan-false-var/tf_content.txt b/tests/test_files/tf_content_generator_files/tfplan-false-var/tf_content.txt
new file mode 100644
index 00000000..5d902651
--- /dev/null
+++ b/tests/test_files/tf_content_generator_files/tfplan-false-var/tf_content.txt
@@ -0,0 +1,14 @@
+resource "aws_s3_bucket" "efrat-env-var-test" {
+ bucket = "efrat-env-var-test"
+ force_destroy = false
+ tags = null
+ timeouts = null
+}
+
+resource "aws_s3_bucket_public_access_block" "efrat-env-var-test" {
+ block_public_acls = false
+ block_public_policy = true
+ ignore_public_acls = false
+ restrict_public_buckets = true
+}
+
diff --git a/tests/test_files/tf_content_generator_files/tfplan-false-var/tfplan.json b/tests/test_files/tf_content_generator_files/tfplan-false-var/tfplan.json
new file mode 100644
index 00000000..2c8d033c
--- /dev/null
+++ b/tests/test_files/tf_content_generator_files/tfplan-false-var/tfplan.json
@@ -0,0 +1,218 @@
+{
+ "format_version": "1.2",
+ "terraform_version": "1.5.4",
+ "variables": {
+ "IT_IS_FALSE": {
+ "value": "false"
+ }
+ },
+ "planned_values": {
+ "root_module": {
+ "resources": [
+ {
+ "address": "aws_s3_bucket.efrat-env-var-test",
+ "mode": "managed",
+ "type": "aws_s3_bucket",
+ "name": "efrat-env-var-test",
+ "provider_name": "registry.terraform.io/hashicorp/aws",
+ "schema_version": 0,
+ "values": {
+ "bucket": "efrat-env-var-test",
+ "force_destroy": false,
+ "tags": null,
+ "timeouts": null
+ },
+ "sensitive_values": {
+ "cors_rule": [],
+ "grant": [],
+ "lifecycle_rule": [],
+ "logging": [],
+ "object_lock_configuration": [],
+ "replication_configuration": [],
+ "server_side_encryption_configuration": [],
+ "tags_all": {},
+ "versioning": [],
+ "website": []
+ }
+ },
+ {
+ "address": "aws_s3_bucket_public_access_block.efrat-env-var-test",
+ "mode": "managed",
+ "type": "aws_s3_bucket_public_access_block",
+ "name": "efrat-env-var-test",
+ "provider_name": "registry.terraform.io/hashicorp/aws",
+ "schema_version": 0,
+ "values": {
+ "block_public_acls": false,
+ "block_public_policy": true,
+ "ignore_public_acls": false,
+ "restrict_public_buckets": true
+ },
+ "sensitive_values": {}
+ }
+ ]
+ }
+ },
+ "resource_changes": [
+ {
+ "address": "aws_s3_bucket.efrat-env-var-test",
+ "mode": "managed",
+ "type": "aws_s3_bucket",
+ "name": "efrat-env-var-test",
+ "provider_name": "registry.terraform.io/hashicorp/aws",
+ "change": {
+ "actions": [
+ "create"
+ ],
+ "before": null,
+ "after": {
+ "bucket": "efrat-env-var-test",
+ "force_destroy": false,
+ "tags": null,
+ "timeouts": null
+ },
+ "after_unknown": {
+ "acceleration_status": true,
+ "acl": true,
+ "arn": true,
+ "bucket_domain_name": true,
+ "bucket_prefix": true,
+ "bucket_regional_domain_name": true,
+ "cors_rule": true,
+ "grant": true,
+ "hosted_zone_id": true,
+ "id": true,
+ "lifecycle_rule": true,
+ "logging": true,
+ "object_lock_configuration": true,
+ "object_lock_enabled": true,
+ "policy": true,
+ "region": true,
+ "replication_configuration": true,
+ "request_payer": true,
+ "server_side_encryption_configuration": true,
+ "tags_all": true,
+ "versioning": true,
+ "website": true,
+ "website_domain": true,
+ "website_endpoint": true
+ },
+ "before_sensitive": false,
+ "after_sensitive": {
+ "cors_rule": [],
+ "grant": [],
+ "lifecycle_rule": [],
+ "logging": [],
+ "object_lock_configuration": [],
+ "replication_configuration": [],
+ "server_side_encryption_configuration": [],
+ "tags_all": {},
+ "versioning": [],
+ "website": []
+ }
+ }
+ },
+ {
+ "address": "aws_s3_bucket_public_access_block.efrat-env-var-test",
+ "mode": "managed",
+ "type": "aws_s3_bucket_public_access_block",
+ "name": "efrat-env-var-test",
+ "provider_name": "registry.terraform.io/hashicorp/aws",
+ "change": {
+ "actions": [
+ "create"
+ ],
+ "before": null,
+ "after": {
+ "block_public_acls": false,
+ "block_public_policy": true,
+ "ignore_public_acls": false,
+ "restrict_public_buckets": true
+ },
+ "after_unknown": {
+ "bucket": true,
+ "id": true
+ },
+ "before_sensitive": false,
+ "after_sensitive": {}
+ }
+ }
+ ],
+ "configuration": {
+ "provider_config": {
+ "aws": {
+ "name": "aws",
+ "full_name": "registry.terraform.io/hashicorp/aws",
+ "expressions": {
+ "profile": {
+ "constant_value": "efrat"
+ },
+ "region": {
+ "constant_value": "us-east-1"
+ }
+ }
+ }
+ },
+ "root_module": {
+ "resources": [
+ {
+ "address": "aws_s3_bucket.efrat-env-var-test",
+ "mode": "managed",
+ "type": "aws_s3_bucket",
+ "name": "efrat-env-var-test",
+ "provider_config_key": "aws",
+ "expressions": {
+ "bucket": {
+ "constant_value": "efrat-env-var-test"
+ }
+ },
+ "schema_version": 0
+ },
+ {
+ "address": "aws_s3_bucket_public_access_block.efrat-env-var-test",
+ "mode": "managed",
+ "type": "aws_s3_bucket_public_access_block",
+ "name": "efrat-env-var-test",
+ "provider_config_key": "aws",
+ "expressions": {
+ "block_public_acls": {
+ "references": [
+ "var.IT_IS_FALSE"
+ ]
+ },
+ "block_public_policy": {
+ "constant_value": true
+ },
+ "bucket": {
+ "references": [
+ "aws_s3_bucket.efrat-env-var-test.id",
+ "aws_s3_bucket.efrat-env-var-test"
+ ]
+ },
+ "ignore_public_acls": {
+ "constant_value": false
+ },
+ "restrict_public_buckets": {
+ "constant_value": true
+ }
+ },
+ "schema_version": 0
+ }
+ ],
+ "variables": {
+ "IT_IS_FALSE": {
+ "description": "This is an example input variable using env variables."
+ }
+ }
+ }
+ },
+ "relevant_attributes": [
+ {
+ "resource": "aws_s3_bucket.efrat-env-var-test",
+ "attribute": [
+ "id"
+ ]
+ }
+ ],
+ "timestamp": "2023-07-31T17:54:18Z"
+}
\ No newline at end of file
diff --git a/tests/test_files/tf_content_generator_files/tfplan-no-op-example/tf_content.txt b/tests/test_files/tf_content_generator_files/tfplan-no-op-example/tf_content.txt
new file mode 100644
index 00000000..be9b8bca
--- /dev/null
+++ b/tests/test_files/tf_content_generator_files/tfplan-no-op-example/tf_content.txt
@@ -0,0 +1,122 @@
+resource "aws_codebuild_project" "terra_ci" {
+ arn = "arn:aws:codebuild:eu-west-1:719261439472:project/terra-ci-runner"
+ artifacts = [{"artifact_identifier": "", "encryption_disabled": false, "location": "terra-ci-artifacts-eu-west-1-000002", "name": "terra-ci-runner", "namespace_type": "NONE", "override_artifact_name": false, "packaging": "NONE", "path": "", "type": "S3"}]
+ badge_enabled = false
+ badge_url = ""
+ build_timeout = 10
+ cache = [{"location": "", "modes": [], "type": "NO_CACHE"}]
+ description = "Deploy environment configuration"
+ encryption_key = "arn:aws:kms:eu-west-1:719261439472:alias/aws/s3"
+ environment = [{"certificate": "", "compute_type": "BUILD_GENERAL1_SMALL", "environment_variable": [], "image": "aws/codebuild/amazonlinux2-x86_64-standard:2.0", "image_pull_credentials_type": "CODEBUILD", "privileged_mode": false, "registry_credential": [], "type": "LINUX_CONTAINER"}]
+ id = "arn:aws:codebuild:eu-west-1:719261439472:project/terra-ci-runner"
+ logs_config = [{"cloudwatch_logs": [{"group_name": "", "status": "ENABLED", "stream_name": ""}], "s3_logs": [{"encryption_disabled": false, "location": "", "status": "DISABLED"}]}]
+ name = "terra-ci-runner"
+ queued_timeout = 480
+ secondary_artifacts = []
+ secondary_sources = []
+ service_role = "arn:aws:iam::719261439472:role/terra_ci_job"
+ source = [{"auth": [], "buildspec": "version: 0.2\nphases:\n install:\n commands:\n - make install_tools\n build:\n commands:\n - make plan_local resource=$TERRA_CI_RESOURCE\nartifacts:\n files:\n - ./tfplan\n name: $TERRA_CI_BUILD_NAME\n\n", "git_clone_depth": 1, "git_submodules_config": [], "insecure_ssl": false, "location": "https://github.com/p0tr3c-terraform/terra-ci-single-account.git", "report_build_status": false, "type": "GITHUB"}]
+ source_version = ""
+ tags = {}
+ vpc_config = []
+}
+
+resource "aws_iam_role" "terra_ci_job" {
+ arn = "arn:aws:iam::719261439472:role/terra_ci_job"
+ assume_role_policy = "{\"Version\":\"2012-10-17\",\"Statement\":[{\"Effect\":\"Allow\",\"Principal\":{\"Service\":\"codebuild.amazonaws.com\"},\"Action\":\"sts:AssumeRole\"}]}"
+ create_date = "2021-05-01T15:08:15Z"
+ description = ""
+ force_detach_policies = false
+ id = "terra_ci_job"
+ inline_policy = [{"name": "terraform-20210501150816628700000001", "policy": "{\n \"Version\": \"2012-10-17\",\n \"Statement\": [\n {\n \"Effect\": \"Allow\",\n \"Action\": \"sts:AssumeRole\",\n \"Resource\": \"arn:aws:iam::719261439472:role/ci\"\n },\n {\n \"Effect\": \"Allow\",\n \"Resource\": [\n \"*\"\n ],\n \"Action\": [\n \"logs:CreateLogGroup\",\n \"logs:CreateLogStream\",\n \"logs:PutLogEvents\"\n ]\n },\n {\n \"Effect\": \"Allow\",\n \"Resource\": [\n \"arn:aws:s3:::terra-ci-artifacts-eu-west-1-000002\",\n \"arn:aws:s3:::terra-ci-artifacts-eu-west-1-000002/*\"\n ],\n \"Action\": [\n \"s3:ListBucket\",\n \"s3:*Object\"\n ]\n }\n ]\n}\n"}]
+ managed_policy_arns = ["arn:aws:iam::aws:policy/AmazonEC2ContainerRegistryPowerUser"]
+ max_session_duration = 3600
+ name = "terra_ci_job"
+ name_prefix = null
+ path = "/"
+ permissions_boundary = null
+ tags = {}
+ unique_id = "AROA2O52SSXYL7LBSM733"
+}
+
+resource "aws_iam_role" "terra_ci_runner" {
+ arn = "arn:aws:iam::719261439472:role/terra_ci_runner"
+ assume_role_policy = "{\"Version\":\"2012-10-17\",\"Statement\":[{\"Effect\":\"Allow\",\"Principal\":{\"Service\":\"states.amazonaws.com\"},\"Action\":\"sts:AssumeRole\"}]}"
+ create_date = "2021-05-01T15:08:15Z"
+ description = ""
+ force_detach_policies = false
+ id = "terra_ci_runner"
+ inline_policy = [{"name": "terraform-20210501150825425000000003", "policy": "{\n \"Version\": \"2012-10-17\",\n \"Statement\": [\n {\n \"Effect\": \"Allow\",\n \"Action\": [\n \"codebuild:StartBuild\",\n \"codebuild:StopBuild\",\n \"codebuild:BatchGetBuilds\"\n ],\n \"Resource\": [\n \"arn:aws:codebuild:eu-west-1:719261439472:project/terra-ci-runner\"\n ]\n },\n {\n \"Effect\": \"Allow\",\n \"Action\": [\n \"events:PutTargets\",\n \"events:PutRule\",\n \"events:DescribeRule\"\n ],\n \"Resource\": [\n \"arn:aws:events:eu-west-1:719261439472:rule/StepFunctionsGetEventForCodeBuildStartBuildRule\"\n ]\n }\n ]\n}\n"}]
+ managed_policy_arns = []
+ max_session_duration = 3600
+ name = "terra_ci_runner"
+ name_prefix = null
+ path = "/"
+ permissions_boundary = null
+ tags = {}
+ unique_id = "AROA2O52SSXYDBYYTG4OB"
+}
+
+resource "aws_iam_role_policy" "terra_ci_job" {
+ id = "terra_ci_job:terraform-20210501150816628700000001"
+ name = "terraform-20210501150816628700000001"
+ name_prefix = null
+ policy = "{\n \"Version\": \"2012-10-17\",\n \"Statement\": [\n {\n \"Effect\": \"Allow\",\n \"Action\": \"sts:AssumeRole\",\n \"Resource\": \"arn:aws:iam::719261439472:role/ci\"\n },\n {\n \"Effect\": \"Allow\",\n \"Resource\": [\n \"*\"\n ],\n \"Action\": [\n \"logs:CreateLogGroup\",\n \"logs:CreateLogStream\",\n \"logs:PutLogEvents\"\n ]\n },\n {\n \"Effect\": \"Allow\",\n \"Resource\": [\n \"arn:aws:s3:::terra-ci-artifacts-eu-west-1-000002\",\n \"arn:aws:s3:::terra-ci-artifacts-eu-west-1-000002/*\"\n ],\n \"Action\": [\n \"s3:ListBucket\",\n \"s3:*Object\"\n ]\n }\n ]\n}\n"
+ role = "terra_ci_job"
+}
+
+resource "aws_iam_role_policy" "terra_ci_runner" {
+ id = "terra_ci_runner:terraform-20210501150825425000000003"
+ name = "terraform-20210501150825425000000003"
+ name_prefix = null
+ policy = "{\n \"Version\": \"2012-10-17\",\n \"Statement\": [\n {\n \"Effect\": \"Allow\",\n \"Action\": [\n \"codebuild:StartBuild\",\n \"codebuild:StopBuild\",\n \"codebuild:BatchGetBuilds\"\n ],\n \"Resource\": [\n \"arn:aws:codebuild:eu-west-1:719261439472:project/terra-ci-runner\"\n ]\n },\n {\n \"Effect\": \"Allow\",\n \"Action\": [\n \"events:PutTargets\",\n \"events:PutRule\",\n \"events:DescribeRule\"\n ],\n \"Resource\": [\n \"arn:aws:events:eu-west-1:719261439472:rule/StepFunctionsGetEventForCodeBuildStartBuildRule\"\n ]\n }\n ]\n}\n"
+ role = "terra_ci_runner"
+}
+
+resource "aws_iam_role_policy_attachment" "terra_ci_job_ecr_access" {
+ id = "terra_ci_job-20210501150817089800000002"
+ policy_arn = "arn:aws:iam::aws:policy/AmazonEC2ContainerRegistryPowerUser"
+ role = "terra_ci_job"
+}
+
+resource "aws_s3_bucket" "terra_ci" {
+ acceleration_status = ""
+ acl = "private"
+ arn = "arn:aws:s3:::terra-ci-artifacts-eu-west-1-000002"
+ bucket = "terra-ci-artifacts-eu-west-1-000002"
+ bucket_domain_name = "terra-ci-artifacts-eu-west-1-000002.s3.amazonaws.com"
+ bucket_prefix = null
+ bucket_regional_domain_name = "terra-ci-artifacts-eu-west-1-000002.s3.eu-west-1.amazonaws.com"
+ cors_rule = []
+ force_destroy = false
+ grant = []
+ hosted_zone_id = "Z1BKCTXD74EZPE"
+ id = "terra-ci-artifacts-eu-west-1-000002"
+ lifecycle_rule = []
+ logging = []
+ object_lock_configuration = []
+ policy = null
+ region = "eu-west-1"
+ replication_configuration = []
+ request_payer = "BucketOwner"
+ server_side_encryption_configuration = [{"rule": [{"apply_server_side_encryption_by_default": [{"kms_master_key_id": "", "sse_algorithm": "aws:kms"}], "bucket_key_enabled": false}]}]
+ tags = {}
+ versioning = [{"enabled": false, "mfa_delete": false}]
+ website = []
+ website_domain = null
+ website_endpoint = null
+}
+
+resource "aws_sfn_state_machine" "terra_ci_runner" {
+ arn = "arn:aws:states:eu-west-1:719261439472:stateMachine:terra-ci-runner"
+ creation_date = "2021-05-01T15:09:28Z"
+ definition = "{\n \"Comment\": \"Run Terragrunt Jobs\",\n \"StartAt\": \"OnBranch?\",\n \"States\": {\n \"OnBranch?\": {\n \"Type\": \"Choice\",\n \"Choices\": [\n {\n \"Variable\": \"$.build.sourceversion\",\n \"IsPresent\": true,\n \"Next\": \"PlanBranch\"\n }\n ],\n \"Default\": \"Plan\"\n },\n \"Plan\": {\n \"Type\": \"Task\",\n \"Resource\": \"arn:aws:states:::codebuild:startBuild.sync\",\n \"Parameters\": {\n \"ProjectName\": \"terra-ci-runner\",\n \"EnvironmentVariablesOverride\": [\n {\n \"Name\": \"TERRA_CI_BUILD_NAME\",\n \"Value.$\": \"$$.Execution.Name\"\n },\n {\n \"Name\": \"TERRA_CI_RESOURCE\",\n \"Value.$\": \"$.build.environment.terra_ci_resource\"\n }\n ]\n },\n \"End\": true\n },\n \"PlanBranch\": {\n \"Type\": \"Task\",\n \"Resource\": \"arn:aws:states:::codebuild:startBuild.sync\",\n \"Parameters\": {\n \"ProjectName\": \"terra-ci-runner\",\n \"SourceVersion.$\": \"$.build.sourceversion\",\n \"EnvironmentVariablesOverride\": [\n {\n \"Name\": \"TERRA_CI_RESOURCE\",\n \"Value.$\": \"$.build.environment.terra_ci_resource\"\n }\n ]\n },\n \"End\": true\n }\n }\n}\n"
+ id = "arn:aws:states:eu-west-1:719261439472:stateMachine:terra-ci-runner"
+ logging_configuration = [{"include_execution_data": false, "level": "OFF", "log_destination": ""}]
+ name = "terra-ci-runner"
+ role_arn = "arn:aws:iam::719261439472:role/terra_ci_runner"
+ status = "ACTIVE"
+ tags = {}
+ type = "STANDARD"
+}
+
diff --git a/tests/test_files/tf_content_generator_files/tfplan-no-op-example/tfplan.json b/tests/test_files/tf_content_generator_files/tfplan-no-op-example/tfplan.json
new file mode 100644
index 00000000..e31a7ea5
--- /dev/null
+++ b/tests/test_files/tf_content_generator_files/tfplan-no-op-example/tfplan.json
@@ -0,0 +1,1634 @@
+{
+ "comment-for-reader": "THIS TERRAFORM FILE REPRESENTS A REAL TF-PLAN OUTPUT WHICH HAS VULNERABILITES IN IT'S CURRENT STATE, BUT NOT IN PROPOSED RESOURCE CHANGES",
+ "format_version": "0.1",
+ "terraform_version": "0.15.0",
+ "variables": {
+ "aws_region": {
+ "value": "eu-west-1"
+ },
+ "repo_url": {
+ "value": "https://github.com/p0tr3c-terraform/terra-ci-single-account.git"
+ },
+ "serial_number": {
+ "value": "000002"
+ }
+ },
+ "planned_values": {
+ "root_module": {
+ "resources": [
+ {
+ "address": "aws_codebuild_project.terra_ci",
+ "mode": "managed",
+ "type": "aws_codebuild_project",
+ "name": "terra_ci",
+ "provider_name": "registry.terraform.io/hashicorp/aws",
+ "schema_version": 0,
+ "values": {
+ "arn": "arn:aws:codebuild:eu-west-1:719261439472:project/terra-ci-runner",
+ "artifacts": [
+ {
+ "artifact_identifier": "",
+ "encryption_disabled": false,
+ "location": "terra-ci-artifacts-eu-west-1-000002",
+ "name": "terra-ci-runner",
+ "namespace_type": "NONE",
+ "override_artifact_name": false,
+ "packaging": "NONE",
+ "path": "",
+ "type": "S3"
+ }
+ ],
+ "badge_enabled": false,
+ "badge_url": "",
+ "build_timeout": 10,
+ "cache": [
+ {
+ "location": "",
+ "modes": [],
+ "type": "NO_CACHE"
+ }
+ ],
+ "description": "Deploy environment configuration",
+ "encryption_key": "arn:aws:kms:eu-west-1:719261439472:alias/aws/s3",
+ "environment": [
+ {
+ "certificate": "",
+ "compute_type": "BUILD_GENERAL1_SMALL",
+ "environment_variable": [],
+ "image": "aws/codebuild/amazonlinux2-x86_64-standard:2.0",
+ "image_pull_credentials_type": "CODEBUILD",
+ "privileged_mode": false,
+ "registry_credential": [],
+ "type": "LINUX_CONTAINER"
+ }
+ ],
+ "id": "arn:aws:codebuild:eu-west-1:719261439472:project/terra-ci-runner",
+ "logs_config": [
+ {
+ "cloudwatch_logs": [
+ {
+ "group_name": "",
+ "status": "ENABLED",
+ "stream_name": ""
+ }
+ ],
+ "s3_logs": [
+ {
+ "encryption_disabled": false,
+ "location": "",
+ "status": "DISABLED"
+ }
+ ]
+ }
+ ],
+ "name": "terra-ci-runner",
+ "queued_timeout": 480,
+ "secondary_artifacts": [],
+ "secondary_sources": [],
+ "service_role": "arn:aws:iam::719261439472:role/terra_ci_job",
+ "source": [
+ {
+ "auth": [],
+ "buildspec": "version: 0.2\nphases:\n install:\n commands:\n - make install_tools\n build:\n commands:\n - make plan_local resource=$TERRA_CI_RESOURCE\nartifacts:\n files:\n - ./tfplan\n name: $TERRA_CI_BUILD_NAME\n\n",
+ "git_clone_depth": 1,
+ "git_submodules_config": [],
+ "insecure_ssl": false,
+ "location": "https://github.com/p0tr3c-terraform/terra-ci-single-account.git",
+ "report_build_status": false,
+ "type": "GITHUB"
+ }
+ ],
+ "source_version": "",
+ "tags": {},
+ "vpc_config": []
+ }
+ },
+ {
+ "address": "aws_iam_role.terra_ci_job",
+ "mode": "managed",
+ "type": "aws_iam_role",
+ "name": "terra_ci_job",
+ "provider_name": "registry.terraform.io/hashicorp/aws",
+ "schema_version": 0,
+ "values": {
+ "arn": "arn:aws:iam::719261439472:role/terra_ci_job",
+ "assume_role_policy": "{\"Version\":\"2012-10-17\",\"Statement\":[{\"Effect\":\"Allow\",\"Principal\":{\"Service\":\"codebuild.amazonaws.com\"},\"Action\":\"sts:AssumeRole\"}]}",
+ "create_date": "2021-05-01T15:08:15Z",
+ "description": "",
+ "force_detach_policies": false,
+ "id": "terra_ci_job",
+ "inline_policy": [
+ {
+ "name": "terraform-20210501150816628700000001",
+ "policy": "{\n \"Version\": \"2012-10-17\",\n \"Statement\": [\n {\n \"Effect\": \"Allow\",\n \"Action\": \"sts:AssumeRole\",\n \"Resource\": \"arn:aws:iam::719261439472:role/ci\"\n },\n {\n \"Effect\": \"Allow\",\n \"Resource\": [\n \"*\"\n ],\n \"Action\": [\n \"logs:CreateLogGroup\",\n \"logs:CreateLogStream\",\n \"logs:PutLogEvents\"\n ]\n },\n {\n \"Effect\": \"Allow\",\n \"Resource\": [\n \"arn:aws:s3:::terra-ci-artifacts-eu-west-1-000002\",\n \"arn:aws:s3:::terra-ci-artifacts-eu-west-1-000002/*\"\n ],\n \"Action\": [\n \"s3:ListBucket\",\n \"s3:*Object\"\n ]\n }\n ]\n}\n"
+ }
+ ],
+ "managed_policy_arns": [
+ "arn:aws:iam::aws:policy/AmazonEC2ContainerRegistryPowerUser"
+ ],
+ "max_session_duration": 3600,
+ "name": "terra_ci_job",
+ "name_prefix": null,
+ "path": "/",
+ "permissions_boundary": null,
+ "tags": {},
+ "unique_id": "AROA2O52SSXYL7LBSM733"
+ }
+ },
+ {
+ "address": "aws_iam_role.terra_ci_runner",
+ "mode": "managed",
+ "type": "aws_iam_role",
+ "name": "terra_ci_runner",
+ "provider_name": "registry.terraform.io/hashicorp/aws",
+ "schema_version": 0,
+ "values": {
+ "arn": "arn:aws:iam::719261439472:role/terra_ci_runner",
+ "assume_role_policy": "{\"Version\":\"2012-10-17\",\"Statement\":[{\"Effect\":\"Allow\",\"Principal\":{\"Service\":\"states.amazonaws.com\"},\"Action\":\"sts:AssumeRole\"}]}",
+ "create_date": "2021-05-01T15:08:15Z",
+ "description": "",
+ "force_detach_policies": false,
+ "id": "terra_ci_runner",
+ "inline_policy": [
+ {
+ "name": "terraform-20210501150825425000000003",
+ "policy": "{\n \"Version\": \"2012-10-17\",\n \"Statement\": [\n {\n \"Effect\": \"Allow\",\n \"Action\": [\n \"codebuild:StartBuild\",\n \"codebuild:StopBuild\",\n \"codebuild:BatchGetBuilds\"\n ],\n \"Resource\": [\n \"arn:aws:codebuild:eu-west-1:719261439472:project/terra-ci-runner\"\n ]\n },\n {\n \"Effect\": \"Allow\",\n \"Action\": [\n \"events:PutTargets\",\n \"events:PutRule\",\n \"events:DescribeRule\"\n ],\n \"Resource\": [\n \"arn:aws:events:eu-west-1:719261439472:rule/StepFunctionsGetEventForCodeBuildStartBuildRule\"\n ]\n }\n ]\n}\n"
+ }
+ ],
+ "managed_policy_arns": [],
+ "max_session_duration": 3600,
+ "name": "terra_ci_runner",
+ "name_prefix": null,
+ "path": "/",
+ "permissions_boundary": null,
+ "tags": {},
+ "unique_id": "AROA2O52SSXYDBYYTG4OB"
+ }
+ },
+ {
+ "address": "aws_iam_role_policy.terra_ci_job",
+ "mode": "managed",
+ "type": "aws_iam_role_policy",
+ "name": "terra_ci_job",
+ "provider_name": "registry.terraform.io/hashicorp/aws",
+ "schema_version": 0,
+ "values": {
+ "id": "terra_ci_job:terraform-20210501150816628700000001",
+ "name": "terraform-20210501150816628700000001",
+ "name_prefix": null,
+ "policy": "{\n \"Version\": \"2012-10-17\",\n \"Statement\": [\n {\n \"Effect\": \"Allow\",\n \"Action\": \"sts:AssumeRole\",\n \"Resource\": \"arn:aws:iam::719261439472:role/ci\"\n },\n {\n \"Effect\": \"Allow\",\n \"Resource\": [\n \"*\"\n ],\n \"Action\": [\n \"logs:CreateLogGroup\",\n \"logs:CreateLogStream\",\n \"logs:PutLogEvents\"\n ]\n },\n {\n \"Effect\": \"Allow\",\n \"Resource\": [\n \"arn:aws:s3:::terra-ci-artifacts-eu-west-1-000002\",\n \"arn:aws:s3:::terra-ci-artifacts-eu-west-1-000002/*\"\n ],\n \"Action\": [\n \"s3:ListBucket\",\n \"s3:*Object\"\n ]\n }\n ]\n}\n",
+ "role": "terra_ci_job"
+ }
+ },
+ {
+ "address": "aws_iam_role_policy.terra_ci_runner",
+ "mode": "managed",
+ "type": "aws_iam_role_policy",
+ "name": "terra_ci_runner",
+ "provider_name": "registry.terraform.io/hashicorp/aws",
+ "schema_version": 0,
+ "values": {
+ "id": "terra_ci_runner:terraform-20210501150825425000000003",
+ "name": "terraform-20210501150825425000000003",
+ "name_prefix": null,
+ "policy": "{\n \"Version\": \"2012-10-17\",\n \"Statement\": [\n {\n \"Effect\": \"Allow\",\n \"Action\": [\n \"codebuild:StartBuild\",\n \"codebuild:StopBuild\",\n \"codebuild:BatchGetBuilds\"\n ],\n \"Resource\": [\n \"arn:aws:codebuild:eu-west-1:719261439472:project/terra-ci-runner\"\n ]\n },\n {\n \"Effect\": \"Allow\",\n \"Action\": [\n \"events:PutTargets\",\n \"events:PutRule\",\n \"events:DescribeRule\"\n ],\n \"Resource\": [\n \"arn:aws:events:eu-west-1:719261439472:rule/StepFunctionsGetEventForCodeBuildStartBuildRule\"\n ]\n }\n ]\n}\n",
+ "role": "terra_ci_runner"
+ }
+ },
+ {
+ "address": "aws_iam_role_policy_attachment.terra_ci_job_ecr_access",
+ "mode": "managed",
+ "type": "aws_iam_role_policy_attachment",
+ "name": "terra_ci_job_ecr_access",
+ "provider_name": "registry.terraform.io/hashicorp/aws",
+ "schema_version": 0,
+ "values": {
+ "id": "terra_ci_job-20210501150817089800000002",
+ "policy_arn": "arn:aws:iam::aws:policy/AmazonEC2ContainerRegistryPowerUser",
+ "role": "terra_ci_job"
+ }
+ },
+ {
+ "address": "aws_s3_bucket.terra_ci",
+ "mode": "managed",
+ "type": "aws_s3_bucket",
+ "name": "terra_ci",
+ "provider_name": "registry.terraform.io/hashicorp/aws",
+ "schema_version": 0,
+ "values": {
+ "acceleration_status": "",
+ "acl": "private",
+ "arn": "arn:aws:s3:::terra-ci-artifacts-eu-west-1-000002",
+ "bucket": "terra-ci-artifacts-eu-west-1-000002",
+ "bucket_domain_name": "terra-ci-artifacts-eu-west-1-000002.s3.amazonaws.com",
+ "bucket_prefix": null,
+ "bucket_regional_domain_name": "terra-ci-artifacts-eu-west-1-000002.s3.eu-west-1.amazonaws.com",
+ "cors_rule": [],
+ "force_destroy": false,
+ "grant": [],
+ "hosted_zone_id": "Z1BKCTXD74EZPE",
+ "id": "terra-ci-artifacts-eu-west-1-000002",
+ "lifecycle_rule": [],
+ "logging": [],
+ "object_lock_configuration": [],
+ "policy": null,
+ "region": "eu-west-1",
+ "replication_configuration": [],
+ "request_payer": "BucketOwner",
+ "server_side_encryption_configuration": [
+ {
+ "rule": [
+ {
+ "apply_server_side_encryption_by_default": [
+ {
+ "kms_master_key_id": "",
+ "sse_algorithm": "aws:kms"
+ }
+ ],
+ "bucket_key_enabled": false
+ }
+ ]
+ }
+ ],
+ "tags": {},
+ "versioning": [
+ {
+ "enabled": false,
+ "mfa_delete": false
+ }
+ ],
+ "website": [],
+ "website_domain": null,
+ "website_endpoint": null
+ }
+ },
+ {
+ "address": "aws_sfn_state_machine.terra_ci_runner",
+ "mode": "managed",
+ "type": "aws_sfn_state_machine",
+ "name": "terra_ci_runner",
+ "provider_name": "registry.terraform.io/hashicorp/aws",
+ "schema_version": 0,
+ "values": {
+ "arn": "arn:aws:states:eu-west-1:719261439472:stateMachine:terra-ci-runner",
+ "creation_date": "2021-05-01T15:09:28Z",
+ "definition": "{\n \"Comment\": \"Run Terragrunt Jobs\",\n \"StartAt\": \"OnBranch?\",\n \"States\": {\n \"OnBranch?\": {\n \"Type\": \"Choice\",\n \"Choices\": [\n {\n \"Variable\": \"$.build.sourceversion\",\n \"IsPresent\": true,\n \"Next\": \"PlanBranch\"\n }\n ],\n \"Default\": \"Plan\"\n },\n \"Plan\": {\n \"Type\": \"Task\",\n \"Resource\": \"arn:aws:states:::codebuild:startBuild.sync\",\n \"Parameters\": {\n \"ProjectName\": \"terra-ci-runner\",\n \"EnvironmentVariablesOverride\": [\n {\n \"Name\": \"TERRA_CI_BUILD_NAME\",\n \"Value.$\": \"$$.Execution.Name\"\n },\n {\n \"Name\": \"TERRA_CI_RESOURCE\",\n \"Value.$\": \"$.build.environment.terra_ci_resource\"\n }\n ]\n },\n \"End\": true\n },\n \"PlanBranch\": {\n \"Type\": \"Task\",\n \"Resource\": \"arn:aws:states:::codebuild:startBuild.sync\",\n \"Parameters\": {\n \"ProjectName\": \"terra-ci-runner\",\n \"SourceVersion.$\": \"$.build.sourceversion\",\n \"EnvironmentVariablesOverride\": [\n {\n \"Name\": \"TERRA_CI_RESOURCE\",\n \"Value.$\": \"$.build.environment.terra_ci_resource\"\n }\n ]\n },\n \"End\": true\n }\n }\n}\n",
+ "id": "arn:aws:states:eu-west-1:719261439472:stateMachine:terra-ci-runner",
+ "logging_configuration": [
+ {
+ "include_execution_data": false,
+ "level": "OFF",
+ "log_destination": ""
+ }
+ ],
+ "name": "terra-ci-runner",
+ "role_arn": "arn:aws:iam::719261439472:role/terra_ci_runner",
+ "status": "ACTIVE",
+ "tags": {},
+ "type": "STANDARD"
+ }
+ }
+ ]
+ }
+ },
+ "resource_changes": [
+ {
+ "address": "aws_codebuild_project.terra_ci",
+ "mode": "managed",
+ "type": "aws_codebuild_project",
+ "name": "terra_ci",
+ "provider_name": "registry.terraform.io/hashicorp/aws",
+ "change": {
+ "actions": [
+ "no-op"
+ ],
+ "before": {
+ "arn": "arn:aws:codebuild:eu-west-1:719261439472:project/terra-ci-runner",
+ "artifacts": [
+ {
+ "artifact_identifier": "",
+ "encryption_disabled": false,
+ "location": "terra-ci-artifacts-eu-west-1-000002",
+ "name": "terra-ci-runner",
+ "namespace_type": "NONE",
+ "override_artifact_name": false,
+ "packaging": "NONE",
+ "path": "",
+ "type": "S3"
+ }
+ ],
+ "badge_enabled": false,
+ "badge_url": "",
+ "build_timeout": 10,
+ "cache": [
+ {
+ "location": "",
+ "modes": [],
+ "type": "NO_CACHE"
+ }
+ ],
+ "description": "Deploy environment configuration",
+ "encryption_key": "arn:aws:kms:eu-west-1:719261439472:alias/aws/s3",
+ "environment": [
+ {
+ "certificate": "",
+ "compute_type": "BUILD_GENERAL1_SMALL",
+ "environment_variable": [],
+ "image": "aws/codebuild/amazonlinux2-x86_64-standard:2.0",
+ "image_pull_credentials_type": "CODEBUILD",
+ "privileged_mode": false,
+ "registry_credential": [],
+ "type": "LINUX_CONTAINER"
+ }
+ ],
+ "id": "arn:aws:codebuild:eu-west-1:719261439472:project/terra-ci-runner",
+ "logs_config": [
+ {
+ "cloudwatch_logs": [
+ {
+ "group_name": "",
+ "status": "ENABLED",
+ "stream_name": ""
+ }
+ ],
+ "s3_logs": [
+ {
+ "encryption_disabled": false,
+ "location": "",
+ "status": "DISABLED"
+ }
+ ]
+ }
+ ],
+ "name": "terra-ci-runner",
+ "queued_timeout": 480,
+ "secondary_artifacts": [],
+ "secondary_sources": [],
+ "service_role": "arn:aws:iam::719261439472:role/terra_ci_job",
+ "source": [
+ {
+ "auth": [],
+ "buildspec": "version: 0.2\nphases:\n install:\n commands:\n - make install_tools\n build:\n commands:\n - make plan_local resource=$TERRA_CI_RESOURCE\nartifacts:\n files:\n - ./tfplan\n name: $TERRA_CI_BUILD_NAME\n\n",
+ "git_clone_depth": 1,
+ "git_submodules_config": [],
+ "insecure_ssl": false,
+ "location": "https://github.com/p0tr3c-terraform/terra-ci-single-account.git",
+ "report_build_status": false,
+ "type": "GITHUB"
+ }
+ ],
+ "source_version": "",
+ "tags": {},
+ "vpc_config": []
+ },
+ "after": {
+ "arn": "arn:aws:codebuild:eu-west-1:719261439472:project/terra-ci-runner",
+ "artifacts": [
+ {
+ "artifact_identifier": "",
+ "encryption_disabled": false,
+ "location": "terra-ci-artifacts-eu-west-1-000002",
+ "name": "terra-ci-runner",
+ "namespace_type": "NONE",
+ "override_artifact_name": false,
+ "packaging": "NONE",
+ "path": "",
+ "type": "S3"
+ }
+ ],
+ "badge_enabled": false,
+ "badge_url": "",
+ "build_timeout": 10,
+ "cache": [
+ {
+ "location": "",
+ "modes": [],
+ "type": "NO_CACHE"
+ }
+ ],
+ "description": "Deploy environment configuration",
+ "encryption_key": "arn:aws:kms:eu-west-1:719261439472:alias/aws/s3",
+ "environment": [
+ {
+ "certificate": "",
+ "compute_type": "BUILD_GENERAL1_SMALL",
+ "environment_variable": [],
+ "image": "aws/codebuild/amazonlinux2-x86_64-standard:2.0",
+ "image_pull_credentials_type": "CODEBUILD",
+ "privileged_mode": false,
+ "registry_credential": [],
+ "type": "LINUX_CONTAINER"
+ }
+ ],
+ "id": "arn:aws:codebuild:eu-west-1:719261439472:project/terra-ci-runner",
+ "logs_config": [
+ {
+ "cloudwatch_logs": [
+ {
+ "group_name": "",
+ "status": "ENABLED",
+ "stream_name": ""
+ }
+ ],
+ "s3_logs": [
+ {
+ "encryption_disabled": false,
+ "location": "",
+ "status": "DISABLED"
+ }
+ ]
+ }
+ ],
+ "name": "terra-ci-runner",
+ "queued_timeout": 480,
+ "secondary_artifacts": [],
+ "secondary_sources": [],
+ "service_role": "arn:aws:iam::719261439472:role/terra_ci_job",
+ "source": [
+ {
+ "auth": [],
+ "buildspec": "version: 0.2\nphases:\n install:\n commands:\n - make install_tools\n build:\n commands:\n - make plan_local resource=$TERRA_CI_RESOURCE\nartifacts:\n files:\n - ./tfplan\n name: $TERRA_CI_BUILD_NAME\n\n",
+ "git_clone_depth": 1,
+ "git_submodules_config": [],
+ "insecure_ssl": false,
+ "location": "https://github.com/p0tr3c-terraform/terra-ci-single-account.git",
+ "report_build_status": false,
+ "type": "GITHUB"
+ }
+ ],
+ "source_version": "",
+ "tags": {},
+ "vpc_config": []
+ },
+ "after_unknown": {},
+ "before_sensitive": {
+ "artifacts": [
+ {}
+ ],
+ "cache": [
+ {
+ "modes": []
+ }
+ ],
+ "environment": [
+ {
+ "environment_variable": [],
+ "registry_credential": []
+ }
+ ],
+ "logs_config": [
+ {
+ "cloudwatch_logs": [
+ {}
+ ],
+ "s3_logs": [
+ {}
+ ]
+ }
+ ],
+ "secondary_artifacts": [],
+ "secondary_sources": [],
+ "source": [
+ {
+ "auth": [],
+ "git_submodules_config": []
+ }
+ ],
+ "tags": {},
+ "vpc_config": []
+ },
+ "after_sensitive": {
+ "artifacts": [
+ {}
+ ],
+ "cache": [
+ {
+ "modes": []
+ }
+ ],
+ "environment": [
+ {
+ "environment_variable": [],
+ "registry_credential": []
+ }
+ ],
+ "logs_config": [
+ {
+ "cloudwatch_logs": [
+ {}
+ ],
+ "s3_logs": [
+ {}
+ ]
+ }
+ ],
+ "secondary_artifacts": [],
+ "secondary_sources": [],
+ "source": [
+ {
+ "auth": [],
+ "git_submodules_config": []
+ }
+ ],
+ "tags": {},
+ "vpc_config": []
+ }
+ }
+ },
+ {
+ "address": "aws_iam_role.terra_ci_job",
+ "mode": "managed",
+ "type": "aws_iam_role",
+ "name": "terra_ci_job",
+ "provider_name": "registry.terraform.io/hashicorp/aws",
+ "change": {
+ "actions": [
+ "no-op"
+ ],
+ "before": {
+ "arn": "arn:aws:iam::719261439472:role/terra_ci_job",
+ "assume_role_policy": "{\"Version\":\"2012-10-17\",\"Statement\":[{\"Effect\":\"Allow\",\"Principal\":{\"Service\":\"codebuild.amazonaws.com\"},\"Action\":\"sts:AssumeRole\"}]}",
+ "create_date": "2021-05-01T15:08:15Z",
+ "description": "",
+ "force_detach_policies": false,
+ "id": "terra_ci_job",
+ "inline_policy": [
+ {
+ "name": "terraform-20210501150816628700000001",
+ "policy": "{\n \"Version\": \"2012-10-17\",\n \"Statement\": [\n {\n \"Effect\": \"Allow\",\n \"Action\": \"sts:AssumeRole\",\n \"Resource\": \"arn:aws:iam::719261439472:role/ci\"\n },\n {\n \"Effect\": \"Allow\",\n \"Resource\": [\n \"*\"\n ],\n \"Action\": [\n \"logs:CreateLogGroup\",\n \"logs:CreateLogStream\",\n \"logs:PutLogEvents\"\n ]\n },\n {\n \"Effect\": \"Allow\",\n \"Resource\": [\n \"arn:aws:s3:::terra-ci-artifacts-eu-west-1-000002\",\n \"arn:aws:s3:::terra-ci-artifacts-eu-west-1-000002/*\"\n ],\n \"Action\": [\n \"s3:ListBucket\",\n \"s3:*Object\"\n ]\n }\n ]\n}\n"
+ }
+ ],
+ "managed_policy_arns": [
+ "arn:aws:iam::aws:policy/AmazonEC2ContainerRegistryPowerUser"
+ ],
+ "max_session_duration": 3600,
+ "name": "terra_ci_job",
+ "name_prefix": null,
+ "path": "/",
+ "permissions_boundary": null,
+ "tags": {},
+ "unique_id": "AROA2O52SSXYL7LBSM733"
+ },
+ "after": {
+ "arn": "arn:aws:iam::719261439472:role/terra_ci_job",
+ "assume_role_policy": "{\"Version\":\"2012-10-17\",\"Statement\":[{\"Effect\":\"Allow\",\"Principal\":{\"Service\":\"codebuild.amazonaws.com\"},\"Action\":\"sts:AssumeRole\"}]}",
+ "create_date": "2021-05-01T15:08:15Z",
+ "description": "",
+ "force_detach_policies": false,
+ "id": "terra_ci_job",
+ "inline_policy": [
+ {
+ "name": "terraform-20210501150816628700000001",
+ "policy": "{\n \"Version\": \"2012-10-17\",\n \"Statement\": [\n {\n \"Effect\": \"Allow\",\n \"Action\": \"sts:AssumeRole\",\n \"Resource\": \"arn:aws:iam::719261439472:role/ci\"\n },\n {\n \"Effect\": \"Allow\",\n \"Resource\": [\n \"*\"\n ],\n \"Action\": [\n \"logs:CreateLogGroup\",\n \"logs:CreateLogStream\",\n \"logs:PutLogEvents\"\n ]\n },\n {\n \"Effect\": \"Allow\",\n \"Resource\": [\n \"arn:aws:s3:::terra-ci-artifacts-eu-west-1-000002\",\n \"arn:aws:s3:::terra-ci-artifacts-eu-west-1-000002/*\"\n ],\n \"Action\": [\n \"s3:ListBucket\",\n \"s3:*Object\"\n ]\n }\n ]\n}\n"
+ }
+ ],
+ "managed_policy_arns": [
+ "arn:aws:iam::aws:policy/AmazonEC2ContainerRegistryPowerUser"
+ ],
+ "max_session_duration": 3600,
+ "name": "terra_ci_job",
+ "name_prefix": null,
+ "path": "/",
+ "permissions_boundary": null,
+ "tags": {},
+ "unique_id": "AROA2O52SSXYL7LBSM733"
+ },
+ "after_unknown": {},
+ "before_sensitive": {
+ "inline_policy": [
+ {}
+ ],
+ "managed_policy_arns": [
+ false
+ ],
+ "tags": {}
+ },
+ "after_sensitive": {
+ "inline_policy": [
+ {}
+ ],
+ "managed_policy_arns": [
+ false
+ ],
+ "tags": {}
+ }
+ }
+ },
+ {
+ "address": "aws_iam_role.terra_ci_runner",
+ "mode": "managed",
+ "type": "aws_iam_role",
+ "name": "terra_ci_runner",
+ "provider_name": "registry.terraform.io/hashicorp/aws",
+ "change": {
+ "actions": [
+ "no-op"
+ ],
+ "before": {
+ "arn": "arn:aws:iam::719261439472:role/terra_ci_runner",
+ "assume_role_policy": "{\"Version\":\"2012-10-17\",\"Statement\":[{\"Effect\":\"Allow\",\"Principal\":{\"Service\":\"states.amazonaws.com\"},\"Action\":\"sts:AssumeRole\"}]}",
+ "create_date": "2021-05-01T15:08:15Z",
+ "description": "",
+ "force_detach_policies": false,
+ "id": "terra_ci_runner",
+ "inline_policy": [
+ {
+ "name": "terraform-20210501150825425000000003",
+ "policy": "{\n \"Version\": \"2012-10-17\",\n \"Statement\": [\n {\n \"Effect\": \"Allow\",\n \"Action\": [\n \"codebuild:StartBuild\",\n \"codebuild:StopBuild\",\n \"codebuild:BatchGetBuilds\"\n ],\n \"Resource\": [\n \"arn:aws:codebuild:eu-west-1:719261439472:project/terra-ci-runner\"\n ]\n },\n {\n \"Effect\": \"Allow\",\n \"Action\": [\n \"events:PutTargets\",\n \"events:PutRule\",\n \"events:DescribeRule\"\n ],\n \"Resource\": [\n \"arn:aws:events:eu-west-1:719261439472:rule/StepFunctionsGetEventForCodeBuildStartBuildRule\"\n ]\n }\n ]\n}\n"
+ }
+ ],
+ "managed_policy_arns": [],
+ "max_session_duration": 3600,
+ "name": "terra_ci_runner",
+ "name_prefix": null,
+ "path": "/",
+ "permissions_boundary": null,
+ "tags": {},
+ "unique_id": "AROA2O52SSXYDBYYTG4OB"
+ },
+ "after": {
+ "arn": "arn:aws:iam::719261439472:role/terra_ci_runner",
+ "assume_role_policy": "{\"Version\":\"2012-10-17\",\"Statement\":[{\"Effect\":\"Allow\",\"Principal\":{\"Service\":\"states.amazonaws.com\"},\"Action\":\"sts:AssumeRole\"}]}",
+ "create_date": "2021-05-01T15:08:15Z",
+ "description": "",
+ "force_detach_policies": false,
+ "id": "terra_ci_runner",
+ "inline_policy": [
+ {
+ "name": "terraform-20210501150825425000000003",
+ "policy": "{\n \"Version\": \"2012-10-17\",\n \"Statement\": [\n {\n \"Effect\": \"Allow\",\n \"Action\": [\n \"codebuild:StartBuild\",\n \"codebuild:StopBuild\",\n \"codebuild:BatchGetBuilds\"\n ],\n \"Resource\": [\n \"arn:aws:codebuild:eu-west-1:719261439472:project/terra-ci-runner\"\n ]\n },\n {\n \"Effect\": \"Allow\",\n \"Action\": [\n \"events:PutTargets\",\n \"events:PutRule\",\n \"events:DescribeRule\"\n ],\n \"Resource\": [\n \"arn:aws:events:eu-west-1:719261439472:rule/StepFunctionsGetEventForCodeBuildStartBuildRule\"\n ]\n }\n ]\n}\n"
+ }
+ ],
+ "managed_policy_arns": [],
+ "max_session_duration": 3600,
+ "name": "terra_ci_runner",
+ "name_prefix": null,
+ "path": "/",
+ "permissions_boundary": null,
+ "tags": {},
+ "unique_id": "AROA2O52SSXYDBYYTG4OB"
+ },
+ "after_unknown": {},
+ "before_sensitive": {
+ "inline_policy": [
+ {}
+ ],
+ "managed_policy_arns": [],
+ "tags": {}
+ },
+ "after_sensitive": {
+ "inline_policy": [
+ {}
+ ],
+ "managed_policy_arns": [],
+ "tags": {}
+ }
+ }
+ },
+ {
+ "address": "aws_iam_role_policy.terra_ci_job",
+ "mode": "managed",
+ "type": "aws_iam_role_policy",
+ "name": "terra_ci_job",
+ "provider_name": "registry.terraform.io/hashicorp/aws",
+ "change": {
+ "actions": [
+ "no-op"
+ ],
+ "before": {
+ "id": "terra_ci_job:terraform-20210501150816628700000001",
+ "name": "terraform-20210501150816628700000001",
+ "name_prefix": null,
+ "policy": "{\n \"Version\": \"2012-10-17\",\n \"Statement\": [\n {\n \"Effect\": \"Allow\",\n \"Action\": \"sts:AssumeRole\",\n \"Resource\": \"arn:aws:iam::719261439472:role/ci\"\n },\n {\n \"Effect\": \"Allow\",\n \"Resource\": [\n \"*\"\n ],\n \"Action\": [\n \"logs:CreateLogGroup\",\n \"logs:CreateLogStream\",\n \"logs:PutLogEvents\"\n ]\n },\n {\n \"Effect\": \"Allow\",\n \"Resource\": [\n \"arn:aws:s3:::terra-ci-artifacts-eu-west-1-000002\",\n \"arn:aws:s3:::terra-ci-artifacts-eu-west-1-000002/*\"\n ],\n \"Action\": [\n \"s3:ListBucket\",\n \"s3:*Object\"\n ]\n }\n ]\n}\n",
+ "role": "terra_ci_job"
+ },
+ "after": {
+ "id": "terra_ci_job:terraform-20210501150816628700000001",
+ "name": "terraform-20210501150816628700000001",
+ "name_prefix": null,
+ "policy": "{\n \"Version\": \"2012-10-17\",\n \"Statement\": [\n {\n \"Effect\": \"Allow\",\n \"Action\": \"sts:AssumeRole\",\n \"Resource\": \"arn:aws:iam::719261439472:role/ci\"\n },\n {\n \"Effect\": \"Allow\",\n \"Resource\": [\n \"*\"\n ],\n \"Action\": [\n \"logs:CreateLogGroup\",\n \"logs:CreateLogStream\",\n \"logs:PutLogEvents\"\n ]\n },\n {\n \"Effect\": \"Allow\",\n \"Resource\": [\n \"arn:aws:s3:::terra-ci-artifacts-eu-west-1-000002\",\n \"arn:aws:s3:::terra-ci-artifacts-eu-west-1-000002/*\"\n ],\n \"Action\": [\n \"s3:ListBucket\",\n \"s3:*Object\"\n ]\n }\n ]\n}\n",
+ "role": "terra_ci_job"
+ },
+ "after_unknown": {},
+ "before_sensitive": {},
+ "after_sensitive": {}
+ }
+ },
+ {
+ "address": "aws_iam_role_policy.terra_ci_runner",
+ "mode": "managed",
+ "type": "aws_iam_role_policy",
+ "name": "terra_ci_runner",
+ "provider_name": "registry.terraform.io/hashicorp/aws",
+ "change": {
+ "actions": [
+ "no-op"
+ ],
+ "before": {
+ "id": "terra_ci_runner:terraform-20210501150825425000000003",
+ "name": "terraform-20210501150825425000000003",
+ "name_prefix": null,
+ "policy": "{\n \"Version\": \"2012-10-17\",\n \"Statement\": [\n {\n \"Effect\": \"Allow\",\n \"Action\": [\n \"codebuild:StartBuild\",\n \"codebuild:StopBuild\",\n \"codebuild:BatchGetBuilds\"\n ],\n \"Resource\": [\n \"arn:aws:codebuild:eu-west-1:719261439472:project/terra-ci-runner\"\n ]\n },\n {\n \"Effect\": \"Allow\",\n \"Action\": [\n \"events:PutTargets\",\n \"events:PutRule\",\n \"events:DescribeRule\"\n ],\n \"Resource\": [\n \"arn:aws:events:eu-west-1:719261439472:rule/StepFunctionsGetEventForCodeBuildStartBuildRule\"\n ]\n }\n ]\n}\n",
+ "role": "terra_ci_runner"
+ },
+ "after": {
+ "id": "terra_ci_runner:terraform-20210501150825425000000003",
+ "name": "terraform-20210501150825425000000003",
+ "name_prefix": null,
+ "policy": "{\n \"Version\": \"2012-10-17\",\n \"Statement\": [\n {\n \"Effect\": \"Allow\",\n \"Action\": [\n \"codebuild:StartBuild\",\n \"codebuild:StopBuild\",\n \"codebuild:BatchGetBuilds\"\n ],\n \"Resource\": [\n \"arn:aws:codebuild:eu-west-1:719261439472:project/terra-ci-runner\"\n ]\n },\n {\n \"Effect\": \"Allow\",\n \"Action\": [\n \"events:PutTargets\",\n \"events:PutRule\",\n \"events:DescribeRule\"\n ],\n \"Resource\": [\n \"arn:aws:events:eu-west-1:719261439472:rule/StepFunctionsGetEventForCodeBuildStartBuildRule\"\n ]\n }\n ]\n}\n",
+ "role": "terra_ci_runner"
+ },
+ "after_unknown": {},
+ "before_sensitive": {},
+ "after_sensitive": {}
+ }
+ },
+ {
+ "address": "aws_iam_role_policy_attachment.terra_ci_job_ecr_access",
+ "mode": "managed",
+ "type": "aws_iam_role_policy_attachment",
+ "name": "terra_ci_job_ecr_access",
+ "provider_name": "registry.terraform.io/hashicorp/aws",
+ "change": {
+ "actions": [
+ "no-op"
+ ],
+ "before": {
+ "id": "terra_ci_job-20210501150817089800000002",
+ "policy_arn": "arn:aws:iam::aws:policy/AmazonEC2ContainerRegistryPowerUser",
+ "role": "terra_ci_job"
+ },
+ "after": {
+ "id": "terra_ci_job-20210501150817089800000002",
+ "policy_arn": "arn:aws:iam::aws:policy/AmazonEC2ContainerRegistryPowerUser",
+ "role": "terra_ci_job"
+ },
+ "after_unknown": {},
+ "before_sensitive": {},
+ "after_sensitive": {}
+ }
+ },
+ {
+ "address": "aws_s3_bucket.terra_ci",
+ "mode": "managed",
+ "type": "aws_s3_bucket",
+ "name": "terra_ci",
+ "provider_name": "registry.terraform.io/hashicorp/aws",
+ "change": {
+ "actions": [
+ "no-op"
+ ],
+ "before": {
+ "acceleration_status": "",
+ "acl": "private",
+ "arn": "arn:aws:s3:::terra-ci-artifacts-eu-west-1-000002",
+ "bucket": "terra-ci-artifacts-eu-west-1-000002",
+ "bucket_domain_name": "terra-ci-artifacts-eu-west-1-000002.s3.amazonaws.com",
+ "bucket_prefix": null,
+ "bucket_regional_domain_name": "terra-ci-artifacts-eu-west-1-000002.s3.eu-west-1.amazonaws.com",
+ "cors_rule": [],
+ "force_destroy": false,
+ "grant": [],
+ "hosted_zone_id": "Z1BKCTXD74EZPE",
+ "id": "terra-ci-artifacts-eu-west-1-000002",
+ "lifecycle_rule": [],
+ "logging": [],
+ "object_lock_configuration": [],
+ "policy": null,
+ "region": "eu-west-1",
+ "replication_configuration": [],
+ "request_payer": "BucketOwner",
+ "server_side_encryption_configuration": [
+ {
+ "rule": [
+ {
+ "apply_server_side_encryption_by_default": [
+ {
+ "kms_master_key_id": "",
+ "sse_algorithm": "aws:kms"
+ }
+ ],
+ "bucket_key_enabled": false
+ }
+ ]
+ }
+ ],
+ "tags": {},
+ "versioning": [
+ {
+ "enabled": false,
+ "mfa_delete": false
+ }
+ ],
+ "website": [],
+ "website_domain": null,
+ "website_endpoint": null
+ },
+ "after": {
+ "acceleration_status": "",
+ "acl": "private",
+ "arn": "arn:aws:s3:::terra-ci-artifacts-eu-west-1-000002",
+ "bucket": "terra-ci-artifacts-eu-west-1-000002",
+ "bucket_domain_name": "terra-ci-artifacts-eu-west-1-000002.s3.amazonaws.com",
+ "bucket_prefix": null,
+ "bucket_regional_domain_name": "terra-ci-artifacts-eu-west-1-000002.s3.eu-west-1.amazonaws.com",
+ "cors_rule": [],
+ "force_destroy": false,
+ "grant": [],
+ "hosted_zone_id": "Z1BKCTXD74EZPE",
+ "id": "terra-ci-artifacts-eu-west-1-000002",
+ "lifecycle_rule": [],
+ "logging": [],
+ "object_lock_configuration": [],
+ "policy": null,
+ "region": "eu-west-1",
+ "replication_configuration": [],
+ "request_payer": "BucketOwner",
+ "server_side_encryption_configuration": [
+ {
+ "rule": [
+ {
+ "apply_server_side_encryption_by_default": [
+ {
+ "kms_master_key_id": "",
+ "sse_algorithm": "aws:kms"
+ }
+ ],
+ "bucket_key_enabled": false
+ }
+ ]
+ }
+ ],
+ "tags": {},
+ "versioning": [
+ {
+ "enabled": false,
+ "mfa_delete": false
+ }
+ ],
+ "website": [],
+ "website_domain": null,
+ "website_endpoint": null
+ },
+ "after_unknown": {},
+ "before_sensitive": {
+ "cors_rule": [],
+ "grant": [],
+ "lifecycle_rule": [],
+ "logging": [],
+ "object_lock_configuration": [],
+ "replication_configuration": [],
+ "server_side_encryption_configuration": [
+ {
+ "rule": [
+ {
+ "apply_server_side_encryption_by_default": [
+ {}
+ ]
+ }
+ ]
+ }
+ ],
+ "tags": {},
+ "versioning": [
+ {}
+ ],
+ "website": []
+ },
+ "after_sensitive": {
+ "cors_rule": [],
+ "grant": [],
+ "lifecycle_rule": [],
+ "logging": [],
+ "object_lock_configuration": [],
+ "replication_configuration": [],
+ "server_side_encryption_configuration": [
+ {
+ "rule": [
+ {
+ "apply_server_side_encryption_by_default": [
+ {}
+ ]
+ }
+ ]
+ }
+ ],
+ "tags": {},
+ "versioning": [
+ {}
+ ],
+ "website": []
+ }
+ }
+ },
+ {
+ "address": "aws_sfn_state_machine.terra_ci_runner",
+ "mode": "managed",
+ "type": "aws_sfn_state_machine",
+ "name": "terra_ci_runner",
+ "provider_name": "registry.terraform.io/hashicorp/aws",
+ "change": {
+ "actions": [
+ "no-op"
+ ],
+ "before": {
+ "arn": "arn:aws:states:eu-west-1:719261439472:stateMachine:terra-ci-runner",
+ "creation_date": "2021-05-01T15:09:28Z",
+ "definition": "{\n \"Comment\": \"Run Terragrunt Jobs\",\n \"StartAt\": \"OnBranch?\",\n \"States\": {\n \"OnBranch?\": {\n \"Type\": \"Choice\",\n \"Choices\": [\n {\n \"Variable\": \"$.build.sourceversion\",\n \"IsPresent\": true,\n \"Next\": \"PlanBranch\"\n }\n ],\n \"Default\": \"Plan\"\n },\n \"Plan\": {\n \"Type\": \"Task\",\n \"Resource\": \"arn:aws:states:::codebuild:startBuild.sync\",\n \"Parameters\": {\n \"ProjectName\": \"terra-ci-runner\",\n \"EnvironmentVariablesOverride\": [\n {\n \"Name\": \"TERRA_CI_BUILD_NAME\",\n \"Value.$\": \"$$.Execution.Name\"\n },\n {\n \"Name\": \"TERRA_CI_RESOURCE\",\n \"Value.$\": \"$.build.environment.terra_ci_resource\"\n }\n ]\n },\n \"End\": true\n },\n \"PlanBranch\": {\n \"Type\": \"Task\",\n \"Resource\": \"arn:aws:states:::codebuild:startBuild.sync\",\n \"Parameters\": {\n \"ProjectName\": \"terra-ci-runner\",\n \"SourceVersion.$\": \"$.build.sourceversion\",\n \"EnvironmentVariablesOverride\": [\n {\n \"Name\": \"TERRA_CI_RESOURCE\",\n \"Value.$\": \"$.build.environment.terra_ci_resource\"\n }\n ]\n },\n \"End\": true\n }\n }\n}\n",
+ "id": "arn:aws:states:eu-west-1:719261439472:stateMachine:terra-ci-runner",
+ "logging_configuration": [
+ {
+ "include_execution_data": false,
+ "level": "OFF",
+ "log_destination": ""
+ }
+ ],
+ "name": "terra-ci-runner",
+ "role_arn": "arn:aws:iam::719261439472:role/terra_ci_runner",
+ "status": "ACTIVE",
+ "tags": {},
+ "type": "STANDARD"
+ },
+ "after": {
+ "arn": "arn:aws:states:eu-west-1:719261439472:stateMachine:terra-ci-runner",
+ "creation_date": "2021-05-01T15:09:28Z",
+ "definition": "{\n \"Comment\": \"Run Terragrunt Jobs\",\n \"StartAt\": \"OnBranch?\",\n \"States\": {\n \"OnBranch?\": {\n \"Type\": \"Choice\",\n \"Choices\": [\n {\n \"Variable\": \"$.build.sourceversion\",\n \"IsPresent\": true,\n \"Next\": \"PlanBranch\"\n }\n ],\n \"Default\": \"Plan\"\n },\n \"Plan\": {\n \"Type\": \"Task\",\n \"Resource\": \"arn:aws:states:::codebuild:startBuild.sync\",\n \"Parameters\": {\n \"ProjectName\": \"terra-ci-runner\",\n \"EnvironmentVariablesOverride\": [\n {\n \"Name\": \"TERRA_CI_BUILD_NAME\",\n \"Value.$\": \"$$.Execution.Name\"\n },\n {\n \"Name\": \"TERRA_CI_RESOURCE\",\n \"Value.$\": \"$.build.environment.terra_ci_resource\"\n }\n ]\n },\n \"End\": true\n },\n \"PlanBranch\": {\n \"Type\": \"Task\",\n \"Resource\": \"arn:aws:states:::codebuild:startBuild.sync\",\n \"Parameters\": {\n \"ProjectName\": \"terra-ci-runner\",\n \"SourceVersion.$\": \"$.build.sourceversion\",\n \"EnvironmentVariablesOverride\": [\n {\n \"Name\": \"TERRA_CI_RESOURCE\",\n \"Value.$\": \"$.build.environment.terra_ci_resource\"\n }\n ]\n },\n \"End\": true\n }\n }\n}\n",
+ "id": "arn:aws:states:eu-west-1:719261439472:stateMachine:terra-ci-runner",
+ "logging_configuration": [
+ {
+ "include_execution_data": false,
+ "level": "OFF",
+ "log_destination": ""
+ }
+ ],
+ "name": "terra-ci-runner",
+ "role_arn": "arn:aws:iam::719261439472:role/terra_ci_runner",
+ "status": "ACTIVE",
+ "tags": {},
+ "type": "STANDARD"
+ },
+ "after_unknown": {},
+ "before_sensitive": {
+ "logging_configuration": [
+ {}
+ ],
+ "tags": {}
+ },
+ "after_sensitive": {
+ "logging_configuration": [
+ {}
+ ],
+ "tags": {}
+ }
+ }
+ }
+ ],
+ "prior_state": {
+ "format_version": "0.1",
+ "terraform_version": "0.15.0",
+ "values": {
+ "root_module": {
+ "resources": [
+ {
+ "address": "aws_codebuild_project.terra_ci",
+ "mode": "managed",
+ "type": "aws_codebuild_project",
+ "name": "terra_ci",
+ "provider_name": "registry.terraform.io/hashicorp/aws",
+ "schema_version": 0,
+ "values": {
+ "arn": "arn:aws:codebuild:eu-west-1:719261439472:project/terra-ci-runner",
+ "artifacts": [
+ {
+ "artifact_identifier": "",
+ "encryption_disabled": false,
+ "location": "terra-ci-artifacts-eu-west-1-000002",
+ "name": "terra-ci-runner",
+ "namespace_type": "NONE",
+ "override_artifact_name": false,
+ "packaging": "NONE",
+ "path": "",
+ "type": "S3"
+ }
+ ],
+ "badge_enabled": false,
+ "badge_url": "",
+ "build_timeout": 10,
+ "cache": [
+ {
+ "location": "",
+ "modes": [],
+ "type": "NO_CACHE"
+ }
+ ],
+ "description": "Deploy environment configuration",
+ "encryption_key": "arn:aws:kms:eu-west-1:719261439472:alias/aws/s3",
+ "environment": [
+ {
+ "certificate": "",
+ "compute_type": "BUILD_GENERAL1_SMALL",
+ "environment_variable": [],
+ "image": "aws/codebuild/amazonlinux2-x86_64-standard:2.0",
+ "image_pull_credentials_type": "CODEBUILD",
+ "privileged_mode": false,
+ "registry_credential": [],
+ "type": "LINUX_CONTAINER"
+ }
+ ],
+ "id": "arn:aws:codebuild:eu-west-1:719261439472:project/terra-ci-runner",
+ "logs_config": [
+ {
+ "cloudwatch_logs": [
+ {
+ "group_name": "",
+ "status": "ENABLED",
+ "stream_name": ""
+ }
+ ],
+ "s3_logs": [
+ {
+ "encryption_disabled": false,
+ "location": "",
+ "status": "DISABLED"
+ }
+ ]
+ }
+ ],
+ "name": "terra-ci-runner",
+ "queued_timeout": 480,
+ "secondary_artifacts": [],
+ "secondary_sources": [],
+ "service_role": "arn:aws:iam::719261439472:role/terra_ci_job",
+ "source": [
+ {
+ "auth": [],
+ "buildspec": "version: 0.2\nphases:\n install:\n commands:\n - make install_tools\n build:\n commands:\n - make plan_local resource=$TERRA_CI_RESOURCE\nartifacts:\n files:\n - ./tfplan\n name: $TERRA_CI_BUILD_NAME\n\n",
+ "git_clone_depth": 1,
+ "git_submodules_config": [],
+ "insecure_ssl": false,
+ "location": "https://github.com/p0tr3c-terraform/terra-ci-single-account.git",
+ "report_build_status": false,
+ "type": "GITHUB"
+ }
+ ],
+ "source_version": "",
+ "tags": {},
+ "vpc_config": []
+ },
+ "depends_on": [
+ "aws_iam_role.terra_ci_job",
+ "aws_s3_bucket.terra_ci",
+ "data.template_file.terra_ci"
+ ]
+ },
+ {
+ "address": "aws_iam_role.terra_ci_job",
+ "mode": "managed",
+ "type": "aws_iam_role",
+ "name": "terra_ci_job",
+ "provider_name": "registry.terraform.io/hashicorp/aws",
+ "schema_version": 0,
+ "values": {
+ "arn": "arn:aws:iam::719261439472:role/terra_ci_job",
+ "assume_role_policy": "{\"Version\":\"2012-10-17\",\"Statement\":[{\"Effect\":\"Allow\",\"Principal\":{\"Service\":\"codebuild.amazonaws.com\"},\"Action\":\"sts:AssumeRole\"}]}",
+ "create_date": "2021-05-01T15:08:15Z",
+ "description": "",
+ "force_detach_policies": false,
+ "id": "terra_ci_job",
+ "inline_policy": [
+ {
+ "name": "terraform-20210501150816628700000001",
+ "policy": "{\n \"Version\": \"2012-10-17\",\n \"Statement\": [\n {\n \"Effect\": \"Allow\",\n \"Action\": \"sts:AssumeRole\",\n \"Resource\": \"arn:aws:iam::719261439472:role/ci\"\n },\n {\n \"Effect\": \"Allow\",\n \"Resource\": [\n \"*\"\n ],\n \"Action\": [\n \"logs:CreateLogGroup\",\n \"logs:CreateLogStream\",\n \"logs:PutLogEvents\"\n ]\n },\n {\n \"Effect\": \"Allow\",\n \"Resource\": [\n \"arn:aws:s3:::terra-ci-artifacts-eu-west-1-000002\",\n \"arn:aws:s3:::terra-ci-artifacts-eu-west-1-000002/*\"\n ],\n \"Action\": [\n \"s3:ListBucket\",\n \"s3:*Object\"\n ]\n }\n ]\n}\n"
+ }
+ ],
+ "managed_policy_arns": [
+ "arn:aws:iam::aws:policy/AmazonEC2ContainerRegistryPowerUser"
+ ],
+ "max_session_duration": 3600,
+ "name": "terra_ci_job",
+ "name_prefix": null,
+ "path": "/",
+ "permissions_boundary": null,
+ "tags": {},
+ "unique_id": "AROA2O52SSXYL7LBSM733"
+ }
+ },
+ {
+ "address": "aws_iam_role.terra_ci_runner",
+ "mode": "managed",
+ "type": "aws_iam_role",
+ "name": "terra_ci_runner",
+ "provider_name": "registry.terraform.io/hashicorp/aws",
+ "schema_version": 0,
+ "values": {
+ "arn": "arn:aws:iam::719261439472:role/terra_ci_runner",
+ "assume_role_policy": "{\"Version\":\"2012-10-17\",\"Statement\":[{\"Effect\":\"Allow\",\"Principal\":{\"Service\":\"states.amazonaws.com\"},\"Action\":\"sts:AssumeRole\"}]}",
+ "create_date": "2021-05-01T15:08:15Z",
+ "description": "",
+ "force_detach_policies": false,
+ "id": "terra_ci_runner",
+ "inline_policy": [
+ {
+ "name": "terraform-20210501150825425000000003",
+ "policy": "{\n \"Version\": \"2012-10-17\",\n \"Statement\": [\n {\n \"Effect\": \"Allow\",\n \"Action\": [\n \"codebuild:StartBuild\",\n \"codebuild:StopBuild\",\n \"codebuild:BatchGetBuilds\"\n ],\n \"Resource\": [\n \"arn:aws:codebuild:eu-west-1:719261439472:project/terra-ci-runner\"\n ]\n },\n {\n \"Effect\": \"Allow\",\n \"Action\": [\n \"events:PutTargets\",\n \"events:PutRule\",\n \"events:DescribeRule\"\n ],\n \"Resource\": [\n \"arn:aws:events:eu-west-1:719261439472:rule/StepFunctionsGetEventForCodeBuildStartBuildRule\"\n ]\n }\n ]\n}\n"
+ }
+ ],
+ "managed_policy_arns": [],
+ "max_session_duration": 3600,
+ "name": "terra_ci_runner",
+ "name_prefix": null,
+ "path": "/",
+ "permissions_boundary": null,
+ "tags": {},
+ "unique_id": "AROA2O52SSXYDBYYTG4OB"
+ }
+ },
+ {
+ "address": "aws_iam_role_policy.terra_ci_job",
+ "mode": "managed",
+ "type": "aws_iam_role_policy",
+ "name": "terra_ci_job",
+ "provider_name": "registry.terraform.io/hashicorp/aws",
+ "schema_version": 0,
+ "values": {
+ "id": "terra_ci_job:terraform-20210501150816628700000001",
+ "name": "terraform-20210501150816628700000001",
+ "name_prefix": null,
+ "policy": "{\n \"Version\": \"2012-10-17\",\n \"Statement\": [\n {\n \"Effect\": \"Allow\",\n \"Action\": \"sts:AssumeRole\",\n \"Resource\": \"arn:aws:iam::719261439472:role/ci\"\n },\n {\n \"Effect\": \"Allow\",\n \"Resource\": [\n \"*\"\n ],\n \"Action\": [\n \"logs:CreateLogGroup\",\n \"logs:CreateLogStream\",\n \"logs:PutLogEvents\"\n ]\n },\n {\n \"Effect\": \"Allow\",\n \"Resource\": [\n \"arn:aws:s3:::terra-ci-artifacts-eu-west-1-000002\",\n \"arn:aws:s3:::terra-ci-artifacts-eu-west-1-000002/*\"\n ],\n \"Action\": [\n \"s3:ListBucket\",\n \"s3:*Object\"\n ]\n }\n ]\n}\n",
+ "role": "terra_ci_job"
+ },
+ "depends_on": [
+ "aws_iam_role.terra_ci_job",
+ "aws_s3_bucket.terra_ci",
+ "data.aws_caller_identity.current"
+ ]
+ },
+ {
+ "address": "aws_iam_role_policy.terra_ci_runner",
+ "mode": "managed",
+ "type": "aws_iam_role_policy",
+ "name": "terra_ci_runner",
+ "provider_name": "registry.terraform.io/hashicorp/aws",
+ "schema_version": 0,
+ "values": {
+ "id": "terra_ci_runner:terraform-20210501150825425000000003",
+ "name": "terraform-20210501150825425000000003",
+ "name_prefix": null,
+ "policy": "{\n \"Version\": \"2012-10-17\",\n \"Statement\": [\n {\n \"Effect\": \"Allow\",\n \"Action\": [\n \"codebuild:StartBuild\",\n \"codebuild:StopBuild\",\n \"codebuild:BatchGetBuilds\"\n ],\n \"Resource\": [\n \"arn:aws:codebuild:eu-west-1:719261439472:project/terra-ci-runner\"\n ]\n },\n {\n \"Effect\": \"Allow\",\n \"Action\": [\n \"events:PutTargets\",\n \"events:PutRule\",\n \"events:DescribeRule\"\n ],\n \"Resource\": [\n \"arn:aws:events:eu-west-1:719261439472:rule/StepFunctionsGetEventForCodeBuildStartBuildRule\"\n ]\n }\n ]\n}\n",
+ "role": "terra_ci_runner"
+ },
+ "depends_on": [
+ "data.template_file.terra_ci",
+ "aws_codebuild_project.terra_ci",
+ "aws_iam_role.terra_ci_job",
+ "aws_iam_role.terra_ci_runner",
+ "aws_s3_bucket.terra_ci",
+ "data.aws_caller_identity.current"
+ ]
+ },
+ {
+ "address": "aws_iam_role_policy_attachment.terra_ci_job_ecr_access",
+ "mode": "managed",
+ "type": "aws_iam_role_policy_attachment",
+ "name": "terra_ci_job_ecr_access",
+ "provider_name": "registry.terraform.io/hashicorp/aws",
+ "schema_version": 0,
+ "values": {
+ "id": "terra_ci_job-20210501150817089800000002",
+ "policy_arn": "arn:aws:iam::aws:policy/AmazonEC2ContainerRegistryPowerUser",
+ "role": "terra_ci_job"
+ },
+ "depends_on": [
+ "aws_iam_role.terra_ci_job"
+ ]
+ },
+ {
+ "address": "aws_s3_bucket.terra_ci",
+ "mode": "managed",
+ "type": "aws_s3_bucket",
+ "name": "terra_ci",
+ "provider_name": "registry.terraform.io/hashicorp/aws",
+ "schema_version": 0,
+ "values": {
+ "acceleration_status": "",
+ "acl": "private",
+ "arn": "arn:aws:s3:::terra-ci-artifacts-eu-west-1-000002",
+ "bucket": "terra-ci-artifacts-eu-west-1-000002",
+ "bucket_domain_name": "terra-ci-artifacts-eu-west-1-000002.s3.amazonaws.com",
+ "bucket_prefix": null,
+ "bucket_regional_domain_name": "terra-ci-artifacts-eu-west-1-000002.s3.eu-west-1.amazonaws.com",
+ "cors_rule": [],
+ "force_destroy": false,
+ "grant": [],
+ "hosted_zone_id": "Z1BKCTXD74EZPE",
+ "id": "terra-ci-artifacts-eu-west-1-000002",
+ "lifecycle_rule": [],
+ "logging": [],
+ "object_lock_configuration": [],
+ "policy": null,
+ "region": "eu-west-1",
+ "replication_configuration": [],
+ "request_payer": "BucketOwner",
+ "server_side_encryption_configuration": [
+ {
+ "rule": [
+ {
+ "apply_server_side_encryption_by_default": [
+ {
+ "kms_master_key_id": "",
+ "sse_algorithm": "aws:kms"
+ }
+ ],
+ "bucket_key_enabled": false
+ }
+ ]
+ }
+ ],
+ "tags": {},
+ "versioning": [
+ {
+ "enabled": false,
+ "mfa_delete": false
+ }
+ ],
+ "website": [],
+ "website_domain": null,
+ "website_endpoint": null
+ }
+ },
+ {
+ "address": "aws_sfn_state_machine.terra_ci_runner",
+ "mode": "managed",
+ "type": "aws_sfn_state_machine",
+ "name": "terra_ci_runner",
+ "provider_name": "registry.terraform.io/hashicorp/aws",
+ "schema_version": 0,
+ "values": {
+ "arn": "arn:aws:states:eu-west-1:719261439472:stateMachine:terra-ci-runner",
+ "creation_date": "2021-05-01T15:09:28Z",
+ "definition": "{\n \"Comment\": \"Run Terragrunt Jobs\",\n \"StartAt\": \"OnBranch?\",\n \"States\": {\n \"OnBranch?\": {\n \"Type\": \"Choice\",\n \"Choices\": [\n {\n \"Variable\": \"$.build.sourceversion\",\n \"IsPresent\": true,\n \"Next\": \"PlanBranch\"\n }\n ],\n \"Default\": \"Plan\"\n },\n \"Plan\": {\n \"Type\": \"Task\",\n \"Resource\": \"arn:aws:states:::codebuild:startBuild.sync\",\n \"Parameters\": {\n \"ProjectName\": \"terra-ci-runner\",\n \"EnvironmentVariablesOverride\": [\n {\n \"Name\": \"TERRA_CI_BUILD_NAME\",\n \"Value.$\": \"$$.Execution.Name\"\n },\n {\n \"Name\": \"TERRA_CI_RESOURCE\",\n \"Value.$\": \"$.build.environment.terra_ci_resource\"\n }\n ]\n },\n \"End\": true\n },\n \"PlanBranch\": {\n \"Type\": \"Task\",\n \"Resource\": \"arn:aws:states:::codebuild:startBuild.sync\",\n \"Parameters\": {\n \"ProjectName\": \"terra-ci-runner\",\n \"SourceVersion.$\": \"$.build.sourceversion\",\n \"EnvironmentVariablesOverride\": [\n {\n \"Name\": \"TERRA_CI_RESOURCE\",\n \"Value.$\": \"$.build.environment.terra_ci_resource\"\n }\n ]\n },\n \"End\": true\n }\n }\n}\n",
+ "id": "arn:aws:states:eu-west-1:719261439472:stateMachine:terra-ci-runner",
+ "logging_configuration": [
+ {
+ "include_execution_data": false,
+ "level": "OFF",
+ "log_destination": ""
+ }
+ ],
+ "name": "terra-ci-runner",
+ "role_arn": "arn:aws:iam::719261439472:role/terra_ci_runner",
+ "status": "ACTIVE",
+ "tags": {},
+ "type": "STANDARD"
+ },
+ "depends_on": [
+ "aws_codebuild_project.terra_ci",
+ "aws_iam_role.terra_ci_job",
+ "aws_iam_role.terra_ci_runner",
+ "aws_s3_bucket.terra_ci",
+ "data.template_file.terra_ci"
+ ]
+ },
+ {
+ "address": "data.aws_caller_identity.current",
+ "mode": "data",
+ "type": "aws_caller_identity",
+ "name": "current",
+ "provider_name": "registry.terraform.io/hashicorp/aws",
+ "schema_version": 0,
+ "values": {
+ "account_id": "719261439472",
+ "arn": "arn:aws:sts::719261439472:assumed-role/ci/1620199336456840848",
+ "id": "719261439472",
+ "user_id": "AROA2O52SSXYLVFYURBIV:1620199336456840848"
+ }
+ },
+ {
+ "address": "data.template_file.terra_ci",
+ "mode": "data",
+ "type": "template_file",
+ "name": "terra_ci",
+ "provider_name": "registry.terraform.io/hashicorp/template",
+ "schema_version": 0,
+ "values": {
+ "filename": null,
+ "id": "64e36ed71e7270140dde96fec9c89d1d55ae5a6e91f7c0be15170200dcf9481b",
+ "rendered": "version: 0.2\nphases:\n install:\n commands:\n - make install_tools\n build:\n commands:\n - make plan_local resource=$TERRA_CI_RESOURCE\nartifacts:\n files:\n - ./tfplan\n name: $TERRA_CI_BUILD_NAME\n\n",
+ "template": "version: 0.2\nphases:\n install:\n commands:\n - make install_tools\n build:\n commands:\n - make plan_local resource=$TERRA_CI_RESOURCE\nartifacts:\n files:\n - ./tfplan\n name: $TERRA_CI_BUILD_NAME\n\n",
+ "vars": null
+ }
+ }
+ ]
+ }
+ }
+ },
+ "configuration": {
+ "provider_config": {
+ "aws": {
+ "name": "aws",
+ "expressions": {
+ "allowed_account_ids": {
+ "constant_value": [
+ "719261439472"
+ ]
+ },
+ "assume_role": [
+ {
+ "role_arn": {
+ "constant_value": "arn:aws:iam::719261439472:role/ci"
+ }
+ }
+ ],
+ "region": {
+ "constant_value": "eu-west-1"
+ }
+ }
+ }
+ },
+ "root_module": {
+ "resources": [
+ {
+ "address": "aws_codebuild_project.terra_ci",
+ "mode": "managed",
+ "type": "aws_codebuild_project",
+ "name": "terra_ci",
+ "provider_config_key": "aws",
+ "expressions": {
+ "artifacts": [
+ {
+ "location": {
+ "references": [
+ "aws_s3_bucket.terra_ci"
+ ]
+ },
+ "type": {
+ "constant_value": "S3"
+ }
+ }
+ ],
+ "build_timeout": {
+ "constant_value": "10"
+ },
+ "description": {
+ "constant_value": "Deploy environment configuration"
+ },
+ "environment": [
+ {
+ "compute_type": {
+ "constant_value": "BUILD_GENERAL1_SMALL"
+ },
+ "image": {
+ "constant_value": "aws/codebuild/amazonlinux2-x86_64-standard:2.0"
+ },
+ "image_pull_credentials_type": {
+ "constant_value": "CODEBUILD"
+ },
+ "privileged_mode": {
+ "constant_value": false
+ },
+ "type": {
+ "constant_value": "LINUX_CONTAINER"
+ }
+ }
+ ],
+ "logs_config": [
+ {
+ "cloudwatch_logs": [
+ {
+ "status": {
+ "constant_value": "ENABLED"
+ }
+ }
+ ],
+ "s3_logs": [
+ {
+ "encryption_disabled": {
+ "constant_value": false
+ },
+ "status": {
+ "constant_value": "DISABLED"
+ }
+ }
+ ]
+ }
+ ],
+ "name": {
+ "constant_value": "terra-ci-runner"
+ },
+ "service_role": {
+ "references": [
+ "aws_iam_role.terra_ci_job"
+ ]
+ },
+ "source": [
+ {
+ "buildspec": {
+ "references": [
+ "data.template_file.terra_ci"
+ ]
+ },
+ "git_clone_depth": {
+ "constant_value": 1
+ },
+ "insecure_ssl": {
+ "constant_value": false
+ },
+ "location": {
+ "references": [
+ "var.repo_url"
+ ]
+ },
+ "report_build_status": {
+ "constant_value": false
+ },
+ "type": {
+ "constant_value": "GITHUB"
+ }
+ }
+ ]
+ },
+ "schema_version": 0
+ },
+ {
+ "address": "aws_iam_role.terra_ci_job",
+ "mode": "managed",
+ "type": "aws_iam_role",
+ "name": "terra_ci_job",
+ "provider_config_key": "aws",
+ "expressions": {
+ "assume_role_policy": {
+ "constant_value": "{\n \"Version\": \"2012-10-17\",\n \"Statement\": [\n {\n \"Effect\": \"Allow\",\n \"Principal\": {\n \"Service\": \"codebuild.amazonaws.com\"\n },\n \"Action\": \"sts:AssumeRole\"\n }\n ]\n}\n"
+ },
+ "name": {
+ "constant_value": "terra_ci_job"
+ }
+ },
+ "schema_version": 0
+ },
+ {
+ "address": "aws_iam_role.terra_ci_runner",
+ "mode": "managed",
+ "type": "aws_iam_role",
+ "name": "terra_ci_runner",
+ "provider_config_key": "aws",
+ "expressions": {
+ "assume_role_policy": {
+ "constant_value": "{\n \"Version\": \"2012-10-17\",\n \"Statement\": [\n {\n \"Effect\": \"Allow\",\n \"Principal\": {\n \"Service\": \"states.amazonaws.com\"\n },\n \"Action\": \"sts:AssumeRole\"\n }\n ]\n}\n"
+ },
+ "name": {
+ "constant_value": "terra_ci_runner"
+ }
+ },
+ "schema_version": 0
+ },
+ {
+ "address": "aws_iam_role_policy.terra_ci_job",
+ "mode": "managed",
+ "type": "aws_iam_role_policy",
+ "name": "terra_ci_job",
+ "provider_config_key": "aws",
+ "expressions": {
+ "policy": {
+ "references": [
+ "data.aws_caller_identity.current",
+ "aws_s3_bucket.terra_ci",
+ "aws_s3_bucket.terra_ci"
+ ]
+ },
+ "role": {
+ "references": [
+ "aws_iam_role.terra_ci_job"
+ ]
+ }
+ },
+ "schema_version": 0
+ },
+ {
+ "address": "aws_iam_role_policy.terra_ci_runner",
+ "mode": "managed",
+ "type": "aws_iam_role_policy",
+ "name": "terra_ci_runner",
+ "provider_config_key": "aws",
+ "expressions": {
+ "policy": {
+ "references": [
+ "aws_codebuild_project.terra_ci",
+ "var.aws_region",
+ "data.aws_caller_identity.current"
+ ]
+ },
+ "role": {
+ "references": [
+ "aws_iam_role.terra_ci_runner"
+ ]
+ }
+ },
+ "schema_version": 0
+ },
+ {
+ "address": "aws_iam_role_policy_attachment.terra_ci_job_ecr_access",
+ "mode": "managed",
+ "type": "aws_iam_role_policy_attachment",
+ "name": "terra_ci_job_ecr_access",
+ "provider_config_key": "aws",
+ "expressions": {
+ "policy_arn": {
+ "constant_value": "arn:aws:iam::aws:policy/AmazonEC2ContainerRegistryPowerUser"
+ },
+ "role": {
+ "references": [
+ "aws_iam_role.terra_ci_job"
+ ]
+ }
+ },
+ "schema_version": 0
+ },
+ {
+ "address": "aws_s3_bucket.terra_ci",
+ "mode": "managed",
+ "type": "aws_s3_bucket",
+ "name": "terra_ci",
+ "provider_config_key": "aws",
+ "expressions": {
+ "acl": {
+ "constant_value": "private"
+ },
+ "bucket": {
+ "references": [
+ "var.aws_region",
+ "var.serial_number"
+ ]
+ },
+ "server_side_encryption_configuration": [
+ {
+ "rule": [
+ {
+ "apply_server_side_encryption_by_default": [
+ {
+ "sse_algorithm": {
+ "constant_value": "aws:kms"
+ }
+ }
+ ],
+ "bucket_key_enabled": {
+ "constant_value": false
+ }
+ }
+ ]
+ }
+ ]
+ },
+ "schema_version": 0
+ },
+ {
+ "address": "aws_sfn_state_machine.terra_ci_runner",
+ "mode": "managed",
+ "type": "aws_sfn_state_machine",
+ "name": "terra_ci_runner",
+ "provider_config_key": "aws",
+ "expressions": {
+ "definition": {
+ "references": [
+ "aws_codebuild_project.terra_ci",
+ "aws_codebuild_project.terra_ci"
+ ]
+ },
+ "name": {
+ "constant_value": "terra-ci-runner"
+ },
+ "role_arn": {
+ "references": [
+ "aws_iam_role.terra_ci_runner"
+ ]
+ }
+ },
+ "schema_version": 0
+ },
+ {
+ "address": "data.aws_caller_identity.current",
+ "mode": "data",
+ "type": "aws_caller_identity",
+ "name": "current",
+ "provider_config_key": "aws",
+ "schema_version": 0
+ },
+ {
+ "address": "data.template_file.terra_ci",
+ "mode": "data",
+ "type": "template_file",
+ "name": "terra_ci",
+ "provider_config_key": "template",
+ "expressions": {
+ "template": {}
+ },
+ "schema_version": 0
+ }
+ ],
+ "variables": {
+ "aws_region": {},
+ "repo_url": {},
+ "serial_number": {}
+ }
+ }
+ }
+ }
diff --git a/tests/test_files/tf_content_generator_files/tfplan-null-example/tf_content.txt b/tests/test_files/tf_content_generator_files/tfplan-null-example/tf_content.txt
new file mode 100644
index 00000000..a0ac1510
--- /dev/null
+++ b/tests/test_files/tf_content_generator_files/tfplan-null-example/tf_content.txt
@@ -0,0 +1,4 @@
+resource "null_resource" "empty" {
+ triggers = null
+}
+
diff --git a/tests/test_files/tf_content_generator_files/tfplan-null-example/tfplan.json b/tests/test_files/tf_content_generator_files/tfplan-null-example/tfplan.json
new file mode 100644
index 00000000..fe05b388
--- /dev/null
+++ b/tests/test_files/tf_content_generator_files/tfplan-null-example/tfplan.json
@@ -0,0 +1,75 @@
+{
+ "format_version": "1.0",
+ "terraform_version": "1.1.9",
+ "variables": {
+ "environment": {
+ "value": "test"
+ }
+ },
+ "planned_values": {
+ "root_module": {
+ "resources": [
+ {
+ "address": "null_resource.empty",
+ "mode": "managed",
+ "type": "null_resource",
+ "name": "empty",
+ "provider_name": "registry.terraform.io/hashicorp/null",
+ "schema_version": 0,
+ "values": {
+ "triggers": null
+ },
+ "sensitive_values": {}
+ }
+ ]
+ }
+ },
+ "resource_changes": [
+ {
+ "address": "null_resource.empty",
+ "mode": "managed",
+ "type": "null_resource",
+ "name": "empty",
+ "provider_name": "registry.terraform.io/hashicorp/null",
+ "change": {
+ "actions": [
+ "create"
+ ],
+ "before": null,
+ "after": {
+ "triggers": null
+ },
+ "after_unknown": {
+ "id": true
+ },
+ "before_sensitive": false,
+ "after_sensitive": {}
+ }
+ }
+ ],
+ "configuration": {
+ "provider_config": {
+ "aws": {
+ "name": "aws",
+ "version_constraint": ">= 4.12.1"
+ }
+ },
+ "root_module": {
+ "resources": [
+ {
+ "address": "null_resource.empty",
+ "mode": "managed",
+ "type": "null_resource",
+ "name": "empty",
+ "provider_config_key": "null",
+ "schema_version": 0
+ }
+ ],
+ "variables": {
+ "environment": {
+ "description": "The name of the deployment environment"
+ }
+ }
+ }
+ }
+}
\ No newline at end of file
diff --git a/tests/test_files/tf_content_generator_files/tfplan-update-example/tf_content.txt b/tests/test_files/tf_content_generator_files/tfplan-update-example/tf_content.txt
new file mode 100644
index 00000000..0e7a588a
--- /dev/null
+++ b/tests/test_files/tf_content_generator_files/tfplan-update-example/tf_content.txt
@@ -0,0 +1,34 @@
+resource "aws_codebuild_project" "some_projed" {
+ arn = "arn:aws:codebuild:eu-west-1:719261439472:project/why-my-project-not-working"
+ artifacts = [{"artifact_identifier": "", "encryption_disabled": true, "location": "terra-ci-artifacts-eu-west-1-000002", "name": "why-my-project-not-working", "namespace_type": "NONE", "override_artifact_name": true, "packaging": "NONE", "path": "", "type": "S3"}]
+ badge_enabled = false
+ badge_url = ""
+ build_timeout = 10
+ cache = [{"location": "", "modes": [], "type": "NO_CACHE"}]
+ description = "Deploy environment configuration"
+ encryption_key = "arn:aws:kms:eu-west-1:719261439472:alias/aws/s3"
+ environment = [{"certificate": "", "compute_type": "BUILD_GENERAL1_SMALL", "environment_variable": [], "image": "aws/codebuild/amazonlinux2-x86_64-standard:2.0", "image_pull_credentials_type": "CODEBUILD", "privileged_mode": false, "registry_credential": [], "type": "LINUX_CONTAINER"}]
+ id = "arn:aws:codebuild:eu-west-1:719261439472:project/why-my-project-not-working"
+ logs_config = [{"cloudwatch_logs": [{"group_name": "", "status": "ENABLED", "stream_name": ""}], "s3_logs": [{"encryption_disabled": false, "location": "", "status": "DISABLED"}]}]
+ name = "why-my-project-not-working"
+ queued_timeout = 480
+ secondary_artifacts = []
+ secondary_sources = []
+ service_role = "arn:aws:iam::719261439472:role/terra_ci_job"
+ source = [{"auth": [], "buildspec": "version: 0.2\nphases:\n install:\n commands:\n - make install_tools\n build:\n commands:\n - make plan_local resource=$TERRA_CI_RESOURCE\nartifacts:\n files:\n - ./tfplan\n name: $TERRA_CI_BUILD_NAME\n", "git_clone_depth": 1, "git_submodules_config": [], "insecure_ssl": false, "location": "https://github.com/p0tr3c-terraform/terra-ci-single-account.git", "report_build_status": false, "type": "GITHUB"}]
+ source_version = ""
+ tags = {}
+ vpc_config = []
+}
+
+resource "aws_iam_user" "ci" {
+ arn = "arn:aws:iam::719261439472:user/ci"
+ force_destroy = false
+ id = "ci"
+ name = "ci"
+ path = "/"
+ permissions_boundary = null
+ tags = {}
+ unique_id = "AIDA2O52SSXYORYI4EPXD"
+}
+
diff --git a/tests/test_files/tf_content_generator_files/tfplan-update-example/tfplan.json b/tests/test_files/tf_content_generator_files/tfplan-update-example/tfplan.json
new file mode 100644
index 00000000..3dde57e2
--- /dev/null
+++ b/tests/test_files/tf_content_generator_files/tfplan-update-example/tfplan.json
@@ -0,0 +1,736 @@
+{
+ "format_version": "0.1",
+ "terraform_version": "0.15.0",
+ "variables": {
+ "AWSServiceRoleForAPIGatewayPresent": {
+ "value": false
+ },
+ "AWSServiceRoleForAmazonEKSPresent": {
+ "value": false
+ },
+ "AWSServiceRoleForAutoScalingPresent": {
+ "value": false
+ },
+ "AWSServiceRoleForOrganizationsPresent": {
+ "value": false
+ },
+ "AWSServiceRoleForSupportPresent": {
+ "value": false
+ },
+ "AWSServiceRoleForTrustedAdvisorPresent": {
+ "value": false
+ },
+ "OrganizationAccountAccessRolePresent": {
+ "value": false
+ },
+ "aws_account_id": {
+ "value": "719261439472"
+ }
+ },
+ "planned_values": {
+ "root_module": {
+ "resources": [
+ {
+ "address": "aws_codebuild_project.some_projed",
+ "mode": "managed",
+ "type": "aws_codebuild_project",
+ "name": "some_projed",
+ "provider_name": "registry.terraform.io/hashicorp/aws",
+ "schema_version": 0,
+ "values": {
+ "arn": "arn:aws:codebuild:eu-west-1:719261439472:project/why-my-project-not-working",
+ "artifacts": [
+ {
+ "artifact_identifier": "",
+ "encryption_disabled": true,
+ "location": "terra-ci-artifacts-eu-west-1-000002",
+ "name": "why-my-project-not-working",
+ "namespace_type": "NONE",
+ "override_artifact_name": true,
+ "packaging": "NONE",
+ "path": "",
+ "type": "S3"
+ }
+ ],
+ "badge_enabled": false,
+ "badge_url": "",
+ "build_timeout": 10,
+ "cache": [
+ {
+ "location": "",
+ "modes": [],
+ "type": "NO_CACHE"
+ }
+ ],
+ "description": "Deploy environment configuration",
+ "encryption_key": "arn:aws:kms:eu-west-1:719261439472:alias/aws/s3",
+ "environment": [
+ {
+ "certificate": "",
+ "compute_type": "BUILD_GENERAL1_SMALL",
+ "environment_variable": [],
+ "image": "aws/codebuild/amazonlinux2-x86_64-standard:2.0",
+ "image_pull_credentials_type": "CODEBUILD",
+ "privileged_mode": false,
+ "registry_credential": [],
+ "type": "LINUX_CONTAINER"
+ }
+ ],
+ "id": "arn:aws:codebuild:eu-west-1:719261439472:project/why-my-project-not-working",
+ "logs_config": [
+ {
+ "cloudwatch_logs": [
+ {
+ "group_name": "",
+ "status": "ENABLED",
+ "stream_name": ""
+ }
+ ],
+ "s3_logs": [
+ {
+ "encryption_disabled": false,
+ "location": "",
+ "status": "DISABLED"
+ }
+ ]
+ }
+ ],
+ "name": "why-my-project-not-working",
+ "queued_timeout": 480,
+ "secondary_artifacts": [],
+ "secondary_sources": [],
+ "service_role": "arn:aws:iam::719261439472:role/terra_ci_job",
+ "source": [
+ {
+ "auth": [],
+ "buildspec": "version: 0.2\nphases:\n install:\n commands:\n - make install_tools\n build:\n commands:\n - make plan_local resource=$TERRA_CI_RESOURCE\nartifacts:\n files:\n - ./tfplan\n name: $TERRA_CI_BUILD_NAME\n",
+ "git_clone_depth": 1,
+ "git_submodules_config": [],
+ "insecure_ssl": false,
+ "location": "https://github.com/p0tr3c-terraform/terra-ci-single-account.git",
+ "report_build_status": false,
+ "type": "GITHUB"
+ }
+ ],
+ "source_version": "",
+ "tags": {},
+ "vpc_config": []
+ }
+ },
+ {
+ "address": "aws_iam_user.ci",
+ "mode": "managed",
+ "type": "aws_iam_user",
+ "name": "ci",
+ "provider_name": "registry.terraform.io/hashicorp/aws",
+ "schema_version": 0,
+ "values": {
+ "arn": "arn:aws:iam::719261439472:user/ci",
+ "force_destroy": false,
+ "id": "ci",
+ "name": "ci",
+ "path": "/",
+ "permissions_boundary": null,
+ "tags": {},
+ "unique_id": "AIDA2O52SSXYORYI4EPXD"
+ }
+ }
+ ]
+ }
+ },
+ "resource_changes": [
+ {
+ "address": "aws_codebuild_project.some_projed",
+ "mode": "managed",
+ "type": "aws_codebuild_project",
+ "name": "some_projed",
+ "provider_name": "registry.terraform.io/hashicorp/aws",
+ "change": {
+ "actions": [
+ "update"
+ ],
+ "before": {
+ "arn": "arn:aws:codebuild:eu-west-1:719261439472:project/why-my-project-not-working",
+ "artifacts": [
+ {
+ "artifact_identifier": "",
+ "encryption_disabled": false,
+ "location": "terra-ci-artifacts-eu-west-1-000002",
+ "name": "why-my-project-not-working",
+ "namespace_type": "NONE",
+ "override_artifact_name": true,
+ "packaging": "NONE",
+ "path": "",
+ "type": "S3"
+ }
+ ],
+ "badge_enabled": false,
+ "badge_url": "",
+ "build_timeout": 10,
+ "cache": [
+ {
+ "location": "",
+ "modes": [],
+ "type": "NO_CACHE"
+ }
+ ],
+ "description": "Deploy environment configuration",
+ "encryption_key": "arn:aws:kms:eu-west-1:719261439472:alias/aws/s3",
+ "environment": [
+ {
+ "certificate": "",
+ "compute_type": "BUILD_GENERAL1_SMALL",
+ "environment_variable": [],
+ "image": "aws/codebuild/amazonlinux2-x86_64-standard:2.0",
+ "image_pull_credentials_type": "CODEBUILD",
+ "privileged_mode": false,
+ "registry_credential": [],
+ "type": "LINUX_CONTAINER"
+ }
+ ],
+ "id": "arn:aws:codebuild:eu-west-1:719261439472:project/why-my-project-not-working",
+ "logs_config": [
+ {
+ "cloudwatch_logs": [
+ {
+ "group_name": "",
+ "status": "ENABLED",
+ "stream_name": ""
+ }
+ ],
+ "s3_logs": [
+ {
+ "encryption_disabled": false,
+ "location": "",
+ "status": "DISABLED"
+ }
+ ]
+ }
+ ],
+ "name": "why-my-project-not-working",
+ "queued_timeout": 480,
+ "secondary_artifacts": [],
+ "secondary_sources": [],
+ "service_role": "arn:aws:iam::719261439472:role/terra_ci_job",
+ "source": [
+ {
+ "auth": [],
+ "buildspec": "version: 0.2\nphases:\n install:\n commands:\n - make install_tools\n build:\n commands:\n - make plan_local resource=$TERRA_CI_RESOURCE\nartifacts:\n files:\n - ./tfplan\n name: $TERRA_CI_BUILD_NAME\n",
+ "git_clone_depth": 1,
+ "git_submodules_config": [],
+ "insecure_ssl": false,
+ "location": "https://github.com/p0tr3c-terraform/terra-ci-single-account.git",
+ "report_build_status": false,
+ "type": "GITHUB"
+ }
+ ],
+ "source_version": "",
+ "tags": {},
+ "vpc_config": []
+ },
+ "after": {
+ "arn": "arn:aws:codebuild:eu-west-1:719261439472:project/why-my-project-not-working",
+ "artifacts": [
+ {
+ "artifact_identifier": "",
+ "encryption_disabled": true,
+ "location": "terra-ci-artifacts-eu-west-1-000002",
+ "name": "why-my-project-not-working",
+ "namespace_type": "NONE",
+ "override_artifact_name": true,
+ "packaging": "NONE",
+ "path": "",
+ "type": "S3"
+ }
+ ],
+ "badge_enabled": false,
+ "badge_url": "",
+ "build_timeout": 10,
+ "cache": [
+ {
+ "location": "",
+ "modes": [],
+ "type": "NO_CACHE"
+ }
+ ],
+ "description": "Deploy environment configuration",
+ "encryption_key": "arn:aws:kms:eu-west-1:719261439472:alias/aws/s3",
+ "environment": [
+ {
+ "certificate": "",
+ "compute_type": "BUILD_GENERAL1_SMALL",
+ "environment_variable": [],
+ "image": "aws/codebuild/amazonlinux2-x86_64-standard:2.0",
+ "image_pull_credentials_type": "CODEBUILD",
+ "privileged_mode": false,
+ "registry_credential": [],
+ "type": "LINUX_CONTAINER"
+ }
+ ],
+ "id": "arn:aws:codebuild:eu-west-1:719261439472:project/why-my-project-not-working",
+ "logs_config": [
+ {
+ "cloudwatch_logs": [
+ {
+ "group_name": "",
+ "status": "ENABLED",
+ "stream_name": ""
+ }
+ ],
+ "s3_logs": [
+ {
+ "encryption_disabled": false,
+ "location": "",
+ "status": "DISABLED"
+ }
+ ]
+ }
+ ],
+ "name": "why-my-project-not-working",
+ "queued_timeout": 480,
+ "secondary_artifacts": [],
+ "secondary_sources": [],
+ "service_role": "arn:aws:iam::719261439472:role/terra_ci_job",
+ "source": [
+ {
+ "auth": [],
+ "buildspec": "version: 0.2\nphases:\n install:\n commands:\n - make install_tools\n build:\n commands:\n - make plan_local resource=$TERRA_CI_RESOURCE\nartifacts:\n files:\n - ./tfplan\n name: $TERRA_CI_BUILD_NAME\n",
+ "git_clone_depth": 1,
+ "git_submodules_config": [],
+ "insecure_ssl": false,
+ "location": "https://github.com/p0tr3c-terraform/terra-ci-single-account.git",
+ "report_build_status": false,
+ "type": "GITHUB"
+ }
+ ],
+ "source_version": "",
+ "tags": {},
+ "vpc_config": []
+ },
+ "after_unknown": {},
+ "before_sensitive": {
+ "artifacts": [
+ {}
+ ],
+ "cache": [
+ {
+ "modes": []
+ }
+ ],
+ "environment": [
+ {
+ "environment_variable": [],
+ "registry_credential": []
+ }
+ ],
+ "logs_config": [
+ {
+ "cloudwatch_logs": [
+ {}
+ ],
+ "s3_logs": [
+ {}
+ ]
+ }
+ ],
+ "secondary_artifacts": [],
+ "secondary_sources": [],
+ "source": [
+ {
+ "auth": [],
+ "git_submodules_config": []
+ }
+ ],
+ "tags": {},
+ "vpc_config": []
+ },
+ "after_sensitive": {
+ "artifacts": [
+ {}
+ ],
+ "cache": [
+ {
+ "modes": []
+ }
+ ],
+ "environment": [
+ {
+ "environment_variable": [],
+ "registry_credential": []
+ }
+ ],
+ "logs_config": [
+ {
+ "cloudwatch_logs": [
+ {}
+ ],
+ "s3_logs": [
+ {}
+ ]
+ }
+ ],
+ "secondary_artifacts": [],
+ "secondary_sources": [],
+ "source": [
+ {
+ "auth": [],
+ "git_submodules_config": []
+ }
+ ],
+ "tags": {},
+ "vpc_config": []
+ }
+ }
+ },
+ {
+ "address": "aws_iam_user.ci",
+ "mode": "managed",
+ "type": "aws_iam_user",
+ "name": "ci",
+ "provider_name": "registry.terraform.io/hashicorp/aws",
+ "change": {
+ "actions": [
+ "no-op"
+ ],
+ "before": {
+ "arn": "arn:aws:iam::719261439472:user/ci",
+ "force_destroy": false,
+ "id": "ci",
+ "name": "ci",
+ "path": "/",
+ "permissions_boundary": null,
+ "tags": {},
+ "unique_id": "AIDA2O52SSXYORYI4EPXD"
+ },
+ "after": {
+ "arn": "arn:aws:iam::719261439472:user/ci",
+ "force_destroy": false,
+ "id": "ci",
+ "name": "ci",
+ "path": "/",
+ "permissions_boundary": null,
+ "tags": {},
+ "unique_id": "AIDA2O52SSXYORYI4EPXD"
+ },
+ "after_unknown": {},
+ "before_sensitive": {
+ "tags": {}
+ },
+ "after_sensitive": {
+ "tags": {}
+ }
+ }
+ }
+ ],
+ "prior_state": {
+ "format_version": "0.1",
+ "terraform_version": "0.15.0",
+ "values": {
+ "root_module": {
+ "resources": [
+ {
+ "address": "aws_codebuild_project.some_projed",
+ "mode": "managed",
+ "type": "aws_codebuild_project",
+ "name": "some_projed",
+ "provider_name": "registry.terraform.io/hashicorp/aws",
+ "schema_version": 0,
+ "values": {
+ "arn": "arn:aws:codebuild:eu-west-1:719261439472:project/why-my-project-not-working",
+ "artifacts": [
+ {
+ "artifact_identifier": "",
+ "encryption_disabled": false,
+ "location": "terra-ci-artifacts-eu-west-1-000002",
+ "name": "why-my-project-not-working",
+ "namespace_type": "NONE",
+ "override_artifact_name": true,
+ "packaging": "NONE",
+ "path": "",
+ "type": "S3"
+ }
+ ],
+ "badge_enabled": false,
+ "badge_url": "",
+ "build_timeout": 10,
+ "cache": [
+ {
+ "location": "",
+ "modes": [],
+ "type": "NO_CACHE"
+ }
+ ],
+ "description": "Deploy environment configuration",
+ "encryption_key": "arn:aws:kms:eu-west-1:719261439472:alias/aws/s3",
+ "environment": [
+ {
+ "certificate": "",
+ "compute_type": "BUILD_GENERAL1_SMALL",
+ "environment_variable": [],
+ "image": "aws/codebuild/amazonlinux2-x86_64-standard:2.0",
+ "image_pull_credentials_type": "CODEBUILD",
+ "privileged_mode": false,
+ "registry_credential": [],
+ "type": "LINUX_CONTAINER"
+ }
+ ],
+ "id": "arn:aws:codebuild:eu-west-1:719261439472:project/why-my-project-not-working",
+ "logs_config": [
+ {
+ "cloudwatch_logs": [
+ {
+ "group_name": "",
+ "status": "ENABLED",
+ "stream_name": ""
+ }
+ ],
+ "s3_logs": [
+ {
+ "encryption_disabled": false,
+ "location": "",
+ "status": "DISABLED"
+ }
+ ]
+ }
+ ],
+ "name": "why-my-project-not-working",
+ "queued_timeout": 480,
+ "secondary_artifacts": [],
+ "secondary_sources": [],
+ "service_role": "arn:aws:iam::719261439472:role/terra_ci_job",
+ "source": [
+ {
+ "auth": [],
+ "buildspec": "version: 0.2\nphases:\n install:\n commands:\n - make install_tools\n build:\n commands:\n - make plan_local resource=$TERRA_CI_RESOURCE\nartifacts:\n files:\n - ./tfplan\n name: $TERRA_CI_BUILD_NAME\n",
+ "git_clone_depth": 1,
+ "git_submodules_config": [],
+ "insecure_ssl": false,
+ "location": "https://github.com/p0tr3c-terraform/terra-ci-single-account.git",
+ "report_build_status": false,
+ "type": "GITHUB"
+ }
+ ],
+ "source_version": "",
+ "tags": {},
+ "vpc_config": []
+ },
+ "depends_on": [
+ "data.template_file.terra_ci"
+ ]
+ },
+ {
+ "address": "aws_iam_user.ci",
+ "mode": "managed",
+ "type": "aws_iam_user",
+ "name": "ci",
+ "provider_name": "registry.terraform.io/hashicorp/aws",
+ "schema_version": 0,
+ "values": {
+ "arn": "arn:aws:iam::719261439472:user/ci",
+ "force_destroy": false,
+ "id": "ci",
+ "name": "ci",
+ "path": "/",
+ "permissions_boundary": null,
+ "tags": {},
+ "unique_id": "AIDA2O52SSXYORYI4EPXD"
+ }
+ },
+ {
+ "address": "data.template_file.terra_ci",
+ "mode": "data",
+ "type": "template_file",
+ "name": "terra_ci",
+ "provider_name": "registry.terraform.io/hashicorp/template",
+ "schema_version": 0,
+ "values": {
+ "filename": null,
+ "id": "71c1f84bdc6733e3bcc0e6a7a4cbcdbaa9725d7238cf8b0cf8fe995a826bf534",
+ "rendered": "version: 0.2\nphases:\n install:\n commands:\n - make install_tools\n build:\n commands:\n - make plan_local resource=$TERRA_CI_RESOURCE\nartifacts:\n files:\n - ./tfplan\n name: $TERRA_CI_BUILD_NAME\n",
+ "template": "version: 0.2\nphases:\n install:\n commands:\n - make install_tools\n build:\n commands:\n - make plan_local resource=$TERRA_CI_RESOURCE\nartifacts:\n files:\n - ./tfplan\n name: $TERRA_CI_BUILD_NAME\n",
+ "vars": null
+ }
+ }
+ ]
+ }
+ }
+ },
+ "configuration": {
+ "provider_config": {
+ "aws": {
+ "name": "aws",
+ "expressions": {
+ "allowed_account_ids": {
+ "constant_value": [
+ "719261439472"
+ ]
+ },
+ "assume_role": [
+ {
+ "role_arn": {
+ "constant_value": "arn:aws:iam::719261439472:role/ci"
+ }
+ }
+ ],
+ "region": {
+ "constant_value": "eu-west-1"
+ }
+ }
+ }
+ },
+ "root_module": {
+ "resources": [
+ {
+ "address": "aws_codebuild_project.some_projed",
+ "mode": "managed",
+ "type": "aws_codebuild_project",
+ "name": "some_projed",
+ "provider_config_key": "aws",
+ "expressions": {
+ "artifacts": [
+ {
+ "encryption_disabled": {
+ "constant_value": true
+ },
+ "location": {
+ "constant_value": "terra-ci-artifacts-eu-west-1-000002"
+ },
+ "override_artifact_name": {
+ "constant_value": true
+ },
+ "type": {
+ "constant_value": "S3"
+ }
+ }
+ ],
+ "build_timeout": {
+ "constant_value": "10"
+ },
+ "description": {
+ "constant_value": "Deploy environment configuration"
+ },
+ "environment": [
+ {
+ "compute_type": {
+ "constant_value": "BUILD_GENERAL1_SMALL"
+ },
+ "image": {
+ "constant_value": "aws/codebuild/amazonlinux2-x86_64-standard:2.0"
+ },
+ "image_pull_credentials_type": {
+ "constant_value": "CODEBUILD"
+ },
+ "privileged_mode": {
+ "constant_value": false
+ },
+ "type": {
+ "constant_value": "LINUX_CONTAINER"
+ }
+ }
+ ],
+ "logs_config": [
+ {
+ "cloudwatch_logs": [
+ {
+ "status": {
+ "constant_value": "ENABLED"
+ }
+ }
+ ],
+ "s3_logs": [
+ {
+ "encryption_disabled": {
+ "constant_value": false
+ },
+ "status": {
+ "constant_value": "DISABLED"
+ }
+ }
+ ]
+ }
+ ],
+ "name": {
+ "constant_value": "why-my-project-not-working"
+ },
+ "service_role": {
+ "constant_value": "arn:aws:iam::719261439472:role/terra_ci_job"
+ },
+ "source": [
+ {
+ "buildspec": {
+ "references": [
+ "data.template_file.terra_ci"
+ ]
+ },
+ "git_clone_depth": {
+ "constant_value": 1
+ },
+ "insecure_ssl": {
+ "constant_value": false
+ },
+ "location": {
+ "constant_value": "https://github.com/p0tr3c-terraform/terra-ci-single-account.git"
+ },
+ "report_build_status": {
+ "constant_value": false
+ },
+ "type": {
+ "constant_value": "GITHUB"
+ }
+ }
+ ]
+ },
+ "schema_version": 0
+ },
+ {
+ "address": "aws_iam_user.ci",
+ "mode": "managed",
+ "type": "aws_iam_user",
+ "name": "ci",
+ "provider_config_key": "aws",
+ "expressions": {
+ "name": {
+ "constant_value": "ci"
+ }
+ },
+ "schema_version": 0
+ },
+ {
+ "address": "data.template_file.terra_ci",
+ "mode": "data",
+ "type": "template_file",
+ "name": "terra_ci",
+ "provider_config_key": "template",
+ "expressions": {
+ "template": {}
+ },
+ "schema_version": 0
+ }
+ ],
+ "variables": {
+ "AWSServiceRoleForAPIGatewayPresent": {
+ "default": false
+ },
+ "AWSServiceRoleForAmazonEKSPresent": {
+ "default": false
+ },
+ "AWSServiceRoleForAutoScalingPresent": {
+ "default": false
+ },
+ "AWSServiceRoleForOrganizationsPresent": {
+ "default": false
+ },
+ "AWSServiceRoleForSupportPresent": {
+ "default": false
+ },
+ "AWSServiceRoleForTrustedAdvisorPresent": {
+ "default": false
+ },
+ "OrganizationAccountAccessRolePresent": {
+ "default": false
+ },
+ "aws_account_id": {}
+ }
+ }
+ }
+}
\ No newline at end of file
From ec8333707ab2590518fd0f36454c8636ccbf1061 Mon Sep 17 00:00:00 2001
From: Peleg Admi <129038284+PelegCycode@users.noreply.github.com>
Date: Wed, 9 Aug 2023 17:30:54 +0300
Subject: [PATCH 025/257] CM-26097 - Add no-restore flag for SCA (#154)
* added disable restore flag to cli
* added shortcut for flag
* changed flag name
* removed cli flag shortcut
* minor fix
* change flag to no-restore
* moved flag reading place
* fixed help description
* Update cycode/cli/main.py
Co-authored-by: Ilya Siamionau
* removed unused import
* updated readme
* remove no restore from scan params
* changed declared to specified
* renamed flag constant
---------
Co-authored-by: Ilya Siamionau
---
README.md | 25 +++++++++++++------------
cycode/cli/code_scanner.py | 3 ++-
cycode/cli/consts.py | 2 ++
cycode/cli/main.py | 18 +++++++++++++++++-
4 files changed, 34 insertions(+), 14 deletions(-)
diff --git a/README.md b/README.md
index 4e3da50a..7cdc5338 100644
--- a/README.md
+++ b/README.md
@@ -232,18 +232,19 @@ The following are the options and commands available with the Cycode CLI applica
The Cycode CLI application offers several types of scans so that you can choose the option that best fits your case. The following are the current options and commands available:
-| Option | Description |
-|--------------------------------------|----------------------------------------------------------------------------|
-| `-t, --scan-type [secret\|iac\|sca\|sast]` | Specify the scan you wish to execute (`secret`/`iac`/`sca`/`sast`), the default is `secret` |
-| `--secret TEXT` | Specify a Cycode client secret for this specific scan execution |
-| `--client-id TEXT` | Specify a Cycode client ID for this specific scan execution |
-| `--show-secret BOOLEAN` | Show secrets in plain text. See [Show/Hide Secrets](#showhide-secrets) section for more details. |
-| `--soft-fail BOOLEAN` | Run scan without failing, always return a non-error status code. See [Soft Fail](#soft-fail) section for more details. |
-| `--severity-threshold [INFO\|LOW\|MEDIUM\|HIGH\|CRITICAL]` | Show only violations at the specified level or higher (supported for the SCA scan type only). |
-| `--sca-scan` | Specify the SCA scan you wish to execute (`package-vulnerabilities`/`license-compliance`). The default is both |
-| `--monitor` | When specified, the scan results will be recorded in the knowledge graph. Please note that when working in `monitor` mode, the knowledge graph will not be updated as a result of SCM events (Push, Repo creation). (Supported for SCA scan type only). |
-| `--report` | When specified, a violations report will be generated. A URL link to the report will be printed as an output to the command execution |
-| `--help` | Show options for given command. |
+| Option | Description |
+|------------------------------------------------------------|---------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------|
+| `-t, --scan-type [secret\|iac\|sca\|sast]` | Specify the scan you wish to execute (`secret`/`iac`/`sca`/`sast`), the default is `secret` |
+| `--secret TEXT` | Specify a Cycode client secret for this specific scan execution |
+| `--client-id TEXT` | Specify a Cycode client ID for this specific scan execution |
+| `--show-secret BOOLEAN` | Show secrets in plain text. See [Show/Hide Secrets](#showhide-secrets) section for more details. |
+| `--soft-fail BOOLEAN` | Run scan without failing, always return a non-error status code. See [Soft Fail](#soft-fail) section for more details. |
+| `--severity-threshold [INFO\|LOW\|MEDIUM\|HIGH\|CRITICAL]` | Show only violations at the specified level or higher (supported for the SCA scan type only). |
+| `--sca-scan` | Specify the SCA scan you wish to execute (`package-vulnerabilities`/`license-compliance`). The default is both |
+| `--monitor` | When specified, the scan results will be recorded in the knowledge graph. Please note that when working in `monitor` mode, the knowledge graph will not be updated as a result of SCM events (Push, Repo creation). (Supported for SCA scan type only). |
+| `--report` | When specified, a violations report will be generated. A URL link to the report will be printed as an output to the command execution |
+| `--no-restore` | When specified, Cycode will not run restore command. Will scan direct dependencies ONLY! |
+| `--help` | Show options for given command. |
| Command | Description |
|----------------------------------------|-----------------------------------------------------------------|
diff --git a/cycode/cli/code_scanner.py b/cycode/cli/code_scanner.py
index 978b4240..f63ebf08 100644
--- a/cycode/cli/code_scanner.py
+++ b/cycode/cli/code_scanner.py
@@ -15,6 +15,7 @@
from cycode.cli import consts
from cycode.cli.ci_integrations import get_commit_range
from cycode.cli.config import configuration_manager
+from cycode.cli.consts import SCA_SKIP_RESTORE_DEPENDENCIES_FLAG
from cycode.cli.exceptions import custom_exceptions
from cycode.cli.helpers import sca_code_scanner, tf_content_generator
from cycode.cli.models import CliError, CliErrors, Document, DocumentDetections, LocalScanResult, Severity
@@ -579,7 +580,7 @@ def create_local_scan_result(
def perform_pre_scan_documents_actions(
context: click.Context, scan_type: str, documents_to_scan: List[Document], is_git_diff: bool = False
) -> None:
- if scan_type == consts.SCA_SCAN_TYPE:
+ if scan_type == consts.SCA_SCAN_TYPE and not context.obj.get(SCA_SKIP_RESTORE_DEPENDENCIES_FLAG):
logger.debug('Perform pre scan document add_dependencies_tree_document action')
sca_code_scanner.add_dependencies_tree_document(context, documents_to_scan, is_git_diff)
diff --git a/cycode/cli/consts.py b/cycode/cli/consts.py
index 76570fde..43046f7f 100644
--- a/cycode/cli/consts.py
+++ b/cycode/cli/consts.py
@@ -189,3 +189,5 @@
# Example: A -> B -> C
# Result: A -> ... -> C
SCA_SHORTCUT_DEPENDENCY_PATHS = 2
+
+SCA_SKIP_RESTORE_DEPENDENCIES_FLAG = 'no-restore'
diff --git a/cycode/cli/main.py b/cycode/cli/main.py
index 821251ad..23c211c3 100644
--- a/cycode/cli/main.py
+++ b/cycode/cli/main.py
@@ -9,7 +9,13 @@
from cycode.cli import code_scanner
from cycode.cli.auth.auth_command import authenticate
from cycode.cli.config import config
-from cycode.cli.consts import CLI_CONTEXT_SETTINGS, ISSUE_DETECTED_STATUS_CODE, NO_ISSUES_STATUS_CODE, PROGRAM_NAME
+from cycode.cli.consts import (
+ CLI_CONTEXT_SETTINGS,
+ ISSUE_DETECTED_STATUS_CODE,
+ NO_ISSUES_STATUS_CODE,
+ PROGRAM_NAME,
+ SCA_SKIP_RESTORE_DEPENDENCIES_FLAG,
+)
from cycode.cli.models import Severity
from cycode.cli.user_settings.configuration_manager import ConfigurationManager
from cycode.cli.user_settings.credentials_manager import CredentialsManager
@@ -99,6 +105,14 @@
type=bool,
required=False,
)
+@click.option(
+ f'--{SCA_SKIP_RESTORE_DEPENDENCIES_FLAG}',
+ is_flag=True,
+ default=False,
+ help='When specified, Cycode will not run restore command. Will scan direct dependencies ONLY!',
+ type=bool,
+ required=False,
+)
@click.pass_context
def code_scan(
context: click.Context,
@@ -111,6 +125,7 @@ def code_scan(
sca_scan: List[str],
monitor: bool,
report: bool,
+ no_restore: bool,
) -> int:
"""Scans for Secrets, IaC, SCA or SAST violations."""
if show_secret:
@@ -128,6 +143,7 @@ def code_scan(
context.obj['severity_threshold'] = severity_threshold
context.obj['monitor'] = monitor
context.obj['report'] = report
+ context.obj[SCA_SKIP_RESTORE_DEPENDENCIES_FLAG] = no_restore
_sca_scan_to_context(context, sca_scan)
From b6d966f6b95722625ee9a5812135008a4bb7c792 Mon Sep 17 00:00:00 2001
From: "codesee-maps[bot]"
<86324825+codesee-maps[bot]@users.noreply.github.com>
Date: Sun, 20 Aug 2023 10:51:26 +0300
Subject: [PATCH 026/257] Install the CodeSee workflow. (#157)
Install the CodeSee workflow. Learn more at https://docs.codesee.io
Co-authored-by: codesee-maps[bot] <86324825+codesee-maps[bot]@users.noreply.github.com>
---
.github/workflows/codesee-arch-diagram.yml | 23 ++++++++++++++++++++++
1 file changed, 23 insertions(+)
create mode 100644 .github/workflows/codesee-arch-diagram.yml
diff --git a/.github/workflows/codesee-arch-diagram.yml b/.github/workflows/codesee-arch-diagram.yml
new file mode 100644
index 00000000..806d41d1
--- /dev/null
+++ b/.github/workflows/codesee-arch-diagram.yml
@@ -0,0 +1,23 @@
+# This workflow was added by CodeSee. Learn more at https://codesee.io/
+# This is v2.0 of this workflow file
+on:
+ push:
+ branches:
+ - main
+ pull_request_target:
+ types: [opened, synchronize, reopened]
+
+name: CodeSee
+
+permissions: read-all
+
+jobs:
+ codesee:
+ runs-on: ubuntu-latest
+ continue-on-error: true
+ name: Analyze the repo with CodeSee
+ steps:
+ - uses: Codesee-io/codesee-action@v2
+ with:
+ codesee-token: ${{ secrets.CODESEE_ARCH_DIAG_API_TOKEN }}
+ codesee-url: https://app.codesee.io
From 39e517187e7f5d3349b549639a4a30d40a447579 Mon Sep 17 00:00:00 2001
From: Ilya Siamionau
Date: Mon, 21 Aug 2023 16:31:35 +0400
Subject: [PATCH 027/257] CM-23216 - Sign Windows CLI executable (#158)
---
.github/workflows/black.yml | 2 ++
.github/workflows/build_executable.yml | 45 +++++++++++++++++++++++++-
.github/workflows/pre_release.yml | 2 ++
.github/workflows/release.yml | 2 ++
.github/workflows/ruff.yml | 2 ++
.github/workflows/tests.yml | 2 ++
.github/workflows/tests_full.yml | 2 ++
7 files changed, 56 insertions(+), 1 deletion(-)
diff --git a/.github/workflows/black.yml b/.github/workflows/black.yml
index 917994f5..d8003685 100644
--- a/.github/workflows/black.yml
+++ b/.github/workflows/black.yml
@@ -36,6 +36,8 @@ jobs:
- name: Setup Poetry
if: steps.cached-poetry.outputs.cache-hit != 'true'
uses: snok/install-poetry@v1
+ with:
+ version: 1.5.1
- name: Add Poetry to PATH
run: echo "$HOME/.local/bin" >> $GITHUB_PATH
diff --git a/.github/workflows/build_executable.yml b/.github/workflows/build_executable.yml
index f3690f11..ed88613e 100644
--- a/.github/workflows/build_executable.yml
+++ b/.github/workflows/build_executable.yml
@@ -51,6 +51,8 @@ jobs:
- name: Setup Poetry
if: steps.cached-poetry.outputs.cache-hit != 'true'
uses: snok/install-poetry@v1
+ with:
+ version: 1.5.1
- name: Add Poetry to PATH
run: echo "$HOME/.local/bin" >> $GITHUB_PATH
@@ -108,10 +110,51 @@ jobs:
# we can't staple the app because it's executable. we should only staple app bundles like .dmg
# xcrun stapler staple dist/cycode
- - name: Test signed executable
+ - name: Test macOS signed executable
if: ${{ startsWith(matrix.os, 'macos') }}
run: ./dist/cycode version
+ - name: Import cert for Windows and setup envs
+ if: ${{ startsWith(matrix.os, 'windows') }}
+ env:
+ SM_CLIENT_CERT_FILE_B64: ${{ secrets.SM_CLIENT_CERT_FILE_B64 }}
+ run: |
+ # import certificate
+ echo "$SM_CLIENT_CERT_FILE_B64" | base64 --decode > /d/Certificate_pkcs12.p12
+ echo "SM_CLIENT_CERT_FILE=D:\\Certificate_pkcs12.p12" >> "$GITHUB_ENV"
+
+ # add required soft to the path
+ echo "C:\Program Files (x86)\Windows Kits\10\App Certification Kit" >> $GITHUB_PATH
+ echo "C:\Program Files\DigiCert\DigiCert One Signing Manager Tools" >> $GITHUB_PATH
+
+ - name: Sign Windows executable
+ if: ${{ startsWith(matrix.os, 'windows') }}
+ shell: cmd
+ env:
+ SM_HOST: ${{ secrets.SM_HOST }}
+ SM_API_KEY: ${{ secrets.SM_API_KEY }}
+ SM_CLIENT_CERT_PASSWORD: ${{ secrets.SM_CLIENT_CERT_PASSWORD }}
+ SM_CODE_SIGNING_CERT_SHA1_HASH: ${{ secrets.SM_CODE_SIGNING_CERT_SHA1_HASH }}
+ run: |
+ :: setup SSM KSP
+ curl -X GET https://one.digicert.com/signingmanager/api-ui/v1/releases/smtools-windows-x64.msi/download -H "x-api-key:%SM_API_KEY%" -o smtools-windows-x64.msi
+ msiexec /i smtools-windows-x64.msi /quiet /qn
+ C:\Windows\System32\certutil.exe -csp "DigiCert Signing Manager KSP" -key -user
+ smksp_cert_sync.exe
+
+ :: sign executable
+ signtool.exe sign /sha1 %SM_CODE_SIGNING_CERT_SHA1_HASH% /tr http://timestamp.digicert.com /td SHA256 /fd SHA256 ".\dist\cycode.exe"
+
+ - name: Test Windows signed executable
+ if: ${{ startsWith(matrix.os, 'windows') }}
+ shell: cmd
+ run: |
+ :: call executable and expect correct output
+ .\dist\cycode.exe version
+
+ :: verify signature
+ signtool.exe verify /v /pa ".\dist\cycode.exe"
+
- uses: actions/upload-artifact@v3
with:
name: cycode-cli-${{ matrix.os }}
diff --git a/.github/workflows/pre_release.yml b/.github/workflows/pre_release.yml
index a2734ca4..342d59bc 100644
--- a/.github/workflows/pre_release.yml
+++ b/.github/workflows/pre_release.yml
@@ -46,6 +46,8 @@ jobs:
- name: Setup Poetry
if: steps.cached-poetry.outputs.cache-hit != 'true'
uses: snok/install-poetry@v1
+ with:
+ version: 1.5.1
- name: Add Poetry to PATH
run: echo "$HOME/.local/bin" >> $GITHUB_PATH
diff --git a/.github/workflows/release.yml b/.github/workflows/release.yml
index 91eeb315..b578f6b6 100644
--- a/.github/workflows/release.yml
+++ b/.github/workflows/release.yml
@@ -45,6 +45,8 @@ jobs:
- name: Setup Poetry
if: steps.cached-poetry.outputs.cache-hit != 'true'
uses: snok/install-poetry@v1
+ with:
+ version: 1.5.1
- name: Add Poetry to PATH
run: echo "$HOME/.local/bin" >> $GITHUB_PATH
diff --git a/.github/workflows/ruff.yml b/.github/workflows/ruff.yml
index 6ef7cefd..919f4f2d 100644
--- a/.github/workflows/ruff.yml
+++ b/.github/workflows/ruff.yml
@@ -36,6 +36,8 @@ jobs:
- name: Setup Poetry
if: steps.cached-poetry.outputs.cache-hit != 'true'
uses: snok/install-poetry@v1
+ with:
+ version: 1.5.1
- name: Add Poetry to PATH
run: echo "$HOME/.local/bin" >> $GITHUB_PATH
diff --git a/.github/workflows/tests.yml b/.github/workflows/tests.yml
index 5b6db7c7..feccb486 100644
--- a/.github/workflows/tests.yml
+++ b/.github/workflows/tests.yml
@@ -39,6 +39,8 @@ jobs:
- name: Setup Poetry
if: steps.cached-poetry.outputs.cache-hit != 'true'
uses: snok/install-poetry@v1
+ with:
+ version: 1.5.1
- name: Add Poetry to PATH
run: echo "$HOME/.local/bin" >> $GITHUB_PATH
diff --git a/.github/workflows/tests_full.yml b/.github/workflows/tests_full.yml
index 461e1231..efd8226f 100644
--- a/.github/workflows/tests_full.yml
+++ b/.github/workflows/tests_full.yml
@@ -52,6 +52,8 @@ jobs:
- name: Setup Poetry
if: steps.cached-poetry.outputs.cache-hit != 'true'
uses: snok/install-poetry@v1
+ with:
+ version: 1.5.1
- name: Add Poetry to PATH
run: echo "$HOME/.local/bin" >> $GITHUB_PATH
From b286097011af62cbf2eeef4d320544b82e8bde1b Mon Sep 17 00:00:00 2001
From: "dependabot[bot]" <49699333+dependabot[bot]@users.noreply.github.com>
Date: Sat, 26 Aug 2023 02:51:23 +0400
Subject: [PATCH 028/257] Bump gitpython from 3.1.31 to 3.1.32 (#155)
---
poetry.lock | 6 +++---
1 file changed, 3 insertions(+), 3 deletions(-)
diff --git a/poetry.lock b/poetry.lock
index e4137a58..df7549f1 100644
--- a/poetry.lock
+++ b/poetry.lock
@@ -329,13 +329,13 @@ smmap = ">=3.0.1,<6"
[[package]]
name = "gitpython"
-version = "3.1.31"
+version = "3.1.32"
description = "GitPython is a Python library used to interact with Git repositories"
optional = false
python-versions = ">=3.7"
files = [
- {file = "GitPython-3.1.31-py3-none-any.whl", hash = "sha256:f04893614f6aa713a60cbbe1e6a97403ef633103cdd0ef5eb6efe0deb98dbe8d"},
- {file = "GitPython-3.1.31.tar.gz", hash = "sha256:8ce3bcf69adfdf7c7d503e78fd3b1c492af782d58893b650adb2ac8912ddd573"},
+ {file = "GitPython-3.1.32-py3-none-any.whl", hash = "sha256:e3d59b1c2c6ebb9dfa7a184daf3b6dd4914237e7488a1730a6d8f6f5d0b4187f"},
+ {file = "GitPython-3.1.32.tar.gz", hash = "sha256:8d9b8cb1e80b9735e8717c9362079d3ce4c6e5ddeebedd0361b228c3a67a62f6"},
]
[package.dependencies]
From 7de199a436bdc4762b083645893cf5f95f468449 Mon Sep 17 00:00:00 2001
From: Maor Davidzon <56628808+MaorDavidzon@users.noreply.github.com>
Date: Sun, 27 Aug 2023 15:24:23 +0300
Subject: [PATCH 029/257] CM-8818 remove codeSee workflow (#159)
---
.github/workflows/codesee-arch-diagram.yml | 23 ----------------------
1 file changed, 23 deletions(-)
delete mode 100644 .github/workflows/codesee-arch-diagram.yml
diff --git a/.github/workflows/codesee-arch-diagram.yml b/.github/workflows/codesee-arch-diagram.yml
deleted file mode 100644
index 806d41d1..00000000
--- a/.github/workflows/codesee-arch-diagram.yml
+++ /dev/null
@@ -1,23 +0,0 @@
-# This workflow was added by CodeSee. Learn more at https://codesee.io/
-# This is v2.0 of this workflow file
-on:
- push:
- branches:
- - main
- pull_request_target:
- types: [opened, synchronize, reopened]
-
-name: CodeSee
-
-permissions: read-all
-
-jobs:
- codesee:
- runs-on: ubuntu-latest
- continue-on-error: true
- name: Analyze the repo with CodeSee
- steps:
- - uses: Codesee-io/codesee-action@v2
- with:
- codesee-token: ${{ secrets.CODESEE_ARCH_DIAG_API_TOKEN }}
- codesee-url: https://app.codesee.io
From d934523e58e10baa6db0c07f24bb00c37e55314f Mon Sep 17 00:00:00 2001
From: Ilya Siamionau
Date: Tue, 12 Sep 2023 10:19:24 +0200
Subject: [PATCH 030/257] CM-27145 - Add setting of logger level for all
loggers; fix stream of loggers; fix setting of logger level from env (#162)
---
cycode/cli/code_scanner.py | 6 ++---
cycode/cli/consts.py | 2 --
cycode/cli/main.py | 9 +++----
cycode/cyclient/config.py | 54 ++++++++++++++++++++++++--------------
4 files changed, 40 insertions(+), 31 deletions(-)
diff --git a/cycode/cli/code_scanner.py b/cycode/cli/code_scanner.py
index f63ebf08..128e8a6f 100644
--- a/cycode/cli/code_scanner.py
+++ b/cycode/cli/code_scanner.py
@@ -33,13 +33,13 @@
load_json,
)
from cycode.cli.utils.progress_bar import ProgressBarSection
-from cycode.cli.utils.progress_bar import logger as progress_bar_logger
from cycode.cli.utils.scan_batch import run_parallel_batched_scan
from cycode.cli.utils.scan_utils import set_issue_detected
from cycode.cli.utils.string_utils import get_content_size, is_binary_content
from cycode.cli.utils.task_timer import TimeoutAfter
from cycode.cli.zip_file import InMemoryZip
from cycode.cyclient import logger
+from cycode.cyclient.config import set_logging_level
from cycode.cyclient.models import Detection, DetectionSchema, DetectionsPerFile, ZippedFileScanResult
if TYPE_CHECKING:
@@ -1399,9 +1399,7 @@ def perform_post_pre_receive_scan_actions(context: click.Context) -> None:
def enable_verbose_mode(context: click.Context) -> None:
context.obj['verbose'] = True
- # TODO(MarshalX): rework setting the log level for loggers
- logger.setLevel(logging.DEBUG)
- progress_bar_logger.setLevel(logging.DEBUG)
+ set_logging_level(logging.DEBUG)
def is_verbose_mode_requested_in_pre_receive_scan() -> bool:
diff --git a/cycode/cli/consts.py b/cycode/cli/consts.py
index 43046f7f..23b7471a 100644
--- a/cycode/cli/consts.py
+++ b/cycode/cli/consts.py
@@ -112,8 +112,6 @@
TIMEOUT_ENV_VAR_NAME = 'TIMEOUT'
CYCODE_CLI_REQUEST_TIMEOUT_ENV_VAR_NAME = 'CYCODE_CLI_REQUEST_TIMEOUT'
LOGGING_LEVEL_ENV_VAR_NAME = 'LOGGING_LEVEL'
-# use only for dev envs locally
-BATCH_SIZE_ENV_VAR_NAME = 'BATCH_SIZE'
VERBOSE_ENV_VAR_NAME = 'CYCODE_CLI_VERBOSE'
CYCODE_CONFIGURATION_DIRECTORY: str = '.cycode'
diff --git a/cycode/cli/main.py b/cycode/cli/main.py
index 23c211c3..94f3ff29 100644
--- a/cycode/cli/main.py
+++ b/cycode/cli/main.py
@@ -22,8 +22,7 @@
from cycode.cli.user_settings.user_settings_commands import add_exclusions, set_credentials
from cycode.cli.utils import scan_utils
from cycode.cli.utils.progress_bar import get_progress_bar
-from cycode.cli.utils.progress_bar import logger as progress_bar_logger
-from cycode.cyclient import logger
+from cycode.cyclient.config import set_logging_level
from cycode.cyclient.cycode_client_base import CycodeClientBase
from cycode.cyclient.models import UserAgentOptionScheme
from cycode.cyclient.scan_config.scan_config_creator import create_scan_client
@@ -228,10 +227,8 @@ def main_cli(
verbose = verbose or configuration_manager.get_verbose_flag()
context.obj['verbose'] = verbose
- # TODO(MarshalX): rework setting the log level for loggers
- log_level = logging.DEBUG if verbose else logging.INFO
- logger.setLevel(log_level)
- progress_bar_logger.setLevel(log_level)
+ if verbose:
+ set_logging_level(logging.DEBUG)
context.obj['output'] = output
if output == 'json':
diff --git a/cycode/cyclient/config.py b/cycode/cyclient/config.py
index 2c2f3c00..da3c6a18 100644
--- a/cycode/cyclient/config.py
+++ b/cycode/cyclient/config.py
@@ -6,17 +6,21 @@
from cycode.cli import consts
from cycode.cli.user_settings.configuration_manager import ConfigurationManager
+from cycode.cyclient.config_dev import DEV_MODE_ENV_VAR_NAME, DEV_TENANT_ID_ENV_VAR_NAME
-# set io encoding (for windows)
-from .config_dev import DEV_MODE_ENV_VAR_NAME, DEV_TENANT_ID_ENV_VAR_NAME
-sys.stdout.reconfigure(encoding='UTF-8')
-sys.stderr.reconfigure(encoding='UTF-8')
+def _set_io_encodings() -> None:
+ # set io encoding (for Windows)
+ sys.stdout.reconfigure(encoding='UTF-8')
+ sys.stderr.reconfigure(encoding='UTF-8')
+
+
+_set_io_encodings()
# logs
logging.basicConfig(
- stream=sys.stdout,
- level=logging.DEBUG,
+ stream=sys.stderr,
+ level=logging.INFO,
format='%(asctime)s [%(name)s] %(levelname)s: %(message)s',
datefmt='%Y-%m-%d %H:%M:%S',
)
@@ -34,19 +38,28 @@
consts.TIMEOUT_ENV_VAR_NAME: 300,
consts.LOGGING_LEVEL_ENV_VAR_NAME: logging.INFO,
DEV_MODE_ENV_VAR_NAME: 'False',
- consts.BATCH_SIZE_ENV_VAR_NAME: 20,
}
configuration = dict(DEFAULT_CONFIGURATION, **os.environ)
+_CREATED_LOGGERS = set()
+
def get_logger(logger_name: Optional[str] = None) -> logging.Logger:
- logger = logging.getLogger(logger_name)
- level = _get_val_as_string(consts.LOGGING_LEVEL_ENV_VAR_NAME)
- level = level if level in logging._nameToLevel else int(level)
- logger.setLevel(level)
+ config_level = _get_val_as_string(consts.LOGGING_LEVEL_ENV_VAR_NAME)
+ level = logging.getLevelName(config_level)
+
+ new_logger = logging.getLogger(logger_name)
+ new_logger.setLevel(level)
+
+ _CREATED_LOGGERS.add(new_logger)
- return logger
+ return new_logger
+
+
+def set_logging_level(level: int) -> None:
+ for created_logger in _CREATED_LOGGERS:
+ created_logger.setLevel(level)
def _get_val_as_string(key: str) -> str:
@@ -66,15 +79,20 @@ def _get_val_as_int(key: str) -> Optional[int]:
return None
-logger = get_logger('cycode cli')
+def _is_valid_url(url: str) -> bool:
+ try:
+ urlparse(url)
+ return True
+ except ValueError as e:
+ logger.warning(f'Invalid cycode api url: {url}, using default value', e)
+ return False
+
+logger = get_logger('cycode cli')
configuration_manager = ConfigurationManager()
cycode_api_url = configuration_manager.get_cycode_api_url()
-try:
- urlparse(cycode_api_url)
-except ValueError as e:
- logger.warning(f'Invalid cycode api url: {cycode_api_url}, using default value', e)
+if not _is_valid_url(cycode_api_url):
cycode_api_url = consts.DEFAULT_CYCODE_API_URL
timeout = _get_val_as_int(consts.CYCODE_CLI_REQUEST_TIMEOUT_ENV_VAR_NAME)
@@ -83,5 +101,3 @@ def _get_val_as_int(key: str) -> Optional[int]:
dev_mode = _get_val_as_bool(DEV_MODE_ENV_VAR_NAME)
dev_tenant_id = _get_val_as_string(DEV_TENANT_ID_ENV_VAR_NAME)
-batch_size = _get_val_as_int(consts.BATCH_SIZE_ENV_VAR_NAME)
-verbose = _get_val_as_bool(consts.VERBOSE_ENV_VAR_NAME)
From 5d0f6330ccbd2f2ffa93a7207f293e51ee1d30c9 Mon Sep 17 00:00:00 2001
From: "dependabot[bot]" <49699333+dependabot[bot]@users.noreply.github.com>
Date: Mon, 18 Sep 2023 14:44:28 +0200
Subject: [PATCH 031/257] Bump gitpython from 3.1.32 to 3.1.35 (#163)
Bumps [gitpython](https://github.com/gitpython-developers/GitPython) from 3.1.32 to 3.1.35.
- [Release notes](https://github.com/gitpython-developers/GitPython/releases)
- [Changelog](https://github.com/gitpython-developers/GitPython/blob/main/CHANGES)
- [Commits](https://github.com/gitpython-developers/GitPython/compare/3.1.32...3.1.35)
---
updated-dependencies:
- dependency-name: gitpython
dependency-type: direct:production
...
Signed-off-by: dependabot[bot]
Co-authored-by: dependabot[bot] <49699333+dependabot[bot]@users.noreply.github.com>
---
poetry.lock | 8 ++++----
1 file changed, 4 insertions(+), 4 deletions(-)
diff --git a/poetry.lock b/poetry.lock
index df7549f1..5e473450 100644
--- a/poetry.lock
+++ b/poetry.lock
@@ -1,4 +1,4 @@
-# This file is automatically @generated by Poetry 1.5.1 and should not be changed by hand.
+# This file is automatically @generated by Poetry 1.6.1 and should not be changed by hand.
[[package]]
name = "altgraph"
@@ -329,13 +329,13 @@ smmap = ">=3.0.1,<6"
[[package]]
name = "gitpython"
-version = "3.1.32"
+version = "3.1.35"
description = "GitPython is a Python library used to interact with Git repositories"
optional = false
python-versions = ">=3.7"
files = [
- {file = "GitPython-3.1.32-py3-none-any.whl", hash = "sha256:e3d59b1c2c6ebb9dfa7a184daf3b6dd4914237e7488a1730a6d8f6f5d0b4187f"},
- {file = "GitPython-3.1.32.tar.gz", hash = "sha256:8d9b8cb1e80b9735e8717c9362079d3ce4c6e5ddeebedd0361b228c3a67a62f6"},
+ {file = "GitPython-3.1.35-py3-none-any.whl", hash = "sha256:c19b4292d7a1d3c0f653858db273ff8a6614100d1eb1528b014ec97286193c09"},
+ {file = "GitPython-3.1.35.tar.gz", hash = "sha256:9cbefbd1789a5fe9bcf621bb34d3f441f3a90c8461d377f84eda73e721d9b06b"},
]
[package.dependencies]
From b9bbd66b04283552e77a7bcb6b2c504a224c7800 Mon Sep 17 00:00:00 2001
From: "dependabot[bot]" <49699333+dependabot[bot]@users.noreply.github.com>
Date: Tue, 3 Oct 2023 13:15:18 +0200
Subject: [PATCH 032/257] Bump urllib3 from 1.26.16 to 1.26.17 (#165)
Bumps [urllib3](https://github.com/urllib3/urllib3) from 1.26.16 to 1.26.17.
- [Release notes](https://github.com/urllib3/urllib3/releases)
- [Changelog](https://github.com/urllib3/urllib3/blob/main/CHANGES.rst)
- [Commits](https://github.com/urllib3/urllib3/compare/1.26.16...1.26.17)
---
updated-dependencies:
- dependency-name: urllib3
dependency-type: direct:production
...
Signed-off-by: dependabot[bot]
Co-authored-by: dependabot[bot] <49699333+dependabot[bot]@users.noreply.github.com>
---
poetry.lock | 10 +++++-----
pyproject.toml | 2 +-
2 files changed, 6 insertions(+), 6 deletions(-)
diff --git a/poetry.lock b/poetry.lock
index 5e473450..46104e63 100644
--- a/poetry.lock
+++ b/poetry.lock
@@ -872,17 +872,17 @@ files = [
[[package]]
name = "urllib3"
-version = "1.26.16"
+version = "1.26.17"
description = "HTTP library with thread-safe connection pooling, file post, and more."
optional = false
python-versions = ">=2.7, !=3.0.*, !=3.1.*, !=3.2.*, !=3.3.*, !=3.4.*, !=3.5.*"
files = [
- {file = "urllib3-1.26.16-py2.py3-none-any.whl", hash = "sha256:8d36afa7616d8ab714608411b4a3b13e58f463aee519024578e062e141dce20f"},
- {file = "urllib3-1.26.16.tar.gz", hash = "sha256:8f135f6502756bde6b2a9b28989df5fbe87c9970cecaa69041edcce7f0589b14"},
+ {file = "urllib3-1.26.17-py2.py3-none-any.whl", hash = "sha256:94a757d178c9be92ef5539b8840d48dc9cf1b2709c9d6b588232a055c524458b"},
+ {file = "urllib3-1.26.17.tar.gz", hash = "sha256:24d6a242c28d29af46c3fae832c36db3bbebcc533dd1bb549172cd739c82df21"},
]
[package.extras]
-brotli = ["brotli (>=1.0.9)", "brotlicffi (>=0.8.0)", "brotlipy (>=0.6.0)"]
+brotli = ["brotli (==1.0.9)", "brotli (>=1.0.9)", "brotlicffi (>=0.8.0)", "brotlipy (>=0.6.0)"]
secure = ["certifi", "cryptography (>=1.3.4)", "idna (>=2.0.0)", "ipaddress", "pyOpenSSL (>=0.14)", "urllib3-secure-extra"]
socks = ["PySocks (>=1.5.6,!=1.5.7,<2.0)"]
@@ -904,4 +904,4 @@ testing = ["big-O", "flake8 (<5)", "jaraco.functools", "jaraco.itertools", "more
[metadata]
lock-version = "2.0"
python-versions = ">=3.7,<3.12"
-content-hash = "ca732947ba4a2d16d4697a43b8c81c77cf2f9b73892ba7f8fa80c43703ec8b0b"
+content-hash = "c02a52cf933b218c70b12ec1b1cc0cd53ee8d43c3ad3a0ceb0a8fb23a5e0b0c9"
diff --git a/pyproject.toml b/pyproject.toml
index 93fa2516..e83d552e 100644
--- a/pyproject.toml
+++ b/pyproject.toml
@@ -37,7 +37,7 @@ arrow = ">=0.17.0,<0.18.0"
binaryornot = ">=0.4.4,<0.5.0"
texttable = ">=1.6.7,<1.7.0"
requests = ">=2.24,<3.0"
-urllib3 = "1.26.16" # lock v1 to avoid issues with openssl and old Python versions (<3.9.11) on macOS
+urllib3 = "1.26.17" # lock v1 to avoid issues with openssl and old Python versions (<3.9.11) on macOS
[tool.poetry.group.test.dependencies]
mock = ">=4.0.3,<4.1.0"
From efc42ced14c03d5dcd1e701047f1f09f236593fc Mon Sep 17 00:00:00 2001
From: Ilya Siamionau
Date: Fri, 6 Oct 2023 14:56:29 +0200
Subject: [PATCH 033/257] CM-24498 - Add SBOM reports (#164)
CM-26214, CM-26215, CM-26216, CM-27640, CM-26254 - Add SBOM reports
---
cycode/cli/code_scanner.py | 462 +++---------------
.../{helpers => commands/report}/__init__.py | 0
cycode/cli/commands/report/report_command.py | 23 +
.../report/sbom}/__init__.py | 0
cycode/cli/commands/report/sbom/common.py | 94 ++++
.../cli/commands/report/sbom/handle_errors.py | 47 ++
.../cli/commands/report/sbom/sbom_command.py | 84 ++++
.../commands/report/sbom/sbom_path_command.py | 65 +++
.../commands/report/sbom/sbom_report_file.py | 49 ++
.../sbom/sbom_repository_url_command.py | 55 +++
cycode/cli/config.yaml | 4 +
cycode/cli/consts.py | 9 +
cycode/cli/exceptions/custom_exceptions.py | 4 +
.../files_collector}/__init__.py | 0
cycode/cli/files_collector/excluder.py | 134 +++++
cycode/cli/files_collector/iac/__init__.py | 0
.../iac}/tf_content_generator.py | 23 +-
cycode/cli/files_collector/models/__init__.py | 0
.../models/in_memory_zip.py} | 14 +-
cycode/cli/files_collector/path_documents.py | 112 +++++
.../files_collector/repository_documents.py | 140 ++++++
cycode/cli/files_collector/sca/__init__.py | 0
.../cli/files_collector/sca/maven/__init__.py | 0
.../maven/base_restore_maven_dependencies.py | 0
.../sca}/maven/restore_gradle_dependencies.py | 2 +-
.../sca}/maven/restore_maven_dependencies.py | 2 +-
.../sca}/sca_code_scanner.py | 14 +-
cycode/cli/files_collector/zip_documents.py | 40 ++
cycode/cli/main.py | 32 +-
.../user_settings/configuration_manager.py | 7 +
cycode/cli/utils/get_api_client.py | 40 ++
cycode/cli/utils/path_utils.py | 40 +-
cycode/cli/utils/progress_bar.py | 113 +++--
cycode/cli/utils/scan_batch.py | 6 +-
cycode/cyclient/client_creator.py | 23 +
cycode/cyclient/models.py | 60 +++
cycode/cyclient/report_client.py | 101 ++++
cycode/cyclient/scan_client.py | 13 +-
.../scan_config/scan_config_creator.py | 29 --
.../{scan_config => }/scan_config_base.py | 0
.../cli/helpers/test_tf_content_generator.py | 2 +-
tests/cli/test_code_scanner.py | 4 +-
tests/conftest.py | 2 +-
.../scan_config/test_default_scan_config.py | 2 +-
.../scan_config/test_dev_scan_config.py | 2 +-
tests/cyclient/test_scan_client.py | 6 +-
tests/test_code_scanner.py | 4 +-
tests/test_zip_file.py | 6 +-
48 files changed, 1315 insertions(+), 554 deletions(-)
rename cycode/cli/{helpers => commands/report}/__init__.py (100%)
create mode 100644 cycode/cli/commands/report/report_command.py
rename cycode/cli/{helpers/maven => commands/report/sbom}/__init__.py (100%)
create mode 100644 cycode/cli/commands/report/sbom/common.py
create mode 100644 cycode/cli/commands/report/sbom/handle_errors.py
create mode 100644 cycode/cli/commands/report/sbom/sbom_command.py
create mode 100644 cycode/cli/commands/report/sbom/sbom_path_command.py
create mode 100644 cycode/cli/commands/report/sbom/sbom_report_file.py
create mode 100644 cycode/cli/commands/report/sbom/sbom_repository_url_command.py
rename cycode/{cyclient/scan_config => cli/files_collector}/__init__.py (100%)
create mode 100644 cycode/cli/files_collector/excluder.py
create mode 100644 cycode/cli/files_collector/iac/__init__.py
rename cycode/cli/{helpers => files_collector/iac}/tf_content_generator.py (73%)
create mode 100644 cycode/cli/files_collector/models/__init__.py
rename cycode/cli/{zip_file.py => files_collector/models/in_memory_zip.py} (74%)
create mode 100644 cycode/cli/files_collector/path_documents.py
create mode 100644 cycode/cli/files_collector/repository_documents.py
create mode 100644 cycode/cli/files_collector/sca/__init__.py
create mode 100644 cycode/cli/files_collector/sca/maven/__init__.py
rename cycode/cli/{helpers => files_collector/sca}/maven/base_restore_maven_dependencies.py (100%)
rename cycode/cli/{helpers => files_collector/sca}/maven/restore_gradle_dependencies.py (88%)
rename cycode/cli/{helpers => files_collector/sca}/maven/restore_maven_dependencies.py (97%)
rename cycode/cli/{helpers => files_collector/sca}/sca_code_scanner.py (88%)
create mode 100644 cycode/cli/files_collector/zip_documents.py
create mode 100644 cycode/cli/utils/get_api_client.py
create mode 100644 cycode/cyclient/client_creator.py
create mode 100644 cycode/cyclient/report_client.py
delete mode 100644 cycode/cyclient/scan_config/scan_config_creator.py
rename cycode/cyclient/{scan_config => }/scan_config_base.py (100%)
diff --git a/cycode/cli/code_scanner.py b/cycode/cli/code_scanner.py
index 128e8a6f..1801d63c 100644
--- a/cycode/cli/code_scanner.py
+++ b/cycode/cli/code_scanner.py
@@ -5,8 +5,7 @@
import time
import traceback
from platform import platform
-from sys import getsizeof
-from typing import TYPE_CHECKING, Callable, Dict, Iterator, List, Optional, Tuple, Union
+from typing import TYPE_CHECKING, Callable, Dict, List, Optional, Tuple
from uuid import UUID, uuid4
import click
@@ -15,39 +14,37 @@
from cycode.cli import consts
from cycode.cli.ci_integrations import get_commit_range
from cycode.cli.config import configuration_manager
-from cycode.cli.consts import SCA_SKIP_RESTORE_DEPENDENCIES_FLAG
from cycode.cli.exceptions import custom_exceptions
-from cycode.cli.helpers import sca_code_scanner, tf_content_generator
+from cycode.cli.files_collector.excluder import exclude_irrelevant_documents_to_scan
+from cycode.cli.files_collector.models.in_memory_zip import InMemoryZip
+from cycode.cli.files_collector.path_documents import get_relevant_document
+from cycode.cli.files_collector.repository_documents import (
+ calculate_pre_receive_commit_range,
+ get_commit_range_modified_documents,
+ get_diff_file_content,
+ get_diff_file_path,
+ get_git_repository_tree_file_entries,
+ get_pre_commit_modified_documents,
+ parse_commit_range,
+)
+from cycode.cli.files_collector.sca import sca_code_scanner
+from cycode.cli.files_collector.sca.sca_code_scanner import perform_pre_scan_documents_actions
+from cycode.cli.files_collector.zip_documents import zip_documents
from cycode.cli.models import CliError, CliErrors, Document, DocumentDetections, LocalScanResult, Severity
from cycode.cli.printers import ConsolePrinter
-from cycode.cli.user_settings.config_file_manager import ConfigFileManager
from cycode.cli.utils import scan_utils
from cycode.cli.utils.path_utils import (
- change_filename_extension,
- get_file_content,
- get_file_size,
get_path_by_os,
- get_relevant_files_in_path,
- is_binary_file,
- is_sub_path,
- load_json,
)
-from cycode.cli.utils.progress_bar import ProgressBarSection
+from cycode.cli.utils.progress_bar import ScanProgressBarSection
from cycode.cli.utils.scan_batch import run_parallel_batched_scan
from cycode.cli.utils.scan_utils import set_issue_detected
-from cycode.cli.utils.string_utils import get_content_size, is_binary_content
from cycode.cli.utils.task_timer import TimeoutAfter
-from cycode.cli.zip_file import InMemoryZip
from cycode.cyclient import logger
from cycode.cyclient.config import set_logging_level
from cycode.cyclient.models import Detection, DetectionSchema, DetectionsPerFile, ZippedFileScanResult
if TYPE_CHECKING:
- from git import Blob, Diff
- from git.objects.base import IndexObjUnion
- from git.objects.tree import TraversedTreeTup
-
- from cycode.cli.utils.progress_bar import BaseProgressBar
from cycode.cyclient.models import ScanDetailsResponse
from cycode.cyclient.scan_client import ScanClient
@@ -78,17 +75,17 @@ def scan_repository(context: click.Context, path: str, branch: str) -> None:
progress_bar.start()
file_entries = list(get_git_repository_tree_file_entries(path, branch))
- progress_bar.set_section_length(ProgressBarSection.PREPARE_LOCAL_FILES, len(file_entries))
+ progress_bar.set_section_length(ScanProgressBarSection.PREPARE_LOCAL_FILES, len(file_entries))
documents_to_scan = []
for file in file_entries:
# FIXME(MarshalX): probably file could be tree or submodule too. we expect blob only
- progress_bar.update(ProgressBarSection.PREPARE_LOCAL_FILES)
+ progress_bar.update(ScanProgressBarSection.PREPARE_LOCAL_FILES)
file_path = file.path if monitor else get_path_by_os(os.path.join(path, file.path))
documents_to_scan.append(Document(file_path, file.data_stream.read().decode('UTF-8', errors='replace')))
- documents_to_scan = exclude_irrelevant_documents_to_scan(context, documents_to_scan)
+ documents_to_scan = exclude_irrelevant_documents_to_scan(scan_type, documents_to_scan)
perform_pre_scan_documents_actions(context, scan_type, documents_to_scan, is_git_diff=False)
@@ -140,16 +137,16 @@ def scan_commit_range(
total_commits_count = int(repo.git.rev_list('--count', commit_range))
logger.debug(f'Calculating diffs for {total_commits_count} commits in the commit range {commit_range}')
- progress_bar.set_section_length(ProgressBarSection.PREPARE_LOCAL_FILES, total_commits_count)
+ progress_bar.set_section_length(ScanProgressBarSection.PREPARE_LOCAL_FILES, total_commits_count)
scanned_commits_count = 0
for commit in repo.iter_commits(rev=commit_range):
if _does_reach_to_max_commits_to_scan_limit(commit_ids_to_scan, max_commits_count):
logger.debug(f'Reached to max commits to scan count. Going to scan only {max_commits_count} last commits')
- progress_bar.update(ProgressBarSection.PREPARE_LOCAL_FILES, total_commits_count - scanned_commits_count)
+ progress_bar.update(ScanProgressBarSection.PREPARE_LOCAL_FILES, total_commits_count - scanned_commits_count)
break
- progress_bar.update(ProgressBarSection.PREPARE_LOCAL_FILES)
+ progress_bar.update(ScanProgressBarSection.PREPARE_LOCAL_FILES)
commit_id = commit.hexsha
commit_ids_to_scan.append(commit_id)
@@ -172,7 +169,7 @@ def scan_commit_range(
{'path': path, 'commit_range': commit_range, 'commit_id': commit_id},
)
- documents_to_scan.extend(exclude_irrelevant_documents_to_scan(context, commit_documents_to_scan))
+ documents_to_scan.extend(exclude_irrelevant_documents_to_scan(scan_type, commit_documents_to_scan))
scanned_commits_count += 1
logger.debug('List of commit ids to scan, %s', {'commit_ids': commit_ids_to_scan})
@@ -199,30 +196,7 @@ def scan_path(context: click.Context, path: str) -> None:
progress_bar.start()
logger.debug('Starting path scan process, %s', {'path': path})
-
- all_files_to_scan = get_relevant_files_in_path(path=path, exclude_patterns=['**/.git/**', '**/.cycode/**'])
-
- # we are double the progress bar section length because we are going to process the files twice
- # first time to get the file list with respect of excluded patterns (excluding takes seconds to execute)
- # second time to get the files content
- progress_bar_section_len = len(all_files_to_scan) * 2
- progress_bar.set_section_length(ProgressBarSection.PREPARE_LOCAL_FILES, progress_bar_section_len)
-
- relevant_files_to_scan = exclude_irrelevant_files(context, all_files_to_scan)
-
- # after finishing the first processing (excluding),
- # we must update the progress bar stage with respect of excluded files.
- # now it's possible that we will not process x2 of the files count
- # because some of them were excluded, we should subtract the excluded files count
- # from the progress bar section length
- excluded_files_count = len(all_files_to_scan) - len(relevant_files_to_scan)
- progress_bar_section_len = progress_bar_section_len - excluded_files_count
- progress_bar.set_section_length(ProgressBarSection.PREPARE_LOCAL_FILES, progress_bar_section_len)
-
- logger.debug(
- 'Found all relevant files for scanning %s', {'path': path, 'file_to_scan_count': len(relevant_files_to_scan)}
- )
- scan_disk_files(context, path, relevant_files_to_scan)
+ scan_disk_files(context, path)
@click.command(short_help='Use this command to scan any content that was not committed yet.')
@@ -240,14 +214,14 @@ def pre_commit_scan(context: click.Context, ignored_args: List[str]) -> None:
diff_files = Repo(os.getcwd()).index.diff('HEAD', create_patch=True, R=True)
- progress_bar.set_section_length(ProgressBarSection.PREPARE_LOCAL_FILES, len(diff_files))
+ progress_bar.set_section_length(ScanProgressBarSection.PREPARE_LOCAL_FILES, len(diff_files))
documents_to_scan = []
for file in diff_files:
- progress_bar.update(ProgressBarSection.PREPARE_LOCAL_FILES)
+ progress_bar.update(ScanProgressBarSection.PREPARE_LOCAL_FILES)
documents_to_scan.append(Document(get_path_by_os(get_diff_file_path(file)), get_diff_file_content(file)))
- documents_to_scan = exclude_irrelevant_documents_to_scan(context, documents_to_scan)
+ documents_to_scan = exclude_irrelevant_documents_to_scan(scan_type, documents_to_scan)
scan_documents(context, documents_to_scan, is_git_diff=True)
@@ -293,10 +267,13 @@ def pre_receive_scan(context: click.Context, ignored_args: List[str]) -> None:
def scan_sca_pre_commit(context: click.Context) -> None:
+ scan_type = context.obj['scan_type']
scan_parameters = get_default_scan_parameters(context)
- git_head_documents, pre_committed_documents = get_pre_commit_modified_documents(context.obj['progress_bar'])
- git_head_documents = exclude_irrelevant_documents_to_scan(context, git_head_documents)
- pre_committed_documents = exclude_irrelevant_documents_to_scan(context, pre_committed_documents)
+ git_head_documents, pre_committed_documents = get_pre_commit_modified_documents(
+ context.obj['progress_bar'], ScanProgressBarSection.PREPARE_LOCAL_FILES
+ )
+ git_head_documents = exclude_irrelevant_documents_to_scan(scan_type, git_head_documents)
+ pre_committed_documents = exclude_irrelevant_documents_to_scan(scan_type, pre_committed_documents)
sca_code_scanner.perform_pre_hook_range_scan_actions(git_head_documents, pre_committed_documents)
scan_commit_range_documents(
context,
@@ -308,15 +285,16 @@ def scan_sca_pre_commit(context: click.Context) -> None:
def scan_sca_commit_range(context: click.Context, path: str, commit_range: str) -> None:
+ scan_type = context.obj['scan_type']
progress_bar = context.obj['progress_bar']
scan_parameters = get_scan_parameters(context, path)
from_commit_rev, to_commit_rev = parse_commit_range(commit_range, path)
from_commit_documents, to_commit_documents = get_commit_range_modified_documents(
- progress_bar, path, from_commit_rev, to_commit_rev
+ progress_bar, ScanProgressBarSection.PREPARE_LOCAL_FILES, path, from_commit_rev, to_commit_rev
)
- from_commit_documents = exclude_irrelevant_documents_to_scan(context, from_commit_documents)
- to_commit_documents = exclude_irrelevant_documents_to_scan(context, to_commit_documents)
+ from_commit_documents = exclude_irrelevant_documents_to_scan(scan_type, from_commit_documents)
+ to_commit_documents = exclude_irrelevant_documents_to_scan(scan_type, to_commit_documents)
sca_code_scanner.perform_pre_commit_range_scan_actions(
path, from_commit_documents, from_commit_rev, to_commit_documents, to_commit_rev
)
@@ -324,27 +302,15 @@ def scan_sca_commit_range(context: click.Context, path: str, commit_range: str)
scan_commit_range_documents(context, from_commit_documents, to_commit_documents, scan_parameters=scan_parameters)
-def scan_disk_files(context: click.Context, path: str, files_to_scan: List[str]) -> None:
+def scan_disk_files(context: click.Context, path: str) -> None:
scan_parameters = get_scan_parameters(context, path)
scan_type = context.obj['scan_type']
progress_bar = context.obj['progress_bar']
- is_git_diff = False
-
try:
- documents: List[Document] = []
- for file in files_to_scan:
- progress_bar.update(ProgressBarSection.PREPARE_LOCAL_FILES)
-
- content = get_file_content(file)
- if not content:
- continue
-
- documents.append(_generate_document(file, scan_type, content, is_git_diff))
-
- perform_pre_scan_documents_actions(context, scan_type, documents, is_git_diff)
- scan_documents(context, documents, is_git_diff=is_git_diff, scan_parameters=scan_parameters)
-
+ documents = get_relevant_document(progress_bar, ScanProgressBarSection.PREPARE_LOCAL_FILES, scan_type, path)
+ perform_pre_scan_documents_actions(context, scan_type, documents)
+ scan_documents(context, documents, scan_parameters=scan_parameters)
except Exception as e:
_handle_exception(context, e)
@@ -370,8 +336,8 @@ def _scan_batch_thread_func(batch: List[Document]) -> Tuple[str, CliError, Local
try:
logger.debug('Preparing local files, %s', {'batch_size': len(batch)})
- zipped_documents = zip_documents_to_scan(scan_type, InMemoryZip(), batch)
- zip_file_size = getsizeof(zipped_documents.in_memory_zip)
+ zipped_documents = zip_documents(scan_type, batch)
+ zip_file_size = zipped_documents.size
scan_result = perform_scan(
cycode_client, zipped_documents, scan_type, scan_id, is_git_diff, is_commit_range, scan_parameters
@@ -442,8 +408,8 @@ def scan_documents(
scan_batch_thread_func, documents_to_scan, progress_bar=progress_bar
)
- progress_bar.set_section_length(ProgressBarSection.GENERATE_REPORT, 1)
- progress_bar.update(ProgressBarSection.GENERATE_REPORT)
+ progress_bar.set_section_length(ScanProgressBarSection.GENERATE_REPORT, 1)
+ progress_bar.update(ScanProgressBarSection.GENERATE_REPORT)
progress_bar.stop()
set_issue_detected_by_scan_results(context, local_scan_results)
@@ -471,19 +437,15 @@ def scan_commit_range_documents(
to_commit_zipped_documents = InMemoryZip()
try:
- progress_bar.set_section_length(ProgressBarSection.SCAN, 1)
+ progress_bar.set_section_length(ScanProgressBarSection.SCAN, 1)
scan_result = init_default_scan_result(scan_id)
if should_scan_documents(from_documents_to_scan, to_documents_to_scan):
logger.debug('Preparing from-commit zip')
- from_commit_zipped_documents = zip_documents_to_scan(
- scan_type, from_commit_zipped_documents, from_documents_to_scan
- )
+ from_commit_zipped_documents = zip_documents(scan_type, from_documents_to_scan)
logger.debug('Preparing to-commit zip')
- to_commit_zipped_documents = zip_documents_to_scan(
- scan_type, to_commit_zipped_documents, to_documents_to_scan
- )
+ to_commit_zipped_documents = zip_documents(scan_type, to_documents_to_scan)
scan_result = perform_commit_range_scan_async(
cycode_client,
@@ -494,15 +456,15 @@ def scan_commit_range_documents(
timeout,
)
- progress_bar.update(ProgressBarSection.SCAN)
- progress_bar.set_section_length(ProgressBarSection.GENERATE_REPORT, 1)
+ progress_bar.update(ScanProgressBarSection.SCAN)
+ progress_bar.set_section_length(ScanProgressBarSection.GENERATE_REPORT, 1)
local_scan_result = create_local_scan_result(
scan_result, to_documents_to_scan, scan_command_type, scan_type, severity_threshold
)
set_issue_detected_by_scan_results(context, [local_scan_result])
- progress_bar.update(ProgressBarSection.GENERATE_REPORT)
+ progress_bar.update(ScanProgressBarSection.GENERATE_REPORT)
progress_bar.stop()
# errors will be handled with try-except block; printing will not occur on errors
@@ -513,9 +475,7 @@ def scan_commit_range_documents(
_handle_exception(context, e)
error_message = str(e)
- zip_file_size = getsizeof(from_commit_zipped_documents.in_memory_zip) + getsizeof(
- to_commit_zipped_documents.in_memory_zip
- )
+ zip_file_size = from_commit_zipped_documents.size + to_commit_zipped_documents.size
detections_count = relevant_detections_count = 0
if local_scan_result:
@@ -577,45 +537,9 @@ def create_local_scan_result(
)
-def perform_pre_scan_documents_actions(
- context: click.Context, scan_type: str, documents_to_scan: List[Document], is_git_diff: bool = False
-) -> None:
- if scan_type == consts.SCA_SCAN_TYPE and not context.obj.get(SCA_SKIP_RESTORE_DEPENDENCIES_FLAG):
- logger.debug('Perform pre scan document add_dependencies_tree_document action')
- sca_code_scanner.add_dependencies_tree_document(context, documents_to_scan, is_git_diff)
-
-
-def zip_documents_to_scan(scan_type: str, zip_file: InMemoryZip, documents: List[Document]) -> InMemoryZip:
- start_zip_creation_time = time.time()
-
- for index, document in enumerate(documents):
- zip_file_size = getsizeof(zip_file.in_memory_zip)
- validate_zip_file_size(scan_type, zip_file_size)
-
- logger.debug(
- 'adding file to zip, %s', {'index': index, 'filename': document.path, 'unique_id': document.unique_id}
- )
- zip_file.append(document.path, document.unique_id, document.content)
- zip_file.close()
-
- end_zip_creation_time = time.time()
- zip_creation_time = int(end_zip_creation_time - start_zip_creation_time)
- logger.debug('finished to create zip file, %s', {'zip_creation_time': zip_creation_time})
- return zip_file
-
-
-def validate_zip_file_size(scan_type: str, zip_file_size: int) -> None:
- if scan_type == consts.SCA_SCAN_TYPE:
- if zip_file_size > consts.SCA_ZIP_MAX_SIZE_LIMIT_IN_BYTES:
- raise custom_exceptions.ZipTooLargeError(consts.SCA_ZIP_MAX_SIZE_LIMIT_IN_BYTES)
- else:
- if zip_file_size > consts.ZIP_MAX_SIZE_LIMIT_IN_BYTES:
- raise custom_exceptions.ZipTooLargeError(consts.ZIP_MAX_SIZE_LIMIT_IN_BYTES)
-
-
def perform_scan(
cycode_client: 'ScanClient',
- zipped_documents: InMemoryZip,
+ zipped_documents: 'InMemoryZip',
scan_type: str,
scan_id: str,
is_git_diff: bool,
@@ -632,7 +556,7 @@ def perform_scan(
def perform_scan_async(
- cycode_client: 'ScanClient', zipped_documents: InMemoryZip, scan_type: str, scan_parameters: dict
+ cycode_client: 'ScanClient', zipped_documents: 'InMemoryZip', scan_type: str, scan_parameters: dict
) -> ZippedFileScanResult:
scan_async_result = cycode_client.zipped_file_scan_async(zipped_documents, scan_type, scan_parameters)
logger.debug('scan request has been triggered successfully, scan id: %s', scan_async_result.scan_id)
@@ -642,8 +566,8 @@ def perform_scan_async(
def perform_commit_range_scan_async(
cycode_client: 'ScanClient',
- from_commit_zipped_documents: InMemoryZip,
- to_commit_zipped_documents: InMemoryZip,
+ from_commit_zipped_documents: 'InMemoryZip',
+ to_commit_zipped_documents: 'InMemoryZip',
scan_type: str,
scan_parameters: dict,
timeout: Optional[int] = None,
@@ -759,56 +683,6 @@ def parse_pre_receive_input() -> str:
return pre_receive_input.splitlines()[0]
-def calculate_pre_receive_commit_range(branch_update_details: str) -> Optional[str]:
- end_commit = get_end_commit_from_branch_update_details(branch_update_details)
-
- # branch is deleted, no need to perform scan
- if end_commit == consts.EMPTY_COMMIT_SHA:
- return None
-
- start_commit = get_oldest_unupdated_commit_for_branch(end_commit)
-
- # no new commit to update found
- if not start_commit:
- return None
-
- return f'{start_commit}~1...{end_commit}'
-
-
-def get_end_commit_from_branch_update_details(update_details: str) -> str:
- # update details pattern: [
- _, end_commit, _ = update_details.split()
- return end_commit
-
-
-def get_oldest_unupdated_commit_for_branch(commit: str) -> Optional[str]:
- # get a list of commits by chronological order that are not in the remote repository yet
- # more info about rev-list command: https://git-scm.com/docs/git-rev-list
- not_updated_commits = Repo(os.getcwd()).git.rev_list(commit, '--topo-order', '--reverse', '--not', '--all')
- commits = not_updated_commits.splitlines()
- if not commits:
- return None
- return commits[0]
-
-
-def get_diff_file_path(file: 'Diff') -> Optional[str]:
- return file.b_path if file.b_path else file.a_path
-
-
-def get_diff_file_content(file: 'Diff') -> str:
- return file.diff.decode('UTF-8', errors='replace')
-
-
-def should_process_git_object(obj: 'Blob', _: int) -> bool:
- return obj.type == 'blob' and obj.size > 0
-
-
-def get_git_repository_tree_file_entries(
- path: str, branch: str
-) -> Union[Iterator['IndexObjUnion'], Iterator['TraversedTreeTup']]:
- return Repo(path).tree(branch).traverse(predicate=should_process_git_object)
-
-
def get_default_scan_parameters(context: click.Context) -> dict:
return {
'monitor': context.obj.get('monitor'),
@@ -839,34 +713,6 @@ def try_get_git_remote_url(path: str) -> Optional[dict]:
return None
-def exclude_irrelevant_documents_to_scan(context: click.Context, documents_to_scan: List[Document]) -> List[Document]:
- logger.debug('Excluding irrelevant documents to scan')
-
- scan_type = context.obj['scan_type']
-
- relevant_documents = []
- for document in documents_to_scan:
- if _is_relevant_document_to_scan(scan_type, document.path, document.content):
- relevant_documents.append(document)
-
- return relevant_documents
-
-
-def exclude_irrelevant_files(context: click.Context, filenames: List[str]) -> List[str]:
- scan_type = context.obj['scan_type']
- progress_bar = context.obj['progress_bar']
-
- relevant_files = []
- for filename in filenames:
- progress_bar.update(ProgressBarSection.PREPARE_LOCAL_FILES)
- if _is_relevant_file_to_scan(scan_type, filename):
- relevant_files.append(filename)
-
- is_sub_path.cache_clear() # free up memory
-
- return relevant_files
-
-
def exclude_irrelevant_detections(
detections: List[Detection], scan_type: str, command_scan_type: str, severity_threshold: str
) -> List[Detection]:
@@ -916,60 +762,6 @@ def _exclude_detections_by_exclusions_configuration(detections: List[Detection],
return [detection for detection in detections if not _should_exclude_detection(detection, exclusions)]
-def get_pre_commit_modified_documents(progress_bar: 'BaseProgressBar') -> Tuple[List[Document], List[Document]]:
- git_head_documents = []
- pre_committed_documents = []
-
- repo = Repo(os.getcwd())
- diff_files = repo.index.diff(consts.GIT_HEAD_COMMIT_REV, create_patch=True, R=True)
- progress_bar.set_section_length(ProgressBarSection.PREPARE_LOCAL_FILES, len(diff_files))
- for file in diff_files:
- progress_bar.update(ProgressBarSection.PREPARE_LOCAL_FILES)
-
- diff_file_path = get_diff_file_path(file)
- file_path = get_path_by_os(diff_file_path)
-
- file_content = sca_code_scanner.get_file_content_from_commit(repo, consts.GIT_HEAD_COMMIT_REV, diff_file_path)
- if file_content is not None:
- git_head_documents.append(Document(file_path, file_content))
-
- if os.path.exists(file_path):
- file_content = get_file_content(file_path)
- pre_committed_documents.append(Document(file_path, file_content))
-
- return git_head_documents, pre_committed_documents
-
-
-def get_commit_range_modified_documents(
- progress_bar: 'BaseProgressBar', path: str, from_commit_rev: str, to_commit_rev: str
-) -> Tuple[List[Document], List[Document]]:
- from_commit_documents = []
- to_commit_documents = []
-
- repo = Repo(path)
- diff = repo.commit(from_commit_rev).diff(to_commit_rev)
-
- modified_files_diff = [
- change for change in diff if change.change_type != consts.COMMIT_DIFF_DELETED_FILE_CHANGE_TYPE
- ]
- progress_bar.set_section_length(ProgressBarSection.PREPARE_LOCAL_FILES, len(modified_files_diff))
- for blob in modified_files_diff:
- progress_bar.update(ProgressBarSection.PREPARE_LOCAL_FILES)
-
- diff_file_path = get_diff_file_path(blob)
- file_path = get_path_by_os(diff_file_path)
-
- file_content = sca_code_scanner.get_file_content_from_commit(repo, from_commit_rev, diff_file_path)
- if file_content is not None:
- from_commit_documents.append(Document(file_path, file_content))
-
- file_content = sca_code_scanner.get_file_content_from_commit(repo, to_commit_rev, diff_file_path)
- if file_content is not None:
- to_commit_documents.append(Document(file_path, file_content))
-
- return from_commit_documents, to_commit_documents
-
-
def _should_exclude_detection(detection: Detection, exclusions: Dict) -> bool:
exclusions_by_value = exclusions.get(consts.EXCLUSIONS_BY_VALUE_SECTION_NAME, [])
if _is_detection_sha_configured_in_exclusions(detection, exclusions_by_value):
@@ -1014,13 +806,6 @@ def _is_detection_sha_configured_in_exclusions(detection: Detection, exclusions:
return detection_sha in exclusions
-def _is_path_configured_in_exclusions(scan_type: str, file_path: str) -> bool:
- exclusions_by_path = configuration_manager.get_exclusions_by_scan_type(scan_type).get(
- consts.EXCLUSIONS_BY_PATH_SECTION_NAME, []
- )
- return any(is_sub_path(exclusion_path, file_path) for exclusion_path in exclusions_by_path)
-
-
def _get_package_name(detection: Detection) -> str:
package_name = detection.detection_details.get('vulnerable_component', '')
package_version = detection.detection_details.get('vulnerable_component_version', '')
@@ -1032,119 +817,6 @@ def _get_package_name(detection: Detection) -> str:
return f'{package_name}@{package_version}'
-def _is_file_relevant_for_sca_scan(filename: str) -> bool:
- if any(sca_excluded_path in filename for sca_excluded_path in consts.SCA_EXCLUDED_PATHS):
- logger.debug("file is irrelevant because it is from node_modules's inner path, %s", {'filename': filename})
- return False
-
- return True
-
-
-def _is_relevant_file_to_scan(scan_type: str, filename: str) -> bool:
- if _is_subpath_of_cycode_configuration_folder(filename):
- logger.debug('file is irrelevant because it is in cycode configuration directory, %s', {'filename': filename})
- return False
-
- if _is_path_configured_in_exclusions(scan_type, filename):
- logger.debug('file is irrelevant because the file path is in the ignore paths list, %s', {'filename': filename})
- return False
-
- if not _is_file_extension_supported(scan_type, filename):
- logger.debug('file is irrelevant because the file extension is not supported, %s', {'filename': filename})
- return False
-
- if is_binary_file(filename):
- logger.debug('file is irrelevant because it is binary file, %s', {'filename': filename})
- return False
-
- if scan_type != consts.SCA_SCAN_TYPE and _does_file_exceed_max_size_limit(filename):
- logger.debug('file is irrelevant because its exceeded max size limit, %s', {'filename': filename})
- return False
-
- if scan_type == consts.SCA_SCAN_TYPE and not _is_file_relevant_for_sca_scan(filename):
- return False
-
- return True
-
-
-def _is_relevant_document_to_scan(scan_type: str, filename: str, content: str) -> bool:
- if _is_subpath_of_cycode_configuration_folder(filename):
- logger.debug(
- 'document is irrelevant because it is in cycode configuration directory, %s', {'filename': filename}
- )
- return False
-
- if _is_path_configured_in_exclusions(scan_type, filename):
- logger.debug(
- 'document is irrelevant because the document path is in the ignore paths list, %s', {'filename': filename}
- )
- return False
-
- if not _is_file_extension_supported(scan_type, filename):
- logger.debug('document is irrelevant because the file extension is not supported, %s', {'filename': filename})
- return False
-
- if is_binary_content(content):
- logger.debug('document is irrelevant because it is binary, %s', {'filename': filename})
- return False
-
- if scan_type != consts.SCA_SCAN_TYPE and _does_document_exceed_max_size_limit(content):
- logger.debug('document is irrelevant because its exceeded max size limit, %s', {'filename': filename})
- return False
- return True
-
-
-def _is_file_extension_supported(scan_type: str, filename: str) -> bool:
- filename = filename.lower()
-
- if scan_type == consts.INFRA_CONFIGURATION_SCAN_TYPE:
- return filename.endswith(consts.INFRA_CONFIGURATION_SCAN_SUPPORTED_FILES)
-
- if scan_type == consts.SCA_SCAN_TYPE:
- return filename.endswith(consts.SCA_CONFIGURATION_SCAN_SUPPORTED_FILES)
-
- return not filename.endswith(consts.SECRET_SCAN_FILE_EXTENSIONS_TO_IGNORE)
-
-
-def _generate_document(file: str, scan_type: str, content: str, is_git_diff: bool) -> Document:
- if _is_iac(scan_type) and _is_tfplan_file(file, content):
- return _handle_tfplan_file(file, content, is_git_diff)
- return Document(file, content, is_git_diff)
-
-
-def _handle_tfplan_file(file: str, content: str, is_git_diff: bool) -> Document:
- document_name = _generate_tfplan_document_name(file)
- tf_content = tf_content_generator.generate_tf_content_from_tfplan(file, content)
- return Document(document_name, tf_content, is_git_diff)
-
-
-def _generate_tfplan_document_name(path: str) -> str:
- document_name = change_filename_extension(path, 'tf')
- timestamp = int(time.time())
- return f'{timestamp}-{document_name}'
-
-
-def _is_iac(scan_type: str) -> bool:
- return scan_type == consts.INFRA_CONFIGURATION_SCAN_TYPE
-
-
-def _is_tfplan_file(file: str, content: str) -> bool:
- if not file.endswith('.json'):
- return False
- tf_plan = load_json(content)
- if not isinstance(tf_plan, dict):
- return False
- return 'resource_changes' in tf_plan
-
-
-def _does_file_exceed_max_size_limit(filename: str) -> bool:
- return get_file_size(filename) > consts.FILE_MAX_SIZE_LIMIT_IN_BYTES
-
-
-def _does_document_exceed_max_size_limit(content: str) -> bool:
- return get_content_size(content) > consts.FILE_MAX_SIZE_LIMIT_IN_BYTES
-
-
def _get_document_by_file_name(
documents: List[Document], file_name: str, unique_id: Optional[str] = None
) -> Optional[Document]:
@@ -1155,14 +827,6 @@ def _get_document_by_file_name(
return None
-def _is_subpath_of_cycode_configuration_folder(filename: str) -> bool:
- return (
- is_sub_path(configuration_manager.global_config_file_manager.get_config_directory_path(), filename)
- or is_sub_path(configuration_manager.local_config_file_manager.get_config_directory_path(), filename)
- or filename.endswith(ConfigFileManager.get_config_file_route())
- )
-
-
def _handle_exception(context: click.Context, e: Exception, *, return_exception: bool = False) -> Optional[CliError]:
context.obj['did_fail'] = True
@@ -1372,18 +1036,6 @@ def _does_reach_to_max_commits_to_scan_limit(commit_ids: List[str], max_commits_
return len(commit_ids) >= max_commits_count
-def parse_commit_range(commit_range: str, path: str) -> Tuple[str, str]:
- from_commit_rev = None
- to_commit_rev = None
-
- for commit in Repo(path).iter_commits(rev=commit_range):
- if not to_commit_rev:
- to_commit_rev = commit.hexsha
- from_commit_rev = commit.hexsha
-
- return from_commit_rev, to_commit_rev
-
-
def _normalize_file_path(path: str) -> str:
if path.startswith('/'):
return path[1:]
diff --git a/cycode/cli/helpers/__init__.py b/cycode/cli/commands/report/__init__.py
similarity index 100%
rename from cycode/cli/helpers/__init__.py
rename to cycode/cli/commands/report/__init__.py
diff --git a/cycode/cli/commands/report/report_command.py b/cycode/cli/commands/report/report_command.py
new file mode 100644
index 00000000..4722a6b2
--- /dev/null
+++ b/cycode/cli/commands/report/report_command.py
@@ -0,0 +1,23 @@
+import click
+
+from cycode.cli.commands.report.sbom.sbom_command import sbom_command
+from cycode.cli.utils.get_api_client import get_report_cycode_client
+from cycode.cli.utils.progress_bar import SBOM_REPORT_PROGRESS_BAR_SECTIONS, get_progress_bar
+
+
+@click.group(
+ commands={
+ 'sbom': sbom_command,
+ },
+ short_help='Generate report. You`ll need to specify which report type to perform.',
+)
+@click.pass_context
+def report_command(
+ context: click.Context,
+) -> int:
+ """Generate report."""
+
+ context.obj['client'] = get_report_cycode_client(hide_response_log=False) # TODO disable log
+ context.obj['progress_bar'] = get_progress_bar(hidden=False, sections=SBOM_REPORT_PROGRESS_BAR_SECTIONS)
+
+ return 1
diff --git a/cycode/cli/helpers/maven/__init__.py b/cycode/cli/commands/report/sbom/__init__.py
similarity index 100%
rename from cycode/cli/helpers/maven/__init__.py
rename to cycode/cli/commands/report/sbom/__init__.py
diff --git a/cycode/cli/commands/report/sbom/common.py b/cycode/cli/commands/report/sbom/common.py
new file mode 100644
index 00000000..334e7275
--- /dev/null
+++ b/cycode/cli/commands/report/sbom/common.py
@@ -0,0 +1,94 @@
+import pathlib
+import time
+from platform import platform
+from typing import TYPE_CHECKING, Optional
+
+from cycode.cli import consts
+from cycode.cli.commands.report.sbom.sbom_report_file import SbomReportFile
+from cycode.cli.config import configuration_manager
+from cycode.cli.exceptions.custom_exceptions import ReportAsyncError
+from cycode.cli.utils.progress_bar import SbomReportProgressBarSection
+from cycode.cyclient import logger
+from cycode.cyclient.models import ReportExecutionSchema
+
+if TYPE_CHECKING:
+ from cycode.cli.utils.progress_bar import BaseProgressBar
+ from cycode.cyclient.report_client import ReportClient
+
+
+def _poll_report_execution_until_completed(
+ progress_bar: 'BaseProgressBar',
+ client: 'ReportClient',
+ report_execution_id: int,
+ polling_timeout: Optional[int] = None,
+) -> ReportExecutionSchema:
+ if polling_timeout is None:
+ polling_timeout = configuration_manager.get_report_polling_timeout_in_seconds()
+
+ end_polling_time = time.time() + polling_timeout
+ while time.time() < end_polling_time:
+ report_execution = client.get_report_execution(report_execution_id)
+ report_label = report_execution.error_message or report_execution.status_message
+
+ progress_bar.update_label(report_label)
+
+ if report_execution.status == consts.REPORT_STATUS_COMPLETED:
+ return report_execution
+
+ if report_execution.status == consts.REPORT_STATUS_ERROR:
+ raise ReportAsyncError(f'Error occurred while trying to generate report: {report_label}')
+
+ time.sleep(consts.REPORT_POLLING_WAIT_INTERVAL_IN_SECONDS)
+
+ raise ReportAsyncError(f'Timeout exceeded while waiting for report to complete. Timeout: {polling_timeout} sec.')
+
+
+def send_report_feedback(
+ client: 'ReportClient',
+ start_scan_time: float,
+ report_type: str,
+ report_command_type: str,
+ request_report_parameters: dict,
+ report_execution_id: int,
+ error_message: Optional[str] = None,
+ request_zip_file_size: Optional[int] = None,
+ **kwargs,
+) -> None:
+ try:
+ request_report_parameters.update(kwargs)
+
+ end_scan_time = time.time()
+ scan_status = {
+ 'report_type': report_type,
+ 'report_command_type': report_command_type,
+ 'request_report_parameters': request_report_parameters,
+ 'operation_system': platform(),
+ 'error_message': error_message,
+ 'execution_time': int(end_scan_time - start_scan_time),
+ 'request_zip_file_size': request_zip_file_size,
+ }
+
+ client.report_status(report_execution_id, scan_status)
+ except Exception as e:
+ logger.debug(f'Failed to send report feedback: {e}')
+
+
+def create_sbom_report(
+ progress_bar: 'BaseProgressBar',
+ client: 'ReportClient',
+ report_execution_id: int,
+ output_file: Optional[pathlib.Path],
+ output_format: str,
+) -> None:
+ report_execution = _poll_report_execution_until_completed(progress_bar, client, report_execution_id)
+
+ progress_bar.set_section_length(SbomReportProgressBarSection.GENERATION)
+
+ report_path = report_execution.storage_details.path
+ report_content = client.get_file_content(report_path)
+
+ progress_bar.set_section_length(SbomReportProgressBarSection.RECEIVE_REPORT)
+ progress_bar.stop()
+
+ sbom_report = SbomReportFile(report_path, output_format, output_file)
+ sbom_report.write(report_content)
diff --git a/cycode/cli/commands/report/sbom/handle_errors.py b/cycode/cli/commands/report/sbom/handle_errors.py
new file mode 100644
index 00000000..b9ca9084
--- /dev/null
+++ b/cycode/cli/commands/report/sbom/handle_errors.py
@@ -0,0 +1,47 @@
+import traceback
+from typing import Optional
+
+import click
+
+from cycode.cli.exceptions import custom_exceptions
+from cycode.cli.models import CliError, CliErrors
+from cycode.cli.printers import ConsolePrinter
+
+
+def handle_report_exception(context: click.Context, err: Exception) -> Optional[CliError]:
+ if context.obj['verbose']:
+ click.secho(f'Error: {traceback.format_exc()}', fg='red')
+
+ errors: CliErrors = {
+ custom_exceptions.NetworkError: CliError(
+ code='cycode_error',
+ message='Cycode was unable to complete this report. '
+ 'Please try again by executing the `cycode report` command',
+ ),
+ custom_exceptions.ScanAsyncError: CliError(
+ code='report_error',
+ message='Cycode was unable to complete this report. '
+ 'Please try again by executing the `cycode report` command',
+ ),
+ custom_exceptions.ReportAsyncError: CliError(
+ code='report_error',
+ message='Cycode was unable to complete this report. '
+ 'Please try again by executing the `cycode report` command',
+ ),
+ custom_exceptions.HttpUnauthorizedError: CliError(
+ code='auth_error',
+ message='Unable to authenticate to Cycode, your token is either invalid or has expired. '
+ 'Please re-generate your token and reconfigure it by running the `cycode configure` command',
+ ),
+ }
+
+ if type(err) in errors:
+ error = errors[type(err)]
+
+ ConsolePrinter(context).print_error(error)
+ return None
+
+ if isinstance(err, click.ClickException):
+ raise err
+
+ raise click.ClickException(str(err))
diff --git a/cycode/cli/commands/report/sbom/sbom_command.py b/cycode/cli/commands/report/sbom/sbom_command.py
new file mode 100644
index 00000000..ecfd2782
--- /dev/null
+++ b/cycode/cli/commands/report/sbom/sbom_command.py
@@ -0,0 +1,84 @@
+import pathlib
+from typing import Optional
+
+import click
+
+from cycode.cli.commands.report.sbom.sbom_path_command import sbom_path_command
+from cycode.cli.commands.report.sbom.sbom_repository_url_command import sbom_repository_url_command
+from cycode.cli.config import config
+from cycode.cyclient.report_client import ReportParameters
+
+
+@click.group(
+ commands={
+ 'path': sbom_path_command,
+ 'repository_url': sbom_repository_url_command,
+ },
+ short_help='Generate SBOM report for remote repository by url or local directory by path.',
+)
+@click.option(
+ '--format',
+ '-f',
+ help='SBOM format.',
+ type=click.Choice(config['scans']['supported_sbom_formats']),
+ required=True,
+)
+@click.option(
+ '--output-format',
+ '-o',
+ default='json',
+ help='Specify the output file format (the default is json).',
+ type=click.Choice(['json']),
+ required=False,
+)
+@click.option(
+ '--output-file',
+ help='Output file (the default is autogenerated filename saved to the current directory).',
+ default=None,
+ type=click.Path(resolve_path=True, writable=True, path_type=pathlib.Path),
+ required=False,
+)
+@click.option(
+ '--include-vulnerabilities',
+ is_flag=True,
+ default=False,
+ help='Include vulnerabilities.',
+ type=bool,
+ required=False,
+)
+@click.option(
+ '--include-dev-dependencies',
+ is_flag=True,
+ default=False,
+ help='Include dev dependencies.',
+ type=bool,
+ required=False,
+)
+@click.pass_context
+def sbom_command(
+ context: click.Context,
+ format: str,
+ output_format: Optional[str],
+ output_file: Optional[pathlib.Path],
+ include_vulnerabilities: bool,
+ include_dev_dependencies: bool,
+) -> int:
+ """Generate SBOM report."""
+ sbom_format_parts = format.split('-')
+ if len(sbom_format_parts) != 2:
+ raise click.ClickException('Invalid SBOM format.')
+
+ sbom_format, sbom_format_version = sbom_format_parts
+
+ report_parameters = ReportParameters(
+ entity_type='SbomCli',
+ sbom_report_type=sbom_format,
+ sbom_version=sbom_format_version,
+ output_format=output_format,
+ include_vulnerabilities=include_vulnerabilities,
+ include_dev_dependencies=include_dev_dependencies,
+ )
+ context.obj['report_parameters'] = report_parameters
+ context.obj['output_file'] = output_file
+
+ return 1
diff --git a/cycode/cli/commands/report/sbom/sbom_path_command.py b/cycode/cli/commands/report/sbom/sbom_path_command.py
new file mode 100644
index 00000000..36b9c4d9
--- /dev/null
+++ b/cycode/cli/commands/report/sbom/sbom_path_command.py
@@ -0,0 +1,65 @@
+import time
+
+import click
+
+from cycode.cli import consts
+from cycode.cli.commands.report.sbom.common import create_sbom_report, send_report_feedback
+from cycode.cli.commands.report.sbom.handle_errors import handle_report_exception
+from cycode.cli.files_collector.path_documents import get_relevant_document
+from cycode.cli.files_collector.sca.sca_code_scanner import perform_pre_scan_documents_actions
+from cycode.cli.files_collector.zip_documents import zip_documents
+from cycode.cli.utils.progress_bar import SbomReportProgressBarSection
+
+
+@click.command(short_help='Generate SBOM report for provided path in the command.')
+@click.argument('path', nargs=1, type=click.Path(exists=True, resolve_path=True), required=True)
+@click.pass_context
+def sbom_path_command(context: click.Context, path: str) -> None:
+ client = context.obj['client']
+ report_parameters = context.obj['report_parameters']
+ output_format = report_parameters.output_format
+ output_file = context.obj['output_file']
+
+ progress_bar = context.obj['progress_bar']
+ progress_bar.start()
+
+ start_scan_time = time.time()
+ report_execution_id = -1
+
+ try:
+ documents = get_relevant_document(
+ progress_bar, SbomReportProgressBarSection.PREPARE_LOCAL_FILES, consts.SCA_SCAN_TYPE, path
+ )
+ # TODO(MarshalX): combine perform_pre_scan_documents_actions with get_relevant_document.
+ # unhardcode usage of context in perform_pre_scan_documents_actions
+ perform_pre_scan_documents_actions(context, consts.SCA_SCAN_TYPE, documents)
+
+ zipped_documents = zip_documents(consts.SCA_SCAN_TYPE, documents)
+ report_execution = client.request_sbom_report_execution(report_parameters, zip_file=zipped_documents)
+ report_execution_id = report_execution.id
+
+ create_sbom_report(progress_bar, client, report_execution_id, output_file, output_format)
+
+ send_report_feedback(
+ client=client,
+ start_scan_time=start_scan_time,
+ report_type='SBOM',
+ report_command_type='path',
+ request_report_parameters=report_parameters.to_dict(without_entity_type=False),
+ report_execution_id=report_execution_id,
+ request_zip_file_size=zipped_documents.size,
+ )
+ except Exception as e:
+ progress_bar.stop()
+
+ send_report_feedback(
+ client=client,
+ start_scan_time=start_scan_time,
+ report_type='SBOM',
+ report_command_type='path',
+ request_report_parameters=report_parameters.to_dict(without_entity_type=False),
+ report_execution_id=report_execution_id,
+ error_message=str(e),
+ )
+
+ handle_report_exception(context, e)
diff --git a/cycode/cli/commands/report/sbom/sbom_report_file.py b/cycode/cli/commands/report/sbom/sbom_report_file.py
new file mode 100644
index 00000000..4d58f89f
--- /dev/null
+++ b/cycode/cli/commands/report/sbom/sbom_report_file.py
@@ -0,0 +1,49 @@
+import os
+import pathlib
+import re
+from typing import Optional
+
+import click
+
+
+class SbomReportFile:
+ def __init__(self, storage_path: str, output_format: str, output_file: Optional[pathlib.Path]) -> None:
+ if output_file is None:
+ output_file = pathlib.Path(storage_path)
+
+ output_ext = f'.{output_format}'
+ if output_file.suffix != output_ext:
+ output_file = output_file.with_suffix(output_ext)
+
+ self._file_path = output_file
+
+ def is_exists(self) -> bool:
+ return self._file_path.exists()
+
+ def _prompt_overwrite(self) -> bool:
+ return click.confirm(f'File {self._file_path} already exists. Save with a different filename?', default=True)
+
+ def _write(self, content: str) -> None:
+ with open(self._file_path, 'w', encoding='UTF-8') as f:
+ f.write(content)
+
+ def _notify_about_saved_file(self) -> None:
+ click.echo(f'Report saved to {self._file_path}')
+
+ def _find_and_set_unique_filename(self) -> None:
+ attempt_no = 0
+ while self.is_exists():
+ attempt_no += 1
+
+ base, ext = os.path.splitext(self._file_path)
+ # Remove previous suffix
+ base = re.sub(r'-\d+$', '', base)
+
+ self._file_path = pathlib.Path(f'{base}-{attempt_no}{ext}')
+
+ def write(self, content: str) -> None:
+ if self.is_exists() and self._prompt_overwrite():
+ self._find_and_set_unique_filename()
+
+ self._write(content)
+ self._notify_about_saved_file()
diff --git a/cycode/cli/commands/report/sbom/sbom_repository_url_command.py b/cycode/cli/commands/report/sbom/sbom_repository_url_command.py
new file mode 100644
index 00000000..a3cb2570
--- /dev/null
+++ b/cycode/cli/commands/report/sbom/sbom_repository_url_command.py
@@ -0,0 +1,55 @@
+import time
+
+import click
+
+from cycode.cli.commands.report.sbom.common import create_sbom_report, send_report_feedback
+from cycode.cli.commands.report.sbom.handle_errors import handle_report_exception
+from cycode.cli.utils.progress_bar import SbomReportProgressBarSection
+
+
+@click.command(short_help='Generate SBOM report for provided repository URI in the command.')
+@click.argument('uri', nargs=1, type=str, required=True)
+@click.pass_context
+def sbom_repository_url_command(context: click.Context, uri: str) -> None:
+ progress_bar = context.obj['progress_bar']
+ progress_bar.start()
+ progress_bar.set_section_length(SbomReportProgressBarSection.PREPARE_LOCAL_FILES)
+
+ client = context.obj['client']
+ report_parameters = context.obj['report_parameters']
+ output_file = context.obj['output_file']
+ output_format = report_parameters.output_format
+
+ start_scan_time = time.time()
+ report_execution_id = -1
+
+ try:
+ report_execution = client.request_sbom_report_execution(report_parameters, repository_url=uri)
+ report_execution_id = report_execution.id
+
+ create_sbom_report(progress_bar, client, report_execution_id, output_file, output_format)
+
+ send_report_feedback(
+ client=client,
+ start_scan_time=start_scan_time,
+ report_type='SBOM',
+ report_command_type='repository_url',
+ request_report_parameters=report_parameters.to_dict(without_entity_type=False),
+ report_execution_id=report_execution_id,
+ repository_uri=uri,
+ )
+ except Exception as e:
+ progress_bar.stop()
+
+ send_report_feedback(
+ client=client,
+ start_scan_time=start_scan_time,
+ report_type='SBOM',
+ report_command_type='repository_url',
+ request_report_parameters=report_parameters.to_dict(without_entity_type=False),
+ report_execution_id=report_execution_id,
+ error_message=str(e),
+ repository_uri=uri,
+ )
+
+ handle_report_exception(context, e)
diff --git a/cycode/cli/config.yaml b/cycode/cli/config.yaml
index 0ffe7abc..875f37c1 100644
--- a/cycode/cli/config.yaml
+++ b/cycode/cli/config.yaml
@@ -8,6 +8,10 @@ scans:
supported_sca_scans:
- package-vulnerabilities
- license-compliance
+ supported_sbom_formats:
+ - spdx-2.2
+ - spdx-2.3
+ - cyclonedx-1.4
result_printer:
default:
lines_to_display: 3
diff --git a/cycode/cli/consts.py b/cycode/cli/consts.py
index 23b7471a..9479765e 100644
--- a/cycode/cli/consts.py
+++ b/cycode/cli/consts.py
@@ -138,6 +138,11 @@
SCAN_BATCH_MAX_PARALLEL_SCANS = 5
SCAN_BATCH_SCANS_PER_CPU = 1
+# report with polling
+REPORT_POLLING_WAIT_INTERVAL_IN_SECONDS = 5
+DEFAULT_REPORT_POLLING_TIMEOUT_IN_SECONDS = 600
+REPORT_POLLING_TIMEOUT_IN_SECONDS_ENV_VAR_NAME = 'REPORT_POLLING_TIMEOUT_IN_SECONDS'
+
# scan with polling
SCAN_POLLING_WAIT_INTERVAL_IN_SECONDS = 5
DEFAULT_SCAN_POLLING_TIMEOUT_IN_SECONDS = 3600
@@ -162,6 +167,10 @@
EXCLUDE_DETECTIONS_IN_DELETED_LINES_ENV_VAR_NAME = 'EXCLUDE_DETECTIONS_IN_DELETED_LINES'
DEFAULT_EXCLUDE_DETECTIONS_IN_DELETED_LINES = True
+# report statuses
+REPORT_STATUS_COMPLETED = 'Completed'
+REPORT_STATUS_ERROR = 'Failed'
+
# scan statuses
SCAN_STATUS_COMPLETED = 'Completed'
SCAN_STATUS_ERROR = 'Error'
diff --git a/cycode/cli/exceptions/custom_exceptions.py b/cycode/cli/exceptions/custom_exceptions.py
index ea98a0aa..1b218353 100644
--- a/cycode/cli/exceptions/custom_exceptions.py
+++ b/cycode/cli/exceptions/custom_exceptions.py
@@ -28,6 +28,10 @@ def __str__(self) -> str:
return f'error occurred during the scan. error message: {self.error_message}'
+class ReportAsyncError(CycodeError):
+ pass
+
+
class HttpUnauthorizedError(CycodeError):
def __init__(self, error_message: str, response: Response) -> None:
self.status_code = 401
diff --git a/cycode/cyclient/scan_config/__init__.py b/cycode/cli/files_collector/__init__.py
similarity index 100%
rename from cycode/cyclient/scan_config/__init__.py
rename to cycode/cli/files_collector/__init__.py
diff --git a/cycode/cli/files_collector/excluder.py b/cycode/cli/files_collector/excluder.py
new file mode 100644
index 00000000..cbbb358f
--- /dev/null
+++ b/cycode/cli/files_collector/excluder.py
@@ -0,0 +1,134 @@
+from typing import TYPE_CHECKING, List
+
+from cycode.cli import consts
+from cycode.cli.config import configuration_manager
+from cycode.cli.user_settings.config_file_manager import ConfigFileManager
+from cycode.cli.utils.path_utils import get_file_size, is_binary_file, is_sub_path
+from cycode.cli.utils.string_utils import get_content_size, is_binary_content
+from cycode.cyclient import logger
+
+if TYPE_CHECKING:
+ from cycode.cli.models import Document
+ from cycode.cli.utils.progress_bar import BaseProgressBar, ProgressBarSection
+
+
+def exclude_irrelevant_files(
+ progress_bar: 'BaseProgressBar', progress_bar_section: 'ProgressBarSection', scan_type: str, filenames: List[str]
+) -> List[str]:
+ relevant_files = []
+ for filename in filenames:
+ progress_bar.update(progress_bar_section)
+ if _is_relevant_file_to_scan(scan_type, filename):
+ relevant_files.append(filename)
+
+ is_sub_path.cache_clear() # free up memory
+
+ return relevant_files
+
+
+def exclude_irrelevant_documents_to_scan(scan_type: str, documents_to_scan: List['Document']) -> List['Document']:
+ logger.debug('Excluding irrelevant documents to scan')
+
+ relevant_documents = []
+ for document in documents_to_scan:
+ if _is_relevant_document_to_scan(scan_type, document.path, document.content):
+ relevant_documents.append(document)
+
+ return relevant_documents
+
+
+def _is_subpath_of_cycode_configuration_folder(filename: str) -> bool:
+ return (
+ is_sub_path(configuration_manager.global_config_file_manager.get_config_directory_path(), filename)
+ or is_sub_path(configuration_manager.local_config_file_manager.get_config_directory_path(), filename)
+ or filename.endswith(ConfigFileManager.get_config_file_route())
+ )
+
+
+def _is_path_configured_in_exclusions(scan_type: str, file_path: str) -> bool:
+ exclusions_by_path = configuration_manager.get_exclusions_by_scan_type(scan_type).get(
+ consts.EXCLUSIONS_BY_PATH_SECTION_NAME, []
+ )
+ return any(is_sub_path(exclusion_path, file_path) for exclusion_path in exclusions_by_path)
+
+
+def _does_file_exceed_max_size_limit(filename: str) -> bool:
+ return get_file_size(filename) > consts.FILE_MAX_SIZE_LIMIT_IN_BYTES
+
+
+def _does_document_exceed_max_size_limit(content: str) -> bool:
+ return get_content_size(content) > consts.FILE_MAX_SIZE_LIMIT_IN_BYTES
+
+
+def _is_relevant_file_to_scan(scan_type: str, filename: str) -> bool:
+ if _is_subpath_of_cycode_configuration_folder(filename):
+ logger.debug('file is irrelevant because it is in cycode configuration directory, %s', {'filename': filename})
+ return False
+
+ if _is_path_configured_in_exclusions(scan_type, filename):
+ logger.debug('file is irrelevant because the file path is in the ignore paths list, %s', {'filename': filename})
+ return False
+
+ if not _is_file_extension_supported(scan_type, filename):
+ logger.debug('file is irrelevant because the file extension is not supported, %s', {'filename': filename})
+ return False
+
+ if is_binary_file(filename):
+ logger.debug('file is irrelevant because it is binary file, %s', {'filename': filename})
+ return False
+
+ if scan_type != consts.SCA_SCAN_TYPE and _does_file_exceed_max_size_limit(filename):
+ logger.debug('file is irrelevant because its exceeded max size limit, %s', {'filename': filename})
+ return False
+
+ if scan_type == consts.SCA_SCAN_TYPE and not _is_file_relevant_for_sca_scan(filename):
+ return False
+
+ return True
+
+
+def _is_file_relevant_for_sca_scan(filename: str) -> bool:
+ if any(sca_excluded_path in filename for sca_excluded_path in consts.SCA_EXCLUDED_PATHS):
+ logger.debug("file is irrelevant because it is from node_modules's inner path, %s", {'filename': filename})
+ return False
+
+ return True
+
+
+def _is_relevant_document_to_scan(scan_type: str, filename: str, content: str) -> bool:
+ if _is_subpath_of_cycode_configuration_folder(filename):
+ logger.debug(
+ 'document is irrelevant because it is in cycode configuration directory, %s', {'filename': filename}
+ )
+ return False
+
+ if _is_path_configured_in_exclusions(scan_type, filename):
+ logger.debug(
+ 'document is irrelevant because the document path is in the ignore paths list, %s', {'filename': filename}
+ )
+ return False
+
+ if not _is_file_extension_supported(scan_type, filename):
+ logger.debug('document is irrelevant because the file extension is not supported, %s', {'filename': filename})
+ return False
+
+ if is_binary_content(content):
+ logger.debug('document is irrelevant because it is binary, %s', {'filename': filename})
+ return False
+
+ if scan_type != consts.SCA_SCAN_TYPE and _does_document_exceed_max_size_limit(content):
+ logger.debug('document is irrelevant because its exceeded max size limit, %s', {'filename': filename})
+ return False
+ return True
+
+
+def _is_file_extension_supported(scan_type: str, filename: str) -> bool:
+ filename = filename.lower()
+
+ if scan_type == consts.INFRA_CONFIGURATION_SCAN_TYPE:
+ return filename.endswith(consts.INFRA_CONFIGURATION_SCAN_SUPPORTED_FILES)
+
+ if scan_type == consts.SCA_SCAN_TYPE:
+ return filename.endswith(consts.SCA_CONFIGURATION_SCAN_SUPPORTED_FILES)
+
+ return not filename.endswith(consts.SECRET_SCAN_FILE_EXTENSIONS_TO_IGNORE)
diff --git a/cycode/cli/files_collector/iac/__init__.py b/cycode/cli/files_collector/iac/__init__.py
new file mode 100644
index 00000000..e69de29b
diff --git a/cycode/cli/helpers/tf_content_generator.py b/cycode/cli/files_collector/iac/tf_content_generator.py
similarity index 73%
rename from cycode/cli/helpers/tf_content_generator.py
rename to cycode/cli/files_collector/iac/tf_content_generator.py
index 7594a96f..4df6d827 100644
--- a/cycode/cli/helpers/tf_content_generator.py
+++ b/cycode/cli/files_collector/iac/tf_content_generator.py
@@ -1,13 +1,34 @@
import json
+import time
from typing import List
+from cycode.cli import consts
from cycode.cli.exceptions.custom_exceptions import TfplanKeyError
from cycode.cli.models import ResourceChange
-from cycode.cli.utils.path_utils import load_json
+from cycode.cli.utils.path_utils import change_filename_extension, load_json
ACTIONS_TO_OMIT_RESOURCE = ['delete']
+def generate_tfplan_document_name(path: str) -> str:
+ document_name = change_filename_extension(path, 'tf')
+ timestamp = int(time.time())
+ return f'{timestamp}-{document_name}'
+
+
+def is_iac(scan_type: str) -> bool:
+ return scan_type == consts.INFRA_CONFIGURATION_SCAN_TYPE
+
+
+def is_tfplan_file(file: str, content: str) -> bool:
+ if not file.endswith('.json'):
+ return False
+ tf_plan = load_json(content)
+ if not isinstance(tf_plan, dict):
+ return False
+ return 'resource_changes' in tf_plan
+
+
def generate_tf_content_from_tfplan(filename: str, tfplan: str) -> str:
planned_resources = _extract_resources(tfplan, filename)
return _generate_tf_content(planned_resources)
diff --git a/cycode/cli/files_collector/models/__init__.py b/cycode/cli/files_collector/models/__init__.py
new file mode 100644
index 00000000..e69de29b
diff --git a/cycode/cli/zip_file.py b/cycode/cli/files_collector/models/in_memory_zip.py
similarity index 74%
rename from cycode/cli/zip_file.py
rename to cycode/cli/files_collector/models/in_memory_zip.py
index 7d659c8e..410d00ca 100644
--- a/cycode/cli/zip_file.py
+++ b/cycode/cli/files_collector/models/in_memory_zip.py
@@ -1,8 +1,10 @@
-import os.path
from io import BytesIO
+from sys import getsizeof
from typing import Optional
from zipfile import ZIP_DEFLATED, ZipFile
+from cycode.cli.utils.path_utils import concat_unique_id
+
class InMemoryZip(object):
def __init__(self) -> None:
@@ -25,10 +27,6 @@ def read(self) -> bytes:
self.in_memory_zip.seek(0)
return self.in_memory_zip.read()
-
-def concat_unique_id(filename: str, unique_id: str) -> str:
- if filename.startswith(os.sep):
- # remove leading slash to join the path correctly
- filename = filename[len(os.sep) :]
-
- return os.path.join(unique_id, filename)
+ @property
+ def size(self) -> int:
+ return getsizeof(self.in_memory_zip)
diff --git a/cycode/cli/files_collector/path_documents.py b/cycode/cli/files_collector/path_documents.py
new file mode 100644
index 00000000..a0df5ac0
--- /dev/null
+++ b/cycode/cli/files_collector/path_documents.py
@@ -0,0 +1,112 @@
+import os
+from typing import TYPE_CHECKING, Iterable, List
+
+import pathspec
+
+from cycode.cli.files_collector.excluder import exclude_irrelevant_files
+from cycode.cli.files_collector.iac.tf_content_generator import (
+ generate_tf_content_from_tfplan,
+ generate_tfplan_document_name,
+ is_iac,
+ is_tfplan_file,
+)
+from cycode.cli.models import Document
+from cycode.cli.utils.path_utils import get_absolute_path, get_file_content
+from cycode.cyclient import logger
+
+if TYPE_CHECKING:
+ from cycode.cli.utils.progress_bar import BaseProgressBar, ProgressBarSection
+
+
+def _get_all_existing_files_in_directory(path: str) -> List[str]:
+ files: List[str] = []
+
+ for root, _, filenames in os.walk(path):
+ for filename in filenames:
+ files.append(os.path.join(root, filename))
+
+ return files
+
+
+def _get_relevant_files_in_path(path: str, exclude_patterns: Iterable[str]) -> List[str]:
+ absolute_path = get_absolute_path(path)
+
+ if not os.path.isfile(absolute_path) and not os.path.isdir(absolute_path):
+ raise FileNotFoundError(f'the specified path was not found, path: {absolute_path}')
+
+ if os.path.isfile(absolute_path):
+ return [absolute_path]
+
+ all_file_paths = set(_get_all_existing_files_in_directory(absolute_path))
+
+ path_spec = pathspec.PathSpec.from_lines(pathspec.patterns.GitWildMatchPattern, exclude_patterns)
+ excluded_file_paths = set(path_spec.match_files(all_file_paths))
+
+ relevant_file_paths = all_file_paths - excluded_file_paths
+
+ return [file_path for file_path in relevant_file_paths if os.path.isfile(file_path)]
+
+
+def _get_relevant_files(
+ progress_bar: 'BaseProgressBar', progress_bar_section: 'ProgressBarSection', scan_type: str, path: str
+) -> List[str]:
+ all_files_to_scan = _get_relevant_files_in_path(path=path, exclude_patterns=['**/.git/**', '**/.cycode/**'])
+
+ # we are double the progress bar section length because we are going to process the files twice
+ # first time to get the file list with respect of excluded patterns (excluding takes seconds to execute)
+ # second time to get the files content
+ progress_bar_section_len = len(all_files_to_scan) * 2
+ progress_bar.set_section_length(progress_bar_section, progress_bar_section_len)
+
+ relevant_files_to_scan = exclude_irrelevant_files(progress_bar, progress_bar_section, scan_type, all_files_to_scan)
+
+ # after finishing the first processing (excluding),
+ # we must update the progress bar stage with respect of excluded files.
+ # now it's possible that we will not process x2 of the files count
+ # because some of them were excluded, we should subtract the excluded files count
+ # from the progress bar section length
+ excluded_files_count = len(all_files_to_scan) - len(relevant_files_to_scan)
+ progress_bar_section_len = progress_bar_section_len - excluded_files_count
+ progress_bar.set_section_length(progress_bar_section, progress_bar_section_len)
+
+ logger.debug(
+ 'Found all relevant files for scanning %s', {'path': path, 'file_to_scan_count': len(relevant_files_to_scan)}
+ )
+
+ return relevant_files_to_scan
+
+
+def _generate_document(file: str, scan_type: str, content: str, is_git_diff: bool) -> Document:
+ if is_iac(scan_type) and is_tfplan_file(file, content):
+ return _handle_tfplan_file(file, content, is_git_diff)
+
+ return Document(file, content, is_git_diff)
+
+
+def _handle_tfplan_file(file: str, content: str, is_git_diff: bool) -> Document:
+ document_name = generate_tfplan_document_name(file)
+ tf_content = generate_tf_content_from_tfplan(file, content)
+ return Document(document_name, tf_content, is_git_diff)
+
+
+def get_relevant_document(
+ progress_bar: 'BaseProgressBar',
+ progress_bar_section: 'ProgressBarSection',
+ scan_type: str,
+ path: str,
+ *,
+ is_git_diff: bool = False,
+) -> List[Document]:
+ relevant_files = _get_relevant_files(progress_bar, progress_bar_section, scan_type, path)
+
+ documents: List[Document] = []
+ for file in relevant_files:
+ progress_bar.update(progress_bar_section)
+
+ content = get_file_content(file)
+ if not content:
+ continue
+
+ documents.append(_generate_document(file, scan_type, content, is_git_diff))
+
+ return documents
diff --git a/cycode/cli/files_collector/repository_documents.py b/cycode/cli/files_collector/repository_documents.py
new file mode 100644
index 00000000..acd9c225
--- /dev/null
+++ b/cycode/cli/files_collector/repository_documents.py
@@ -0,0 +1,140 @@
+import os
+from typing import TYPE_CHECKING, Iterator, List, Optional, Tuple, Union
+
+from cycode.cli import consts
+from cycode.cli.files_collector.sca import sca_code_scanner
+from cycode.cli.models import Document
+from cycode.cli.utils.path_utils import get_file_content, get_path_by_os
+
+if TYPE_CHECKING:
+ from git import Blob, Diff
+ from git.objects.base import IndexObjUnion
+ from git.objects.tree import TraversedTreeTup
+
+ from cycode.cli.utils.progress_bar import BaseProgressBar, ProgressBarSection
+
+from git import Repo
+
+
+def should_process_git_object(obj: 'Blob', _: int) -> bool:
+ return obj.type == 'blob' and obj.size > 0
+
+
+def get_git_repository_tree_file_entries(
+ path: str, branch: str
+) -> Union[Iterator['IndexObjUnion'], Iterator['TraversedTreeTup']]:
+ return Repo(path).tree(branch).traverse(predicate=should_process_git_object)
+
+
+def parse_commit_range(commit_range: str, path: str) -> Tuple[str, str]:
+ from_commit_rev = None
+ to_commit_rev = None
+
+ for commit in Repo(path).iter_commits(rev=commit_range):
+ if not to_commit_rev:
+ to_commit_rev = commit.hexsha
+ from_commit_rev = commit.hexsha
+
+ return from_commit_rev, to_commit_rev
+
+
+def get_diff_file_path(file: 'Diff') -> Optional[str]:
+ return file.b_path if file.b_path else file.a_path
+
+
+def get_diff_file_content(file: 'Diff') -> str:
+ return file.diff.decode('UTF-8', errors='replace')
+
+
+def get_pre_commit_modified_documents(
+ progress_bar: 'BaseProgressBar', progress_bar_section: 'ProgressBarSection'
+) -> Tuple[List[Document], List[Document]]:
+ git_head_documents = []
+ pre_committed_documents = []
+
+ repo = Repo(os.getcwd())
+ diff_files = repo.index.diff(consts.GIT_HEAD_COMMIT_REV, create_patch=True, R=True)
+ progress_bar.set_section_length(progress_bar_section, len(diff_files))
+ for file in diff_files:
+ progress_bar.update(progress_bar_section)
+
+ diff_file_path = get_diff_file_path(file)
+ file_path = get_path_by_os(diff_file_path)
+
+ file_content = sca_code_scanner.get_file_content_from_commit(repo, consts.GIT_HEAD_COMMIT_REV, diff_file_path)
+ if file_content is not None:
+ git_head_documents.append(Document(file_path, file_content))
+
+ if os.path.exists(file_path):
+ file_content = get_file_content(file_path)
+ pre_committed_documents.append(Document(file_path, file_content))
+
+ return git_head_documents, pre_committed_documents
+
+
+def get_commit_range_modified_documents(
+ progress_bar: 'BaseProgressBar',
+ progress_bar_section: 'ProgressBarSection',
+ path: str,
+ from_commit_rev: str,
+ to_commit_rev: str,
+) -> Tuple[List[Document], List[Document]]:
+ from_commit_documents = []
+ to_commit_documents = []
+
+ repo = Repo(path)
+ diff = repo.commit(from_commit_rev).diff(to_commit_rev)
+
+ modified_files_diff = [
+ change for change in diff if change.change_type != consts.COMMIT_DIFF_DELETED_FILE_CHANGE_TYPE
+ ]
+ progress_bar.set_section_length(progress_bar_section, len(modified_files_diff))
+ for blob in modified_files_diff:
+ progress_bar.update(progress_bar_section)
+
+ diff_file_path = get_diff_file_path(blob)
+ file_path = get_path_by_os(diff_file_path)
+
+ file_content = sca_code_scanner.get_file_content_from_commit(repo, from_commit_rev, diff_file_path)
+ if file_content is not None:
+ from_commit_documents.append(Document(file_path, file_content))
+
+ file_content = sca_code_scanner.get_file_content_from_commit(repo, to_commit_rev, diff_file_path)
+ if file_content is not None:
+ to_commit_documents.append(Document(file_path, file_content))
+
+ return from_commit_documents, to_commit_documents
+
+
+def calculate_pre_receive_commit_range(branch_update_details: str) -> Optional[str]:
+ end_commit = _get_end_commit_from_branch_update_details(branch_update_details)
+
+ # branch is deleted, no need to perform scan
+ if end_commit == consts.EMPTY_COMMIT_SHA:
+ return None
+
+ start_commit = _get_oldest_unupdated_commit_for_branch(end_commit)
+
+ # no new commit to update found
+ if not start_commit:
+ return None
+
+ return f'{start_commit}~1...{end_commit}'
+
+
+def _get_end_commit_from_branch_update_details(update_details: str) -> str:
+ # update details pattern: ][
+ _, end_commit, _ = update_details.split()
+ return end_commit
+
+
+def _get_oldest_unupdated_commit_for_branch(commit: str) -> Optional[str]:
+ # get a list of commits by chronological order that are not in the remote repository yet
+ # more info about rev-list command: https://git-scm.com/docs/git-rev-list
+ not_updated_commits = Repo(os.getcwd()).git.rev_list(commit, '--topo-order', '--reverse', '--not', '--all')
+
+ commits = not_updated_commits.splitlines()
+ if not commits:
+ return None
+
+ return commits[0]
diff --git a/cycode/cli/files_collector/sca/__init__.py b/cycode/cli/files_collector/sca/__init__.py
new file mode 100644
index 00000000..e69de29b
diff --git a/cycode/cli/files_collector/sca/maven/__init__.py b/cycode/cli/files_collector/sca/maven/__init__.py
new file mode 100644
index 00000000..e69de29b
diff --git a/cycode/cli/helpers/maven/base_restore_maven_dependencies.py b/cycode/cli/files_collector/sca/maven/base_restore_maven_dependencies.py
similarity index 100%
rename from cycode/cli/helpers/maven/base_restore_maven_dependencies.py
rename to cycode/cli/files_collector/sca/maven/base_restore_maven_dependencies.py
diff --git a/cycode/cli/helpers/maven/restore_gradle_dependencies.py b/cycode/cli/files_collector/sca/maven/restore_gradle_dependencies.py
similarity index 88%
rename from cycode/cli/helpers/maven/restore_gradle_dependencies.py
rename to cycode/cli/files_collector/sca/maven/restore_gradle_dependencies.py
index f8cd2fec..ef975ba5 100644
--- a/cycode/cli/helpers/maven/restore_gradle_dependencies.py
+++ b/cycode/cli/files_collector/sca/maven/restore_gradle_dependencies.py
@@ -2,7 +2,7 @@
import click
-from cycode.cli.helpers.maven.base_restore_maven_dependencies import BaseRestoreMavenDependencies
+from cycode.cli.files_collector.sca.maven.base_restore_maven_dependencies import BaseRestoreMavenDependencies
from cycode.cli.models import Document
BUILD_GRADLE_FILE_NAME = 'build.gradle'
diff --git a/cycode/cli/helpers/maven/restore_maven_dependencies.py b/cycode/cli/files_collector/sca/maven/restore_maven_dependencies.py
similarity index 97%
rename from cycode/cli/helpers/maven/restore_maven_dependencies.py
rename to cycode/cli/files_collector/sca/maven/restore_maven_dependencies.py
index d8e6675f..0e21df12 100644
--- a/cycode/cli/helpers/maven/restore_maven_dependencies.py
+++ b/cycode/cli/files_collector/sca/maven/restore_maven_dependencies.py
@@ -3,7 +3,7 @@
import click
-from cycode.cli.helpers.maven.base_restore_maven_dependencies import (
+from cycode.cli.files_collector.sca.maven.base_restore_maven_dependencies import (
BaseRestoreMavenDependencies,
build_dep_tree_path,
execute_command,
diff --git a/cycode/cli/helpers/sca_code_scanner.py b/cycode/cli/files_collector/sca/sca_code_scanner.py
similarity index 88%
rename from cycode/cli/helpers/sca_code_scanner.py
rename to cycode/cli/files_collector/sca/sca_code_scanner.py
index 227b553e..a6aa6b78 100644
--- a/cycode/cli/helpers/sca_code_scanner.py
+++ b/cycode/cli/files_collector/sca/sca_code_scanner.py
@@ -5,14 +5,14 @@
from git import GitCommandError, Repo
from cycode.cli import consts
-from cycode.cli.helpers.maven.restore_gradle_dependencies import RestoreGradleDependencies
-from cycode.cli.helpers.maven.restore_maven_dependencies import RestoreMavenDependencies
+from cycode.cli.files_collector.sca.maven.restore_gradle_dependencies import RestoreGradleDependencies
+from cycode.cli.files_collector.sca.maven.restore_maven_dependencies import RestoreMavenDependencies
from cycode.cli.models import Document
from cycode.cli.utils.path_utils import get_file_content, get_file_dir, join_paths
from cycode.cyclient import logger
if TYPE_CHECKING:
- from cycode.cli.helpers.maven.base_restore_maven_dependencies import BaseRestoreMavenDependencies
+ from cycode.cli.files_collector.sca.maven.base_restore_maven_dependencies import BaseRestoreMavenDependencies
BUILD_GRADLE_FILE_NAME = 'build.gradle'
BUILD_GRADLE_KTS_FILE_NAME = 'build.gradle.kts'
@@ -141,3 +141,11 @@ def get_file_content_from_commit(repo: Repo, commit: str, file_path: str) -> Opt
return repo.git.show(f'{commit}:{file_path}')
except GitCommandError:
return None
+
+
+def perform_pre_scan_documents_actions(
+ context: click.Context, scan_type: str, documents_to_scan: List[Document], is_git_diff: bool = False
+) -> None:
+ if scan_type == consts.SCA_SCAN_TYPE and not context.obj.get(consts.SCA_SKIP_RESTORE_DEPENDENCIES_FLAG):
+ logger.debug('Perform pre scan document add_dependencies_tree_document action')
+ add_dependencies_tree_document(context, documents_to_scan, is_git_diff)
diff --git a/cycode/cli/files_collector/zip_documents.py b/cycode/cli/files_collector/zip_documents.py
new file mode 100644
index 00000000..b2b252f4
--- /dev/null
+++ b/cycode/cli/files_collector/zip_documents.py
@@ -0,0 +1,40 @@
+import time
+from typing import List, Optional
+
+from cycode.cli import consts
+from cycode.cli.exceptions import custom_exceptions
+from cycode.cli.files_collector.models.in_memory_zip import InMemoryZip
+from cycode.cli.models import Document
+from cycode.cyclient import logger
+
+
+def _validate_zip_file_size(scan_type: str, zip_file_size: int) -> None:
+ if scan_type == consts.SCA_SCAN_TYPE:
+ if zip_file_size > consts.SCA_ZIP_MAX_SIZE_LIMIT_IN_BYTES:
+ raise custom_exceptions.ZipTooLargeError(consts.SCA_ZIP_MAX_SIZE_LIMIT_IN_BYTES)
+ else:
+ if zip_file_size > consts.ZIP_MAX_SIZE_LIMIT_IN_BYTES:
+ raise custom_exceptions.ZipTooLargeError(consts.ZIP_MAX_SIZE_LIMIT_IN_BYTES)
+
+
+def zip_documents(scan_type: str, documents: List[Document], zip_file: Optional[InMemoryZip] = None) -> InMemoryZip:
+ if zip_file is None:
+ zip_file = InMemoryZip()
+
+ start_zip_creation_time = time.time()
+
+ for index, document in enumerate(documents):
+ _validate_zip_file_size(scan_type, zip_file.size)
+
+ logger.debug(
+ 'adding file to zip, %s', {'index': index, 'filename': document.path, 'unique_id': document.unique_id}
+ )
+ zip_file.append(document.path, document.unique_id, document.content)
+
+ zip_file.close()
+
+ end_zip_creation_time = time.time()
+ zip_creation_time = int(end_zip_creation_time - start_zip_creation_time)
+ logger.debug('finished to create zip file, %s', {'zip_creation_time': zip_creation_time})
+
+ return zip_file
diff --git a/cycode/cli/main.py b/cycode/cli/main.py
index 94f3ff29..efa2b200 100644
--- a/cycode/cli/main.py
+++ b/cycode/cli/main.py
@@ -1,13 +1,14 @@
import json
import logging
import sys
-from typing import TYPE_CHECKING, List, Optional, Tuple
+from typing import List, Optional
import click
from cycode import __version__
from cycode.cli import code_scanner
from cycode.cli.auth.auth_command import authenticate
+from cycode.cli.commands.report.report_command import report_command
from cycode.cli.config import config
from cycode.cli.consts import (
CLI_CONTEXT_SETTINGS,
@@ -18,17 +19,13 @@
)
from cycode.cli.models import Severity
from cycode.cli.user_settings.configuration_manager import ConfigurationManager
-from cycode.cli.user_settings.credentials_manager import CredentialsManager
from cycode.cli.user_settings.user_settings_commands import add_exclusions, set_credentials
from cycode.cli.utils import scan_utils
-from cycode.cli.utils.progress_bar import get_progress_bar
+from cycode.cli.utils.get_api_client import get_scan_cycode_client
+from cycode.cli.utils.progress_bar import SCAN_PROGRESS_BAR_SECTIONS, get_progress_bar
from cycode.cyclient.config import set_logging_level
from cycode.cyclient.cycode_client_base import CycodeClientBase
from cycode.cyclient.models import UserAgentOptionScheme
-from cycode.cyclient.scan_config.scan_config_creator import create_scan_client
-
-if TYPE_CHECKING:
- from cycode.cyclient.scan_client import ScanClient
@click.group(
@@ -137,7 +134,7 @@ def code_scan(
else:
context.obj['soft_fail'] = config['soft_fail']
- context.obj['client'] = get_cycode_client(client_id, secret, not context.obj['show_secret'])
+ context.obj['client'] = get_scan_cycode_client(client_id, secret, not context.obj['show_secret'])
context.obj['scan_type'] = scan_type
context.obj['severity_threshold'] = severity_threshold
context.obj['monitor'] = monitor
@@ -185,6 +182,7 @@ def version(context: click.Context) -> None:
@click.group(
commands={
'scan': code_scan,
+ 'report': report_command,
'configure': set_credentials,
'ignore': add_exclusions,
'auth': authenticate,
@@ -234,29 +232,13 @@ def main_cli(
if output == 'json':
no_progress_meter = True
- context.obj['progress_bar'] = get_progress_bar(hidden=no_progress_meter)
+ context.obj['progress_bar'] = get_progress_bar(hidden=no_progress_meter, sections=SCAN_PROGRESS_BAR_SECTIONS)
if user_agent:
user_agent_option = UserAgentOptionScheme().loads(user_agent)
CycodeClientBase.enrich_user_agent(user_agent_option.user_agent_suffix)
-def get_cycode_client(client_id: str, client_secret: str, hide_response_log: bool) -> 'ScanClient':
- if not client_id or not client_secret:
- client_id, client_secret = _get_configured_credentials()
- if not client_id:
- raise click.ClickException('Cycode client id needed.')
- if not client_secret:
- raise click.ClickException('Cycode client secret is needed.')
-
- return create_scan_client(client_id, client_secret, hide_response_log)
-
-
-def _get_configured_credentials() -> Tuple[str, str]:
- credentials_manager = CredentialsManager()
- return credentials_manager.get_credentials()
-
-
def _should_fail_scan(context: click.Context) -> bool:
return scan_utils.is_scan_failed(context)
diff --git a/cycode/cli/user_settings/configuration_manager.py b/cycode/cli/user_settings/configuration_manager.py
index 98e62e07..65da08fc 100644
--- a/cycode/cli/user_settings/configuration_manager.py
+++ b/cycode/cli/user_settings/configuration_manager.py
@@ -103,6 +103,13 @@ def get_scan_polling_timeout_in_seconds(self) -> int:
)
)
+ def get_report_polling_timeout_in_seconds(self) -> int:
+ return int(
+ self._get_value_from_environment_variables(
+ consts.REPORT_POLLING_TIMEOUT_IN_SECONDS_ENV_VAR_NAME, consts.DEFAULT_REPORT_POLLING_TIMEOUT_IN_SECONDS
+ )
+ )
+
def get_sca_pre_commit_timeout_in_seconds(self) -> int:
return int(
self._get_value_from_environment_variables(
diff --git a/cycode/cli/utils/get_api_client.py b/cycode/cli/utils/get_api_client.py
new file mode 100644
index 00000000..7bbfa2d9
--- /dev/null
+++ b/cycode/cli/utils/get_api_client.py
@@ -0,0 +1,40 @@
+from typing import TYPE_CHECKING, Optional, Tuple, Union
+
+import click
+
+from cycode.cli.user_settings.credentials_manager import CredentialsManager
+from cycode.cyclient.client_creator import create_report_client, create_scan_client
+
+if TYPE_CHECKING:
+ from cycode.cyclient.report_client import ReportClient
+ from cycode.cyclient.scan_client import ScanClient
+
+
+def _get_cycode_client(
+ create_client_func: callable, client_id: Optional[str], client_secret: Optional[str], hide_response_log: bool
+) -> Union['ScanClient', 'ReportClient']:
+ if not client_id or not client_secret:
+ client_id, client_secret = _get_configured_credentials()
+ if not client_id:
+ raise click.ClickException('Cycode client id needed.')
+ if not client_secret:
+ raise click.ClickException('Cycode client secret is needed.')
+
+ return create_client_func(client_id, client_secret, hide_response_log)
+
+
+def get_scan_cycode_client(
+ client_id: Optional[str] = None, client_secret: Optional[str] = None, hide_response_log: bool = True
+) -> 'ScanClient':
+ return _get_cycode_client(create_scan_client, client_id, client_secret, hide_response_log)
+
+
+def get_report_cycode_client(
+ client_id: Optional[str] = None, client_secret: Optional[str] = None, hide_response_log: bool = True
+) -> 'ReportClient':
+ return _get_cycode_client(create_report_client, client_id, client_secret, hide_response_log)
+
+
+def _get_configured_credentials() -> Tuple[str, str]:
+ credentials_manager = CredentialsManager()
+ return credentials_manager.get_credentials()
diff --git a/cycode/cli/utils/path_utils.py b/cycode/cli/utils/path_utils.py
index ad5ce94e..e0cedc88 100644
--- a/cycode/cli/utils/path_utils.py
+++ b/cycode/cli/utils/path_utils.py
@@ -1,31 +1,11 @@
import json
import os
from functools import lru_cache
-from typing import AnyStr, Iterable, List, Optional
+from typing import AnyStr, List, Optional
-import pathspec
from binaryornot.check import is_binary
-def get_relevant_files_in_path(path: str, exclude_patterns: Iterable[str]) -> List[str]:
- absolute_path = get_absolute_path(path)
-
- if not os.path.isfile(absolute_path) and not os.path.isdir(absolute_path):
- raise FileNotFoundError(f'the specified path was not found, path: {absolute_path}')
-
- if os.path.isfile(absolute_path):
- return [absolute_path]
-
- all_file_paths = set(_get_all_existing_files_in_directory(absolute_path))
-
- path_spec = pathspec.PathSpec.from_lines(pathspec.patterns.GitWildMatchPattern, exclude_patterns)
- excluded_file_paths = set(path_spec.match_files(all_file_paths))
-
- relevant_file_paths = all_file_paths - excluded_file_paths
-
- return [file_path for file_path in relevant_file_paths if os.path.isfile(file_path)]
-
-
@lru_cache(maxsize=None)
def is_sub_path(path: str, sub_path: str) -> bool:
try:
@@ -54,16 +34,6 @@ def get_path_by_os(filename: str) -> str:
return filename.replace('/', os.sep)
-def _get_all_existing_files_in_directory(path: str) -> List[str]:
- files: List[str] = []
-
- for root, _, filenames in os.walk(path):
- for filename in filenames:
- files.append(os.path.join(root, filename))
-
- return files
-
-
def is_path_exists(path: str) -> bool:
return os.path.exists(path)
@@ -98,3 +68,11 @@ def load_json(txt: str) -> Optional[dict]:
def change_filename_extension(filename: str, extension: str) -> str:
base_name, _ = os.path.splitext(filename)
return f'{base_name}.{extension}'
+
+
+def concat_unique_id(filename: str, unique_id: str) -> str:
+ if filename.startswith(os.sep):
+ # remove leading slash to join the path correctly
+ filename = filename[len(os.sep) :]
+
+ return os.path.join(unique_id, filename)
diff --git a/cycode/cli/utils/progress_bar.py b/cycode/cli/utils/progress_bar.py
index 083d0715..b0e94d92 100644
--- a/cycode/cli/utils/progress_bar.py
+++ b/cycode/cli/utils/progress_bar.py
@@ -16,15 +16,11 @@
class ProgressBarSection(AutoCountEnum):
- PREPARE_LOCAL_FILES = auto()
- SCAN = auto()
- GENERATE_REPORT = auto()
-
def has_next(self) -> bool:
- return self.value < len(ProgressBarSection) - 1
+ return self.value < len(type(self)) - 1
def next(self) -> 'ProgressBarSection':
- return ProgressBarSection(self.value + 1)
+ return type(self)(self.value + 1)
class ProgressBarSectionInfo(NamedTuple):
@@ -32,25 +28,62 @@ class ProgressBarSectionInfo(NamedTuple):
label: str
start_percent: int
stop_percent: int
+ initial: bool = False
_PROGRESS_BAR_LENGTH = 100
-_PROGRESS_BAR_SECTIONS = {
- ProgressBarSection.PREPARE_LOCAL_FILES: ProgressBarSectionInfo(
- ProgressBarSection.PREPARE_LOCAL_FILES, 'Prepare local files', start_percent=0, stop_percent=5
+ProgressBarSections = Dict[ProgressBarSection, ProgressBarSectionInfo]
+
+
+class ScanProgressBarSection(ProgressBarSection):
+ PREPARE_LOCAL_FILES = auto()
+ SCAN = auto()
+ GENERATE_REPORT = auto()
+
+
+SCAN_PROGRESS_BAR_SECTIONS: ProgressBarSections = {
+ ScanProgressBarSection.PREPARE_LOCAL_FILES: ProgressBarSectionInfo(
+ ScanProgressBarSection.PREPARE_LOCAL_FILES, 'Prepare local files', start_percent=0, stop_percent=5, initial=True
+ ),
+ ScanProgressBarSection.SCAN: ProgressBarSectionInfo(
+ ScanProgressBarSection.SCAN, 'Scan in progress', start_percent=5, stop_percent=95
+ ),
+ ScanProgressBarSection.GENERATE_REPORT: ProgressBarSectionInfo(
+ ScanProgressBarSection.GENERATE_REPORT, 'Generate report', start_percent=95, stop_percent=100
+ ),
+}
+
+
+class SbomReportProgressBarSection(ProgressBarSection):
+ PREPARE_LOCAL_FILES = auto()
+ GENERATION = auto()
+ RECEIVE_REPORT = auto()
+
+
+SBOM_REPORT_PROGRESS_BAR_SECTIONS: ProgressBarSections = {
+ SbomReportProgressBarSection.PREPARE_LOCAL_FILES: ProgressBarSectionInfo(
+ SbomReportProgressBarSection.PREPARE_LOCAL_FILES,
+ 'Prepare local files',
+ start_percent=0,
+ stop_percent=30,
+ initial=True,
),
- ProgressBarSection.SCAN: ProgressBarSectionInfo(
- ProgressBarSection.SCAN, 'Scan in progress', start_percent=5, stop_percent=95
+ SbomReportProgressBarSection.GENERATION: ProgressBarSectionInfo(
+ SbomReportProgressBarSection.GENERATION, 'Report generation in progress', start_percent=30, stop_percent=90
),
- ProgressBarSection.GENERATE_REPORT: ProgressBarSectionInfo(
- ProgressBarSection.GENERATE_REPORT, 'Generate report', start_percent=95, stop_percent=100
+ SbomReportProgressBarSection.RECEIVE_REPORT: ProgressBarSectionInfo(
+ SbomReportProgressBarSection.RECEIVE_REPORT, 'Receive report', start_percent=90, stop_percent=100
),
}
-def _get_section_length(section: 'ProgressBarSection') -> int:
- return _PROGRESS_BAR_SECTIONS[section].stop_percent - _PROGRESS_BAR_SECTIONS[section].start_percent
+def _get_initial_section(progress_bar_sections: ProgressBarSections) -> ProgressBarSectionInfo:
+ for section in progress_bar_sections.values():
+ if section.initial:
+ return section
+
+ raise ValueError('No initial section found')
class BaseProgressBar(ABC):
@@ -75,13 +108,17 @@ def stop(self) -> None:
...
@abstractmethod
- def set_section_length(self, section: 'ProgressBarSection', length: int) -> None:
+ def set_section_length(self, section: 'ProgressBarSection', length: int = 0) -> None:
...
@abstractmethod
def update(self, section: 'ProgressBarSection') -> None:
...
+ @abstractmethod
+ def update_label(self, label: Optional[str] = None) -> None:
+ ...
+
class DummyProgressBar(BaseProgressBar):
def __init__(self, *args, **kwargs) -> None:
@@ -99,16 +136,22 @@ def start(self) -> None:
def stop(self) -> None:
pass
- def set_section_length(self, section: 'ProgressBarSection', length: int) -> None:
+ def set_section_length(self, section: 'ProgressBarSection', length: int = 0) -> None:
pass
def update(self, section: 'ProgressBarSection') -> None:
pass
+ def update_label(self, label: Optional[str] = None) -> None:
+ pass
+
class CompositeProgressBar(BaseProgressBar):
- def __init__(self) -> None:
+ def __init__(self, progress_bar_sections: ProgressBarSections) -> None:
super().__init__()
+
+ self._progress_bar_sections = progress_bar_sections
+
self._progress_bar_context_manager = click.progressbar(
length=_PROGRESS_BAR_LENGTH,
item_show_func=self._progress_bar_item_show_func,
@@ -121,7 +164,7 @@ def __init__(self) -> None:
self._section_values: Dict[ProgressBarSection, int] = {}
self._current_section_value = 0
- self._current_section: ProgressBarSectionInfo = _PROGRESS_BAR_SECTIONS[ProgressBarSection.PREPARE_LOCAL_FILES]
+ self._current_section: ProgressBarSectionInfo = _get_initial_section(self._progress_bar_sections)
def __enter__(self) -> 'CompositeProgressBar':
self._progress_bar = self._progress_bar_context_manager.__enter__()
@@ -140,7 +183,7 @@ def stop(self) -> None:
if self._run:
self.__exit__(None, None, None)
- def set_section_length(self, section: 'ProgressBarSection', length: int) -> None:
+ def set_section_length(self, section: 'ProgressBarSection', length: int = 0) -> None:
logger.debug(f'set_section_length: {section} {length}')
self._section_lengths[section] = length
@@ -149,8 +192,12 @@ def set_section_length(self, section: 'ProgressBarSection', length: int) -> None
else:
self._maybe_update_current_section()
+ def _get_section_length(self, section: 'ProgressBarSection') -> int:
+ section_info = self._progress_bar_sections[section]
+ return section_info.stop_percent - section_info.start_percent
+
def _skip_section(self, section: 'ProgressBarSection') -> None:
- self._progress_bar.update(_get_section_length(section))
+ self._progress_bar.update(self._get_section_length(section))
self._maybe_update_current_section()
def _increment_section_value(self, section: 'ProgressBarSection', value: int) -> None:
@@ -164,7 +211,7 @@ def _rerender_progress_bar(self) -> None:
"""Used to update label right after changing the progress bar section."""
self._progress_bar.update(0)
- def _increment_progress(self, section: ProgressBarSection) -> None:
+ def _increment_progress(self, section: 'ProgressBarSection') -> None:
increment_value = self._get_increment_progress_value(section)
self._current_section_value += increment_value
@@ -177,7 +224,7 @@ def _maybe_update_current_section(self) -> None:
max_val = self._section_lengths.get(self._current_section.section, 0)
cur_val = self._section_values.get(self._current_section.section, 0)
if cur_val >= max_val:
- next_section = _PROGRESS_BAR_SECTIONS[self._current_section.section.next()]
+ next_section = self._progress_bar_sections[self._current_section.section.next()]
logger.debug(f'_update_current_section: {self._current_section.section} -> {next_section.section}')
self._current_section = next_section
@@ -188,7 +235,7 @@ def _get_increment_progress_value(self, section: 'ProgressBarSection') -> int:
max_val = self._section_lengths[section]
cur_val = self._section_values[section]
- expected_value = round(_get_section_length(section) * (cur_val / max_val))
+ expected_value = round(self._get_section_length(section) * (cur_val / max_val))
return expected_value - self._current_section_value
@@ -210,12 +257,19 @@ def update(self, section: 'ProgressBarSection', value: int = 1) -> None:
self._increment_progress(section)
self._maybe_update_current_section()
+ def update_label(self, label: Optional[str] = None) -> None:
+ if not self._progress_bar:
+ raise ValueError('Progress bar is not initialized. Call start() first or use "with" statement.')
+
+ self._progress_bar.label = label or ''
+ self._progress_bar.render_progress()
-def get_progress_bar(*, hidden: bool) -> BaseProgressBar:
+
+def get_progress_bar(*, hidden: bool, sections: ProgressBarSections) -> BaseProgressBar:
if hidden:
return DummyProgressBar()
- return CompositeProgressBar()
+ return CompositeProgressBar(sections)
if __name__ == '__main__':
@@ -223,15 +277,18 @@ def get_progress_bar(*, hidden: bool) -> BaseProgressBar:
import random
import time
- bar = get_progress_bar(hidden=False)
+ bar = get_progress_bar(hidden=False, sections=SCAN_PROGRESS_BAR_SECTIONS)
bar.start()
- for bar_section in ProgressBarSection:
+ for bar_section in ScanProgressBarSection:
section_capacity = random.randint(500, 1000) # noqa: S311
bar.set_section_length(bar_section, section_capacity)
for _i in range(section_capacity):
time.sleep(0.01)
+ bar.update_label(f'{bar_section} {_i}/{section_capacity}')
bar.update(bar_section)
+ bar.update_label()
+
bar.stop()
diff --git a/cycode/cli/utils/scan_batch.py b/cycode/cli/utils/scan_batch.py
index 4c839440..ede229e2 100644
--- a/cycode/cli/utils/scan_batch.py
+++ b/cycode/cli/utils/scan_batch.py
@@ -9,7 +9,7 @@
SCAN_BATCH_SCANS_PER_CPU,
)
from cycode.cli.models import Document
-from cycode.cli.utils.progress_bar import ProgressBarSection
+from cycode.cli.utils.progress_bar import ScanProgressBarSection
if TYPE_CHECKING:
from cycode.cli.models import CliError, LocalScanResult
@@ -56,7 +56,7 @@ def run_parallel_batched_scan(
max_files_count: int = SCAN_BATCH_MAX_FILES_COUNT,
) -> Tuple[Dict[str, 'CliError'], List['LocalScanResult']]:
batches = split_documents_into_batches(documents, max_size_mb, max_files_count)
- progress_bar.set_section_length(ProgressBarSection.SCAN, len(batches)) # * 3
+ progress_bar.set_section_length(ScanProgressBarSection.SCAN, len(batches)) # * 3
# TODO(MarshalX): we should multiply the count of batches in SCAN section because each batch has 3 steps:
# 1. scan creation
# 2. scan completion
@@ -73,6 +73,6 @@ def run_parallel_batched_scan(
if err:
cli_errors[scan_id] = err
- progress_bar.update(ProgressBarSection.SCAN)
+ progress_bar.update(ScanProgressBarSection.SCAN)
return cli_errors, local_scan_results
diff --git a/cycode/cyclient/client_creator.py b/cycode/cyclient/client_creator.py
new file mode 100644
index 00000000..da62bd5a
--- /dev/null
+++ b/cycode/cyclient/client_creator.py
@@ -0,0 +1,23 @@
+from cycode.cyclient.config import dev_mode
+from cycode.cyclient.config_dev import DEV_CYCODE_API_URL
+from cycode.cyclient.cycode_dev_based_client import CycodeDevBasedClient
+from cycode.cyclient.cycode_token_based_client import CycodeTokenBasedClient
+from cycode.cyclient.report_client import ReportClient
+from cycode.cyclient.scan_client import ScanClient
+from cycode.cyclient.scan_config_base import DefaultScanConfig, DevScanConfig
+
+
+def create_scan_client(client_id: str, client_secret: str, hide_response_log: bool) -> ScanClient:
+ if dev_mode:
+ client = CycodeDevBasedClient(DEV_CYCODE_API_URL)
+ scan_config = DevScanConfig()
+ else:
+ client = CycodeTokenBasedClient(client_id, client_secret)
+ scan_config = DefaultScanConfig()
+
+ return ScanClient(client, scan_config, hide_response_log)
+
+
+def create_report_client(client_id: str, client_secret: str, hide_response_log: bool) -> ReportClient:
+ client = CycodeDevBasedClient(DEV_CYCODE_API_URL) if dev_mode else CycodeTokenBasedClient(client_id, client_secret)
+ return ReportClient(client, hide_response_log)
diff --git a/cycode/cyclient/models.py b/cycode/cyclient/models.py
index f5983083..0401e3fb 100644
--- a/cycode/cyclient/models.py
+++ b/cycode/cyclient/models.py
@@ -344,3 +344,63 @@ def user_agent_suffix(self) -> str:
f'EnvName: {self.env_name}; EnvVersion: {self.env_version}'
f')'
)
+
+
+@dataclass
+class SbomReportStorageDetails:
+ path: str
+ folder: str
+ size: int
+
+
+class SbomReportStorageDetailsSchema(Schema):
+ class Meta:
+ unknown = EXCLUDE
+
+ path = fields.String()
+ folder = fields.String()
+ size = fields.Integer()
+
+ @post_load
+ def build_dto(self, data: Dict[str, Any], **_) -> SbomReportStorageDetails:
+ return SbomReportStorageDetails(**data)
+
+
+@dataclass
+class ReportExecution:
+ id: int
+ status: str
+ error_message: Optional[str] = None
+ status_message: Optional[str] = None
+ storage_details: Optional[SbomReportStorageDetails] = None
+
+
+class ReportExecutionSchema(Schema):
+ class Meta:
+ unknown = EXCLUDE
+
+ id = fields.Integer()
+ status = fields.String()
+ error_message = fields.String(allow_none=True)
+ status_message = fields.String(allow_none=True)
+ storage_details = fields.Nested(SbomReportStorageDetailsSchema, allow_none=True)
+
+ @post_load
+ def build_dto(self, data: Dict[str, Any], **_) -> ReportExecution:
+ return ReportExecution(**data)
+
+
+@dataclass
+class SbomReport:
+ report_executions: List[ReportExecution]
+
+
+class RequestedSbomReportResultSchema(Schema):
+ class Meta:
+ unknown = EXCLUDE
+
+ report_executions = fields.List(fields.Nested(ReportExecutionSchema))
+
+ @post_load
+ def build_dto(self, data: Dict[str, Any], **_) -> SbomReport:
+ return SbomReport(**data)
diff --git a/cycode/cyclient/report_client.py b/cycode/cyclient/report_client.py
new file mode 100644
index 00000000..ade7d850
--- /dev/null
+++ b/cycode/cyclient/report_client.py
@@ -0,0 +1,101 @@
+import dataclasses
+import json
+from typing import List, Optional
+
+from requests import Response
+
+from cycode.cli.exceptions.custom_exceptions import CycodeError
+from cycode.cli.files_collector.models.in_memory_zip import InMemoryZip
+from cycode.cyclient import models
+from cycode.cyclient.cycode_client_base import CycodeClientBase
+
+
+@dataclasses.dataclass
+class ReportParameters:
+ entity_type: str
+ sbom_report_type: str
+ sbom_version: str
+ output_format: str
+ include_vulnerabilities: bool
+ include_dev_dependencies: bool
+
+ def to_dict(self, *, without_entity_type: bool) -> dict:
+ model_dict = dataclasses.asdict(self)
+ if without_entity_type:
+ del model_dict['entity_type']
+ return model_dict
+
+ def to_json(self, *, without_entity_type: bool) -> str:
+ return json.dumps(self.to_dict(without_entity_type=without_entity_type))
+
+
+class ReportClient:
+ SERVICE_NAME: str = 'report'
+ CREATE_SBOM_REPORT_REQUEST_PATH: str = 'api/v2/report/{report_type}/sbom'
+ GET_EXECUTIONS_STATUS_PATH: str = 'api/v2/report/executions'
+ REPORT_STATUS_PATH: str = 'api/v2/report/{report_execution_id}/status'
+
+ DOWNLOAD_REPORT_PATH: str = 'files/api/v1/file/sbom/{file_name}' # not in the report service
+
+ def __init__(self, client: CycodeClientBase, hide_response_log: bool = True) -> None:
+ self.client = client
+ self._hide_response_log = hide_response_log
+
+ def request_sbom_report_execution(
+ self, params: ReportParameters, zip_file: InMemoryZip = None, repository_url: Optional[str] = None
+ ) -> models.ReportExecution:
+ report_type = 'zipped-file' if zip_file else 'repository-url'
+ url_path = f'{self.SERVICE_NAME}/{self.CREATE_SBOM_REPORT_REQUEST_PATH}'.format(report_type=report_type)
+
+ # entity type required only for zipped-file
+ request_data = {'report_parameters': params.to_json(without_entity_type=zip_file is None)}
+ if repository_url:
+ request_data['repository_url'] = repository_url
+
+ request_args = {
+ 'url_path': url_path,
+ 'data': request_data,
+ 'hide_response_content_log': self._hide_response_log,
+ }
+
+ if zip_file:
+ request_args['files'] = {'file': ('sca_files.zip', zip_file.read())}
+
+ response = self.client.post(**request_args)
+ sbom_report = self.parse_requested_sbom_report_response(response)
+ if not sbom_report.report_executions:
+ raise CycodeError('Failed to get SBOM report. No executions found.')
+
+ return sbom_report.report_executions[0]
+
+ def get_report_execution(self, report_execution_id: int) -> models.ReportExecutionSchema:
+ url_path = f'{self.SERVICE_NAME}/{self.GET_EXECUTIONS_STATUS_PATH}'
+ params = {
+ 'executions_ids': report_execution_id,
+ 'include_orphan_executions': True,
+ }
+ response = self.client.get(url_path=url_path, params=params)
+
+ report_executions = self.parse_execution_status_response(response)
+ if not report_executions:
+ raise CycodeError('Failed to get report execution.')
+
+ return report_executions[0]
+
+ def get_file_content(self, file_name: str) -> str:
+ response = self.client.get(
+ url_path=self.DOWNLOAD_REPORT_PATH.format(file_name=file_name), params={'include_hidden': True}
+ )
+ return response.text
+
+ def report_status(self, report_execution_id: int, status: dict) -> None:
+ url_path = f'{self.SERVICE_NAME}/{self.REPORT_STATUS_PATH}'.format(report_execution_id=report_execution_id)
+ self.client.post(url_path=url_path, body=status)
+
+ @staticmethod
+ def parse_requested_sbom_report_response(response: Response) -> models.SbomReport:
+ return models.RequestedSbomReportResultSchema().load(response.json())
+
+ @staticmethod
+ def parse_execution_status_response(response: Response) -> List[models.ReportExecutionSchema]:
+ return models.ReportExecutionSchema().load(response.json(), many=True)
diff --git a/cycode/cyclient/scan_client.py b/cycode/cyclient/scan_client.py
index f09a96ef..5830e9dc 100644
--- a/cycode/cyclient/scan_client.py
+++ b/cycode/cyclient/scan_client.py
@@ -1,18 +1,19 @@
import json
-from typing import List, Optional
+from typing import TYPE_CHECKING, List, Optional
from requests import Response
-from cycode.cli.zip_file import InMemoryZip
+from cycode.cli.files_collector.models.in_memory_zip import InMemoryZip
+from cycode.cyclient import models
+from cycode.cyclient.cycode_client_base import CycodeClientBase
-from . import models
-from .cycode_client_base import CycodeClientBase
-from .scan_config.scan_config_base import ScanConfigBase
+if TYPE_CHECKING:
+ from .scan_config_base import ScanConfigBase
class ScanClient:
def __init__(
- self, scan_cycode_client: CycodeClientBase, scan_config: ScanConfigBase, hide_response_log: bool = True
+ self, scan_cycode_client: CycodeClientBase, scan_config: 'ScanConfigBase', hide_response_log: bool = True
) -> None:
self.scan_cycode_client = scan_cycode_client
self.scan_config = scan_config
diff --git a/cycode/cyclient/scan_config/scan_config_creator.py b/cycode/cyclient/scan_config/scan_config_creator.py
deleted file mode 100644
index f17be424..00000000
--- a/cycode/cyclient/scan_config/scan_config_creator.py
+++ /dev/null
@@ -1,29 +0,0 @@
-from typing import Tuple
-
-from cycode.cyclient.config import dev_mode
-from cycode.cyclient.config_dev import DEV_CYCODE_API_URL
-from cycode.cyclient.cycode_dev_based_client import CycodeDevBasedClient
-from cycode.cyclient.cycode_token_based_client import CycodeTokenBasedClient
-from cycode.cyclient.scan_client import ScanClient
-from cycode.cyclient.scan_config.scan_config_base import DefaultScanConfig, DevScanConfig
-
-
-def create_scan_client(client_id: str, client_secret: str, hide_response_log: bool) -> ScanClient:
- if dev_mode:
- scan_cycode_client, scan_config = create_scan_for_dev_env()
- else:
- scan_cycode_client, scan_config = create_scan(client_id, client_secret)
-
- return ScanClient(scan_cycode_client, scan_config, hide_response_log)
-
-
-def create_scan(client_id: str, client_secret: str) -> Tuple[CycodeTokenBasedClient, DefaultScanConfig]:
- scan_cycode_client = CycodeTokenBasedClient(client_id, client_secret)
- scan_config = DefaultScanConfig()
- return scan_cycode_client, scan_config
-
-
-def create_scan_for_dev_env() -> Tuple[CycodeDevBasedClient, DevScanConfig]:
- scan_cycode_client = CycodeDevBasedClient(DEV_CYCODE_API_URL)
- scan_config = DevScanConfig()
- return scan_cycode_client, scan_config
diff --git a/cycode/cyclient/scan_config/scan_config_base.py b/cycode/cyclient/scan_config_base.py
similarity index 100%
rename from cycode/cyclient/scan_config/scan_config_base.py
rename to cycode/cyclient/scan_config_base.py
diff --git a/tests/cli/helpers/test_tf_content_generator.py b/tests/cli/helpers/test_tf_content_generator.py
index ae19b2f6..7953ed81 100644
--- a/tests/cli/helpers/test_tf_content_generator.py
+++ b/tests/cli/helpers/test_tf_content_generator.py
@@ -1,6 +1,6 @@
import os
-from cycode.cli.helpers import tf_content_generator
+from cycode.cli.files_collector.iac import tf_content_generator
from cycode.cli.utils.path_utils import get_file_content, get_immediate_subdirectories
from tests.conftest import TEST_FILES_PATH
diff --git a/tests/cli/test_code_scanner.py b/tests/cli/test_code_scanner.py
index b715e9c6..f4fe4f69 100644
--- a/tests/cli/test_code_scanner.py
+++ b/tests/cli/test_code_scanner.py
@@ -8,8 +8,10 @@
from requests import Response
from cycode.cli import consts
-from cycode.cli.code_scanner import _generate_document, _handle_exception, _is_file_relevant_for_sca_scan
+from cycode.cli.code_scanner import _handle_exception
from cycode.cli.exceptions import custom_exceptions
+from cycode.cli.files_collector.excluder import _is_file_relevant_for_sca_scan
+from cycode.cli.files_collector.path_documents import _generate_document
from cycode.cli.models import Document
if TYPE_CHECKING:
diff --git a/tests/conftest.py b/tests/conftest.py
index a763f6bb..fdb02ec2 100644
--- a/tests/conftest.py
+++ b/tests/conftest.py
@@ -3,9 +3,9 @@
import pytest
import responses
+from cycode.cyclient.client_creator import create_scan_client
from cycode.cyclient.cycode_token_based_client import CycodeTokenBasedClient
from cycode.cyclient.scan_client import ScanClient
-from cycode.cyclient.scan_config.scan_config_creator import create_scan_client
_EXPECTED_API_TOKEN = 'someJWT'
diff --git a/tests/cyclient/scan_config/test_default_scan_config.py b/tests/cyclient/scan_config/test_default_scan_config.py
index 0945402b..e0a84ad2 100644
--- a/tests/cyclient/scan_config/test_default_scan_config.py
+++ b/tests/cyclient/scan_config/test_default_scan_config.py
@@ -1,4 +1,4 @@
-from cycode.cyclient.scan_config.scan_config_creator import DefaultScanConfig
+from cycode.cyclient.scan_config_base import DefaultScanConfig
def test_get_service_name() -> None:
diff --git a/tests/cyclient/scan_config/test_dev_scan_config.py b/tests/cyclient/scan_config/test_dev_scan_config.py
index 0673d601..3ea3127e 100644
--- a/tests/cyclient/scan_config/test_dev_scan_config.py
+++ b/tests/cyclient/scan_config/test_dev_scan_config.py
@@ -1,4 +1,4 @@
-from cycode.cyclient.scan_config.scan_config_creator import DevScanConfig
+from cycode.cyclient.scan_config_base import DevScanConfig
def test_get_service_name() -> None:
diff --git a/tests/cyclient/test_scan_client.py b/tests/cyclient/test_scan_client.py
index db867a9f..2ca374b2 100644
--- a/tests/cyclient/test_scan_client.py
+++ b/tests/cyclient/test_scan_client.py
@@ -8,11 +8,11 @@
from requests import Timeout
from requests.exceptions import ProxyError
-from cycode.cli.code_scanner import zip_documents_to_scan
+from cycode.cli.code_scanner import zip_documents
from cycode.cli.config import config
from cycode.cli.exceptions.custom_exceptions import CycodeError, HttpUnauthorizedError
+from cycode.cli.files_collector.models.in_memory_zip import InMemoryZip
from cycode.cli.models import Document
-from cycode.cli.zip_file import InMemoryZip
from cycode.cyclient.scan_client import ScanClient
from tests.conftest import TEST_FILES_PATH
@@ -42,7 +42,7 @@ def get_test_zip_file(scan_type: str) -> InMemoryZip:
with open(path, 'r', encoding='UTF-8') as f:
test_documents.append(Document(path, f.read(), is_git_diff_format=False))
- return zip_documents_to_scan(scan_type, InMemoryZip(), test_documents)
+ return zip_documents(scan_type, test_documents)
def get_zipped_file_scan_response(url: str, scan_id: Optional[UUID] = None) -> responses.Response:
diff --git a/tests/test_code_scanner.py b/tests/test_code_scanner.py
index b1f7e163..6eb494e9 100644
--- a/tests/test_code_scanner.py
+++ b/tests/test_code_scanner.py
@@ -1,9 +1,9 @@
import os
-from cycode.cli import code_scanner
+from cycode.cli.files_collector.excluder import _is_relevant_file_to_scan
from tests.conftest import TEST_FILES_PATH
def test_is_relevant_file_to_scan_sca() -> None:
path = os.path.join(TEST_FILES_PATH, 'package.json')
- assert code_scanner._is_relevant_file_to_scan('sca', path) is True
+ assert _is_relevant_file_to_scan('sca', path) is True
diff --git a/tests/test_zip_file.py b/tests/test_zip_file.py
index f73514c8..15c53c17 100644
--- a/tests/test_zip_file.py
+++ b/tests/test_zip_file.py
@@ -1,6 +1,6 @@
import os
-from cycode.cli import zip_file
+from cycode.cli.utils.path_utils import concat_unique_id
def test_concat_unique_id_to_file_with_leading_slash() -> None:
@@ -10,7 +10,7 @@ def test_concat_unique_id_to_file_with_leading_slash() -> None:
expected_path = os.path.join(unique_id, filename)
filename = os.sep + filename
- assert zip_file.concat_unique_id(filename, unique_id) == expected_path
+ assert concat_unique_id(filename, unique_id) == expected_path
def test_concat_unique_id_to_file_without_leading_slash() -> None:
@@ -19,4 +19,4 @@ def test_concat_unique_id_to_file_without_leading_slash() -> None:
expected_path = os.path.join(unique_id, *filename.split('/'))
- assert zip_file.concat_unique_id(filename, unique_id) == expected_path
+ assert concat_unique_id(filename, unique_id) == expected_path
From 5e10e073551ba4be20b844c94905027d83da3e05 Mon Sep 17 00:00:00 2001
From: Ilya Siamionau
Date: Mon, 9 Oct 2023 19:31:01 +0200
Subject: [PATCH 034/257] CM-27780 - Support Python 3.12 (#166)
---
.github/workflows/tests_full.yml | 2 +-
poetry.lock | 531 ++++++++++++++++---------------
pyproject.toml | 5 +-
3 files changed, 283 insertions(+), 255 deletions(-)
diff --git a/.github/workflows/tests_full.yml b/.github/workflows/tests_full.yml
index efd8226f..aa2c0fc2 100644
--- a/.github/workflows/tests_full.yml
+++ b/.github/workflows/tests_full.yml
@@ -13,7 +13,7 @@ jobs:
strategy:
matrix:
os: [ macos-latest, ubuntu-latest, windows-latest ]
- python-version: [ "3.7", "3.8", "3.9", "3.10", "3.11" ]
+ python-version: [ "3.7", "3.8", "3.9", "3.10", "3.11", "3.12" ]
runs-on: ${{matrix.os}}
diff --git a/poetry.lock b/poetry.lock
index 46104e63..a6a0126b 100644
--- a/poetry.lock
+++ b/poetry.lock
@@ -2,13 +2,13 @@
[[package]]
name = "altgraph"
-version = "0.17.3"
+version = "0.17.4"
description = "Python graph (network) package"
optional = false
python-versions = "*"
files = [
- {file = "altgraph-0.17.3-py2.py3-none-any.whl", hash = "sha256:c8ac1ca6772207179ed8003ce7687757c04b0b71536f81e2ac5755c6226458fe"},
- {file = "altgraph-0.17.3.tar.gz", hash = "sha256:ad33358114df7c9416cdb8fa1eaa5852166c505118717021c6a8c7c7abbd03dd"},
+ {file = "altgraph-0.17.4-py2.py3-none-any.whl", hash = "sha256:642743b4750de17e655e6711601b077bc6598dbfa3ba5fa2b2a35ce12b508dff"},
+ {file = "altgraph-0.17.4.tar.gz", hash = "sha256:1b5afbb98f6c4dcadb2e2ae6ab9fa994bbb8c1d75f4fa96d340f9437ae454406"},
]
[[package]]
@@ -102,108 +102,123 @@ files = [
[[package]]
name = "chardet"
-version = "5.1.0"
+version = "5.2.0"
description = "Universal encoding detector for Python 3"
optional = false
python-versions = ">=3.7"
files = [
- {file = "chardet-5.1.0-py3-none-any.whl", hash = "sha256:362777fb014af596ad31334fde1e8c327dfdb076e1960d1694662d46a6917ab9"},
- {file = "chardet-5.1.0.tar.gz", hash = "sha256:0d62712b956bc154f85fb0a266e2a3c5913c2967e00348701b32411d6def31e5"},
+ {file = "chardet-5.2.0-py3-none-any.whl", hash = "sha256:e1cf59446890a00105fe7b7912492ea04b6e6f06d4b742b2c788469e34c82970"},
+ {file = "chardet-5.2.0.tar.gz", hash = "sha256:1b3b6ff479a8c414bc3fa2c0852995695c4a026dcd6d0633b2dd092ca39c1cf7"},
]
[[package]]
name = "charset-normalizer"
-version = "3.1.0"
+version = "3.3.0"
description = "The Real First Universal Charset Detector. Open, modern and actively maintained alternative to Chardet."
optional = false
python-versions = ">=3.7.0"
files = [
- {file = "charset-normalizer-3.1.0.tar.gz", hash = "sha256:34e0a2f9c370eb95597aae63bf85eb5e96826d81e3dcf88b8886012906f509b5"},
- {file = "charset_normalizer-3.1.0-cp310-cp310-macosx_10_9_universal2.whl", hash = "sha256:e0ac8959c929593fee38da1c2b64ee9778733cdf03c482c9ff1d508b6b593b2b"},
- {file = "charset_normalizer-3.1.0-cp310-cp310-macosx_10_9_x86_64.whl", hash = "sha256:d7fc3fca01da18fbabe4625d64bb612b533533ed10045a2ac3dd194bfa656b60"},
- {file = "charset_normalizer-3.1.0-cp310-cp310-macosx_11_0_arm64.whl", hash = "sha256:04eefcee095f58eaabe6dc3cc2262f3bcd776d2c67005880894f447b3f2cb9c1"},
- {file = "charset_normalizer-3.1.0-cp310-cp310-manylinux_2_17_aarch64.manylinux2014_aarch64.whl", hash = "sha256:20064ead0717cf9a73a6d1e779b23d149b53daf971169289ed2ed43a71e8d3b0"},
- {file = "charset_normalizer-3.1.0-cp310-cp310-manylinux_2_17_ppc64le.manylinux2014_ppc64le.whl", hash = "sha256:1435ae15108b1cb6fffbcea2af3d468683b7afed0169ad718451f8db5d1aff6f"},
- {file = "charset_normalizer-3.1.0-cp310-cp310-manylinux_2_17_s390x.manylinux2014_s390x.whl", hash = "sha256:c84132a54c750fda57729d1e2599bb598f5fa0344085dbde5003ba429a4798c0"},
- {file = "charset_normalizer-3.1.0-cp310-cp310-manylinux_2_17_x86_64.manylinux2014_x86_64.whl", hash = "sha256:75f2568b4189dda1c567339b48cba4ac7384accb9c2a7ed655cd86b04055c795"},
- {file = "charset_normalizer-3.1.0-cp310-cp310-manylinux_2_5_i686.manylinux1_i686.manylinux_2_17_i686.manylinux2014_i686.whl", hash = "sha256:11d3bcb7be35e7b1bba2c23beedac81ee893ac9871d0ba79effc7fc01167db6c"},
- {file = "charset_normalizer-3.1.0-cp310-cp310-musllinux_1_1_aarch64.whl", hash = "sha256:891cf9b48776b5c61c700b55a598621fdb7b1e301a550365571e9624f270c203"},
- {file = "charset_normalizer-3.1.0-cp310-cp310-musllinux_1_1_i686.whl", hash = "sha256:5f008525e02908b20e04707a4f704cd286d94718f48bb33edddc7d7b584dddc1"},
- {file = "charset_normalizer-3.1.0-cp310-cp310-musllinux_1_1_ppc64le.whl", hash = "sha256:b06f0d3bf045158d2fb8837c5785fe9ff9b8c93358be64461a1089f5da983137"},
- {file = "charset_normalizer-3.1.0-cp310-cp310-musllinux_1_1_s390x.whl", hash = "sha256:49919f8400b5e49e961f320c735388ee686a62327e773fa5b3ce6721f7e785ce"},
- {file = "charset_normalizer-3.1.0-cp310-cp310-musllinux_1_1_x86_64.whl", hash = "sha256:22908891a380d50738e1f978667536f6c6b526a2064156203d418f4856d6e86a"},
- {file = "charset_normalizer-3.1.0-cp310-cp310-win32.whl", hash = "sha256:12d1a39aa6b8c6f6248bb54550efcc1c38ce0d8096a146638fd4738e42284448"},
- {file = "charset_normalizer-3.1.0-cp310-cp310-win_amd64.whl", hash = "sha256:65ed923f84a6844de5fd29726b888e58c62820e0769b76565480e1fdc3d062f8"},
- {file = "charset_normalizer-3.1.0-cp311-cp311-macosx_10_9_universal2.whl", hash = "sha256:9a3267620866c9d17b959a84dd0bd2d45719b817245e49371ead79ed4f710d19"},
- {file = "charset_normalizer-3.1.0-cp311-cp311-macosx_10_9_x86_64.whl", hash = "sha256:6734e606355834f13445b6adc38b53c0fd45f1a56a9ba06c2058f86893ae8017"},
- {file = "charset_normalizer-3.1.0-cp311-cp311-macosx_11_0_arm64.whl", hash = "sha256:f8303414c7b03f794347ad062c0516cee0e15f7a612abd0ce1e25caf6ceb47df"},
- {file = "charset_normalizer-3.1.0-cp311-cp311-manylinux_2_17_aarch64.manylinux2014_aarch64.whl", hash = "sha256:aaf53a6cebad0eae578f062c7d462155eada9c172bd8c4d250b8c1d8eb7f916a"},
- {file = "charset_normalizer-3.1.0-cp311-cp311-manylinux_2_17_ppc64le.manylinux2014_ppc64le.whl", hash = "sha256:3dc5b6a8ecfdc5748a7e429782598e4f17ef378e3e272eeb1340ea57c9109f41"},
- {file = "charset_normalizer-3.1.0-cp311-cp311-manylinux_2_17_s390x.manylinux2014_s390x.whl", hash = "sha256:e1b25e3ad6c909f398df8921780d6a3d120d8c09466720226fc621605b6f92b1"},
- {file = "charset_normalizer-3.1.0-cp311-cp311-manylinux_2_17_x86_64.manylinux2014_x86_64.whl", hash = "sha256:0ca564606d2caafb0abe6d1b5311c2649e8071eb241b2d64e75a0d0065107e62"},
- {file = "charset_normalizer-3.1.0-cp311-cp311-manylinux_2_5_i686.manylinux1_i686.manylinux_2_17_i686.manylinux2014_i686.whl", hash = "sha256:b82fab78e0b1329e183a65260581de4375f619167478dddab510c6c6fb04d9b6"},
- {file = "charset_normalizer-3.1.0-cp311-cp311-musllinux_1_1_aarch64.whl", hash = "sha256:bd7163182133c0c7701b25e604cf1611c0d87712e56e88e7ee5d72deab3e76b5"},
- {file = "charset_normalizer-3.1.0-cp311-cp311-musllinux_1_1_i686.whl", hash = "sha256:11d117e6c63e8f495412d37e7dc2e2fff09c34b2d09dbe2bee3c6229577818be"},
- {file = "charset_normalizer-3.1.0-cp311-cp311-musllinux_1_1_ppc64le.whl", hash = "sha256:cf6511efa4801b9b38dc5546d7547d5b5c6ef4b081c60b23e4d941d0eba9cbeb"},
- {file = "charset_normalizer-3.1.0-cp311-cp311-musllinux_1_1_s390x.whl", hash = "sha256:abc1185d79f47c0a7aaf7e2412a0eb2c03b724581139193d2d82b3ad8cbb00ac"},
- {file = "charset_normalizer-3.1.0-cp311-cp311-musllinux_1_1_x86_64.whl", hash = "sha256:cb7b2ab0188829593b9de646545175547a70d9a6e2b63bf2cd87a0a391599324"},
- {file = "charset_normalizer-3.1.0-cp311-cp311-win32.whl", hash = "sha256:c36bcbc0d5174a80d6cccf43a0ecaca44e81d25be4b7f90f0ed7bcfbb5a00909"},
- {file = "charset_normalizer-3.1.0-cp311-cp311-win_amd64.whl", hash = "sha256:cca4def576f47a09a943666b8f829606bcb17e2bc2d5911a46c8f8da45f56755"},
- {file = "charset_normalizer-3.1.0-cp37-cp37m-macosx_10_9_x86_64.whl", hash = "sha256:0c95f12b74681e9ae127728f7e5409cbbef9cd914d5896ef238cc779b8152373"},
- {file = "charset_normalizer-3.1.0-cp37-cp37m-manylinux_2_17_aarch64.manylinux2014_aarch64.whl", hash = "sha256:fca62a8301b605b954ad2e9c3666f9d97f63872aa4efcae5492baca2056b74ab"},
- {file = "charset_normalizer-3.1.0-cp37-cp37m-manylinux_2_17_ppc64le.manylinux2014_ppc64le.whl", hash = "sha256:ac0aa6cd53ab9a31d397f8303f92c42f534693528fafbdb997c82bae6e477ad9"},
- {file = "charset_normalizer-3.1.0-cp37-cp37m-manylinux_2_17_s390x.manylinux2014_s390x.whl", hash = "sha256:c3af8e0f07399d3176b179f2e2634c3ce9c1301379a6b8c9c9aeecd481da494f"},
- {file = "charset_normalizer-3.1.0-cp37-cp37m-manylinux_2_17_x86_64.manylinux2014_x86_64.whl", hash = "sha256:3a5fc78f9e3f501a1614a98f7c54d3969f3ad9bba8ba3d9b438c3bc5d047dd28"},
- {file = "charset_normalizer-3.1.0-cp37-cp37m-manylinux_2_5_i686.manylinux1_i686.manylinux_2_17_i686.manylinux2014_i686.whl", hash = "sha256:628c985afb2c7d27a4800bfb609e03985aaecb42f955049957814e0491d4006d"},
- {file = "charset_normalizer-3.1.0-cp37-cp37m-musllinux_1_1_aarch64.whl", hash = "sha256:74db0052d985cf37fa111828d0dd230776ac99c740e1a758ad99094be4f1803d"},
- {file = "charset_normalizer-3.1.0-cp37-cp37m-musllinux_1_1_i686.whl", hash = "sha256:1e8fcdd8f672a1c4fc8d0bd3a2b576b152d2a349782d1eb0f6b8e52e9954731d"},
- {file = "charset_normalizer-3.1.0-cp37-cp37m-musllinux_1_1_ppc64le.whl", hash = "sha256:04afa6387e2b282cf78ff3dbce20f0cc071c12dc8f685bd40960cc68644cfea6"},
- {file = "charset_normalizer-3.1.0-cp37-cp37m-musllinux_1_1_s390x.whl", hash = "sha256:dd5653e67b149503c68c4018bf07e42eeed6b4e956b24c00ccdf93ac79cdff84"},
- {file = "charset_normalizer-3.1.0-cp37-cp37m-musllinux_1_1_x86_64.whl", hash = "sha256:d2686f91611f9e17f4548dbf050e75b079bbc2a82be565832bc8ea9047b61c8c"},
- {file = "charset_normalizer-3.1.0-cp37-cp37m-win32.whl", hash = "sha256:4155b51ae05ed47199dc5b2a4e62abccb274cee6b01da5b895099b61b1982974"},
- {file = "charset_normalizer-3.1.0-cp37-cp37m-win_amd64.whl", hash = "sha256:322102cdf1ab682ecc7d9b1c5eed4ec59657a65e1c146a0da342b78f4112db23"},
- {file = "charset_normalizer-3.1.0-cp38-cp38-macosx_10_9_universal2.whl", hash = "sha256:e633940f28c1e913615fd624fcdd72fdba807bf53ea6925d6a588e84e1151531"},
- {file = "charset_normalizer-3.1.0-cp38-cp38-macosx_10_9_x86_64.whl", hash = "sha256:3a06f32c9634a8705f4ca9946d667609f52cf130d5548881401f1eb2c39b1e2c"},
- {file = "charset_normalizer-3.1.0-cp38-cp38-macosx_11_0_arm64.whl", hash = "sha256:7381c66e0561c5757ffe616af869b916c8b4e42b367ab29fedc98481d1e74e14"},
- {file = "charset_normalizer-3.1.0-cp38-cp38-manylinux_2_17_aarch64.manylinux2014_aarch64.whl", hash = "sha256:3573d376454d956553c356df45bb824262c397c6e26ce43e8203c4c540ee0acb"},
- {file = "charset_normalizer-3.1.0-cp38-cp38-manylinux_2_17_ppc64le.manylinux2014_ppc64le.whl", hash = "sha256:e89df2958e5159b811af9ff0f92614dabf4ff617c03a4c1c6ff53bf1c399e0e1"},
- {file = "charset_normalizer-3.1.0-cp38-cp38-manylinux_2_17_s390x.manylinux2014_s390x.whl", hash = "sha256:78cacd03e79d009d95635e7d6ff12c21eb89b894c354bd2b2ed0b4763373693b"},
- {file = "charset_normalizer-3.1.0-cp38-cp38-manylinux_2_17_x86_64.manylinux2014_x86_64.whl", hash = "sha256:de5695a6f1d8340b12a5d6d4484290ee74d61e467c39ff03b39e30df62cf83a0"},
- {file = "charset_normalizer-3.1.0-cp38-cp38-manylinux_2_5_i686.manylinux1_i686.manylinux_2_17_i686.manylinux2014_i686.whl", hash = "sha256:1c60b9c202d00052183c9be85e5eaf18a4ada0a47d188a83c8f5c5b23252f649"},
- {file = "charset_normalizer-3.1.0-cp38-cp38-musllinux_1_1_aarch64.whl", hash = "sha256:f645caaf0008bacf349875a974220f1f1da349c5dbe7c4ec93048cdc785a3326"},
- {file = "charset_normalizer-3.1.0-cp38-cp38-musllinux_1_1_i686.whl", hash = "sha256:ea9f9c6034ea2d93d9147818f17c2a0860d41b71c38b9ce4d55f21b6f9165a11"},
- {file = "charset_normalizer-3.1.0-cp38-cp38-musllinux_1_1_ppc64le.whl", hash = "sha256:80d1543d58bd3d6c271b66abf454d437a438dff01c3e62fdbcd68f2a11310d4b"},
- {file = "charset_normalizer-3.1.0-cp38-cp38-musllinux_1_1_s390x.whl", hash = "sha256:73dc03a6a7e30b7edc5b01b601e53e7fc924b04e1835e8e407c12c037e81adbd"},
- {file = "charset_normalizer-3.1.0-cp38-cp38-musllinux_1_1_x86_64.whl", hash = "sha256:6f5c2e7bc8a4bf7c426599765b1bd33217ec84023033672c1e9a8b35eaeaaaf8"},
- {file = "charset_normalizer-3.1.0-cp38-cp38-win32.whl", hash = "sha256:12a2b561af122e3d94cdb97fe6fb2bb2b82cef0cdca131646fdb940a1eda04f0"},
- {file = "charset_normalizer-3.1.0-cp38-cp38-win_amd64.whl", hash = "sha256:3160a0fd9754aab7d47f95a6b63ab355388d890163eb03b2d2b87ab0a30cfa59"},
- {file = "charset_normalizer-3.1.0-cp39-cp39-macosx_10_9_universal2.whl", hash = "sha256:38e812a197bf8e71a59fe55b757a84c1f946d0ac114acafaafaf21667a7e169e"},
- {file = "charset_normalizer-3.1.0-cp39-cp39-macosx_10_9_x86_64.whl", hash = "sha256:6baf0baf0d5d265fa7944feb9f7451cc316bfe30e8df1a61b1bb08577c554f31"},
- {file = "charset_normalizer-3.1.0-cp39-cp39-macosx_11_0_arm64.whl", hash = "sha256:8f25e17ab3039b05f762b0a55ae0b3632b2e073d9c8fc88e89aca31a6198e88f"},
- {file = "charset_normalizer-3.1.0-cp39-cp39-manylinux_2_17_aarch64.manylinux2014_aarch64.whl", hash = "sha256:3747443b6a904001473370d7810aa19c3a180ccd52a7157aacc264a5ac79265e"},
- {file = "charset_normalizer-3.1.0-cp39-cp39-manylinux_2_17_ppc64le.manylinux2014_ppc64le.whl", hash = "sha256:b116502087ce8a6b7a5f1814568ccbd0e9f6cfd99948aa59b0e241dc57cf739f"},
- {file = "charset_normalizer-3.1.0-cp39-cp39-manylinux_2_17_s390x.manylinux2014_s390x.whl", hash = "sha256:d16fd5252f883eb074ca55cb622bc0bee49b979ae4e8639fff6ca3ff44f9f854"},
- {file = "charset_normalizer-3.1.0-cp39-cp39-manylinux_2_17_x86_64.manylinux2014_x86_64.whl", hash = "sha256:21fa558996782fc226b529fdd2ed7866c2c6ec91cee82735c98a197fae39f706"},
- {file = "charset_normalizer-3.1.0-cp39-cp39-manylinux_2_5_i686.manylinux1_i686.manylinux_2_17_i686.manylinux2014_i686.whl", hash = "sha256:6f6c7a8a57e9405cad7485f4c9d3172ae486cfef1344b5ddd8e5239582d7355e"},
- {file = "charset_normalizer-3.1.0-cp39-cp39-musllinux_1_1_aarch64.whl", hash = "sha256:ac3775e3311661d4adace3697a52ac0bab17edd166087d493b52d4f4f553f9f0"},
- {file = "charset_normalizer-3.1.0-cp39-cp39-musllinux_1_1_i686.whl", hash = "sha256:10c93628d7497c81686e8e5e557aafa78f230cd9e77dd0c40032ef90c18f2230"},
- {file = "charset_normalizer-3.1.0-cp39-cp39-musllinux_1_1_ppc64le.whl", hash = "sha256:6f4f4668e1831850ebcc2fd0b1cd11721947b6dc7c00bf1c6bd3c929ae14f2c7"},
- {file = "charset_normalizer-3.1.0-cp39-cp39-musllinux_1_1_s390x.whl", hash = "sha256:0be65ccf618c1e7ac9b849c315cc2e8a8751d9cfdaa43027d4f6624bd587ab7e"},
- {file = "charset_normalizer-3.1.0-cp39-cp39-musllinux_1_1_x86_64.whl", hash = "sha256:53d0a3fa5f8af98a1e261de6a3943ca631c526635eb5817a87a59d9a57ebf48f"},
- {file = "charset_normalizer-3.1.0-cp39-cp39-win32.whl", hash = "sha256:a04f86f41a8916fe45ac5024ec477f41f886b3c435da2d4e3d2709b22ab02af1"},
- {file = "charset_normalizer-3.1.0-cp39-cp39-win_amd64.whl", hash = "sha256:830d2948a5ec37c386d3170c483063798d7879037492540f10a475e3fd6f244b"},
- {file = "charset_normalizer-3.1.0-py3-none-any.whl", hash = "sha256:3d9098b479e78c85080c98e1e35ff40b4a31d8953102bb0fd7d1b6f8a2111a3d"},
+ {file = "charset-normalizer-3.3.0.tar.gz", hash = "sha256:63563193aec44bce707e0c5ca64ff69fa72ed7cf34ce6e11d5127555756fd2f6"},
+ {file = "charset_normalizer-3.3.0-cp310-cp310-macosx_10_9_universal2.whl", hash = "sha256:effe5406c9bd748a871dbcaf3ac69167c38d72db8c9baf3ff954c344f31c4cbe"},
+ {file = "charset_normalizer-3.3.0-cp310-cp310-macosx_10_9_x86_64.whl", hash = "sha256:4162918ef3098851fcd8a628bf9b6a98d10c380725df9e04caf5ca6dd48c847a"},
+ {file = "charset_normalizer-3.3.0-cp310-cp310-macosx_11_0_arm64.whl", hash = "sha256:0570d21da019941634a531444364f2482e8db0b3425fcd5ac0c36565a64142c8"},
+ {file = "charset_normalizer-3.3.0-cp310-cp310-manylinux_2_17_aarch64.manylinux2014_aarch64.whl", hash = "sha256:5707a746c6083a3a74b46b3a631d78d129edab06195a92a8ece755aac25a3f3d"},
+ {file = "charset_normalizer-3.3.0-cp310-cp310-manylinux_2_17_ppc64le.manylinux2014_ppc64le.whl", hash = "sha256:278c296c6f96fa686d74eb449ea1697f3c03dc28b75f873b65b5201806346a69"},
+ {file = "charset_normalizer-3.3.0-cp310-cp310-manylinux_2_17_s390x.manylinux2014_s390x.whl", hash = "sha256:a4b71f4d1765639372a3b32d2638197f5cd5221b19531f9245fcc9ee62d38f56"},
+ {file = "charset_normalizer-3.3.0-cp310-cp310-manylinux_2_17_x86_64.manylinux2014_x86_64.whl", hash = "sha256:f5969baeaea61c97efa706b9b107dcba02784b1601c74ac84f2a532ea079403e"},
+ {file = "charset_normalizer-3.3.0-cp310-cp310-manylinux_2_5_i686.manylinux1_i686.manylinux_2_17_i686.manylinux2014_i686.whl", hash = "sha256:a3f93dab657839dfa61025056606600a11d0b696d79386f974e459a3fbc568ec"},
+ {file = "charset_normalizer-3.3.0-cp310-cp310-musllinux_1_1_aarch64.whl", hash = "sha256:db756e48f9c5c607b5e33dd36b1d5872d0422e960145b08ab0ec7fd420e9d649"},
+ {file = "charset_normalizer-3.3.0-cp310-cp310-musllinux_1_1_i686.whl", hash = "sha256:232ac332403e37e4a03d209a3f92ed9071f7d3dbda70e2a5e9cff1c4ba9f0678"},
+ {file = "charset_normalizer-3.3.0-cp310-cp310-musllinux_1_1_ppc64le.whl", hash = "sha256:e5c1502d4ace69a179305abb3f0bb6141cbe4714bc9b31d427329a95acfc8bdd"},
+ {file = "charset_normalizer-3.3.0-cp310-cp310-musllinux_1_1_s390x.whl", hash = "sha256:2502dd2a736c879c0f0d3e2161e74d9907231e25d35794584b1ca5284e43f596"},
+ {file = "charset_normalizer-3.3.0-cp310-cp310-musllinux_1_1_x86_64.whl", hash = "sha256:23e8565ab7ff33218530bc817922fae827420f143479b753104ab801145b1d5b"},
+ {file = "charset_normalizer-3.3.0-cp310-cp310-win32.whl", hash = "sha256:1872d01ac8c618a8da634e232f24793883d6e456a66593135aeafe3784b0848d"},
+ {file = "charset_normalizer-3.3.0-cp310-cp310-win_amd64.whl", hash = "sha256:557b21a44ceac6c6b9773bc65aa1b4cc3e248a5ad2f5b914b91579a32e22204d"},
+ {file = "charset_normalizer-3.3.0-cp311-cp311-macosx_10_9_universal2.whl", hash = "sha256:d7eff0f27edc5afa9e405f7165f85a6d782d308f3b6b9d96016c010597958e63"},
+ {file = "charset_normalizer-3.3.0-cp311-cp311-macosx_10_9_x86_64.whl", hash = "sha256:6a685067d05e46641d5d1623d7c7fdf15a357546cbb2f71b0ebde91b175ffc3e"},
+ {file = "charset_normalizer-3.3.0-cp311-cp311-macosx_11_0_arm64.whl", hash = "sha256:0d3d5b7db9ed8a2b11a774db2bbea7ba1884430a205dbd54a32d61d7c2a190fa"},
+ {file = "charset_normalizer-3.3.0-cp311-cp311-manylinux_2_17_aarch64.manylinux2014_aarch64.whl", hash = "sha256:2935ffc78db9645cb2086c2f8f4cfd23d9b73cc0dc80334bc30aac6f03f68f8c"},
+ {file = "charset_normalizer-3.3.0-cp311-cp311-manylinux_2_17_ppc64le.manylinux2014_ppc64le.whl", hash = "sha256:9fe359b2e3a7729010060fbca442ca225280c16e923b37db0e955ac2a2b72a05"},
+ {file = "charset_normalizer-3.3.0-cp311-cp311-manylinux_2_17_s390x.manylinux2014_s390x.whl", hash = "sha256:380c4bde80bce25c6e4f77b19386f5ec9db230df9f2f2ac1e5ad7af2caa70459"},
+ {file = "charset_normalizer-3.3.0-cp311-cp311-manylinux_2_17_x86_64.manylinux2014_x86_64.whl", hash = "sha256:f0d1e3732768fecb052d90d62b220af62ead5748ac51ef61e7b32c266cac9293"},
+ {file = "charset_normalizer-3.3.0-cp311-cp311-manylinux_2_5_i686.manylinux1_i686.manylinux_2_17_i686.manylinux2014_i686.whl", hash = "sha256:1b2919306936ac6efb3aed1fbf81039f7087ddadb3160882a57ee2ff74fd2382"},
+ {file = "charset_normalizer-3.3.0-cp311-cp311-musllinux_1_1_aarch64.whl", hash = "sha256:f8888e31e3a85943743f8fc15e71536bda1c81d5aa36d014a3c0c44481d7db6e"},
+ {file = "charset_normalizer-3.3.0-cp311-cp311-musllinux_1_1_i686.whl", hash = "sha256:82eb849f085624f6a607538ee7b83a6d8126df6d2f7d3b319cb837b289123078"},
+ {file = "charset_normalizer-3.3.0-cp311-cp311-musllinux_1_1_ppc64le.whl", hash = "sha256:7b8b8bf1189b3ba9b8de5c8db4d541b406611a71a955bbbd7385bbc45fcb786c"},
+ {file = "charset_normalizer-3.3.0-cp311-cp311-musllinux_1_1_s390x.whl", hash = "sha256:5adf257bd58c1b8632046bbe43ee38c04e1038e9d37de9c57a94d6bd6ce5da34"},
+ {file = "charset_normalizer-3.3.0-cp311-cp311-musllinux_1_1_x86_64.whl", hash = "sha256:c350354efb159b8767a6244c166f66e67506e06c8924ed74669b2c70bc8735b1"},
+ {file = "charset_normalizer-3.3.0-cp311-cp311-win32.whl", hash = "sha256:02af06682e3590ab952599fbadac535ede5d60d78848e555aa58d0c0abbde786"},
+ {file = "charset_normalizer-3.3.0-cp311-cp311-win_amd64.whl", hash = "sha256:86d1f65ac145e2c9ed71d8ffb1905e9bba3a91ae29ba55b4c46ae6fc31d7c0d4"},
+ {file = "charset_normalizer-3.3.0-cp312-cp312-macosx_10_9_universal2.whl", hash = "sha256:3b447982ad46348c02cb90d230b75ac34e9886273df3a93eec0539308a6296d7"},
+ {file = "charset_normalizer-3.3.0-cp312-cp312-macosx_10_9_x86_64.whl", hash = "sha256:abf0d9f45ea5fb95051c8bfe43cb40cda383772f7e5023a83cc481ca2604d74e"},
+ {file = "charset_normalizer-3.3.0-cp312-cp312-macosx_11_0_arm64.whl", hash = "sha256:b09719a17a2301178fac4470d54b1680b18a5048b481cb8890e1ef820cb80455"},
+ {file = "charset_normalizer-3.3.0-cp312-cp312-manylinux_2_17_aarch64.manylinux2014_aarch64.whl", hash = "sha256:b3d9b48ee6e3967b7901c052b670c7dda6deb812c309439adaffdec55c6d7b78"},
+ {file = "charset_normalizer-3.3.0-cp312-cp312-manylinux_2_17_ppc64le.manylinux2014_ppc64le.whl", hash = "sha256:edfe077ab09442d4ef3c52cb1f9dab89bff02f4524afc0acf2d46be17dc479f5"},
+ {file = "charset_normalizer-3.3.0-cp312-cp312-manylinux_2_17_s390x.manylinux2014_s390x.whl", hash = "sha256:3debd1150027933210c2fc321527c2299118aa929c2f5a0a80ab6953e3bd1908"},
+ {file = "charset_normalizer-3.3.0-cp312-cp312-manylinux_2_17_x86_64.manylinux2014_x86_64.whl", hash = "sha256:86f63face3a527284f7bb8a9d4f78988e3c06823f7bea2bd6f0e0e9298ca0403"},
+ {file = "charset_normalizer-3.3.0-cp312-cp312-manylinux_2_5_i686.manylinux1_i686.manylinux_2_17_i686.manylinux2014_i686.whl", hash = "sha256:24817cb02cbef7cd499f7c9a2735286b4782bd47a5b3516a0e84c50eab44b98e"},
+ {file = "charset_normalizer-3.3.0-cp312-cp312-musllinux_1_1_aarch64.whl", hash = "sha256:c71f16da1ed8949774ef79f4a0260d28b83b3a50c6576f8f4f0288d109777989"},
+ {file = "charset_normalizer-3.3.0-cp312-cp312-musllinux_1_1_i686.whl", hash = "sha256:9cf3126b85822c4e53aa28c7ec9869b924d6fcfb76e77a45c44b83d91afd74f9"},
+ {file = "charset_normalizer-3.3.0-cp312-cp312-musllinux_1_1_ppc64le.whl", hash = "sha256:b3b2316b25644b23b54a6f6401074cebcecd1244c0b8e80111c9a3f1c8e83d65"},
+ {file = "charset_normalizer-3.3.0-cp312-cp312-musllinux_1_1_s390x.whl", hash = "sha256:03680bb39035fbcffe828eae9c3f8afc0428c91d38e7d61aa992ef7a59fb120e"},
+ {file = "charset_normalizer-3.3.0-cp312-cp312-musllinux_1_1_x86_64.whl", hash = "sha256:4cc152c5dd831641e995764f9f0b6589519f6f5123258ccaca8c6d34572fefa8"},
+ {file = "charset_normalizer-3.3.0-cp312-cp312-win32.whl", hash = "sha256:b8f3307af845803fb0b060ab76cf6dd3a13adc15b6b451f54281d25911eb92df"},
+ {file = "charset_normalizer-3.3.0-cp312-cp312-win_amd64.whl", hash = "sha256:8eaf82f0eccd1505cf39a45a6bd0a8cf1c70dcfc30dba338207a969d91b965c0"},
+ {file = "charset_normalizer-3.3.0-cp37-cp37m-macosx_10_9_x86_64.whl", hash = "sha256:dc45229747b67ffc441b3de2f3ae5e62877a282ea828a5bdb67883c4ee4a8810"},
+ {file = "charset_normalizer-3.3.0-cp37-cp37m-manylinux_2_17_aarch64.manylinux2014_aarch64.whl", hash = "sha256:2f4a0033ce9a76e391542c182f0d48d084855b5fcba5010f707c8e8c34663d77"},
+ {file = "charset_normalizer-3.3.0-cp37-cp37m-manylinux_2_17_ppc64le.manylinux2014_ppc64le.whl", hash = "sha256:ada214c6fa40f8d800e575de6b91a40d0548139e5dc457d2ebb61470abf50186"},
+ {file = "charset_normalizer-3.3.0-cp37-cp37m-manylinux_2_17_s390x.manylinux2014_s390x.whl", hash = "sha256:b1121de0e9d6e6ca08289583d7491e7fcb18a439305b34a30b20d8215922d43c"},
+ {file = "charset_normalizer-3.3.0-cp37-cp37m-manylinux_2_17_x86_64.manylinux2014_x86_64.whl", hash = "sha256:1063da2c85b95f2d1a430f1c33b55c9c17ffaf5e612e10aeaad641c55a9e2b9d"},
+ {file = "charset_normalizer-3.3.0-cp37-cp37m-manylinux_2_5_i686.manylinux1_i686.manylinux_2_17_i686.manylinux2014_i686.whl", hash = "sha256:70f1d09c0d7748b73290b29219e854b3207aea922f839437870d8cc2168e31cc"},
+ {file = "charset_normalizer-3.3.0-cp37-cp37m-musllinux_1_1_aarch64.whl", hash = "sha256:250c9eb0f4600361dd80d46112213dff2286231d92d3e52af1e5a6083d10cad9"},
+ {file = "charset_normalizer-3.3.0-cp37-cp37m-musllinux_1_1_i686.whl", hash = "sha256:750b446b2ffce1739e8578576092179160f6d26bd5e23eb1789c4d64d5af7dc7"},
+ {file = "charset_normalizer-3.3.0-cp37-cp37m-musllinux_1_1_ppc64le.whl", hash = "sha256:fc52b79d83a3fe3a360902d3f5d79073a993597d48114c29485e9431092905d8"},
+ {file = "charset_normalizer-3.3.0-cp37-cp37m-musllinux_1_1_s390x.whl", hash = "sha256:588245972aca710b5b68802c8cad9edaa98589b1b42ad2b53accd6910dad3545"},
+ {file = "charset_normalizer-3.3.0-cp37-cp37m-musllinux_1_1_x86_64.whl", hash = "sha256:e39c7eb31e3f5b1f88caff88bcff1b7f8334975b46f6ac6e9fc725d829bc35d4"},
+ {file = "charset_normalizer-3.3.0-cp37-cp37m-win32.whl", hash = "sha256:abecce40dfebbfa6abf8e324e1860092eeca6f7375c8c4e655a8afb61af58f2c"},
+ {file = "charset_normalizer-3.3.0-cp37-cp37m-win_amd64.whl", hash = "sha256:24a91a981f185721542a0b7c92e9054b7ab4fea0508a795846bc5b0abf8118d4"},
+ {file = "charset_normalizer-3.3.0-cp38-cp38-macosx_10_9_universal2.whl", hash = "sha256:67b8cc9574bb518ec76dc8e705d4c39ae78bb96237cb533edac149352c1f39fe"},
+ {file = "charset_normalizer-3.3.0-cp38-cp38-macosx_10_9_x86_64.whl", hash = "sha256:ac71b2977fb90c35d41c9453116e283fac47bb9096ad917b8819ca8b943abecd"},
+ {file = "charset_normalizer-3.3.0-cp38-cp38-macosx_11_0_arm64.whl", hash = "sha256:3ae38d325b512f63f8da31f826e6cb6c367336f95e418137286ba362925c877e"},
+ {file = "charset_normalizer-3.3.0-cp38-cp38-manylinux_2_17_aarch64.manylinux2014_aarch64.whl", hash = "sha256:542da1178c1c6af8873e143910e2269add130a299c9106eef2594e15dae5e482"},
+ {file = "charset_normalizer-3.3.0-cp38-cp38-manylinux_2_17_ppc64le.manylinux2014_ppc64le.whl", hash = "sha256:30a85aed0b864ac88309b7d94be09f6046c834ef60762a8833b660139cfbad13"},
+ {file = "charset_normalizer-3.3.0-cp38-cp38-manylinux_2_17_s390x.manylinux2014_s390x.whl", hash = "sha256:aae32c93e0f64469f74ccc730a7cb21c7610af3a775157e50bbd38f816536b38"},
+ {file = "charset_normalizer-3.3.0-cp38-cp38-manylinux_2_17_x86_64.manylinux2014_x86_64.whl", hash = "sha256:15b26ddf78d57f1d143bdf32e820fd8935d36abe8a25eb9ec0b5a71c82eb3895"},
+ {file = "charset_normalizer-3.3.0-cp38-cp38-manylinux_2_5_i686.manylinux1_i686.manylinux_2_17_i686.manylinux2014_i686.whl", hash = "sha256:7f5d10bae5d78e4551b7be7a9b29643a95aded9d0f602aa2ba584f0388e7a557"},
+ {file = "charset_normalizer-3.3.0-cp38-cp38-musllinux_1_1_aarch64.whl", hash = "sha256:249c6470a2b60935bafd1d1d13cd613f8cd8388d53461c67397ee6a0f5dce741"},
+ {file = "charset_normalizer-3.3.0-cp38-cp38-musllinux_1_1_i686.whl", hash = "sha256:c5a74c359b2d47d26cdbbc7845e9662d6b08a1e915eb015d044729e92e7050b7"},
+ {file = "charset_normalizer-3.3.0-cp38-cp38-musllinux_1_1_ppc64le.whl", hash = "sha256:b5bcf60a228acae568e9911f410f9d9e0d43197d030ae5799e20dca8df588287"},
+ {file = "charset_normalizer-3.3.0-cp38-cp38-musllinux_1_1_s390x.whl", hash = "sha256:187d18082694a29005ba2944c882344b6748d5be69e3a89bf3cc9d878e548d5a"},
+ {file = "charset_normalizer-3.3.0-cp38-cp38-musllinux_1_1_x86_64.whl", hash = "sha256:81bf654678e575403736b85ba3a7867e31c2c30a69bc57fe88e3ace52fb17b89"},
+ {file = "charset_normalizer-3.3.0-cp38-cp38-win32.whl", hash = "sha256:85a32721ddde63c9df9ebb0d2045b9691d9750cb139c161c80e500d210f5e26e"},
+ {file = "charset_normalizer-3.3.0-cp38-cp38-win_amd64.whl", hash = "sha256:468d2a840567b13a590e67dd276c570f8de00ed767ecc611994c301d0f8c014f"},
+ {file = "charset_normalizer-3.3.0-cp39-cp39-macosx_10_9_universal2.whl", hash = "sha256:e0fc42822278451bc13a2e8626cf2218ba570f27856b536e00cfa53099724828"},
+ {file = "charset_normalizer-3.3.0-cp39-cp39-macosx_10_9_x86_64.whl", hash = "sha256:09c77f964f351a7369cc343911e0df63e762e42bac24cd7d18525961c81754f4"},
+ {file = "charset_normalizer-3.3.0-cp39-cp39-macosx_11_0_arm64.whl", hash = "sha256:12ebea541c44fdc88ccb794a13fe861cc5e35d64ed689513a5c03d05b53b7c82"},
+ {file = "charset_normalizer-3.3.0-cp39-cp39-manylinux_2_17_aarch64.manylinux2014_aarch64.whl", hash = "sha256:805dfea4ca10411a5296bcc75638017215a93ffb584c9e344731eef0dcfb026a"},
+ {file = "charset_normalizer-3.3.0-cp39-cp39-manylinux_2_17_ppc64le.manylinux2014_ppc64le.whl", hash = "sha256:96c2b49eb6a72c0e4991d62406e365d87067ca14c1a729a870d22354e6f68115"},
+ {file = "charset_normalizer-3.3.0-cp39-cp39-manylinux_2_17_s390x.manylinux2014_s390x.whl", hash = "sha256:aaf7b34c5bc56b38c931a54f7952f1ff0ae77a2e82496583b247f7c969eb1479"},
+ {file = "charset_normalizer-3.3.0-cp39-cp39-manylinux_2_17_x86_64.manylinux2014_x86_64.whl", hash = "sha256:619d1c96099be5823db34fe89e2582b336b5b074a7f47f819d6b3a57ff7bdb86"},
+ {file = "charset_normalizer-3.3.0-cp39-cp39-manylinux_2_5_i686.manylinux1_i686.manylinux_2_17_i686.manylinux2014_i686.whl", hash = "sha256:a0ac5e7015a5920cfce654c06618ec40c33e12801711da6b4258af59a8eff00a"},
+ {file = "charset_normalizer-3.3.0-cp39-cp39-musllinux_1_1_aarch64.whl", hash = "sha256:93aa7eef6ee71c629b51ef873991d6911b906d7312c6e8e99790c0f33c576f89"},
+ {file = "charset_normalizer-3.3.0-cp39-cp39-musllinux_1_1_i686.whl", hash = "sha256:7966951325782121e67c81299a031f4c115615e68046f79b85856b86ebffc4cd"},
+ {file = "charset_normalizer-3.3.0-cp39-cp39-musllinux_1_1_ppc64le.whl", hash = "sha256:02673e456dc5ab13659f85196c534dc596d4ef260e4d86e856c3b2773ce09843"},
+ {file = "charset_normalizer-3.3.0-cp39-cp39-musllinux_1_1_s390x.whl", hash = "sha256:c2af80fb58f0f24b3f3adcb9148e6203fa67dd3f61c4af146ecad033024dde43"},
+ {file = "charset_normalizer-3.3.0-cp39-cp39-musllinux_1_1_x86_64.whl", hash = "sha256:153e7b6e724761741e0974fc4dcd406d35ba70b92bfe3fedcb497226c93b9da7"},
+ {file = "charset_normalizer-3.3.0-cp39-cp39-win32.whl", hash = "sha256:d47ecf253780c90ee181d4d871cd655a789da937454045b17b5798da9393901a"},
+ {file = "charset_normalizer-3.3.0-cp39-cp39-win_amd64.whl", hash = "sha256:d97d85fa63f315a8bdaba2af9a6a686e0eceab77b3089af45133252618e70884"},
+ {file = "charset_normalizer-3.3.0-py3-none-any.whl", hash = "sha256:e46cd37076971c1040fc8c41273a8b3e2c624ce4f2be3f5dfcb7a430c1d3acc2"},
]
[[package]]
name = "click"
-version = "8.1.3"
+version = "8.1.7"
description = "Composable command line interface toolkit"
optional = false
python-versions = ">=3.7"
files = [
- {file = "click-8.1.3-py3-none-any.whl", hash = "sha256:bb4d8133cb15a609f44e8213d9b391b0809795062913b383c62be0ee95b1db48"},
- {file = "click-8.1.3.tar.gz", hash = "sha256:7682dc8afb30297001674575ea00d1814d808d6a36af415a82bd481d37ba7b8e"},
+ {file = "click-8.1.7-py3-none-any.whl", hash = "sha256:ae74fb96c20a0277a1d615f1e4d73c8414f5a98db8b799a7931d1582f3390c28"},
+ {file = "click-8.1.7.tar.gz", hash = "sha256:ca9853ad459e787e2192211578cc907e7594e294c7ccc834310722b41b9ca6de"},
]
[package.dependencies]
@@ -223,62 +238,71 @@ files = [
[[package]]
name = "coverage"
-version = "7.2.5"
+version = "7.2.7"
description = "Code coverage measurement for Python"
optional = false
python-versions = ">=3.7"
files = [
- {file = "coverage-7.2.5-cp310-cp310-macosx_10_9_x86_64.whl", hash = "sha256:883123d0bbe1c136f76b56276074b0c79b5817dd4238097ffa64ac67257f4b6c"},
- {file = "coverage-7.2.5-cp310-cp310-macosx_11_0_arm64.whl", hash = "sha256:d2fbc2a127e857d2f8898aaabcc34c37771bf78a4d5e17d3e1f5c30cd0cbc62a"},
- {file = "coverage-7.2.5-cp310-cp310-manylinux_2_17_aarch64.manylinux2014_aarch64.whl", hash = "sha256:5f3671662dc4b422b15776cdca89c041a6349b4864a43aa2350b6b0b03bbcc7f"},
- {file = "coverage-7.2.5-cp310-cp310-manylinux_2_5_i686.manylinux1_i686.manylinux_2_17_i686.manylinux2014_i686.whl", hash = "sha256:780551e47d62095e088f251f5db428473c26db7829884323e56d9c0c3118791a"},
- {file = "coverage-7.2.5-cp310-cp310-manylinux_2_5_x86_64.manylinux1_x86_64.manylinux_2_17_x86_64.manylinux2014_x86_64.whl", hash = "sha256:066b44897c493e0dcbc9e6a6d9f8bbb6607ef82367cf6810d387c09f0cd4fe9a"},
- {file = "coverage-7.2.5-cp310-cp310-musllinux_1_1_aarch64.whl", hash = "sha256:b9a4ee55174b04f6af539218f9f8083140f61a46eabcaa4234f3c2a452c4ed11"},
- {file = "coverage-7.2.5-cp310-cp310-musllinux_1_1_i686.whl", hash = "sha256:706ec567267c96717ab9363904d846ec009a48d5f832140b6ad08aad3791b1f5"},
- {file = "coverage-7.2.5-cp310-cp310-musllinux_1_1_x86_64.whl", hash = "sha256:ae453f655640157d76209f42c62c64c4d4f2c7f97256d3567e3b439bd5c9b06c"},
- {file = "coverage-7.2.5-cp310-cp310-win32.whl", hash = "sha256:f81c9b4bd8aa747d417407a7f6f0b1469a43b36a85748145e144ac4e8d303cb5"},
- {file = "coverage-7.2.5-cp310-cp310-win_amd64.whl", hash = "sha256:dc945064a8783b86fcce9a0a705abd7db2117d95e340df8a4333f00be5efb64c"},
- {file = "coverage-7.2.5-cp311-cp311-macosx_10_9_x86_64.whl", hash = "sha256:40cc0f91c6cde033da493227797be2826cbf8f388eaa36a0271a97a332bfd7ce"},
- {file = "coverage-7.2.5-cp311-cp311-macosx_11_0_arm64.whl", hash = "sha256:a66e055254a26c82aead7ff420d9fa8dc2da10c82679ea850d8feebf11074d88"},
- {file = "coverage-7.2.5-cp311-cp311-manylinux_2_17_aarch64.manylinux2014_aarch64.whl", hash = "sha256:c10fbc8a64aa0f3ed136b0b086b6b577bc64d67d5581acd7cc129af52654384e"},
- {file = "coverage-7.2.5-cp311-cp311-manylinux_2_5_i686.manylinux1_i686.manylinux_2_17_i686.manylinux2014_i686.whl", hash = "sha256:9a22cbb5ede6fade0482111fa7f01115ff04039795d7092ed0db43522431b4f2"},
- {file = "coverage-7.2.5-cp311-cp311-manylinux_2_5_x86_64.manylinux1_x86_64.manylinux_2_17_x86_64.manylinux2014_x86_64.whl", hash = "sha256:292300f76440651529b8ceec283a9370532f4ecba9ad67d120617021bb5ef139"},
- {file = "coverage-7.2.5-cp311-cp311-musllinux_1_1_aarch64.whl", hash = "sha256:7ff8f3fb38233035028dbc93715551d81eadc110199e14bbbfa01c5c4a43f8d8"},
- {file = "coverage-7.2.5-cp311-cp311-musllinux_1_1_i686.whl", hash = "sha256:a08c7401d0b24e8c2982f4e307124b671c6736d40d1c39e09d7a8687bddf83ed"},
- {file = "coverage-7.2.5-cp311-cp311-musllinux_1_1_x86_64.whl", hash = "sha256:ef9659d1cda9ce9ac9585c045aaa1e59223b143f2407db0eaee0b61a4f266fb6"},
- {file = "coverage-7.2.5-cp311-cp311-win32.whl", hash = "sha256:30dcaf05adfa69c2a7b9f7dfd9f60bc8e36b282d7ed25c308ef9e114de7fc23b"},
- {file = "coverage-7.2.5-cp311-cp311-win_amd64.whl", hash = "sha256:97072cc90f1009386c8a5b7de9d4fc1a9f91ba5ef2146c55c1f005e7b5c5e068"},
- {file = "coverage-7.2.5-cp37-cp37m-macosx_10_9_x86_64.whl", hash = "sha256:bebea5f5ed41f618797ce3ffb4606c64a5de92e9c3f26d26c2e0aae292f015c1"},
- {file = "coverage-7.2.5-cp37-cp37m-manylinux_2_17_aarch64.manylinux2014_aarch64.whl", hash = "sha256:828189fcdda99aae0d6bf718ea766b2e715eabc1868670a0a07bf8404bf58c33"},
- {file = "coverage-7.2.5-cp37-cp37m-manylinux_2_5_i686.manylinux1_i686.manylinux_2_17_i686.manylinux2014_i686.whl", hash = "sha256:6e8a95f243d01ba572341c52f89f3acb98a3b6d1d5d830efba86033dd3687ade"},
- {file = "coverage-7.2.5-cp37-cp37m-manylinux_2_5_x86_64.manylinux1_x86_64.manylinux_2_17_x86_64.manylinux2014_x86_64.whl", hash = "sha256:e8834e5f17d89e05697c3c043d3e58a8b19682bf365048837383abfe39adaed5"},
- {file = "coverage-7.2.5-cp37-cp37m-musllinux_1_1_aarch64.whl", hash = "sha256:d1f25ee9de21a39b3a8516f2c5feb8de248f17da7eead089c2e04aa097936b47"},
- {file = "coverage-7.2.5-cp37-cp37m-musllinux_1_1_i686.whl", hash = "sha256:1637253b11a18f453e34013c665d8bf15904c9e3c44fbda34c643fbdc9d452cd"},
- {file = "coverage-7.2.5-cp37-cp37m-musllinux_1_1_x86_64.whl", hash = "sha256:8e575a59315a91ccd00c7757127f6b2488c2f914096077c745c2f1ba5b8c0969"},
- {file = "coverage-7.2.5-cp37-cp37m-win32.whl", hash = "sha256:509ecd8334c380000d259dc66feb191dd0a93b21f2453faa75f7f9cdcefc0718"},
- {file = "coverage-7.2.5-cp37-cp37m-win_amd64.whl", hash = "sha256:12580845917b1e59f8a1c2ffa6af6d0908cb39220f3019e36c110c943dc875b0"},
- {file = "coverage-7.2.5-cp38-cp38-macosx_10_9_x86_64.whl", hash = "sha256:b5016e331b75310610c2cf955d9f58a9749943ed5f7b8cfc0bb89c6134ab0a84"},
- {file = "coverage-7.2.5-cp38-cp38-macosx_11_0_arm64.whl", hash = "sha256:373ea34dca98f2fdb3e5cb33d83b6d801007a8074f992b80311fc589d3e6b790"},
- {file = "coverage-7.2.5-cp38-cp38-manylinux_2_17_aarch64.manylinux2014_aarch64.whl", hash = "sha256:a063aad9f7b4c9f9da7b2550eae0a582ffc7623dca1c925e50c3fbde7a579771"},
- {file = "coverage-7.2.5-cp38-cp38-manylinux_2_5_i686.manylinux1_i686.manylinux_2_17_i686.manylinux2014_i686.whl", hash = "sha256:38c0a497a000d50491055805313ed83ddba069353d102ece8aef5d11b5faf045"},
- {file = "coverage-7.2.5-cp38-cp38-manylinux_2_5_x86_64.manylinux1_x86_64.manylinux_2_17_x86_64.manylinux2014_x86_64.whl", hash = "sha256:a2b3b05e22a77bb0ae1a3125126a4e08535961c946b62f30985535ed40e26614"},
- {file = "coverage-7.2.5-cp38-cp38-musllinux_1_1_aarch64.whl", hash = "sha256:0342a28617e63ad15d96dca0f7ae9479a37b7d8a295f749c14f3436ea59fdcb3"},
- {file = "coverage-7.2.5-cp38-cp38-musllinux_1_1_i686.whl", hash = "sha256:cf97ed82ca986e5c637ea286ba2793c85325b30f869bf64d3009ccc1a31ae3fd"},
- {file = "coverage-7.2.5-cp38-cp38-musllinux_1_1_x86_64.whl", hash = "sha256:c2c41c1b1866b670573657d584de413df701f482574bad7e28214a2362cb1fd1"},
- {file = "coverage-7.2.5-cp38-cp38-win32.whl", hash = "sha256:10b15394c13544fce02382360cab54e51a9e0fd1bd61ae9ce012c0d1e103c813"},
- {file = "coverage-7.2.5-cp38-cp38-win_amd64.whl", hash = "sha256:a0b273fe6dc655b110e8dc89b8ec7f1a778d78c9fd9b4bda7c384c8906072212"},
- {file = "coverage-7.2.5-cp39-cp39-macosx_10_9_x86_64.whl", hash = "sha256:5c587f52c81211d4530fa6857884d37f514bcf9453bdeee0ff93eaaf906a5c1b"},
- {file = "coverage-7.2.5-cp39-cp39-macosx_11_0_arm64.whl", hash = "sha256:4436cc9ba5414c2c998eaedee5343f49c02ca93b21769c5fdfa4f9d799e84200"},
- {file = "coverage-7.2.5-cp39-cp39-manylinux_2_17_aarch64.manylinux2014_aarch64.whl", hash = "sha256:6599bf92f33ab041e36e06d25890afbdf12078aacfe1f1d08c713906e49a3fe5"},
- {file = "coverage-7.2.5-cp39-cp39-manylinux_2_5_i686.manylinux1_i686.manylinux_2_17_i686.manylinux2014_i686.whl", hash = "sha256:857abe2fa6a4973f8663e039ead8d22215d31db613ace76e4a98f52ec919068e"},
- {file = "coverage-7.2.5-cp39-cp39-manylinux_2_5_x86_64.manylinux1_x86_64.manylinux_2_17_x86_64.manylinux2014_x86_64.whl", hash = "sha256:f6f5cab2d7f0c12f8187a376cc6582c477d2df91d63f75341307fcdcb5d60303"},
- {file = "coverage-7.2.5-cp39-cp39-musllinux_1_1_aarch64.whl", hash = "sha256:aa387bd7489f3e1787ff82068b295bcaafbf6f79c3dad3cbc82ef88ce3f48ad3"},
- {file = "coverage-7.2.5-cp39-cp39-musllinux_1_1_i686.whl", hash = "sha256:156192e5fd3dbbcb11cd777cc469cf010a294f4c736a2b2c891c77618cb1379a"},
- {file = "coverage-7.2.5-cp39-cp39-musllinux_1_1_x86_64.whl", hash = "sha256:bd3b4b8175c1db502adf209d06136c000df4d245105c8839e9d0be71c94aefe1"},
- {file = "coverage-7.2.5-cp39-cp39-win32.whl", hash = "sha256:ddc5a54edb653e9e215f75de377354e2455376f416c4378e1d43b08ec50acc31"},
- {file = "coverage-7.2.5-cp39-cp39-win_amd64.whl", hash = "sha256:338aa9d9883aaaad53695cb14ccdeb36d4060485bb9388446330bef9c361c252"},
- {file = "coverage-7.2.5-pp37.pp38.pp39-none-any.whl", hash = "sha256:8877d9b437b35a85c18e3c6499b23674684bf690f5d96c1006a1ef61f9fdf0f3"},
- {file = "coverage-7.2.5.tar.gz", hash = "sha256:f99ef080288f09ffc687423b8d60978cf3a465d3f404a18d1a05474bd8575a47"},
+ {file = "coverage-7.2.7-cp310-cp310-macosx_10_9_x86_64.whl", hash = "sha256:d39b5b4f2a66ccae8b7263ac3c8170994b65266797fb96cbbfd3fb5b23921db8"},
+ {file = "coverage-7.2.7-cp310-cp310-macosx_11_0_arm64.whl", hash = "sha256:6d040ef7c9859bb11dfeb056ff5b3872436e3b5e401817d87a31e1750b9ae2fb"},
+ {file = "coverage-7.2.7-cp310-cp310-manylinux_2_17_aarch64.manylinux2014_aarch64.whl", hash = "sha256:ba90a9563ba44a72fda2e85302c3abc71c5589cea608ca16c22b9804262aaeb6"},
+ {file = "coverage-7.2.7-cp310-cp310-manylinux_2_5_i686.manylinux1_i686.manylinux_2_17_i686.manylinux2014_i686.whl", hash = "sha256:e7d9405291c6928619403db1d10bd07888888ec1abcbd9748fdaa971d7d661b2"},
+ {file = "coverage-7.2.7-cp310-cp310-manylinux_2_5_x86_64.manylinux1_x86_64.manylinux_2_17_x86_64.manylinux2014_x86_64.whl", hash = "sha256:31563e97dae5598556600466ad9beea39fb04e0229e61c12eaa206e0aa202063"},
+ {file = "coverage-7.2.7-cp310-cp310-musllinux_1_1_aarch64.whl", hash = "sha256:ebba1cd308ef115925421d3e6a586e655ca5a77b5bf41e02eb0e4562a111f2d1"},
+ {file = "coverage-7.2.7-cp310-cp310-musllinux_1_1_i686.whl", hash = "sha256:cb017fd1b2603ef59e374ba2063f593abe0fc45f2ad9abdde5b4d83bd922a353"},
+ {file = "coverage-7.2.7-cp310-cp310-musllinux_1_1_x86_64.whl", hash = "sha256:d62a5c7dad11015c66fbb9d881bc4caa5b12f16292f857842d9d1871595f4495"},
+ {file = "coverage-7.2.7-cp310-cp310-win32.whl", hash = "sha256:ee57190f24fba796e36bb6d3aa8a8783c643d8fa9760c89f7a98ab5455fbf818"},
+ {file = "coverage-7.2.7-cp310-cp310-win_amd64.whl", hash = "sha256:f75f7168ab25dd93110c8a8117a22450c19976afbc44234cbf71481094c1b850"},
+ {file = "coverage-7.2.7-cp311-cp311-macosx_10_9_x86_64.whl", hash = "sha256:06a9a2be0b5b576c3f18f1a241f0473575c4a26021b52b2a85263a00f034d51f"},
+ {file = "coverage-7.2.7-cp311-cp311-macosx_11_0_arm64.whl", hash = "sha256:5baa06420f837184130752b7c5ea0808762083bf3487b5038d68b012e5937dbe"},
+ {file = "coverage-7.2.7-cp311-cp311-manylinux_2_17_aarch64.manylinux2014_aarch64.whl", hash = "sha256:fdec9e8cbf13a5bf63290fc6013d216a4c7232efb51548594ca3631a7f13c3a3"},
+ {file = "coverage-7.2.7-cp311-cp311-manylinux_2_5_i686.manylinux1_i686.manylinux_2_17_i686.manylinux2014_i686.whl", hash = "sha256:52edc1a60c0d34afa421c9c37078817b2e67a392cab17d97283b64c5833f427f"},
+ {file = "coverage-7.2.7-cp311-cp311-manylinux_2_5_x86_64.manylinux1_x86_64.manylinux_2_17_x86_64.manylinux2014_x86_64.whl", hash = "sha256:63426706118b7f5cf6bb6c895dc215d8a418d5952544042c8a2d9fe87fcf09cb"},
+ {file = "coverage-7.2.7-cp311-cp311-musllinux_1_1_aarch64.whl", hash = "sha256:afb17f84d56068a7c29f5fa37bfd38d5aba69e3304af08ee94da8ed5b0865833"},
+ {file = "coverage-7.2.7-cp311-cp311-musllinux_1_1_i686.whl", hash = "sha256:48c19d2159d433ccc99e729ceae7d5293fbffa0bdb94952d3579983d1c8c9d97"},
+ {file = "coverage-7.2.7-cp311-cp311-musllinux_1_1_x86_64.whl", hash = "sha256:0e1f928eaf5469c11e886fe0885ad2bf1ec606434e79842a879277895a50942a"},
+ {file = "coverage-7.2.7-cp311-cp311-win32.whl", hash = "sha256:33d6d3ea29d5b3a1a632b3c4e4f4ecae24ef170b0b9ee493883f2df10039959a"},
+ {file = "coverage-7.2.7-cp311-cp311-win_amd64.whl", hash = "sha256:5b7540161790b2f28143191f5f8ec02fb132660ff175b7747b95dcb77ac26562"},
+ {file = "coverage-7.2.7-cp312-cp312-macosx_10_9_x86_64.whl", hash = "sha256:f2f67fe12b22cd130d34d0ef79206061bfb5eda52feb6ce0dba0644e20a03cf4"},
+ {file = "coverage-7.2.7-cp312-cp312-manylinux_2_17_aarch64.manylinux2014_aarch64.whl", hash = "sha256:a342242fe22407f3c17f4b499276a02b01e80f861f1682ad1d95b04018e0c0d4"},
+ {file = "coverage-7.2.7-cp312-cp312-manylinux_2_5_i686.manylinux1_i686.manylinux_2_17_i686.manylinux2014_i686.whl", hash = "sha256:171717c7cb6b453aebac9a2ef603699da237f341b38eebfee9be75d27dc38e01"},
+ {file = "coverage-7.2.7-cp312-cp312-manylinux_2_5_x86_64.manylinux1_x86_64.manylinux_2_17_x86_64.manylinux2014_x86_64.whl", hash = "sha256:49969a9f7ffa086d973d91cec8d2e31080436ef0fb4a359cae927e742abfaaa6"},
+ {file = "coverage-7.2.7-cp312-cp312-musllinux_1_1_aarch64.whl", hash = "sha256:b46517c02ccd08092f4fa99f24c3b83d8f92f739b4657b0f146246a0ca6a831d"},
+ {file = "coverage-7.2.7-cp312-cp312-musllinux_1_1_i686.whl", hash = "sha256:a3d33a6b3eae87ceaefa91ffdc130b5e8536182cd6dfdbfc1aa56b46ff8c86de"},
+ {file = "coverage-7.2.7-cp312-cp312-musllinux_1_1_x86_64.whl", hash = "sha256:976b9c42fb2a43ebf304fa7d4a310e5f16cc99992f33eced91ef6f908bd8f33d"},
+ {file = "coverage-7.2.7-cp312-cp312-win32.whl", hash = "sha256:8de8bb0e5ad103888d65abef8bca41ab93721647590a3f740100cd65c3b00511"},
+ {file = "coverage-7.2.7-cp312-cp312-win_amd64.whl", hash = "sha256:9e31cb64d7de6b6f09702bb27c02d1904b3aebfca610c12772452c4e6c21a0d3"},
+ {file = "coverage-7.2.7-cp37-cp37m-macosx_10_9_x86_64.whl", hash = "sha256:58c2ccc2f00ecb51253cbe5d8d7122a34590fac9646a960d1430d5b15321d95f"},
+ {file = "coverage-7.2.7-cp37-cp37m-manylinux_2_17_aarch64.manylinux2014_aarch64.whl", hash = "sha256:d22656368f0e6189e24722214ed8d66b8022db19d182927b9a248a2a8a2f67eb"},
+ {file = "coverage-7.2.7-cp37-cp37m-manylinux_2_5_i686.manylinux1_i686.manylinux_2_17_i686.manylinux2014_i686.whl", hash = "sha256:a895fcc7b15c3fc72beb43cdcbdf0ddb7d2ebc959edac9cef390b0d14f39f8a9"},
+ {file = "coverage-7.2.7-cp37-cp37m-manylinux_2_5_x86_64.manylinux1_x86_64.manylinux_2_17_x86_64.manylinux2014_x86_64.whl", hash = "sha256:e84606b74eb7de6ff581a7915e2dab7a28a0517fbe1c9239eb227e1354064dcd"},
+ {file = "coverage-7.2.7-cp37-cp37m-musllinux_1_1_aarch64.whl", hash = "sha256:0a5f9e1dbd7fbe30196578ca36f3fba75376fb99888c395c5880b355e2875f8a"},
+ {file = "coverage-7.2.7-cp37-cp37m-musllinux_1_1_i686.whl", hash = "sha256:419bfd2caae268623dd469eff96d510a920c90928b60f2073d79f8fe2bbc5959"},
+ {file = "coverage-7.2.7-cp37-cp37m-musllinux_1_1_x86_64.whl", hash = "sha256:2aee274c46590717f38ae5e4650988d1af340fe06167546cc32fe2f58ed05b02"},
+ {file = "coverage-7.2.7-cp37-cp37m-win32.whl", hash = "sha256:61b9a528fb348373c433e8966535074b802c7a5d7f23c4f421e6c6e2f1697a6f"},
+ {file = "coverage-7.2.7-cp37-cp37m-win_amd64.whl", hash = "sha256:b1c546aca0ca4d028901d825015dc8e4d56aac4b541877690eb76490f1dc8ed0"},
+ {file = "coverage-7.2.7-cp38-cp38-macosx_10_9_x86_64.whl", hash = "sha256:54b896376ab563bd38453cecb813c295cf347cf5906e8b41d340b0321a5433e5"},
+ {file = "coverage-7.2.7-cp38-cp38-macosx_11_0_arm64.whl", hash = "sha256:3d376df58cc111dc8e21e3b6e24606b5bb5dee6024f46a5abca99124b2229ef5"},
+ {file = "coverage-7.2.7-cp38-cp38-manylinux_2_17_aarch64.manylinux2014_aarch64.whl", hash = "sha256:5e330fc79bd7207e46c7d7fd2bb4af2963f5f635703925543a70b99574b0fea9"},
+ {file = "coverage-7.2.7-cp38-cp38-manylinux_2_5_i686.manylinux1_i686.manylinux_2_17_i686.manylinux2014_i686.whl", hash = "sha256:1e9d683426464e4a252bf70c3498756055016f99ddaec3774bf368e76bbe02b6"},
+ {file = "coverage-7.2.7-cp38-cp38-manylinux_2_5_x86_64.manylinux1_x86_64.manylinux_2_17_x86_64.manylinux2014_x86_64.whl", hash = "sha256:8d13c64ee2d33eccf7437961b6ea7ad8673e2be040b4f7fd4fd4d4d28d9ccb1e"},
+ {file = "coverage-7.2.7-cp38-cp38-musllinux_1_1_aarch64.whl", hash = "sha256:b7aa5f8a41217360e600da646004f878250a0d6738bcdc11a0a39928d7dc2050"},
+ {file = "coverage-7.2.7-cp38-cp38-musllinux_1_1_i686.whl", hash = "sha256:8fa03bce9bfbeeef9f3b160a8bed39a221d82308b4152b27d82d8daa7041fee5"},
+ {file = "coverage-7.2.7-cp38-cp38-musllinux_1_1_x86_64.whl", hash = "sha256:245167dd26180ab4c91d5e1496a30be4cd721a5cf2abf52974f965f10f11419f"},
+ {file = "coverage-7.2.7-cp38-cp38-win32.whl", hash = "sha256:d2c2db7fd82e9b72937969bceac4d6ca89660db0a0967614ce2481e81a0b771e"},
+ {file = "coverage-7.2.7-cp38-cp38-win_amd64.whl", hash = "sha256:2e07b54284e381531c87f785f613b833569c14ecacdcb85d56b25c4622c16c3c"},
+ {file = "coverage-7.2.7-cp39-cp39-macosx_10_9_x86_64.whl", hash = "sha256:537891ae8ce59ef63d0123f7ac9e2ae0fc8b72c7ccbe5296fec45fd68967b6c9"},
+ {file = "coverage-7.2.7-cp39-cp39-macosx_11_0_arm64.whl", hash = "sha256:06fb182e69f33f6cd1d39a6c597294cff3143554b64b9825d1dc69d18cc2fff2"},
+ {file = "coverage-7.2.7-cp39-cp39-manylinux_2_17_aarch64.manylinux2014_aarch64.whl", hash = "sha256:201e7389591af40950a6480bd9edfa8ed04346ff80002cec1a66cac4549c1ad7"},
+ {file = "coverage-7.2.7-cp39-cp39-manylinux_2_5_i686.manylinux1_i686.manylinux_2_17_i686.manylinux2014_i686.whl", hash = "sha256:f6951407391b639504e3b3be51b7ba5f3528adbf1a8ac3302b687ecababf929e"},
+ {file = "coverage-7.2.7-cp39-cp39-manylinux_2_5_x86_64.manylinux1_x86_64.manylinux_2_17_x86_64.manylinux2014_x86_64.whl", hash = "sha256:6f48351d66575f535669306aa7d6d6f71bc43372473b54a832222803eb956fd1"},
+ {file = "coverage-7.2.7-cp39-cp39-musllinux_1_1_aarch64.whl", hash = "sha256:b29019c76039dc3c0fd815c41392a044ce555d9bcdd38b0fb60fb4cd8e475ba9"},
+ {file = "coverage-7.2.7-cp39-cp39-musllinux_1_1_i686.whl", hash = "sha256:81c13a1fc7468c40f13420732805a4c38a105d89848b7c10af65a90beff25250"},
+ {file = "coverage-7.2.7-cp39-cp39-musllinux_1_1_x86_64.whl", hash = "sha256:975d70ab7e3c80a3fe86001d8751f6778905ec723f5b110aed1e450da9d4b7f2"},
+ {file = "coverage-7.2.7-cp39-cp39-win32.whl", hash = "sha256:7ee7d9d4822c8acc74a5e26c50604dff824710bc8de424904c0982e25c39c6cb"},
+ {file = "coverage-7.2.7-cp39-cp39-win_amd64.whl", hash = "sha256:eb393e5ebc85245347950143969b241d08b52b88a3dc39479822e073a1a8eb27"},
+ {file = "coverage-7.2.7-pp37.pp38.pp39-none-any.whl", hash = "sha256:b7b4c971f05e6ae490fef852c218b0e79d4e52f79ef0c8475566584a8fb3e01d"},
+ {file = "coverage-7.2.7.tar.gz", hash = "sha256:924d94291ca674905fe9481f12294eb11f2d3d3fd1adb20314ba89e94f44ed59"},
]
[package.extras]
@@ -301,13 +325,13 @@ packaging = ">=20.9"
[[package]]
name = "exceptiongroup"
-version = "1.1.1"
+version = "1.1.3"
description = "Backport of PEP 654 (exception groups)"
optional = false
python-versions = ">=3.7"
files = [
- {file = "exceptiongroup-1.1.1-py3-none-any.whl", hash = "sha256:232c37c63e4f682982c8b6459f33a8981039e5fb8756b2074364e5055c498c9e"},
- {file = "exceptiongroup-1.1.1.tar.gz", hash = "sha256:d484c3090ba2889ae2928419117447a14daf3c1231d5e30d0aae34f354f01785"},
+ {file = "exceptiongroup-1.1.3-py3-none-any.whl", hash = "sha256:343280667a4585d195ca1cf9cef84a4e178c4b6cf2274caef9859782b567d5e3"},
+ {file = "exceptiongroup-1.1.3.tar.gz", hash = "sha256:097acd85d473d75af5bb98e41b61ff7fe35efe6675e4f9370ec6ec5126d160e9"},
]
[package.extras]
@@ -329,19 +353,22 @@ smmap = ">=3.0.1,<6"
[[package]]
name = "gitpython"
-version = "3.1.35"
+version = "3.1.37"
description = "GitPython is a Python library used to interact with Git repositories"
optional = false
python-versions = ">=3.7"
files = [
- {file = "GitPython-3.1.35-py3-none-any.whl", hash = "sha256:c19b4292d7a1d3c0f653858db273ff8a6614100d1eb1528b014ec97286193c09"},
- {file = "GitPython-3.1.35.tar.gz", hash = "sha256:9cbefbd1789a5fe9bcf621bb34d3f441f3a90c8461d377f84eda73e721d9b06b"},
+ {file = "GitPython-3.1.37-py3-none-any.whl", hash = "sha256:5f4c4187de49616d710a77e98ddf17b4782060a1788df441846bddefbb89ab33"},
+ {file = "GitPython-3.1.37.tar.gz", hash = "sha256:f9b9ddc0761c125d5780eab2d64be4873fc6817c2899cbcb34b02344bdc7bc54"},
]
[package.dependencies]
gitdb = ">=4.0.1,<5"
typing-extensions = {version = ">=3.7.4.3", markers = "python_version < \"3.8\""}
+[package.extras]
+test = ["black", "coverage[toml]", "ddt (>=1.1.1,!=1.4.3)", "mypy", "pre-commit", "pytest", "pytest-cov", "pytest-sugar"]
+
[[package]]
name = "idna"
version = "3.4"
@@ -355,13 +382,13 @@ files = [
[[package]]
name = "importlib-metadata"
-version = "6.6.0"
+version = "6.7.0"
description = "Read metadata from Python packages"
optional = false
python-versions = ">=3.7"
files = [
- {file = "importlib_metadata-6.6.0-py3-none-any.whl", hash = "sha256:43dd286a2cd8995d5eaef7fee2066340423b818ed3fd70adf0bad5f1fac53fed"},
- {file = "importlib_metadata-6.6.0.tar.gz", hash = "sha256:92501cdf9cc66ebd3e612f1b4f0c0765dfa42f0fa38ffb319b6bd84dd675d705"},
+ {file = "importlib_metadata-6.7.0-py3-none-any.whl", hash = "sha256:cb52082e659e97afc5dac71e79de97d8681de3aa07ff18578330904a9d18e5b5"},
+ {file = "importlib_metadata-6.7.0.tar.gz", hash = "sha256:1aaf550d4f73e5d6783e7acb77aec43d49da8017410afae93822cc9cca98c4d4"},
]
[package.dependencies]
@@ -371,7 +398,7 @@ zipp = ">=0.5"
[package.extras]
docs = ["furo", "jaraco.packaging (>=9)", "jaraco.tidelift (>=1.4)", "rst.linker (>=1.9)", "sphinx (>=3.5)", "sphinx-lint"]
perf = ["ipython"]
-testing = ["flake8 (<5)", "flufl.flake8", "importlib-resources (>=1.3)", "packaging", "pyfakefs", "pytest (>=6)", "pytest-black (>=0.3.7)", "pytest-checkdocs (>=2.4)", "pytest-cov", "pytest-enabler (>=1.3)", "pytest-flake8", "pytest-mypy (>=0.9.1)", "pytest-perf (>=0.9.2)"]
+testing = ["flufl.flake8", "importlib-resources (>=1.3)", "packaging", "pyfakefs", "pytest (>=6)", "pytest-black (>=0.3.7)", "pytest-checkdocs (>=2.4)", "pytest-cov", "pytest-enabler (>=1.3)", "pytest-mypy (>=0.9.1)", "pytest-perf (>=0.9.2)", "pytest-ruff"]
[[package]]
name = "iniconfig"
@@ -386,13 +413,13 @@ files = [
[[package]]
name = "macholib"
-version = "1.16.2"
+version = "1.16.3"
description = "Mach-O header analysis and editing"
optional = false
python-versions = "*"
files = [
- {file = "macholib-1.16.2-py2.py3-none-any.whl", hash = "sha256:44c40f2cd7d6726af8fa6fe22549178d3a4dfecc35a9cd15ea916d9c83a688e0"},
- {file = "macholib-1.16.2.tar.gz", hash = "sha256:557bbfa1bb255c20e9abafe7ed6cd8046b48d9525db2f9b77d3122a63a2a8bf8"},
+ {file = "macholib-1.16.3-py2.py3-none-any.whl", hash = "sha256:0e315d7583d38b8c77e815b1ecbdbf504a8258d8b3e17b61165c6feb60d18f2c"},
+ {file = "macholib-1.16.3.tar.gz", hash = "sha256:07ae9e15e8e4cd9a788013d81f5908b3609aa76f9b1421bae9c4d7606ec86a30"},
]
[package.dependencies]
@@ -444,24 +471,24 @@ files = [
[[package]]
name = "packaging"
-version = "23.1"
+version = "23.2"
description = "Core utilities for Python packages"
optional = false
python-versions = ">=3.7"
files = [
- {file = "packaging-23.1-py3-none-any.whl", hash = "sha256:994793af429502c4ea2ebf6bf664629d07c1a9fe974af92966e4b8d2df7edc61"},
- {file = "packaging-23.1.tar.gz", hash = "sha256:a392980d2b6cffa644431898be54b0045151319d1e7ec34f0cfed48767dd334f"},
+ {file = "packaging-23.2-py3-none-any.whl", hash = "sha256:8c491190033a9af7e1d931d0b5dacc2ef47509b34dd0de67ed209b5203fc88c7"},
+ {file = "packaging-23.2.tar.gz", hash = "sha256:048fb0e9405036518eaaf48a55953c750c11e1a1b68e0dd1a9d62ed0c092cfc5"},
]
[[package]]
name = "pathspec"
-version = "0.11.1"
+version = "0.11.2"
description = "Utility library for gitignore style pattern matching of file paths."
optional = false
python-versions = ">=3.7"
files = [
- {file = "pathspec-0.11.1-py3-none-any.whl", hash = "sha256:d8af70af76652554bd134c22b3e8a1cc46ed7d91edcdd721ef1a0c51a84a5293"},
- {file = "pathspec-0.11.1.tar.gz", hash = "sha256:2798de800fa92780e33acca925945e9a19a133b715067cf165b8866c15a31687"},
+ {file = "pathspec-0.11.2-py3-none-any.whl", hash = "sha256:1d6ed233af05e679efb96b1851550ea95bbb64b7c490b0f5aa52996c11e92a20"},
+ {file = "pathspec-0.11.2.tar.gz", hash = "sha256:e0d8d0ac2f12da61956eb2306b69f9469b42f4deb0f3cb6ed47b9cce9996ced3"},
]
[[package]]
@@ -477,31 +504,31 @@ files = [
[[package]]
name = "platformdirs"
-version = "3.8.0"
+version = "3.11.0"
description = "A small Python package for determining appropriate platform-specific dirs, e.g. a \"user data dir\"."
optional = false
python-versions = ">=3.7"
files = [
- {file = "platformdirs-3.8.0-py3-none-any.whl", hash = "sha256:ca9ed98ce73076ba72e092b23d3c93ea6c4e186b3f1c3dad6edd98ff6ffcca2e"},
- {file = "platformdirs-3.8.0.tar.gz", hash = "sha256:b0cabcb11063d21a0b261d557acb0a9d2126350e63b70cdf7db6347baea456dc"},
+ {file = "platformdirs-3.11.0-py3-none-any.whl", hash = "sha256:e9d171d00af68be50e9202731309c4e658fd8bc76f55c11c7dd760d023bda68e"},
+ {file = "platformdirs-3.11.0.tar.gz", hash = "sha256:cf8ee52a3afdb965072dcc652433e0c7e3e40cf5ea1477cd4b3b1d2eb75495b3"},
]
[package.dependencies]
-typing-extensions = {version = ">=4.6.3", markers = "python_version < \"3.8\""}
+typing-extensions = {version = ">=4.7.1", markers = "python_version < \"3.8\""}
[package.extras]
-docs = ["furo (>=2023.5.20)", "proselint (>=0.13)", "sphinx (>=7.0.1)", "sphinx-autodoc-typehints (>=1.23,!=1.23.4)"]
-test = ["appdirs (==1.4.4)", "covdefaults (>=2.3)", "pytest (>=7.3.1)", "pytest-cov (>=4.1)", "pytest-mock (>=3.10)"]
+docs = ["furo (>=2023.7.26)", "proselint (>=0.13)", "sphinx (>=7.1.1)", "sphinx-autodoc-typehints (>=1.24)"]
+test = ["appdirs (==1.4.4)", "covdefaults (>=2.3)", "pytest (>=7.4)", "pytest-cov (>=4.1)", "pytest-mock (>=3.11.1)"]
[[package]]
name = "pluggy"
-version = "1.0.0"
+version = "1.2.0"
description = "plugin and hook calling mechanisms for python"
optional = false
-python-versions = ">=3.6"
+python-versions = ">=3.7"
files = [
- {file = "pluggy-1.0.0-py2.py3-none-any.whl", hash = "sha256:74134bbf457f031a36d68416e1509f34bd5ccc019f0bcc952c7b909d06b37bd3"},
- {file = "pluggy-1.0.0.tar.gz", hash = "sha256:4224373bacce55f955a878bf9cfa763c1e360858e330072059e10bad68531159"},
+ {file = "pluggy-1.2.0-py3-none-any.whl", hash = "sha256:c2fd55a7d7a3863cba1a013e4e2414658b1d07b6bc57b3919e0c63c9abb99849"},
+ {file = "pluggy-1.2.0.tar.gz", hash = "sha256:d12f0c4b579b15f5e054301bb226ee85eeeba08ffec228092f8defbaa3a4c4b3"},
]
[package.dependencies]
@@ -513,23 +540,23 @@ testing = ["pytest", "pytest-benchmark"]
[[package]]
name = "pyinstaller"
-version = "5.11.0"
+version = "5.13.2"
description = "PyInstaller bundles a Python application and all its dependencies into a single package."
optional = false
-python-versions = "<3.12,>=3.7"
+python-versions = "<3.13,>=3.7"
files = [
- {file = "pyinstaller-5.11.0-py3-none-macosx_10_13_universal2.whl", hash = "sha256:8454bac8f3cb2219a3ce2227fd039bdaf943dcba60e8c55732958ea3a6d81263"},
- {file = "pyinstaller-5.11.0-py3-none-manylinux2014_aarch64.whl", hash = "sha256:b3c6299fd7526c6ca87ea5f9017fb1928d47046df0b9f983d6bbd893801010dc"},
- {file = "pyinstaller-5.11.0-py3-none-manylinux2014_i686.whl", hash = "sha256:e359571327bbef434fc61324891399f9117efbb685b5065234eebb01713650a8"},
- {file = "pyinstaller-5.11.0-py3-none-manylinux2014_ppc64le.whl", hash = "sha256:a445a91b85c9a1ea3985268643a674900dd86f244cc4be4ff4ec4c6367ff99a9"},
- {file = "pyinstaller-5.11.0-py3-none-manylinux2014_s390x.whl", hash = "sha256:2a1fe6d0da22f207cfa4b3221fe365503cba071c77aac19f76a75503f67d9ff9"},
- {file = "pyinstaller-5.11.0-py3-none-manylinux2014_x86_64.whl", hash = "sha256:b4cac0e7b0d63c6a869843113008f59fd5b38b2959ffa6059e7fac4bb05de92b"},
- {file = "pyinstaller-5.11.0-py3-none-musllinux_1_1_aarch64.whl", hash = "sha256:0af9d11a09ce217d32f95c79c984054457b310671387ff32bae1496876308556"},
- {file = "pyinstaller-5.11.0-py3-none-musllinux_1_1_x86_64.whl", hash = "sha256:b8a4f6834e5c85150948e22c74dd3ab8b98aa4ccdf964d880ac14d2f78d9c1a4"},
- {file = "pyinstaller-5.11.0-py3-none-win32.whl", hash = "sha256:049cdc3524aefb5ca015a63d2c81b6bf1567cc818ac066859fbfde702c6165d3"},
- {file = "pyinstaller-5.11.0-py3-none-win_amd64.whl", hash = "sha256:42fdea67e4c2217cedd54d17d1d402736df3ba718db2b497df65df5a68ae4f93"},
- {file = "pyinstaller-5.11.0-py3-none-win_arm64.whl", hash = "sha256:036a062a228af41f6bb6370a4e87cef34858cc839200a07ace7f8738ef64ad86"},
- {file = "pyinstaller-5.11.0.tar.gz", hash = "sha256:cb87cee0b3c81ccd74d4bf3f4faf03b5e1e39bb91f1a894b2ce4cd22363bf779"},
+ {file = "pyinstaller-5.13.2-py3-none-macosx_10_13_universal2.whl", hash = "sha256:16cbd66b59a37f4ee59373a003608d15df180a0d9eb1a29ff3bfbfae64b23d0f"},
+ {file = "pyinstaller-5.13.2-py3-none-manylinux2014_aarch64.whl", hash = "sha256:8f6dd0e797ae7efdd79226f78f35eb6a4981db16c13325e962a83395c0ec7420"},
+ {file = "pyinstaller-5.13.2-py3-none-manylinux2014_i686.whl", hash = "sha256:65133ed89467edb2862036b35d7c5ebd381670412e1e4361215e289c786dd4e6"},
+ {file = "pyinstaller-5.13.2-py3-none-manylinux2014_ppc64le.whl", hash = "sha256:7d51734423685ab2a4324ab2981d9781b203dcae42839161a9ee98bfeaabdade"},
+ {file = "pyinstaller-5.13.2-py3-none-manylinux2014_s390x.whl", hash = "sha256:2c2fe9c52cb4577a3ac39626b84cf16cf30c2792f785502661286184f162ae0d"},
+ {file = "pyinstaller-5.13.2-py3-none-manylinux2014_x86_64.whl", hash = "sha256:c63ef6133eefe36c4b2f4daf4cfea3d6412ece2ca218f77aaf967e52a95ac9b8"},
+ {file = "pyinstaller-5.13.2-py3-none-musllinux_1_1_aarch64.whl", hash = "sha256:aadafb6f213549a5906829bb252e586e2cf72a7fbdb5731810695e6516f0ab30"},
+ {file = "pyinstaller-5.13.2-py3-none-musllinux_1_1_x86_64.whl", hash = "sha256:b2e1c7f5cceb5e9800927ddd51acf9cc78fbaa9e79e822c48b0ee52d9ce3c892"},
+ {file = "pyinstaller-5.13.2-py3-none-win32.whl", hash = "sha256:421cd24f26144f19b66d3868b49ed673176765f92fa9f7914cd2158d25b6d17e"},
+ {file = "pyinstaller-5.13.2-py3-none-win_amd64.whl", hash = "sha256:ddcc2b36052a70052479a9e5da1af067b4496f43686ca3cdda99f8367d0627e4"},
+ {file = "pyinstaller-5.13.2-py3-none-win_arm64.whl", hash = "sha256:27cd64e7cc6b74c5b1066cbf47d75f940b71356166031deb9778a2579bb874c6"},
+ {file = "pyinstaller-5.13.2.tar.gz", hash = "sha256:c8e5d3489c3a7cc5f8401c2d1f48a70e588f9967e391c3b06ddac1f685f8d5d2"},
]
[package.dependencies]
@@ -538,7 +565,7 @@ importlib-metadata = {version = ">=1.4", markers = "python_version < \"3.8\""}
macholib = {version = ">=1.8", markers = "sys_platform == \"darwin\""}
pefile = {version = ">=2022.5.30", markers = "sys_platform == \"win32\""}
pyinstaller-hooks-contrib = ">=2021.4"
-pywin32-ctypes = {version = ">=0.2.0", markers = "sys_platform == \"win32\""}
+pywin32-ctypes = {version = ">=0.2.1", markers = "sys_platform == \"win32\""}
setuptools = ">=42.0.0"
[package.extras]
@@ -547,24 +574,24 @@ hook-testing = ["execnet (>=1.5.0)", "psutil", "pytest (>=2.7.3)"]
[[package]]
name = "pyinstaller-hooks-contrib"
-version = "2023.3"
+version = "2023.9"
description = "Community maintained hooks for PyInstaller"
optional = false
python-versions = ">=3.7"
files = [
- {file = "pyinstaller-hooks-contrib-2023.3.tar.gz", hash = "sha256:bb39e1038e3e0972420455e0b39cd9dce73f3d80acaf4bf2b3615fea766ff370"},
- {file = "pyinstaller_hooks_contrib-2023.3-py2.py3-none-any.whl", hash = "sha256:062ad7a1746e1cfc24d3a8c4be4e606fced3b123bda7d419f14fcf7507804b07"},
+ {file = "pyinstaller-hooks-contrib-2023.9.tar.gz", hash = "sha256:76084b5988e3957a9df169d2a935d65500136967e710ddebf57263f1a909cd80"},
+ {file = "pyinstaller_hooks_contrib-2023.9-py2.py3-none-any.whl", hash = "sha256:f34f4c6807210025c8073ebe665f422a3aa2ac5f4c7ebf4c2a26cc77bebf63b5"},
]
[[package]]
name = "pytest"
-version = "7.3.1"
+version = "7.3.2"
description = "pytest: simple powerful testing with Python"
optional = false
python-versions = ">=3.7"
files = [
- {file = "pytest-7.3.1-py3-none-any.whl", hash = "sha256:3799fa815351fea3a5e96ac7e503a96fa51cc9942c3753cda7651b93c1cfa362"},
- {file = "pytest-7.3.1.tar.gz", hash = "sha256:434afafd78b1d78ed0addf160ad2b77a30d35d4bdf8af234fe621919d9ed15e3"},
+ {file = "pytest-7.3.2-py3-none-any.whl", hash = "sha256:cdcbd012c9312258922f8cd3f1b62a6580fdced17db6014896053d47cddf9295"},
+ {file = "pytest-7.3.2.tar.gz", hash = "sha256:ee990a3cc55ba808b80795a79944756f315c67c12b56abd3ac993a7b8c17030b"},
]
[package.dependencies]
@@ -577,7 +604,7 @@ pluggy = ">=0.12,<2.0"
tomli = {version = ">=1.0.0", markers = "python_version < \"3.11\""}
[package.extras]
-testing = ["argcomplete", "attrs (>=19.2.0)", "hypothesis (>=3.56)", "mock", "nose", "pygments (>=2.7.2)", "requests", "xmlschema"]
+testing = ["argcomplete", "attrs (>=19.2.0)", "hypothesis (>=3.56)", "mock", "nose", "pygments (>=2.7.2)", "requests", "setuptools", "xmlschema"]
[[package]]
name = "pytest-mock"
@@ -612,62 +639,62 @@ six = ">=1.5"
[[package]]
name = "pywin32-ctypes"
-version = "0.2.0"
-description = ""
+version = "0.2.2"
+description = "A (partial) reimplementation of pywin32 using ctypes/cffi"
optional = false
-python-versions = "*"
+python-versions = ">=3.6"
files = [
- {file = "pywin32-ctypes-0.2.0.tar.gz", hash = "sha256:24ffc3b341d457d48e8922352130cf2644024a4ff09762a2261fd34c36ee5942"},
- {file = "pywin32_ctypes-0.2.0-py2.py3-none-any.whl", hash = "sha256:9dc2d991b3479cc2df15930958b674a48a227d5361d413827a4cfd0b5876fc98"},
+ {file = "pywin32-ctypes-0.2.2.tar.gz", hash = "sha256:3426e063bdd5fd4df74a14fa3cf80a0b42845a87e1d1e81f6549f9daec593a60"},
+ {file = "pywin32_ctypes-0.2.2-py3-none-any.whl", hash = "sha256:bf490a1a709baf35d688fe0ecf980ed4de11d2b3e37b51e5442587a75d9957e7"},
]
[[package]]
name = "pyyaml"
-version = "6.0"
+version = "6.0.1"
description = "YAML parser and emitter for Python"
optional = false
python-versions = ">=3.6"
files = [
- {file = "PyYAML-6.0-cp310-cp310-macosx_10_9_x86_64.whl", hash = "sha256:d4db7c7aef085872ef65a8fd7d6d09a14ae91f691dec3e87ee5ee0539d516f53"},
- {file = "PyYAML-6.0-cp310-cp310-macosx_11_0_arm64.whl", hash = "sha256:9df7ed3b3d2e0ecfe09e14741b857df43adb5a3ddadc919a2d94fbdf78fea53c"},
- {file = "PyYAML-6.0-cp310-cp310-manylinux_2_17_aarch64.manylinux2014_aarch64.whl", hash = "sha256:77f396e6ef4c73fdc33a9157446466f1cff553d979bd00ecb64385760c6babdc"},
- {file = "PyYAML-6.0-cp310-cp310-manylinux_2_17_s390x.manylinux2014_s390x.whl", hash = "sha256:a80a78046a72361de73f8f395f1f1e49f956c6be882eed58505a15f3e430962b"},
- {file = "PyYAML-6.0-cp310-cp310-manylinux_2_5_x86_64.manylinux1_x86_64.manylinux_2_12_x86_64.manylinux2010_x86_64.whl", hash = "sha256:f84fbc98b019fef2ee9a1cb3ce93e3187a6df0b2538a651bfb890254ba9f90b5"},
- {file = "PyYAML-6.0-cp310-cp310-win32.whl", hash = "sha256:2cd5df3de48857ed0544b34e2d40e9fac445930039f3cfe4bcc592a1f836d513"},
- {file = "PyYAML-6.0-cp310-cp310-win_amd64.whl", hash = "sha256:daf496c58a8c52083df09b80c860005194014c3698698d1a57cbcfa182142a3a"},
- {file = "PyYAML-6.0-cp311-cp311-macosx_10_9_x86_64.whl", hash = "sha256:d4b0ba9512519522b118090257be113b9468d804b19d63c71dbcf4a48fa32358"},
- {file = "PyYAML-6.0-cp311-cp311-macosx_11_0_arm64.whl", hash = "sha256:81957921f441d50af23654aa6c5e5eaf9b06aba7f0a19c18a538dc7ef291c5a1"},
- {file = "PyYAML-6.0-cp311-cp311-manylinux_2_17_aarch64.manylinux2014_aarch64.whl", hash = "sha256:afa17f5bc4d1b10afd4466fd3a44dc0e245382deca5b3c353d8b757f9e3ecb8d"},
- {file = "PyYAML-6.0-cp311-cp311-manylinux_2_17_s390x.manylinux2014_s390x.whl", hash = "sha256:dbad0e9d368bb989f4515da330b88a057617d16b6a8245084f1b05400f24609f"},
- {file = "PyYAML-6.0-cp311-cp311-manylinux_2_17_x86_64.manylinux2014_x86_64.whl", hash = "sha256:432557aa2c09802be39460360ddffd48156e30721f5e8d917f01d31694216782"},
- {file = "PyYAML-6.0-cp311-cp311-win32.whl", hash = "sha256:bfaef573a63ba8923503d27530362590ff4f576c626d86a9fed95822a8255fd7"},
- {file = "PyYAML-6.0-cp311-cp311-win_amd64.whl", hash = "sha256:01b45c0191e6d66c470b6cf1b9531a771a83c1c4208272ead47a3ae4f2f603bf"},
- {file = "PyYAML-6.0-cp36-cp36m-macosx_10_9_x86_64.whl", hash = "sha256:897b80890765f037df3403d22bab41627ca8811ae55e9a722fd0392850ec4d86"},
- {file = "PyYAML-6.0-cp36-cp36m-manylinux_2_17_aarch64.manylinux2014_aarch64.whl", hash = "sha256:50602afada6d6cbfad699b0c7bb50d5ccffa7e46a3d738092afddc1f9758427f"},
- {file = "PyYAML-6.0-cp36-cp36m-manylinux_2_17_s390x.manylinux2014_s390x.whl", hash = "sha256:48c346915c114f5fdb3ead70312bd042a953a8ce5c7106d5bfb1a5254e47da92"},
- {file = "PyYAML-6.0-cp36-cp36m-manylinux_2_5_x86_64.manylinux1_x86_64.manylinux_2_12_x86_64.manylinux2010_x86_64.whl", hash = "sha256:98c4d36e99714e55cfbaaee6dd5badbc9a1ec339ebfc3b1f52e293aee6bb71a4"},
- {file = "PyYAML-6.0-cp36-cp36m-win32.whl", hash = "sha256:0283c35a6a9fbf047493e3a0ce8d79ef5030852c51e9d911a27badfde0605293"},
- {file = "PyYAML-6.0-cp36-cp36m-win_amd64.whl", hash = "sha256:07751360502caac1c067a8132d150cf3d61339af5691fe9e87803040dbc5db57"},
- {file = "PyYAML-6.0-cp37-cp37m-macosx_10_9_x86_64.whl", hash = "sha256:819b3830a1543db06c4d4b865e70ded25be52a2e0631ccd2f6a47a2822f2fd7c"},
- {file = "PyYAML-6.0-cp37-cp37m-manylinux_2_17_aarch64.manylinux2014_aarch64.whl", hash = "sha256:473f9edb243cb1935ab5a084eb238d842fb8f404ed2193a915d1784b5a6b5fc0"},
- {file = "PyYAML-6.0-cp37-cp37m-manylinux_2_17_s390x.manylinux2014_s390x.whl", hash = "sha256:0ce82d761c532fe4ec3f87fc45688bdd3a4c1dc5e0b4a19814b9009a29baefd4"},
- {file = "PyYAML-6.0-cp37-cp37m-manylinux_2_5_x86_64.manylinux1_x86_64.manylinux_2_12_x86_64.manylinux2010_x86_64.whl", hash = "sha256:231710d57adfd809ef5d34183b8ed1eeae3f76459c18fb4a0b373ad56bedcdd9"},
- {file = "PyYAML-6.0-cp37-cp37m-win32.whl", hash = "sha256:c5687b8d43cf58545ade1fe3e055f70eac7a5a1a0bf42824308d868289a95737"},
- {file = "PyYAML-6.0-cp37-cp37m-win_amd64.whl", hash = "sha256:d15a181d1ecd0d4270dc32edb46f7cb7733c7c508857278d3d378d14d606db2d"},
- {file = "PyYAML-6.0-cp38-cp38-macosx_10_9_x86_64.whl", hash = "sha256:0b4624f379dab24d3725ffde76559cff63d9ec94e1736b556dacdfebe5ab6d4b"},
- {file = "PyYAML-6.0-cp38-cp38-manylinux_2_17_aarch64.manylinux2014_aarch64.whl", hash = "sha256:213c60cd50106436cc818accf5baa1aba61c0189ff610f64f4a3e8c6726218ba"},
- {file = "PyYAML-6.0-cp38-cp38-manylinux_2_17_s390x.manylinux2014_s390x.whl", hash = "sha256:9fa600030013c4de8165339db93d182b9431076eb98eb40ee068700c9c813e34"},
- {file = "PyYAML-6.0-cp38-cp38-manylinux_2_5_x86_64.manylinux1_x86_64.manylinux_2_12_x86_64.manylinux2010_x86_64.whl", hash = "sha256:277a0ef2981ca40581a47093e9e2d13b3f1fbbeffae064c1d21bfceba2030287"},
- {file = "PyYAML-6.0-cp38-cp38-win32.whl", hash = "sha256:d4eccecf9adf6fbcc6861a38015c2a64f38b9d94838ac1810a9023a0609e1b78"},
- {file = "PyYAML-6.0-cp38-cp38-win_amd64.whl", hash = "sha256:1e4747bc279b4f613a09eb64bba2ba602d8a6664c6ce6396a4d0cd413a50ce07"},
- {file = "PyYAML-6.0-cp39-cp39-macosx_10_9_x86_64.whl", hash = "sha256:055d937d65826939cb044fc8c9b08889e8c743fdc6a32b33e2390f66013e449b"},
- {file = "PyYAML-6.0-cp39-cp39-macosx_11_0_arm64.whl", hash = "sha256:e61ceaab6f49fb8bdfaa0f92c4b57bcfbea54c09277b1b4f7ac376bfb7a7c174"},
- {file = "PyYAML-6.0-cp39-cp39-manylinux_2_17_aarch64.manylinux2014_aarch64.whl", hash = "sha256:d67d839ede4ed1b28a4e8909735fc992a923cdb84e618544973d7dfc71540803"},
- {file = "PyYAML-6.0-cp39-cp39-manylinux_2_17_s390x.manylinux2014_s390x.whl", hash = "sha256:cba8c411ef271aa037d7357a2bc8f9ee8b58b9965831d9e51baf703280dc73d3"},
- {file = "PyYAML-6.0-cp39-cp39-manylinux_2_5_x86_64.manylinux1_x86_64.manylinux_2_12_x86_64.manylinux2010_x86_64.whl", hash = "sha256:40527857252b61eacd1d9af500c3337ba8deb8fc298940291486c465c8b46ec0"},
- {file = "PyYAML-6.0-cp39-cp39-win32.whl", hash = "sha256:b5b9eccad747aabaaffbc6064800670f0c297e52c12754eb1d976c57e4f74dcb"},
- {file = "PyYAML-6.0-cp39-cp39-win_amd64.whl", hash = "sha256:b3d267842bf12586ba6c734f89d1f5b871df0273157918b0ccefa29deb05c21c"},
- {file = "PyYAML-6.0.tar.gz", hash = "sha256:68fb519c14306fec9720a2a5b45bc9f0c8d1b9c72adf45c37baedfcd949c35a2"},
+ {file = "PyYAML-6.0.1-cp310-cp310-macosx_10_9_x86_64.whl", hash = "sha256:d858aa552c999bc8a8d57426ed01e40bef403cd8ccdd0fc5f6f04a00414cac2a"},
+ {file = "PyYAML-6.0.1-cp310-cp310-macosx_11_0_arm64.whl", hash = "sha256:fd66fc5d0da6d9815ba2cebeb4205f95818ff4b79c3ebe268e75d961704af52f"},
+ {file = "PyYAML-6.0.1-cp310-cp310-manylinux_2_17_aarch64.manylinux2014_aarch64.whl", hash = "sha256:69b023b2b4daa7548bcfbd4aa3da05b3a74b772db9e23b982788168117739938"},
+ {file = "PyYAML-6.0.1-cp310-cp310-manylinux_2_17_s390x.manylinux2014_s390x.whl", hash = "sha256:81e0b275a9ecc9c0c0c07b4b90ba548307583c125f54d5b6946cfee6360c733d"},
+ {file = "PyYAML-6.0.1-cp310-cp310-manylinux_2_17_x86_64.manylinux2014_x86_64.whl", hash = "sha256:ba336e390cd8e4d1739f42dfe9bb83a3cc2e80f567d8805e11b46f4a943f5515"},
+ {file = "PyYAML-6.0.1-cp310-cp310-win32.whl", hash = "sha256:bd4af7373a854424dabd882decdc5579653d7868b8fb26dc7d0e99f823aa5924"},
+ {file = "PyYAML-6.0.1-cp310-cp310-win_amd64.whl", hash = "sha256:fd1592b3fdf65fff2ad0004b5e363300ef59ced41c2e6b3a99d4089fa8c5435d"},
+ {file = "PyYAML-6.0.1-cp311-cp311-macosx_10_9_x86_64.whl", hash = "sha256:6965a7bc3cf88e5a1c3bd2e0b5c22f8d677dc88a455344035f03399034eb3007"},
+ {file = "PyYAML-6.0.1-cp311-cp311-macosx_11_0_arm64.whl", hash = "sha256:f003ed9ad21d6a4713f0a9b5a7a0a79e08dd0f221aff4525a2be4c346ee60aab"},
+ {file = "PyYAML-6.0.1-cp311-cp311-manylinux_2_17_aarch64.manylinux2014_aarch64.whl", hash = "sha256:42f8152b8dbc4fe7d96729ec2b99c7097d656dc1213a3229ca5383f973a5ed6d"},
+ {file = "PyYAML-6.0.1-cp311-cp311-manylinux_2_17_s390x.manylinux2014_s390x.whl", hash = "sha256:062582fca9fabdd2c8b54a3ef1c978d786e0f6b3a1510e0ac93ef59e0ddae2bc"},
+ {file = "PyYAML-6.0.1-cp311-cp311-manylinux_2_17_x86_64.manylinux2014_x86_64.whl", hash = "sha256:d2b04aac4d386b172d5b9692e2d2da8de7bfb6c387fa4f801fbf6fb2e6ba4673"},
+ {file = "PyYAML-6.0.1-cp311-cp311-win32.whl", hash = "sha256:1635fd110e8d85d55237ab316b5b011de701ea0f29d07611174a1b42f1444741"},
+ {file = "PyYAML-6.0.1-cp311-cp311-win_amd64.whl", hash = "sha256:bf07ee2fef7014951eeb99f56f39c9bb4af143d8aa3c21b1677805985307da34"},
+ {file = "PyYAML-6.0.1-cp36-cp36m-macosx_10_9_x86_64.whl", hash = "sha256:50550eb667afee136e9a77d6dc71ae76a44df8b3e51e41b77f6de2932bfe0f47"},
+ {file = "PyYAML-6.0.1-cp36-cp36m-manylinux_2_17_aarch64.manylinux2014_aarch64.whl", hash = "sha256:1fe35611261b29bd1de0070f0b2f47cb6ff71fa6595c077e42bd0c419fa27b98"},
+ {file = "PyYAML-6.0.1-cp36-cp36m-manylinux_2_17_s390x.manylinux2014_s390x.whl", hash = "sha256:704219a11b772aea0d8ecd7058d0082713c3562b4e271b849ad7dc4a5c90c13c"},
+ {file = "PyYAML-6.0.1-cp36-cp36m-manylinux_2_17_x86_64.manylinux2014_x86_64.whl", hash = "sha256:afd7e57eddb1a54f0f1a974bc4391af8bcce0b444685d936840f125cf046d5bd"},
+ {file = "PyYAML-6.0.1-cp36-cp36m-win32.whl", hash = "sha256:fca0e3a251908a499833aa292323f32437106001d436eca0e6e7833256674585"},
+ {file = "PyYAML-6.0.1-cp36-cp36m-win_amd64.whl", hash = "sha256:f22ac1c3cac4dbc50079e965eba2c1058622631e526bd9afd45fedd49ba781fa"},
+ {file = "PyYAML-6.0.1-cp37-cp37m-macosx_10_9_x86_64.whl", hash = "sha256:b1275ad35a5d18c62a7220633c913e1b42d44b46ee12554e5fd39c70a243d6a3"},
+ {file = "PyYAML-6.0.1-cp37-cp37m-manylinux_2_17_aarch64.manylinux2014_aarch64.whl", hash = "sha256:18aeb1bf9a78867dc38b259769503436b7c72f7a1f1f4c93ff9a17de54319b27"},
+ {file = "PyYAML-6.0.1-cp37-cp37m-manylinux_2_17_s390x.manylinux2014_s390x.whl", hash = "sha256:596106435fa6ad000c2991a98fa58eeb8656ef2325d7e158344fb33864ed87e3"},
+ {file = "PyYAML-6.0.1-cp37-cp37m-manylinux_2_17_x86_64.manylinux2014_x86_64.whl", hash = "sha256:baa90d3f661d43131ca170712d903e6295d1f7a0f595074f151c0aed377c9b9c"},
+ {file = "PyYAML-6.0.1-cp37-cp37m-win32.whl", hash = "sha256:9046c58c4395dff28dd494285c82ba00b546adfc7ef001486fbf0324bc174fba"},
+ {file = "PyYAML-6.0.1-cp37-cp37m-win_amd64.whl", hash = "sha256:4fb147e7a67ef577a588a0e2c17b6db51dda102c71de36f8549b6816a96e1867"},
+ {file = "PyYAML-6.0.1-cp38-cp38-macosx_10_9_x86_64.whl", hash = "sha256:1d4c7e777c441b20e32f52bd377e0c409713e8bb1386e1099c2415f26e479595"},
+ {file = "PyYAML-6.0.1-cp38-cp38-manylinux_2_17_aarch64.manylinux2014_aarch64.whl", hash = "sha256:a0cd17c15d3bb3fa06978b4e8958dcdc6e0174ccea823003a106c7d4d7899ac5"},
+ {file = "PyYAML-6.0.1-cp38-cp38-manylinux_2_17_s390x.manylinux2014_s390x.whl", hash = "sha256:28c119d996beec18c05208a8bd78cbe4007878c6dd15091efb73a30e90539696"},
+ {file = "PyYAML-6.0.1-cp38-cp38-manylinux_2_17_x86_64.manylinux2014_x86_64.whl", hash = "sha256:7e07cbde391ba96ab58e532ff4803f79c4129397514e1413a7dc761ccd755735"},
+ {file = "PyYAML-6.0.1-cp38-cp38-win32.whl", hash = "sha256:184c5108a2aca3c5b3d3bf9395d50893a7ab82a38004c8f61c258d4428e80206"},
+ {file = "PyYAML-6.0.1-cp38-cp38-win_amd64.whl", hash = "sha256:1e2722cc9fbb45d9b87631ac70924c11d3a401b2d7f410cc0e3bbf249f2dca62"},
+ {file = "PyYAML-6.0.1-cp39-cp39-macosx_10_9_x86_64.whl", hash = "sha256:9eb6caa9a297fc2c2fb8862bc5370d0303ddba53ba97e71f08023b6cd73d16a8"},
+ {file = "PyYAML-6.0.1-cp39-cp39-macosx_11_0_arm64.whl", hash = "sha256:c8098ddcc2a85b61647b2590f825f3db38891662cfc2fc776415143f599bb859"},
+ {file = "PyYAML-6.0.1-cp39-cp39-manylinux_2_17_aarch64.manylinux2014_aarch64.whl", hash = "sha256:5773183b6446b2c99bb77e77595dd486303b4faab2b086e7b17bc6bef28865f6"},
+ {file = "PyYAML-6.0.1-cp39-cp39-manylinux_2_17_s390x.manylinux2014_s390x.whl", hash = "sha256:b786eecbdf8499b9ca1d697215862083bd6d2a99965554781d0d8d1ad31e13a0"},
+ {file = "PyYAML-6.0.1-cp39-cp39-manylinux_2_17_x86_64.manylinux2014_x86_64.whl", hash = "sha256:bc1bf2925a1ecd43da378f4db9e4f799775d6367bdb94671027b73b393a7c42c"},
+ {file = "PyYAML-6.0.1-cp39-cp39-win32.whl", hash = "sha256:faca3bdcf85b2fc05d06ff3fbc1f83e1391b3e724afa3feba7d13eeab355484c"},
+ {file = "PyYAML-6.0.1-cp39-cp39-win_amd64.whl", hash = "sha256:510c9deebc5c0225e8c96813043e62b680ba2f9c50a08d3724c7f28a747d1486"},
+ {file = "PyYAML-6.0.1.tar.gz", hash = "sha256:bfdf460b1736c775f2ba9f6a92bca30bc2095067b8a9d77876d1fad6cc3b4a43"},
]
[[package]]
@@ -693,21 +720,21 @@ use-chardet-on-py3 = ["chardet (>=3.0.2,<6)"]
[[package]]
name = "responses"
-version = "0.23.1"
+version = "0.23.3"
description = "A utility library for mocking out the `requests` Python library."
optional = false
python-versions = ">=3.7"
files = [
- {file = "responses-0.23.1-py3-none-any.whl", hash = "sha256:8a3a5915713483bf353b6f4079ba8b2a29029d1d1090a503c70b0dc5d9d0c7bd"},
- {file = "responses-0.23.1.tar.gz", hash = "sha256:c4d9aa9fc888188f0c673eff79a8dadbe2e75b7fe879dc80a221a06e0a68138f"},
+ {file = "responses-0.23.3-py3-none-any.whl", hash = "sha256:e6fbcf5d82172fecc0aa1860fd91e58cbfd96cee5e96da5b63fa6eb3caa10dd3"},
+ {file = "responses-0.23.3.tar.gz", hash = "sha256:205029e1cb334c21cb4ec64fc7599be48b859a0fd381a42443cdd600bfe8b16a"},
]
[package.dependencies]
pyyaml = "*"
-requests = ">=2.22.0,<3.0"
+requests = ">=2.30.0,<3.0"
types-PyYAML = "*"
typing-extensions = {version = "*", markers = "python_version < \"3.8\""}
-urllib3 = ">=1.25.10"
+urllib3 = ">=1.25.10,<3.0"
[package.extras]
tests = ["coverage (>=6.0.0)", "flake8", "mypy", "pytest (>=7.0.0)", "pytest-asyncio", "pytest-cov", "pytest-httpserver", "tomli", "tomli-w", "types-requests"]
@@ -740,18 +767,18 @@ files = [
[[package]]
name = "setuptools"
-version = "67.7.2"
+version = "68.0.0"
description = "Easily download, build, install, upgrade, and uninstall Python packages"
optional = false
python-versions = ">=3.7"
files = [
- {file = "setuptools-67.7.2-py3-none-any.whl", hash = "sha256:23aaf86b85ca52ceb801d32703f12d77517b2556af839621c641fca11287952b"},
- {file = "setuptools-67.7.2.tar.gz", hash = "sha256:f104fa03692a2602fa0fec6c6a9e63b6c8a968de13e17c026957dd1f53d80990"},
+ {file = "setuptools-68.0.0-py3-none-any.whl", hash = "sha256:11e52c67415a381d10d6b462ced9cfb97066179f0e871399e006c4ab101fc85f"},
+ {file = "setuptools-68.0.0.tar.gz", hash = "sha256:baf1fdb41c6da4cd2eae722e135500da913332ab3f2f5c7d33af9b492acb5235"},
]
[package.extras]
docs = ["furo", "jaraco.packaging (>=9)", "jaraco.tidelift (>=1.4)", "pygments-github-lexers (==0.0.5)", "rst.linker (>=1.9)", "sphinx (>=3.5)", "sphinx-favicon", "sphinx-hoverxref (<2)", "sphinx-inline-tabs", "sphinx-lint", "sphinx-notfound-page (==0.8.3)", "sphinx-reredirects", "sphinxcontrib-towncrier"]
-testing = ["build[virtualenv]", "filelock (>=3.4.0)", "flake8 (<5)", "flake8-2020", "ini2toml[lite] (>=0.9)", "jaraco.envs (>=2.2)", "jaraco.path (>=3.2.0)", "pip (>=19.1)", "pip-run (>=8.8)", "pytest (>=6)", "pytest-black (>=0.3.7)", "pytest-checkdocs (>=2.4)", "pytest-cov", "pytest-enabler (>=1.3)", "pytest-flake8", "pytest-mypy (>=0.9.1)", "pytest-perf", "pytest-timeout", "pytest-xdist", "tomli-w (>=1.0.0)", "virtualenv (>=13.0.0)", "wheel"]
+testing = ["build[virtualenv]", "filelock (>=3.4.0)", "flake8-2020", "ini2toml[lite] (>=0.9)", "jaraco.envs (>=2.2)", "jaraco.path (>=3.2.0)", "pip (>=19.1)", "pip-run (>=8.8)", "pytest (>=6)", "pytest-black (>=0.3.7)", "pytest-checkdocs (>=2.4)", "pytest-cov", "pytest-enabler (>=1.3)", "pytest-mypy (>=0.9.1)", "pytest-perf", "pytest-ruff", "pytest-timeout", "pytest-xdist", "tomli-w (>=1.0.0)", "virtualenv (>=13.0.0)", "wheel"]
testing-integration = ["build[virtualenv]", "filelock (>=3.4.0)", "jaraco.envs (>=2.2)", "jaraco.path (>=3.2.0)", "pytest", "pytest-enabler", "pytest-xdist", "tomli", "virtualenv (>=13.0.0)", "wheel"]
[[package]]
@@ -767,13 +794,13 @@ files = [
[[package]]
name = "smmap"
-version = "5.0.0"
+version = "5.0.1"
description = "A pure Python implementation of a sliding window memory map manager"
optional = false
-python-versions = ">=3.6"
+python-versions = ">=3.7"
files = [
- {file = "smmap-5.0.0-py3-none-any.whl", hash = "sha256:2aba19d6a040e78d8b09de5c57e96207b09ed71d8e55ce0959eeee6c8e190d94"},
- {file = "smmap-5.0.0.tar.gz", hash = "sha256:c840e62059cd3be204b0c9c9f74be2c09d5648eddd4580d9314c3ecde0b30936"},
+ {file = "smmap-5.0.1-py3-none-any.whl", hash = "sha256:e6d8668fa5f93e706934a62d7b4db19c8d9eb8cf2adbb75ef1b675aa332b69da"},
+ {file = "smmap-5.0.1.tar.gz", hash = "sha256:dceeb6c0028fdb6734471eb07c0cd2aae706ccaecab45965ee83f11c8d3b1f62"},
]
[[package]]
@@ -850,13 +877,13 @@ files = [
[[package]]
name = "types-pyyaml"
-version = "6.0.12.9"
+version = "6.0.12.12"
description = "Typing stubs for PyYAML"
optional = false
python-versions = "*"
files = [
- {file = "types-PyYAML-6.0.12.9.tar.gz", hash = "sha256:c51b1bd6d99ddf0aa2884a7a328810ebf70a4262c292195d3f4f9a0005f9eeb6"},
- {file = "types_PyYAML-6.0.12.9-py3-none-any.whl", hash = "sha256:5aed5aa66bd2d2e158f75dda22b059570ede988559f030cf294871d3b647e3e8"},
+ {file = "types-PyYAML-6.0.12.12.tar.gz", hash = "sha256:334373d392fde0fdf95af5c3f1661885fa10c52167b14593eb856289e1855062"},
+ {file = "types_PyYAML-6.0.12.12-py3-none-any.whl", hash = "sha256:c05bc6c158facb0676674b7f11fe3960db4f389718e19e62bd2b84d6205cfd24"},
]
[[package]]
@@ -903,5 +930,5 @@ testing = ["big-O", "flake8 (<5)", "jaraco.functools", "jaraco.itertools", "more
[metadata]
lock-version = "2.0"
-python-versions = ">=3.7,<3.12"
-content-hash = "c02a52cf933b218c70b12ec1b1cc0cd53ee8d43c3ad3a0ceb0a8fb23a5e0b0c9"
+python-versions = ">=3.7,<3.13"
+content-hash = "a82953605d241f689dba7d16b5500360d09aadbb26b7484a16f5bef5e298eb49"
diff --git a/pyproject.toml b/pyproject.toml
index e83d552e..adf79415 100644
--- a/pyproject.toml
+++ b/pyproject.toml
@@ -20,13 +20,14 @@ classifiers = [
"Programming Language :: Python :: 3.9",
"Programming Language :: Python :: 3.10",
"Programming Language :: Python :: 3.11",
+ "Programming Language :: Python :: 3.12",
]
[tool.poetry.scripts]
cycode = "cycode.cli.main:main_cli"
[tool.poetry.dependencies]
-python = ">=3.7,<3.12"
+python = ">=3.7,<3.13"
click = ">=8.1.0,<8.2.0"
colorama = ">=0.4.3,<0.5.0"
pyyaml = ">=6.0,<7.0"
@@ -47,7 +48,7 @@ coverage = ">=7.2.3,<7.3.0"
responses = ">=0.23.1,<0.24.0"
[tool.poetry.group.executable.dependencies]
-pyinstaller = ">=5.11.0,<5.12.0"
+pyinstaller = ">=5.13.0,<5.14.0"
dunamai = ">=1.16.1,<1.17.0"
[tool.poetry.group.dev.dependencies]
From 47e2b2d662053a01457a857e5108c1a8e41cea01 Mon Sep 17 00:00:00 2001
From: Ilya Siamionau
Date: Tue, 10 Oct 2023 11:29:48 +0200
Subject: [PATCH 035/257] CM-27690 - Configure API URL and APP URL using
"cycode configure" (#167)
---
cycode/cli/commands/configure/__init__.py | 0
.../commands/configure/configure_command.py | 137 +++++++++++
cycode/cli/commands/ignore/__init__.py | 0
.../ignore/ignore_command.py} | 79 +------
cycode/cli/main.py | 7 +-
.../cli/user_settings/config_file_manager.py | 8 +-
.../user_settings/configuration_manager.py | 4 -
tests/cli/test_configure_command.py | 220 ++++++++++++++++++
.../test_user_settings_commands.py | 123 ----------
9 files changed, 374 insertions(+), 204 deletions(-)
create mode 100644 cycode/cli/commands/configure/__init__.py
create mode 100644 cycode/cli/commands/configure/configure_command.py
create mode 100644 cycode/cli/commands/ignore/__init__.py
rename cycode/cli/{user_settings/user_settings_commands.py => commands/ignore/ignore_command.py} (56%)
create mode 100644 tests/cli/test_configure_command.py
delete mode 100644 tests/user_settings/test_user_settings_commands.py
diff --git a/cycode/cli/commands/configure/__init__.py b/cycode/cli/commands/configure/__init__.py
new file mode 100644
index 00000000..e69de29b
diff --git a/cycode/cli/commands/configure/configure_command.py b/cycode/cli/commands/configure/configure_command.py
new file mode 100644
index 00000000..5f9bad0e
--- /dev/null
+++ b/cycode/cli/commands/configure/configure_command.py
@@ -0,0 +1,137 @@
+from typing import Optional
+
+import click
+
+from cycode.cli import config, consts
+from cycode.cli.user_settings.configuration_manager import ConfigurationManager
+from cycode.cli.user_settings.credentials_manager import CredentialsManager
+from cycode.cli.utils.string_utils import obfuscate_text
+
+_URLS_UPDATED_SUCCESSFULLY_MESSAGE = 'Successfully configured Cycode URLs! Saved to: {filename}'
+_URLS_ARE_SET_IN_ENVIRONMENT_VARIABLES_MESSAGE = (
+ 'Note that the URLs (APP and API) that already exist in environment variables '
+ f'({consts.CYCODE_API_URL_ENV_VAR_NAME} and {consts.CYCODE_APP_URL_ENV_VAR_NAME}) '
+ 'take precedent over these URLs; either update or remove the environment variables.'
+)
+_CREDENTIALS_UPDATED_SUCCESSFULLY_MESSAGE = 'Successfully configured CLI credentials! Saved to: {filename}'
+_CREDENTIALS_ARE_SET_IN_ENVIRONMENT_VARIABLES_MESSAGE = (
+ 'Note that the credentials that already exist in environment variables '
+ f'({config.CYCODE_CLIENT_ID_ENV_VAR_NAME} and {config.CYCODE_CLIENT_SECRET_ENV_VAR_NAME}) '
+ 'take precedent over these credentials; either update or remove the environment variables.'
+)
+_CREDENTIALS_MANAGER = CredentialsManager()
+_CONFIGURATION_MANAGER = ConfigurationManager()
+
+
+@click.command(short_help='Initial command to configure your CLI client authentication.')
+def configure_command() -> None:
+ """Configure your CLI client authentication manually."""
+ global_config_manager = _CONFIGURATION_MANAGER.global_config_file_manager
+
+ current_api_url = global_config_manager.get_api_url()
+ current_app_url = global_config_manager.get_app_url()
+ api_url = _get_api_url_input(current_api_url)
+ app_url = _get_app_url_input(current_app_url)
+
+ config_updated = False
+ if _should_update_value(current_api_url, api_url):
+ global_config_manager.update_api_base_url(api_url)
+ config_updated = True
+ if _should_update_value(current_app_url, app_url):
+ global_config_manager.update_app_base_url(app_url)
+ config_updated = True
+
+ current_client_id, current_client_secret = _CREDENTIALS_MANAGER.get_credentials_from_file()
+ client_id = _get_client_id_input(current_client_id)
+ client_secret = _get_client_secret_input(current_client_secret)
+
+ credentials_updated = False
+ if _should_update_value(current_client_id, client_id) or _should_update_value(current_client_secret, client_secret):
+ credentials_updated = True
+ _CREDENTIALS_MANAGER.update_credentials_file(client_id, client_secret)
+
+ if config_updated:
+ click.echo(_get_urls_update_result_message())
+ if credentials_updated:
+ click.echo(_get_credentials_update_result_message())
+
+
+def _get_client_id_input(current_client_id: Optional[str]) -> Optional[str]:
+ prompt_text = 'Cycode Client ID'
+
+ prompt_suffix = ' []: '
+ if current_client_id:
+ prompt_suffix = f' [{obfuscate_text(current_client_id)}]: '
+
+ new_client_id = click.prompt(text=prompt_text, prompt_suffix=prompt_suffix, default='', show_default=False)
+ return new_client_id or current_client_id
+
+
+def _get_client_secret_input(current_client_secret: Optional[str]) -> Optional[str]:
+ prompt_text = 'Cycode Client Secret'
+
+ prompt_suffix = ' []: '
+ if current_client_secret:
+ prompt_suffix = f' [{obfuscate_text(current_client_secret)}]: '
+
+ new_client_secret = click.prompt(text=prompt_text, prompt_suffix=prompt_suffix, default='', show_default=False)
+ return new_client_secret or current_client_secret
+
+
+def _get_app_url_input(current_app_url: Optional[str]) -> str:
+ prompt_text = 'Cycode APP URL'
+
+ default = consts.DEFAULT_CYCODE_APP_URL
+ if current_app_url:
+ default = current_app_url
+
+ return click.prompt(text=prompt_text, default=default, type=click.STRING)
+
+
+def _get_api_url_input(current_api_url: Optional[str]) -> str:
+ prompt_text = 'Cycode API URL'
+
+ default = consts.DEFAULT_CYCODE_API_URL
+ if current_api_url:
+ default = current_api_url
+
+ return click.prompt(text=prompt_text, default=default, type=click.STRING)
+
+
+def _get_credentials_update_result_message() -> str:
+ success_message = _CREDENTIALS_UPDATED_SUCCESSFULLY_MESSAGE.format(filename=_CREDENTIALS_MANAGER.get_filename())
+ if _are_credentials_exist_in_environment_variables():
+ return f'{success_message}. {_CREDENTIALS_ARE_SET_IN_ENVIRONMENT_VARIABLES_MESSAGE}'
+
+ return success_message
+
+
+def _are_credentials_exist_in_environment_variables() -> bool:
+ client_id, client_secret = _CREDENTIALS_MANAGER.get_credentials_from_environment_variables()
+ return any([client_id, client_secret])
+
+
+def _get_urls_update_result_message() -> str:
+ success_message = _URLS_UPDATED_SUCCESSFULLY_MESSAGE.format(
+ filename=_CONFIGURATION_MANAGER.global_config_file_manager.get_filename()
+ )
+ if _are_urls_exist_in_environment_variables():
+ return f'{success_message}. {_URLS_ARE_SET_IN_ENVIRONMENT_VARIABLES_MESSAGE}'
+
+ return success_message
+
+
+def _are_urls_exist_in_environment_variables() -> bool:
+ api_url = _CONFIGURATION_MANAGER.get_api_url_from_environment_variables()
+ app_url = _CONFIGURATION_MANAGER.get_app_url_from_environment_variables()
+ return any([api_url, app_url])
+
+
+def _should_update_value(
+ old_value: Optional[str],
+ new_value: Optional[str],
+) -> bool:
+ if not new_value:
+ return False
+
+ return old_value != new_value
diff --git a/cycode/cli/commands/ignore/__init__.py b/cycode/cli/commands/ignore/__init__.py
new file mode 100644
index 00000000..e69de29b
diff --git a/cycode/cli/user_settings/user_settings_commands.py b/cycode/cli/commands/ignore/ignore_command.py
similarity index 56%
rename from cycode/cli/user_settings/user_settings_commands.py
rename to cycode/cli/commands/ignore/ignore_command.py
index 9629de1e..66515447 100644
--- a/cycode/cli/user_settings/user_settings_commands.py
+++ b/cycode/cli/commands/ignore/ignore_command.py
@@ -1,41 +1,21 @@
-import os.path
+import os
import re
-from typing import Optional
import click
from cycode.cli import consts
from cycode.cli.config import config, configuration_manager
-from cycode.cli.user_settings.credentials_manager import CredentialsManager
from cycode.cli.utils.path_utils import get_absolute_path
-from cycode.cli.utils.string_utils import hash_string_to_sha256, obfuscate_text
+from cycode.cli.utils.string_utils import hash_string_to_sha256
from cycode.cyclient import logger
-CREDENTIALS_UPDATED_SUCCESSFULLY_MESSAGE = 'Successfully configured CLI credentials!'
-CREDENTIALS_ARE_SET_IN_ENVIRONMENT_VARIABLES_MESSAGE = (
- 'Note that the credentials that already exist in environment'
- ' variables (CYCODE_CLIENT_ID and CYCODE_CLIENT_SECRET) take'
- ' precedent over these credentials; either update or remove '
- 'the environment variables.'
-)
-credentials_manager = CredentialsManager()
-
-@click.command(
- short_help='Initial command to authenticate your CLI client with Cycode using a client ID and client secret.'
-)
-def set_credentials() -> None:
- """Authenticates your CLI client with Cycode manually by using a client ID and client secret."""
- click.echo(f'Update credentials in file ({credentials_manager.get_filename()})')
- current_client_id, current_client_secret = credentials_manager.get_credentials_from_file()
- client_id = _get_client_id_input(current_client_id)
- client_secret = _get_client_secret_input(current_client_secret)
+def _is_path_to_ignore_exists(path: str) -> bool:
+ return os.path.exists(path)
- if not _should_update_credentials(current_client_id, current_client_secret, client_id, client_secret):
- return
- credentials_manager.update_credentials_file(client_id, client_secret)
- click.echo(_get_credentials_update_result_message())
+def _is_package_pattern_valid(package: str) -> bool:
+ return re.search('^[^@]+@[^@]+$', package) is not None
@click.command(short_help='Ignores a specific value, path or rule ID.')
@@ -83,7 +63,7 @@ def set_credentials() -> None:
required=False,
help='Add an ignore rule to the global CLI config.',
)
-def add_exclusions(
+def ignore_command(
by_value: str, by_sha: str, by_path: str, by_rule: str, by_package: str, scan_type: str, is_global: bool
) -> None:
"""Ignores a specific value, path or rule ID."""
@@ -126,48 +106,3 @@ def add_exclusions(
},
)
configuration_manager.add_exclusion(configuration_scope, scan_type, exclusion_type, exclusion_value)
-
-
-def _get_client_id_input(current_client_id: str) -> str:
- new_client_id = click.prompt(
- f'cycode client id [{_obfuscate_credential(current_client_id)}]', default='', show_default=False
- )
-
- return new_client_id if new_client_id else current_client_id
-
-
-def _get_client_secret_input(current_client_secret: str) -> str:
- new_client_secret = click.prompt(
- f'cycode client secret [{_obfuscate_credential(current_client_secret)}]', default='', show_default=False
- )
- return new_client_secret if new_client_secret else current_client_secret
-
-
-def _get_credentials_update_result_message() -> str:
- if not _are_credentials_exist_in_environment_variables():
- return CREDENTIALS_UPDATED_SUCCESSFULLY_MESSAGE
-
- return CREDENTIALS_UPDATED_SUCCESSFULLY_MESSAGE + ' ' + CREDENTIALS_ARE_SET_IN_ENVIRONMENT_VARIABLES_MESSAGE
-
-
-def _are_credentials_exist_in_environment_variables() -> bool:
- client_id, client_secret = credentials_manager.get_credentials_from_environment_variables()
- return client_id is not None or client_secret is not None
-
-
-def _should_update_credentials(
- current_client_id: str, current_client_secret: str, new_client_id: str, new_client_secret: str
-) -> bool:
- return current_client_id != new_client_id or current_client_secret != new_client_secret
-
-
-def _obfuscate_credential(credential: Optional[str]) -> str:
- return '' if not credential else obfuscate_text(credential)
-
-
-def _is_path_to_ignore_exists(path: str) -> bool:
- return os.path.exists(path)
-
-
-def _is_package_pattern_valid(package: str) -> bool:
- return re.search('^[^@]+@[^@]+$', package) is not None
diff --git a/cycode/cli/main.py b/cycode/cli/main.py
index efa2b200..082cca3a 100644
--- a/cycode/cli/main.py
+++ b/cycode/cli/main.py
@@ -8,6 +8,8 @@
from cycode import __version__
from cycode.cli import code_scanner
from cycode.cli.auth.auth_command import authenticate
+from cycode.cli.commands.configure.configure_command import configure_command
+from cycode.cli.commands.ignore.ignore_command import ignore_command
from cycode.cli.commands.report.report_command import report_command
from cycode.cli.config import config
from cycode.cli.consts import (
@@ -19,7 +21,6 @@
)
from cycode.cli.models import Severity
from cycode.cli.user_settings.configuration_manager import ConfigurationManager
-from cycode.cli.user_settings.user_settings_commands import add_exclusions, set_credentials
from cycode.cli.utils import scan_utils
from cycode.cli.utils.get_api_client import get_scan_cycode_client
from cycode.cli.utils.progress_bar import SCAN_PROGRESS_BAR_SECTIONS, get_progress_bar
@@ -183,8 +184,8 @@ def version(context: click.Context) -> None:
commands={
'scan': code_scan,
'report': report_command,
- 'configure': set_credentials,
- 'ignore': add_exclusions,
+ 'configure': configure_command,
+ 'ignore': ignore_command,
'auth': authenticate,
'version': version,
},
diff --git a/cycode/cli/user_settings/config_file_manager.py b/cycode/cli/user_settings/config_file_manager.py
index acec4d17..e4e5e6b1 100644
--- a/cycode/cli/user_settings/config_file_manager.py
+++ b/cycode/cli/user_settings/config_file_manager.py
@@ -52,8 +52,12 @@ def get_exclude_detections_in_deleted_lines(self, command_scan_type: str) -> Opt
command_scan_type, self.EXCLUDE_DETECTIONS_IN_DELETED_LINES
)
- def update_base_url(self, base_url: str) -> None:
- update_data = {self.ENVIRONMENT_SECTION_NAME: {self.API_URL_FIELD_NAME: base_url}}
+ def update_api_base_url(self, api_url: str) -> None:
+ update_data = {self.ENVIRONMENT_SECTION_NAME: {self.API_URL_FIELD_NAME: api_url}}
+ self.write_content_to_file(update_data)
+
+ def update_app_base_url(self, app_url: str) -> None:
+ update_data = {self.ENVIRONMENT_SECTION_NAME: {self.APP_URL_FIELD_NAME: app_url}}
self.write_content_to_file(update_data)
def get_installation_id(self) -> Optional[str]:
diff --git a/cycode/cli/user_settings/configuration_manager.py b/cycode/cli/user_settings/configuration_manager.py
index 65da08fc..4ceec970 100644
--- a/cycode/cli/user_settings/configuration_manager.py
+++ b/cycode/cli/user_settings/configuration_manager.py
@@ -76,10 +76,6 @@ def _merge_exclusions(self, local_exclusions: Dict, global_exclusions: Dict) ->
keys = set(list(local_exclusions.keys()) + list(global_exclusions.keys()))
return {key: local_exclusions.get(key, []) + global_exclusions.get(key, []) for key in keys}
- def update_base_url(self, base_url: str, scope: str = 'local') -> None:
- config_file_manager = self.get_config_file_manager(scope)
- config_file_manager.update_base_url(base_url)
-
def get_or_create_installation_id(self) -> str:
config_file_manager = self.get_config_file_manager()
diff --git a/tests/cli/test_configure_command.py b/tests/cli/test_configure_command.py
new file mode 100644
index 00000000..4c42971b
--- /dev/null
+++ b/tests/cli/test_configure_command.py
@@ -0,0 +1,220 @@
+from typing import TYPE_CHECKING
+
+from click.testing import CliRunner
+
+from cycode.cli.commands.configure.configure_command import configure_command
+
+if TYPE_CHECKING:
+ from pytest_mock import MockerFixture
+
+
+def test_configure_command_no_exist_values_in_file(mocker: 'MockerFixture') -> None:
+ # Arrange
+ app_url_user_input = 'new app url'
+ api_url_user_input = 'new api url'
+ client_id_user_input = 'new client id'
+ client_secret_user_input = 'new client secret'
+
+ mocker.patch(
+ 'cycode.cli.user_settings.credentials_manager.CredentialsManager.get_credentials_from_file',
+ return_value=(None, None),
+ )
+ mocker.patch(
+ 'cycode.cli.user_settings.config_file_manager.ConfigFileManager.get_api_url',
+ return_value=None,
+ )
+ mocker.patch(
+ 'cycode.cli.user_settings.config_file_manager.ConfigFileManager.get_app_url',
+ return_value=None,
+ )
+
+ # side effect - multiple return values, each item in the list represents return of a call
+ mocker.patch(
+ 'click.prompt',
+ side_effect=[api_url_user_input, app_url_user_input, client_id_user_input, client_secret_user_input],
+ )
+
+ mocked_update_credentials = mocker.patch(
+ 'cycode.cli.user_settings.credentials_manager.CredentialsManager.update_credentials_file'
+ )
+ mocked_update_api_base_url = mocker.patch(
+ 'cycode.cli.user_settings.config_file_manager.ConfigFileManager.update_api_base_url'
+ )
+ mocked_update_app_base_url = mocker.patch(
+ 'cycode.cli.user_settings.config_file_manager.ConfigFileManager.update_app_base_url'
+ )
+
+ # Act
+ CliRunner().invoke(configure_command)
+
+ # Assert
+ mocked_update_credentials.assert_called_once_with(client_id_user_input, client_secret_user_input)
+ mocked_update_api_base_url.assert_called_once_with(api_url_user_input)
+ mocked_update_app_base_url.assert_called_once_with(app_url_user_input)
+
+
+def test_configure_command_update_current_configs_in_files(mocker: 'MockerFixture') -> None:
+ # Arrange
+ app_url_user_input = 'new app url'
+ api_url_user_input = 'new api url'
+ client_id_user_input = 'new client id'
+ client_secret_user_input = 'new client secret'
+
+ mocker.patch(
+ 'cycode.cli.user_settings.credentials_manager.CredentialsManager.get_credentials_from_file',
+ return_value=('client id file', 'client secret file'),
+ )
+ mocker.patch(
+ 'cycode.cli.user_settings.config_file_manager.ConfigFileManager.get_api_url',
+ return_value='api url file',
+ )
+ mocker.patch(
+ 'cycode.cli.user_settings.config_file_manager.ConfigFileManager.get_app_url',
+ return_value='app url file',
+ )
+
+ # side effect - multiple return values, each item in the list represents return of a call
+ mocker.patch(
+ 'click.prompt',
+ side_effect=[api_url_user_input, app_url_user_input, client_id_user_input, client_secret_user_input],
+ )
+
+ mocked_update_credentials = mocker.patch(
+ 'cycode.cli.user_settings.credentials_manager.CredentialsManager.update_credentials_file'
+ )
+ mocked_update_api_base_url = mocker.patch(
+ 'cycode.cli.user_settings.config_file_manager.ConfigFileManager.update_api_base_url'
+ )
+ mocked_update_app_base_url = mocker.patch(
+ 'cycode.cli.user_settings.config_file_manager.ConfigFileManager.update_app_base_url'
+ )
+
+ # Act
+ CliRunner().invoke(configure_command)
+
+ # Assert
+ mocked_update_credentials.assert_called_once_with(client_id_user_input, client_secret_user_input)
+ mocked_update_api_base_url.assert_called_once_with(api_url_user_input)
+ mocked_update_app_base_url.assert_called_once_with(app_url_user_input)
+
+
+def test_set_credentials_update_only_client_id(mocker: 'MockerFixture') -> None:
+ # Arrange
+ client_id_user_input = 'new client id'
+ current_client_id = 'client secret file'
+ mocker.patch(
+ 'cycode.cli.user_settings.credentials_manager.CredentialsManager.get_credentials_from_file',
+ return_value=('client id file', 'client secret file'),
+ )
+
+ # side effect - multiple return values, each item in the list represents return of a call
+ mocker.patch('click.prompt', side_effect=['', '', client_id_user_input, ''])
+ mocked_update_credentials = mocker.patch(
+ 'cycode.cli.user_settings.credentials_manager.CredentialsManager.update_credentials_file'
+ )
+
+ # Act
+ CliRunner().invoke(configure_command)
+
+ # Assert
+ mocked_update_credentials.assert_called_once_with(client_id_user_input, current_client_id)
+
+
+def test_configure_command_update_only_client_secret(mocker: 'MockerFixture') -> None:
+ # Arrange
+ client_secret_user_input = 'new client secret'
+ current_client_id = 'client secret file'
+
+ mocker.patch(
+ 'cycode.cli.user_settings.credentials_manager.CredentialsManager.get_credentials_from_file',
+ return_value=(current_client_id, 'client secret file'),
+ )
+
+ # side effect - multiple return values, each item in the list represents return of a call
+ mocker.patch('click.prompt', side_effect=['', '', '', client_secret_user_input])
+ mocked_update_credentials = mocker.patch(
+ 'cycode.cli.user_settings.credentials_manager.CredentialsManager.update_credentials_file'
+ )
+
+ # Act
+ CliRunner().invoke(configure_command)
+
+ # Assert
+ mocked_update_credentials.assert_called_once_with(current_client_id, client_secret_user_input)
+
+
+def test_configure_command_update_only_api_url(mocker: 'MockerFixture') -> None:
+ # Arrange
+ api_url_user_input = 'new api url'
+ current_api_url = 'api url'
+
+ mocker.patch(
+ 'cycode.cli.user_settings.config_file_manager.ConfigFileManager.get_api_url',
+ return_value=current_api_url,
+ )
+
+ # side effect - multiple return values, each item in the list represents return of a call
+ mocker.patch('click.prompt', side_effect=[api_url_user_input, '', '', ''])
+ mocked_update_api_base_url = mocker.patch(
+ 'cycode.cli.user_settings.config_file_manager.ConfigFileManager.update_api_base_url'
+ )
+
+ # Act
+ CliRunner().invoke(configure_command)
+
+ # Assert
+ mocked_update_api_base_url.assert_called_once_with(api_url_user_input)
+
+
+def test_configure_command_should_not_update_credentials_file(mocker: 'MockerFixture') -> None:
+ # Arrange
+ client_id_user_input = ''
+ client_secret_user_input = ''
+
+ mocker.patch(
+ 'cycode.cli.user_settings.credentials_manager.CredentialsManager.get_credentials_from_file',
+ return_value=('client id file', 'client secret file'),
+ )
+
+ # side effect - multiple return values, each item in the list represents return of a call
+ mocker.patch('click.prompt', side_effect=['', '', client_id_user_input, client_secret_user_input])
+ mocked_update_credentials = mocker.patch(
+ 'cycode.cli.user_settings.credentials_manager.CredentialsManager.update_credentials_file'
+ )
+
+ # Act
+ CliRunner().invoke(configure_command)
+
+ # Assert
+ assert not mocked_update_credentials.called
+
+
+def test_configure_command_should_not_update_config_file(mocker: 'MockerFixture') -> None:
+ # Arrange
+ app_url_user_input = ''
+ api_url_user_input = ''
+
+ mocker.patch(
+ 'cycode.cli.user_settings.config_file_manager.ConfigFileManager.get_api_url',
+ return_value='api url file',
+ )
+ mocker.patch(
+ 'cycode.cli.user_settings.config_file_manager.ConfigFileManager.get_app_url',
+ return_value='app url file',
+ )
+
+ # side effect - multiple return values, each item in the list represents return of a call
+ mocker.patch('click.prompt', side_effect=[api_url_user_input, app_url_user_input, '', ''])
+ mocked_update_api_base_url = mocker.patch(
+ 'cycode.cli.user_settings.config_file_manager.ConfigFileManager.update_api_base_url'
+ )
+ mocked_update_app_base_url = mocker.patch(
+ 'cycode.cli.user_settings.config_file_manager.ConfigFileManager.update_app_base_url'
+ )
+
+ # Act
+ CliRunner().invoke(configure_command)
+
+ # Assert
+ assert not mocked_update_api_base_url.called
+ assert not mocked_update_app_base_url.called
diff --git a/tests/user_settings/test_user_settings_commands.py b/tests/user_settings/test_user_settings_commands.py
deleted file mode 100644
index 6ef0cf2e..00000000
--- a/tests/user_settings/test_user_settings_commands.py
+++ /dev/null
@@ -1,123 +0,0 @@
-from typing import TYPE_CHECKING
-
-from click.testing import CliRunner
-
-from cycode.cli.user_settings.user_settings_commands import set_credentials
-
-if TYPE_CHECKING:
- from pytest_mock import MockerFixture
-
-
-def test_set_credentials_no_exist_credentials_in_file(mocker: 'MockerFixture') -> None:
- # Arrange
- client_id_user_input = 'new client id'
- client_secret_user_input = 'new client secret'
- mocker.patch(
- 'cycode.cli.user_settings.credentials_manager.CredentialsManager.get_credentials_from_file',
- return_value=(None, None),
- )
-
- # side effect - multiple return values, each item in the list represent return of a call
- mocker.patch('click.prompt', side_effect=[client_id_user_input, client_secret_user_input])
- mocked_update_credentials = mocker.patch(
- 'cycode.cli.user_settings.credentials_manager.CredentialsManager.update_credentials_file'
- )
- click = CliRunner()
-
- # Act
- click.invoke(set_credentials)
-
- # Assert
- mocked_update_credentials.assert_called_once_with(client_id_user_input, client_secret_user_input)
-
-
-def test_set_credentials_update_current_credentials_in_file(mocker: 'MockerFixture') -> None:
- # Arrange
- client_id_user_input = 'new client id'
- client_secret_user_input = 'new client secret'
- mocker.patch(
- 'cycode.cli.user_settings.credentials_manager.CredentialsManager.get_credentials_from_file',
- return_value=('client id file', 'client secret file'),
- )
-
- # side effect - multiple return values, each item in the list represents return of a call
- mocker.patch('click.prompt', side_effect=[client_id_user_input, client_secret_user_input])
- mocked_update_credentials = mocker.patch(
- 'cycode.cli.user_settings.credentials_manager.CredentialsManager.update_credentials_file'
- )
- click = CliRunner()
-
- # Act
- click.invoke(set_credentials)
-
- # Assert
- mocked_update_credentials.assert_called_once_with(client_id_user_input, client_secret_user_input)
-
-
-def test_set_credentials_update_only_client_id(mocker: 'MockerFixture') -> None:
- # Arrange
- client_id_user_input = 'new client id'
- current_client_id = 'client secret file'
- mocker.patch(
- 'cycode.cli.user_settings.credentials_manager.CredentialsManager.get_credentials_from_file',
- return_value=('client id file', 'client secret file'),
- )
-
- # side effect - multiple return values, each item in the list represent return of a call
- mocker.patch('click.prompt', side_effect=[client_id_user_input, ''])
- mocked_update_credentials = mocker.patch(
- 'cycode.cli.user_settings.credentials_manager.CredentialsManager.update_credentials_file'
- )
- click = CliRunner()
-
- # Act
- click.invoke(set_credentials)
-
- # Assert
- mocked_update_credentials.assert_called_once_with(client_id_user_input, current_client_id)
-
-
-def test_set_credentials_update_only_client_secret(mocker: 'MockerFixture') -> None:
- # Arrange
- client_secret_user_input = 'new client secret'
- current_client_id = 'client secret file'
- mocker.patch(
- 'cycode.cli.user_settings.credentials_manager.CredentialsManager.get_credentials_from_file',
- return_value=(current_client_id, 'client secret file'),
- )
-
- # side effect - multiple return values, each item in the list represent return of a call
- mocker.patch('click.prompt', side_effect=['', client_secret_user_input])
- mocked_update_credentials = mocker.patch(
- 'cycode.cli.user_settings.credentials_manager.CredentialsManager.update_credentials_file'
- )
- click = CliRunner()
-
- # Act
- click.invoke(set_credentials)
-
- # Assert
- mocked_update_credentials.assert_called_once_with(current_client_id, client_secret_user_input)
-
-
-def test_set_credentials_should_not_update_file(mocker: 'MockerFixture') -> None:
- # Arrange
- client_id_user_input = ''
- client_secret_user_input = ''
- mocker.patch(
- 'cycode.cli.user_settings.credentials_manager.CredentialsManager.get_credentials_from_file',
- return_value=('client id file', 'client secret file'),
- )
-
- # side effect - multiple return values, each item in the list represent return of a call
- mocker.patch('click.prompt', side_effect=[client_id_user_input, client_secret_user_input])
- mocked_update_credentials = mocker.patch(
- 'cycode.cli.user_settings.credentials_manager.CredentialsManager.update_credentials_file'
- )
- click = CliRunner()
-
- # Act
- click.invoke(set_credentials)
-
- # Assert
- assert not mocked_update_credentials.called
From a35fb4910d2007252e55330c31bd900c850719be Mon Sep 17 00:00:00 2001
From: Ilya Siamionau
Date: Tue, 10 Oct 2023 12:34:37 +0200
Subject: [PATCH 036/257] CM-27947 - Fix required authorization for sbom --help
command (#168)
---
cycode/cli/commands/report/report_command.py | 4 ----
cycode/cli/commands/report/sbom/sbom_path_command.py | 3 ++-
.../commands/report/sbom/sbom_repository_url_command.py | 3 ++-
cycode/cyclient/client_creator.py | 4 ++--
cycode/cyclient/report_client.py | 8 ++++----
5 files changed, 10 insertions(+), 12 deletions(-)
diff --git a/cycode/cli/commands/report/report_command.py b/cycode/cli/commands/report/report_command.py
index 4722a6b2..7bfb73c6 100644
--- a/cycode/cli/commands/report/report_command.py
+++ b/cycode/cli/commands/report/report_command.py
@@ -1,7 +1,6 @@
import click
from cycode.cli.commands.report.sbom.sbom_command import sbom_command
-from cycode.cli.utils.get_api_client import get_report_cycode_client
from cycode.cli.utils.progress_bar import SBOM_REPORT_PROGRESS_BAR_SECTIONS, get_progress_bar
@@ -16,8 +15,5 @@ def report_command(
context: click.Context,
) -> int:
"""Generate report."""
-
- context.obj['client'] = get_report_cycode_client(hide_response_log=False) # TODO disable log
context.obj['progress_bar'] = get_progress_bar(hidden=False, sections=SBOM_REPORT_PROGRESS_BAR_SECTIONS)
-
return 1
diff --git a/cycode/cli/commands/report/sbom/sbom_path_command.py b/cycode/cli/commands/report/sbom/sbom_path_command.py
index 36b9c4d9..23062cab 100644
--- a/cycode/cli/commands/report/sbom/sbom_path_command.py
+++ b/cycode/cli/commands/report/sbom/sbom_path_command.py
@@ -8,6 +8,7 @@
from cycode.cli.files_collector.path_documents import get_relevant_document
from cycode.cli.files_collector.sca.sca_code_scanner import perform_pre_scan_documents_actions
from cycode.cli.files_collector.zip_documents import zip_documents
+from cycode.cli.utils.get_api_client import get_report_cycode_client
from cycode.cli.utils.progress_bar import SbomReportProgressBarSection
@@ -15,7 +16,7 @@
@click.argument('path', nargs=1, type=click.Path(exists=True, resolve_path=True), required=True)
@click.pass_context
def sbom_path_command(context: click.Context, path: str) -> None:
- client = context.obj['client']
+ client = get_report_cycode_client()
report_parameters = context.obj['report_parameters']
output_format = report_parameters.output_format
output_file = context.obj['output_file']
diff --git a/cycode/cli/commands/report/sbom/sbom_repository_url_command.py b/cycode/cli/commands/report/sbom/sbom_repository_url_command.py
index a3cb2570..4d5ee4a3 100644
--- a/cycode/cli/commands/report/sbom/sbom_repository_url_command.py
+++ b/cycode/cli/commands/report/sbom/sbom_repository_url_command.py
@@ -4,6 +4,7 @@
from cycode.cli.commands.report.sbom.common import create_sbom_report, send_report_feedback
from cycode.cli.commands.report.sbom.handle_errors import handle_report_exception
+from cycode.cli.utils.get_api_client import get_report_cycode_client
from cycode.cli.utils.progress_bar import SbomReportProgressBarSection
@@ -15,7 +16,7 @@ def sbom_repository_url_command(context: click.Context, uri: str) -> None:
progress_bar.start()
progress_bar.set_section_length(SbomReportProgressBarSection.PREPARE_LOCAL_FILES)
- client = context.obj['client']
+ client = get_report_cycode_client()
report_parameters = context.obj['report_parameters']
output_file = context.obj['output_file']
output_format = report_parameters.output_format
diff --git a/cycode/cyclient/client_creator.py b/cycode/cyclient/client_creator.py
index da62bd5a..45911589 100644
--- a/cycode/cyclient/client_creator.py
+++ b/cycode/cyclient/client_creator.py
@@ -18,6 +18,6 @@ def create_scan_client(client_id: str, client_secret: str, hide_response_log: bo
return ScanClient(client, scan_config, hide_response_log)
-def create_report_client(client_id: str, client_secret: str, hide_response_log: bool) -> ReportClient:
+def create_report_client(client_id: str, client_secret: str, _: bool) -> ReportClient:
client = CycodeDevBasedClient(DEV_CYCODE_API_URL) if dev_mode else CycodeTokenBasedClient(client_id, client_secret)
- return ReportClient(client, hide_response_log)
+ return ReportClient(client)
diff --git a/cycode/cyclient/report_client.py b/cycode/cyclient/report_client.py
index ade7d850..fa8e0c3f 100644
--- a/cycode/cyclient/report_client.py
+++ b/cycode/cyclient/report_client.py
@@ -37,9 +37,8 @@ class ReportClient:
DOWNLOAD_REPORT_PATH: str = 'files/api/v1/file/sbom/{file_name}' # not in the report service
- def __init__(self, client: CycodeClientBase, hide_response_log: bool = True) -> None:
+ def __init__(self, client: CycodeClientBase) -> None:
self.client = client
- self._hide_response_log = hide_response_log
def request_sbom_report_execution(
self, params: ReportParameters, zip_file: InMemoryZip = None, repository_url: Optional[str] = None
@@ -55,7 +54,6 @@ def request_sbom_report_execution(
request_args = {
'url_path': url_path,
'data': request_data,
- 'hide_response_content_log': self._hide_response_log,
}
if zip_file:
@@ -84,7 +82,9 @@ def get_report_execution(self, report_execution_id: int) -> models.ReportExecuti
def get_file_content(self, file_name: str) -> str:
response = self.client.get(
- url_path=self.DOWNLOAD_REPORT_PATH.format(file_name=file_name), params={'include_hidden': True}
+ url_path=self.DOWNLOAD_REPORT_PATH.format(file_name=file_name),
+ params={'include_hidden': True},
+ hide_response_content_log=True,
)
return response.text
From bb0413f1e88b8408e6b4c20e334d2811c139cc7a Mon Sep 17 00:00:00 2001
From: Ilya Siamionau
Date: Tue, 10 Oct 2023 13:19:14 +0200
Subject: [PATCH 037/257] CM-27780 - Support Python 3.12 (#169)
Upgrade marshmallow
---
poetry.lock | 34 +++++++++++++++++++---------------
pyproject.toml | 6 +++---
2 files changed, 22 insertions(+), 18 deletions(-)
diff --git a/poetry.lock b/poetry.lock
index a6a0126b..06df1ccb 100644
--- a/poetry.lock
+++ b/poetry.lock
@@ -13,17 +13,18 @@ files = [
[[package]]
name = "arrow"
-version = "0.17.0"
+version = "1.2.3"
description = "Better dates & times for Python"
optional = false
-python-versions = ">=2.7, !=3.0.*, !=3.1.*, !=3.2.*, !=3.3.*, !=3.4.*"
+python-versions = ">=3.6"
files = [
- {file = "arrow-0.17.0-py2.py3-none-any.whl", hash = "sha256:e098abbd9af3665aea81bdd6c869e93af4feb078e98468dd351c383af187aac5"},
- {file = "arrow-0.17.0.tar.gz", hash = "sha256:ff08d10cda1d36c68657d6ad20d74fbea493d980f8b2d45344e00d6ed2bf6ed4"},
+ {file = "arrow-1.2.3-py3-none-any.whl", hash = "sha256:5a49ab92e3b7b71d96cd6bfcc4df14efefc9dfa96ea19045815914a6ab6b1fe2"},
+ {file = "arrow-1.2.3.tar.gz", hash = "sha256:3934b30ca1b9f292376d9db15b19446088d12ec58629bc3f0da28fd55fb633a1"},
]
[package.dependencies]
python-dateutil = ">=2.7.0"
+typing-extensions = {version = "*", markers = "python_version < \"3.8\""}
[[package]]
name = "binaryornot"
@@ -427,19 +428,22 @@ altgraph = ">=0.17"
[[package]]
name = "marshmallow"
-version = "3.8.0"
+version = "3.19.0"
description = "A lightweight library for converting complex datatypes to and from native Python datatypes."
optional = false
-python-versions = ">=3.5"
+python-versions = ">=3.7"
files = [
- {file = "marshmallow-3.8.0-py2.py3-none-any.whl", hash = "sha256:2272273505f1644580fbc66c6b220cc78f893eb31f1ecde2af98ad28011e9811"},
- {file = "marshmallow-3.8.0.tar.gz", hash = "sha256:47911dd7c641a27160f0df5fd0fe94667160ffe97f70a42c3cc18388d86098cc"},
+ {file = "marshmallow-3.19.0-py3-none-any.whl", hash = "sha256:93f0958568da045b0021ec6aeb7ac37c81bfcccbb9a0e7ed8559885070b3a19b"},
+ {file = "marshmallow-3.19.0.tar.gz", hash = "sha256:90032c0fd650ce94b6ec6dc8dfeb0e3ff50c144586462c389b81a07205bedb78"},
]
+[package.dependencies]
+packaging = ">=17.0"
+
[package.extras]
-dev = ["flake8 (==3.8.3)", "flake8-bugbear (==20.1.4)", "mypy (==0.782)", "pre-commit (>=2.4,<3.0)", "pytest", "pytz", "simplejson", "tox"]
-docs = ["alabaster (==0.7.12)", "autodocsumm (==0.2.0)", "sphinx (==3.2.1)", "sphinx-issues (==1.2.0)", "sphinx-version-warning (==1.1.2)"]
-lint = ["flake8 (==3.8.3)", "flake8-bugbear (==20.1.4)", "mypy (==0.782)", "pre-commit (>=2.4,<3.0)"]
+dev = ["flake8 (==5.0.4)", "flake8-bugbear (==22.10.25)", "mypy (==0.990)", "pre-commit (>=2.4,<3.0)", "pytest", "pytz", "simplejson", "tox"]
+docs = ["alabaster (==0.7.12)", "autodocsumm (==0.2.9)", "sphinx (==5.3.0)", "sphinx-issues (==3.0.1)", "sphinx-version-warning (==1.1.2)"]
+lint = ["flake8 (==5.0.4)", "flake8-bugbear (==22.10.25)", "mypy (==0.990)", "pre-commit (>=2.4,<3.0)"]
tests = ["pytest", "pytz", "simplejson"]
[[package]]
@@ -805,13 +809,13 @@ files = [
[[package]]
name = "texttable"
-version = "1.6.7"
+version = "1.7.0"
description = "module to create simple ASCII tables"
optional = false
python-versions = "*"
files = [
- {file = "texttable-1.6.7-py2.py3-none-any.whl", hash = "sha256:b7b68139aa8a6339d2c320ca8b1dc42d13a7831a346b446cb9eb385f0c76310c"},
- {file = "texttable-1.6.7.tar.gz", hash = "sha256:290348fb67f7746931bcdfd55ac7584ecd4e5b0846ab164333f0794b121760f2"},
+ {file = "texttable-1.7.0-py2.py3-none-any.whl", hash = "sha256:72227d592c82b3d7f672731ae73e4d1f88cd8e2ef5b075a7a7f01a23a3743917"},
+ {file = "texttable-1.7.0.tar.gz", hash = "sha256:2d2068fb55115807d3ac77a4ca68fa48803e84ebb0ee2340f858107a36522638"},
]
[[package]]
@@ -931,4 +935,4 @@ testing = ["big-O", "flake8 (<5)", "jaraco.functools", "jaraco.itertools", "more
[metadata]
lock-version = "2.0"
python-versions = ">=3.7,<3.13"
-content-hash = "a82953605d241f689dba7d16b5500360d09aadbb26b7484a16f5bef5e298eb49"
+content-hash = "24ef8c4f25c36ad05c1f44b80fcde9ddb0cb2fc208d789f9f2e91aa62223d798"
diff --git a/pyproject.toml b/pyproject.toml
index adf79415..c43cf129 100644
--- a/pyproject.toml
+++ b/pyproject.toml
@@ -31,12 +31,12 @@ python = ">=3.7,<3.13"
click = ">=8.1.0,<8.2.0"
colorama = ">=0.4.3,<0.5.0"
pyyaml = ">=6.0,<7.0"
-marshmallow = ">=3.8.0,<3.9.0"
+marshmallow = ">=3.15.0,<3.21.0"
pathspec = ">=0.11.1,<0.12.0"
gitpython = ">=3.1.30,<3.2.0"
-arrow = ">=0.17.0,<0.18.0"
+arrow = ">=0.17.0,<1.3.0"
binaryornot = ">=0.4.4,<0.5.0"
-texttable = ">=1.6.7,<1.7.0"
+texttable = ">=1.6.7,<1.8.0"
requests = ">=2.24,<3.0"
urllib3 = "1.26.17" # lock v1 to avoid issues with openssl and old Python versions (<3.9.11) on macOS
From b6c14c22f61808038c898496ce952a15c8bb79ca Mon Sep 17 00:00:00 2001
From: "dependabot[bot]" <49699333+dependabot[bot]@users.noreply.github.com>
Date: Wed, 18 Oct 2023 12:20:10 +0200
Subject: [PATCH 038/257] Bump urllib3 from 1.26.17 to 1.26.18 (#170)
Bumps [urllib3](https://github.com/urllib3/urllib3) from 1.26.17 to 1.26.18.
- [Release notes](https://github.com/urllib3/urllib3/releases)
- [Changelog](https://github.com/urllib3/urllib3/blob/main/CHANGES.rst)
- [Commits](https://github.com/urllib3/urllib3/compare/1.26.17...1.26.18)
---
updated-dependencies:
- dependency-name: urllib3
dependency-type: direct:production
...
Signed-off-by: dependabot[bot]
Co-authored-by: dependabot[bot] <49699333+dependabot[bot]@users.noreply.github.com>
---
poetry.lock | 18 ++++++++++++++----
pyproject.toml | 2 +-
2 files changed, 15 insertions(+), 5 deletions(-)
diff --git a/poetry.lock b/poetry.lock
index 06df1ccb..dd0cfec3 100644
--- a/poetry.lock
+++ b/poetry.lock
@@ -664,6 +664,7 @@ files = [
{file = "PyYAML-6.0.1-cp310-cp310-manylinux_2_17_aarch64.manylinux2014_aarch64.whl", hash = "sha256:69b023b2b4daa7548bcfbd4aa3da05b3a74b772db9e23b982788168117739938"},
{file = "PyYAML-6.0.1-cp310-cp310-manylinux_2_17_s390x.manylinux2014_s390x.whl", hash = "sha256:81e0b275a9ecc9c0c0c07b4b90ba548307583c125f54d5b6946cfee6360c733d"},
{file = "PyYAML-6.0.1-cp310-cp310-manylinux_2_17_x86_64.manylinux2014_x86_64.whl", hash = "sha256:ba336e390cd8e4d1739f42dfe9bb83a3cc2e80f567d8805e11b46f4a943f5515"},
+ {file = "PyYAML-6.0.1-cp310-cp310-musllinux_1_1_x86_64.whl", hash = "sha256:326c013efe8048858a6d312ddd31d56e468118ad4cdeda36c719bf5bb6192290"},
{file = "PyYAML-6.0.1-cp310-cp310-win32.whl", hash = "sha256:bd4af7373a854424dabd882decdc5579653d7868b8fb26dc7d0e99f823aa5924"},
{file = "PyYAML-6.0.1-cp310-cp310-win_amd64.whl", hash = "sha256:fd1592b3fdf65fff2ad0004b5e363300ef59ced41c2e6b3a99d4089fa8c5435d"},
{file = "PyYAML-6.0.1-cp311-cp311-macosx_10_9_x86_64.whl", hash = "sha256:6965a7bc3cf88e5a1c3bd2e0b5c22f8d677dc88a455344035f03399034eb3007"},
@@ -671,8 +672,15 @@ files = [
{file = "PyYAML-6.0.1-cp311-cp311-manylinux_2_17_aarch64.manylinux2014_aarch64.whl", hash = "sha256:42f8152b8dbc4fe7d96729ec2b99c7097d656dc1213a3229ca5383f973a5ed6d"},
{file = "PyYAML-6.0.1-cp311-cp311-manylinux_2_17_s390x.manylinux2014_s390x.whl", hash = "sha256:062582fca9fabdd2c8b54a3ef1c978d786e0f6b3a1510e0ac93ef59e0ddae2bc"},
{file = "PyYAML-6.0.1-cp311-cp311-manylinux_2_17_x86_64.manylinux2014_x86_64.whl", hash = "sha256:d2b04aac4d386b172d5b9692e2d2da8de7bfb6c387fa4f801fbf6fb2e6ba4673"},
+ {file = "PyYAML-6.0.1-cp311-cp311-musllinux_1_1_x86_64.whl", hash = "sha256:e7d73685e87afe9f3b36c799222440d6cf362062f78be1013661b00c5c6f678b"},
{file = "PyYAML-6.0.1-cp311-cp311-win32.whl", hash = "sha256:1635fd110e8d85d55237ab316b5b011de701ea0f29d07611174a1b42f1444741"},
{file = "PyYAML-6.0.1-cp311-cp311-win_amd64.whl", hash = "sha256:bf07ee2fef7014951eeb99f56f39c9bb4af143d8aa3c21b1677805985307da34"},
+ {file = "PyYAML-6.0.1-cp312-cp312-macosx_10_9_x86_64.whl", hash = "sha256:855fb52b0dc35af121542a76b9a84f8d1cd886ea97c84703eaa6d88e37a2ad28"},
+ {file = "PyYAML-6.0.1-cp312-cp312-macosx_11_0_arm64.whl", hash = "sha256:40df9b996c2b73138957fe23a16a4f0ba614f4c0efce1e9406a184b6d07fa3a9"},
+ {file = "PyYAML-6.0.1-cp312-cp312-manylinux_2_17_x86_64.manylinux2014_x86_64.whl", hash = "sha256:6c22bec3fbe2524cde73d7ada88f6566758a8f7227bfbf93a408a9d86bcc12a0"},
+ {file = "PyYAML-6.0.1-cp312-cp312-musllinux_1_1_x86_64.whl", hash = "sha256:8d4e9c88387b0f5c7d5f281e55304de64cf7f9c0021a3525bd3b1c542da3b0e4"},
+ {file = "PyYAML-6.0.1-cp312-cp312-win32.whl", hash = "sha256:d483d2cdf104e7c9fa60c544d92981f12ad66a457afae824d146093b8c294c54"},
+ {file = "PyYAML-6.0.1-cp312-cp312-win_amd64.whl", hash = "sha256:0d3304d8c0adc42be59c5f8a4d9e3d7379e6955ad754aa9d6ab7a398b59dd1df"},
{file = "PyYAML-6.0.1-cp36-cp36m-macosx_10_9_x86_64.whl", hash = "sha256:50550eb667afee136e9a77d6dc71ae76a44df8b3e51e41b77f6de2932bfe0f47"},
{file = "PyYAML-6.0.1-cp36-cp36m-manylinux_2_17_aarch64.manylinux2014_aarch64.whl", hash = "sha256:1fe35611261b29bd1de0070f0b2f47cb6ff71fa6595c077e42bd0c419fa27b98"},
{file = "PyYAML-6.0.1-cp36-cp36m-manylinux_2_17_s390x.manylinux2014_s390x.whl", hash = "sha256:704219a11b772aea0d8ecd7058d0082713c3562b4e271b849ad7dc4a5c90c13c"},
@@ -689,6 +697,7 @@ files = [
{file = "PyYAML-6.0.1-cp38-cp38-manylinux_2_17_aarch64.manylinux2014_aarch64.whl", hash = "sha256:a0cd17c15d3bb3fa06978b4e8958dcdc6e0174ccea823003a106c7d4d7899ac5"},
{file = "PyYAML-6.0.1-cp38-cp38-manylinux_2_17_s390x.manylinux2014_s390x.whl", hash = "sha256:28c119d996beec18c05208a8bd78cbe4007878c6dd15091efb73a30e90539696"},
{file = "PyYAML-6.0.1-cp38-cp38-manylinux_2_17_x86_64.manylinux2014_x86_64.whl", hash = "sha256:7e07cbde391ba96ab58e532ff4803f79c4129397514e1413a7dc761ccd755735"},
+ {file = "PyYAML-6.0.1-cp38-cp38-musllinux_1_1_x86_64.whl", hash = "sha256:49a183be227561de579b4a36efbb21b3eab9651dd81b1858589f796549873dd6"},
{file = "PyYAML-6.0.1-cp38-cp38-win32.whl", hash = "sha256:184c5108a2aca3c5b3d3bf9395d50893a7ab82a38004c8f61c258d4428e80206"},
{file = "PyYAML-6.0.1-cp38-cp38-win_amd64.whl", hash = "sha256:1e2722cc9fbb45d9b87631ac70924c11d3a401b2d7f410cc0e3bbf249f2dca62"},
{file = "PyYAML-6.0.1-cp39-cp39-macosx_10_9_x86_64.whl", hash = "sha256:9eb6caa9a297fc2c2fb8862bc5370d0303ddba53ba97e71f08023b6cd73d16a8"},
@@ -696,6 +705,7 @@ files = [
{file = "PyYAML-6.0.1-cp39-cp39-manylinux_2_17_aarch64.manylinux2014_aarch64.whl", hash = "sha256:5773183b6446b2c99bb77e77595dd486303b4faab2b086e7b17bc6bef28865f6"},
{file = "PyYAML-6.0.1-cp39-cp39-manylinux_2_17_s390x.manylinux2014_s390x.whl", hash = "sha256:b786eecbdf8499b9ca1d697215862083bd6d2a99965554781d0d8d1ad31e13a0"},
{file = "PyYAML-6.0.1-cp39-cp39-manylinux_2_17_x86_64.manylinux2014_x86_64.whl", hash = "sha256:bc1bf2925a1ecd43da378f4db9e4f799775d6367bdb94671027b73b393a7c42c"},
+ {file = "PyYAML-6.0.1-cp39-cp39-musllinux_1_1_x86_64.whl", hash = "sha256:04ac92ad1925b2cff1db0cfebffb6ffc43457495c9b3c39d3fcae417d7125dc5"},
{file = "PyYAML-6.0.1-cp39-cp39-win32.whl", hash = "sha256:faca3bdcf85b2fc05d06ff3fbc1f83e1391b3e724afa3feba7d13eeab355484c"},
{file = "PyYAML-6.0.1-cp39-cp39-win_amd64.whl", hash = "sha256:510c9deebc5c0225e8c96813043e62b680ba2f9c50a08d3724c7f28a747d1486"},
{file = "PyYAML-6.0.1.tar.gz", hash = "sha256:bfdf460b1736c775f2ba9f6a92bca30bc2095067b8a9d77876d1fad6cc3b4a43"},
@@ -903,13 +913,13 @@ files = [
[[package]]
name = "urllib3"
-version = "1.26.17"
+version = "1.26.18"
description = "HTTP library with thread-safe connection pooling, file post, and more."
optional = false
python-versions = ">=2.7, !=3.0.*, !=3.1.*, !=3.2.*, !=3.3.*, !=3.4.*, !=3.5.*"
files = [
- {file = "urllib3-1.26.17-py2.py3-none-any.whl", hash = "sha256:94a757d178c9be92ef5539b8840d48dc9cf1b2709c9d6b588232a055c524458b"},
- {file = "urllib3-1.26.17.tar.gz", hash = "sha256:24d6a242c28d29af46c3fae832c36db3bbebcc533dd1bb549172cd739c82df21"},
+ {file = "urllib3-1.26.18-py2.py3-none-any.whl", hash = "sha256:34b97092d7e0a3a8cf7cd10e386f401b3737364026c45e622aa02903dffe0f07"},
+ {file = "urllib3-1.26.18.tar.gz", hash = "sha256:f8ecc1bba5667413457c529ab955bf8c67b45db799d159066261719e328580a0"},
]
[package.extras]
@@ -935,4 +945,4 @@ testing = ["big-O", "flake8 (<5)", "jaraco.functools", "jaraco.itertools", "more
[metadata]
lock-version = "2.0"
python-versions = ">=3.7,<3.13"
-content-hash = "24ef8c4f25c36ad05c1f44b80fcde9ddb0cb2fc208d789f9f2e91aa62223d798"
+content-hash = "5b143fd05c0d713bd821c03e16cb4c087ddd4f48c17f7dabf479fb6e67ab9cbb"
diff --git a/pyproject.toml b/pyproject.toml
index c43cf129..5a6ac164 100644
--- a/pyproject.toml
+++ b/pyproject.toml
@@ -38,7 +38,7 @@ arrow = ">=0.17.0,<1.3.0"
binaryornot = ">=0.4.4,<0.5.0"
texttable = ">=1.6.7,<1.8.0"
requests = ">=2.24,<3.0"
-urllib3 = "1.26.17" # lock v1 to avoid issues with openssl and old Python versions (<3.9.11) on macOS
+urllib3 = "1.26.18" # lock v1 to avoid issues with openssl and old Python versions (<3.9.11) on macOS
[tool.poetry.group.test.dependencies]
mock = ">=4.0.3,<4.1.0"
From f328471fbcff33f6e1ba1267d63b47a7d5e20420 Mon Sep 17 00:00:00 2001
From: jenia-sakirko <142144387+jenia-sakirko@users.noreply.github.com>
Date: Thu, 19 Oct 2023 23:47:46 +0300
Subject: [PATCH 039/257] CM-28234 - Add SBOM report to the readme (#171)
---
README.md | 166 ++++++++++++++++++++++++++++++++++++------------------
1 file changed, 110 insertions(+), 56 deletions(-)
diff --git a/README.md b/README.md
index 7cdc5338..7673a272 100644
--- a/README.md
+++ b/README.md
@@ -15,35 +15,39 @@ This guide will guide you through both installation and usage.
1. [On Unix/Linux](#on-unixlinux)
2. [On Windows](#on-windows)
2. [Install Pre-Commit Hook](#install-pre-commit-hook)
-3. [Cycode Command](#cycode-command)
-4. [Running a Scan](#running-a-scan)
- 1. [Repository Scan](#repository-scan)
- 1. [Branch Option](#branch-option)
- 2. [Monitor Option](#monitor-option)
- 3. [Report Option](#report-option)
- 4. [Package Vulnerabilities Scan](#package-vulnerabilities-option)
- 1. [License Compliance Option](#license-compliance-option)
- 2. [Severity Threshold](#severity-threshold)
- 5. [Path Scan](#path-scan)
- 1. [Terraform Plan Scan](#terraform-plan-scan)
- 6. [Commit History Scan](#commit-history-scan)
- 1. [Commit Range Option](#commit-range-option)
- 7. [Pre-Commit Scan](#pre-commit-scan)
-5. [Scan Results](#scan-results)
- 1. [Show/Hide Secrets](#showhide-secrets)
- 2. [Soft Fail](#soft-fail)
- 3. [Example Scan Results](#example-scan-results)
- 1. [Secrets Result Example](#secrets-result-example)
- 2. [IaC Result Example](#iac-result-example)
- 3. [SCA Result Example](#sca-result-example)
- 4. [SAST Result Example](#sast-result-example)
-6. [Ignoring Scan Results](#ignoring-scan-results)
- 1. [Ignoring a Secret Value](#ignoring-a-secret-value)
- 2. [Ignoring a Secret SHA Value](#ignoring-a-secret-sha-value)
- 3. [Ignoring a Path](#ignoring-a-path)
- 4. [Ignoring a Secret, IaC, or SCA Rule](#ignoring-a-secret-iac-sca-or-sast-rule)
- 5. [Ignoring a Package](#ignoring-a-package)
-7. [Syntax Help](#syntax-help)
+3. [Cycode Command](#cycode-cli-commands)
+4. [Scan Command](#scan-command)
+ 1. [Running a Scan](#running-a-scan)
+ 1. [Repository Scan](#repository-scan)
+ 1. [Branch Option](#branch-option)
+ 2. [Monitor Option](#monitor-option)
+ 3. [Report Option](#report-option)
+ 4. [Package Vulnerabilities Scan](#package-vulnerabilities-option)
+ 1. [License Compliance Option](#license-compliance-option)
+ 2. [Severity Threshold](#severity-threshold)
+ 5. [Path Scan](#path-scan)
+ 1. [Terraform Plan Scan](#terraform-plan-scan)
+ 6. [Commit History Scan](#commit-history-scan)
+ 1. [Commit Range Option](#commit-range-option)
+ 7. [Pre-Commit Scan](#pre-commit-scan)
+ 2. [Scan Results](#scan-results)
+ 1. [Show/Hide Secrets](#showhide-secrets)
+ 2. [Soft Fail](#soft-fail)
+ 3. [Example Scan Results](#example-scan-results)
+ 1. [Secrets Result Example](#secrets-result-example)
+ 2. [IaC Result Example](#iac-result-example)
+ 3. [SCA Result Example](#sca-result-example)
+ 4. [SAST Result Example](#sast-result-example)
+ 3. [Ignoring Scan Results](#ignoring-scan-results)
+ 1. [Ignoring a Secret Value](#ignoring-a-secret-value)
+ 2. [Ignoring a Secret SHA Value](#ignoring-a-secret-sha-value)
+ 3. [Ignoring a Path](#ignoring-a-path)
+ 4. [Ignoring a Secret, IaC, or SCA Rule](#ignoring-a-secret-iac-sca-or-sast-rule)
+ 5. [Ignoring a Package](#ignoring-a-package)
+5. [Report command](#report-command)
+ 1. [Generating Report](#generating-report)
+ 2. [Report Result](#report-results)
+6. [Syntax Help](#syntax-help)
# Prerequisites
@@ -226,9 +230,12 @@ The following are the options and commands available with the Cycode CLI applica
| [configure](#use-configure-command) | Initial command to authenticate your CLI client with Cycode using client ID and client secret. |
| [ignore](#ingoring-scan-results) | Ignore a specific value, path or rule ID. |
| [scan](#running-a-scan) | Scan content for secrets/IaC/SCA/SAST violations. You need to specify which scan type: `ci`/`commit_history`/`path`/`repository`/etc. |
+| [report](#running-a-report) | Generate report for SCA SBOM. |
| version | Show the version and exit. |
-# Running a Scan
+# Scan Command
+
+## Running a Scan
The Cycode CLI application offers several types of scans so that you can choose the option that best fits your case. The following are the current options and commands available:
@@ -253,7 +260,7 @@ The Cycode CLI application offers several types of scans so that you can choose
| [pre_commit](#pre-commit-scan) | Use this command to scan the content that was not committed yet |
| [repository](#repository-scan) | Scan git repository including its history |
-## Repository Scan
+### Repository Scan
A repository scan examines an entire local repository for any exposed secrets or insecure misconfigurations. This more holistic scan type looks at everything: the current state of your repository and its commit history. It will look not only for secrets that are currently exposed within the repository but previously deleted secrets as well.
@@ -271,7 +278,7 @@ The following option is available for use with this command:
|---------------------|-------------|
| `-b, --branch TEXT` | Branch to scan, if not set scanning the default branch |
-### Branch Option
+#### Branch Option
To scan a specific branch of your local repository, add the argument `-b` (alternatively, `--branch`) followed by the name of the branch you wish to scan.
@@ -283,7 +290,7 @@ or:
`cycode scan repository ~/home/git/codebase --branch dev`
-## Monitor Option
+### Monitor Option
> :memo: **Note**]
> This option is only available to SCA scans.
@@ -303,7 +310,7 @@ When using this option, the scan results from this scan will appear in the knowl
> :warning: **NOTE**
> You must be an `owner` or an `admin` in Cycode to view the knowledge graph page.
-## Report Option
+### Report Option
> :memo: **Note**
> This option is only available to SCA scans.
@@ -366,7 +373,7 @@ The report page will look something like below:
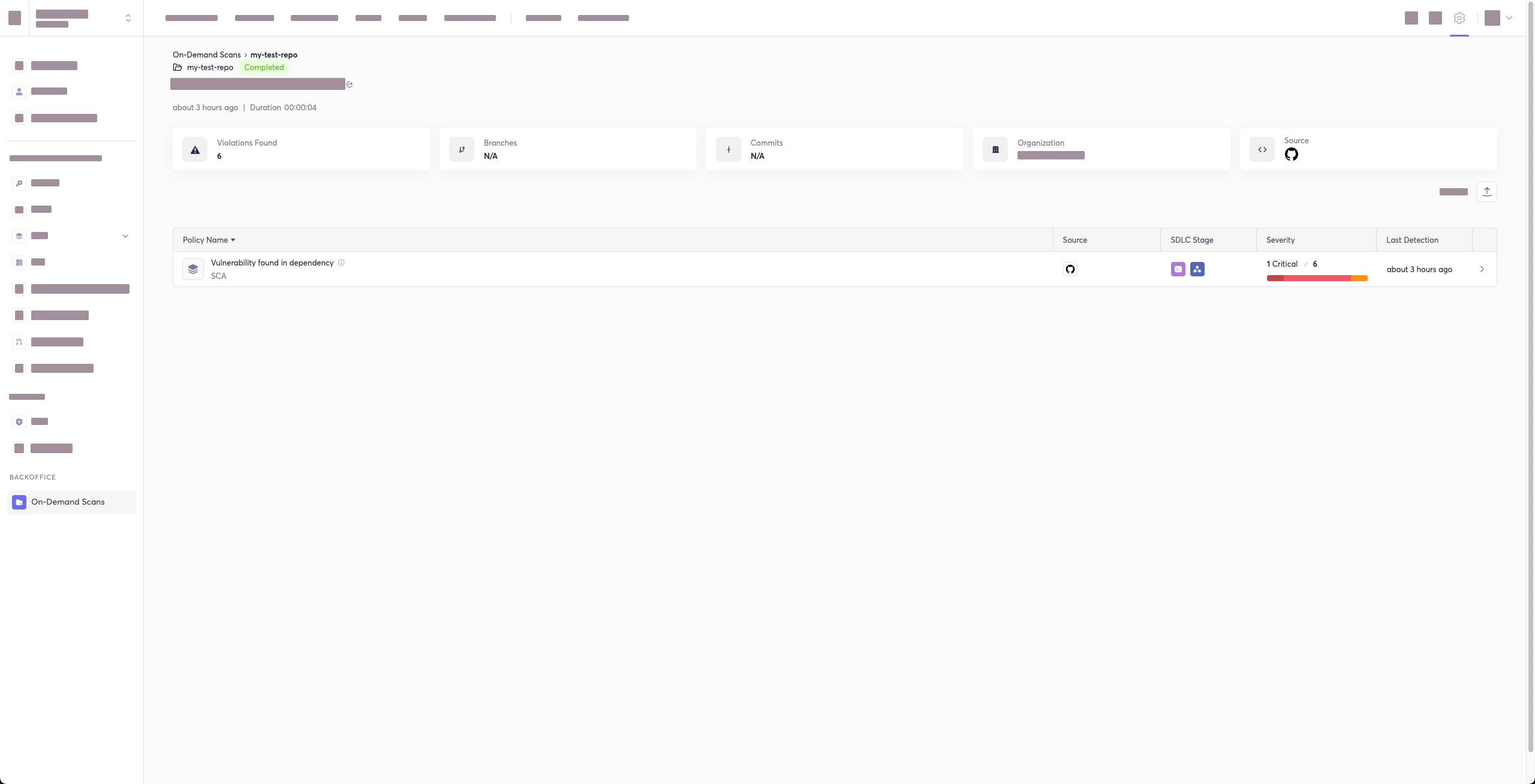
-## Package Vulnerabilities Option
+### Package Vulnerabilities Option
> :memo: **Note**
> This option is only available to SCA scans.
@@ -381,7 +388,7 @@ or:
`cycode scan --scan-type sca --sca-scan package-vulnerabilities repository ~/home/git/codebase`
-### License Compliance Option
+#### License Compliance Option
> :memo: **Note**
> This option is only available to SCA scans.
@@ -396,7 +403,7 @@ or:
`cycode scan --scan-type sca --sca-scan license-compliance repository ~/home/git/codebase`
-### Severity Threshold
+#### Severity Threshold
> :memo: **Note**
> This option is only available to SCA scans.
@@ -411,7 +418,7 @@ or:
`cycode scan --scan-type sca --security-threshold MEDIUM repository ~/home/git/codebase`
-## Path Scan
+### Path Scan
A path scan examines a specific local directory and all the contents within it, instead of focusing solely on a GIT repository.
@@ -424,7 +431,7 @@ For example, consider a scenario in which you want to scan the directory located
`cycode scan path ~/home/git/codebase`
-### Terraform Plan Scan
+#### Terraform Plan Scan
Cycode CLI supports Terraform plan scanning (supporting Terraform 0.12 and later)
@@ -453,7 +460,7 @@ _How to generate a Terraform plan from Terraform configuration file?_
`cycode scan -t iac path ~/PATH/TO/YOUR/{tfplan}.json`
-## Commit History Scan
+### Commit History Scan
A commit history scan is limited to a local repository’s previous commits, focused on finding any secrets within the commit history, instead of examining the repository’s current state.
@@ -471,7 +478,7 @@ The following options are available for use with this command:
|---------------------------|-------------|
| `-r, --commit_range TEXT` | Scan a commit range in this git repository, by default cycode scans all commit history (example: HEAD~1) |
-### Commit Range Option
+#### Commit Range Option
The commit history scan, by default, examines the repository’s entire commit history, all the way back to the initial commit. You can instead limit the scan to a specific commit range by adding the argument `--commit_range` followed by the name you specify.
@@ -483,7 +490,7 @@ OR
`cycode scan commit_history --commit_range {{from-commit-id}}...{{to-commit-id}} ~/home/git/codebase`
-## Pre-Commit Scan
+### Pre-Commit Scan
A pre-commit scan automatically identifies any issues before you commit changes to your repository. There is no need to manually execute this scan; simply configure the pre-commit hook as detailed under the Installation section of this guide.
@@ -491,7 +498,7 @@ After your install the pre-commit hook and, you may, on occasion, wish to skip s
`SKIP=cycode git commit -m `
-# Scan Results
+## Scan Results
Each scan will complete with a message stating if any issues were found or not.
@@ -511,7 +518,7 @@ Secret SHA: a44081db3296c84b82d12a35c446a3cba19411dddfa0380134c75f7b3973bff0
In the event an issue is found, review the file in question for the specific line highlighted by the result message. Implement any changes required to resolve the issue, then execute the scan again.
-## Show/Hide Secrets
+### Show/Hide Secrets
In the above example, a secret was found in the file `secret_test`, located in the subfolder `cli`. The second part of the message shows the specific line the secret appears in, which in this case is a value assigned to `googleApiKey`.
@@ -533,15 +540,15 @@ Secret SHA: a44081db3296c84b82d12a35c446a3cba19411dddfa0380134c75f7b3973bff0
2 | \ No newline at end of file
```
-## Soft Fail
+### Soft Fail
Utilizing the soft fail feature will not fail the CI/CD step within the pipeline if the Cycode scan finds an issue. Additionally, in case an issue occurs from Cycode’s side, a soft fail will automatically execute to avoid interference.
Add the `--soft-fail` argument to any type of scan to configure this feature, then assign a value of `1` if you want found issues to result in a failure within the CI/CD tool or `0` for scan results to have no impact (result in a `success` result).
-## Example Scan Results
+### Example Scan Results
-### Secrets Result Example
+#### Secrets Result Example
```bash
⛔ Found issue of type: generic-password (rule ID: ce3a4de0-9dfc-448b-a004-c538cf8b4710) in file: config/my_config.py
@@ -551,7 +558,7 @@ Secret SHA: a44081db3296c84b82d12a35c446a3cba19411dddfa0380134c75f7b3973bff0
2 | \ No newline at end of file
```
-### IaC Result Example
+#### IaC Result Example
```bash
⛔ Found issue of type: Resource should use non-default namespace (rule ID: bdaa88e2-5e7c-46ff-ac2a-29721418c59c) in file: ./k8s/k8s.yaml ⛔
@@ -561,7 +568,7 @@ Secret SHA: a44081db3296c84b82d12a35c446a3cba19411dddfa0380134c75f7b3973bff0
9 | resourceVersion: "4228"
```
-### SCA Result Example
+#### SCA Result Example
```bash
⛔ Found issue of type: Security vulnerability in package 'pyyaml' referenced in project 'Users/myuser/my-test-repo': Improper Input Validation in PyYAML (rule ID: d003b23a-a2eb-42f3-83c9-7a84505603e5) in file: Users/myuser/my-test-repo/requirements.txt ⛔
@@ -571,7 +578,7 @@ Secret SHA: a44081db3296c84b82d12a35c446a3cba19411dddfa0380134c75f7b3973bff0
3 | cleo==1.0.0a5
```
-### SAST Result Example
+#### SAST Result Example
```bash
⛔ Found issue of type: Detected a request using 'http://'. This request will be unencrypted, and attackers could listen into traffic on the network and be able to obtain sensitive information. Use 'https://' instead. (rule ID: 3fbbd34b-b00d-4415-b9d9-f861c076b9f2) in file: ./requests.py ⛔
@@ -581,7 +588,7 @@ Secret SHA: a44081db3296c84b82d12a35c446a3cba19411dddfa0380134c75f7b3973bff0
4 | print(res.content)
```
-# Ignoring Scan Results
+## Ignoring Scan Results
Ignore rules can be added to ignore specific secret values, specific SHA512 values, specific paths, and specific Cycode secret and IaC rule IDs. This will cause the scan to not alert these values. The ignore rules are written and saved locally in the `./.cycode/config.yaml` file.
@@ -612,7 +619,7 @@ Secret SHA: a44081db3296c84b82d12a35c446a3cba19411dddfa0380134c75f7b3973bff0
If this is a value that is not a valid secret, then use the the `cycode ignore` command to ignore the secret by its value, SHA value, specific path, or rule ID. If this is an IaC scan, then you can ignore that result by its path or rule ID.
-## Ignoring a Secret Value
+### Ignoring a Secret Value
To ignore a specific secret value, you will need to use the `--by-value` flag. This will ignore the given secret value from all future scans. Use the following command to add a secret value to be ignored:
@@ -624,7 +631,7 @@ In the example at the top of this section, the command to ignore a specific secr
In the example above, replace the `h3110w0r1d!@#$350` value with your non-masked secret value. See the Cycode scan options for details on how to see secret values in the scan results.
-## Ignoring a Secret SHA Value
+### Ignoring a Secret SHA Value
To ignore a specific secret SHA value, you will need to use the `--by-sha` flag. This will ignore the given secret SHA value from all future scans. Use the following command to add a secret SHA value to be ignored:
@@ -636,7 +643,7 @@ In the example at the top of this section, the command to ignore a specific secr
In the example above, replace the `a44081db3296c84b82d12a35c446a3cba19411dddfa0380134c75f7b3973bff0` value with your secret SHA value.
-## Ignoring a Path
+### Ignoring a Path
To ignore a specific path for either secret, IaC, or SCA scans, you will need to use the `--by-path` flag in conjunction with the `-t, --scan-type` flag (you must specify the scan type). This will ignore the given path from all future scans for the given scan type. Use the following command to add a path to be ignored:
@@ -664,7 +671,7 @@ In the example at the top of this section, the command to ignore a specific path
In the example above, replace the `~/home/my-repo/config` value with your path value.
-## Ignoring a Secret, IaC, SCA, or SAST Rule
+### Ignoring a Secret, IaC, SCA, or SAST Rule
To ignore a specific secret, IaC, SCA, or SAST rule, you will need to use the `--by-rule` flag in conjunction with the `-t, --scan-type` flag (you must specify the scan type). This will ignore the given rule ID value from all future scans. Use the following command to add a rule ID value to be ignored:
@@ -692,7 +699,7 @@ In the example at the top of this section, the command to ignore the specific SC
In the example above, replace the `dc21bc6b-9f4f-46fb-9f92-e4327ea03f6b` value with the rule ID you want to ignore.
-## Ignoring a Package
+### Ignoring a Package
> :memo: **Note**
> This option is only available to the SCA scans.
@@ -711,6 +718,44 @@ In the example below, the command to ignore a specific SCA package is as follows
In the example above, replace `pyyaml` with package name and `5.3.1` with the package version you want to ignore.
+# Report Command
+
+## Generating SBOM Report
+
+A software bill of materials (SBOM) is an inventory of all constituent components and software dependencies involved in the development and delivery of an application.
+Using this command you can create an SBOM report for your local project or for your repository URI.
+
+The following options are available for use with this command:
+| Option | Description | Required | Default |
+|---------------------|-------------|----------|---------|
+| `-f, --format [spdx-2.2\|spdx-2.3\|cyclonedx-1.4]` | SBOM format | Yes | |
+| `-o, --output-format [JSON]` | Specify the output file format | No | json |
+| `--output-file PATH` | Output file | No | autogenerated filename saved to the current directory |
+| `--include-vulnerabilities` | Include vulnerabilities | No | False |
+| `--include-dev-dependencies` | Include dev dependencies | No | False |
+
+The following commands are available for use with this command:
+| Command | Description |
+|---------------------|-------------|
+| `path` | Generate SBOM report for provided path in the command |
+| `repository_url` | Generate SBOM report for provided repository URI in the command |
+
+### Repository
+
+To create an SBOM report for a repository URI:\
+`cycode report sbom --format --include-vulnerabilities --include-dev-dependencies --output-file repository_url `
+
+For example:\
+`cycode report sbom --format spdx-2.3 --include-vulnerabilities --include-dev-dependencies repository_url https://github.com/cycodehq-public/cycode-cli.git`
+
+### Local Project
+
+To create an SBOM report for a path:\
+`cycode report sbom --format --include-vulnerabilities --include-dev-dependencies --output-file path `
+
+For example:\
+`cycode report sbom --format spdx-2.3 --include-vulnerabilities --include-dev-dependencies path /path/to/local/project`
+
# Syntax Help
You may add the `--help` argument to any command at any time to see a help message that will display available options and their syntax.
@@ -734,3 +779,12 @@ For example, to see options available for a Path Scan, you would simply enter:
To see the options available for the ignore scan function, use this command:
`cycode ignore --help`
+
+To see the options available for report, use this command:
+
+`cycode report --help`
+
+
+To see the options available for a specific type of report, enter:
+
+`cycode scan {{option}} --help`
From 6025e9b4b3f66d7262413c3b13435180d8c94abf Mon Sep 17 00:00:00 2001
From: Ilya Siamionau
Date: Mon, 23 Oct 2023 10:59:12 +0200
Subject: [PATCH 040/257] CM-26497 - Attach signed executables and their
checksums as assets to GitHub releases (#172)
---
.github/workflows/build_executable.yml | 65 ++++++++++++++++++++++----
1 file changed, 55 insertions(+), 10 deletions(-)
diff --git a/.github/workflows/build_executable.yml b/.github/workflows/build_executable.yml
index ed88613e..daecd99f 100644
--- a/.github/workflows/build_executable.yml
+++ b/.github/workflows/build_executable.yml
@@ -1,10 +1,14 @@
-name: Build executable version of CLI
+name: Build executable version of CLI and upload artifact. On dispatch event build the latest tag and upload to release assets
on:
+ workflow_dispatch:
push:
branches:
- main
+permissions:
+ contents: write
+
jobs:
build:
strategy:
@@ -32,10 +36,17 @@ jobs:
pypi.org
- name: Checkout repository
- uses: actions/checkout@v3
+ uses: actions/checkout@v4
with:
fetch-depth: 0
+ - name: Checkout latest release tag
+ if: ${{ github.event_name == 'workflow_dispatch' }}
+ run: |
+ LATEST_TAG=$(git describe --tags `git rev-list --tags --max-count=1`)
+ git checkout $LATEST_TAG
+ echo "LATEST_TAG=$LATEST_TAG" >> $GITHUB_ENV
+
- name: Set up Python 3.7
uses: actions/setup-python@v4
with:
@@ -67,7 +78,7 @@ jobs:
run: ./dist/cycode version
- name: Sign macOS executable
- if: ${{ startsWith(matrix.os, 'macos') }}
+ if: runner.os == 'macOS'
env:
APPLE_CERT: ${{ secrets.APPLE_CERT }}
APPLE_CERT_PWD: ${{ secrets.APPLE_CERT_PWD }}
@@ -92,7 +103,7 @@ jobs:
codesign --deep --force --options=runtime --entitlements entitlements.plist --sign "$APPLE_CERT_NAME" --timestamp dist/cycode
- name: Notarize macOS executable
- if: ${{ startsWith(matrix.os, 'macos') }}
+ if: runner.os == 'macOS'
env:
APPLE_NOTARIZATION_EMAIL: ${{ secrets.APPLE_NOTARIZATION_EMAIL }}
APPLE_NOTARIZATION_PWD: ${{ secrets.APPLE_NOTARIZATION_PWD }}
@@ -111,11 +122,11 @@ jobs:
# xcrun stapler staple dist/cycode
- name: Test macOS signed executable
- if: ${{ startsWith(matrix.os, 'macos') }}
+ if: runner.os == 'macOS'
run: ./dist/cycode version
- name: Import cert for Windows and setup envs
- if: ${{ startsWith(matrix.os, 'windows') }}
+ if: runner.os == 'Windows'
env:
SM_CLIENT_CERT_FILE_B64: ${{ secrets.SM_CLIENT_CERT_FILE_B64 }}
run: |
@@ -128,7 +139,7 @@ jobs:
echo "C:\Program Files\DigiCert\DigiCert One Signing Manager Tools" >> $GITHUB_PATH
- name: Sign Windows executable
- if: ${{ startsWith(matrix.os, 'windows') }}
+ if: runner.os == 'Windows'
shell: cmd
env:
SM_HOST: ${{ secrets.SM_HOST }}
@@ -146,7 +157,7 @@ jobs:
signtool.exe sign /sha1 %SM_CODE_SIGNING_CERT_SHA1_HASH% /tr http://timestamp.digicert.com /td SHA256 /fd SHA256 ".\dist\cycode.exe"
- name: Test Windows signed executable
- if: ${{ startsWith(matrix.os, 'windows') }}
+ if: runner.os == 'Windows'
shell: cmd
run: |
:: call executable and expect correct output
@@ -155,7 +166,41 @@ jobs:
:: verify signature
signtool.exe verify /v /pa ".\dist\cycode.exe"
- - uses: actions/upload-artifact@v3
+ - name: Prepare files on Windows
+ if: runner.os == 'Windows'
+ run: |
+ echo "ARTIFACT_NAME=cycode-win" >> $GITHUB_ENV
+ mv dist/cycode.exe dist/cycode-win.exe
+ powershell -Command "(Get-FileHash -Algorithm SHA256 dist/cycode-win.exe).Hash" > sha256
+ head -c 64 sha256 > dist/cycode-win.exe.sha256
+
+ - name: Prepare files on macOS
+ if: runner.os == 'macOS'
+ run: |
+ echo "ARTIFACT_NAME=cycode-mac" >> $GITHUB_ENV
+ mv dist/cycode dist/cycode-mac
+ shasum -a 256 dist/cycode-mac > sha256
+ head -c 64 sha256 > dist/cycode-mac.sha256
+
+ - name: Prepare files on Linux
+ if: runner.os == 'Linux'
+ run: |
+ echo "ARTIFACT_NAME=cycode-linux" >> $GITHUB_ENV
+ mv dist/cycode dist/cycode-linux
+ sha256sum dist/cycode-linux > sha256
+ head -c 64 sha256 > dist/cycode-linux.sha256
+
+ - name: Upload files as artifact
+ uses: actions/upload-artifact@v3
with:
- name: cycode-cli-${{ matrix.os }}
+ name: ${{ env.ARTIFACT_NAME }}
path: dist
+
+ - name: Upload files to release
+ if: ${{ github.event_name == 'workflow_dispatch' }}
+ uses: svenstaro/upload-release-action@v2
+ with:
+ file: dist/*
+ tag: ${{ env.LATEST_TAG }}
+ overwrite: true
+ file_glob: true
From 4549b2b74973e70ce0a71b815e18304c7c4aec8d Mon Sep 17 00:00:00 2001
From: Ilya Siamionau
Date: Mon, 23 Oct 2023 11:38:30 +0200
Subject: [PATCH 041/257] CM-26497 - Fix CIMON (#173)
---
.github/workflows/build_executable.yml | 1 +
1 file changed, 1 insertion(+)
diff --git a/.github/workflows/build_executable.yml b/.github/workflows/build_executable.yml
index daecd99f..a0a0e706 100644
--- a/.github/workflows/build_executable.yml
+++ b/.github/workflows/build_executable.yml
@@ -34,6 +34,7 @@ jobs:
files.pythonhosted.org
install.python-poetry.org
pypi.org
+ uploads.github.com
- name: Checkout repository
uses: actions/checkout@v4
From bc33ae05c2cd291aa0a478dcb1a037a51f495d61 Mon Sep 17 00:00:00 2001
From: Ilya Siamionau
Date: Tue, 24 Oct 2023 11:43:18 +0200
Subject: [PATCH 042/257] CM-28389 - Update "cycode configure" section in
README (#174)
---
README.md | 32 ++++++++++++++++++++++----------
1 file changed, 22 insertions(+), 10 deletions(-)
diff --git a/README.md b/README.md
index 7673a272..ffbaf350 100644
--- a/README.md
+++ b/README.md
@@ -119,38 +119,50 @@ To install the Cycode CLI application on your local machine, perform the followi
### Using the Configure Command
> :memo: **Note**
-> If you already set up your Cycode client ID and client secret through the Linux or Windows environment variables, those credentials will take precedent over this method.
+> If you already set up your Cycode Client ID and Client Secret through the Linux or Windows environment variables, those credentials will take precedent over this method.
1. Type the following command into your terminal/command line window:
`cycode configure`
- You will see the following appear:
+2. Enter your Cycode API URL value (you can leave blank to use default value).
```bash
- Update credentials in file (/Users/travislloyd/.cycode/credentials.yaml)
- cycode client id []:
+ Cycode API URL [https://api.cycode.com]: https://api.onpremise.com
```
-2. Enter your Cycode client ID value.
+3. Enter your Cycode APP URL value (you can leave blank to use default value).
```bash
- cycode client id []: 7fe5346b-xxxx-xxxx-xxxx-55157625c72d
+ Cycode APP URL [https://app.cycode.com]: https://app.onpremise.com
```
-3. Enter your Cycode client secret value.
+4. Enter your Cycode Client ID value.
```bash
- cycode client secret []: c1e24929-xxxx-xxxx-xxxx-8b08c1839a2e
+ Cycode Client ID []: 7fe5346b-xxxx-xxxx-xxxx-55157625c72d
```
-4. If the values were entered successfully, you'll see the following message:
+5. Enter your Cycode Client Secret value.
+
+ ```bash
+ Cycode Client Secret []: c1e24929-xxxx-xxxx-xxxx-8b08c1839a2e
+ ```
+
+6. If the values were entered successfully, you'll see the following message:
```bash
Successfully configured CLI credentials!
```
-If you go into the `.cycode` folder under your user folder, you'll find these credentials were created and placed in the `credentials.yaml` file in that folder.
+ or/and
+
+ ```bash
+ Successfully configured Cycode URLs!
+ ```
+
+If you go into the `.cycode` folder under your user folder, you'll find these credentials were created and placed in the `credentials.yaml` file in that folder.
+And the URLs were placed in the `config.yaml` file in that folder.
### Add to Environment Variables
From 640b58679988a7e2254e5c5eda75fb48d941e8ac Mon Sep 17 00:00:00 2001
From: Ilya Siamionau
Date: Wed, 25 Oct 2023 16:20:11 +0200
Subject: [PATCH 043/257] CM-28473 - Upgrade dynamic versioning (fix
compatibility with Poetry) (#175)
---
.github/workflows/tests_full.yml | 14 +-
poetry.lock | 220 +++++++++++++++----------------
pyproject.toml | 4 +-
3 files changed, 118 insertions(+), 120 deletions(-)
diff --git a/.github/workflows/tests_full.yml b/.github/workflows/tests_full.yml
index aa2c0fc2..aaa58d89 100644
--- a/.github/workflows/tests_full.yml
+++ b/.github/workflows/tests_full.yml
@@ -35,7 +35,9 @@ jobs:
pypi.org
- name: Checkout repository
- uses: actions/checkout@v3
+ uses: actions/checkout@v4
+ with:
+ fetch-depth: 0
- name: Set up Python
uses: actions/setup-python@v4
@@ -47,7 +49,7 @@ jobs:
uses: actions/cache@v3
with:
path: ~/.local
- key: poetry-${{ matrix.os }}-0 # increment to reset cache
+ key: poetry-${{ matrix.os }}-1 # increment to reset cache
- name: Setup Poetry
if: steps.cached-poetry.outputs.cache-hit != 'true'
@@ -61,5 +63,11 @@ jobs:
- name: Install dependencies
run: poetry install
- - name: Run Tests
+ - name: Run executable test
+ if: runner.os == 'Linux'
+ run: |
+ poetry run pyinstaller pyinstaller.spec
+ ./dist/cycode version
+
+ - name: Run pytest
run: poetry run pytest
diff --git a/poetry.lock b/poetry.lock
index dd0cfec3..04f7b712 100644
--- a/poetry.lock
+++ b/poetry.lock
@@ -114,101 +114,101 @@ files = [
[[package]]
name = "charset-normalizer"
-version = "3.3.0"
+version = "3.3.1"
description = "The Real First Universal Charset Detector. Open, modern and actively maintained alternative to Chardet."
optional = false
python-versions = ">=3.7.0"
files = [
- {file = "charset-normalizer-3.3.0.tar.gz", hash = "sha256:63563193aec44bce707e0c5ca64ff69fa72ed7cf34ce6e11d5127555756fd2f6"},
- {file = "charset_normalizer-3.3.0-cp310-cp310-macosx_10_9_universal2.whl", hash = "sha256:effe5406c9bd748a871dbcaf3ac69167c38d72db8c9baf3ff954c344f31c4cbe"},
- {file = "charset_normalizer-3.3.0-cp310-cp310-macosx_10_9_x86_64.whl", hash = "sha256:4162918ef3098851fcd8a628bf9b6a98d10c380725df9e04caf5ca6dd48c847a"},
- {file = "charset_normalizer-3.3.0-cp310-cp310-macosx_11_0_arm64.whl", hash = "sha256:0570d21da019941634a531444364f2482e8db0b3425fcd5ac0c36565a64142c8"},
- {file = "charset_normalizer-3.3.0-cp310-cp310-manylinux_2_17_aarch64.manylinux2014_aarch64.whl", hash = "sha256:5707a746c6083a3a74b46b3a631d78d129edab06195a92a8ece755aac25a3f3d"},
- {file = "charset_normalizer-3.3.0-cp310-cp310-manylinux_2_17_ppc64le.manylinux2014_ppc64le.whl", hash = "sha256:278c296c6f96fa686d74eb449ea1697f3c03dc28b75f873b65b5201806346a69"},
- {file = "charset_normalizer-3.3.0-cp310-cp310-manylinux_2_17_s390x.manylinux2014_s390x.whl", hash = "sha256:a4b71f4d1765639372a3b32d2638197f5cd5221b19531f9245fcc9ee62d38f56"},
- {file = "charset_normalizer-3.3.0-cp310-cp310-manylinux_2_17_x86_64.manylinux2014_x86_64.whl", hash = "sha256:f5969baeaea61c97efa706b9b107dcba02784b1601c74ac84f2a532ea079403e"},
- {file = "charset_normalizer-3.3.0-cp310-cp310-manylinux_2_5_i686.manylinux1_i686.manylinux_2_17_i686.manylinux2014_i686.whl", hash = "sha256:a3f93dab657839dfa61025056606600a11d0b696d79386f974e459a3fbc568ec"},
- {file = "charset_normalizer-3.3.0-cp310-cp310-musllinux_1_1_aarch64.whl", hash = "sha256:db756e48f9c5c607b5e33dd36b1d5872d0422e960145b08ab0ec7fd420e9d649"},
- {file = "charset_normalizer-3.3.0-cp310-cp310-musllinux_1_1_i686.whl", hash = "sha256:232ac332403e37e4a03d209a3f92ed9071f7d3dbda70e2a5e9cff1c4ba9f0678"},
- {file = "charset_normalizer-3.3.0-cp310-cp310-musllinux_1_1_ppc64le.whl", hash = "sha256:e5c1502d4ace69a179305abb3f0bb6141cbe4714bc9b31d427329a95acfc8bdd"},
- {file = "charset_normalizer-3.3.0-cp310-cp310-musllinux_1_1_s390x.whl", hash = "sha256:2502dd2a736c879c0f0d3e2161e74d9907231e25d35794584b1ca5284e43f596"},
- {file = "charset_normalizer-3.3.0-cp310-cp310-musllinux_1_1_x86_64.whl", hash = "sha256:23e8565ab7ff33218530bc817922fae827420f143479b753104ab801145b1d5b"},
- {file = "charset_normalizer-3.3.0-cp310-cp310-win32.whl", hash = "sha256:1872d01ac8c618a8da634e232f24793883d6e456a66593135aeafe3784b0848d"},
- {file = "charset_normalizer-3.3.0-cp310-cp310-win_amd64.whl", hash = "sha256:557b21a44ceac6c6b9773bc65aa1b4cc3e248a5ad2f5b914b91579a32e22204d"},
- {file = "charset_normalizer-3.3.0-cp311-cp311-macosx_10_9_universal2.whl", hash = "sha256:d7eff0f27edc5afa9e405f7165f85a6d782d308f3b6b9d96016c010597958e63"},
- {file = "charset_normalizer-3.3.0-cp311-cp311-macosx_10_9_x86_64.whl", hash = "sha256:6a685067d05e46641d5d1623d7c7fdf15a357546cbb2f71b0ebde91b175ffc3e"},
- {file = "charset_normalizer-3.3.0-cp311-cp311-macosx_11_0_arm64.whl", hash = "sha256:0d3d5b7db9ed8a2b11a774db2bbea7ba1884430a205dbd54a32d61d7c2a190fa"},
- {file = "charset_normalizer-3.3.0-cp311-cp311-manylinux_2_17_aarch64.manylinux2014_aarch64.whl", hash = "sha256:2935ffc78db9645cb2086c2f8f4cfd23d9b73cc0dc80334bc30aac6f03f68f8c"},
- {file = "charset_normalizer-3.3.0-cp311-cp311-manylinux_2_17_ppc64le.manylinux2014_ppc64le.whl", hash = "sha256:9fe359b2e3a7729010060fbca442ca225280c16e923b37db0e955ac2a2b72a05"},
- {file = "charset_normalizer-3.3.0-cp311-cp311-manylinux_2_17_s390x.manylinux2014_s390x.whl", hash = "sha256:380c4bde80bce25c6e4f77b19386f5ec9db230df9f2f2ac1e5ad7af2caa70459"},
- {file = "charset_normalizer-3.3.0-cp311-cp311-manylinux_2_17_x86_64.manylinux2014_x86_64.whl", hash = "sha256:f0d1e3732768fecb052d90d62b220af62ead5748ac51ef61e7b32c266cac9293"},
- {file = "charset_normalizer-3.3.0-cp311-cp311-manylinux_2_5_i686.manylinux1_i686.manylinux_2_17_i686.manylinux2014_i686.whl", hash = "sha256:1b2919306936ac6efb3aed1fbf81039f7087ddadb3160882a57ee2ff74fd2382"},
- {file = "charset_normalizer-3.3.0-cp311-cp311-musllinux_1_1_aarch64.whl", hash = "sha256:f8888e31e3a85943743f8fc15e71536bda1c81d5aa36d014a3c0c44481d7db6e"},
- {file = "charset_normalizer-3.3.0-cp311-cp311-musllinux_1_1_i686.whl", hash = "sha256:82eb849f085624f6a607538ee7b83a6d8126df6d2f7d3b319cb837b289123078"},
- {file = "charset_normalizer-3.3.0-cp311-cp311-musllinux_1_1_ppc64le.whl", hash = "sha256:7b8b8bf1189b3ba9b8de5c8db4d541b406611a71a955bbbd7385bbc45fcb786c"},
- {file = "charset_normalizer-3.3.0-cp311-cp311-musllinux_1_1_s390x.whl", hash = "sha256:5adf257bd58c1b8632046bbe43ee38c04e1038e9d37de9c57a94d6bd6ce5da34"},
- {file = "charset_normalizer-3.3.0-cp311-cp311-musllinux_1_1_x86_64.whl", hash = "sha256:c350354efb159b8767a6244c166f66e67506e06c8924ed74669b2c70bc8735b1"},
- {file = "charset_normalizer-3.3.0-cp311-cp311-win32.whl", hash = "sha256:02af06682e3590ab952599fbadac535ede5d60d78848e555aa58d0c0abbde786"},
- {file = "charset_normalizer-3.3.0-cp311-cp311-win_amd64.whl", hash = "sha256:86d1f65ac145e2c9ed71d8ffb1905e9bba3a91ae29ba55b4c46ae6fc31d7c0d4"},
- {file = "charset_normalizer-3.3.0-cp312-cp312-macosx_10_9_universal2.whl", hash = "sha256:3b447982ad46348c02cb90d230b75ac34e9886273df3a93eec0539308a6296d7"},
- {file = "charset_normalizer-3.3.0-cp312-cp312-macosx_10_9_x86_64.whl", hash = "sha256:abf0d9f45ea5fb95051c8bfe43cb40cda383772f7e5023a83cc481ca2604d74e"},
- {file = "charset_normalizer-3.3.0-cp312-cp312-macosx_11_0_arm64.whl", hash = "sha256:b09719a17a2301178fac4470d54b1680b18a5048b481cb8890e1ef820cb80455"},
- {file = "charset_normalizer-3.3.0-cp312-cp312-manylinux_2_17_aarch64.manylinux2014_aarch64.whl", hash = "sha256:b3d9b48ee6e3967b7901c052b670c7dda6deb812c309439adaffdec55c6d7b78"},
- {file = "charset_normalizer-3.3.0-cp312-cp312-manylinux_2_17_ppc64le.manylinux2014_ppc64le.whl", hash = "sha256:edfe077ab09442d4ef3c52cb1f9dab89bff02f4524afc0acf2d46be17dc479f5"},
- {file = "charset_normalizer-3.3.0-cp312-cp312-manylinux_2_17_s390x.manylinux2014_s390x.whl", hash = "sha256:3debd1150027933210c2fc321527c2299118aa929c2f5a0a80ab6953e3bd1908"},
- {file = "charset_normalizer-3.3.0-cp312-cp312-manylinux_2_17_x86_64.manylinux2014_x86_64.whl", hash = "sha256:86f63face3a527284f7bb8a9d4f78988e3c06823f7bea2bd6f0e0e9298ca0403"},
- {file = "charset_normalizer-3.3.0-cp312-cp312-manylinux_2_5_i686.manylinux1_i686.manylinux_2_17_i686.manylinux2014_i686.whl", hash = "sha256:24817cb02cbef7cd499f7c9a2735286b4782bd47a5b3516a0e84c50eab44b98e"},
- {file = "charset_normalizer-3.3.0-cp312-cp312-musllinux_1_1_aarch64.whl", hash = "sha256:c71f16da1ed8949774ef79f4a0260d28b83b3a50c6576f8f4f0288d109777989"},
- {file = "charset_normalizer-3.3.0-cp312-cp312-musllinux_1_1_i686.whl", hash = "sha256:9cf3126b85822c4e53aa28c7ec9869b924d6fcfb76e77a45c44b83d91afd74f9"},
- {file = "charset_normalizer-3.3.0-cp312-cp312-musllinux_1_1_ppc64le.whl", hash = "sha256:b3b2316b25644b23b54a6f6401074cebcecd1244c0b8e80111c9a3f1c8e83d65"},
- {file = "charset_normalizer-3.3.0-cp312-cp312-musllinux_1_1_s390x.whl", hash = "sha256:03680bb39035fbcffe828eae9c3f8afc0428c91d38e7d61aa992ef7a59fb120e"},
- {file = "charset_normalizer-3.3.0-cp312-cp312-musllinux_1_1_x86_64.whl", hash = "sha256:4cc152c5dd831641e995764f9f0b6589519f6f5123258ccaca8c6d34572fefa8"},
- {file = "charset_normalizer-3.3.0-cp312-cp312-win32.whl", hash = "sha256:b8f3307af845803fb0b060ab76cf6dd3a13adc15b6b451f54281d25911eb92df"},
- {file = "charset_normalizer-3.3.0-cp312-cp312-win_amd64.whl", hash = "sha256:8eaf82f0eccd1505cf39a45a6bd0a8cf1c70dcfc30dba338207a969d91b965c0"},
- {file = "charset_normalizer-3.3.0-cp37-cp37m-macosx_10_9_x86_64.whl", hash = "sha256:dc45229747b67ffc441b3de2f3ae5e62877a282ea828a5bdb67883c4ee4a8810"},
- {file = "charset_normalizer-3.3.0-cp37-cp37m-manylinux_2_17_aarch64.manylinux2014_aarch64.whl", hash = "sha256:2f4a0033ce9a76e391542c182f0d48d084855b5fcba5010f707c8e8c34663d77"},
- {file = "charset_normalizer-3.3.0-cp37-cp37m-manylinux_2_17_ppc64le.manylinux2014_ppc64le.whl", hash = "sha256:ada214c6fa40f8d800e575de6b91a40d0548139e5dc457d2ebb61470abf50186"},
- {file = "charset_normalizer-3.3.0-cp37-cp37m-manylinux_2_17_s390x.manylinux2014_s390x.whl", hash = "sha256:b1121de0e9d6e6ca08289583d7491e7fcb18a439305b34a30b20d8215922d43c"},
- {file = "charset_normalizer-3.3.0-cp37-cp37m-manylinux_2_17_x86_64.manylinux2014_x86_64.whl", hash = "sha256:1063da2c85b95f2d1a430f1c33b55c9c17ffaf5e612e10aeaad641c55a9e2b9d"},
- {file = "charset_normalizer-3.3.0-cp37-cp37m-manylinux_2_5_i686.manylinux1_i686.manylinux_2_17_i686.manylinux2014_i686.whl", hash = "sha256:70f1d09c0d7748b73290b29219e854b3207aea922f839437870d8cc2168e31cc"},
- {file = "charset_normalizer-3.3.0-cp37-cp37m-musllinux_1_1_aarch64.whl", hash = "sha256:250c9eb0f4600361dd80d46112213dff2286231d92d3e52af1e5a6083d10cad9"},
- {file = "charset_normalizer-3.3.0-cp37-cp37m-musllinux_1_1_i686.whl", hash = "sha256:750b446b2ffce1739e8578576092179160f6d26bd5e23eb1789c4d64d5af7dc7"},
- {file = "charset_normalizer-3.3.0-cp37-cp37m-musllinux_1_1_ppc64le.whl", hash = "sha256:fc52b79d83a3fe3a360902d3f5d79073a993597d48114c29485e9431092905d8"},
- {file = "charset_normalizer-3.3.0-cp37-cp37m-musllinux_1_1_s390x.whl", hash = "sha256:588245972aca710b5b68802c8cad9edaa98589b1b42ad2b53accd6910dad3545"},
- {file = "charset_normalizer-3.3.0-cp37-cp37m-musllinux_1_1_x86_64.whl", hash = "sha256:e39c7eb31e3f5b1f88caff88bcff1b7f8334975b46f6ac6e9fc725d829bc35d4"},
- {file = "charset_normalizer-3.3.0-cp37-cp37m-win32.whl", hash = "sha256:abecce40dfebbfa6abf8e324e1860092eeca6f7375c8c4e655a8afb61af58f2c"},
- {file = "charset_normalizer-3.3.0-cp37-cp37m-win_amd64.whl", hash = "sha256:24a91a981f185721542a0b7c92e9054b7ab4fea0508a795846bc5b0abf8118d4"},
- {file = "charset_normalizer-3.3.0-cp38-cp38-macosx_10_9_universal2.whl", hash = "sha256:67b8cc9574bb518ec76dc8e705d4c39ae78bb96237cb533edac149352c1f39fe"},
- {file = "charset_normalizer-3.3.0-cp38-cp38-macosx_10_9_x86_64.whl", hash = "sha256:ac71b2977fb90c35d41c9453116e283fac47bb9096ad917b8819ca8b943abecd"},
- {file = "charset_normalizer-3.3.0-cp38-cp38-macosx_11_0_arm64.whl", hash = "sha256:3ae38d325b512f63f8da31f826e6cb6c367336f95e418137286ba362925c877e"},
- {file = "charset_normalizer-3.3.0-cp38-cp38-manylinux_2_17_aarch64.manylinux2014_aarch64.whl", hash = "sha256:542da1178c1c6af8873e143910e2269add130a299c9106eef2594e15dae5e482"},
- {file = "charset_normalizer-3.3.0-cp38-cp38-manylinux_2_17_ppc64le.manylinux2014_ppc64le.whl", hash = "sha256:30a85aed0b864ac88309b7d94be09f6046c834ef60762a8833b660139cfbad13"},
- {file = "charset_normalizer-3.3.0-cp38-cp38-manylinux_2_17_s390x.manylinux2014_s390x.whl", hash = "sha256:aae32c93e0f64469f74ccc730a7cb21c7610af3a775157e50bbd38f816536b38"},
- {file = "charset_normalizer-3.3.0-cp38-cp38-manylinux_2_17_x86_64.manylinux2014_x86_64.whl", hash = "sha256:15b26ddf78d57f1d143bdf32e820fd8935d36abe8a25eb9ec0b5a71c82eb3895"},
- {file = "charset_normalizer-3.3.0-cp38-cp38-manylinux_2_5_i686.manylinux1_i686.manylinux_2_17_i686.manylinux2014_i686.whl", hash = "sha256:7f5d10bae5d78e4551b7be7a9b29643a95aded9d0f602aa2ba584f0388e7a557"},
- {file = "charset_normalizer-3.3.0-cp38-cp38-musllinux_1_1_aarch64.whl", hash = "sha256:249c6470a2b60935bafd1d1d13cd613f8cd8388d53461c67397ee6a0f5dce741"},
- {file = "charset_normalizer-3.3.0-cp38-cp38-musllinux_1_1_i686.whl", hash = "sha256:c5a74c359b2d47d26cdbbc7845e9662d6b08a1e915eb015d044729e92e7050b7"},
- {file = "charset_normalizer-3.3.0-cp38-cp38-musllinux_1_1_ppc64le.whl", hash = "sha256:b5bcf60a228acae568e9911f410f9d9e0d43197d030ae5799e20dca8df588287"},
- {file = "charset_normalizer-3.3.0-cp38-cp38-musllinux_1_1_s390x.whl", hash = "sha256:187d18082694a29005ba2944c882344b6748d5be69e3a89bf3cc9d878e548d5a"},
- {file = "charset_normalizer-3.3.0-cp38-cp38-musllinux_1_1_x86_64.whl", hash = "sha256:81bf654678e575403736b85ba3a7867e31c2c30a69bc57fe88e3ace52fb17b89"},
- {file = "charset_normalizer-3.3.0-cp38-cp38-win32.whl", hash = "sha256:85a32721ddde63c9df9ebb0d2045b9691d9750cb139c161c80e500d210f5e26e"},
- {file = "charset_normalizer-3.3.0-cp38-cp38-win_amd64.whl", hash = "sha256:468d2a840567b13a590e67dd276c570f8de00ed767ecc611994c301d0f8c014f"},
- {file = "charset_normalizer-3.3.0-cp39-cp39-macosx_10_9_universal2.whl", hash = "sha256:e0fc42822278451bc13a2e8626cf2218ba570f27856b536e00cfa53099724828"},
- {file = "charset_normalizer-3.3.0-cp39-cp39-macosx_10_9_x86_64.whl", hash = "sha256:09c77f964f351a7369cc343911e0df63e762e42bac24cd7d18525961c81754f4"},
- {file = "charset_normalizer-3.3.0-cp39-cp39-macosx_11_0_arm64.whl", hash = "sha256:12ebea541c44fdc88ccb794a13fe861cc5e35d64ed689513a5c03d05b53b7c82"},
- {file = "charset_normalizer-3.3.0-cp39-cp39-manylinux_2_17_aarch64.manylinux2014_aarch64.whl", hash = "sha256:805dfea4ca10411a5296bcc75638017215a93ffb584c9e344731eef0dcfb026a"},
- {file = "charset_normalizer-3.3.0-cp39-cp39-manylinux_2_17_ppc64le.manylinux2014_ppc64le.whl", hash = "sha256:96c2b49eb6a72c0e4991d62406e365d87067ca14c1a729a870d22354e6f68115"},
- {file = "charset_normalizer-3.3.0-cp39-cp39-manylinux_2_17_s390x.manylinux2014_s390x.whl", hash = "sha256:aaf7b34c5bc56b38c931a54f7952f1ff0ae77a2e82496583b247f7c969eb1479"},
- {file = "charset_normalizer-3.3.0-cp39-cp39-manylinux_2_17_x86_64.manylinux2014_x86_64.whl", hash = "sha256:619d1c96099be5823db34fe89e2582b336b5b074a7f47f819d6b3a57ff7bdb86"},
- {file = "charset_normalizer-3.3.0-cp39-cp39-manylinux_2_5_i686.manylinux1_i686.manylinux_2_17_i686.manylinux2014_i686.whl", hash = "sha256:a0ac5e7015a5920cfce654c06618ec40c33e12801711da6b4258af59a8eff00a"},
- {file = "charset_normalizer-3.3.0-cp39-cp39-musllinux_1_1_aarch64.whl", hash = "sha256:93aa7eef6ee71c629b51ef873991d6911b906d7312c6e8e99790c0f33c576f89"},
- {file = "charset_normalizer-3.3.0-cp39-cp39-musllinux_1_1_i686.whl", hash = "sha256:7966951325782121e67c81299a031f4c115615e68046f79b85856b86ebffc4cd"},
- {file = "charset_normalizer-3.3.0-cp39-cp39-musllinux_1_1_ppc64le.whl", hash = "sha256:02673e456dc5ab13659f85196c534dc596d4ef260e4d86e856c3b2773ce09843"},
- {file = "charset_normalizer-3.3.0-cp39-cp39-musllinux_1_1_s390x.whl", hash = "sha256:c2af80fb58f0f24b3f3adcb9148e6203fa67dd3f61c4af146ecad033024dde43"},
- {file = "charset_normalizer-3.3.0-cp39-cp39-musllinux_1_1_x86_64.whl", hash = "sha256:153e7b6e724761741e0974fc4dcd406d35ba70b92bfe3fedcb497226c93b9da7"},
- {file = "charset_normalizer-3.3.0-cp39-cp39-win32.whl", hash = "sha256:d47ecf253780c90ee181d4d871cd655a789da937454045b17b5798da9393901a"},
- {file = "charset_normalizer-3.3.0-cp39-cp39-win_amd64.whl", hash = "sha256:d97d85fa63f315a8bdaba2af9a6a686e0eceab77b3089af45133252618e70884"},
- {file = "charset_normalizer-3.3.0-py3-none-any.whl", hash = "sha256:e46cd37076971c1040fc8c41273a8b3e2c624ce4f2be3f5dfcb7a430c1d3acc2"},
+ {file = "charset-normalizer-3.3.1.tar.gz", hash = "sha256:d9137a876020661972ca6eec0766d81aef8a5627df628b664b234b73396e727e"},
+ {file = "charset_normalizer-3.3.1-cp310-cp310-macosx_10_9_universal2.whl", hash = "sha256:8aee051c89e13565c6bd366813c386939f8e928af93c29fda4af86d25b73d8f8"},
+ {file = "charset_normalizer-3.3.1-cp310-cp310-macosx_10_9_x86_64.whl", hash = "sha256:352a88c3df0d1fa886562384b86f9a9e27563d4704ee0e9d56ec6fcd270ea690"},
+ {file = "charset_normalizer-3.3.1-cp310-cp310-macosx_11_0_arm64.whl", hash = "sha256:223b4d54561c01048f657fa6ce41461d5ad8ff128b9678cfe8b2ecd951e3f8a2"},
+ {file = "charset_normalizer-3.3.1-cp310-cp310-manylinux_2_17_aarch64.manylinux2014_aarch64.whl", hash = "sha256:4f861d94c2a450b974b86093c6c027888627b8082f1299dfd5a4bae8e2292821"},
+ {file = "charset_normalizer-3.3.1-cp310-cp310-manylinux_2_17_ppc64le.manylinux2014_ppc64le.whl", hash = "sha256:1171ef1fc5ab4693c5d151ae0fdad7f7349920eabbaca6271f95969fa0756c2d"},
+ {file = "charset_normalizer-3.3.1-cp310-cp310-manylinux_2_17_s390x.manylinux2014_s390x.whl", hash = "sha256:28f512b9a33235545fbbdac6a330a510b63be278a50071a336afc1b78781b147"},
+ {file = "charset_normalizer-3.3.1-cp310-cp310-manylinux_2_17_x86_64.manylinux2014_x86_64.whl", hash = "sha256:c0e842112fe3f1a4ffcf64b06dc4c61a88441c2f02f373367f7b4c1aa9be2ad5"},
+ {file = "charset_normalizer-3.3.1-cp310-cp310-manylinux_2_5_i686.manylinux1_i686.manylinux_2_17_i686.manylinux2014_i686.whl", hash = "sha256:3f9bc2ce123637a60ebe819f9fccc614da1bcc05798bbbaf2dd4ec91f3e08846"},
+ {file = "charset_normalizer-3.3.1-cp310-cp310-musllinux_1_1_aarch64.whl", hash = "sha256:f194cce575e59ffe442c10a360182a986535fd90b57f7debfaa5c845c409ecc3"},
+ {file = "charset_normalizer-3.3.1-cp310-cp310-musllinux_1_1_i686.whl", hash = "sha256:9a74041ba0bfa9bc9b9bb2cd3238a6ab3b7618e759b41bd15b5f6ad958d17605"},
+ {file = "charset_normalizer-3.3.1-cp310-cp310-musllinux_1_1_ppc64le.whl", hash = "sha256:b578cbe580e3b41ad17b1c428f382c814b32a6ce90f2d8e39e2e635d49e498d1"},
+ {file = "charset_normalizer-3.3.1-cp310-cp310-musllinux_1_1_s390x.whl", hash = "sha256:6db3cfb9b4fcecb4390db154e75b49578c87a3b9979b40cdf90d7e4b945656e1"},
+ {file = "charset_normalizer-3.3.1-cp310-cp310-musllinux_1_1_x86_64.whl", hash = "sha256:debb633f3f7856f95ad957d9b9c781f8e2c6303ef21724ec94bea2ce2fcbd056"},
+ {file = "charset_normalizer-3.3.1-cp310-cp310-win32.whl", hash = "sha256:87071618d3d8ec8b186d53cb6e66955ef2a0e4fa63ccd3709c0c90ac5a43520f"},
+ {file = "charset_normalizer-3.3.1-cp310-cp310-win_amd64.whl", hash = "sha256:e372d7dfd154009142631de2d316adad3cc1c36c32a38b16a4751ba78da2a397"},
+ {file = "charset_normalizer-3.3.1-cp311-cp311-macosx_10_9_universal2.whl", hash = "sha256:ae4070f741f8d809075ef697877fd350ecf0b7c5837ed68738607ee0a2c572cf"},
+ {file = "charset_normalizer-3.3.1-cp311-cp311-macosx_10_9_x86_64.whl", hash = "sha256:58e875eb7016fd014c0eea46c6fa92b87b62c0cb31b9feae25cbbe62c919f54d"},
+ {file = "charset_normalizer-3.3.1-cp311-cp311-macosx_11_0_arm64.whl", hash = "sha256:dbd95e300367aa0827496fe75a1766d198d34385a58f97683fe6e07f89ca3e3c"},
+ {file = "charset_normalizer-3.3.1-cp311-cp311-manylinux_2_17_aarch64.manylinux2014_aarch64.whl", hash = "sha256:de0b4caa1c8a21394e8ce971997614a17648f94e1cd0640fbd6b4d14cab13a72"},
+ {file = "charset_normalizer-3.3.1-cp311-cp311-manylinux_2_17_ppc64le.manylinux2014_ppc64le.whl", hash = "sha256:985c7965f62f6f32bf432e2681173db41336a9c2611693247069288bcb0c7f8b"},
+ {file = "charset_normalizer-3.3.1-cp311-cp311-manylinux_2_17_s390x.manylinux2014_s390x.whl", hash = "sha256:a15c1fe6d26e83fd2e5972425a772cca158eae58b05d4a25a4e474c221053e2d"},
+ {file = "charset_normalizer-3.3.1-cp311-cp311-manylinux_2_17_x86_64.manylinux2014_x86_64.whl", hash = "sha256:ae55d592b02c4349525b6ed8f74c692509e5adffa842e582c0f861751701a673"},
+ {file = "charset_normalizer-3.3.1-cp311-cp311-manylinux_2_5_i686.manylinux1_i686.manylinux_2_17_i686.manylinux2014_i686.whl", hash = "sha256:be4d9c2770044a59715eb57c1144dedea7c5d5ae80c68fb9959515037cde2008"},
+ {file = "charset_normalizer-3.3.1-cp311-cp311-musllinux_1_1_aarch64.whl", hash = "sha256:851cf693fb3aaef71031237cd68699dded198657ec1e76a76eb8be58c03a5d1f"},
+ {file = "charset_normalizer-3.3.1-cp311-cp311-musllinux_1_1_i686.whl", hash = "sha256:31bbaba7218904d2eabecf4feec0d07469284e952a27400f23b6628439439fa7"},
+ {file = "charset_normalizer-3.3.1-cp311-cp311-musllinux_1_1_ppc64le.whl", hash = "sha256:871d045d6ccc181fd863a3cd66ee8e395523ebfbc57f85f91f035f50cee8e3d4"},
+ {file = "charset_normalizer-3.3.1-cp311-cp311-musllinux_1_1_s390x.whl", hash = "sha256:501adc5eb6cd5f40a6f77fbd90e5ab915c8fd6e8c614af2db5561e16c600d6f3"},
+ {file = "charset_normalizer-3.3.1-cp311-cp311-musllinux_1_1_x86_64.whl", hash = "sha256:f5fb672c396d826ca16a022ac04c9dce74e00a1c344f6ad1a0fdc1ba1f332213"},
+ {file = "charset_normalizer-3.3.1-cp311-cp311-win32.whl", hash = "sha256:bb06098d019766ca16fc915ecaa455c1f1cd594204e7f840cd6258237b5079a8"},
+ {file = "charset_normalizer-3.3.1-cp311-cp311-win_amd64.whl", hash = "sha256:8af5a8917b8af42295e86b64903156b4f110a30dca5f3b5aedea123fbd638bff"},
+ {file = "charset_normalizer-3.3.1-cp312-cp312-macosx_10_9_universal2.whl", hash = "sha256:7ae8e5142dcc7a49168f4055255dbcced01dc1714a90a21f87448dc8d90617d1"},
+ {file = "charset_normalizer-3.3.1-cp312-cp312-macosx_10_9_x86_64.whl", hash = "sha256:5b70bab78accbc672f50e878a5b73ca692f45f5b5e25c8066d748c09405e6a55"},
+ {file = "charset_normalizer-3.3.1-cp312-cp312-macosx_11_0_arm64.whl", hash = "sha256:5ceca5876032362ae73b83347be8b5dbd2d1faf3358deb38c9c88776779b2e2f"},
+ {file = "charset_normalizer-3.3.1-cp312-cp312-manylinux_2_17_aarch64.manylinux2014_aarch64.whl", hash = "sha256:34d95638ff3613849f473afc33f65c401a89f3b9528d0d213c7037c398a51296"},
+ {file = "charset_normalizer-3.3.1-cp312-cp312-manylinux_2_17_ppc64le.manylinux2014_ppc64le.whl", hash = "sha256:9edbe6a5bf8b56a4a84533ba2b2f489d0046e755c29616ef8830f9e7d9cf5728"},
+ {file = "charset_normalizer-3.3.1-cp312-cp312-manylinux_2_17_s390x.manylinux2014_s390x.whl", hash = "sha256:f6a02a3c7950cafaadcd46a226ad9e12fc9744652cc69f9e5534f98b47f3bbcf"},
+ {file = "charset_normalizer-3.3.1-cp312-cp312-manylinux_2_17_x86_64.manylinux2014_x86_64.whl", hash = "sha256:10b8dd31e10f32410751b3430996f9807fc4d1587ca69772e2aa940a82ab571a"},
+ {file = "charset_normalizer-3.3.1-cp312-cp312-manylinux_2_5_i686.manylinux1_i686.manylinux_2_17_i686.manylinux2014_i686.whl", hash = "sha256:edc0202099ea1d82844316604e17d2b175044f9bcb6b398aab781eba957224bd"},
+ {file = "charset_normalizer-3.3.1-cp312-cp312-musllinux_1_1_aarch64.whl", hash = "sha256:b891a2f68e09c5ef989007fac11476ed33c5c9994449a4e2c3386529d703dc8b"},
+ {file = "charset_normalizer-3.3.1-cp312-cp312-musllinux_1_1_i686.whl", hash = "sha256:71ef3b9be10070360f289aea4838c784f8b851be3ba58cf796262b57775c2f14"},
+ {file = "charset_normalizer-3.3.1-cp312-cp312-musllinux_1_1_ppc64le.whl", hash = "sha256:55602981b2dbf8184c098bc10287e8c245e351cd4fdcad050bd7199d5a8bf514"},
+ {file = "charset_normalizer-3.3.1-cp312-cp312-musllinux_1_1_s390x.whl", hash = "sha256:46fb9970aa5eeca547d7aa0de5d4b124a288b42eaefac677bde805013c95725c"},
+ {file = "charset_normalizer-3.3.1-cp312-cp312-musllinux_1_1_x86_64.whl", hash = "sha256:520b7a142d2524f999447b3a0cf95115df81c4f33003c51a6ab637cbda9d0bf4"},
+ {file = "charset_normalizer-3.3.1-cp312-cp312-win32.whl", hash = "sha256:8ec8ef42c6cd5856a7613dcd1eaf21e5573b2185263d87d27c8edcae33b62a61"},
+ {file = "charset_normalizer-3.3.1-cp312-cp312-win_amd64.whl", hash = "sha256:baec8148d6b8bd5cee1ae138ba658c71f5b03e0d69d5907703e3e1df96db5e41"},
+ {file = "charset_normalizer-3.3.1-cp37-cp37m-macosx_10_9_x86_64.whl", hash = "sha256:63a6f59e2d01310f754c270e4a257426fe5a591dc487f1983b3bbe793cf6bac6"},
+ {file = "charset_normalizer-3.3.1-cp37-cp37m-manylinux_2_17_aarch64.manylinux2014_aarch64.whl", hash = "sha256:1d6bfc32a68bc0933819cfdfe45f9abc3cae3877e1d90aac7259d57e6e0f85b1"},
+ {file = "charset_normalizer-3.3.1-cp37-cp37m-manylinux_2_17_ppc64le.manylinux2014_ppc64le.whl", hash = "sha256:4f3100d86dcd03c03f7e9c3fdb23d92e32abbca07e7c13ebd7ddfbcb06f5991f"},
+ {file = "charset_normalizer-3.3.1-cp37-cp37m-manylinux_2_17_s390x.manylinux2014_s390x.whl", hash = "sha256:39b70a6f88eebe239fa775190796d55a33cfb6d36b9ffdd37843f7c4c1b5dc67"},
+ {file = "charset_normalizer-3.3.1-cp37-cp37m-manylinux_2_17_x86_64.manylinux2014_x86_64.whl", hash = "sha256:4e12f8ee80aa35e746230a2af83e81bd6b52daa92a8afaef4fea4a2ce9b9f4fa"},
+ {file = "charset_normalizer-3.3.1-cp37-cp37m-manylinux_2_5_i686.manylinux1_i686.manylinux_2_17_i686.manylinux2014_i686.whl", hash = "sha256:7b6cefa579e1237ce198619b76eaa148b71894fb0d6bcf9024460f9bf30fd228"},
+ {file = "charset_normalizer-3.3.1-cp37-cp37m-musllinux_1_1_aarch64.whl", hash = "sha256:61f1e3fb621f5420523abb71f5771a204b33c21d31e7d9d86881b2cffe92c47c"},
+ {file = "charset_normalizer-3.3.1-cp37-cp37m-musllinux_1_1_i686.whl", hash = "sha256:4f6e2a839f83a6a76854d12dbebde50e4b1afa63e27761549d006fa53e9aa80e"},
+ {file = "charset_normalizer-3.3.1-cp37-cp37m-musllinux_1_1_ppc64le.whl", hash = "sha256:1ec937546cad86d0dce5396748bf392bb7b62a9eeb8c66efac60e947697f0e58"},
+ {file = "charset_normalizer-3.3.1-cp37-cp37m-musllinux_1_1_s390x.whl", hash = "sha256:82ca51ff0fc5b641a2d4e1cc8c5ff108699b7a56d7f3ad6f6da9dbb6f0145b48"},
+ {file = "charset_normalizer-3.3.1-cp37-cp37m-musllinux_1_1_x86_64.whl", hash = "sha256:633968254f8d421e70f91c6ebe71ed0ab140220469cf87a9857e21c16687c034"},
+ {file = "charset_normalizer-3.3.1-cp37-cp37m-win32.whl", hash = "sha256:c0c72d34e7de5604df0fde3644cc079feee5e55464967d10b24b1de268deceb9"},
+ {file = "charset_normalizer-3.3.1-cp37-cp37m-win_amd64.whl", hash = "sha256:63accd11149c0f9a99e3bc095bbdb5a464862d77a7e309ad5938fbc8721235ae"},
+ {file = "charset_normalizer-3.3.1-cp38-cp38-macosx_10_9_universal2.whl", hash = "sha256:5a3580a4fdc4ac05f9e53c57f965e3594b2f99796231380adb2baaab96e22761"},
+ {file = "charset_normalizer-3.3.1-cp38-cp38-macosx_10_9_x86_64.whl", hash = "sha256:2465aa50c9299d615d757c1c888bc6fef384b7c4aec81c05a0172b4400f98557"},
+ {file = "charset_normalizer-3.3.1-cp38-cp38-macosx_11_0_arm64.whl", hash = "sha256:cb7cd68814308aade9d0c93c5bd2ade9f9441666f8ba5aa9c2d4b389cb5e2a45"},
+ {file = "charset_normalizer-3.3.1-cp38-cp38-manylinux_2_17_aarch64.manylinux2014_aarch64.whl", hash = "sha256:91e43805ccafa0a91831f9cd5443aa34528c0c3f2cc48c4cb3d9a7721053874b"},
+ {file = "charset_normalizer-3.3.1-cp38-cp38-manylinux_2_17_ppc64le.manylinux2014_ppc64le.whl", hash = "sha256:854cc74367180beb327ab9d00f964f6d91da06450b0855cbbb09187bcdb02de5"},
+ {file = "charset_normalizer-3.3.1-cp38-cp38-manylinux_2_17_s390x.manylinux2014_s390x.whl", hash = "sha256:c15070ebf11b8b7fd1bfff7217e9324963c82dbdf6182ff7050519e350e7ad9f"},
+ {file = "charset_normalizer-3.3.1-cp38-cp38-manylinux_2_17_x86_64.manylinux2014_x86_64.whl", hash = "sha256:2c4c99f98fc3a1835af8179dcc9013f93594d0670e2fa80c83aa36346ee763d2"},
+ {file = "charset_normalizer-3.3.1-cp38-cp38-manylinux_2_5_i686.manylinux1_i686.manylinux_2_17_i686.manylinux2014_i686.whl", hash = "sha256:3fb765362688821404ad6cf86772fc54993ec11577cd5a92ac44b4c2ba52155b"},
+ {file = "charset_normalizer-3.3.1-cp38-cp38-musllinux_1_1_aarch64.whl", hash = "sha256:dced27917823df984fe0c80a5c4ad75cf58df0fbfae890bc08004cd3888922a2"},
+ {file = "charset_normalizer-3.3.1-cp38-cp38-musllinux_1_1_i686.whl", hash = "sha256:a66bcdf19c1a523e41b8e9d53d0cedbfbac2e93c649a2e9502cb26c014d0980c"},
+ {file = "charset_normalizer-3.3.1-cp38-cp38-musllinux_1_1_ppc64le.whl", hash = "sha256:ecd26be9f112c4f96718290c10f4caea6cc798459a3a76636b817a0ed7874e42"},
+ {file = "charset_normalizer-3.3.1-cp38-cp38-musllinux_1_1_s390x.whl", hash = "sha256:3f70fd716855cd3b855316b226a1ac8bdb3caf4f7ea96edcccc6f484217c9597"},
+ {file = "charset_normalizer-3.3.1-cp38-cp38-musllinux_1_1_x86_64.whl", hash = "sha256:17a866d61259c7de1bdadef418a37755050ddb4b922df8b356503234fff7932c"},
+ {file = "charset_normalizer-3.3.1-cp38-cp38-win32.whl", hash = "sha256:548eefad783ed787b38cb6f9a574bd8664468cc76d1538215d510a3cd41406cb"},
+ {file = "charset_normalizer-3.3.1-cp38-cp38-win_amd64.whl", hash = "sha256:45f053a0ece92c734d874861ffe6e3cc92150e32136dd59ab1fb070575189c97"},
+ {file = "charset_normalizer-3.3.1-cp39-cp39-macosx_10_9_universal2.whl", hash = "sha256:bc791ec3fd0c4309a753f95bb6c749ef0d8ea3aea91f07ee1cf06b7b02118f2f"},
+ {file = "charset_normalizer-3.3.1-cp39-cp39-macosx_10_9_x86_64.whl", hash = "sha256:0c8c61fb505c7dad1d251c284e712d4e0372cef3b067f7ddf82a7fa82e1e9a93"},
+ {file = "charset_normalizer-3.3.1-cp39-cp39-macosx_11_0_arm64.whl", hash = "sha256:2c092be3885a1b7899cd85ce24acedc1034199d6fca1483fa2c3a35c86e43041"},
+ {file = "charset_normalizer-3.3.1-cp39-cp39-manylinux_2_17_aarch64.manylinux2014_aarch64.whl", hash = "sha256:c2000c54c395d9e5e44c99dc7c20a64dc371f777faf8bae4919ad3e99ce5253e"},
+ {file = "charset_normalizer-3.3.1-cp39-cp39-manylinux_2_17_ppc64le.manylinux2014_ppc64le.whl", hash = "sha256:4cb50a0335382aac15c31b61d8531bc9bb657cfd848b1d7158009472189f3d62"},
+ {file = "charset_normalizer-3.3.1-cp39-cp39-manylinux_2_17_s390x.manylinux2014_s390x.whl", hash = "sha256:c30187840d36d0ba2893bc3271a36a517a717f9fd383a98e2697ee890a37c273"},
+ {file = "charset_normalizer-3.3.1-cp39-cp39-manylinux_2_17_x86_64.manylinux2014_x86_64.whl", hash = "sha256:fe81b35c33772e56f4b6cf62cf4aedc1762ef7162a31e6ac7fe5e40d0149eb67"},
+ {file = "charset_normalizer-3.3.1-cp39-cp39-manylinux_2_5_i686.manylinux1_i686.manylinux_2_17_i686.manylinux2014_i686.whl", hash = "sha256:d0bf89afcbcf4d1bb2652f6580e5e55a840fdf87384f6063c4a4f0c95e378656"},
+ {file = "charset_normalizer-3.3.1-cp39-cp39-musllinux_1_1_aarch64.whl", hash = "sha256:06cf46bdff72f58645434d467bf5228080801298fbba19fe268a01b4534467f5"},
+ {file = "charset_normalizer-3.3.1-cp39-cp39-musllinux_1_1_i686.whl", hash = "sha256:3c66df3f41abee950d6638adc7eac4730a306b022570f71dd0bd6ba53503ab57"},
+ {file = "charset_normalizer-3.3.1-cp39-cp39-musllinux_1_1_ppc64le.whl", hash = "sha256:cd805513198304026bd379d1d516afbf6c3c13f4382134a2c526b8b854da1c2e"},
+ {file = "charset_normalizer-3.3.1-cp39-cp39-musllinux_1_1_s390x.whl", hash = "sha256:9505dc359edb6a330efcd2be825fdb73ee3e628d9010597aa1aee5aa63442e97"},
+ {file = "charset_normalizer-3.3.1-cp39-cp39-musllinux_1_1_x86_64.whl", hash = "sha256:31445f38053476a0c4e6d12b047b08ced81e2c7c712e5a1ad97bc913256f91b2"},
+ {file = "charset_normalizer-3.3.1-cp39-cp39-win32.whl", hash = "sha256:bd28b31730f0e982ace8663d108e01199098432a30a4c410d06fe08fdb9e93f4"},
+ {file = "charset_normalizer-3.3.1-cp39-cp39-win_amd64.whl", hash = "sha256:555fe186da0068d3354cdf4bbcbc609b0ecae4d04c921cc13e209eece7720727"},
+ {file = "charset_normalizer-3.3.1-py3-none-any.whl", hash = "sha256:800561453acdecedaac137bf09cd719c7a440b6800ec182f077bb8e7025fb708"},
]
[[package]]
@@ -311,13 +311,13 @@ toml = ["tomli"]
[[package]]
name = "dunamai"
-version = "1.16.1"
+version = "1.18.1"
description = "Dynamic version generation"
optional = false
python-versions = ">=3.5,<4.0"
files = [
- {file = "dunamai-1.16.1-py3-none-any.whl", hash = "sha256:b9f169183147f6f1d3a5b3d913ffdd67247d90948006e205cbc499fe98d45554"},
- {file = "dunamai-1.16.1.tar.gz", hash = "sha256:4f3bc2c5b0f9d83fa9c90b943100273bb087167c90a0519ac66e9e2e0d2a8210"},
+ {file = "dunamai-1.18.1-py3-none-any.whl", hash = "sha256:ee7b042f7a687fa04fc383258eb93bd819c7bd8aec62e0974f3c69747e5958f2"},
+ {file = "dunamai-1.18.1.tar.gz", hash = "sha256:5e9a91e43d16bb56fa8fcddcf92fa31b2e1126e060c3dcc8d094d9b508061f9d"},
]
[package.dependencies]
@@ -340,13 +340,13 @@ test = ["pytest (>=6)"]
[[package]]
name = "gitdb"
-version = "4.0.10"
+version = "4.0.11"
description = "Git Object Database"
optional = false
python-versions = ">=3.7"
files = [
- {file = "gitdb-4.0.10-py3-none-any.whl", hash = "sha256:c286cf298426064079ed96a9e4a9d39e7f3e9bf15ba60701e95f5492f28415c7"},
- {file = "gitdb-4.0.10.tar.gz", hash = "sha256:6eb990b69df4e15bad899ea868dc46572c3f75339735663b81de79b06f17eb9a"},
+ {file = "gitdb-4.0.11-py3-none-any.whl", hash = "sha256:81a3407ddd2ee8df444cbacea00e2d038e40150acfa3001696fe0dcf1d3adfa4"},
+ {file = "gitdb-4.0.11.tar.gz", hash = "sha256:bf5421126136d6d0af55bc1e7c1af1c397a34f5b7bd79e776cd3e89785c2b04b"},
]
[package.dependencies]
@@ -354,13 +354,13 @@ smmap = ">=3.0.1,<6"
[[package]]
name = "gitpython"
-version = "3.1.37"
+version = "3.1.40"
description = "GitPython is a Python library used to interact with Git repositories"
optional = false
python-versions = ">=3.7"
files = [
- {file = "GitPython-3.1.37-py3-none-any.whl", hash = "sha256:5f4c4187de49616d710a77e98ddf17b4782060a1788df441846bddefbb89ab33"},
- {file = "GitPython-3.1.37.tar.gz", hash = "sha256:f9b9ddc0761c125d5780eab2d64be4873fc6817c2899cbcb34b02344bdc7bc54"},
+ {file = "GitPython-3.1.40-py3-none-any.whl", hash = "sha256:cf14627d5a8049ffbf49915732e5eddbe8134c3bdb9d476e6182b676fc573f8a"},
+ {file = "GitPython-3.1.40.tar.gz", hash = "sha256:22b126e9ffb671fdd0c129796343a02bf67bf2994b35449ffc9321aa755e18a4"},
]
[package.dependencies]
@@ -368,7 +368,7 @@ gitdb = ">=4.0.1,<5"
typing-extensions = {version = ">=3.7.4.3", markers = "python_version < \"3.8\""}
[package.extras]
-test = ["black", "coverage[toml]", "ddt (>=1.1.1,!=1.4.3)", "mypy", "pre-commit", "pytest", "pytest-cov", "pytest-sugar"]
+test = ["black", "coverage[toml]", "ddt (>=1.1.1,!=1.4.3)", "mock", "mypy", "pre-commit", "pytest", "pytest-cov", "pytest-instafail", "pytest-subtests", "pytest-sugar"]
[[package]]
name = "idna"
@@ -578,13 +578,13 @@ hook-testing = ["execnet (>=1.5.0)", "psutil", "pytest (>=2.7.3)"]
[[package]]
name = "pyinstaller-hooks-contrib"
-version = "2023.9"
+version = "2023.10"
description = "Community maintained hooks for PyInstaller"
optional = false
python-versions = ">=3.7"
files = [
- {file = "pyinstaller-hooks-contrib-2023.9.tar.gz", hash = "sha256:76084b5988e3957a9df169d2a935d65500136967e710ddebf57263f1a909cd80"},
- {file = "pyinstaller_hooks_contrib-2023.9-py2.py3-none-any.whl", hash = "sha256:f34f4c6807210025c8073ebe665f422a3aa2ac5f4c7ebf4c2a26cc77bebf63b5"},
+ {file = "pyinstaller-hooks-contrib-2023.10.tar.gz", hash = "sha256:4b4a998036abb713774cb26534ca06b7e6e09e4c628196017a10deb11a48747f"},
+ {file = "pyinstaller_hooks_contrib-2023.10-py2.py3-none-any.whl", hash = "sha256:6dc1786a8f452941245d5bb85893e2a33632ebdcbc4c23eea41f2ee08281b0c0"},
]
[[package]]
@@ -664,7 +664,6 @@ files = [
{file = "PyYAML-6.0.1-cp310-cp310-manylinux_2_17_aarch64.manylinux2014_aarch64.whl", hash = "sha256:69b023b2b4daa7548bcfbd4aa3da05b3a74b772db9e23b982788168117739938"},
{file = "PyYAML-6.0.1-cp310-cp310-manylinux_2_17_s390x.manylinux2014_s390x.whl", hash = "sha256:81e0b275a9ecc9c0c0c07b4b90ba548307583c125f54d5b6946cfee6360c733d"},
{file = "PyYAML-6.0.1-cp310-cp310-manylinux_2_17_x86_64.manylinux2014_x86_64.whl", hash = "sha256:ba336e390cd8e4d1739f42dfe9bb83a3cc2e80f567d8805e11b46f4a943f5515"},
- {file = "PyYAML-6.0.1-cp310-cp310-musllinux_1_1_x86_64.whl", hash = "sha256:326c013efe8048858a6d312ddd31d56e468118ad4cdeda36c719bf5bb6192290"},
{file = "PyYAML-6.0.1-cp310-cp310-win32.whl", hash = "sha256:bd4af7373a854424dabd882decdc5579653d7868b8fb26dc7d0e99f823aa5924"},
{file = "PyYAML-6.0.1-cp310-cp310-win_amd64.whl", hash = "sha256:fd1592b3fdf65fff2ad0004b5e363300ef59ced41c2e6b3a99d4089fa8c5435d"},
{file = "PyYAML-6.0.1-cp311-cp311-macosx_10_9_x86_64.whl", hash = "sha256:6965a7bc3cf88e5a1c3bd2e0b5c22f8d677dc88a455344035f03399034eb3007"},
@@ -672,15 +671,8 @@ files = [
{file = "PyYAML-6.0.1-cp311-cp311-manylinux_2_17_aarch64.manylinux2014_aarch64.whl", hash = "sha256:42f8152b8dbc4fe7d96729ec2b99c7097d656dc1213a3229ca5383f973a5ed6d"},
{file = "PyYAML-6.0.1-cp311-cp311-manylinux_2_17_s390x.manylinux2014_s390x.whl", hash = "sha256:062582fca9fabdd2c8b54a3ef1c978d786e0f6b3a1510e0ac93ef59e0ddae2bc"},
{file = "PyYAML-6.0.1-cp311-cp311-manylinux_2_17_x86_64.manylinux2014_x86_64.whl", hash = "sha256:d2b04aac4d386b172d5b9692e2d2da8de7bfb6c387fa4f801fbf6fb2e6ba4673"},
- {file = "PyYAML-6.0.1-cp311-cp311-musllinux_1_1_x86_64.whl", hash = "sha256:e7d73685e87afe9f3b36c799222440d6cf362062f78be1013661b00c5c6f678b"},
{file = "PyYAML-6.0.1-cp311-cp311-win32.whl", hash = "sha256:1635fd110e8d85d55237ab316b5b011de701ea0f29d07611174a1b42f1444741"},
{file = "PyYAML-6.0.1-cp311-cp311-win_amd64.whl", hash = "sha256:bf07ee2fef7014951eeb99f56f39c9bb4af143d8aa3c21b1677805985307da34"},
- {file = "PyYAML-6.0.1-cp312-cp312-macosx_10_9_x86_64.whl", hash = "sha256:855fb52b0dc35af121542a76b9a84f8d1cd886ea97c84703eaa6d88e37a2ad28"},
- {file = "PyYAML-6.0.1-cp312-cp312-macosx_11_0_arm64.whl", hash = "sha256:40df9b996c2b73138957fe23a16a4f0ba614f4c0efce1e9406a184b6d07fa3a9"},
- {file = "PyYAML-6.0.1-cp312-cp312-manylinux_2_17_x86_64.manylinux2014_x86_64.whl", hash = "sha256:6c22bec3fbe2524cde73d7ada88f6566758a8f7227bfbf93a408a9d86bcc12a0"},
- {file = "PyYAML-6.0.1-cp312-cp312-musllinux_1_1_x86_64.whl", hash = "sha256:8d4e9c88387b0f5c7d5f281e55304de64cf7f9c0021a3525bd3b1c542da3b0e4"},
- {file = "PyYAML-6.0.1-cp312-cp312-win32.whl", hash = "sha256:d483d2cdf104e7c9fa60c544d92981f12ad66a457afae824d146093b8c294c54"},
- {file = "PyYAML-6.0.1-cp312-cp312-win_amd64.whl", hash = "sha256:0d3304d8c0adc42be59c5f8a4d9e3d7379e6955ad754aa9d6ab7a398b59dd1df"},
{file = "PyYAML-6.0.1-cp36-cp36m-macosx_10_9_x86_64.whl", hash = "sha256:50550eb667afee136e9a77d6dc71ae76a44df8b3e51e41b77f6de2932bfe0f47"},
{file = "PyYAML-6.0.1-cp36-cp36m-manylinux_2_17_aarch64.manylinux2014_aarch64.whl", hash = "sha256:1fe35611261b29bd1de0070f0b2f47cb6ff71fa6595c077e42bd0c419fa27b98"},
{file = "PyYAML-6.0.1-cp36-cp36m-manylinux_2_17_s390x.manylinux2014_s390x.whl", hash = "sha256:704219a11b772aea0d8ecd7058d0082713c3562b4e271b849ad7dc4a5c90c13c"},
@@ -697,7 +689,6 @@ files = [
{file = "PyYAML-6.0.1-cp38-cp38-manylinux_2_17_aarch64.manylinux2014_aarch64.whl", hash = "sha256:a0cd17c15d3bb3fa06978b4e8958dcdc6e0174ccea823003a106c7d4d7899ac5"},
{file = "PyYAML-6.0.1-cp38-cp38-manylinux_2_17_s390x.manylinux2014_s390x.whl", hash = "sha256:28c119d996beec18c05208a8bd78cbe4007878c6dd15091efb73a30e90539696"},
{file = "PyYAML-6.0.1-cp38-cp38-manylinux_2_17_x86_64.manylinux2014_x86_64.whl", hash = "sha256:7e07cbde391ba96ab58e532ff4803f79c4129397514e1413a7dc761ccd755735"},
- {file = "PyYAML-6.0.1-cp38-cp38-musllinux_1_1_x86_64.whl", hash = "sha256:49a183be227561de579b4a36efbb21b3eab9651dd81b1858589f796549873dd6"},
{file = "PyYAML-6.0.1-cp38-cp38-win32.whl", hash = "sha256:184c5108a2aca3c5b3d3bf9395d50893a7ab82a38004c8f61c258d4428e80206"},
{file = "PyYAML-6.0.1-cp38-cp38-win_amd64.whl", hash = "sha256:1e2722cc9fbb45d9b87631ac70924c11d3a401b2d7f410cc0e3bbf249f2dca62"},
{file = "PyYAML-6.0.1-cp39-cp39-macosx_10_9_x86_64.whl", hash = "sha256:9eb6caa9a297fc2c2fb8862bc5370d0303ddba53ba97e71f08023b6cd73d16a8"},
@@ -705,7 +696,6 @@ files = [
{file = "PyYAML-6.0.1-cp39-cp39-manylinux_2_17_aarch64.manylinux2014_aarch64.whl", hash = "sha256:5773183b6446b2c99bb77e77595dd486303b4faab2b086e7b17bc6bef28865f6"},
{file = "PyYAML-6.0.1-cp39-cp39-manylinux_2_17_s390x.manylinux2014_s390x.whl", hash = "sha256:b786eecbdf8499b9ca1d697215862083bd6d2a99965554781d0d8d1ad31e13a0"},
{file = "PyYAML-6.0.1-cp39-cp39-manylinux_2_17_x86_64.manylinux2014_x86_64.whl", hash = "sha256:bc1bf2925a1ecd43da378f4db9e4f799775d6367bdb94671027b73b393a7c42c"},
- {file = "PyYAML-6.0.1-cp39-cp39-musllinux_1_1_x86_64.whl", hash = "sha256:04ac92ad1925b2cff1db0cfebffb6ffc43457495c9b3c39d3fcae417d7125dc5"},
{file = "PyYAML-6.0.1-cp39-cp39-win32.whl", hash = "sha256:faca3bdcf85b2fc05d06ff3fbc1f83e1391b3e724afa3feba7d13eeab355484c"},
{file = "PyYAML-6.0.1-cp39-cp39-win_amd64.whl", hash = "sha256:510c9deebc5c0225e8c96813043e62b680ba2f9c50a08d3724c7f28a747d1486"},
{file = "PyYAML-6.0.1.tar.gz", hash = "sha256:bfdf460b1736c775f2ba9f6a92bca30bc2095067b8a9d77876d1fad6cc3b4a43"},
@@ -945,4 +935,4 @@ testing = ["big-O", "flake8 (<5)", "jaraco.functools", "jaraco.itertools", "more
[metadata]
lock-version = "2.0"
python-versions = ">=3.7,<3.13"
-content-hash = "5b143fd05c0d713bd821c03e16cb4c087ddd4f48c17f7dabf479fb6e67ab9cbb"
+content-hash = "016a02b0698698558aa590693fdda4a0ce558e247da4ed1eaf7b9315881575f6"
diff --git a/pyproject.toml b/pyproject.toml
index 5a6ac164..c51a57c2 100644
--- a/pyproject.toml
+++ b/pyproject.toml
@@ -49,7 +49,7 @@ responses = ">=0.23.1,<0.24.0"
[tool.poetry.group.executable.dependencies]
pyinstaller = ">=5.13.0,<5.14.0"
-dunamai = ">=1.16.1,<1.17.0"
+dunamai = ">=1.18.0,<1.19.0"
[tool.poetry.group.dev.dependencies]
black = ">=23.3.0,<23.4.0"
@@ -137,5 +137,5 @@ inline-quotes = "single"
"cycode/*.py" = ["BLE001"]
[build-system]
-requires = ["poetry-core>=1.0.0", "poetry-dynamic-versioning>=0.25.0"]
+requires = ["poetry-core>=1.0.0", "poetry-dynamic-versioning>=1.0.0,<2.0.0"]
build-backend = "poetry_dynamic_versioning.backend"
From ebbca2c880420dc60750826dea28799df499a9f9 Mon Sep 17 00:00:00 2001
From: Ilya Siamionau
Date: Mon, 30 Oct 2023 14:50:57 +0100
Subject: [PATCH 044/257] CM-22319 - Run secrets scanning asynchronously using
polling mechanism (#136)
---
cycode/cli/code_scanner.py | 12 +-
cycode/cyclient/scan_client.py | 45 +++--
cycode/cyclient/scan_config_base.py | 16 ++
tests/cli/test_main.py | 11 +-
tests/conftest.py | 2 +
tests/cyclient/mocked_responses/__init__.py | 0
.../mocked_responses/data/detections.json | 83 +++++++++
.../cyclient/mocked_responses/scan_client.py | 158 ++++++++++++++++++
tests/cyclient/test_scan_client.py | 67 +-------
9 files changed, 311 insertions(+), 83 deletions(-)
create mode 100644 tests/cyclient/mocked_responses/__init__.py
create mode 100644 tests/cyclient/mocked_responses/data/detections.json
create mode 100644 tests/cyclient/mocked_responses/scan_client.py
diff --git a/cycode/cli/code_scanner.py b/cycode/cli/code_scanner.py
index 1801d63c..5920fc80 100644
--- a/cycode/cli/code_scanner.py
+++ b/cycode/cli/code_scanner.py
@@ -546,13 +546,13 @@ def perform_scan(
is_commit_range: bool,
scan_parameters: dict,
) -> ZippedFileScanResult:
- if scan_type in (consts.SCA_SCAN_TYPE, consts.SAST_SCAN_TYPE):
- return perform_scan_async(cycode_client, zipped_documents, scan_type, scan_parameters)
-
if is_commit_range:
return cycode_client.commit_range_zipped_file_scan(scan_type, zipped_documents, scan_id)
- return cycode_client.zipped_file_scan(scan_type, zipped_documents, scan_id, scan_parameters, is_git_diff)
+ if scan_type == consts.INFRA_CONFIGURATION_SCAN_TYPE:
+ return cycode_client.zipped_file_scan(scan_type, zipped_documents, scan_id, scan_parameters, is_git_diff)
+
+ return perform_scan_async(cycode_client, zipped_documents, scan_type, scan_parameters)
def perform_scan_async(
@@ -1025,6 +1025,10 @@ def _map_detections_per_file(detections: List[dict]) -> List[DetectionsPerFile]:
def _get_file_name_from_detection(detection: dict) -> str:
if detection['category'] == 'SAST':
return detection['detection_details']['file_path']
+ if detection['category'] == 'SecretDetection':
+ file_path = detection['detection_details']['file_path']
+ file_name = detection['detection_details']['file_name']
+ return os.path.join(file_path, file_name)
return detection['detection_details']['file_name']
diff --git a/cycode/cyclient/scan_client.py b/cycode/cyclient/scan_client.py
index 5830e9dc..50ee0e79 100644
--- a/cycode/cyclient/scan_client.py
+++ b/cycode/cyclient/scan_client.py
@@ -31,14 +31,16 @@ def content_scan(self, scan_type: str, file_name: str, content: str, is_git_diff
)
return self.parse_scan_response(response)
+ def get_zipped_file_scan_url_path(self, scan_type: str) -> str:
+ return f'{self.scan_config.get_service_name(scan_type)}/{self.SCAN_CONTROLLER_PATH}/zipped-file'
+
def zipped_file_scan(
self, scan_type: str, zip_file: InMemoryZip, scan_id: str, scan_parameters: dict, is_git_diff: bool = False
) -> models.ZippedFileScanResult:
- url_path = f'{self.scan_config.get_service_name(scan_type)}/{self.SCAN_CONTROLLER_PATH}/zipped-file'
files = {'file': ('multiple_files_scan.zip', zip_file.read())}
response = self.scan_cycode_client.post(
- url_path=url_path,
+ url_path=self.get_zipped_file_scan_url_path(scan_type),
data={'scan_id': scan_id, 'is_git_diff': is_git_diff, 'scan_parameters': json.dumps(scan_parameters)},
files=files,
hide_response_content_log=self._hide_response_log,
@@ -46,13 +48,19 @@ def zipped_file_scan(
return self.parse_zipped_file_scan_response(response)
+ def get_zipped_file_scan_async_url_path(self, scan_type: str) -> str:
+ async_scan_type = self.scan_config.get_async_scan_type(scan_type)
+ async_entity_type = self.scan_config.get_async_entity_type(scan_type)
+
+ url_prefix = self.scan_config.get_scans_prefix()
+ return f'{url_prefix}/{self.SCAN_CONTROLLER_PATH}/{async_scan_type}/{async_entity_type}'
+
def zipped_file_scan_async(
self, zip_file: InMemoryZip, scan_type: str, scan_parameters: dict, is_git_diff: bool = False
) -> models.ScanInitializationResponse:
- url_path = f'{self.scan_config.get_scans_prefix()}/{self.SCAN_CONTROLLER_PATH}/{scan_type}/repository'
files = {'file': ('multiple_files_scan.zip', zip_file.read())}
response = self.scan_cycode_client.post(
- url_path=url_path,
+ url_path=self.get_zipped_file_scan_async_url_path(scan_type),
data={'is_git_diff': is_git_diff, 'scan_parameters': json.dumps(scan_parameters)},
files=files,
)
@@ -80,13 +88,17 @@ def multiple_zipped_file_scan_async(
)
return models.ScanInitializationResponseSchema().load(response.json())
+ def get_scan_details_path(self, scan_id: str) -> str:
+ return f'{self.scan_config.get_scans_prefix()}/{self.SCAN_CONTROLLER_PATH}/{scan_id}'
+
def get_scan_details(self, scan_id: str) -> models.ScanDetailsResponse:
- url_path = f'{self.scan_config.get_scans_prefix()}/{self.SCAN_CONTROLLER_PATH}/{scan_id}'
- response = self.scan_cycode_client.get(url_path=url_path)
+ response = self.scan_cycode_client.get(url_path=self.get_scan_details_path(scan_id))
return models.ScanDetailsResponseSchema().load(response.json())
+ def get_scan_detections_path(self) -> str:
+ return f'{self.scan_config.get_detections_prefix()}/{self.DETECTIONS_SERVICE_CONTROLLER_PATH}'
+
def get_scan_detections(self, scan_id: str) -> List[dict]:
- url_path = f'{self.scan_config.get_detections_prefix()}/{self.DETECTIONS_SERVICE_CONTROLLER_PATH}'
params = {'scan_id': scan_id}
page_size = 200
@@ -100,7 +112,9 @@ def get_scan_detections(self, scan_id: str) -> List[dict]:
params['page_number'] = page_number
response = self.scan_cycode_client.get(
- url_path=url_path, params=params, hide_response_content_log=self._hide_response_log
+ url_path=self.get_scan_detections_path(),
+ params=params,
+ hide_response_content_log=self._hide_response_log,
).json()
detections.extend(response)
@@ -109,9 +123,13 @@ def get_scan_detections(self, scan_id: str) -> List[dict]:
return detections
+ def get_get_scan_detections_count_path(self) -> str:
+ return f'{self.scan_config.get_detections_prefix()}/{self.DETECTIONS_SERVICE_CONTROLLER_PATH}/count'
+
def get_scan_detections_count(self, scan_id: str) -> int:
- url_path = f'{self.scan_config.get_detections_prefix()}/{self.DETECTIONS_SERVICE_CONTROLLER_PATH}/count'
- response = self.scan_cycode_client.get(url_path=url_path, params={'scan_id': scan_id})
+ response = self.scan_cycode_client.get(
+ url_path=self.get_get_scan_detections_count_path(), params={'scan_id': scan_id}
+ )
return response.json().get('count', 0)
def commit_range_zipped_file_scan(
@@ -126,9 +144,11 @@ def commit_range_zipped_file_scan(
)
return self.parse_zipped_file_scan_response(response)
+ def get_report_scan_status_path(self, scan_type: str, scan_id: str) -> str:
+ return f'{self.scan_config.get_service_name(scan_type)}/{self.SCAN_CONTROLLER_PATH}/{scan_id}/status'
+
def report_scan_status(self, scan_type: str, scan_id: str, scan_status: dict) -> None:
- url_path = f'{self.scan_config.get_service_name(scan_type)}/{self.SCAN_CONTROLLER_PATH}/{scan_id}/status'
- self.scan_cycode_client.post(url_path=url_path, body=scan_status)
+ self.scan_cycode_client.post(url_path=self.get_report_scan_status_path(scan_type, scan_id), body=scan_status)
@staticmethod
def parse_scan_response(response: Response) -> models.ScanResult:
@@ -140,6 +160,7 @@ def parse_zipped_file_scan_response(response: Response) -> models.ZippedFileScan
@staticmethod
def get_service_name(scan_type: str) -> Optional[str]:
+ # TODO(MarshalX): get_service_name should be removed from ScanClient? Because it exists in ScanConfig
if scan_type == 'secret':
return 'secret'
if scan_type == 'iac':
diff --git a/cycode/cyclient/scan_config_base.py b/cycode/cyclient/scan_config_base.py
index 976008bb..0fffa1a2 100644
--- a/cycode/cyclient/scan_config_base.py
+++ b/cycode/cyclient/scan_config_base.py
@@ -6,6 +6,22 @@ class ScanConfigBase(ABC):
def get_service_name(self, scan_type: str) -> str:
...
+ @staticmethod
+ def get_async_scan_type(scan_type: str) -> str:
+ if scan_type == 'secret':
+ return 'Secrets'
+ if scan_type == 'iac':
+ return 'InfraConfiguration'
+
+ return scan_type.upper()
+
+ @staticmethod
+ def get_async_entity_type(scan_type: str) -> str:
+ if scan_type == 'secret':
+ return 'zippedfile'
+
+ return 'repository'
+
@abstractmethod
def get_scans_prefix(self) -> str:
...
diff --git a/tests/cli/test_main.py b/tests/cli/test_main.py
index 8c3c6246..aa196c0e 100644
--- a/tests/cli/test_main.py
+++ b/tests/cli/test_main.py
@@ -1,13 +1,14 @@
import json
from typing import TYPE_CHECKING
+from uuid import UUID
import pytest
import responses
from click.testing import CliRunner
from cycode.cli.main import main_cli
-from tests.conftest import CLI_ENV_VARS, TEST_FILES_PATH
-from tests.cyclient.test_scan_client import get_zipped_file_scan_response, get_zipped_file_scan_url
+from tests.conftest import CLI_ENV_VARS, TEST_FILES_PATH, ZIP_CONTENT_PATH
+from tests.cyclient.mocked_responses.scan_client import mock_scan_async_responses
_PATH_TO_SCAN = TEST_FILES_PATH.joinpath('zip_content').absolute()
@@ -27,12 +28,10 @@ def _is_json(plain: str) -> bool:
@pytest.mark.parametrize('output', ['text', 'json'])
def test_passing_output_option(output: str, scan_client: 'ScanClient', api_token_response: responses.Response) -> None:
scan_type = 'secret'
+ scan_id = UUID('12345678-418f-47ee-abb0-012345678901')
- responses.add(get_zipped_file_scan_response(get_zipped_file_scan_url(scan_type, scan_client)))
responses.add(api_token_response)
- # Scan report is not mocked.
- # This raises connection error on the attempt to report scan.
- # It doesn't perform real request
+ mock_scan_async_responses(responses, scan_type, scan_client, scan_id, ZIP_CONTENT_PATH)
args = ['--output', output, 'scan', '--soft-fail', 'path', str(_PATH_TO_SCAN)]
result = CliRunner().invoke(main_cli, args, env=CLI_ENV_VARS)
diff --git a/tests/conftest.py b/tests/conftest.py
index fdb02ec2..dc1a84fe 100644
--- a/tests/conftest.py
+++ b/tests/conftest.py
@@ -15,6 +15,8 @@
CLI_ENV_VARS = {'CYCODE_CLIENT_ID': _CLIENT_ID, 'CYCODE_CLIENT_SECRET': _CLIENT_SECRET}
TEST_FILES_PATH = Path(__file__).parent.joinpath('test_files').absolute()
+MOCKED_RESPONSES_PATH = Path(__file__).parent.joinpath('cyclient/mocked_responses/data').absolute()
+ZIP_CONTENT_PATH = TEST_FILES_PATH.joinpath('zip_content').absolute()
@pytest.fixture(scope='session')
diff --git a/tests/cyclient/mocked_responses/__init__.py b/tests/cyclient/mocked_responses/__init__.py
new file mode 100644
index 00000000..e69de29b
diff --git a/tests/cyclient/mocked_responses/data/detections.json b/tests/cyclient/mocked_responses/data/detections.json
new file mode 100644
index 00000000..89196489
--- /dev/null
+++ b/tests/cyclient/mocked_responses/data/detections.json
@@ -0,0 +1,83 @@
+[
+ {
+ "source_policy_name": "Secrets detection",
+ "source_policy_type": "SensitiveContent",
+ "source_entity_name": null,
+ "source_entity_id": null,
+ "detection_type_id": "7dff932a-418f-47ee-abb0-703e0f6592cd",
+ "root_id": null,
+ "status": "Open",
+ "status_updated_at": null,
+ "status_reason": null,
+ "status_change_message": null,
+ "source_entity_type": "Audit",
+ "detection_details": {
+ "organization_name": null,
+ "organization_id": "",
+ "sha512": "6e6c867188c04340d9ecfa1b7e56a356e605f2a70fbda865f11b4a57eb07e634",
+ "provider": "CycodeCli",
+ "concrete_provider": "CycodeCli",
+ "length": 55,
+ "start_position": 19,
+ "line": 0,
+ "commit_id": null,
+ "member_id": "",
+ "member_name": "",
+ "member_email": "",
+ "author_name": "",
+ "author_email": "",
+ "branch_name": "",
+ "committer_name": "",
+ "committed_at": "0001-01-01T00:00:00+00:00",
+ "file_path": "%FILEPATH%",
+ "file_name": "secrets.py",
+ "file_extension": ".py",
+ "url": null,
+ "should_resolve_upon_branch_deletion": false,
+ "position_in_line": 19,
+ "repository_name": null,
+ "repository_id": null,
+ "old_detection_id": "f35c42f99d3712d4593d5ee16a9ceb36ca9fb20b33e68edd0e00847e6a02a7b6"
+ },
+ "severity": "Medium",
+ "remediable": false,
+ "correlation_message": "Secret of type 'Slack Token' was found in filename 'secrets.py' within '' repository",
+ "provider": "CycodeCli",
+ "scan_id": "%SCAN_ID%",
+ "assignee_id": null,
+ "type": "slack-token",
+ "is_hidden": false,
+ "tags": [],
+ "detection_rule_id": "26ab3395-2522-4061-a50a-c69c2d622ca1",
+ "classification": null,
+ "priority": 0,
+ "metadata": null,
+ "labels": [],
+ "detection_id": "f35c42f99d3712d4593d5ee16a9ceb36ca9fb20b33e68edd0e00847e6a02a7b6",
+ "internal_note": null,
+ "sdlc_stages": [
+ "Code",
+ "Container Registry",
+ "Productivity Tools",
+ "Cloud",
+ "Build"
+ ],
+ "policy_labels": [],
+ "category": "SecretDetection",
+ "sub_category": "SensitiveContent",
+ "sub_category_v2": "Messaging Systems",
+ "policy_tags": [],
+ "remediations": [],
+ "instruction_details": {
+ "instruction_name_to_single_id_map": null,
+ "instruction_name_to_multiple_ids_map": null,
+ "instruction_tags": null
+ },
+ "external_detection_references": [],
+ "project_ids": [],
+ "tenant_id": "123456-663f-4e27-9170-e559c2379292",
+ "id": "123456-895a-4830-b6c1-b948e99b71a4",
+ "created_date": "2023-10-25T11:07:14.7516793+00:00",
+ "updated_date": "2023-10-25T11:07:14.7616063+00:00"
+ }
+]
\ No newline at end of file
diff --git a/tests/cyclient/mocked_responses/scan_client.py b/tests/cyclient/mocked_responses/scan_client.py
new file mode 100644
index 00000000..8518e2b9
--- /dev/null
+++ b/tests/cyclient/mocked_responses/scan_client.py
@@ -0,0 +1,158 @@
+import json
+from pathlib import Path
+from typing import Optional
+from uuid import UUID, uuid4
+
+import responses
+
+from cycode.cyclient.scan_client import ScanClient
+from tests.conftest import MOCKED_RESPONSES_PATH
+
+
+def get_zipped_file_scan_url(scan_type: str, scan_client: ScanClient) -> str:
+ api_url = scan_client.scan_cycode_client.api_url
+ service_url = scan_client.get_zipped_file_scan_url_path(scan_type)
+ return f'{api_url}/{service_url}'
+
+
+def get_zipped_file_scan_response(
+ url: str, zip_content_path: Path, scan_id: Optional[UUID] = None
+) -> responses.Response:
+ if not scan_id:
+ scan_id = uuid4()
+
+ json_response = {
+ 'did_detect': True,
+ 'scan_id': str(scan_id), # not always as expected due to _get_scan_id and passing scan_id to cxt of CLI
+ 'detections_per_file': [
+ {
+ 'file_name': str(zip_content_path.joinpath('secrets.py')),
+ 'commit_id': None,
+ 'detections': [
+ {
+ 'detection_type_id': '12345678-418f-47ee-abb0-012345678901',
+ 'detection_rule_id': '12345678-aea1-4304-a6e9-012345678901',
+ 'message': "Secret of type 'Slack Token' was found in filename 'secrets.py'",
+ 'type': 'slack-token',
+ 'is_research': False,
+ 'detection_details': {
+ 'sha512': 'sha hash',
+ 'length': 55,
+ 'start_position': 19,
+ 'line': 0,
+ 'committed_at': '0001-01-01T00:00:00+00:00',
+ 'file_path': str(zip_content_path),
+ 'file_name': 'secrets.py',
+ 'file_extension': '.py',
+ 'should_resolve_upon_branch_deletion': False,
+ },
+ }
+ ],
+ }
+ ],
+ 'report_url': None,
+ }
+
+ return responses.Response(method=responses.POST, url=url, json=json_response, status=200)
+
+
+def get_zipped_file_scan_async_url(scan_type: str, scan_client: ScanClient) -> str:
+ api_url = scan_client.scan_cycode_client.api_url
+ service_url = scan_client.get_zipped_file_scan_async_url_path(scan_type)
+ return f'{api_url}/{service_url}'
+
+
+def get_zipped_file_scan_async_response(url: str, scan_id: Optional[UUID] = None) -> responses.Response:
+ if not scan_id:
+ scan_id = uuid4()
+
+ json_response = {
+ 'scan_id': str(scan_id), # not always as expected due to _get_scan_id and passing scan_id to cxt of CLI
+ }
+
+ return responses.Response(method=responses.POST, url=url, json=json_response, status=200)
+
+
+def get_scan_details_url(scan_id: Optional[UUID], scan_client: ScanClient) -> str:
+ api_url = scan_client.scan_cycode_client.api_url
+ service_url = scan_client.get_scan_details_path(str(scan_id))
+ return f'{api_url}/{service_url}'
+
+
+def get_scan_details_response(url: str, scan_id: Optional[UUID] = None) -> responses.Response:
+ if not scan_id:
+ scan_id = uuid4()
+
+ json_response = {
+ 'id': str(scan_id),
+ 'scan_type': 'Secrets',
+ 'metadata': f'Path: {scan_id}, Folder: scans, Size: 465',
+ 'entity_type': 'ZippedFile',
+ 'entity_id': 'Repository',
+ 'parent_entity_id': 'Organization',
+ 'organization_id': 'Organization',
+ 'scm_provider': 'CycodeCli',
+ 'started_at': '2023-10-25T10:02:23.048282+00:00',
+ 'finished_at': '2023-10-25T10:02:26.867082+00:00',
+ 'scan_status': 'Completed', # mark as completed to avoid mocking repeated requests
+ 'message': None,
+ 'results_count': 1,
+ 'scan_update_at': '2023-10-25T10:02:26.867216+00:00',
+ 'duration': {'days': 0, 'hours': 0, 'minutes': 0, 'seconds': 3, 'milliseconds': 818},
+ 'is_hidden': False,
+ 'is_initial_scan': False,
+ 'detection_messages': [],
+ }
+
+ return responses.Response(method=responses.GET, url=url, json=json_response, status=200)
+
+
+def get_scan_detections_count_url(scan_client: ScanClient) -> str:
+ api_url = scan_client.scan_cycode_client.api_url
+ service_url = scan_client.get_get_scan_detections_count_path()
+ return f'{api_url}/{service_url}'
+
+
+def get_scan_detections_count_response(url: str) -> responses.Response:
+ json_response = {'count': 1}
+
+ return responses.Response(method=responses.GET, url=url, json=json_response, status=200)
+
+
+def get_scan_detections_url(scan_client: ScanClient) -> str:
+ api_url = scan_client.scan_cycode_client.api_url
+ service_url = scan_client.get_scan_detections_path()
+ return f'{api_url}/{service_url}'
+
+
+def get_scan_detections_response(url: str, scan_id: UUID, zip_content_path: Path) -> responses.Response:
+ with open(MOCKED_RESPONSES_PATH.joinpath('detections.json'), encoding='UTF-8') as f:
+ content = f.read()
+ content = content.replace('%FILEPATH%', str(zip_content_path.absolute().as_posix()))
+ content = content.replace('%SCAN_ID%', str(scan_id))
+
+ json_response = json.loads(content)
+
+ return responses.Response(method=responses.GET, url=url, json=json_response, status=200)
+
+
+def get_report_scan_status_url(scan_type: str, scan_id: UUID, scan_client: ScanClient) -> str:
+ api_url = scan_client.scan_cycode_client.api_url
+ service_url = scan_client.get_report_scan_status_path(scan_type, str(scan_id))
+ return f'{api_url}/{service_url}'
+
+
+def get_report_scan_status_response(url: str) -> responses.Response:
+ return responses.Response(method=responses.POST, url=url, status=200)
+
+
+def mock_scan_async_responses(
+ responses_module: responses, scan_type: str, scan_client: ScanClient, scan_id: UUID, zip_content_path: Path
+) -> None:
+ responses_module.add(
+ get_zipped_file_scan_async_response(get_zipped_file_scan_async_url(scan_type, scan_client), scan_id)
+ )
+ responses_module.add(get_scan_details_response(get_scan_details_url(scan_id, scan_client), scan_id))
+ responses_module.add(get_scan_detections_count_response(get_scan_detections_count_url(scan_client)))
+ responses_module.add(get_scan_detections_response(get_scan_detections_url(scan_client), scan_id, zip_content_path))
+ responses_module.add(get_report_scan_status_response(get_report_scan_status_url(scan_type, scan_id, scan_client)))
diff --git a/tests/cyclient/test_scan_client.py b/tests/cyclient/test_scan_client.py
index 2ca374b2..1f8ed462 100644
--- a/tests/cyclient/test_scan_client.py
+++ b/tests/cyclient/test_scan_client.py
@@ -1,6 +1,6 @@
import os
-from typing import List, Optional, Tuple
-from uuid import UUID, uuid4
+from typing import List, Tuple
+from uuid import uuid4
import pytest
import requests
@@ -14,9 +14,8 @@
from cycode.cli.files_collector.models.in_memory_zip import InMemoryZip
from cycode.cli.models import Document
from cycode.cyclient.scan_client import ScanClient
-from tests.conftest import TEST_FILES_PATH
-
-_ZIP_CONTENT_PATH = TEST_FILES_PATH.joinpath('zip_content').absolute()
+from tests.conftest import ZIP_CONTENT_PATH
+from tests.cyclient.mocked_responses.scan_client import get_zipped_file_scan_response, get_zipped_file_scan_url
def zip_scan_resources(scan_type: str, scan_client: ScanClient) -> Tuple[str, InMemoryZip]:
@@ -26,17 +25,10 @@ def zip_scan_resources(scan_type: str, scan_client: ScanClient) -> Tuple[str, In
return url, zip_file
-def get_zipped_file_scan_url(scan_type: str, scan_client: ScanClient) -> str:
- api_url = scan_client.scan_cycode_client.api_url
- # TODO(MarshalX): create method in the scan client to build this url
- service_url = f'{api_url}/{scan_client.scan_config.get_service_name(scan_type)}'
- return f'{service_url}/{scan_client.SCAN_CONTROLLER_PATH}/zipped-file'
-
-
def get_test_zip_file(scan_type: str) -> InMemoryZip:
# TODO(MarshalX): refactor scan_disk_files in code_scanner.py to reuse method here instead of this
test_documents: List[Document] = []
- for root, _, files in os.walk(_ZIP_CONTENT_PATH):
+ for root, _, files in os.walk(ZIP_CONTENT_PATH):
for name in files:
path = os.path.join(root, name)
with open(path, 'r', encoding='UTF-8') as f:
@@ -45,53 +37,6 @@ def get_test_zip_file(scan_type: str) -> InMemoryZip:
return zip_documents(scan_type, test_documents)
-def get_zipped_file_scan_response(url: str, scan_id: Optional[UUID] = None) -> responses.Response:
- if not scan_id:
- scan_id = uuid4()
-
- json_response = {
- 'did_detect': True,
- 'scan_id': str(scan_id), # not always as expected due to _get_scan_id and passing scan_id to cxt of CLI
- 'detections_per_file': [
- {
- 'file_name': str(_ZIP_CONTENT_PATH.joinpath('secrets.py')),
- 'commit_id': None,
- 'detections': [
- {
- 'detection_type_id': '12345678-418f-47ee-abb0-012345678901',
- 'detection_rule_id': '12345678-aea1-4304-a6e9-012345678901',
- 'message': "Secret of type 'Slack Token' was found in filename 'secrets.py'",
- 'type': 'slack-token',
- 'is_research': False,
- 'detection_details': {
- 'sha512': 'sha hash',
- 'length': 55,
- 'start_position': 19,
- 'line': 0,
- 'committed_at': '0001-01-01T00:00:00+00:00',
- 'file_path': str(_ZIP_CONTENT_PATH),
- 'file_name': 'secrets.py',
- 'file_extension': '.py',
- 'should_resolve_upon_branch_deletion': False,
- },
- }
- ],
- }
- ],
- 'report_url': None,
- }
-
- return responses.Response(method=responses.POST, url=url, json=json_response, status=200)
-
-
-def test_get_service_name(scan_client: ScanClient) -> None:
- # TODO(MarshalX): get_service_name should be removed from ScanClient? Because it exists in ScanConfig
- assert scan_client.get_service_name('secret') == 'secret'
- assert scan_client.get_service_name('iac') == 'iac'
- assert scan_client.get_service_name('sca') == 'scans'
- assert scan_client.get_service_name('sast') == 'scans'
-
-
@pytest.mark.parametrize('scan_type', config['scans']['supported_scans'])
@responses.activate
def test_zipped_file_scan(scan_type: str, scan_client: ScanClient, api_token_response: responses.Response) -> None:
@@ -99,7 +44,7 @@ def test_zipped_file_scan(scan_type: str, scan_client: ScanClient, api_token_res
expected_scan_id = uuid4()
responses.add(api_token_response) # mock token based client
- responses.add(get_zipped_file_scan_response(url, expected_scan_id))
+ responses.add(get_zipped_file_scan_response(url, ZIP_CONTENT_PATH, expected_scan_id))
zipped_file_scan_response = scan_client.zipped_file_scan(
scan_type, zip_file, scan_id=str(expected_scan_id), scan_parameters={}
From aa72f50462752281be12eb4838f4a2aad0e018fb Mon Sep 17 00:00:00 2001
From: Ilya Siamionau
Date: Mon, 6 Nov 2023 13:22:06 +0100
Subject: [PATCH 045/257] CM-28230 - Update GitHub organization name (#176)
---
LICENCE | 2 +-
README.md | 25 ++++---
poetry.lock | 182 ++++++++++++++++++++++++-------------------------
pyproject.toml | 2 +-
4 files changed, 105 insertions(+), 106 deletions(-)
diff --git a/LICENCE b/LICENCE
index 404e3d08..8d72be9a 100644
--- a/LICENCE
+++ b/LICENCE
@@ -1,6 +1,6 @@
MIT License
-Copyright (c) 2022 cycodehq-public
+Copyright (c) 2022 Cycode Ltd.
Permission is hereby granted, free of charge, to any person obtaining a copy
of this software and associated documentation files (the "Software"), to deal
diff --git a/README.md b/README.md
index ffbaf350..e1efe9d9 100644
--- a/README.md
+++ b/README.md
@@ -91,24 +91,24 @@ To install the Cycode CLI application on your local machine, perform the followi
2. A browser window will appear, asking you to log into Cycode (as seen below):
-
+
3. Enter your login credentials on this page and log in.
4. You will eventually be taken to the page below, where you'll be asked to choose the business group you want to authorize Cycode with (if applicable):
-
+
> :memo: **Note**
> This will be the default method for authenticating with the Cycode CLI.
5. Click the **Allow** button to authorize the Cycode CLI on the selected business group.
-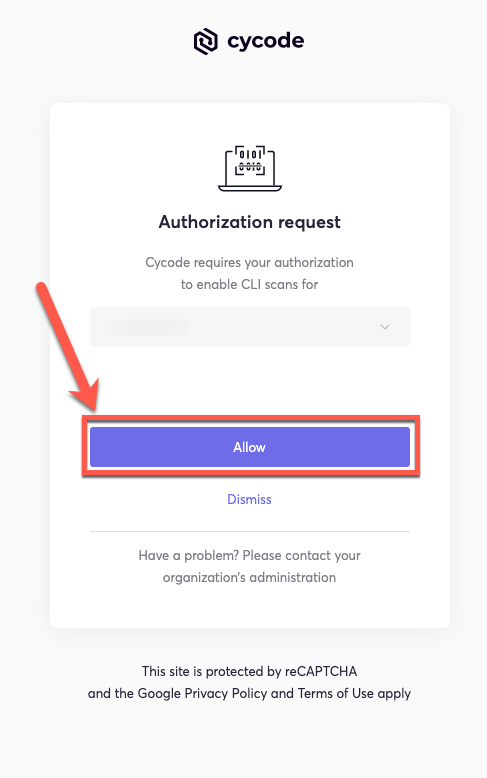
+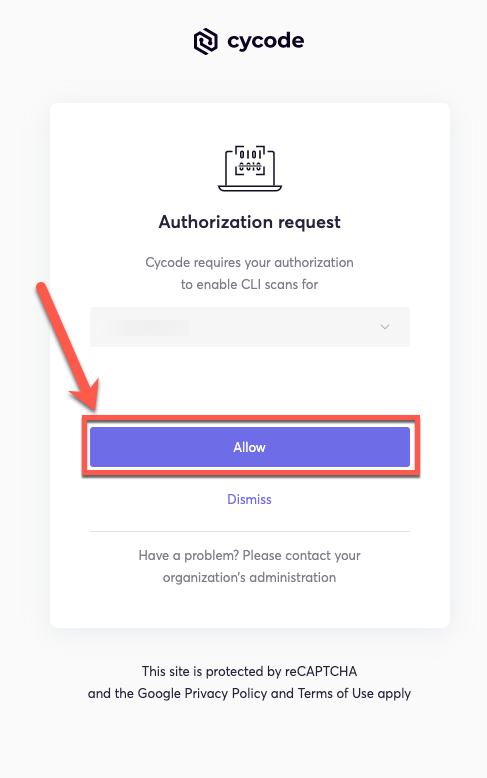
6. Once completed, you'll see the following screen, if it was selected successfully:
-
+
7. In the terminal/command line screen, you will see the following when exiting the browser window:
@@ -177,19 +177,19 @@ export CYCODE_CLIENT_SECRET={your Cycode Secret Key}
1. From the Control Panel, navigate to the System menu:
-
+
2. Next, click Advanced system settings:
-
+
3. In the System Properties window that opens, click the Environment Variables button:
-
+
4. Create `CYCODE_CLIENT_ID` and `CYCODE_CLIENT_SECRET` variables with values matching your ID and Secret Key, respectively:
-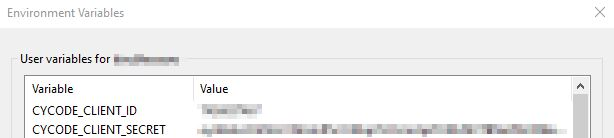
+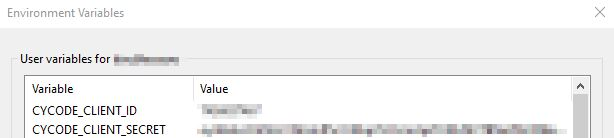
5. Insert the cycode.exe into the path to complete the installation.
@@ -209,11 +209,10 @@ Perform the following steps to install the pre-commit hook:
```yaml
repos:
- - repo: https://github.com/cycodehq-public/cycode-cli
- rev: stable
+ - repo: https://github.com/cycodehq/cycode-cli
+ rev: v1.4.0
hooks:
- id: cycode
- language_version: python3
stages:
- commit
```
@@ -383,7 +382,7 @@ Report URL: https://app.cycode.com/on-demand-scans/617ecc3d-9ff2-493e-8be8-2c1fe
The report page will look something like below:
-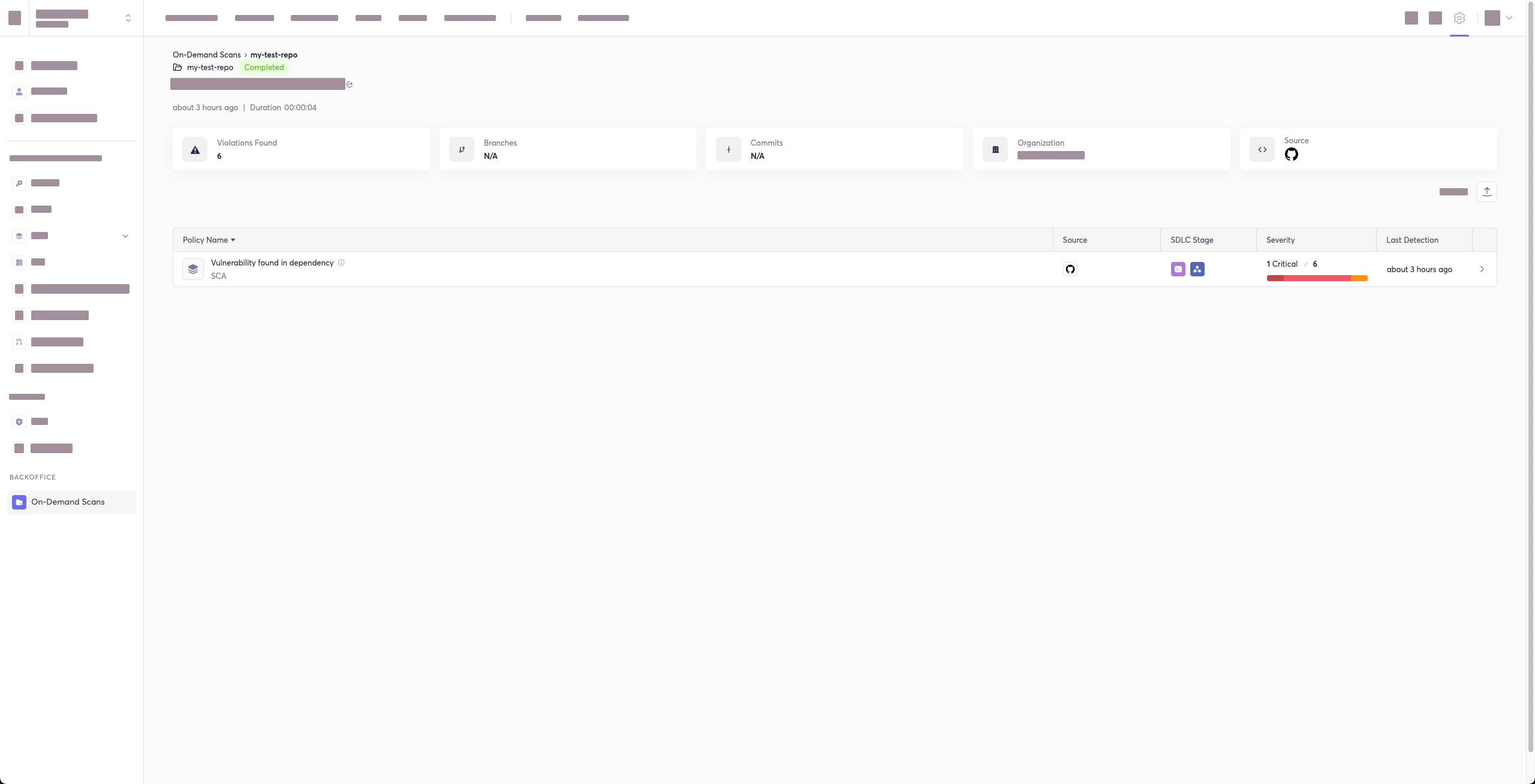
+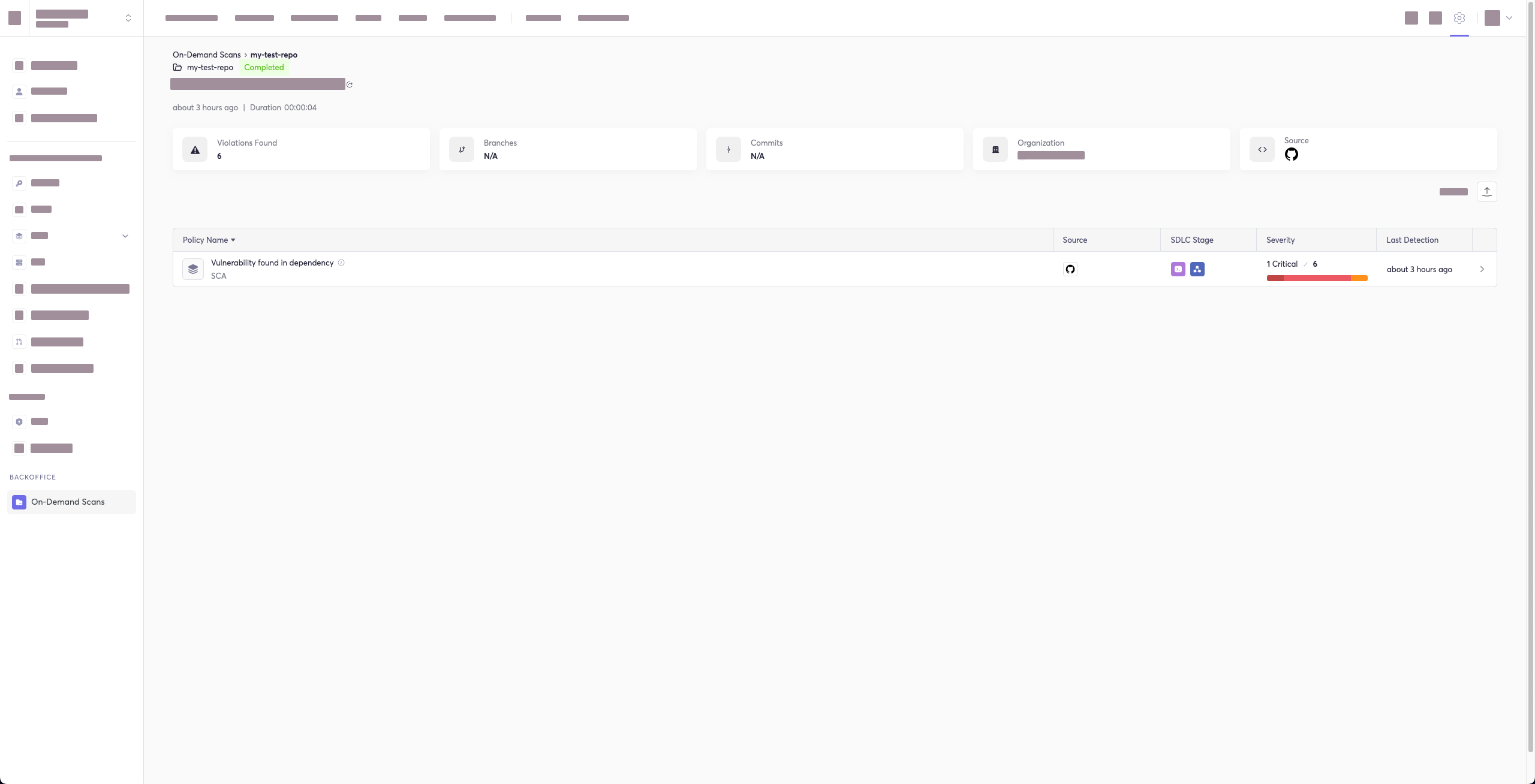
### Package Vulnerabilities Option
@@ -758,7 +757,7 @@ To create an SBOM report for a repository URI:\
`cycode report sbom --format --include-vulnerabilities --include-dev-dependencies --output-file repository_url `
For example:\
-`cycode report sbom --format spdx-2.3 --include-vulnerabilities --include-dev-dependencies repository_url https://github.com/cycodehq-public/cycode-cli.git`
+`cycode report sbom --format spdx-2.3 --include-vulnerabilities --include-dev-dependencies repository_url https://github.com/cycodehq/cycode-cli.git`
### Local Project
diff --git a/poetry.lock b/poetry.lock
index 04f7b712..46d5ffcd 100644
--- a/poetry.lock
+++ b/poetry.lock
@@ -114,101 +114,101 @@ files = [
[[package]]
name = "charset-normalizer"
-version = "3.3.1"
+version = "3.3.2"
description = "The Real First Universal Charset Detector. Open, modern and actively maintained alternative to Chardet."
optional = false
python-versions = ">=3.7.0"
files = [
- {file = "charset-normalizer-3.3.1.tar.gz", hash = "sha256:d9137a876020661972ca6eec0766d81aef8a5627df628b664b234b73396e727e"},
- {file = "charset_normalizer-3.3.1-cp310-cp310-macosx_10_9_universal2.whl", hash = "sha256:8aee051c89e13565c6bd366813c386939f8e928af93c29fda4af86d25b73d8f8"},
- {file = "charset_normalizer-3.3.1-cp310-cp310-macosx_10_9_x86_64.whl", hash = "sha256:352a88c3df0d1fa886562384b86f9a9e27563d4704ee0e9d56ec6fcd270ea690"},
- {file = "charset_normalizer-3.3.1-cp310-cp310-macosx_11_0_arm64.whl", hash = "sha256:223b4d54561c01048f657fa6ce41461d5ad8ff128b9678cfe8b2ecd951e3f8a2"},
- {file = "charset_normalizer-3.3.1-cp310-cp310-manylinux_2_17_aarch64.manylinux2014_aarch64.whl", hash = "sha256:4f861d94c2a450b974b86093c6c027888627b8082f1299dfd5a4bae8e2292821"},
- {file = "charset_normalizer-3.3.1-cp310-cp310-manylinux_2_17_ppc64le.manylinux2014_ppc64le.whl", hash = "sha256:1171ef1fc5ab4693c5d151ae0fdad7f7349920eabbaca6271f95969fa0756c2d"},
- {file = "charset_normalizer-3.3.1-cp310-cp310-manylinux_2_17_s390x.manylinux2014_s390x.whl", hash = "sha256:28f512b9a33235545fbbdac6a330a510b63be278a50071a336afc1b78781b147"},
- {file = "charset_normalizer-3.3.1-cp310-cp310-manylinux_2_17_x86_64.manylinux2014_x86_64.whl", hash = "sha256:c0e842112fe3f1a4ffcf64b06dc4c61a88441c2f02f373367f7b4c1aa9be2ad5"},
- {file = "charset_normalizer-3.3.1-cp310-cp310-manylinux_2_5_i686.manylinux1_i686.manylinux_2_17_i686.manylinux2014_i686.whl", hash = "sha256:3f9bc2ce123637a60ebe819f9fccc614da1bcc05798bbbaf2dd4ec91f3e08846"},
- {file = "charset_normalizer-3.3.1-cp310-cp310-musllinux_1_1_aarch64.whl", hash = "sha256:f194cce575e59ffe442c10a360182a986535fd90b57f7debfaa5c845c409ecc3"},
- {file = "charset_normalizer-3.3.1-cp310-cp310-musllinux_1_1_i686.whl", hash = "sha256:9a74041ba0bfa9bc9b9bb2cd3238a6ab3b7618e759b41bd15b5f6ad958d17605"},
- {file = "charset_normalizer-3.3.1-cp310-cp310-musllinux_1_1_ppc64le.whl", hash = "sha256:b578cbe580e3b41ad17b1c428f382c814b32a6ce90f2d8e39e2e635d49e498d1"},
- {file = "charset_normalizer-3.3.1-cp310-cp310-musllinux_1_1_s390x.whl", hash = "sha256:6db3cfb9b4fcecb4390db154e75b49578c87a3b9979b40cdf90d7e4b945656e1"},
- {file = "charset_normalizer-3.3.1-cp310-cp310-musllinux_1_1_x86_64.whl", hash = "sha256:debb633f3f7856f95ad957d9b9c781f8e2c6303ef21724ec94bea2ce2fcbd056"},
- {file = "charset_normalizer-3.3.1-cp310-cp310-win32.whl", hash = "sha256:87071618d3d8ec8b186d53cb6e66955ef2a0e4fa63ccd3709c0c90ac5a43520f"},
- {file = "charset_normalizer-3.3.1-cp310-cp310-win_amd64.whl", hash = "sha256:e372d7dfd154009142631de2d316adad3cc1c36c32a38b16a4751ba78da2a397"},
- {file = "charset_normalizer-3.3.1-cp311-cp311-macosx_10_9_universal2.whl", hash = "sha256:ae4070f741f8d809075ef697877fd350ecf0b7c5837ed68738607ee0a2c572cf"},
- {file = "charset_normalizer-3.3.1-cp311-cp311-macosx_10_9_x86_64.whl", hash = "sha256:58e875eb7016fd014c0eea46c6fa92b87b62c0cb31b9feae25cbbe62c919f54d"},
- {file = "charset_normalizer-3.3.1-cp311-cp311-macosx_11_0_arm64.whl", hash = "sha256:dbd95e300367aa0827496fe75a1766d198d34385a58f97683fe6e07f89ca3e3c"},
- {file = "charset_normalizer-3.3.1-cp311-cp311-manylinux_2_17_aarch64.manylinux2014_aarch64.whl", hash = "sha256:de0b4caa1c8a21394e8ce971997614a17648f94e1cd0640fbd6b4d14cab13a72"},
- {file = "charset_normalizer-3.3.1-cp311-cp311-manylinux_2_17_ppc64le.manylinux2014_ppc64le.whl", hash = "sha256:985c7965f62f6f32bf432e2681173db41336a9c2611693247069288bcb0c7f8b"},
- {file = "charset_normalizer-3.3.1-cp311-cp311-manylinux_2_17_s390x.manylinux2014_s390x.whl", hash = "sha256:a15c1fe6d26e83fd2e5972425a772cca158eae58b05d4a25a4e474c221053e2d"},
- {file = "charset_normalizer-3.3.1-cp311-cp311-manylinux_2_17_x86_64.manylinux2014_x86_64.whl", hash = "sha256:ae55d592b02c4349525b6ed8f74c692509e5adffa842e582c0f861751701a673"},
- {file = "charset_normalizer-3.3.1-cp311-cp311-manylinux_2_5_i686.manylinux1_i686.manylinux_2_17_i686.manylinux2014_i686.whl", hash = "sha256:be4d9c2770044a59715eb57c1144dedea7c5d5ae80c68fb9959515037cde2008"},
- {file = "charset_normalizer-3.3.1-cp311-cp311-musllinux_1_1_aarch64.whl", hash = "sha256:851cf693fb3aaef71031237cd68699dded198657ec1e76a76eb8be58c03a5d1f"},
- {file = "charset_normalizer-3.3.1-cp311-cp311-musllinux_1_1_i686.whl", hash = "sha256:31bbaba7218904d2eabecf4feec0d07469284e952a27400f23b6628439439fa7"},
- {file = "charset_normalizer-3.3.1-cp311-cp311-musllinux_1_1_ppc64le.whl", hash = "sha256:871d045d6ccc181fd863a3cd66ee8e395523ebfbc57f85f91f035f50cee8e3d4"},
- {file = "charset_normalizer-3.3.1-cp311-cp311-musllinux_1_1_s390x.whl", hash = "sha256:501adc5eb6cd5f40a6f77fbd90e5ab915c8fd6e8c614af2db5561e16c600d6f3"},
- {file = "charset_normalizer-3.3.1-cp311-cp311-musllinux_1_1_x86_64.whl", hash = "sha256:f5fb672c396d826ca16a022ac04c9dce74e00a1c344f6ad1a0fdc1ba1f332213"},
- {file = "charset_normalizer-3.3.1-cp311-cp311-win32.whl", hash = "sha256:bb06098d019766ca16fc915ecaa455c1f1cd594204e7f840cd6258237b5079a8"},
- {file = "charset_normalizer-3.3.1-cp311-cp311-win_amd64.whl", hash = "sha256:8af5a8917b8af42295e86b64903156b4f110a30dca5f3b5aedea123fbd638bff"},
- {file = "charset_normalizer-3.3.1-cp312-cp312-macosx_10_9_universal2.whl", hash = "sha256:7ae8e5142dcc7a49168f4055255dbcced01dc1714a90a21f87448dc8d90617d1"},
- {file = "charset_normalizer-3.3.1-cp312-cp312-macosx_10_9_x86_64.whl", hash = "sha256:5b70bab78accbc672f50e878a5b73ca692f45f5b5e25c8066d748c09405e6a55"},
- {file = "charset_normalizer-3.3.1-cp312-cp312-macosx_11_0_arm64.whl", hash = "sha256:5ceca5876032362ae73b83347be8b5dbd2d1faf3358deb38c9c88776779b2e2f"},
- {file = "charset_normalizer-3.3.1-cp312-cp312-manylinux_2_17_aarch64.manylinux2014_aarch64.whl", hash = "sha256:34d95638ff3613849f473afc33f65c401a89f3b9528d0d213c7037c398a51296"},
- {file = "charset_normalizer-3.3.1-cp312-cp312-manylinux_2_17_ppc64le.manylinux2014_ppc64le.whl", hash = "sha256:9edbe6a5bf8b56a4a84533ba2b2f489d0046e755c29616ef8830f9e7d9cf5728"},
- {file = "charset_normalizer-3.3.1-cp312-cp312-manylinux_2_17_s390x.manylinux2014_s390x.whl", hash = "sha256:f6a02a3c7950cafaadcd46a226ad9e12fc9744652cc69f9e5534f98b47f3bbcf"},
- {file = "charset_normalizer-3.3.1-cp312-cp312-manylinux_2_17_x86_64.manylinux2014_x86_64.whl", hash = "sha256:10b8dd31e10f32410751b3430996f9807fc4d1587ca69772e2aa940a82ab571a"},
- {file = "charset_normalizer-3.3.1-cp312-cp312-manylinux_2_5_i686.manylinux1_i686.manylinux_2_17_i686.manylinux2014_i686.whl", hash = "sha256:edc0202099ea1d82844316604e17d2b175044f9bcb6b398aab781eba957224bd"},
- {file = "charset_normalizer-3.3.1-cp312-cp312-musllinux_1_1_aarch64.whl", hash = "sha256:b891a2f68e09c5ef989007fac11476ed33c5c9994449a4e2c3386529d703dc8b"},
- {file = "charset_normalizer-3.3.1-cp312-cp312-musllinux_1_1_i686.whl", hash = "sha256:71ef3b9be10070360f289aea4838c784f8b851be3ba58cf796262b57775c2f14"},
- {file = "charset_normalizer-3.3.1-cp312-cp312-musllinux_1_1_ppc64le.whl", hash = "sha256:55602981b2dbf8184c098bc10287e8c245e351cd4fdcad050bd7199d5a8bf514"},
- {file = "charset_normalizer-3.3.1-cp312-cp312-musllinux_1_1_s390x.whl", hash = "sha256:46fb9970aa5eeca547d7aa0de5d4b124a288b42eaefac677bde805013c95725c"},
- {file = "charset_normalizer-3.3.1-cp312-cp312-musllinux_1_1_x86_64.whl", hash = "sha256:520b7a142d2524f999447b3a0cf95115df81c4f33003c51a6ab637cbda9d0bf4"},
- {file = "charset_normalizer-3.3.1-cp312-cp312-win32.whl", hash = "sha256:8ec8ef42c6cd5856a7613dcd1eaf21e5573b2185263d87d27c8edcae33b62a61"},
- {file = "charset_normalizer-3.3.1-cp312-cp312-win_amd64.whl", hash = "sha256:baec8148d6b8bd5cee1ae138ba658c71f5b03e0d69d5907703e3e1df96db5e41"},
- {file = "charset_normalizer-3.3.1-cp37-cp37m-macosx_10_9_x86_64.whl", hash = "sha256:63a6f59e2d01310f754c270e4a257426fe5a591dc487f1983b3bbe793cf6bac6"},
- {file = "charset_normalizer-3.3.1-cp37-cp37m-manylinux_2_17_aarch64.manylinux2014_aarch64.whl", hash = "sha256:1d6bfc32a68bc0933819cfdfe45f9abc3cae3877e1d90aac7259d57e6e0f85b1"},
- {file = "charset_normalizer-3.3.1-cp37-cp37m-manylinux_2_17_ppc64le.manylinux2014_ppc64le.whl", hash = "sha256:4f3100d86dcd03c03f7e9c3fdb23d92e32abbca07e7c13ebd7ddfbcb06f5991f"},
- {file = "charset_normalizer-3.3.1-cp37-cp37m-manylinux_2_17_s390x.manylinux2014_s390x.whl", hash = "sha256:39b70a6f88eebe239fa775190796d55a33cfb6d36b9ffdd37843f7c4c1b5dc67"},
- {file = "charset_normalizer-3.3.1-cp37-cp37m-manylinux_2_17_x86_64.manylinux2014_x86_64.whl", hash = "sha256:4e12f8ee80aa35e746230a2af83e81bd6b52daa92a8afaef4fea4a2ce9b9f4fa"},
- {file = "charset_normalizer-3.3.1-cp37-cp37m-manylinux_2_5_i686.manylinux1_i686.manylinux_2_17_i686.manylinux2014_i686.whl", hash = "sha256:7b6cefa579e1237ce198619b76eaa148b71894fb0d6bcf9024460f9bf30fd228"},
- {file = "charset_normalizer-3.3.1-cp37-cp37m-musllinux_1_1_aarch64.whl", hash = "sha256:61f1e3fb621f5420523abb71f5771a204b33c21d31e7d9d86881b2cffe92c47c"},
- {file = "charset_normalizer-3.3.1-cp37-cp37m-musllinux_1_1_i686.whl", hash = "sha256:4f6e2a839f83a6a76854d12dbebde50e4b1afa63e27761549d006fa53e9aa80e"},
- {file = "charset_normalizer-3.3.1-cp37-cp37m-musllinux_1_1_ppc64le.whl", hash = "sha256:1ec937546cad86d0dce5396748bf392bb7b62a9eeb8c66efac60e947697f0e58"},
- {file = "charset_normalizer-3.3.1-cp37-cp37m-musllinux_1_1_s390x.whl", hash = "sha256:82ca51ff0fc5b641a2d4e1cc8c5ff108699b7a56d7f3ad6f6da9dbb6f0145b48"},
- {file = "charset_normalizer-3.3.1-cp37-cp37m-musllinux_1_1_x86_64.whl", hash = "sha256:633968254f8d421e70f91c6ebe71ed0ab140220469cf87a9857e21c16687c034"},
- {file = "charset_normalizer-3.3.1-cp37-cp37m-win32.whl", hash = "sha256:c0c72d34e7de5604df0fde3644cc079feee5e55464967d10b24b1de268deceb9"},
- {file = "charset_normalizer-3.3.1-cp37-cp37m-win_amd64.whl", hash = "sha256:63accd11149c0f9a99e3bc095bbdb5a464862d77a7e309ad5938fbc8721235ae"},
- {file = "charset_normalizer-3.3.1-cp38-cp38-macosx_10_9_universal2.whl", hash = "sha256:5a3580a4fdc4ac05f9e53c57f965e3594b2f99796231380adb2baaab96e22761"},
- {file = "charset_normalizer-3.3.1-cp38-cp38-macosx_10_9_x86_64.whl", hash = "sha256:2465aa50c9299d615d757c1c888bc6fef384b7c4aec81c05a0172b4400f98557"},
- {file = "charset_normalizer-3.3.1-cp38-cp38-macosx_11_0_arm64.whl", hash = "sha256:cb7cd68814308aade9d0c93c5bd2ade9f9441666f8ba5aa9c2d4b389cb5e2a45"},
- {file = "charset_normalizer-3.3.1-cp38-cp38-manylinux_2_17_aarch64.manylinux2014_aarch64.whl", hash = "sha256:91e43805ccafa0a91831f9cd5443aa34528c0c3f2cc48c4cb3d9a7721053874b"},
- {file = "charset_normalizer-3.3.1-cp38-cp38-manylinux_2_17_ppc64le.manylinux2014_ppc64le.whl", hash = "sha256:854cc74367180beb327ab9d00f964f6d91da06450b0855cbbb09187bcdb02de5"},
- {file = "charset_normalizer-3.3.1-cp38-cp38-manylinux_2_17_s390x.manylinux2014_s390x.whl", hash = "sha256:c15070ebf11b8b7fd1bfff7217e9324963c82dbdf6182ff7050519e350e7ad9f"},
- {file = "charset_normalizer-3.3.1-cp38-cp38-manylinux_2_17_x86_64.manylinux2014_x86_64.whl", hash = "sha256:2c4c99f98fc3a1835af8179dcc9013f93594d0670e2fa80c83aa36346ee763d2"},
- {file = "charset_normalizer-3.3.1-cp38-cp38-manylinux_2_5_i686.manylinux1_i686.manylinux_2_17_i686.manylinux2014_i686.whl", hash = "sha256:3fb765362688821404ad6cf86772fc54993ec11577cd5a92ac44b4c2ba52155b"},
- {file = "charset_normalizer-3.3.1-cp38-cp38-musllinux_1_1_aarch64.whl", hash = "sha256:dced27917823df984fe0c80a5c4ad75cf58df0fbfae890bc08004cd3888922a2"},
- {file = "charset_normalizer-3.3.1-cp38-cp38-musllinux_1_1_i686.whl", hash = "sha256:a66bcdf19c1a523e41b8e9d53d0cedbfbac2e93c649a2e9502cb26c014d0980c"},
- {file = "charset_normalizer-3.3.1-cp38-cp38-musllinux_1_1_ppc64le.whl", hash = "sha256:ecd26be9f112c4f96718290c10f4caea6cc798459a3a76636b817a0ed7874e42"},
- {file = "charset_normalizer-3.3.1-cp38-cp38-musllinux_1_1_s390x.whl", hash = "sha256:3f70fd716855cd3b855316b226a1ac8bdb3caf4f7ea96edcccc6f484217c9597"},
- {file = "charset_normalizer-3.3.1-cp38-cp38-musllinux_1_1_x86_64.whl", hash = "sha256:17a866d61259c7de1bdadef418a37755050ddb4b922df8b356503234fff7932c"},
- {file = "charset_normalizer-3.3.1-cp38-cp38-win32.whl", hash = "sha256:548eefad783ed787b38cb6f9a574bd8664468cc76d1538215d510a3cd41406cb"},
- {file = "charset_normalizer-3.3.1-cp38-cp38-win_amd64.whl", hash = "sha256:45f053a0ece92c734d874861ffe6e3cc92150e32136dd59ab1fb070575189c97"},
- {file = "charset_normalizer-3.3.1-cp39-cp39-macosx_10_9_universal2.whl", hash = "sha256:bc791ec3fd0c4309a753f95bb6c749ef0d8ea3aea91f07ee1cf06b7b02118f2f"},
- {file = "charset_normalizer-3.3.1-cp39-cp39-macosx_10_9_x86_64.whl", hash = "sha256:0c8c61fb505c7dad1d251c284e712d4e0372cef3b067f7ddf82a7fa82e1e9a93"},
- {file = "charset_normalizer-3.3.1-cp39-cp39-macosx_11_0_arm64.whl", hash = "sha256:2c092be3885a1b7899cd85ce24acedc1034199d6fca1483fa2c3a35c86e43041"},
- {file = "charset_normalizer-3.3.1-cp39-cp39-manylinux_2_17_aarch64.manylinux2014_aarch64.whl", hash = "sha256:c2000c54c395d9e5e44c99dc7c20a64dc371f777faf8bae4919ad3e99ce5253e"},
- {file = "charset_normalizer-3.3.1-cp39-cp39-manylinux_2_17_ppc64le.manylinux2014_ppc64le.whl", hash = "sha256:4cb50a0335382aac15c31b61d8531bc9bb657cfd848b1d7158009472189f3d62"},
- {file = "charset_normalizer-3.3.1-cp39-cp39-manylinux_2_17_s390x.manylinux2014_s390x.whl", hash = "sha256:c30187840d36d0ba2893bc3271a36a517a717f9fd383a98e2697ee890a37c273"},
- {file = "charset_normalizer-3.3.1-cp39-cp39-manylinux_2_17_x86_64.manylinux2014_x86_64.whl", hash = "sha256:fe81b35c33772e56f4b6cf62cf4aedc1762ef7162a31e6ac7fe5e40d0149eb67"},
- {file = "charset_normalizer-3.3.1-cp39-cp39-manylinux_2_5_i686.manylinux1_i686.manylinux_2_17_i686.manylinux2014_i686.whl", hash = "sha256:d0bf89afcbcf4d1bb2652f6580e5e55a840fdf87384f6063c4a4f0c95e378656"},
- {file = "charset_normalizer-3.3.1-cp39-cp39-musllinux_1_1_aarch64.whl", hash = "sha256:06cf46bdff72f58645434d467bf5228080801298fbba19fe268a01b4534467f5"},
- {file = "charset_normalizer-3.3.1-cp39-cp39-musllinux_1_1_i686.whl", hash = "sha256:3c66df3f41abee950d6638adc7eac4730a306b022570f71dd0bd6ba53503ab57"},
- {file = "charset_normalizer-3.3.1-cp39-cp39-musllinux_1_1_ppc64le.whl", hash = "sha256:cd805513198304026bd379d1d516afbf6c3c13f4382134a2c526b8b854da1c2e"},
- {file = "charset_normalizer-3.3.1-cp39-cp39-musllinux_1_1_s390x.whl", hash = "sha256:9505dc359edb6a330efcd2be825fdb73ee3e628d9010597aa1aee5aa63442e97"},
- {file = "charset_normalizer-3.3.1-cp39-cp39-musllinux_1_1_x86_64.whl", hash = "sha256:31445f38053476a0c4e6d12b047b08ced81e2c7c712e5a1ad97bc913256f91b2"},
- {file = "charset_normalizer-3.3.1-cp39-cp39-win32.whl", hash = "sha256:bd28b31730f0e982ace8663d108e01199098432a30a4c410d06fe08fdb9e93f4"},
- {file = "charset_normalizer-3.3.1-cp39-cp39-win_amd64.whl", hash = "sha256:555fe186da0068d3354cdf4bbcbc609b0ecae4d04c921cc13e209eece7720727"},
- {file = "charset_normalizer-3.3.1-py3-none-any.whl", hash = "sha256:800561453acdecedaac137bf09cd719c7a440b6800ec182f077bb8e7025fb708"},
+ {file = "charset-normalizer-3.3.2.tar.gz", hash = "sha256:f30c3cb33b24454a82faecaf01b19c18562b1e89558fb6c56de4d9118a032fd5"},
+ {file = "charset_normalizer-3.3.2-cp310-cp310-macosx_10_9_universal2.whl", hash = "sha256:25baf083bf6f6b341f4121c2f3c548875ee6f5339300e08be3f2b2ba1721cdd3"},
+ {file = "charset_normalizer-3.3.2-cp310-cp310-macosx_10_9_x86_64.whl", hash = "sha256:06435b539f889b1f6f4ac1758871aae42dc3a8c0e24ac9e60c2384973ad73027"},
+ {file = "charset_normalizer-3.3.2-cp310-cp310-macosx_11_0_arm64.whl", hash = "sha256:9063e24fdb1e498ab71cb7419e24622516c4a04476b17a2dab57e8baa30d6e03"},
+ {file = "charset_normalizer-3.3.2-cp310-cp310-manylinux_2_17_aarch64.manylinux2014_aarch64.whl", hash = "sha256:6897af51655e3691ff853668779c7bad41579facacf5fd7253b0133308cf000d"},
+ {file = "charset_normalizer-3.3.2-cp310-cp310-manylinux_2_17_ppc64le.manylinux2014_ppc64le.whl", hash = "sha256:1d3193f4a680c64b4b6a9115943538edb896edc190f0b222e73761716519268e"},
+ {file = "charset_normalizer-3.3.2-cp310-cp310-manylinux_2_17_s390x.manylinux2014_s390x.whl", hash = "sha256:cd70574b12bb8a4d2aaa0094515df2463cb429d8536cfb6c7ce983246983e5a6"},
+ {file = "charset_normalizer-3.3.2-cp310-cp310-manylinux_2_17_x86_64.manylinux2014_x86_64.whl", hash = "sha256:8465322196c8b4d7ab6d1e049e4c5cb460d0394da4a27d23cc242fbf0034b6b5"},
+ {file = "charset_normalizer-3.3.2-cp310-cp310-manylinux_2_5_i686.manylinux1_i686.manylinux_2_17_i686.manylinux2014_i686.whl", hash = "sha256:a9a8e9031d613fd2009c182b69c7b2c1ef8239a0efb1df3f7c8da66d5dd3d537"},
+ {file = "charset_normalizer-3.3.2-cp310-cp310-musllinux_1_1_aarch64.whl", hash = "sha256:beb58fe5cdb101e3a055192ac291b7a21e3b7ef4f67fa1d74e331a7f2124341c"},
+ {file = "charset_normalizer-3.3.2-cp310-cp310-musllinux_1_1_i686.whl", hash = "sha256:e06ed3eb3218bc64786f7db41917d4e686cc4856944f53d5bdf83a6884432e12"},
+ {file = "charset_normalizer-3.3.2-cp310-cp310-musllinux_1_1_ppc64le.whl", hash = "sha256:2e81c7b9c8979ce92ed306c249d46894776a909505d8f5a4ba55b14206e3222f"},
+ {file = "charset_normalizer-3.3.2-cp310-cp310-musllinux_1_1_s390x.whl", hash = "sha256:572c3763a264ba47b3cf708a44ce965d98555f618ca42c926a9c1616d8f34269"},
+ {file = "charset_normalizer-3.3.2-cp310-cp310-musllinux_1_1_x86_64.whl", hash = "sha256:fd1abc0d89e30cc4e02e4064dc67fcc51bd941eb395c502aac3ec19fab46b519"},
+ {file = "charset_normalizer-3.3.2-cp310-cp310-win32.whl", hash = "sha256:3d47fa203a7bd9c5b6cee4736ee84ca03b8ef23193c0d1ca99b5089f72645c73"},
+ {file = "charset_normalizer-3.3.2-cp310-cp310-win_amd64.whl", hash = "sha256:10955842570876604d404661fbccbc9c7e684caf432c09c715ec38fbae45ae09"},
+ {file = "charset_normalizer-3.3.2-cp311-cp311-macosx_10_9_universal2.whl", hash = "sha256:802fe99cca7457642125a8a88a084cef28ff0cf9407060f7b93dca5aa25480db"},
+ {file = "charset_normalizer-3.3.2-cp311-cp311-macosx_10_9_x86_64.whl", hash = "sha256:573f6eac48f4769d667c4442081b1794f52919e7edada77495aaed9236d13a96"},
+ {file = "charset_normalizer-3.3.2-cp311-cp311-macosx_11_0_arm64.whl", hash = "sha256:549a3a73da901d5bc3ce8d24e0600d1fa85524c10287f6004fbab87672bf3e1e"},
+ {file = "charset_normalizer-3.3.2-cp311-cp311-manylinux_2_17_aarch64.manylinux2014_aarch64.whl", hash = "sha256:f27273b60488abe721a075bcca6d7f3964f9f6f067c8c4c605743023d7d3944f"},
+ {file = "charset_normalizer-3.3.2-cp311-cp311-manylinux_2_17_ppc64le.manylinux2014_ppc64le.whl", hash = "sha256:1ceae2f17a9c33cb48e3263960dc5fc8005351ee19db217e9b1bb15d28c02574"},
+ {file = "charset_normalizer-3.3.2-cp311-cp311-manylinux_2_17_s390x.manylinux2014_s390x.whl", hash = "sha256:65f6f63034100ead094b8744b3b97965785388f308a64cf8d7c34f2f2e5be0c4"},
+ {file = "charset_normalizer-3.3.2-cp311-cp311-manylinux_2_17_x86_64.manylinux2014_x86_64.whl", hash = "sha256:753f10e867343b4511128c6ed8c82f7bec3bd026875576dfd88483c5c73b2fd8"},
+ {file = "charset_normalizer-3.3.2-cp311-cp311-manylinux_2_5_i686.manylinux1_i686.manylinux_2_17_i686.manylinux2014_i686.whl", hash = "sha256:4a78b2b446bd7c934f5dcedc588903fb2f5eec172f3d29e52a9096a43722adfc"},
+ {file = "charset_normalizer-3.3.2-cp311-cp311-musllinux_1_1_aarch64.whl", hash = "sha256:e537484df0d8f426ce2afb2d0f8e1c3d0b114b83f8850e5f2fbea0e797bd82ae"},
+ {file = "charset_normalizer-3.3.2-cp311-cp311-musllinux_1_1_i686.whl", hash = "sha256:eb6904c354526e758fda7167b33005998fb68c46fbc10e013ca97f21ca5c8887"},
+ {file = "charset_normalizer-3.3.2-cp311-cp311-musllinux_1_1_ppc64le.whl", hash = "sha256:deb6be0ac38ece9ba87dea880e438f25ca3eddfac8b002a2ec3d9183a454e8ae"},
+ {file = "charset_normalizer-3.3.2-cp311-cp311-musllinux_1_1_s390x.whl", hash = "sha256:4ab2fe47fae9e0f9dee8c04187ce5d09f48eabe611be8259444906793ab7cbce"},
+ {file = "charset_normalizer-3.3.2-cp311-cp311-musllinux_1_1_x86_64.whl", hash = "sha256:80402cd6ee291dcb72644d6eac93785fe2c8b9cb30893c1af5b8fdd753b9d40f"},
+ {file = "charset_normalizer-3.3.2-cp311-cp311-win32.whl", hash = "sha256:7cd13a2e3ddeed6913a65e66e94b51d80a041145a026c27e6bb76c31a853c6ab"},
+ {file = "charset_normalizer-3.3.2-cp311-cp311-win_amd64.whl", hash = "sha256:663946639d296df6a2bb2aa51b60a2454ca1cb29835324c640dafb5ff2131a77"},
+ {file = "charset_normalizer-3.3.2-cp312-cp312-macosx_10_9_universal2.whl", hash = "sha256:0b2b64d2bb6d3fb9112bafa732def486049e63de9618b5843bcdd081d8144cd8"},
+ {file = "charset_normalizer-3.3.2-cp312-cp312-macosx_10_9_x86_64.whl", hash = "sha256:ddbb2551d7e0102e7252db79ba445cdab71b26640817ab1e3e3648dad515003b"},
+ {file = "charset_normalizer-3.3.2-cp312-cp312-macosx_11_0_arm64.whl", hash = "sha256:55086ee1064215781fff39a1af09518bc9255b50d6333f2e4c74ca09fac6a8f6"},
+ {file = "charset_normalizer-3.3.2-cp312-cp312-manylinux_2_17_aarch64.manylinux2014_aarch64.whl", hash = "sha256:8f4a014bc36d3c57402e2977dada34f9c12300af536839dc38c0beab8878f38a"},
+ {file = "charset_normalizer-3.3.2-cp312-cp312-manylinux_2_17_ppc64le.manylinux2014_ppc64le.whl", hash = "sha256:a10af20b82360ab00827f916a6058451b723b4e65030c5a18577c8b2de5b3389"},
+ {file = "charset_normalizer-3.3.2-cp312-cp312-manylinux_2_17_s390x.manylinux2014_s390x.whl", hash = "sha256:8d756e44e94489e49571086ef83b2bb8ce311e730092d2c34ca8f7d925cb20aa"},
+ {file = "charset_normalizer-3.3.2-cp312-cp312-manylinux_2_17_x86_64.manylinux2014_x86_64.whl", hash = "sha256:90d558489962fd4918143277a773316e56c72da56ec7aa3dc3dbbe20fdfed15b"},
+ {file = "charset_normalizer-3.3.2-cp312-cp312-manylinux_2_5_i686.manylinux1_i686.manylinux_2_17_i686.manylinux2014_i686.whl", hash = "sha256:6ac7ffc7ad6d040517be39eb591cac5ff87416c2537df6ba3cba3bae290c0fed"},
+ {file = "charset_normalizer-3.3.2-cp312-cp312-musllinux_1_1_aarch64.whl", hash = "sha256:7ed9e526742851e8d5cc9e6cf41427dfc6068d4f5a3bb03659444b4cabf6bc26"},
+ {file = "charset_normalizer-3.3.2-cp312-cp312-musllinux_1_1_i686.whl", hash = "sha256:8bdb58ff7ba23002a4c5808d608e4e6c687175724f54a5dade5fa8c67b604e4d"},
+ {file = "charset_normalizer-3.3.2-cp312-cp312-musllinux_1_1_ppc64le.whl", hash = "sha256:6b3251890fff30ee142c44144871185dbe13b11bab478a88887a639655be1068"},
+ {file = "charset_normalizer-3.3.2-cp312-cp312-musllinux_1_1_s390x.whl", hash = "sha256:b4a23f61ce87adf89be746c8a8974fe1c823c891d8f86eb218bb957c924bb143"},
+ {file = "charset_normalizer-3.3.2-cp312-cp312-musllinux_1_1_x86_64.whl", hash = "sha256:efcb3f6676480691518c177e3b465bcddf57cea040302f9f4e6e191af91174d4"},
+ {file = "charset_normalizer-3.3.2-cp312-cp312-win32.whl", hash = "sha256:d965bba47ddeec8cd560687584e88cf699fd28f192ceb452d1d7ee807c5597b7"},
+ {file = "charset_normalizer-3.3.2-cp312-cp312-win_amd64.whl", hash = "sha256:96b02a3dc4381e5494fad39be677abcb5e6634bf7b4fa83a6dd3112607547001"},
+ {file = "charset_normalizer-3.3.2-cp37-cp37m-macosx_10_9_x86_64.whl", hash = "sha256:95f2a5796329323b8f0512e09dbb7a1860c46a39da62ecb2324f116fa8fdc85c"},
+ {file = "charset_normalizer-3.3.2-cp37-cp37m-manylinux_2_17_aarch64.manylinux2014_aarch64.whl", hash = "sha256:c002b4ffc0be611f0d9da932eb0f704fe2602a9a949d1f738e4c34c75b0863d5"},
+ {file = "charset_normalizer-3.3.2-cp37-cp37m-manylinux_2_17_ppc64le.manylinux2014_ppc64le.whl", hash = "sha256:a981a536974bbc7a512cf44ed14938cf01030a99e9b3a06dd59578882f06f985"},
+ {file = "charset_normalizer-3.3.2-cp37-cp37m-manylinux_2_17_s390x.manylinux2014_s390x.whl", hash = "sha256:3287761bc4ee9e33561a7e058c72ac0938c4f57fe49a09eae428fd88aafe7bb6"},
+ {file = "charset_normalizer-3.3.2-cp37-cp37m-manylinux_2_17_x86_64.manylinux2014_x86_64.whl", hash = "sha256:42cb296636fcc8b0644486d15c12376cb9fa75443e00fb25de0b8602e64c1714"},
+ {file = "charset_normalizer-3.3.2-cp37-cp37m-manylinux_2_5_i686.manylinux1_i686.manylinux_2_17_i686.manylinux2014_i686.whl", hash = "sha256:0a55554a2fa0d408816b3b5cedf0045f4b8e1a6065aec45849de2d6f3f8e9786"},
+ {file = "charset_normalizer-3.3.2-cp37-cp37m-musllinux_1_1_aarch64.whl", hash = "sha256:c083af607d2515612056a31f0a8d9e0fcb5876b7bfc0abad3ecd275bc4ebc2d5"},
+ {file = "charset_normalizer-3.3.2-cp37-cp37m-musllinux_1_1_i686.whl", hash = "sha256:87d1351268731db79e0f8e745d92493ee2841c974128ef629dc518b937d9194c"},
+ {file = "charset_normalizer-3.3.2-cp37-cp37m-musllinux_1_1_ppc64le.whl", hash = "sha256:bd8f7df7d12c2db9fab40bdd87a7c09b1530128315d047a086fa3ae3435cb3a8"},
+ {file = "charset_normalizer-3.3.2-cp37-cp37m-musllinux_1_1_s390x.whl", hash = "sha256:c180f51afb394e165eafe4ac2936a14bee3eb10debc9d9e4db8958fe36afe711"},
+ {file = "charset_normalizer-3.3.2-cp37-cp37m-musllinux_1_1_x86_64.whl", hash = "sha256:8c622a5fe39a48f78944a87d4fb8a53ee07344641b0562c540d840748571b811"},
+ {file = "charset_normalizer-3.3.2-cp37-cp37m-win32.whl", hash = "sha256:db364eca23f876da6f9e16c9da0df51aa4f104a972735574842618b8c6d999d4"},
+ {file = "charset_normalizer-3.3.2-cp37-cp37m-win_amd64.whl", hash = "sha256:86216b5cee4b06df986d214f664305142d9c76df9b6512be2738aa72a2048f99"},
+ {file = "charset_normalizer-3.3.2-cp38-cp38-macosx_10_9_universal2.whl", hash = "sha256:6463effa3186ea09411d50efc7d85360b38d5f09b870c48e4600f63af490e56a"},
+ {file = "charset_normalizer-3.3.2-cp38-cp38-macosx_10_9_x86_64.whl", hash = "sha256:6c4caeef8fa63d06bd437cd4bdcf3ffefe6738fb1b25951440d80dc7df8c03ac"},
+ {file = "charset_normalizer-3.3.2-cp38-cp38-macosx_11_0_arm64.whl", hash = "sha256:37e55c8e51c236f95b033f6fb391d7d7970ba5fe7ff453dad675e88cf303377a"},
+ {file = "charset_normalizer-3.3.2-cp38-cp38-manylinux_2_17_aarch64.manylinux2014_aarch64.whl", hash = "sha256:fb69256e180cb6c8a894fee62b3afebae785babc1ee98b81cdf68bbca1987f33"},
+ {file = "charset_normalizer-3.3.2-cp38-cp38-manylinux_2_17_ppc64le.manylinux2014_ppc64le.whl", hash = "sha256:ae5f4161f18c61806f411a13b0310bea87f987c7d2ecdbdaad0e94eb2e404238"},
+ {file = "charset_normalizer-3.3.2-cp38-cp38-manylinux_2_17_s390x.manylinux2014_s390x.whl", hash = "sha256:b2b0a0c0517616b6869869f8c581d4eb2dd83a4d79e0ebcb7d373ef9956aeb0a"},
+ {file = "charset_normalizer-3.3.2-cp38-cp38-manylinux_2_17_x86_64.manylinux2014_x86_64.whl", hash = "sha256:45485e01ff4d3630ec0d9617310448a8702f70e9c01906b0d0118bdf9d124cf2"},
+ {file = "charset_normalizer-3.3.2-cp38-cp38-manylinux_2_5_i686.manylinux1_i686.manylinux_2_17_i686.manylinux2014_i686.whl", hash = "sha256:eb00ed941194665c332bf8e078baf037d6c35d7c4f3102ea2d4f16ca94a26dc8"},
+ {file = "charset_normalizer-3.3.2-cp38-cp38-musllinux_1_1_aarch64.whl", hash = "sha256:2127566c664442652f024c837091890cb1942c30937add288223dc895793f898"},
+ {file = "charset_normalizer-3.3.2-cp38-cp38-musllinux_1_1_i686.whl", hash = "sha256:a50aebfa173e157099939b17f18600f72f84eed3049e743b68ad15bd69b6bf99"},
+ {file = "charset_normalizer-3.3.2-cp38-cp38-musllinux_1_1_ppc64le.whl", hash = "sha256:4d0d1650369165a14e14e1e47b372cfcb31d6ab44e6e33cb2d4e57265290044d"},
+ {file = "charset_normalizer-3.3.2-cp38-cp38-musllinux_1_1_s390x.whl", hash = "sha256:923c0c831b7cfcb071580d3f46c4baf50f174be571576556269530f4bbd79d04"},
+ {file = "charset_normalizer-3.3.2-cp38-cp38-musllinux_1_1_x86_64.whl", hash = "sha256:06a81e93cd441c56a9b65d8e1d043daeb97a3d0856d177d5c90ba85acb3db087"},
+ {file = "charset_normalizer-3.3.2-cp38-cp38-win32.whl", hash = "sha256:6ef1d82a3af9d3eecdba2321dc1b3c238245d890843e040e41e470ffa64c3e25"},
+ {file = "charset_normalizer-3.3.2-cp38-cp38-win_amd64.whl", hash = "sha256:eb8821e09e916165e160797a6c17edda0679379a4be5c716c260e836e122f54b"},
+ {file = "charset_normalizer-3.3.2-cp39-cp39-macosx_10_9_universal2.whl", hash = "sha256:c235ebd9baae02f1b77bcea61bce332cb4331dc3617d254df3323aa01ab47bd4"},
+ {file = "charset_normalizer-3.3.2-cp39-cp39-macosx_10_9_x86_64.whl", hash = "sha256:5b4c145409bef602a690e7cfad0a15a55c13320ff7a3ad7ca59c13bb8ba4d45d"},
+ {file = "charset_normalizer-3.3.2-cp39-cp39-macosx_11_0_arm64.whl", hash = "sha256:68d1f8a9e9e37c1223b656399be5d6b448dea850bed7d0f87a8311f1ff3dabb0"},
+ {file = "charset_normalizer-3.3.2-cp39-cp39-manylinux_2_17_aarch64.manylinux2014_aarch64.whl", hash = "sha256:22afcb9f253dac0696b5a4be4a1c0f8762f8239e21b99680099abd9b2b1b2269"},
+ {file = "charset_normalizer-3.3.2-cp39-cp39-manylinux_2_17_ppc64le.manylinux2014_ppc64le.whl", hash = "sha256:e27ad930a842b4c5eb8ac0016b0a54f5aebbe679340c26101df33424142c143c"},
+ {file = "charset_normalizer-3.3.2-cp39-cp39-manylinux_2_17_s390x.manylinux2014_s390x.whl", hash = "sha256:1f79682fbe303db92bc2b1136016a38a42e835d932bab5b3b1bfcfbf0640e519"},
+ {file = "charset_normalizer-3.3.2-cp39-cp39-manylinux_2_17_x86_64.manylinux2014_x86_64.whl", hash = "sha256:b261ccdec7821281dade748d088bb6e9b69e6d15b30652b74cbbac25e280b796"},
+ {file = "charset_normalizer-3.3.2-cp39-cp39-manylinux_2_5_i686.manylinux1_i686.manylinux_2_17_i686.manylinux2014_i686.whl", hash = "sha256:122c7fa62b130ed55f8f285bfd56d5f4b4a5b503609d181f9ad85e55c89f4185"},
+ {file = "charset_normalizer-3.3.2-cp39-cp39-musllinux_1_1_aarch64.whl", hash = "sha256:d0eccceffcb53201b5bfebb52600a5fb483a20b61da9dbc885f8b103cbe7598c"},
+ {file = "charset_normalizer-3.3.2-cp39-cp39-musllinux_1_1_i686.whl", hash = "sha256:9f96df6923e21816da7e0ad3fd47dd8f94b2a5ce594e00677c0013018b813458"},
+ {file = "charset_normalizer-3.3.2-cp39-cp39-musllinux_1_1_ppc64le.whl", hash = "sha256:7f04c839ed0b6b98b1a7501a002144b76c18fb1c1850c8b98d458ac269e26ed2"},
+ {file = "charset_normalizer-3.3.2-cp39-cp39-musllinux_1_1_s390x.whl", hash = "sha256:34d1c8da1e78d2e001f363791c98a272bb734000fcef47a491c1e3b0505657a8"},
+ {file = "charset_normalizer-3.3.2-cp39-cp39-musllinux_1_1_x86_64.whl", hash = "sha256:ff8fa367d09b717b2a17a052544193ad76cd49979c805768879cb63d9ca50561"},
+ {file = "charset_normalizer-3.3.2-cp39-cp39-win32.whl", hash = "sha256:aed38f6e4fb3f5d6bf81bfa990a07806be9d83cf7bacef998ab1a9bd660a581f"},
+ {file = "charset_normalizer-3.3.2-cp39-cp39-win_amd64.whl", hash = "sha256:b01b88d45a6fcb69667cd6d2f7a9aeb4bf53760d7fc536bf679ec94fe9f3ff3d"},
+ {file = "charset_normalizer-3.3.2-py3-none-any.whl", hash = "sha256:3e4d1f6587322d2788836a99c69062fbb091331ec940e02d12d179c1d53e25fc"},
]
[[package]]
diff --git a/pyproject.toml b/pyproject.toml
index c51a57c2..b0057fd1 100644
--- a/pyproject.toml
+++ b/pyproject.toml
@@ -5,7 +5,7 @@ description = "Boost security in your dev lifecycle via SAST, SCA, Secrets & IaC
keywords=["secret-scan", "cycode", "devops", "token", "secret", "security", "cycode", "code"]
authors = ["Cycode "]
license = "MIT"
-repository = "https://github.com/cycodehq-public/cycode-cli"
+repository = "https://github.com/cycodehq/cycode-cli"
readme = "README.md"
classifiers = [
"Development Status :: 5 - Production/Stable",
From 774d731b48a7b1ab6ea53ec8ccc8105935c20f70 Mon Sep 17 00:00:00 2001
From: Ilya Siamionau
Date: Mon, 20 Nov 2023 16:07:34 +0100
Subject: [PATCH 046/257] CM-28796 - Update the CLI documentation regarding
committing config file with ignores to repo (#177)
---
README.md | 237 ++++++++++++++++++++++++++++++++++++------------------
1 file changed, 159 insertions(+), 78 deletions(-)
diff --git a/README.md b/README.md
index e1efe9d9..301e8944 100644
--- a/README.md
+++ b/README.md
@@ -9,8 +9,8 @@ This guide will guide you through both installation and usage.
1. [Prerequisites](#prerequisites)
2. [Installation](#installation)
1. [Install Cycode CLI](#install-cycode-cli)
- 1. [Use `auth` command](#use-auth-command)
- 2. [Use `configure` command](#use-configure-command)
+ 1. [Using the Auth Command](#using-the-auth-command)
+ 2. [Using the Configure Command](#using-the-configure-command)
3. [Add to Environment Variables](#add-to-environment-variables)
1. [On Unix/Linux](#on-unixlinux)
2. [On Windows](#on-windows)
@@ -44,22 +44,22 @@ This guide will guide you through both installation and usage.
3. [Ignoring a Path](#ignoring-a-path)
4. [Ignoring a Secret, IaC, or SCA Rule](#ignoring-a-secret-iac-sca-or-sast-rule)
5. [Ignoring a Package](#ignoring-a-package)
+ 6. [Ignoring using config file](#ignoring-using-config-file)
5. [Report command](#report-command)
- 1. [Generating Report](#generating-report)
- 2. [Report Result](#report-results)
+ 1. [Generating SBOM Report](#generating-sbom-report)
6. [Syntax Help](#syntax-help)
# Prerequisites
- The Cycode CLI application requires Python version 3.7 or later.
-- Use the [`cycode auth` command](#use-auth-command) to authenticate to Cycode with the CLI
+- Use the [`cycode auth` command](#using-the-auth-command) to authenticate to Cycode with the CLI
- Alternatively, you can obtain a Cycode Client ID and Client Secret Key by following the steps detailed in the [Service Account Token](https://docs.cycode.com/reference/creating-a-service-account-access-token) and [Personal Access Token](https://docs.cycode.com/reference/creating-a-personal-access-token-1) pages, which contain details on obtaining these values.
# Installation
The following installation steps are applicable to both Windows and UNIX / Linux operating systems.
-> :memo: **Note**
+> [!NOTE]
> The following steps assume the use of `python3` and `pip3` for Python-related commands; however, some systems may instead use the `python` and `pip` commands, depending on your Python environment’s configuration.
## Install Cycode CLI
@@ -76,13 +76,13 @@ To install the Cycode CLI application on your local machine, perform the followi
4. There are three methods to set the Cycode client ID and client secret:
- - [cycode auth](#use-auth-command) (**Recommended**)
- - [cycode configure](#use-configure-command)
+ - [cycode auth](#using-the-auth-command) (**Recommended**)
+ - [cycode configure](#using-the-configure-command)
- Add them to your [environment variables](#add-to-environment-variables)
-### Useing the Auth Command
+### Using the Auth Command
-> :memo: **Note**
+> [!NOTE]
> This is the **recommended** method for setting up your local machine to authenticate with Cycode CLI.
1. Type the following command into your terminal/command line window:
@@ -91,24 +91,24 @@ To install the Cycode CLI application on your local machine, perform the followi
2. A browser window will appear, asking you to log into Cycode (as seen below):
-
+ 
3. Enter your login credentials on this page and log in.
4. You will eventually be taken to the page below, where you'll be asked to choose the business group you want to authorize Cycode with (if applicable):
-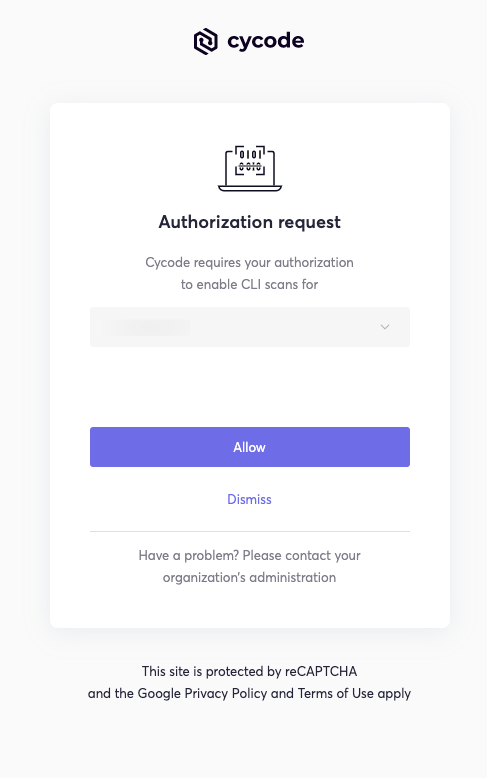
+ 
-> :memo: **Note**
-> This will be the default method for authenticating with the Cycode CLI.
+ > [!NOTE]
+ > This will be the default method for authenticating with the Cycode CLI.
5. Click the **Allow** button to authorize the Cycode CLI on the selected business group.
-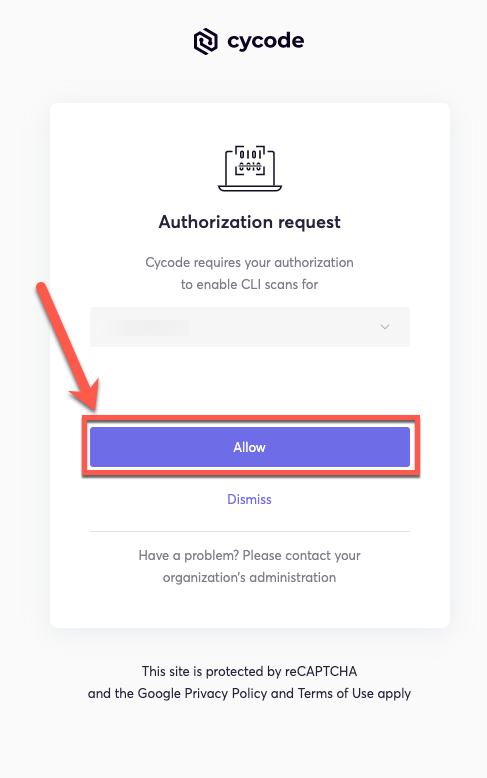
+ 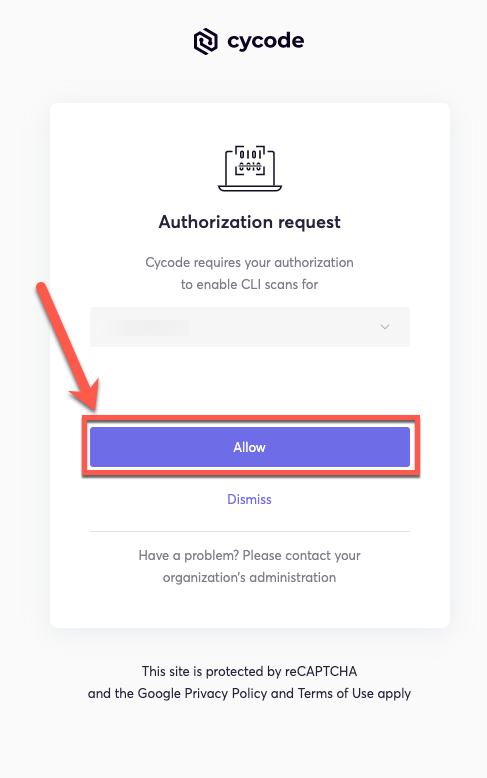
6. Once completed, you'll see the following screen, if it was selected successfully:
-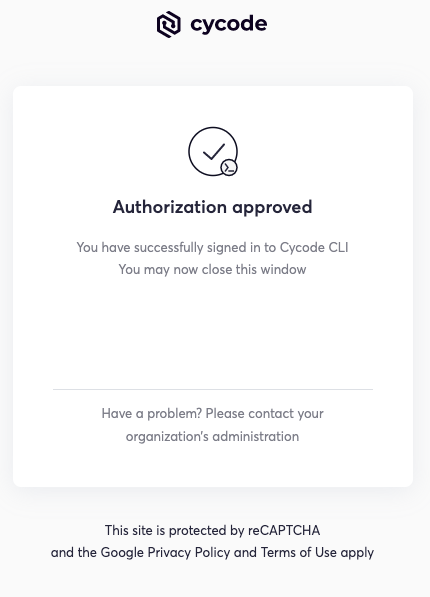
+ 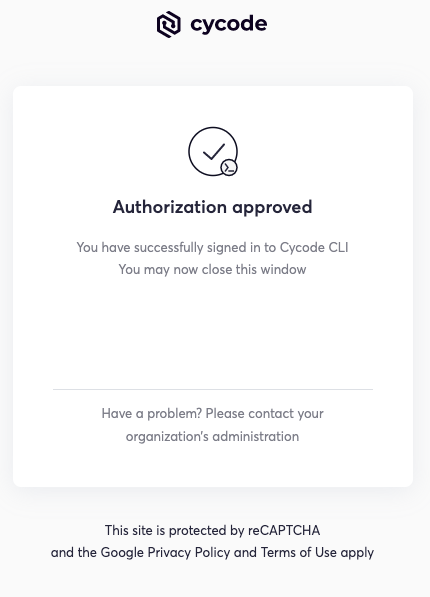
7. In the terminal/command line screen, you will see the following when exiting the browser window:
@@ -118,7 +118,7 @@ To install the Cycode CLI application on your local machine, perform the followi
### Using the Configure Command
-> :memo: **Note**
+> [!NOTE]
> If you already set up your Cycode Client ID and Client Secret through the Linux or Windows environment variables, those credentials will take precedent over this method.
1. Type the following command into your terminal/command line window:
@@ -177,19 +177,19 @@ export CYCODE_CLIENT_SECRET={your Cycode Secret Key}
1. From the Control Panel, navigate to the System menu:
-
+ 
2. Next, click Advanced system settings:
-
+ 
3. In the System Properties window that opens, click the Environment Variables button:
-
+ 
4. Create `CYCODE_CLIENT_ID` and `CYCODE_CLIENT_SECRET` variables with values matching your ID and Secret Key, respectively:
-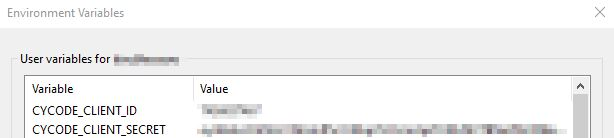
+ 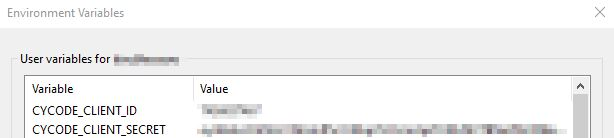
5. Insert the cycode.exe into the path to complete the installation.
@@ -207,21 +207,21 @@ Perform the following steps to install the pre-commit hook:
3. Create a new YAML file named `.pre-commit-config.yaml` (include the beginning `.`) in the repository’s top directory that contains the following:
-```yaml
-repos:
- - repo: https://github.com/cycodehq/cycode-cli
- rev: v1.4.0
- hooks:
- - id: cycode
- stages:
- - commit
-```
+ ```yaml
+ repos:
+ - repo: https://github.com/cycodehq/cycode-cli
+ rev: v1.4.0
+ hooks:
+ - id: cycode
+ stages:
+ - commit
+ ```
4. Install Cycode’s hook:
`pre-commit install`
-> :memo: **Note**
+> [!NOTE]
> A successful hook installation will result in the message:
`Pre-commit installed at .git/hooks/pre-commit`
@@ -235,14 +235,14 @@ The following are the options and commands available with the Cycode CLI applica
| `-v`, `--verbose` | Show detailed logs. |
| `--help` | Show options for given command. |
-| Command | Description |
-|-------------------------------------|---------------------------------------------------------------------------------------------------------------------------------------|
-| [auth](#use-auth-command) | Authenticates your machine to associate CLI with your Cycode account. |
-| [configure](#use-configure-command) | Initial command to authenticate your CLI client with Cycode using client ID and client secret. |
-| [ignore](#ingoring-scan-results) | Ignore a specific value, path or rule ID. |
-| [scan](#running-a-scan) | Scan content for secrets/IaC/SCA/SAST violations. You need to specify which scan type: `ci`/`commit_history`/`path`/`repository`/etc. |
-| [report](#running-a-report) | Generate report for SCA SBOM. |
-| version | Show the version and exit. |
+| Command | Description |
+|-------------------------------------------|---------------------------------------------------------------------------------------------------------------------------------------|
+| [auth](#using-the-auth-command) | Authenticates your machine to associate CLI with your Cycode account. |
+| [configure](#using-the-configure-command) | Initial command to authenticate your CLI client with Cycode using client ID and client secret. |
+| [ignore](#ignoring-scan-results) | Ignore a specific value, path or rule ID. |
+| [scan](#running-a-scan) | Scan content for secrets/IaC/SCA/SAST violations. You need to specify which scan type: `ci`/`commit_history`/`path`/`repository`/etc. |
+| [report](#report-command) | Generate report for SCA SBOM. |
+| version | Show the version and exit. |
# Scan Command
@@ -285,8 +285,8 @@ For example, consider a scenario in which you want to scan your repository store
The following option is available for use with this command:
-| Option | Description |
-|---------------------|-------------|
+| Option | Description |
+|---------------------|--------------------------------------------------------|
| `-b, --branch TEXT` | Branch to scan, if not set scanning the default branch |
#### Branch Option
@@ -303,7 +303,7 @@ or:
### Monitor Option
-> :memo: **Note**
+> [!NOTE]
> This option is only available to SCA scans.
To push scan results tied to the [SCA policies](https://docs.cycode.com/docs/sca-policies) found in an SCA type scan to Cycode's knowledge graph, add the argument `--monitor` to the scan command.
@@ -318,12 +318,12 @@ or:
When using this option, the scan results from this scan will appear in the knowledge graph, which can be found [here](https://app.cycode.com/query-builder).
-> :warning: **NOTE**
+> [!WARNING]
> You must be an `owner` or an `admin` in Cycode to view the knowledge graph page.
### Report Option
-> :memo: **Note**
+> [!NOTE]
> This option is only available to SCA scans.
To push scan results tied to the [SCA policies](https://docs.cycode.com/docs/sca-policies) found in the Repository scan to Cycode, add the argument `--report` to the scan command.
@@ -386,7 +386,7 @@ The report page will look something like below:
### Package Vulnerabilities Option
-> :memo: **Note**
+> [!NOTE]
> This option is only available to SCA scans.
To scan a specific package vulnerability of your local repository, add the argument `--sca-scan package-vulnerabilities` following the `-t sca` or `--scan-type sca` option.
@@ -401,7 +401,7 @@ or:
#### License Compliance Option
-> :memo: **Note**
+> [!NOTE]
> This option is only available to SCA scans.
To scan a specific branch of your local repository, add the argument `--sca-scan license-compliance` followed by the name of the branch you wish to scan.
@@ -416,7 +416,7 @@ or:
#### Severity Threshold
-> :memo: **Note**
+> [!NOTE]
> This option is only available to SCA scans.
To limit the results of the `sca` scan to a specific severity threshold, add the argument `--severity-threshold` to the scan command.
@@ -448,29 +448,24 @@ Cycode CLI supports Terraform plan scanning (supporting Terraform 0.12 and later
Terraform plan file must be in JSON format (having `.json` extension)
-
_How to generate a Terraform plan from Terraform configuration file?_
1. Initialize a working directory that contains Terraform configuration file:
`terraform init`
-
2. Create Terraform execution plan and save the binary output:
`terraform plan -out={tfplan_output}`
-
3. Convert the binary output file into readable JSON:
`terraform show -json {tfplan_output} > {tfplan}.json`
-
4. Scan your `{tfplan}.json` with Cycode CLI:
`cycode scan -t iac path ~/PATH/TO/YOUR/{tfplan}.json`
-
### Commit History Scan
A commit history scan is limited to a local repository’s previous commits, focused on finding any secrets within the commit history, instead of examining the repository’s current state.
@@ -485,8 +480,8 @@ For example, consider a scenario in which you want to scan the commit history fo
The following options are available for use with this command:
-| Option | Description |
-|---------------------------|-------------|
+| Option | Description |
+|---------------------------|----------------------------------------------------------------------------------------------------------|
| `-r, --commit_range TEXT` | Scan a commit range in this git repository, by default cycode scans all commit history (example: HEAD~1) |
#### Commit Range Option
@@ -608,15 +603,15 @@ Ignore rules can be added to ignore specific secret values, specific SHA512 valu
The following are the options available for the `cycode ignore` command:
-| Option | Description |
-|---------------------------------|-------------|
-| `--by-value TEXT` | Ignore a specific value while scanning for secrets. See [Ignoring a Secret Value](#ignoring-a-secret-value) for more details. |
-| `--by-sha TEXT` | Ignore a specific SHA512 representation of a string while scanning for secrets. See [Ignoring a Secret SHA Value](#ignoring-a-secret-sha-value) for more details. |
-| `--by-path TEXT` | Avoid scanning a specific path. Need to specify scan type. See [Ignoring a Path](#ignoring-a-path) for more details. |
-| `--by-rule TEXT` | Ignore scanning a specific secret rule ID/IaC rule ID/SCA rule ID. See [Ignoring a Secret or Iac Rule](#ignoring-a-secret-or-iac-rule) for more details. |
-| `--by-package TEXT` | Ignore scanning a specific package version while running an SCA scan. Expected pattern - `name@version`. See [Ignoring a Package](#ignoring-a-package) for more details. |
-| `-t, --scan-type [secret\|iac\|sca\|sast]` | Specify the scan you wish to execute (`secret`/`iac`/`sca`/`sast`), The default value is `secret` |
-| `-g, --global` | Add an ignore rule and update it in the global `.cycode` config file |
+| Option | Description |
+|--------------------------------------------|--------------------------------------------------------------------------------------------------------------------------------------------------------------------------|
+| `--by-value TEXT` | Ignore a specific value while scanning for secrets. See [Ignoring a Secret Value](#ignoring-a-secret-value) for more details. |
+| `--by-sha TEXT` | Ignore a specific SHA512 representation of a string while scanning for secrets. See [Ignoring a Secret SHA Value](#ignoring-a-secret-sha-value) for more details. |
+| `--by-path TEXT` | Avoid scanning a specific path. Need to specify scan type. See [Ignoring a Path](#ignoring-a-path) for more details. |
+| `--by-rule TEXT` | Ignore scanning a specific secret rule ID/IaC rule ID/SCA rule ID. See [Ignoring a Secret or Iac Rule](#ignoring-a-secret-iac-sca-or-sast-rule) for more details. |
+| `--by-package TEXT` | Ignore scanning a specific package version while running an SCA scan. Expected pattern - `name@version`. See [Ignoring a Package](#ignoring-a-package) for more details. |
+| `-t, --scan-type [secret\|iac\|sca\|sast]` | Specify the scan you wish to execute (`secret`/`iac`/`sca`/`sast`), The default value is `secret` |
+| `-g, --global` | Add an ignore rule and update it in the global `.cycode` config file |
In the following example, a pre-commit scan runs and finds the following:
@@ -628,7 +623,7 @@ Secret SHA: a44081db3296c84b82d12a35c446a3cba19411dddfa0380134c75f7b3973bff0
2 | \ No newline at end of file
```
-If this is a value that is not a valid secret, then use the the `cycode ignore` command to ignore the secret by its value, SHA value, specific path, or rule ID. If this is an IaC scan, then you can ignore that result by its path or rule ID.
+If this is a value that is not a valid secret, then use the `cycode ignore` command to ignore the secret by its value, SHA value, specific path, or rule ID. If this is an IaC scan, then you can ignore that result by its path or rule ID.
### Ignoring a Secret Value
@@ -712,7 +707,7 @@ In the example above, replace the `dc21bc6b-9f4f-46fb-9f92-e4327ea03f6b` value w
### Ignoring a Package
-> :memo: **Note**
+> [!NOTE]
> This option is only available to the SCA scans.
To ignore a specific package in the SCA scans, you will need to use the `--by-package` flag in conjunction with the `-t, --scan-type` flag (you must specify the `sca` scan type). This will ignore the given package, using the `{{package_name}}@{{package_version}}` formatting, from all future scans. Use the following command to add a package and version to be ignored:
@@ -729,6 +724,90 @@ In the example below, the command to ignore a specific SCA package is as follows
In the example above, replace `pyyaml` with package name and `5.3.1` with the package version you want to ignore.
+### Ignoring using config file
+
+The applied ignoring rules are stored in the configuration file called `config.yaml`.
+This file could be easily shared between developers or even committed to remote Git.
+These files are always located in the `.cycode` folder.
+The folder starts with a dot (.), and you should enable the displaying of hidden files to see it.
+
+#### Path of the config files
+
+By default, all `cycode ignore` commands save the ignoring rule to the current directory from which CLI has been run.
+
+Example: running ignoring CLI command from `/Users/name/projects/backend` will create `config.yaml` in `/Users/name/projects/backend/.cycode`
+
+```shell
+➜ backend pwd
+/Users/name/projects/backend
+➜ backend cycode ignore --by-value test-value
+➜ backend tree -a
+.
+└── .cycode
+ └── config.yaml
+
+2 directories, 1 file
+```
+
+The second option is to save ignoring rules to the global configuration files.
+The path of the global config is `~/.cycode/config.yaml`,
+where `~` means user\`s home directory, for example, `/Users/name` on macOS.
+
+Saving to the global space could be performed with the `-g` flag of the `cycode ignore` command.
+For example: `cycode ignore -g --by-value test-value`.
+
+#### Proper working directory
+
+This is incredibly important to place the `.cycode` folder and run CLI from the same place.
+You should double-check it when working with different environments like CI/CD (GitHub Actions, Jenkins, etc.).
+
+You could commit the `.cycode` folder to the root of your repository.
+In this scenario, you must run CLI scans from the repository root.
+If it doesn't fit your requirements, you could temporarily copy the `.cycode` folder
+wherever you want and perform a CLI scan from this folder.
+
+#### Structure ignoring rules in the config
+
+It's important to understand how CLI stores ignore rules to be able to read these configuration files or even modify them without CLI.
+
+The abstract YAML structure:
+```yaml
+exclusions:
+ *scanTypeName*:
+ *ignoringType:
+ - *ignoringValue1*
+ - *ignoringValue2*
+```
+
+Possible values of `scanTypeName`: `iac`, `sca`, `sast`, `secret`.
+Possible values of `ignoringType`: `paths`, `values`, `rules`, `packages`, `shas`.
+
+> [!WARNING]
+> Values for "ignore by value" are not stored as plain text!
+> CLI stores sha256 hashes of the values instead.
+> You should put hashes of the string when modifying the configuration file by hand.
+
+Example of real `config.yaml`:
+```yaml
+exclusions:
+ iac:
+ rules:
+ - bdaa88e2-5e7c-46ff-ac2a-29721418c59c
+ sca:
+ packages:
+ - pyyaml@5.3.1
+ secret:
+ paths:
+ - /Users/name/projects/build
+ rules:
+ - ce3a4de0-9dfc-448b-a004-c538cf8b4710
+ shas:
+ - a44081db3296c84b82d12a35c446a3cba19411dddfa0380134c75f7b3973bff0
+ values:
+ - a665a45920422f9d417e4867efdc4fb8a04a1f3fff1fa07e998e86f7f7a27ae3
+ - 60303ae22b998861bce3b28f33eec1be758a213c86c93c076dbe9f558c11c752
+```
+
# Report Command
## Generating SBOM Report
@@ -737,19 +816,21 @@ A software bill of materials (SBOM) is an inventory of all constituent component
Using this command you can create an SBOM report for your local project or for your repository URI.
The following options are available for use with this command:
-| Option | Description | Required | Default |
-|---------------------|-------------|----------|---------|
-| `-f, --format [spdx-2.2\|spdx-2.3\|cyclonedx-1.4]` | SBOM format | Yes | |
-| `-o, --output-format [JSON]` | Specify the output file format | No | json |
-| `--output-file PATH` | Output file | No | autogenerated filename saved to the current directory |
-| `--include-vulnerabilities` | Include vulnerabilities | No | False |
-| `--include-dev-dependencies` | Include dev dependencies | No | False |
-
-The following commands are available for use with this command:
-| Command | Description |
-|---------------------|-------------|
-| `path` | Generate SBOM report for provided path in the command |
-| `repository_url` | Generate SBOM report for provided repository URI in the command |
+
+| Option | Description | Required | Default |
+|----------------------------------------------------|--------------------------------|----------|-------------------------------------------------------|
+| `-f, --format [spdx-2.2\|spdx-2.3\|cyclonedx-1.4]` | SBOM format | Yes | |
+| `-o, --output-format [JSON]` | Specify the output file format | No | json |
+| `--output-file PATH` | Output file | No | autogenerated filename saved to the current directory |
+| `--include-vulnerabilities` | Include vulnerabilities | No | False |
+| `--include-dev-dependencies` | Include dev dependencies | No | False |
+
+The following commands are available for use with this command:
+
+| Command | Description |
+|------------------|-----------------------------------------------------------------|
+| `path` | Generate SBOM report for provided path in the command |
+| `repository_url` | Generate SBOM report for provided repository URI in the command |
### Repository
From eb488c4efb3bb2402884c975524d7a722a950eb4 Mon Sep 17 00:00:00 2001
From: Ilya Siamionau
Date: Wed, 29 Nov 2023 17:39:37 +0100
Subject: [PATCH 047/257] CM-26396 - Add Elixir support for SCA (#179)
---
cycode/cli/consts.py | 3 +++
1 file changed, 3 insertions(+)
diff --git a/cycode/cli/consts.py b/cycode/cli/consts.py
index 9479765e..bbae235b 100644
--- a/cycode/cli/consts.py
+++ b/cycode/cli/consts.py
@@ -79,6 +79,8 @@
'pipfile.lock',
'requirements.txt',
'setup.py',
+ 'mix.exs',
+ 'mix.lock',
)
SCA_EXCLUDED_PATHS = ('node_modules',)
@@ -97,6 +99,7 @@
'pypi_pipenv': ['Pipfile', 'Pipfile.lock'],
'pypi_requirements': ['requirements.txt'],
'pypi_setup': ['setup.py'],
+ 'hex': ['mix.exs', 'mix.lock'],
}
COMMIT_RANGE_SCAN_SUPPORTED_SCAN_TYPES = [SECRET_SCAN_TYPE, SCA_SCAN_TYPE]
From b4f510e8f70a798473deedd58cc0a785e1be1f53 Mon Sep 17 00:00:00 2001
From: Ilya Siamionau
Date: Thu, 30 Nov 2023 10:30:15 +0100
Subject: [PATCH 048/257] CM-27046 - Improve UX of SCA table with results by
grouping and sorting data (#180)
---
.../cli/printers/tables/sca_table_printer.py | 74 +++++++++++++++----
1 file changed, 60 insertions(+), 14 deletions(-)
diff --git a/cycode/cli/printers/tables/sca_table_printer.py b/cycode/cli/printers/tables/sca_table_printer.py
index 92247d41..e9c0e937 100644
--- a/cycode/cli/printers/tables/sca_table_printer.py
+++ b/cycode/cli/printers/tables/sca_table_printer.py
@@ -4,7 +4,7 @@
import click
from cycode.cli.consts import LICENSE_COMPLIANCE_POLICY_ID, PACKAGE_VULNERABILITY_POLICY_ID
-from cycode.cli.models import Detection
+from cycode.cli.models import Detection, Severity
from cycode.cli.printers.tables.table import Table
from cycode.cli.printers.tables.table_models import ColumnInfoBuilder, ColumnWidths
from cycode.cli.printers.tables.table_printer_base import TablePrinterBase
@@ -19,21 +19,21 @@
# Building must have strict order. Represents the order of the columns in the table (from left to right)
SEVERITY_COLUMN = column_builder.build(name='Severity')
REPOSITORY_COLUMN = column_builder.build(name='Repository')
-
-FILE_PATH_COLUMN = column_builder.build(name='File Path')
+CODE_PROJECT_COLUMN = column_builder.build(name='Code Project') # File path to manifest file
ECOSYSTEM_COLUMN = column_builder.build(name='Ecosystem')
-DEPENDENCY_NAME_COLUMN = column_builder.build(name='Dependency Name')
-DIRECT_DEPENDENCY_COLUMN = column_builder.build(name='Direct Dependency')
-DEVELOPMENT_DEPENDENCY_COLUMN = column_builder.build(name='Development Dependency')
-DEPENDENCY_PATHS_COLUMN = column_builder.build(name='Dependency Paths')
-
+PACKAGE_COLUMN = column_builder.build(name='Package')
CVE_COLUMNS = column_builder.build(name='CVE')
+DEPENDENCY_PATHS_COLUMN = column_builder.build(name='Dependency Paths')
UPGRADE_COLUMN = column_builder.build(name='Upgrade')
LICENSE_COLUMN = column_builder.build(name='License')
+DIRECT_DEPENDENCY_COLUMN = column_builder.build(name='Direct Dependency')
+DEVELOPMENT_DEPENDENCY_COLUMN = column_builder.build(name='Development Dependency')
+
COLUMN_WIDTHS_CONFIG: ColumnWidths = {
REPOSITORY_COLUMN: 2,
- FILE_PATH_COLUMN: 3,
+ CODE_PROJECT_COLUMN: 2,
+ PACKAGE_COLUMN: 3,
CVE_COLUMNS: 5,
UPGRADE_COLUMN: 3,
LICENSE_COLUMN: 2,
@@ -47,7 +47,7 @@ def _print_results(self, local_scan_results: List['LocalScanResult']) -> None:
table = self._get_table(policy_id)
table.set_cols_width(COLUMN_WIDTHS_CONFIG)
- for detection in detections:
+ for detection in self._sort_and_group_detections(detections):
self._enrich_table_with_values(table, detection)
self._print_summary_issues(len(detections), self._get_title(policy_id))
@@ -64,6 +64,52 @@ def _get_title(policy_id: str) -> str:
return 'Unknown'
+ @staticmethod
+ def __group_by(detections: List[Detection], details_field_name: str) -> Dict[str, List[Detection]]:
+ grouped = defaultdict(list)
+ for detection in detections:
+ grouped[detection.detection_details.get(details_field_name)].append(detection)
+ return grouped
+
+ @staticmethod
+ def __severity_sort_key(detection: Detection) -> int:
+ severity = detection.detection_details.get('advisory_severity')
+ return Severity.try_get_value(severity)
+
+ def _sort_detections_by_severity(self, detections: List[Detection]) -> List[Detection]:
+ return sorted(detections, key=self.__severity_sort_key, reverse=True)
+
+ @staticmethod
+ def __package_sort_key(detection: Detection) -> int:
+ return detection.detection_details.get('package_name')
+
+ def _sort_detections_by_package(self, detections: List[Detection]) -> List[Detection]:
+ return sorted(detections, key=self.__package_sort_key)
+
+ def _sort_and_group_detections(self, detections: List[Detection]) -> List[Detection]:
+ """Sort detections by severity and group by repository, code project and package name.
+
+ Note:
+ Code Project is path to manifest file.
+
+ Grouping by code projects also groups by ecosystem.
+ Because manifest files are unique per ecosystem.
+ """
+ result = []
+
+ # we sort detections by package name to make persist output order
+ sorted_detections = self._sort_detections_by_package(detections)
+
+ grouped_by_repository = self.__group_by(sorted_detections, 'repository_name')
+ for repository_group in grouped_by_repository.values():
+ grouped_by_code_project = self.__group_by(repository_group, 'file_name')
+ for code_project_group in grouped_by_code_project.values():
+ grouped_by_package = self.__group_by(code_project_group, 'package_name')
+ for package_group in grouped_by_package.values():
+ result.extend(self._sort_detections_by_severity(package_group))
+
+ return result
+
def _get_table(self, policy_id: str) -> Table:
table = Table()
@@ -77,9 +123,9 @@ def _get_table(self, policy_id: str) -> Table:
if self._is_git_repository():
table.add(REPOSITORY_COLUMN)
- table.add(FILE_PATH_COLUMN)
+ table.add(CODE_PROJECT_COLUMN)
table.add(ECOSYSTEM_COLUMN)
- table.add(DEPENDENCY_NAME_COLUMN)
+ table.add(PACKAGE_COLUMN)
table.add(DIRECT_DEPENDENCY_COLUMN)
table.add(DEVELOPMENT_DEPENDENCY_COLUMN)
table.add(DEPENDENCY_PATHS_COLUMN)
@@ -93,9 +139,9 @@ def _enrich_table_with_values(table: Table, detection: Detection) -> None:
table.set(SEVERITY_COLUMN, detection_details.get('advisory_severity'))
table.set(REPOSITORY_COLUMN, detection_details.get('repository_name'))
- table.set(FILE_PATH_COLUMN, detection_details.get('file_name'))
+ table.set(CODE_PROJECT_COLUMN, detection_details.get('file_name'))
table.set(ECOSYSTEM_COLUMN, detection_details.get('ecosystem'))
- table.set(DEPENDENCY_NAME_COLUMN, detection_details.get('package_name'))
+ table.set(PACKAGE_COLUMN, detection_details.get('package_name'))
table.set(DIRECT_DEPENDENCY_COLUMN, detection_details.get('is_direct_dependency_str'))
table.set(DEVELOPMENT_DEPENDENCY_COLUMN, detection_details.get('is_dev_dependency_str'))
From 91d3ea57edcb48a2f09e8ce072e1870f2e781aa8 Mon Sep 17 00:00:00 2001
From: Ilya Siamionau
Date: Mon, 4 Dec 2023 14:39:44 +0100
Subject: [PATCH 049/257] CM-29799 - Revert async flow for secrets (#181)
---
cycode/cli/code_scanner.py | 12 ++++--------
cycode/cyclient/scan_config_base.py | 6 ++----
tests/cli/test_main.py | 10 ++++++----
tests/cyclient/mocked_responses/scan_client.py | 9 +++++++++
tests/cyclient/test_scan_client.py | 8 ++++++++
5 files changed, 29 insertions(+), 16 deletions(-)
diff --git a/cycode/cli/code_scanner.py b/cycode/cli/code_scanner.py
index 5920fc80..1801d63c 100644
--- a/cycode/cli/code_scanner.py
+++ b/cycode/cli/code_scanner.py
@@ -546,13 +546,13 @@ def perform_scan(
is_commit_range: bool,
scan_parameters: dict,
) -> ZippedFileScanResult:
+ if scan_type in (consts.SCA_SCAN_TYPE, consts.SAST_SCAN_TYPE):
+ return perform_scan_async(cycode_client, zipped_documents, scan_type, scan_parameters)
+
if is_commit_range:
return cycode_client.commit_range_zipped_file_scan(scan_type, zipped_documents, scan_id)
- if scan_type == consts.INFRA_CONFIGURATION_SCAN_TYPE:
- return cycode_client.zipped_file_scan(scan_type, zipped_documents, scan_id, scan_parameters, is_git_diff)
-
- return perform_scan_async(cycode_client, zipped_documents, scan_type, scan_parameters)
+ return cycode_client.zipped_file_scan(scan_type, zipped_documents, scan_id, scan_parameters, is_git_diff)
def perform_scan_async(
@@ -1025,10 +1025,6 @@ def _map_detections_per_file(detections: List[dict]) -> List[DetectionsPerFile]:
def _get_file_name_from_detection(detection: dict) -> str:
if detection['category'] == 'SAST':
return detection['detection_details']['file_path']
- if detection['category'] == 'SecretDetection':
- file_path = detection['detection_details']['file_path']
- file_name = detection['detection_details']['file_name']
- return os.path.join(file_path, file_name)
return detection['detection_details']['file_name']
diff --git a/cycode/cyclient/scan_config_base.py b/cycode/cyclient/scan_config_base.py
index 0fffa1a2..0b791348 100644
--- a/cycode/cyclient/scan_config_base.py
+++ b/cycode/cyclient/scan_config_base.py
@@ -16,10 +16,8 @@ def get_async_scan_type(scan_type: str) -> str:
return scan_type.upper()
@staticmethod
- def get_async_entity_type(scan_type: str) -> str:
- if scan_type == 'secret':
- return 'zippedfile'
-
+ def get_async_entity_type(_: str) -> str:
+ # we are migrating to "zippedfile" entity type. will be used later
return 'repository'
@abstractmethod
diff --git a/tests/cli/test_main.py b/tests/cli/test_main.py
index aa196c0e..3f41ed6a 100644
--- a/tests/cli/test_main.py
+++ b/tests/cli/test_main.py
@@ -1,6 +1,6 @@
import json
from typing import TYPE_CHECKING
-from uuid import UUID
+from uuid import uuid4
import pytest
import responses
@@ -8,7 +8,8 @@
from cycode.cli.main import main_cli
from tests.conftest import CLI_ENV_VARS, TEST_FILES_PATH, ZIP_CONTENT_PATH
-from tests.cyclient.mocked_responses.scan_client import mock_scan_async_responses
+from tests.cyclient.mocked_responses.scan_client import mock_scan_responses
+from tests.cyclient.test_scan_client import get_zipped_file_scan_response, get_zipped_file_scan_url
_PATH_TO_SCAN = TEST_FILES_PATH.joinpath('zip_content').absolute()
@@ -28,10 +29,11 @@ def _is_json(plain: str) -> bool:
@pytest.mark.parametrize('output', ['text', 'json'])
def test_passing_output_option(output: str, scan_client: 'ScanClient', api_token_response: responses.Response) -> None:
scan_type = 'secret'
- scan_id = UUID('12345678-418f-47ee-abb0-012345678901')
+ scan_id = uuid4()
+ mock_scan_responses(responses, scan_type, scan_client, scan_id, ZIP_CONTENT_PATH)
+ responses.add(get_zipped_file_scan_response(get_zipped_file_scan_url(scan_type, scan_client), ZIP_CONTENT_PATH))
responses.add(api_token_response)
- mock_scan_async_responses(responses, scan_type, scan_client, scan_id, ZIP_CONTENT_PATH)
args = ['--output', output, 'scan', '--soft-fail', 'path', str(_PATH_TO_SCAN)]
result = CliRunner().invoke(main_cli, args, env=CLI_ENV_VARS)
diff --git a/tests/cyclient/mocked_responses/scan_client.py b/tests/cyclient/mocked_responses/scan_client.py
index 8518e2b9..dff10003 100644
--- a/tests/cyclient/mocked_responses/scan_client.py
+++ b/tests/cyclient/mocked_responses/scan_client.py
@@ -156,3 +156,12 @@ def mock_scan_async_responses(
responses_module.add(get_scan_detections_count_response(get_scan_detections_count_url(scan_client)))
responses_module.add(get_scan_detections_response(get_scan_detections_url(scan_client), scan_id, zip_content_path))
responses_module.add(get_report_scan_status_response(get_report_scan_status_url(scan_type, scan_id, scan_client)))
+
+
+def mock_scan_responses(
+ responses_module: responses, scan_type: str, scan_client: ScanClient, scan_id: UUID, zip_content_path: Path
+) -> None:
+ responses_module.add(
+ get_zipped_file_scan_response(get_zipped_file_scan_url(scan_type, scan_client), zip_content_path)
+ )
+ responses_module.add(get_report_scan_status_response(get_report_scan_status_url(scan_type, scan_id, scan_client)))
diff --git a/tests/cyclient/test_scan_client.py b/tests/cyclient/test_scan_client.py
index 1f8ed462..6df7b544 100644
--- a/tests/cyclient/test_scan_client.py
+++ b/tests/cyclient/test_scan_client.py
@@ -37,6 +37,14 @@ def get_test_zip_file(scan_type: str) -> InMemoryZip:
return zip_documents(scan_type, test_documents)
+def test_get_service_name(scan_client: ScanClient) -> None:
+ # TODO(MarshalX): get_service_name should be removed from ScanClient? Because it exists in ScanConfig
+ assert scan_client.get_service_name('secret') == 'secret'
+ assert scan_client.get_service_name('iac') == 'iac'
+ assert scan_client.get_service_name('sca') == 'scans'
+ assert scan_client.get_service_name('sast') == 'scans'
+
+
@pytest.mark.parametrize('scan_type', config['scans']['supported_scans'])
@responses.activate
def test_zipped_file_scan(scan_type: str, scan_client: ScanClient, api_token_response: responses.Response) -> None:
From 16bc696f8635f0a5650d4118a11e39bb87458822 Mon Sep 17 00:00:00 2001
From: Ilya Siamionau
Date: Wed, 6 Dec 2023 13:22:08 +0100
Subject: [PATCH 050/257] CM-29960 - Migrate all CLI commands to new project
structure (#182)
---
cycode/cli/{auth => commands}/__init__.py | 0
.../cli/commands/auth}/__init__.py | 0
.../cli/{ => commands}/auth/auth_command.py | 6 +-
.../cli/{ => commands}/auth/auth_manager.py | 0
cycode/cli/commands/main_cli.py | 79 ++++
.../cli/commands/report/sbom/path/__init__.py | 0
.../path_command.py} | 4 +-
.../report/sbom/repository_url/__init__.py | 0
.../repository_url_command.py} | 4 +-
.../cli/commands/report/sbom/sbom_command.py | 8 +-
cycode/cli/commands/scan/__init__.py | 0
.../cli/{ => commands/scan}/code_scanner.py | 364 ++++--------------
.../commands/scan/commit_history/__init__.py | 0
.../commit_history/commit_history_command.py | 24 ++
cycode/cli/commands/scan/path/__init__.py | 0
cycode/cli/commands/scan/path/path_command.py | 15 +
.../cli/commands/scan/pre_commit/__init__.py | 0
.../scan/pre_commit/pre_commit_command.py | 44 +++
.../cli/commands/scan/pre_receive/__init__.py | 0
.../scan/pre_receive/pre_receive_command.py | 62 +++
.../cli/commands/scan/repository/__init__.py | 0
.../scan/repository/repisotiry_command.py | 60 +++
cycode/cli/commands/scan/scan_ci/__init__.py | 0
.../scan/scan_ci}/ci_integrations.py | 0
.../commands/scan/scan_ci/scan_ci_command.py | 15 +
cycode/cli/commands/scan/scan_command.py | 159 ++++++++
cycode/cli/commands/version/__init__.py | 0
.../cli/commands/version/version_command.py | 22 ++
.../handle_report_sbom_errors.py} | 0
cycode/cli/exceptions/handle_scan_errors.py | 80 ++++
cycode/cli/main.py | 251 +-----------
tests/cli/commands/__init__.py | 0
tests/cli/commands/configure/__init__.py | 0
.../configure}/test_configure_command.py | 0
tests/cli/commands/scan/__init__.py | 0
.../{ => commands/scan}/test_code_scanner.py | 66 ----
.../test_main_command.py} | 2 +-
tests/cli/exceptions/__init__.py | 0
.../cli/exceptions/test_handle_scan_errors.py | 67 ++++
tests/cli/files_collector/iac/__init__.py | 0
.../iac}/test_tf_content_generator.py | 0
tests/cyclient/test_auth_client.py | 5 +-
tests/cyclient/test_scan_client.py | 2 +-
43 files changed, 711 insertions(+), 628 deletions(-)
rename cycode/cli/{auth => commands}/__init__.py (100%)
rename {tests/cli/helpers => cycode/cli/commands/auth}/__init__.py (100%)
rename cycode/cli/{ => commands}/auth/auth_command.py (95%)
rename cycode/cli/{ => commands}/auth/auth_manager.py (100%)
create mode 100644 cycode/cli/commands/main_cli.py
create mode 100644 cycode/cli/commands/report/sbom/path/__init__.py
rename cycode/cli/commands/report/sbom/{sbom_path_command.py => path/path_command.py} (94%)
create mode 100644 cycode/cli/commands/report/sbom/repository_url/__init__.py
rename cycode/cli/commands/report/sbom/{sbom_repository_url_command.py => repository_url/repository_url_command.py} (92%)
create mode 100644 cycode/cli/commands/scan/__init__.py
rename cycode/cli/{ => commands/scan}/code_scanner.py (77%)
create mode 100644 cycode/cli/commands/scan/commit_history/__init__.py
create mode 100644 cycode/cli/commands/scan/commit_history/commit_history_command.py
create mode 100644 cycode/cli/commands/scan/path/__init__.py
create mode 100644 cycode/cli/commands/scan/path/path_command.py
create mode 100644 cycode/cli/commands/scan/pre_commit/__init__.py
create mode 100644 cycode/cli/commands/scan/pre_commit/pre_commit_command.py
create mode 100644 cycode/cli/commands/scan/pre_receive/__init__.py
create mode 100644 cycode/cli/commands/scan/pre_receive/pre_receive_command.py
create mode 100644 cycode/cli/commands/scan/repository/__init__.py
create mode 100644 cycode/cli/commands/scan/repository/repisotiry_command.py
create mode 100644 cycode/cli/commands/scan/scan_ci/__init__.py
rename cycode/cli/{ => commands/scan/scan_ci}/ci_integrations.py (100%)
create mode 100644 cycode/cli/commands/scan/scan_ci/scan_ci_command.py
create mode 100644 cycode/cli/commands/scan/scan_command.py
create mode 100644 cycode/cli/commands/version/__init__.py
create mode 100644 cycode/cli/commands/version/version_command.py
rename cycode/cli/{commands/report/sbom/handle_errors.py => exceptions/handle_report_sbom_errors.py} (100%)
create mode 100644 cycode/cli/exceptions/handle_scan_errors.py
create mode 100644 tests/cli/commands/__init__.py
create mode 100644 tests/cli/commands/configure/__init__.py
rename tests/cli/{ => commands/configure}/test_configure_command.py (100%)
create mode 100644 tests/cli/commands/scan/__init__.py
rename tests/cli/{ => commands/scan}/test_code_scanner.py (55%)
rename tests/cli/{test_main.py => commands/test_main_command.py} (96%)
create mode 100644 tests/cli/exceptions/__init__.py
create mode 100644 tests/cli/exceptions/test_handle_scan_errors.py
create mode 100644 tests/cli/files_collector/iac/__init__.py
rename tests/cli/{helpers => files_collector/iac}/test_tf_content_generator.py (100%)
diff --git a/cycode/cli/auth/__init__.py b/cycode/cli/commands/__init__.py
similarity index 100%
rename from cycode/cli/auth/__init__.py
rename to cycode/cli/commands/__init__.py
diff --git a/tests/cli/helpers/__init__.py b/cycode/cli/commands/auth/__init__.py
similarity index 100%
rename from tests/cli/helpers/__init__.py
rename to cycode/cli/commands/auth/__init__.py
diff --git a/cycode/cli/auth/auth_command.py b/cycode/cli/commands/auth/auth_command.py
similarity index 95%
rename from cycode/cli/auth/auth_command.py
rename to cycode/cli/commands/auth/auth_command.py
index c7853068..51eb212b 100644
--- a/cycode/cli/auth/auth_command.py
+++ b/cycode/cli/commands/auth/auth_command.py
@@ -2,7 +2,7 @@
import click
-from cycode.cli.auth.auth_manager import AuthManager
+from cycode.cli.commands.auth.auth_manager import AuthManager
from cycode.cli.exceptions.custom_exceptions import AuthProcessError, HttpUnauthorizedError, NetworkError
from cycode.cli.models import CliError, CliErrors, CliResult
from cycode.cli.printers import ConsolePrinter
@@ -15,7 +15,7 @@
invoke_without_command=True, short_help='Authenticate your machine to associate the CLI with your Cycode account.'
)
@click.pass_context
-def authenticate(context: click.Context) -> None:
+def auth_command(context: click.Context) -> None:
"""Authenticates your machine."""
if context.invoked_subcommand is not None:
# if it is a subcommand, do nothing
@@ -33,7 +33,7 @@ def authenticate(context: click.Context) -> None:
_handle_exception(context, e)
-@authenticate.command(
+@auth_command.command(
name='check', short_help='Checks that your machine is associating the CLI with your Cycode account.'
)
@click.pass_context
diff --git a/cycode/cli/auth/auth_manager.py b/cycode/cli/commands/auth/auth_manager.py
similarity index 100%
rename from cycode/cli/auth/auth_manager.py
rename to cycode/cli/commands/auth/auth_manager.py
diff --git a/cycode/cli/commands/main_cli.py b/cycode/cli/commands/main_cli.py
new file mode 100644
index 00000000..e418cf7f
--- /dev/null
+++ b/cycode/cli/commands/main_cli.py
@@ -0,0 +1,79 @@
+import logging
+from typing import Optional
+
+import click
+
+from cycode.cli.commands.auth.auth_command import auth_command
+from cycode.cli.commands.configure.configure_command import configure_command
+from cycode.cli.commands.ignore.ignore_command import ignore_command
+from cycode.cli.commands.report.report_command import report_command
+from cycode.cli.commands.scan.scan_command import scan_command
+from cycode.cli.commands.version.version_command import version_command
+from cycode.cli.consts import (
+ CLI_CONTEXT_SETTINGS,
+)
+from cycode.cli.user_settings.configuration_manager import ConfigurationManager
+from cycode.cli.utils.progress_bar import SCAN_PROGRESS_BAR_SECTIONS, get_progress_bar
+from cycode.cyclient.config import set_logging_level
+from cycode.cyclient.cycode_client_base import CycodeClientBase
+from cycode.cyclient.models import UserAgentOptionScheme
+
+
+@click.group(
+ commands={
+ 'scan': scan_command,
+ 'report': report_command,
+ 'configure': configure_command,
+ 'ignore': ignore_command,
+ 'auth': auth_command,
+ 'version': version_command,
+ },
+ context_settings=CLI_CONTEXT_SETTINGS,
+)
+@click.option(
+ '--verbose',
+ '-v',
+ is_flag=True,
+ default=False,
+ help='Show detailed logs.',
+)
+@click.option(
+ '--no-progress-meter',
+ is_flag=True,
+ default=False,
+ help='Do not show the progress meter.',
+)
+@click.option(
+ '--output',
+ '-o',
+ default='text',
+ help='Specify the output type (the default is text).',
+ type=click.Choice(['text', 'json', 'table']),
+)
+@click.option(
+ '--user-agent',
+ default=None,
+ help='Characteristic JSON object that lets servers identify the application.',
+ type=str,
+)
+@click.pass_context
+def main_cli(
+ context: click.Context, verbose: bool, no_progress_meter: bool, output: str, user_agent: Optional[str]
+) -> None:
+ context.ensure_object(dict)
+ configuration_manager = ConfigurationManager()
+
+ verbose = verbose or configuration_manager.get_verbose_flag()
+ context.obj['verbose'] = verbose
+ if verbose:
+ set_logging_level(logging.DEBUG)
+
+ context.obj['output'] = output
+ if output == 'json':
+ no_progress_meter = True
+
+ context.obj['progress_bar'] = get_progress_bar(hidden=no_progress_meter, sections=SCAN_PROGRESS_BAR_SECTIONS)
+
+ if user_agent:
+ user_agent_option = UserAgentOptionScheme().loads(user_agent)
+ CycodeClientBase.enrich_user_agent(user_agent_option.user_agent_suffix)
diff --git a/cycode/cli/commands/report/sbom/path/__init__.py b/cycode/cli/commands/report/sbom/path/__init__.py
new file mode 100644
index 00000000..e69de29b
diff --git a/cycode/cli/commands/report/sbom/sbom_path_command.py b/cycode/cli/commands/report/sbom/path/path_command.py
similarity index 94%
rename from cycode/cli/commands/report/sbom/sbom_path_command.py
rename to cycode/cli/commands/report/sbom/path/path_command.py
index 23062cab..323eb62b 100644
--- a/cycode/cli/commands/report/sbom/sbom_path_command.py
+++ b/cycode/cli/commands/report/sbom/path/path_command.py
@@ -4,7 +4,7 @@
from cycode.cli import consts
from cycode.cli.commands.report.sbom.common import create_sbom_report, send_report_feedback
-from cycode.cli.commands.report.sbom.handle_errors import handle_report_exception
+from cycode.cli.exceptions.handle_report_sbom_errors import handle_report_exception
from cycode.cli.files_collector.path_documents import get_relevant_document
from cycode.cli.files_collector.sca.sca_code_scanner import perform_pre_scan_documents_actions
from cycode.cli.files_collector.zip_documents import zip_documents
@@ -15,7 +15,7 @@
@click.command(short_help='Generate SBOM report for provided path in the command.')
@click.argument('path', nargs=1, type=click.Path(exists=True, resolve_path=True), required=True)
@click.pass_context
-def sbom_path_command(context: click.Context, path: str) -> None:
+def path_command(context: click.Context, path: str) -> None:
client = get_report_cycode_client()
report_parameters = context.obj['report_parameters']
output_format = report_parameters.output_format
diff --git a/cycode/cli/commands/report/sbom/repository_url/__init__.py b/cycode/cli/commands/report/sbom/repository_url/__init__.py
new file mode 100644
index 00000000..e69de29b
diff --git a/cycode/cli/commands/report/sbom/sbom_repository_url_command.py b/cycode/cli/commands/report/sbom/repository_url/repository_url_command.py
similarity index 92%
rename from cycode/cli/commands/report/sbom/sbom_repository_url_command.py
rename to cycode/cli/commands/report/sbom/repository_url/repository_url_command.py
index 4d5ee4a3..4f54cac1 100644
--- a/cycode/cli/commands/report/sbom/sbom_repository_url_command.py
+++ b/cycode/cli/commands/report/sbom/repository_url/repository_url_command.py
@@ -3,7 +3,7 @@
import click
from cycode.cli.commands.report.sbom.common import create_sbom_report, send_report_feedback
-from cycode.cli.commands.report.sbom.handle_errors import handle_report_exception
+from cycode.cli.exceptions.handle_report_sbom_errors import handle_report_exception
from cycode.cli.utils.get_api_client import get_report_cycode_client
from cycode.cli.utils.progress_bar import SbomReportProgressBarSection
@@ -11,7 +11,7 @@
@click.command(short_help='Generate SBOM report for provided repository URI in the command.')
@click.argument('uri', nargs=1, type=str, required=True)
@click.pass_context
-def sbom_repository_url_command(context: click.Context, uri: str) -> None:
+def repository_url_command(context: click.Context, uri: str) -> None:
progress_bar = context.obj['progress_bar']
progress_bar.start()
progress_bar.set_section_length(SbomReportProgressBarSection.PREPARE_LOCAL_FILES)
diff --git a/cycode/cli/commands/report/sbom/sbom_command.py b/cycode/cli/commands/report/sbom/sbom_command.py
index ecfd2782..870f4e0c 100644
--- a/cycode/cli/commands/report/sbom/sbom_command.py
+++ b/cycode/cli/commands/report/sbom/sbom_command.py
@@ -3,16 +3,16 @@
import click
-from cycode.cli.commands.report.sbom.sbom_path_command import sbom_path_command
-from cycode.cli.commands.report.sbom.sbom_repository_url_command import sbom_repository_url_command
+from cycode.cli.commands.report.sbom.path.path_command import path_command
+from cycode.cli.commands.report.sbom.repository_url.repository_url_command import repository_url_command
from cycode.cli.config import config
from cycode.cyclient.report_client import ReportParameters
@click.group(
commands={
- 'path': sbom_path_command,
- 'repository_url': sbom_repository_url_command,
+ 'path': path_command,
+ 'repository_url': repository_url_command,
},
short_help='Generate SBOM report for remote repository by url or local directory by path.',
)
diff --git a/cycode/cli/commands/scan/__init__.py b/cycode/cli/commands/scan/__init__.py
new file mode 100644
index 00000000..e69de29b
diff --git a/cycode/cli/code_scanner.py b/cycode/cli/commands/scan/code_scanner.py
similarity index 77%
rename from cycode/cli/code_scanner.py
rename to cycode/cli/commands/scan/code_scanner.py
index 1801d63c..be1014de 100644
--- a/cycode/cli/code_scanner.py
+++ b/cycode/cli/commands/scan/code_scanner.py
@@ -3,34 +3,30 @@
import os
import sys
import time
-import traceback
from platform import platform
from typing import TYPE_CHECKING, Callable, Dict, List, Optional, Tuple
from uuid import UUID, uuid4
import click
-from git import NULL_TREE, InvalidGitRepositoryError, Repo
+from git import NULL_TREE, Repo
from cycode.cli import consts
-from cycode.cli.ci_integrations import get_commit_range
from cycode.cli.config import configuration_manager
from cycode.cli.exceptions import custom_exceptions
+from cycode.cli.exceptions.handle_scan_errors import handle_scan_exception
from cycode.cli.files_collector.excluder import exclude_irrelevant_documents_to_scan
from cycode.cli.files_collector.models.in_memory_zip import InMemoryZip
from cycode.cli.files_collector.path_documents import get_relevant_document
from cycode.cli.files_collector.repository_documents import (
- calculate_pre_receive_commit_range,
get_commit_range_modified_documents,
- get_diff_file_content,
get_diff_file_path,
- get_git_repository_tree_file_entries,
get_pre_commit_modified_documents,
parse_commit_range,
)
from cycode.cli.files_collector.sca import sca_code_scanner
from cycode.cli.files_collector.sca.sca_code_scanner import perform_pre_scan_documents_actions
from cycode.cli.files_collector.zip_documents import zip_documents
-from cycode.cli.models import CliError, CliErrors, Document, DocumentDetections, LocalScanResult, Severity
+from cycode.cli.models import CliError, Document, DocumentDetections, LocalScanResult, Severity
from cycode.cli.printers import ConsolePrinter
from cycode.cli.utils import scan_utils
from cycode.cli.utils.path_utils import (
@@ -39,7 +35,6 @@
from cycode.cli.utils.progress_bar import ScanProgressBarSection
from cycode.cli.utils.scan_batch import run_parallel_batched_scan
from cycode.cli.utils.scan_utils import set_issue_detected
-from cycode.cli.utils.task_timer import TimeoutAfter
from cycode.cyclient import logger
from cycode.cyclient.config import set_logging_level
from cycode.cyclient.models import Detection, DetectionSchema, DetectionsPerFile, ZippedFileScanResult
@@ -51,221 +46,6 @@
start_scan_time = time.time()
-@click.command(short_help='Scan the git repository including its history.')
-@click.argument('path', nargs=1, type=click.Path(exists=True, resolve_path=True), required=True)
-@click.option(
- '--branch',
- '-b',
- default=None,
- help='Branch to scan, if not set scanning the default branch',
- type=str,
- required=False,
-)
-@click.pass_context
-def scan_repository(context: click.Context, path: str, branch: str) -> None:
- try:
- logger.debug('Starting repository scan process, %s', {'path': path, 'branch': branch})
-
- scan_type = context.obj['scan_type']
- monitor = context.obj.get('monitor')
- if monitor and scan_type != consts.SCA_SCAN_TYPE:
- raise click.ClickException('Monitor flag is currently supported for SCA scan type only')
-
- progress_bar = context.obj['progress_bar']
- progress_bar.start()
-
- file_entries = list(get_git_repository_tree_file_entries(path, branch))
- progress_bar.set_section_length(ScanProgressBarSection.PREPARE_LOCAL_FILES, len(file_entries))
-
- documents_to_scan = []
- for file in file_entries:
- # FIXME(MarshalX): probably file could be tree or submodule too. we expect blob only
- progress_bar.update(ScanProgressBarSection.PREPARE_LOCAL_FILES)
-
- file_path = file.path if monitor else get_path_by_os(os.path.join(path, file.path))
- documents_to_scan.append(Document(file_path, file.data_stream.read().decode('UTF-8', errors='replace')))
-
- documents_to_scan = exclude_irrelevant_documents_to_scan(scan_type, documents_to_scan)
-
- perform_pre_scan_documents_actions(context, scan_type, documents_to_scan, is_git_diff=False)
-
- logger.debug('Found all relevant files for scanning %s', {'path': path, 'branch': branch})
- scan_documents(
- context, documents_to_scan, is_git_diff=False, scan_parameters=get_scan_parameters(context, path)
- )
- except Exception as e:
- _handle_exception(context, e)
-
-
-@click.command(short_help='Scan all the commits history in this git repository.')
-@click.argument('path', nargs=1, type=click.Path(exists=True, resolve_path=True), required=True)
-@click.option(
- '--commit_range',
- '-r',
- help='Scan a commit range in this git repository, by default cycode scans all commit history (example: HEAD~1)',
- type=click.STRING,
- default='--all',
- required=False,
-)
-@click.pass_context
-def scan_repository_commit_history(context: click.Context, path: str, commit_range: str) -> None:
- try:
- logger.debug('Starting commit history scan process, %s', {'path': path, 'commit_range': commit_range})
- scan_commit_range(context, path=path, commit_range=commit_range)
- except Exception as e:
- _handle_exception(context, e)
-
-
-def scan_commit_range(
- context: click.Context, path: str, commit_range: str, max_commits_count: Optional[int] = None
-) -> None:
- scan_type = context.obj['scan_type']
-
- progress_bar = context.obj['progress_bar']
- progress_bar.start()
-
- if scan_type not in consts.COMMIT_RANGE_SCAN_SUPPORTED_SCAN_TYPES:
- raise click.ClickException(f'Commit range scanning for {str.upper(scan_type)} is not supported')
-
- if scan_type == consts.SCA_SCAN_TYPE:
- return scan_sca_commit_range(context, path, commit_range)
-
- documents_to_scan = []
- commit_ids_to_scan = []
-
- repo = Repo(path)
- total_commits_count = int(repo.git.rev_list('--count', commit_range))
- logger.debug(f'Calculating diffs for {total_commits_count} commits in the commit range {commit_range}')
-
- progress_bar.set_section_length(ScanProgressBarSection.PREPARE_LOCAL_FILES, total_commits_count)
-
- scanned_commits_count = 0
- for commit in repo.iter_commits(rev=commit_range):
- if _does_reach_to_max_commits_to_scan_limit(commit_ids_to_scan, max_commits_count):
- logger.debug(f'Reached to max commits to scan count. Going to scan only {max_commits_count} last commits')
- progress_bar.update(ScanProgressBarSection.PREPARE_LOCAL_FILES, total_commits_count - scanned_commits_count)
- break
-
- progress_bar.update(ScanProgressBarSection.PREPARE_LOCAL_FILES)
-
- commit_id = commit.hexsha
- commit_ids_to_scan.append(commit_id)
- parent = commit.parents[0] if commit.parents else NULL_TREE
- diff = commit.diff(parent, create_patch=True, R=True)
- commit_documents_to_scan = []
- for blob in diff:
- blob_path = get_path_by_os(os.path.join(path, get_diff_file_path(blob)))
- commit_documents_to_scan.append(
- Document(
- path=blob_path,
- content=blob.diff.decode('UTF-8', errors='replace'),
- is_git_diff_format=True,
- unique_id=commit_id,
- )
- )
-
- logger.debug(
- 'Found all relevant files in commit %s',
- {'path': path, 'commit_range': commit_range, 'commit_id': commit_id},
- )
-
- documents_to_scan.extend(exclude_irrelevant_documents_to_scan(scan_type, commit_documents_to_scan))
- scanned_commits_count += 1
-
- logger.debug('List of commit ids to scan, %s', {'commit_ids': commit_ids_to_scan})
- logger.debug('Starting to scan commit range (It may take a few minutes)')
-
- scan_documents(context, documents_to_scan, is_git_diff=True, is_commit_range=True)
- return None
-
-
-@click.command(
- short_help='Execute scan in a CI environment which relies on the '
- 'CYCODE_TOKEN and CYCODE_REPO_LOCATION environment variables'
-)
-@click.pass_context
-def scan_ci(context: click.Context) -> None:
- scan_commit_range(context, path=os.getcwd(), commit_range=get_commit_range())
-
-
-@click.command(short_help='Scan the files in the path provided in the command.')
-@click.argument('path', nargs=1, type=click.Path(exists=True, resolve_path=True), required=True)
-@click.pass_context
-def scan_path(context: click.Context, path: str) -> None:
- progress_bar = context.obj['progress_bar']
- progress_bar.start()
-
- logger.debug('Starting path scan process, %s', {'path': path})
- scan_disk_files(context, path)
-
-
-@click.command(short_help='Use this command to scan any content that was not committed yet.')
-@click.argument('ignored_args', nargs=-1, type=click.UNPROCESSED)
-@click.pass_context
-def pre_commit_scan(context: click.Context, ignored_args: List[str]) -> None:
- scan_type = context.obj['scan_type']
-
- progress_bar = context.obj['progress_bar']
- progress_bar.start()
-
- if scan_type == consts.SCA_SCAN_TYPE:
- scan_sca_pre_commit(context)
- return
-
- diff_files = Repo(os.getcwd()).index.diff('HEAD', create_patch=True, R=True)
-
- progress_bar.set_section_length(ScanProgressBarSection.PREPARE_LOCAL_FILES, len(diff_files))
-
- documents_to_scan = []
- for file in diff_files:
- progress_bar.update(ScanProgressBarSection.PREPARE_LOCAL_FILES)
- documents_to_scan.append(Document(get_path_by_os(get_diff_file_path(file)), get_diff_file_content(file)))
-
- documents_to_scan = exclude_irrelevant_documents_to_scan(scan_type, documents_to_scan)
- scan_documents(context, documents_to_scan, is_git_diff=True)
-
-
-@click.command(short_help='Use this command to scan commits on the server side before pushing them to the repository.')
-@click.argument('ignored_args', nargs=-1, type=click.UNPROCESSED)
-@click.pass_context
-def pre_receive_scan(context: click.Context, ignored_args: List[str]) -> None:
- try:
- scan_type = context.obj['scan_type']
- if scan_type != consts.SECRET_SCAN_TYPE:
- raise click.ClickException(f'Commit range scanning for {scan_type.upper()} is not supported')
-
- if should_skip_pre_receive_scan():
- logger.info(
- 'A scan has been skipped as per your request.'
- ' Please note that this may leave your system vulnerable to secrets that have not been detected'
- )
- return
-
- if is_verbose_mode_requested_in_pre_receive_scan():
- enable_verbose_mode(context)
- logger.debug('Verbose mode enabled, all log levels will be displayed')
-
- command_scan_type = context.info_name
- timeout = configuration_manager.get_pre_receive_command_timeout(command_scan_type)
- with TimeoutAfter(timeout):
- if scan_type not in consts.COMMIT_RANGE_SCAN_SUPPORTED_SCAN_TYPES:
- raise click.ClickException(f'Commit range scanning for {scan_type.upper()} is not supported')
-
- branch_update_details = parse_pre_receive_input()
- commit_range = calculate_pre_receive_commit_range(branch_update_details)
- if not commit_range:
- logger.info(
- 'No new commits found for pushed branch, %s', {'branch_update_details': branch_update_details}
- )
- return
-
- max_commits_to_scan = configuration_manager.get_pre_receive_max_commits_to_scan_count(command_scan_type)
- scan_commit_range(context, os.getcwd(), commit_range, max_commits_count=max_commits_to_scan)
- perform_post_pre_receive_scan_actions(context)
- except Exception as e:
- _handle_exception(context, e)
-
-
def scan_sca_pre_commit(context: click.Context) -> None:
scan_type = context.obj['scan_type']
scan_parameters = get_default_scan_parameters(context)
@@ -312,7 +92,7 @@ def scan_disk_files(context: click.Context, path: str) -> None:
perform_pre_scan_documents_actions(context, scan_type, documents)
scan_documents(context, documents, scan_parameters=scan_parameters)
except Exception as e:
- _handle_exception(context, e)
+ handle_scan_exception(context, e)
def set_issue_detected_by_scan_results(context: click.Context, scan_results: List[LocalScanResult]) -> None:
@@ -349,7 +129,7 @@ def _scan_batch_thread_func(batch: List[Document]) -> Tuple[str, CliError, Local
scan_completed = True
except Exception as e:
- error = _handle_exception(context, e, return_exception=True)
+ error = handle_scan_exception(context, e, return_exception=True)
error_message = str(e)
if local_scan_result:
@@ -384,6 +164,69 @@ def _scan_batch_thread_func(batch: List[Document]) -> Tuple[str, CliError, Local
return _scan_batch_thread_func
+def scan_commit_range(
+ context: click.Context, path: str, commit_range: str, max_commits_count: Optional[int] = None
+) -> None:
+ scan_type = context.obj['scan_type']
+
+ progress_bar = context.obj['progress_bar']
+ progress_bar.start()
+
+ if scan_type not in consts.COMMIT_RANGE_SCAN_SUPPORTED_SCAN_TYPES:
+ raise click.ClickException(f'Commit range scanning for {str.upper(scan_type)} is not supported')
+
+ if scan_type == consts.SCA_SCAN_TYPE:
+ return scan_sca_commit_range(context, path, commit_range)
+
+ documents_to_scan = []
+ commit_ids_to_scan = []
+
+ repo = Repo(path)
+ total_commits_count = int(repo.git.rev_list('--count', commit_range))
+ logger.debug(f'Calculating diffs for {total_commits_count} commits in the commit range {commit_range}')
+
+ progress_bar.set_section_length(ScanProgressBarSection.PREPARE_LOCAL_FILES, total_commits_count)
+
+ scanned_commits_count = 0
+ for commit in repo.iter_commits(rev=commit_range):
+ if _does_reach_to_max_commits_to_scan_limit(commit_ids_to_scan, max_commits_count):
+ logger.debug(f'Reached to max commits to scan count. Going to scan only {max_commits_count} last commits')
+ progress_bar.update(ScanProgressBarSection.PREPARE_LOCAL_FILES, total_commits_count - scanned_commits_count)
+ break
+
+ progress_bar.update(ScanProgressBarSection.PREPARE_LOCAL_FILES)
+
+ commit_id = commit.hexsha
+ commit_ids_to_scan.append(commit_id)
+ parent = commit.parents[0] if commit.parents else NULL_TREE
+ diff = commit.diff(parent, create_patch=True, R=True)
+ commit_documents_to_scan = []
+ for blob in diff:
+ blob_path = get_path_by_os(os.path.join(path, get_diff_file_path(blob)))
+ commit_documents_to_scan.append(
+ Document(
+ path=blob_path,
+ content=blob.diff.decode('UTF-8', errors='replace'),
+ is_git_diff_format=True,
+ unique_id=commit_id,
+ )
+ )
+
+ logger.debug(
+ 'Found all relevant files in commit %s',
+ {'path': path, 'commit_range': commit_range, 'commit_id': commit_id},
+ )
+
+ documents_to_scan.extend(exclude_irrelevant_documents_to_scan(scan_type, commit_documents_to_scan))
+ scanned_commits_count += 1
+
+ logger.debug('List of commit ids to scan, %s', {'commit_ids': commit_ids_to_scan})
+ logger.debug('Starting to scan commit range (It may take a few minutes)')
+
+ scan_documents(context, documents_to_scan, is_git_diff=True, is_commit_range=True)
+ return None
+
+
def scan_documents(
context: click.Context,
documents_to_scan: List[Document],
@@ -472,7 +315,7 @@ def scan_commit_range_documents(
scan_completed = True
except Exception as e:
- _handle_exception(context, e)
+ handle_scan_exception(context, e)
error_message = str(e)
zip_file_size = from_commit_zipped_documents.size + to_commit_zipped_documents.size
@@ -827,75 +670,6 @@ def _get_document_by_file_name(
return None
-def _handle_exception(context: click.Context, e: Exception, *, return_exception: bool = False) -> Optional[CliError]:
- context.obj['did_fail'] = True
-
- if context.obj['verbose']:
- click.secho(f'Error: {traceback.format_exc()}', fg='red')
-
- errors: CliErrors = {
- custom_exceptions.NetworkError: CliError(
- soft_fail=True,
- code='cycode_error',
- message='Cycode was unable to complete this scan. '
- 'Please try again by executing the `cycode scan` command',
- ),
- custom_exceptions.ScanAsyncError: CliError(
- soft_fail=True,
- code='scan_error',
- message='Cycode was unable to complete this scan. '
- 'Please try again by executing the `cycode scan` command',
- ),
- custom_exceptions.HttpUnauthorizedError: CliError(
- soft_fail=True,
- code='auth_error',
- message='Unable to authenticate to Cycode, your token is either invalid or has expired. '
- 'Please re-generate your token and reconfigure it by running the `cycode configure` command',
- ),
- custom_exceptions.ZipTooLargeError: CliError(
- soft_fail=True,
- code='zip_too_large_error',
- message='The path you attempted to scan exceeds the current maximum scanning size cap (10MB). '
- 'Please try ignoring irrelevant paths using the `cycode ignore --by-path` command '
- 'and execute the scan again',
- ),
- custom_exceptions.TfplanKeyError: CliError(
- soft_fail=True,
- code='key_error',
- message=f'\n{e!s}\n'
- 'A crucial field is missing in your terraform plan file. '
- 'Please make sure that your file is well formed '
- 'and execute the scan again',
- ),
- InvalidGitRepositoryError: CliError(
- soft_fail=False,
- code='invalid_git_error',
- message='The path you supplied does not correlate to a git repository. '
- 'If you still wish to scan this path, use: `cycode scan path `',
- ),
- }
-
- if type(e) in errors:
- error = errors[type(e)]
-
- if error.soft_fail is True:
- context.obj['soft_fail'] = True
-
- if return_exception:
- return error
-
- ConsolePrinter(context).print_error(error)
- return None
-
- if return_exception:
- return CliError(code='unknown_error', message=str(e))
-
- if isinstance(e, click.ClickException):
- raise e
-
- raise click.ClickException(str(e))
-
-
def _report_scan_status(
cycode_client: 'ScanClient',
scan_type: str,
diff --git a/cycode/cli/commands/scan/commit_history/__init__.py b/cycode/cli/commands/scan/commit_history/__init__.py
new file mode 100644
index 00000000..e69de29b
diff --git a/cycode/cli/commands/scan/commit_history/commit_history_command.py b/cycode/cli/commands/scan/commit_history/commit_history_command.py
new file mode 100644
index 00000000..f7db9404
--- /dev/null
+++ b/cycode/cli/commands/scan/commit_history/commit_history_command.py
@@ -0,0 +1,24 @@
+import click
+
+from cycode.cli.commands.scan.code_scanner import scan_commit_range
+from cycode.cli.exceptions.handle_scan_errors import handle_scan_exception
+from cycode.cyclient import logger
+
+
+@click.command(short_help='Scan all the commits history in this git repository.')
+@click.argument('path', nargs=1, type=click.Path(exists=True, resolve_path=True), required=True)
+@click.option(
+ '--commit_range',
+ '-r',
+ help='Scan a commit range in this git repository, by default cycode scans all commit history (example: HEAD~1)',
+ type=click.STRING,
+ default='--all',
+ required=False,
+)
+@click.pass_context
+def commit_history_command(context: click.Context, path: str, commit_range: str) -> None:
+ try:
+ logger.debug('Starting commit history scan process, %s', {'path': path, 'commit_range': commit_range})
+ scan_commit_range(context, path=path, commit_range=commit_range)
+ except Exception as e:
+ handle_scan_exception(context, e)
diff --git a/cycode/cli/commands/scan/path/__init__.py b/cycode/cli/commands/scan/path/__init__.py
new file mode 100644
index 00000000..e69de29b
diff --git a/cycode/cli/commands/scan/path/path_command.py b/cycode/cli/commands/scan/path/path_command.py
new file mode 100644
index 00000000..7098016e
--- /dev/null
+++ b/cycode/cli/commands/scan/path/path_command.py
@@ -0,0 +1,15 @@
+import click
+
+from cycode.cli.commands.scan.code_scanner import scan_disk_files
+from cycode.cyclient import logger
+
+
+@click.command(short_help='Scan the files in the path provided in the command.')
+@click.argument('path', nargs=1, type=click.Path(exists=True, resolve_path=True), required=True)
+@click.pass_context
+def path_command(context: click.Context, path: str) -> None:
+ progress_bar = context.obj['progress_bar']
+ progress_bar.start()
+
+ logger.debug('Starting path scan process, %s', {'path': path})
+ scan_disk_files(context, path)
diff --git a/cycode/cli/commands/scan/pre_commit/__init__.py b/cycode/cli/commands/scan/pre_commit/__init__.py
new file mode 100644
index 00000000..e69de29b
diff --git a/cycode/cli/commands/scan/pre_commit/pre_commit_command.py b/cycode/cli/commands/scan/pre_commit/pre_commit_command.py
new file mode 100644
index 00000000..a758f0f5
--- /dev/null
+++ b/cycode/cli/commands/scan/pre_commit/pre_commit_command.py
@@ -0,0 +1,44 @@
+import os
+from typing import List
+
+import click
+from git import Repo
+
+from cycode.cli import consts
+from cycode.cli.commands.scan.code_scanner import scan_documents, scan_sca_pre_commit
+from cycode.cli.files_collector.excluder import exclude_irrelevant_documents_to_scan
+from cycode.cli.files_collector.repository_documents import (
+ get_diff_file_content,
+ get_diff_file_path,
+)
+from cycode.cli.models import Document
+from cycode.cli.utils.path_utils import (
+ get_path_by_os,
+)
+from cycode.cli.utils.progress_bar import ScanProgressBarSection
+
+
+@click.command(short_help='Use this command to scan any content that was not committed yet.')
+@click.argument('ignored_args', nargs=-1, type=click.UNPROCESSED)
+@click.pass_context
+def pre_commit_command(context: click.Context, ignored_args: List[str]) -> None:
+ scan_type = context.obj['scan_type']
+
+ progress_bar = context.obj['progress_bar']
+ progress_bar.start()
+
+ if scan_type == consts.SCA_SCAN_TYPE:
+ scan_sca_pre_commit(context)
+ return
+
+ diff_files = Repo(os.getcwd()).index.diff('HEAD', create_patch=True, R=True)
+
+ progress_bar.set_section_length(ScanProgressBarSection.PREPARE_LOCAL_FILES, len(diff_files))
+
+ documents_to_scan = []
+ for file in diff_files:
+ progress_bar.update(ScanProgressBarSection.PREPARE_LOCAL_FILES)
+ documents_to_scan.append(Document(get_path_by_os(get_diff_file_path(file)), get_diff_file_content(file)))
+
+ documents_to_scan = exclude_irrelevant_documents_to_scan(scan_type, documents_to_scan)
+ scan_documents(context, documents_to_scan, is_git_diff=True)
diff --git a/cycode/cli/commands/scan/pre_receive/__init__.py b/cycode/cli/commands/scan/pre_receive/__init__.py
new file mode 100644
index 00000000..e69de29b
diff --git a/cycode/cli/commands/scan/pre_receive/pre_receive_command.py b/cycode/cli/commands/scan/pre_receive/pre_receive_command.py
new file mode 100644
index 00000000..71cd82c1
--- /dev/null
+++ b/cycode/cli/commands/scan/pre_receive/pre_receive_command.py
@@ -0,0 +1,62 @@
+import os
+from typing import List
+
+import click
+
+from cycode.cli import consts
+from cycode.cli.commands.scan.code_scanner import (
+ enable_verbose_mode,
+ is_verbose_mode_requested_in_pre_receive_scan,
+ parse_pre_receive_input,
+ perform_post_pre_receive_scan_actions,
+ scan_commit_range,
+ should_skip_pre_receive_scan,
+)
+from cycode.cli.config import configuration_manager
+from cycode.cli.exceptions.handle_scan_errors import handle_scan_exception
+from cycode.cli.files_collector.repository_documents import (
+ calculate_pre_receive_commit_range,
+)
+from cycode.cli.utils.task_timer import TimeoutAfter
+from cycode.cyclient import logger
+
+
+@click.command(short_help='Use this command to scan commits on the server side before pushing them to the repository.')
+@click.argument('ignored_args', nargs=-1, type=click.UNPROCESSED)
+@click.pass_context
+def pre_receive_command(context: click.Context, ignored_args: List[str]) -> None:
+ try:
+ scan_type = context.obj['scan_type']
+ if scan_type != consts.SECRET_SCAN_TYPE:
+ raise click.ClickException(f'Commit range scanning for {scan_type.upper()} is not supported')
+
+ if should_skip_pre_receive_scan():
+ logger.info(
+ 'A scan has been skipped as per your request.'
+ ' Please note that this may leave your system vulnerable to secrets that have not been detected'
+ )
+ return
+
+ if is_verbose_mode_requested_in_pre_receive_scan():
+ enable_verbose_mode(context)
+ logger.debug('Verbose mode enabled, all log levels will be displayed')
+
+ command_scan_type = context.info_name
+ timeout = configuration_manager.get_pre_receive_command_timeout(command_scan_type)
+ with TimeoutAfter(timeout):
+ if scan_type not in consts.COMMIT_RANGE_SCAN_SUPPORTED_SCAN_TYPES:
+ raise click.ClickException(f'Commit range scanning for {scan_type.upper()} is not supported')
+
+ branch_update_details = parse_pre_receive_input()
+ commit_range = calculate_pre_receive_commit_range(branch_update_details)
+ if not commit_range:
+ logger.info(
+ 'No new commits found for pushed branch, %s', {'branch_update_details': branch_update_details}
+ )
+ return
+
+ max_commits_to_scan = configuration_manager.get_pre_receive_max_commits_to_scan_count(command_scan_type)
+ scan_commit_range(context, os.getcwd(), commit_range, max_commits_count=max_commits_to_scan)
+ perform_post_pre_receive_scan_actions(context)
+ except Exception as e:
+ handle_scan_exception(context, e)
diff --git a/cycode/cli/commands/scan/repository/__init__.py b/cycode/cli/commands/scan/repository/__init__.py
new file mode 100644
index 00000000..e69de29b
diff --git a/cycode/cli/commands/scan/repository/repisotiry_command.py b/cycode/cli/commands/scan/repository/repisotiry_command.py
new file mode 100644
index 00000000..38aab411
--- /dev/null
+++ b/cycode/cli/commands/scan/repository/repisotiry_command.py
@@ -0,0 +1,60 @@
+import os
+
+import click
+
+from cycode.cli import consts
+from cycode.cli.commands.scan.code_scanner import get_scan_parameters, scan_documents
+from cycode.cli.exceptions.handle_scan_errors import handle_scan_exception
+from cycode.cli.files_collector.excluder import exclude_irrelevant_documents_to_scan
+from cycode.cli.files_collector.repository_documents import get_git_repository_tree_file_entries
+from cycode.cli.files_collector.sca.sca_code_scanner import perform_pre_scan_documents_actions
+from cycode.cli.models import Document
+from cycode.cli.utils.path_utils import get_path_by_os
+from cycode.cli.utils.progress_bar import ScanProgressBarSection
+from cycode.cyclient import logger
+
+
+@click.command(short_help='Scan the git repository including its history.')
+@click.argument('path', nargs=1, type=click.Path(exists=True, resolve_path=True), required=True)
+@click.option(
+ '--branch',
+ '-b',
+ default=None,
+ help='Branch to scan, if not set scanning the default branch',
+ type=str,
+ required=False,
+)
+@click.pass_context
+def repisotiry_command(context: click.Context, path: str, branch: str) -> None:
+ try:
+ logger.debug('Starting repository scan process, %s', {'path': path, 'branch': branch})
+
+ scan_type = context.obj['scan_type']
+ monitor = context.obj.get('monitor')
+ if monitor and scan_type != consts.SCA_SCAN_TYPE:
+ raise click.ClickException('Monitor flag is currently supported for SCA scan type only')
+
+ progress_bar = context.obj['progress_bar']
+ progress_bar.start()
+
+ file_entries = list(get_git_repository_tree_file_entries(path, branch))
+ progress_bar.set_section_length(ScanProgressBarSection.PREPARE_LOCAL_FILES, len(file_entries))
+
+ documents_to_scan = []
+ for file in file_entries:
+ # FIXME(MarshalX): probably file could be tree or submodule too. we expect blob only
+ progress_bar.update(ScanProgressBarSection.PREPARE_LOCAL_FILES)
+
+ file_path = file.path if monitor else get_path_by_os(os.path.join(path, file.path))
+ documents_to_scan.append(Document(file_path, file.data_stream.read().decode('UTF-8', errors='replace')))
+
+ documents_to_scan = exclude_irrelevant_documents_to_scan(scan_type, documents_to_scan)
+
+ perform_pre_scan_documents_actions(context, scan_type, documents_to_scan, is_git_diff=False)
+
+ logger.debug('Found all relevant files for scanning %s', {'path': path, 'branch': branch})
+ scan_documents(
+ context, documents_to_scan, is_git_diff=False, scan_parameters=get_scan_parameters(context, path)
+ )
+ except Exception as e:
+ handle_scan_exception(context, e)
diff --git a/cycode/cli/commands/scan/scan_ci/__init__.py b/cycode/cli/commands/scan/scan_ci/__init__.py
new file mode 100644
index 00000000..e69de29b
diff --git a/cycode/cli/ci_integrations.py b/cycode/cli/commands/scan/scan_ci/ci_integrations.py
similarity index 100%
rename from cycode/cli/ci_integrations.py
rename to cycode/cli/commands/scan/scan_ci/ci_integrations.py
diff --git a/cycode/cli/commands/scan/scan_ci/scan_ci_command.py b/cycode/cli/commands/scan/scan_ci/scan_ci_command.py
new file mode 100644
index 00000000..594aad63
--- /dev/null
+++ b/cycode/cli/commands/scan/scan_ci/scan_ci_command.py
@@ -0,0 +1,15 @@
+import os
+
+import click
+
+from cycode.cli.commands.scan.code_scanner import scan_commit_range
+from cycode.cli.commands.scan.scan_ci.ci_integrations import get_commit_range
+
+
+@click.command(
+ short_help='Execute scan in a CI environment which relies on the '
+ 'CYCODE_TOKEN and CYCODE_REPO_LOCATION environment variables'
+)
+@click.pass_context
+def scan_ci_command(context: click.Context) -> None:
+ scan_commit_range(context, path=os.getcwd(), commit_range=get_commit_range())
diff --git a/cycode/cli/commands/scan/scan_command.py b/cycode/cli/commands/scan/scan_command.py
new file mode 100644
index 00000000..920b8be2
--- /dev/null
+++ b/cycode/cli/commands/scan/scan_command.py
@@ -0,0 +1,159 @@
+import sys
+from typing import List
+
+import click
+
+from cycode.cli.commands.scan.commit_history.commit_history_command import commit_history_command
+from cycode.cli.commands.scan.path.path_command import path_command
+from cycode.cli.commands.scan.pre_commit.pre_commit_command import pre_commit_command
+from cycode.cli.commands.scan.pre_receive.pre_receive_command import pre_receive_command
+from cycode.cli.commands.scan.repository.repisotiry_command import repisotiry_command
+from cycode.cli.config import config
+from cycode.cli.consts import (
+ ISSUE_DETECTED_STATUS_CODE,
+ NO_ISSUES_STATUS_CODE,
+ SCA_SKIP_RESTORE_DEPENDENCIES_FLAG,
+)
+from cycode.cli.models import Severity
+from cycode.cli.utils import scan_utils
+from cycode.cli.utils.get_api_client import get_scan_cycode_client
+
+
+@click.group(
+ commands={
+ 'repository': repisotiry_command,
+ 'commit_history': commit_history_command,
+ 'path': path_command,
+ 'pre_commit': pre_commit_command,
+ 'pre_receive': pre_receive_command,
+ },
+ short_help='Scan the content for Secrets/IaC/SCA/SAST violations. '
+ 'You`ll need to specify which scan type to perform: ci/commit_history/path/repository/etc.',
+)
+@click.option(
+ '--scan-type',
+ '-t',
+ default='secret',
+ help='Specify the type of scan you wish to execute (the default is Secrets)',
+ type=click.Choice(config['scans']['supported_scans']),
+)
+@click.option(
+ '--secret',
+ default=None,
+ help='Specify a Cycode client secret for this specific scan execution.',
+ type=str,
+ required=False,
+)
+@click.option(
+ '--client-id',
+ default=None,
+ help='Specify a Cycode client ID for this specific scan execution.',
+ type=str,
+ required=False,
+)
+@click.option(
+ '--show-secret', is_flag=True, default=False, help='Show Secrets in plain text.', type=bool, required=False
+)
+@click.option(
+ '--soft-fail',
+ is_flag=True,
+ default=False,
+ help='Run the scan without failing; always return a non-error status code.',
+ type=bool,
+ required=False,
+)
+@click.option(
+ '--severity-threshold',
+ default=None,
+ help='Show violations only for the specified level or higher (supported for SCA scan types only).',
+ type=click.Choice([e.name for e in Severity]),
+ required=False,
+)
+@click.option(
+ '--sca-scan',
+ default=None,
+ help='Specify the type of SCA scan you wish to execute (the default is both).',
+ multiple=True,
+ type=click.Choice(config['scans']['supported_sca_scans']),
+)
+@click.option(
+ '--monitor',
+ is_flag=True,
+ default=False,
+ help='Used for SCA scan types only; when specified, the scan results are recorded in the Discovery module.',
+ type=bool,
+ required=False,
+)
+@click.option(
+ '--report',
+ is_flag=True,
+ default=False,
+ help='When specified, generates a violations report. A link to the report will be displayed in the console output.',
+ type=bool,
+ required=False,
+)
+@click.option(
+ f'--{SCA_SKIP_RESTORE_DEPENDENCIES_FLAG}',
+ is_flag=True,
+ default=False,
+ help='When specified, Cycode will not run restore command. Will scan direct dependencies ONLY!',
+ type=bool,
+ required=False,
+)
+@click.pass_context
+def scan_command(
+ context: click.Context,
+ scan_type: str,
+ secret: str,
+ client_id: str,
+ show_secret: bool,
+ soft_fail: bool,
+ severity_threshold: str,
+ sca_scan: List[str],
+ monitor: bool,
+ report: bool,
+ no_restore: bool,
+) -> int:
+ """Scans for Secrets, IaC, SCA or SAST violations."""
+ if show_secret:
+ context.obj['show_secret'] = show_secret
+ else:
+ context.obj['show_secret'] = config['result_printer']['default']['show_secret']
+
+ if soft_fail:
+ context.obj['soft_fail'] = soft_fail
+ else:
+ context.obj['soft_fail'] = config['soft_fail']
+
+ context.obj['client'] = get_scan_cycode_client(client_id, secret, not context.obj['show_secret'])
+ context.obj['scan_type'] = scan_type
+ context.obj['severity_threshold'] = severity_threshold
+ context.obj['monitor'] = monitor
+ context.obj['report'] = report
+ context.obj[SCA_SKIP_RESTORE_DEPENDENCIES_FLAG] = no_restore
+
+ _sca_scan_to_context(context, sca_scan)
+
+ return 1
+
+
+def _sca_scan_to_context(context: click.Context, sca_scan_user_selected: List[str]) -> None:
+ for sca_scan_option_selected in sca_scan_user_selected:
+ context.obj[sca_scan_option_selected] = True
+
+
+@scan_command.result_callback()
+@click.pass_context
+def finalize(context: click.Context, *_, **__) -> None:
+ progress_bar = context.obj.get('progress_bar')
+ if progress_bar:
+ progress_bar.stop()
+
+ if context.obj['soft_fail']:
+ sys.exit(0)
+
+ exit_code = NO_ISSUES_STATUS_CODE
+ if scan_utils.is_scan_failed(context):
+ exit_code = ISSUE_DETECTED_STATUS_CODE
+
+ sys.exit(exit_code)
diff --git a/cycode/cli/commands/version/__init__.py b/cycode/cli/commands/version/__init__.py
new file mode 100644
index 00000000..e69de29b
diff --git a/cycode/cli/commands/version/version_command.py b/cycode/cli/commands/version/version_command.py
new file mode 100644
index 00000000..55755e24
--- /dev/null
+++ b/cycode/cli/commands/version/version_command.py
@@ -0,0 +1,22 @@
+import json
+
+import click
+
+from cycode import __version__
+from cycode.cli.consts import PROGRAM_NAME
+
+
+@click.command(short_help='Show the CLI version and exit.')
+@click.pass_context
+def version_command(context: click.Context) -> None:
+ output = context.obj['output']
+
+ prog = PROGRAM_NAME
+ ver = __version__
+
+ message = f'{prog}, version {ver}'
+ if output == 'json':
+ message = json.dumps({'name': prog, 'version': ver})
+
+ click.echo(message, color=context.color)
+ context.exit()
diff --git a/cycode/cli/commands/report/sbom/handle_errors.py b/cycode/cli/exceptions/handle_report_sbom_errors.py
similarity index 100%
rename from cycode/cli/commands/report/sbom/handle_errors.py
rename to cycode/cli/exceptions/handle_report_sbom_errors.py
diff --git a/cycode/cli/exceptions/handle_scan_errors.py b/cycode/cli/exceptions/handle_scan_errors.py
new file mode 100644
index 00000000..1ee026f8
--- /dev/null
+++ b/cycode/cli/exceptions/handle_scan_errors.py
@@ -0,0 +1,80 @@
+import traceback
+from typing import Optional
+
+import click
+from git import InvalidGitRepositoryError
+
+from cycode.cli.exceptions import custom_exceptions
+from cycode.cli.models import CliError, CliErrors
+from cycode.cli.printers import ConsolePrinter
+
+
+def handle_scan_exception(
+ context: click.Context, e: Exception, *, return_exception: bool = False
+) -> Optional[CliError]:
+ context.obj['did_fail'] = True
+
+ if context.obj['verbose']:
+ click.secho(f'Error: {traceback.format_exc()}', fg='red')
+
+ errors: CliErrors = {
+ custom_exceptions.NetworkError: CliError(
+ soft_fail=True,
+ code='cycode_error',
+ message='Cycode was unable to complete this scan. '
+ 'Please try again by executing the `cycode scan` command',
+ ),
+ custom_exceptions.ScanAsyncError: CliError(
+ soft_fail=True,
+ code='scan_error',
+ message='Cycode was unable to complete this scan. '
+ 'Please try again by executing the `cycode scan` command',
+ ),
+ custom_exceptions.HttpUnauthorizedError: CliError(
+ soft_fail=True,
+ code='auth_error',
+ message='Unable to authenticate to Cycode, your token is either invalid or has expired. '
+ 'Please re-generate your token and reconfigure it by running the `cycode configure` command',
+ ),
+ custom_exceptions.ZipTooLargeError: CliError(
+ soft_fail=True,
+ code='zip_too_large_error',
+ message='The path you attempted to scan exceeds the current maximum scanning size cap (10MB). '
+ 'Please try ignoring irrelevant paths using the `cycode ignore --by-path` command '
+ 'and execute the scan again',
+ ),
+ custom_exceptions.TfplanKeyError: CliError(
+ soft_fail=True,
+ code='key_error',
+ message=f'\n{e!s}\n'
+ 'A crucial field is missing in your terraform plan file. '
+ 'Please make sure that your file is well formed '
+ 'and execute the scan again',
+ ),
+ InvalidGitRepositoryError: CliError(
+ soft_fail=False,
+ code='invalid_git_error',
+ message='The path you supplied does not correlate to a git repository. '
+ 'If you still wish to scan this path, use: `cycode scan path `',
+ ),
+ }
+
+ if type(e) in errors:
+ error = errors[type(e)]
+
+ if error.soft_fail is True:
+ context.obj['soft_fail'] = True
+
+ if return_exception:
+ return error
+
+ ConsolePrinter(context).print_error(error)
+ return None
+
+ if return_exception:
+ return CliError(code='unknown_error', message=str(e))
+
+ if isinstance(e, click.ClickException):
+ raise e
+
+ raise click.ClickException(str(e))
diff --git a/cycode/cli/main.py b/cycode/cli/main.py
index 082cca3a..b27c98e2 100644
--- a/cycode/cli/main.py
+++ b/cycode/cli/main.py
@@ -1,253 +1,4 @@
-import json
-import logging
-import sys
-from typing import List, Optional
-
-import click
-
-from cycode import __version__
-from cycode.cli import code_scanner
-from cycode.cli.auth.auth_command import authenticate
-from cycode.cli.commands.configure.configure_command import configure_command
-from cycode.cli.commands.ignore.ignore_command import ignore_command
-from cycode.cli.commands.report.report_command import report_command
-from cycode.cli.config import config
-from cycode.cli.consts import (
- CLI_CONTEXT_SETTINGS,
- ISSUE_DETECTED_STATUS_CODE,
- NO_ISSUES_STATUS_CODE,
- PROGRAM_NAME,
- SCA_SKIP_RESTORE_DEPENDENCIES_FLAG,
-)
-from cycode.cli.models import Severity
-from cycode.cli.user_settings.configuration_manager import ConfigurationManager
-from cycode.cli.utils import scan_utils
-from cycode.cli.utils.get_api_client import get_scan_cycode_client
-from cycode.cli.utils.progress_bar import SCAN_PROGRESS_BAR_SECTIONS, get_progress_bar
-from cycode.cyclient.config import set_logging_level
-from cycode.cyclient.cycode_client_base import CycodeClientBase
-from cycode.cyclient.models import UserAgentOptionScheme
-
-
-@click.group(
- commands={
- 'repository': code_scanner.scan_repository,
- 'commit_history': code_scanner.scan_repository_commit_history,
- 'path': code_scanner.scan_path,
- 'pre_commit': code_scanner.pre_commit_scan,
- 'pre_receive': code_scanner.pre_receive_scan,
- },
- short_help='Scan the content for Secrets/IaC/SCA/SAST violations. '
- 'You`ll need to specify which scan type to perform: ci/commit_history/path/repository/etc.',
-)
-@click.option(
- '--scan-type',
- '-t',
- default='secret',
- help='Specify the type of scan you wish to execute (the default is Secrets)',
- type=click.Choice(config['scans']['supported_scans']),
-)
-@click.option(
- '--secret',
- default=None,
- help='Specify a Cycode client secret for this specific scan execution.',
- type=str,
- required=False,
-)
-@click.option(
- '--client-id',
- default=None,
- help='Specify a Cycode client ID for this specific scan execution.',
- type=str,
- required=False,
-)
-@click.option(
- '--show-secret', is_flag=True, default=False, help='Show Secrets in plain text.', type=bool, required=False
-)
-@click.option(
- '--soft-fail',
- is_flag=True,
- default=False,
- help='Run the scan without failing; always return a non-error status code.',
- type=bool,
- required=False,
-)
-@click.option(
- '--severity-threshold',
- default=None,
- help='Show violations only for the specified level or higher (supported for SCA scan types only).',
- type=click.Choice([e.name for e in Severity]),
- required=False,
-)
-@click.option(
- '--sca-scan',
- default=None,
- help='Specify the type of SCA scan you wish to execute (the default is both).',
- multiple=True,
- type=click.Choice(config['scans']['supported_sca_scans']),
-)
-@click.option(
- '--monitor',
- is_flag=True,
- default=False,
- help='Used for SCA scan types only; when specified, the scan results are recorded in the Discovery module.',
- type=bool,
- required=False,
-)
-@click.option(
- '--report',
- is_flag=True,
- default=False,
- help='When specified, generates a violations report. A link to the report will be displayed in the console output.',
- type=bool,
- required=False,
-)
-@click.option(
- f'--{SCA_SKIP_RESTORE_DEPENDENCIES_FLAG}',
- is_flag=True,
- default=False,
- help='When specified, Cycode will not run restore command. Will scan direct dependencies ONLY!',
- type=bool,
- required=False,
-)
-@click.pass_context
-def code_scan(
- context: click.Context,
- scan_type: str,
- secret: str,
- client_id: str,
- show_secret: bool,
- soft_fail: bool,
- severity_threshold: str,
- sca_scan: List[str],
- monitor: bool,
- report: bool,
- no_restore: bool,
-) -> int:
- """Scans for Secrets, IaC, SCA or SAST violations."""
- if show_secret:
- context.obj['show_secret'] = show_secret
- else:
- context.obj['show_secret'] = config['result_printer']['default']['show_secret']
-
- if soft_fail:
- context.obj['soft_fail'] = soft_fail
- else:
- context.obj['soft_fail'] = config['soft_fail']
-
- context.obj['client'] = get_scan_cycode_client(client_id, secret, not context.obj['show_secret'])
- context.obj['scan_type'] = scan_type
- context.obj['severity_threshold'] = severity_threshold
- context.obj['monitor'] = monitor
- context.obj['report'] = report
- context.obj[SCA_SKIP_RESTORE_DEPENDENCIES_FLAG] = no_restore
-
- _sca_scan_to_context(context, sca_scan)
-
- return 1
-
-
-@code_scan.result_callback()
-@click.pass_context
-def finalize(context: click.Context, *_, **__) -> None:
- progress_bar = context.obj.get('progress_bar')
- if progress_bar:
- progress_bar.stop()
-
- if context.obj['soft_fail']:
- sys.exit(0)
-
- exit_code = NO_ISSUES_STATUS_CODE
- if _should_fail_scan(context):
- exit_code = ISSUE_DETECTED_STATUS_CODE
-
- sys.exit(exit_code)
-
-
-@click.command(short_help='Show the CLI version and exit.')
-@click.pass_context
-def version(context: click.Context) -> None:
- output = context.obj['output']
-
- prog = PROGRAM_NAME
- ver = __version__
-
- message = f'{prog}, version {ver}'
- if output == 'json':
- message = json.dumps({'name': prog, 'version': ver})
-
- click.echo(message, color=context.color)
- context.exit()
-
-
-@click.group(
- commands={
- 'scan': code_scan,
- 'report': report_command,
- 'configure': configure_command,
- 'ignore': ignore_command,
- 'auth': authenticate,
- 'version': version,
- },
- context_settings=CLI_CONTEXT_SETTINGS,
-)
-@click.option(
- '--verbose',
- '-v',
- is_flag=True,
- default=False,
- help='Show detailed logs.',
-)
-@click.option(
- '--no-progress-meter',
- is_flag=True,
- default=False,
- help='Do not show the progress meter.',
-)
-@click.option(
- '--output',
- '-o',
- default='text',
- help='Specify the output type (the default is text).',
- type=click.Choice(['text', 'json', 'table']),
-)
-@click.option(
- '--user-agent',
- default=None,
- help='Characteristic JSON object that lets servers identify the application.',
- type=str,
-)
-@click.pass_context
-def main_cli(
- context: click.Context, verbose: bool, no_progress_meter: bool, output: str, user_agent: Optional[str]
-) -> None:
- context.ensure_object(dict)
- configuration_manager = ConfigurationManager()
-
- verbose = verbose or configuration_manager.get_verbose_flag()
- context.obj['verbose'] = verbose
- if verbose:
- set_logging_level(logging.DEBUG)
-
- context.obj['output'] = output
- if output == 'json':
- no_progress_meter = True
-
- context.obj['progress_bar'] = get_progress_bar(hidden=no_progress_meter, sections=SCAN_PROGRESS_BAR_SECTIONS)
-
- if user_agent:
- user_agent_option = UserAgentOptionScheme().loads(user_agent)
- CycodeClientBase.enrich_user_agent(user_agent_option.user_agent_suffix)
-
-
-def _should_fail_scan(context: click.Context) -> bool:
- return scan_utils.is_scan_failed(context)
-
-
-def _sca_scan_to_context(context: click.Context, sca_scan_user_selected: List[str]) -> None:
- for sca_scan_option_selected in sca_scan_user_selected:
- context.obj[sca_scan_option_selected] = True
-
+from cycode.cli.commands.main_cli import main_cli
if __name__ == '__main__':
main_cli()
diff --git a/tests/cli/commands/__init__.py b/tests/cli/commands/__init__.py
new file mode 100644
index 00000000..e69de29b
diff --git a/tests/cli/commands/configure/__init__.py b/tests/cli/commands/configure/__init__.py
new file mode 100644
index 00000000..e69de29b
diff --git a/tests/cli/test_configure_command.py b/tests/cli/commands/configure/test_configure_command.py
similarity index 100%
rename from tests/cli/test_configure_command.py
rename to tests/cli/commands/configure/test_configure_command.py
diff --git a/tests/cli/commands/scan/__init__.py b/tests/cli/commands/scan/__init__.py
new file mode 100644
index 00000000..e69de29b
diff --git a/tests/cli/test_code_scanner.py b/tests/cli/commands/scan/test_code_scanner.py
similarity index 55%
rename from tests/cli/test_code_scanner.py
rename to tests/cli/commands/scan/test_code_scanner.py
index f4fe4f69..c993958c 100644
--- a/tests/cli/test_code_scanner.py
+++ b/tests/cli/commands/scan/test_code_scanner.py
@@ -1,76 +1,10 @@
import os
-from typing import TYPE_CHECKING
-
-import click
-import pytest
-from click import ClickException
-from git import InvalidGitRepositoryError
-from requests import Response
from cycode.cli import consts
-from cycode.cli.code_scanner import _handle_exception
-from cycode.cli.exceptions import custom_exceptions
from cycode.cli.files_collector.excluder import _is_file_relevant_for_sca_scan
from cycode.cli.files_collector.path_documents import _generate_document
from cycode.cli.models import Document
-if TYPE_CHECKING:
- from _pytest.monkeypatch import MonkeyPatch
-
-
-@pytest.fixture()
-def ctx() -> click.Context:
- return click.Context(click.Command('path'), obj={'verbose': False, 'output': 'text'})
-
-
-@pytest.mark.parametrize(
- 'exception, expected_soft_fail',
- [
- (custom_exceptions.NetworkError(400, 'msg', Response()), True),
- (custom_exceptions.ScanAsyncError('msg'), True),
- (custom_exceptions.HttpUnauthorizedError('msg', Response()), True),
- (custom_exceptions.ZipTooLargeError(1000), True),
- (custom_exceptions.TfplanKeyError('msg'), True),
- (InvalidGitRepositoryError(), None),
- ],
-)
-def test_handle_exception_soft_fail(
- ctx: click.Context, exception: custom_exceptions.CycodeError, expected_soft_fail: bool
-) -> None:
- with ctx:
- _handle_exception(ctx, exception)
-
- assert ctx.obj.get('did_fail') is True
- assert ctx.obj.get('soft_fail') is expected_soft_fail
-
-
-def test_handle_exception_unhandled_error(ctx: click.Context) -> None:
- with ctx, pytest.raises(ClickException):
- _handle_exception(ctx, ValueError('test'))
-
- assert ctx.obj.get('did_fail') is True
- assert ctx.obj.get('soft_fail') is None
-
-
-def test_handle_exception_click_error(ctx: click.Context) -> None:
- with ctx, pytest.raises(ClickException):
- _handle_exception(ctx, click.ClickException('test'))
-
- assert ctx.obj.get('did_fail') is True
- assert ctx.obj.get('soft_fail') is None
-
-
-def test_handle_exception_verbose(monkeypatch: 'MonkeyPatch') -> None:
- ctx = click.Context(click.Command('path'), obj={'verbose': True, 'output': 'text'})
-
- def mock_secho(msg: str, *_, **__) -> None:
- assert 'Error:' in msg
-
- monkeypatch.setattr(click, 'secho', mock_secho)
-
- with ctx, pytest.raises(ClickException):
- _handle_exception(ctx, ValueError('test'))
-
def test_is_file_relevant_for_sca_scan() -> None:
path = os.path.join('some_package', 'node_modules', 'package.json')
diff --git a/tests/cli/test_main.py b/tests/cli/commands/test_main_command.py
similarity index 96%
rename from tests/cli/test_main.py
rename to tests/cli/commands/test_main_command.py
index 3f41ed6a..d74a2c40 100644
--- a/tests/cli/test_main.py
+++ b/tests/cli/commands/test_main_command.py
@@ -6,7 +6,7 @@
import responses
from click.testing import CliRunner
-from cycode.cli.main import main_cli
+from cycode.cli.commands.main_cli import main_cli
from tests.conftest import CLI_ENV_VARS, TEST_FILES_PATH, ZIP_CONTENT_PATH
from tests.cyclient.mocked_responses.scan_client import mock_scan_responses
from tests.cyclient.test_scan_client import get_zipped_file_scan_response, get_zipped_file_scan_url
diff --git a/tests/cli/exceptions/__init__.py b/tests/cli/exceptions/__init__.py
new file mode 100644
index 00000000..e69de29b
diff --git a/tests/cli/exceptions/test_handle_scan_errors.py b/tests/cli/exceptions/test_handle_scan_errors.py
new file mode 100644
index 00000000..7d63802b
--- /dev/null
+++ b/tests/cli/exceptions/test_handle_scan_errors.py
@@ -0,0 +1,67 @@
+from typing import TYPE_CHECKING
+
+import click
+import pytest
+from click import ClickException
+from git import InvalidGitRepositoryError
+from requests import Response
+
+from cycode.cli.exceptions import custom_exceptions
+from cycode.cli.exceptions.handle_scan_errors import handle_scan_exception
+
+if TYPE_CHECKING:
+ from _pytest.monkeypatch import MonkeyPatch
+
+
+@pytest.fixture()
+def ctx() -> click.Context:
+ return click.Context(click.Command('path'), obj={'verbose': False, 'output': 'text'})
+
+
+@pytest.mark.parametrize(
+ 'exception, expected_soft_fail',
+ [
+ (custom_exceptions.NetworkError(400, 'msg', Response()), True),
+ (custom_exceptions.ScanAsyncError('msg'), True),
+ (custom_exceptions.HttpUnauthorizedError('msg', Response()), True),
+ (custom_exceptions.ZipTooLargeError(1000), True),
+ (custom_exceptions.TfplanKeyError('msg'), True),
+ (InvalidGitRepositoryError(), None),
+ ],
+)
+def test_handle_exception_soft_fail(
+ ctx: click.Context, exception: custom_exceptions.CycodeError, expected_soft_fail: bool
+) -> None:
+ with ctx:
+ handle_scan_exception(ctx, exception)
+
+ assert ctx.obj.get('did_fail') is True
+ assert ctx.obj.get('soft_fail') is expected_soft_fail
+
+
+def test_handle_exception_unhandled_error(ctx: click.Context) -> None:
+ with ctx, pytest.raises(ClickException):
+ handle_scan_exception(ctx, ValueError('test'))
+
+ assert ctx.obj.get('did_fail') is True
+ assert ctx.obj.get('soft_fail') is None
+
+
+def test_handle_exception_click_error(ctx: click.Context) -> None:
+ with ctx, pytest.raises(ClickException):
+ handle_scan_exception(ctx, click.ClickException('test'))
+
+ assert ctx.obj.get('did_fail') is True
+ assert ctx.obj.get('soft_fail') is None
+
+
+def test_handle_exception_verbose(monkeypatch: 'MonkeyPatch') -> None:
+ ctx = click.Context(click.Command('path'), obj={'verbose': True, 'output': 'text'})
+
+ def mock_secho(msg: str, *_, **__) -> None:
+ assert 'Error:' in msg
+
+ monkeypatch.setattr(click, 'secho', mock_secho)
+
+ with ctx, pytest.raises(ClickException):
+ handle_scan_exception(ctx, ValueError('test'))
diff --git a/tests/cli/files_collector/iac/__init__.py b/tests/cli/files_collector/iac/__init__.py
new file mode 100644
index 00000000..e69de29b
diff --git a/tests/cli/helpers/test_tf_content_generator.py b/tests/cli/files_collector/iac/test_tf_content_generator.py
similarity index 100%
rename from tests/cli/helpers/test_tf_content_generator.py
rename to tests/cli/files_collector/iac/test_tf_content_generator.py
diff --git a/tests/cyclient/test_auth_client.py b/tests/cyclient/test_auth_client.py
index 0a34d3b2..51618e3c 100644
--- a/tests/cyclient/test_auth_client.py
+++ b/tests/cyclient/test_auth_client.py
@@ -3,6 +3,7 @@
import responses
from requests import Timeout
+from cycode.cli.commands.auth.auth_manager import AuthManager
from cycode.cli.exceptions.custom_exceptions import CycodeError
from cycode.cyclient.auth_client import AuthClient
from cycode.cyclient.models import (
@@ -14,16 +15,12 @@
@pytest.fixture(scope='module')
def code_challenge() -> str:
- from cycode.cli.auth.auth_manager import AuthManager
-
code_challenge, _ = AuthManager()._generate_pkce_code_pair()
return code_challenge
@pytest.fixture(scope='module')
def code_verifier() -> str:
- from cycode.cli.auth.auth_manager import AuthManager
-
_, code_verifier = AuthManager()._generate_pkce_code_pair()
return code_verifier
diff --git a/tests/cyclient/test_scan_client.py b/tests/cyclient/test_scan_client.py
index 6df7b544..69d657b2 100644
--- a/tests/cyclient/test_scan_client.py
+++ b/tests/cyclient/test_scan_client.py
@@ -8,10 +8,10 @@
from requests import Timeout
from requests.exceptions import ProxyError
-from cycode.cli.code_scanner import zip_documents
from cycode.cli.config import config
from cycode.cli.exceptions.custom_exceptions import CycodeError, HttpUnauthorizedError
from cycode.cli.files_collector.models.in_memory_zip import InMemoryZip
+from cycode.cli.files_collector.zip_documents import zip_documents
from cycode.cli.models import Document
from cycode.cyclient.scan_client import ScanClient
from tests.conftest import ZIP_CONTENT_PATH
From 0366b40d8dde7e29b7942df97dbdbcaa3ca6d914 Mon Sep 17 00:00:00 2001
From: Ilya Siamionau
Date: Thu, 7 Dec 2023 11:20:55 +0100
Subject: [PATCH 051/257] CM-29953 - Scanning many paths in one CLI run (#183)
---
.../commands/report/sbom/path/path_command.py | 6 +--
cycode/cli/commands/scan/code_scanner.py | 37 ++++++++++++-------
cycode/cli/commands/scan/path/path_command.py | 10 +++--
...otiry_command.py => repository_command.py} | 4 +-
.../commands/scan/scan_ci/scan_ci_command.py | 2 +
cycode/cli/commands/scan/scan_command.py | 6 +--
cycode/cli/files_collector/path_documents.py | 18 +++++----
7 files changed, 50 insertions(+), 33 deletions(-)
rename cycode/cli/commands/scan/repository/{repisotiry_command.py => repository_command.py} (95%)
diff --git a/cycode/cli/commands/report/sbom/path/path_command.py b/cycode/cli/commands/report/sbom/path/path_command.py
index 323eb62b..8e88bd10 100644
--- a/cycode/cli/commands/report/sbom/path/path_command.py
+++ b/cycode/cli/commands/report/sbom/path/path_command.py
@@ -5,7 +5,7 @@
from cycode.cli import consts
from cycode.cli.commands.report.sbom.common import create_sbom_report, send_report_feedback
from cycode.cli.exceptions.handle_report_sbom_errors import handle_report_exception
-from cycode.cli.files_collector.path_documents import get_relevant_document
+from cycode.cli.files_collector.path_documents import get_relevant_documents
from cycode.cli.files_collector.sca.sca_code_scanner import perform_pre_scan_documents_actions
from cycode.cli.files_collector.zip_documents import zip_documents
from cycode.cli.utils.get_api_client import get_report_cycode_client
@@ -28,8 +28,8 @@ def path_command(context: click.Context, path: str) -> None:
report_execution_id = -1
try:
- documents = get_relevant_document(
- progress_bar, SbomReportProgressBarSection.PREPARE_LOCAL_FILES, consts.SCA_SCAN_TYPE, path
+ documents = get_relevant_documents(
+ progress_bar, SbomReportProgressBarSection.PREPARE_LOCAL_FILES, consts.SCA_SCAN_TYPE, (path,)
)
# TODO(MarshalX): combine perform_pre_scan_documents_actions with get_relevant_document.
# unhardcode usage of context in perform_pre_scan_documents_actions
diff --git a/cycode/cli/commands/scan/code_scanner.py b/cycode/cli/commands/scan/code_scanner.py
index be1014de..8ac6c05b 100644
--- a/cycode/cli/commands/scan/code_scanner.py
+++ b/cycode/cli/commands/scan/code_scanner.py
@@ -16,7 +16,7 @@
from cycode.cli.exceptions.handle_scan_errors import handle_scan_exception
from cycode.cli.files_collector.excluder import exclude_irrelevant_documents_to_scan
from cycode.cli.files_collector.models.in_memory_zip import InMemoryZip
-from cycode.cli.files_collector.path_documents import get_relevant_document
+from cycode.cli.files_collector.path_documents import get_relevant_documents
from cycode.cli.files_collector.repository_documents import (
get_commit_range_modified_documents,
get_diff_file_path,
@@ -68,7 +68,7 @@ def scan_sca_commit_range(context: click.Context, path: str, commit_range: str)
scan_type = context.obj['scan_type']
progress_bar = context.obj['progress_bar']
- scan_parameters = get_scan_parameters(context, path)
+ scan_parameters = get_scan_parameters(context, (path,))
from_commit_rev, to_commit_rev = parse_commit_range(commit_range, path)
from_commit_documents, to_commit_documents = get_commit_range_modified_documents(
progress_bar, ScanProgressBarSection.PREPARE_LOCAL_FILES, path, from_commit_rev, to_commit_rev
@@ -82,13 +82,13 @@ def scan_sca_commit_range(context: click.Context, path: str, commit_range: str)
scan_commit_range_documents(context, from_commit_documents, to_commit_documents, scan_parameters=scan_parameters)
-def scan_disk_files(context: click.Context, path: str) -> None:
- scan_parameters = get_scan_parameters(context, path)
+def scan_disk_files(context: click.Context, paths: Tuple[str]) -> None:
+ scan_parameters = get_scan_parameters(context, paths)
scan_type = context.obj['scan_type']
progress_bar = context.obj['progress_bar']
try:
- documents = get_relevant_document(progress_bar, ScanProgressBarSection.PREPARE_LOCAL_FILES, scan_type, path)
+ documents = get_relevant_documents(progress_bar, ScanProgressBarSection.PREPARE_LOCAL_FILES, scan_type, paths)
perform_pre_scan_documents_actions(context, scan_type, documents)
scan_documents(context, documents, scan_parameters=scan_parameters)
except Exception as e:
@@ -535,22 +535,31 @@ def get_default_scan_parameters(context: click.Context) -> dict:
}
-def get_scan_parameters(context: click.Context, path: str) -> dict:
+def get_scan_parameters(context: click.Context, paths: Tuple[str]) -> dict:
scan_parameters = get_default_scan_parameters(context)
- remote_url = try_get_git_remote_url(path)
+
+ if len(paths) != 1:
+ # ignore remote url if multiple paths are provided
+ return scan_parameters
+
+ remote_url = try_get_git_remote_url(paths[0])
if remote_url:
- # TODO(MarshalX): remove hardcode
+ # TODO(MarshalX): remove hardcode in context
context.obj['remote_url'] = remote_url
- scan_parameters.update(remote_url)
+ scan_parameters.update(
+ {
+ 'remote_url': remote_url,
+ }
+ )
+
return scan_parameters
-def try_get_git_remote_url(path: str) -> Optional[dict]:
+def try_get_git_remote_url(path: str) -> Optional[str]:
try:
- git_remote_url = Repo(path).remotes[0].config_reader.get('url')
- return {
- 'remote_url': git_remote_url,
- }
+ remote_url = Repo(path).remotes[0].config_reader.get('url')
+ logger.debug(f'Found Git remote URL "{remote_url}" in path "{path}"')
+ return remote_url
except Exception as e:
logger.debug('Failed to get git remote URL. %s', {'exception_message': str(e)})
return None
diff --git a/cycode/cli/commands/scan/path/path_command.py b/cycode/cli/commands/scan/path/path_command.py
index 7098016e..63182577 100644
--- a/cycode/cli/commands/scan/path/path_command.py
+++ b/cycode/cli/commands/scan/path/path_command.py
@@ -1,3 +1,5 @@
+from typing import Tuple
+
import click
from cycode.cli.commands.scan.code_scanner import scan_disk_files
@@ -5,11 +7,11 @@
@click.command(short_help='Scan the files in the path provided in the command.')
-@click.argument('path', nargs=1, type=click.Path(exists=True, resolve_path=True), required=True)
+@click.argument('paths', nargs=-1, type=click.Path(exists=True, resolve_path=True), required=True)
@click.pass_context
-def path_command(context: click.Context, path: str) -> None:
+def path_command(context: click.Context, paths: Tuple[str]) -> None:
progress_bar = context.obj['progress_bar']
progress_bar.start()
- logger.debug('Starting path scan process, %s', {'path': path})
- scan_disk_files(context, path)
+ logger.debug('Starting path scan process, %s', {'paths': paths})
+ scan_disk_files(context, paths)
diff --git a/cycode/cli/commands/scan/repository/repisotiry_command.py b/cycode/cli/commands/scan/repository/repository_command.py
similarity index 95%
rename from cycode/cli/commands/scan/repository/repisotiry_command.py
rename to cycode/cli/commands/scan/repository/repository_command.py
index 38aab411..cf560c26 100644
--- a/cycode/cli/commands/scan/repository/repisotiry_command.py
+++ b/cycode/cli/commands/scan/repository/repository_command.py
@@ -25,7 +25,7 @@
required=False,
)
@click.pass_context
-def repisotiry_command(context: click.Context, path: str, branch: str) -> None:
+def repository_command(context: click.Context, path: str, branch: str) -> None:
try:
logger.debug('Starting repository scan process, %s', {'path': path, 'branch': branch})
@@ -54,7 +54,7 @@ def repisotiry_command(context: click.Context, path: str, branch: str) -> None:
logger.debug('Found all relevant files for scanning %s', {'path': path, 'branch': branch})
scan_documents(
- context, documents_to_scan, is_git_diff=False, scan_parameters=get_scan_parameters(context, path)
+ context, documents_to_scan, is_git_diff=False, scan_parameters=get_scan_parameters(context, (path,))
)
except Exception as e:
handle_scan_exception(context, e)
diff --git a/cycode/cli/commands/scan/scan_ci/scan_ci_command.py b/cycode/cli/commands/scan/scan_ci/scan_ci_command.py
index 594aad63..70383422 100644
--- a/cycode/cli/commands/scan/scan_ci/scan_ci_command.py
+++ b/cycode/cli/commands/scan/scan_ci/scan_ci_command.py
@@ -5,6 +5,8 @@
from cycode.cli.commands.scan.code_scanner import scan_commit_range
from cycode.cli.commands.scan.scan_ci.ci_integrations import get_commit_range
+# This command is not finished yet. It is not used in the codebase.
+
@click.command(
short_help='Execute scan in a CI environment which relies on the '
diff --git a/cycode/cli/commands/scan/scan_command.py b/cycode/cli/commands/scan/scan_command.py
index 920b8be2..a53f501b 100644
--- a/cycode/cli/commands/scan/scan_command.py
+++ b/cycode/cli/commands/scan/scan_command.py
@@ -7,7 +7,7 @@
from cycode.cli.commands.scan.path.path_command import path_command
from cycode.cli.commands.scan.pre_commit.pre_commit_command import pre_commit_command
from cycode.cli.commands.scan.pre_receive.pre_receive_command import pre_receive_command
-from cycode.cli.commands.scan.repository.repisotiry_command import repisotiry_command
+from cycode.cli.commands.scan.repository.repository_command import repository_command
from cycode.cli.config import config
from cycode.cli.consts import (
ISSUE_DETECTED_STATUS_CODE,
@@ -21,14 +21,14 @@
@click.group(
commands={
- 'repository': repisotiry_command,
+ 'repository': repository_command,
'commit_history': commit_history_command,
'path': path_command,
'pre_commit': pre_commit_command,
'pre_receive': pre_receive_command,
},
short_help='Scan the content for Secrets/IaC/SCA/SAST violations. '
- 'You`ll need to specify which scan type to perform: ci/commit_history/path/repository/etc.',
+ 'You`ll need to specify which scan type to perform: commit_history/path/repository/etc.',
)
@click.option(
'--scan-type',
diff --git a/cycode/cli/files_collector/path_documents.py b/cycode/cli/files_collector/path_documents.py
index a0df5ac0..1d16e4f9 100644
--- a/cycode/cli/files_collector/path_documents.py
+++ b/cycode/cli/files_collector/path_documents.py
@@ -1,5 +1,5 @@
import os
-from typing import TYPE_CHECKING, Iterable, List
+from typing import TYPE_CHECKING, Iterable, List, Tuple
import pathspec
@@ -48,9 +48,13 @@ def _get_relevant_files_in_path(path: str, exclude_patterns: Iterable[str]) -> L
def _get_relevant_files(
- progress_bar: 'BaseProgressBar', progress_bar_section: 'ProgressBarSection', scan_type: str, path: str
+ progress_bar: 'BaseProgressBar', progress_bar_section: 'ProgressBarSection', scan_type: str, paths: Tuple[str]
) -> List[str]:
- all_files_to_scan = _get_relevant_files_in_path(path=path, exclude_patterns=['**/.git/**', '**/.cycode/**'])
+ all_files_to_scan = []
+ for path in paths:
+ all_files_to_scan.extend(
+ _get_relevant_files_in_path(path=path, exclude_patterns=['**/.git/**', '**/.cycode/**'])
+ )
# we are double the progress bar section length because we are going to process the files twice
# first time to get the file list with respect of excluded patterns (excluding takes seconds to execute)
@@ -70,7 +74,7 @@ def _get_relevant_files(
progress_bar.set_section_length(progress_bar_section, progress_bar_section_len)
logger.debug(
- 'Found all relevant files for scanning %s', {'path': path, 'file_to_scan_count': len(relevant_files_to_scan)}
+ 'Found all relevant files for scanning %s', {'paths': paths, 'file_to_scan_count': len(relevant_files_to_scan)}
)
return relevant_files_to_scan
@@ -89,15 +93,15 @@ def _handle_tfplan_file(file: str, content: str, is_git_diff: bool) -> Document:
return Document(document_name, tf_content, is_git_diff)
-def get_relevant_document(
+def get_relevant_documents(
progress_bar: 'BaseProgressBar',
progress_bar_section: 'ProgressBarSection',
scan_type: str,
- path: str,
+ paths: Tuple[str],
*,
is_git_diff: bool = False,
) -> List[Document]:
- relevant_files = _get_relevant_files(progress_bar, progress_bar_section, scan_type, path)
+ relevant_files = _get_relevant_files(progress_bar, progress_bar_section, scan_type, paths)
documents: List[Document] = []
for file in relevant_files:
From 081eda60734e2e3fa2994e9a733f6092042fd7b3 Mon Sep 17 00:00:00 2001
From: Ilya Siamionau
Date: Wed, 13 Dec 2023 10:46:37 +0100
Subject: [PATCH 052/257] CM-30139 - Add Company Guidelines (#184)
---
cycode/cli/commands/scan/code_scanner.py | 31 ++++++++++
cycode/cli/printers/text_printer.py | 14 ++++-
cycode/cyclient/models.py | 36 ++++++++++++
cycode/cyclient/scan_client.py | 57 ++++++++++++++++++-
.../data/detection_rules.json | 20 +++++++
.../cyclient/mocked_responses/scan_client.py | 15 +++++
6 files changed, 170 insertions(+), 3 deletions(-)
create mode 100644 tests/cyclient/mocked_responses/data/detection_rules.json
diff --git a/cycode/cli/commands/scan/code_scanner.py b/cycode/cli/commands/scan/code_scanner.py
index 8ac6c05b..7cd596d0 100644
--- a/cycode/cli/commands/scan/code_scanner.py
+++ b/cycode/cli/commands/scan/code_scanner.py
@@ -99,6 +99,35 @@ def set_issue_detected_by_scan_results(context: click.Context, scan_results: Lis
set_issue_detected(context, any(scan_result.issue_detected for scan_result in scan_results))
+def _enrich_scan_result_with_data_from_detection_rules(
+ cycode_client: 'ScanClient', scan_type: str, scan_result: ZippedFileScanResult
+) -> None:
+ # TODO(MarshalX): remove scan_type arg after migration to new backend filter
+ if scan_type != consts.SECRET_SCAN_TYPE:
+ # not yet
+ return
+
+ detection_rule_ids = set()
+ for detections_per_file in scan_result.detections_per_file:
+ for detection in detections_per_file.detections:
+ detection_rule_ids.add(detection.detection_rule_id)
+
+ detection_rules = cycode_client.get_detection_rules(scan_type, detection_rule_ids)
+ detection_rules_by_id = {detection_rule.detection_rule_id: detection_rule for detection_rule in detection_rules}
+
+ for detections_per_file in scan_result.detections_per_file:
+ for detection in detections_per_file.detections:
+ detection_rule = detection_rules_by_id.get(detection.detection_rule_id)
+ if not detection_rule:
+ # we want to make sure that BE returned it. better to not map data instead of failed scan
+ continue
+
+ # TODO(MarshalX): here we can also map severity without migrating secrets to async flow
+
+ # detection_details never was typed properly. so not a problem for now
+ detection.detection_details['custom_remediation_guidelines'] = detection_rule.custom_remediation_guidelines
+
+
def _get_scan_documents_thread_func(
context: click.Context, is_git_diff: bool, is_commit_range: bool, scan_parameters: dict
) -> Callable[[List[Document]], Tuple[str, CliError, LocalScanResult]]:
@@ -123,6 +152,8 @@ def _scan_batch_thread_func(batch: List[Document]) -> Tuple[str, CliError, Local
cycode_client, zipped_documents, scan_type, scan_id, is_git_diff, is_commit_range, scan_parameters
)
+ _enrich_scan_result_with_data_from_detection_rules(cycode_client, scan_type, scan_result)
+
local_scan_result = create_local_scan_result(
scan_result, batch, command_scan_type, scan_type, severity_threshold
)
diff --git a/cycode/cli/printers/text_printer.py b/cycode/cli/printers/text_printer.py
index 821e755f..2bbab6a3 100644
--- a/cycode/cli/printers/text_printer.py
+++ b/cycode/cli/printers/text_printer.py
@@ -68,6 +68,7 @@ def _print_detection_summary(
self, detection: Detection, document_path: str, scan_id: str, report_url: Optional[str]
) -> None:
detection_name = detection.type if self.scan_type == SECRET_SCAN_TYPE else detection.message
+ detection_name_styled = click.style(detection_name, fg='bright_red', bold=True)
detection_sha = detection.detection_details.get('sha512')
detection_sha_message = f'\nSecret SHA: {detection_sha}' if detection_sha else ''
@@ -78,10 +79,19 @@ def _print_detection_summary(
detection_commit_id = detection.detection_details.get('commit_id')
detection_commit_id_message = f'\nCommit SHA: {detection_commit_id}' if detection_commit_id else ''
+ company_guidelines = detection.detection_details.get('custom_remediation_guidelines')
+ company_guidelines_message = f'\nCompany Guideline: {company_guidelines}' if company_guidelines else ''
+
click.echo(
- f'⛔ Found issue of type: {click.style(detection_name, fg="bright_red", bold=True)} '
+ f'⛔ '
+ f'Found issue of type: {detection_name_styled} '
f'(rule ID: {detection.detection_rule_id}) in file: {click.format_filename(document_path)} '
- f'{detection_sha_message}{scan_id_message}{report_url_message}{detection_commit_id_message} ⛔'
+ f'{detection_sha_message}'
+ f'{scan_id_message}'
+ f'{report_url_message}'
+ f'{detection_commit_id_message}'
+ f'{company_guidelines_message}'
+ f' ⛔'
)
def _print_detection_code_segment(self, detection: Detection, document: Document, code_segment_size: int) -> None:
diff --git a/cycode/cyclient/models.py b/cycode/cyclient/models.py
index 0401e3fb..aef9748d 100644
--- a/cycode/cyclient/models.py
+++ b/cycode/cyclient/models.py
@@ -404,3 +404,39 @@ class Meta:
@post_load
def build_dto(self, data: Dict[str, Any], **_) -> SbomReport:
return SbomReport(**data)
+
+
+@dataclass
+class ClassificationData:
+ severity: str
+
+
+class ClassificationDataSchema(Schema):
+ class Meta:
+ unknown = EXCLUDE
+
+ severity = fields.String()
+
+ @post_load
+ def build_dto(self, data: Dict[str, Any], **_) -> ClassificationData:
+ return ClassificationData(**data)
+
+
+@dataclass
+class DetectionRule:
+ classification_data: List[ClassificationData]
+ detection_rule_id: str
+ custom_remediation_guidelines: Optional[str] = None
+
+
+class DetectionRuleSchema(Schema):
+ class Meta:
+ unknown = EXCLUDE
+
+ classification_data = fields.Nested(ClassificationDataSchema, many=True)
+ detection_rule_id = fields.String()
+ custom_remediation_guidelines = fields.String(allow_none=True)
+
+ @post_load
+ def build_dto(self, data: Dict[str, Any], **_) -> DetectionRule:
+ return DetectionRule(**data)
diff --git a/cycode/cyclient/scan_client.py b/cycode/cyclient/scan_client.py
index 50ee0e79..30036fcd 100644
--- a/cycode/cyclient/scan_client.py
+++ b/cycode/cyclient/scan_client.py
@@ -1,8 +1,10 @@
import json
-from typing import TYPE_CHECKING, List, Optional
+from typing import TYPE_CHECKING, List, Optional, Set, Union
from requests import Response
+from cycode.cli import consts
+from cycode.cli.exceptions.custom_exceptions import CycodeError
from cycode.cli.files_collector.models.in_memory_zip import InMemoryZip
from cycode.cyclient import models
from cycode.cyclient.cycode_client_base import CycodeClientBase
@@ -20,6 +22,7 @@ def __init__(
self.SCAN_CONTROLLER_PATH = 'api/v1/scan'
self.DETECTIONS_SERVICE_CONTROLLER_PATH = 'api/v1/detections'
+ self.POLICIES_SERVICE_CONTROLLER_PATH_V3 = 'api/v3/policies'
self._hide_response_log = hide_response_log
@@ -95,6 +98,58 @@ def get_scan_details(self, scan_id: str) -> models.ScanDetailsResponse:
response = self.scan_cycode_client.get(url_path=self.get_scan_details_path(scan_id))
return models.ScanDetailsResponseSchema().load(response.json())
+ def get_detection_rules_path(self) -> str:
+ return (
+ f'{self.scan_config.get_detections_prefix()}/'
+ f'{self.POLICIES_SERVICE_CONTROLLER_PATH_V3}/'
+ f'detection_rules'
+ )
+
+ @staticmethod
+ def _get_policy_type_by_scan_type(scan_type: str) -> str:
+ scan_type_to_policy_type = {
+ consts.INFRA_CONFIGURATION_SCAN_TYPE: 'IaC',
+ consts.SCA_SCAN_TYPE: 'SCA',
+ consts.SECRET_SCAN_TYPE: 'SecretDetection',
+ consts.SAST_SCAN_TYPE: 'SAST',
+ }
+
+ if scan_type not in scan_type_to_policy_type:
+ raise CycodeError('Invalid scan type')
+
+ return scan_type_to_policy_type[scan_type]
+
+ @staticmethod
+ def _filter_detection_rules_by_ids(
+ detection_rules: List[models.DetectionRule], detection_rules_ids: Union[Set[str], List[str]]
+ ) -> List[models.DetectionRule]:
+ ids = set(detection_rules_ids) # cast to set to perform faster search
+ return [rule for rule in detection_rules if rule.detection_rule_id in ids]
+
+ @staticmethod
+ def parse_detection_rules_response(response: Response) -> List[models.DetectionRule]:
+ return models.DetectionRuleSchema().load(response.json(), many=True)
+
+ def get_detection_rules(
+ self, scan_type: str, detection_rules_ids: Union[Set[str], List[str]]
+ ) -> List[models.DetectionRule]:
+ # TODO(MarshalX): use filter by list of IDs instead of policy_type when BE will be ready
+ params = {
+ 'include_hidden': False,
+ 'include_only_enabled_detection_rules': True,
+ 'page_number': 0,
+ 'page_size': 5000,
+ 'policy_types_v2': self._get_policy_type_by_scan_type(scan_type),
+ }
+ response = self.scan_cycode_client.get(
+ url_path=self.get_detection_rules_path(),
+ params=params,
+ hide_response_content_log=self._hide_response_log,
+ )
+
+ # we are filtering rules by ids in-place for smooth migration when backend will be ready
+ return self._filter_detection_rules_by_ids(self.parse_detection_rules_response(response), detection_rules_ids)
+
def get_scan_detections_path(self) -> str:
return f'{self.scan_config.get_detections_prefix()}/{self.DETECTIONS_SERVICE_CONTROLLER_PATH}'
diff --git a/tests/cyclient/mocked_responses/data/detection_rules.json b/tests/cyclient/mocked_responses/data/detection_rules.json
new file mode 100644
index 00000000..b221951a
--- /dev/null
+++ b/tests/cyclient/mocked_responses/data/detection_rules.json
@@ -0,0 +1,20 @@
+[
+ {
+ "classification_data": [
+ {
+ "severity": "High",
+ "classification_rule_id": "e4e826bd-5820-4cc9-ae5b-bbfceb500a21"
+ }
+ ],
+ "detection_rule_id": "26ab3395-2522-4061-a50a-c69c2d622ca1"
+ },
+ {
+ "classification_data": [
+ {
+ "severity": "High",
+ "classification_rule_id": "e4e826bd-5820-4cc9-ae5b-bbfceb500a22"
+ }
+ ],
+ "detection_rule_id": "12345678-aea1-4304-a6e9-012345678901"
+ }
+]
diff --git a/tests/cyclient/mocked_responses/scan_client.py b/tests/cyclient/mocked_responses/scan_client.py
index dff10003..de1613c9 100644
--- a/tests/cyclient/mocked_responses/scan_client.py
+++ b/tests/cyclient/mocked_responses/scan_client.py
@@ -146,6 +146,19 @@ def get_report_scan_status_response(url: str) -> responses.Response:
return responses.Response(method=responses.POST, url=url, status=200)
+def get_detection_rules_url(scan_client: ScanClient) -> str:
+ api_url = scan_client.scan_cycode_client.api_url
+ service_url = scan_client.get_detection_rules_path()
+ return f'{api_url}/{service_url}'
+
+
+def get_detection_rules_response(url: str) -> responses.Response:
+ with open(MOCKED_RESPONSES_PATH.joinpath('detection_rules.json'), encoding='UTF-8') as f:
+ json_response = json.load(f)
+
+ return responses.Response(method=responses.GET, url=url, json=json_response, status=200)
+
+
def mock_scan_async_responses(
responses_module: responses, scan_type: str, scan_client: ScanClient, scan_id: UUID, zip_content_path: Path
) -> None:
@@ -153,6 +166,7 @@ def mock_scan_async_responses(
get_zipped_file_scan_async_response(get_zipped_file_scan_async_url(scan_type, scan_client), scan_id)
)
responses_module.add(get_scan_details_response(get_scan_details_url(scan_id, scan_client), scan_id))
+ responses_module.add(get_detection_rules_response(get_detection_rules_url(scan_client)))
responses_module.add(get_scan_detections_count_response(get_scan_detections_count_url(scan_client)))
responses_module.add(get_scan_detections_response(get_scan_detections_url(scan_client), scan_id, zip_content_path))
responses_module.add(get_report_scan_status_response(get_report_scan_status_url(scan_type, scan_id, scan_client)))
@@ -164,4 +178,5 @@ def mock_scan_responses(
responses_module.add(
get_zipped_file_scan_response(get_zipped_file_scan_url(scan_type, scan_client), zip_content_path)
)
+ responses_module.add(get_detection_rules_response(get_detection_rules_url(scan_client)))
responses_module.add(get_report_scan_status_response(get_report_scan_status_url(scan_type, scan_id, scan_client)))
From ed45fad26e21f8da655d5fc0c100f3a0e648116e Mon Sep 17 00:00:00 2001
From: Ilya Siamionau
Date: Wed, 13 Dec 2023 12:13:11 +0100
Subject: [PATCH 053/257] CM-30183 - Add severity for secret detections (#185)
---
cycode/cli/commands/scan/code_scanner.py | 6 +++++-
1 file changed, 5 insertions(+), 1 deletion(-)
diff --git a/cycode/cli/commands/scan/code_scanner.py b/cycode/cli/commands/scan/code_scanner.py
index 7cd596d0..753f1410 100644
--- a/cycode/cli/commands/scan/code_scanner.py
+++ b/cycode/cli/commands/scan/code_scanner.py
@@ -122,7 +122,11 @@ def _enrich_scan_result_with_data_from_detection_rules(
# we want to make sure that BE returned it. better to not map data instead of failed scan
continue
- # TODO(MarshalX): here we can also map severity without migrating secrets to async flow
+ if detection_rule.classification_data:
+ # it's fine to take the first one, because:
+ # - for "secrets" and "iac" there is only one classification rule per detection rule
+ # - for "sca" and "sast" we get severity from detection service
+ detection.severity = detection_rule.classification_data[0].severity
# detection_details never was typed properly. so not a problem for now
detection.detection_details['custom_remediation_guidelines'] = detection_rule.custom_remediation_guidelines
From d5014e3ac3cdd23bc93ea8c1f62a54fd3ce2480a Mon Sep 17 00:00:00 2001
From: Ilya Siamionau
Date: Thu, 21 Dec 2023 14:59:33 +0100
Subject: [PATCH 054/257] CM-30405 - Add building of executable CLI in the
onedir mode and ARM macOS (#187)
---
.github/workflows/build_executable.yml | 91 ++++++++++++++++++--------
.github/workflows/tests_full.yml | 3 +-
poetry.lock | 26 ++++----
pyinstaller.spec | 60 +++++++----------
pyproject.toml | 2 +-
5 files changed, 102 insertions(+), 80 deletions(-)
diff --git a/.github/workflows/build_executable.yml b/.github/workflows/build_executable.yml
index a0a0e706..0de165b6 100644
--- a/.github/workflows/build_executable.yml
+++ b/.github/workflows/build_executable.yml
@@ -11,10 +11,17 @@ permissions:
jobs:
build:
+ name: Build on ${{ matrix.os }} (${{ matrix.mode }} mode)
strategy:
fail-fast: false
matrix:
- os: [ ubuntu-20.04, macos-11, windows-2019 ]
+ os: [ ubuntu-20.04, macos-11, macos-13-xlarge, windows-2019 ]
+ mode: [ 'onefile', 'onedir' ]
+ exclude:
+ - os: ubuntu-20.04
+ mode: onedir
+ - os: windows-2019
+ mode: onedir
runs-on: ${{ matrix.os }}
@@ -48,17 +55,17 @@ jobs:
git checkout $LATEST_TAG
echo "LATEST_TAG=$LATEST_TAG" >> $GITHUB_ENV
- - name: Set up Python 3.7
+ - name: Set up Python 3.12
uses: actions/setup-python@v4
with:
- python-version: '3.7'
+ python-version: '3.12'
- name: Load cached Poetry setup
id: cached-poetry
uses: actions/cache@v3
with:
path: ~/.local
- key: poetry-${{ matrix.os }}-0 # increment to reset cache
+ key: poetry-${{ matrix.os }}-1 # increment to reset cache
- name: Setup Poetry
if: steps.cached-poetry.outputs.cache-hit != 'true'
@@ -70,15 +77,9 @@ jobs:
run: echo "$HOME/.local/bin" >> $GITHUB_PATH
- name: Install dependencies
- run: poetry install
+ run: poetry install --without dev,test
- - name: Build executable
- run: poetry run pyinstaller pyinstaller.spec
-
- - name: Test executable
- run: ./dist/cycode version
-
- - name: Sign macOS executable
+ - name: Import macOS signing certificate
if: runner.os == 'macOS'
env:
APPLE_CERT: ${{ secrets.APPLE_CERT }}
@@ -100,8 +101,25 @@ jobs:
security import $CERTIFICATE_PATH -P "$APPLE_CERT_PWD" -A -t cert -f pkcs12 -k $KEYCHAIN_PATH
security list-keychain -d user -s $KEYCHAIN_PATH
- # sign executable
- codesign --deep --force --options=runtime --entitlements entitlements.plist --sign "$APPLE_CERT_NAME" --timestamp dist/cycode
+ - name: Build executable (onefile)
+ if: matrix.mode == 'onefile'
+ env:
+ APPLE_CERT_NAME: ${{ secrets.APPLE_CERT_NAME }}
+ run: |
+ poetry run pyinstaller pyinstaller.spec
+ echo "PATH_TO_CYCODE_CLI_EXECUTABLE=dist/cycode-cli" >> $GITHUB_ENV
+
+ - name: Build executable (onedir)
+ if: matrix.mode == 'onedir'
+ env:
+ CYCODE_ONEDIR_MODE: 1
+ APPLE_CERT_NAME: ${{ secrets.APPLE_CERT_NAME }}
+ run: |
+ poetry run pyinstaller pyinstaller.spec
+ echo "PATH_TO_CYCODE_CLI_EXECUTABLE=dist/cycode-cli/cycode-cli" >> $GITHUB_ENV
+
+ - name: Test executable
+ run: time $PATH_TO_CYCODE_CLI_EXECUTABLE version
- name: Notarize macOS executable
if: runner.os == 'macOS'
@@ -114,17 +132,20 @@ jobs:
xcrun notarytool store-credentials "notarytool-profile" --apple-id "$APPLE_NOTARIZATION_EMAIL" --team-id "$APPLE_NOTARIZATION_TEAM_ID" --password "$APPLE_NOTARIZATION_PWD"
# create zip file (notarization does not support binaries)
- ditto -c -k --keepParent dist/cycode notarization.zip
+ ditto -c -k --keepParent dist/cycode-cli notarization.zip
# notarize app (this will take a while)
xcrun notarytool submit notarization.zip --keychain-profile "notarytool-profile" --wait
- # we can't staple the app because it's executable. we should only staple app bundles like .dmg
- # xcrun stapler staple dist/cycode
+ # we can't staple the app because it's executable
- name: Test macOS signed executable
if: runner.os == 'macOS'
- run: ./dist/cycode version
+ run: |
+ time $PATH_TO_CYCODE_CLI_EXECUTABLE version
+
+ # verify signature
+ codesign -dv --verbose=4 $PATH_TO_CYCODE_CLI_EXECUTABLE
- name: Import cert for Windows and setup envs
if: runner.os == 'Windows'
@@ -155,39 +176,57 @@ jobs:
smksp_cert_sync.exe
:: sign executable
- signtool.exe sign /sha1 %SM_CODE_SIGNING_CERT_SHA1_HASH% /tr http://timestamp.digicert.com /td SHA256 /fd SHA256 ".\dist\cycode.exe"
+ signtool.exe sign /sha1 %SM_CODE_SIGNING_CERT_SHA1_HASH% /tr http://timestamp.digicert.com /td SHA256 /fd SHA256 ".\dist\cycode-cli.exe"
- name: Test Windows signed executable
if: runner.os == 'Windows'
shell: cmd
run: |
:: call executable and expect correct output
- .\dist\cycode.exe version
+ .\dist\cycode-cli.exe version
:: verify signature
- signtool.exe verify /v /pa ".\dist\cycode.exe"
+ signtool.exe verify /v /pa ".\dist\cycode-cli.exe"
- name: Prepare files on Windows
if: runner.os == 'Windows'
run: |
echo "ARTIFACT_NAME=cycode-win" >> $GITHUB_ENV
- mv dist/cycode.exe dist/cycode-win.exe
+ mv dist/cycode-cli.exe dist/cycode-win.exe
powershell -Command "(Get-FileHash -Algorithm SHA256 dist/cycode-win.exe).Hash" > sha256
head -c 64 sha256 > dist/cycode-win.exe.sha256
- - name: Prepare files on macOS
- if: runner.os == 'macOS'
+ - name: Prepare files on Intel macOS (onefile)
+ if: runner.os == 'macOS' && runner.arch == 'X64' && matrix.mode == 'onefile'
run: |
echo "ARTIFACT_NAME=cycode-mac" >> $GITHUB_ENV
- mv dist/cycode dist/cycode-mac
+ mv dist/cycode-cli dist/cycode-mac
shasum -a 256 dist/cycode-mac > sha256
head -c 64 sha256 > dist/cycode-mac.sha256
+ - name: Prepare files on Apple Silicon macOS (onefile)
+ if: runner.os == 'macOS' && runner.arch == 'ARM64' && matrix.mode == 'onefile'
+ run: |
+ echo "ARTIFACT_NAME=cycode-mac-arm" >> $GITHUB_ENV
+ mv dist/cycode-cli dist/cycode-mac-arm
+ shasum -a 256 dist/cycode-mac-arm > sha256
+ head -c 64 sha256 > dist/cycode-mac-arm.sha256
+
+ - name: Prepare files on Intel macOS (onedir)
+ if: runner.os == 'macOS' && runner.arch == 'X64' && matrix.mode == 'onedir'
+ run: |
+ echo "ARTIFACT_NAME=cycode-mac-onedir" >> $GITHUB_ENV
+
+ - name: Prepare files on Apple Silicon macOS (onedir)
+ if: runner.os == 'macOS' && runner.arch == 'ARM64' && matrix.mode == 'onedir'
+ run: |
+ echo "ARTIFACT_NAME=cycode-mac-arm-onedir" >> $GITHUB_ENV
+
- name: Prepare files on Linux
if: runner.os == 'Linux'
run: |
echo "ARTIFACT_NAME=cycode-linux" >> $GITHUB_ENV
- mv dist/cycode dist/cycode-linux
+ mv dist/cycode-cli dist/cycode-linux
sha256sum dist/cycode-linux > sha256
head -c 64 sha256 > dist/cycode-linux.sha256
diff --git a/.github/workflows/tests_full.yml b/.github/workflows/tests_full.yml
index aaa58d89..8225b0c3 100644
--- a/.github/workflows/tests_full.yml
+++ b/.github/workflows/tests_full.yml
@@ -64,10 +64,9 @@ jobs:
run: poetry install
- name: Run executable test
- if: runner.os == 'Linux'
run: |
poetry run pyinstaller pyinstaller.spec
- ./dist/cycode version
+ ./dist/cycode-cli version
- name: Run pytest
run: poetry run pytest
diff --git a/poetry.lock b/poetry.lock
index 46d5ffcd..e4e96a4d 100644
--- a/poetry.lock
+++ b/poetry.lock
@@ -92,13 +92,13 @@ uvloop = ["uvloop (>=0.15.2)"]
[[package]]
name = "certifi"
-version = "2023.7.22"
+version = "2023.11.17"
description = "Python package for providing Mozilla's CA Bundle."
optional = false
python-versions = ">=3.6"
files = [
- {file = "certifi-2023.7.22-py3-none-any.whl", hash = "sha256:92d6037539857d8206b8f6ae472e8b77db8058fec5937a1ef3f54304089edbb9"},
- {file = "certifi-2023.7.22.tar.gz", hash = "sha256:539cc1d13202e33ca466e88b2807e29f4c13049d6d87031a3c110744495cb082"},
+ {file = "certifi-2023.11.17-py3-none-any.whl", hash = "sha256:e036ab49d5b79556f99cfc2d9320b34cfbe5be05c5871b51de9329f0603b0474"},
+ {file = "certifi-2023.11.17.tar.gz", hash = "sha256:9b469f3a900bf28dc19b8cfbf8019bf47f7fdd1a65a1d4ffb98fc14166beb4d1"},
]
[[package]]
@@ -326,13 +326,13 @@ packaging = ">=20.9"
[[package]]
name = "exceptiongroup"
-version = "1.1.3"
+version = "1.2.0"
description = "Backport of PEP 654 (exception groups)"
optional = false
python-versions = ">=3.7"
files = [
- {file = "exceptiongroup-1.1.3-py3-none-any.whl", hash = "sha256:343280667a4585d195ca1cf9cef84a4e178c4b6cf2274caef9859782b567d5e3"},
- {file = "exceptiongroup-1.1.3.tar.gz", hash = "sha256:097acd85d473d75af5bb98e41b61ff7fe35efe6675e4f9370ec6ec5126d160e9"},
+ {file = "exceptiongroup-1.2.0-py3-none-any.whl", hash = "sha256:4bfd3996ac73b41e9b9628b04e079f193850720ea5945fc96a08633c66912f14"},
+ {file = "exceptiongroup-1.2.0.tar.gz", hash = "sha256:91f5c769735f051a4290d52edd0858999b57e5876e9f85937691bd4c9fa3ed68"},
]
[package.extras]
@@ -372,13 +372,13 @@ test = ["black", "coverage[toml]", "ddt (>=1.1.1,!=1.4.3)", "mock", "mypy", "pre
[[package]]
name = "idna"
-version = "3.4"
+version = "3.6"
description = "Internationalized Domain Names in Applications (IDNA)"
optional = false
python-versions = ">=3.5"
files = [
- {file = "idna-3.4-py3-none-any.whl", hash = "sha256:90b77e79eaa3eba6de819a0c442c0b4ceefc341a7a2ab77d7562bf49f425c5c2"},
- {file = "idna-3.4.tar.gz", hash = "sha256:814f528e8dead7d329833b91c5faa87d60bf71824cd12a7530b5526063d02cb4"},
+ {file = "idna-3.6-py3-none-any.whl", hash = "sha256:c05567e9c24a6b9faaa835c4821bad0590fbb9d5779e7caa6e1cc4978e7eb24f"},
+ {file = "idna-3.6.tar.gz", hash = "sha256:9ecdbbd083b06798ae1e86adcbfe8ab1479cf864e4ee30fe4e46a003d12491ca"},
]
[[package]]
@@ -508,13 +508,13 @@ files = [
[[package]]
name = "platformdirs"
-version = "3.11.0"
+version = "4.0.0"
description = "A small Python package for determining appropriate platform-specific dirs, e.g. a \"user data dir\"."
optional = false
python-versions = ">=3.7"
files = [
- {file = "platformdirs-3.11.0-py3-none-any.whl", hash = "sha256:e9d171d00af68be50e9202731309c4e658fd8bc76f55c11c7dd760d023bda68e"},
- {file = "platformdirs-3.11.0.tar.gz", hash = "sha256:cf8ee52a3afdb965072dcc652433e0c7e3e40cf5ea1477cd4b3b1d2eb75495b3"},
+ {file = "platformdirs-4.0.0-py3-none-any.whl", hash = "sha256:118c954d7e949b35437270383a3f2531e99dd93cf7ce4dc8340d3356d30f173b"},
+ {file = "platformdirs-4.0.0.tar.gz", hash = "sha256:cb633b2bcf10c51af60beb0ab06d2f1d69064b43abf4c185ca6b28865f3f9731"},
]
[package.dependencies]
@@ -935,4 +935,4 @@ testing = ["big-O", "flake8 (<5)", "jaraco.functools", "jaraco.itertools", "more
[metadata]
lock-version = "2.0"
python-versions = ">=3.7,<3.13"
-content-hash = "016a02b0698698558aa590693fdda4a0ce558e247da4ed1eaf7b9315881575f6"
+content-hash = "9c77c886972dc6da818e14a175507a87fe32c773824ef40ee3fab9c0725e9fe4"
diff --git a/pyinstaller.spec b/pyinstaller.spec
index 6409682a..cb3382d4 100644
--- a/pyinstaller.spec
+++ b/pyinstaller.spec
@@ -1,64 +1,48 @@
# -*- mode: python ; coding: utf-8 -*-
# Run `poetry run pyinstaller pyinstaller.spec` to generate the binary.
+# Set the env var `CYCODE_ONEDIR_MODE` to generate a single directory instead of a single file.
-
-block_cipher = None
-
-INIT_FILE_PATH = os.path.join('cycode', '__init__.py')
+_INIT_FILE_PATH = os.path.join('cycode', '__init__.py')
+_CODESIGN_IDENTITY = os.environ.get('APPLE_CERT_NAME')
+_ONEDIR_MODE = os.environ.get('CYCODE_ONEDIR_MODE') is not None
# save the prev content of __init__ file
-with open(INIT_FILE_PATH, 'r', encoding='UTF-8') as file:
+with open(_INIT_FILE_PATH, 'r', encoding='UTF-8') as file:
prev_content = file.read()
import dunamai as _dunamai
+
VERSION_PLACEHOLDER = '0.0.0'
CLI_VERSION = _dunamai.get_version('cycode', first_choice=_dunamai.Version.from_git).serialize(
metadata=False, bump=True, style=_dunamai.Style.Pep440
)
-# write version from Git Tag to freeze the value and don't depend on Git
-with open(INIT_FILE_PATH, 'w', encoding='UTF-8') as file:
+# write the version from Git Tag to freeze the value and don't depend on Git
+with open(_INIT_FILE_PATH, 'w', encoding='UTF-8') as file:
file.write(prev_content.replace(VERSION_PLACEHOLDER, CLI_VERSION))
a = Analysis(
- ['cycode/cli/main.py'],
- pathex=[],
- binaries=[],
+ scripts=['cycode/cli/main.py'],
datas=[('cycode/cli/config.yaml', 'cycode/cli'), ('cycode/cyclient/config.yaml', 'cycode/cyclient')],
- hiddenimports=[],
- hookspath=[],
- hooksconfig={},
- runtime_hooks=[],
excludes=['tests'],
- win_no_prefer_redirects=False,
- win_private_assemblies=False,
- cipher=block_cipher,
- noarchive=False,
)
-pyz = PYZ(a.pure, a.zipped_data, cipher=block_cipher)
+
+exe_args = [PYZ(a.pure, a.zipped_data), a.scripts, a.binaries, a.zipfiles, a.datas]
+if _ONEDIR_MODE:
+ exe_args = [PYZ(a.pure), a.scripts]
exe = EXE(
- pyz,
- a.scripts,
- a.binaries,
- a.zipfiles,
- a.datas,
- [],
- name='cycode',
- debug=False,
- bootloader_ignore_signals=False,
- strip=False,
- upx=True,
- upx_exclude=[],
- runtime_tmpdir=None,
- console=True,
- disable_windowed_traceback=False,
- argv_emulation=False,
+ *exe_args,
+ name='cycode-cli',
+ exclude_binaries=bool(_ONEDIR_MODE),
target_arch=None,
- codesign_identity=None,
- entitlements_file=None,
+ codesign_identity=_CODESIGN_IDENTITY,
+ entitlements_file='entitlements.plist',
)
+if _ONEDIR_MODE:
+ coll = COLLECT(exe, a.binaries, a.datas, name='cycode-cli')
+
# rollback the prev content of the __init__ file
-with open(INIT_FILE_PATH, 'w', encoding='UTF-8') as file:
+with open(_INIT_FILE_PATH, 'w', encoding='UTF-8') as file:
file.write(prev_content)
diff --git a/pyproject.toml b/pyproject.toml
index b0057fd1..272e3bb2 100644
--- a/pyproject.toml
+++ b/pyproject.toml
@@ -48,7 +48,7 @@ coverage = ">=7.2.3,<7.3.0"
responses = ">=0.23.1,<0.24.0"
[tool.poetry.group.executable.dependencies]
-pyinstaller = ">=5.13.0,<5.14.0"
+pyinstaller = ">=5.13.2,<5.14.0"
dunamai = ">=1.18.0,<1.19.0"
[tool.poetry.group.dev.dependencies]
From dbab52b6a35a3a4071d9b43e0324cbc59ed01426 Mon Sep 17 00:00:00 2001
From: morsa4406 <104304449+morsa4406@users.noreply.github.com>
Date: Mon, 1 Jan 2024 12:46:33 +0200
Subject: [PATCH 055/257] CM-30756 fixing route to scan-service and
detectionsonline-service in order to skip check projects (#188)
---
cycode/cyclient/scan_client.py | 6 +++---
1 file changed, 3 insertions(+), 3 deletions(-)
diff --git a/cycode/cyclient/scan_client.py b/cycode/cyclient/scan_client.py
index 30036fcd..cf15798f 100644
--- a/cycode/cyclient/scan_client.py
+++ b/cycode/cyclient/scan_client.py
@@ -20,8 +20,8 @@ def __init__(
self.scan_cycode_client = scan_cycode_client
self.scan_config = scan_config
- self.SCAN_CONTROLLER_PATH = 'api/v1/scan'
- self.DETECTIONS_SERVICE_CONTROLLER_PATH = 'api/v1/detections'
+ self.SCAN_CONTROLLER_PATH = 'api/v1/cli-scan'
+ self.DETECTIONS_SERVICE_CONTROLLER_PATH = 'api/v1/detections/cli'
self.POLICIES_SERVICE_CONTROLLER_PATH_V3 = 'api/v3/policies'
self._hide_response_log = hide_response_log
@@ -151,7 +151,7 @@ def get_detection_rules(
return self._filter_detection_rules_by_ids(self.parse_detection_rules_response(response), detection_rules_ids)
def get_scan_detections_path(self) -> str:
- return f'{self.scan_config.get_detections_prefix()}/{self.DETECTIONS_SERVICE_CONTROLLER_PATH}'
+ return f'{self.scan_config.get_detections_prefix()}/{self.DETECTIONS_SERVICE_CONTROLLER_PATH}/detections'
def get_scan_detections(self, scan_id: str) -> List[dict]:
params = {'scan_id': scan_id}
From 64e2f28af28410e3e3fd31276cbe1a1460ef8ac8 Mon Sep 17 00:00:00 2001
From: Ilya Siamionau
Date: Tue, 9 Jan 2024 12:12:29 +0100
Subject: [PATCH 056/257] CM-30406 - Attach onedir CLI to GitHub releases with
checksums (#189)
---
.github/workflows/build_executable.yml | 43 +------
process_executable_file.py | 164 +++++++++++++++++++++++++
2 files changed, 166 insertions(+), 41 deletions(-)
create mode 100755 process_executable_file.py
diff --git a/.github/workflows/build_executable.yml b/.github/workflows/build_executable.yml
index 0de165b6..dcf2a42b 100644
--- a/.github/workflows/build_executable.yml
+++ b/.github/workflows/build_executable.yml
@@ -188,47 +188,8 @@ jobs:
:: verify signature
signtool.exe verify /v /pa ".\dist\cycode-cli.exe"
- - name: Prepare files on Windows
- if: runner.os == 'Windows'
- run: |
- echo "ARTIFACT_NAME=cycode-win" >> $GITHUB_ENV
- mv dist/cycode-cli.exe dist/cycode-win.exe
- powershell -Command "(Get-FileHash -Algorithm SHA256 dist/cycode-win.exe).Hash" > sha256
- head -c 64 sha256 > dist/cycode-win.exe.sha256
-
- - name: Prepare files on Intel macOS (onefile)
- if: runner.os == 'macOS' && runner.arch == 'X64' && matrix.mode == 'onefile'
- run: |
- echo "ARTIFACT_NAME=cycode-mac" >> $GITHUB_ENV
- mv dist/cycode-cli dist/cycode-mac
- shasum -a 256 dist/cycode-mac > sha256
- head -c 64 sha256 > dist/cycode-mac.sha256
-
- - name: Prepare files on Apple Silicon macOS (onefile)
- if: runner.os == 'macOS' && runner.arch == 'ARM64' && matrix.mode == 'onefile'
- run: |
- echo "ARTIFACT_NAME=cycode-mac-arm" >> $GITHUB_ENV
- mv dist/cycode-cli dist/cycode-mac-arm
- shasum -a 256 dist/cycode-mac-arm > sha256
- head -c 64 sha256 > dist/cycode-mac-arm.sha256
-
- - name: Prepare files on Intel macOS (onedir)
- if: runner.os == 'macOS' && runner.arch == 'X64' && matrix.mode == 'onedir'
- run: |
- echo "ARTIFACT_NAME=cycode-mac-onedir" >> $GITHUB_ENV
-
- - name: Prepare files on Apple Silicon macOS (onedir)
- if: runner.os == 'macOS' && runner.arch == 'ARM64' && matrix.mode == 'onedir'
- run: |
- echo "ARTIFACT_NAME=cycode-mac-arm-onedir" >> $GITHUB_ENV
-
- - name: Prepare files on Linux
- if: runner.os == 'Linux'
- run: |
- echo "ARTIFACT_NAME=cycode-linux" >> $GITHUB_ENV
- mv dist/cycode-cli dist/cycode-linux
- sha256sum dist/cycode-linux > sha256
- head -c 64 sha256 > dist/cycode-linux.sha256
+ - name: Prepare files for artifact and release (rename and calculate sha256)
+ run: echo "ARTIFACT_NAME=$(./process_executable_file.py dist/cycode-cli)" >> $GITHUB_ENV
- name: Upload files as artifact
uses: actions/upload-artifact@v3
diff --git a/process_executable_file.py b/process_executable_file.py
new file mode 100755
index 00000000..eafeada3
--- /dev/null
+++ b/process_executable_file.py
@@ -0,0 +1,164 @@
+#!/usr/bin/env python3
+
+"""
+Used in the GitHub Actions workflow (build_executable.yml) to process the executable file.
+This script calculates hash and renames executable file depending on the OS, arch, and build mode.
+It also creates a file with the hash of the executable file.
+It uses SHA256 algorithm to calculate the hash.
+It returns the name of the executable file which is used as artifact name.
+"""
+
+import argparse
+import hashlib
+import os
+import platform
+from pathlib import Path
+from string import Template
+from typing import List, Tuple, Union
+
+_HASH_FILE_EXT = '.sha256'
+_OS_TO_CLI_DIST_TEMPLATE = {
+ 'darwin': Template('cycode-mac$suffix$ext'),
+ 'linux': Template('cycode-linux$suffix$ext'),
+ 'windows': Template('cycode-win$suffix.exe$ext'),
+}
+_WINDOWS = 'windows'
+_WINDOWS_EXECUTABLE_SUFFIX = '.exe'
+
+DirHashes = List[Tuple[str, str]]
+
+
+def get_hash_of_file(file_path: Union[str, Path]) -> str:
+ with open(file_path, 'rb') as f:
+ return hashlib.sha256(f.read()).hexdigest()
+
+
+def get_hashes_of_many_files(root: str, file_paths: List[str]) -> DirHashes:
+ hashes = []
+
+ for file_path in file_paths:
+ file_path = os.path.join(root, file_path)
+ file_hash = get_hash_of_file(file_path)
+
+ hashes.append((file_hash, file_path))
+
+ return hashes
+
+
+def get_hashes_of_every_file_in_the_directory(dir_path: Path) -> DirHashes:
+ hashes = []
+
+ for root, _, files in os.walk(dir_path):
+ hashes.extend(get_hashes_of_many_files(root, files,))
+
+ return hashes
+
+
+def normalize_hashes_db(hashes: DirHashes, dir_path: Path) -> DirHashes:
+ normalized_hashes = []
+
+ for file_hash, file_path in hashes:
+ relative_file_path = file_path[file_path.find(dir_path.name):]
+ normalized_hashes.append((file_hash, relative_file_path))
+
+ # sort by file path
+ normalized_hashes.sort(key=lambda hash_item: hash_item[1])
+
+ return normalized_hashes
+
+
+def is_arm() -> bool:
+ return platform.machine().lower() in ('arm', 'arm64', 'aarch64')
+
+
+def get_os_name() -> str:
+ return platform.system().lower()
+
+
+def get_cli_file_name(suffix: str = '', ext: str = '') -> str:
+ os_name = get_os_name()
+ if os_name not in _OS_TO_CLI_DIST_TEMPLATE:
+ raise Exception(f'Unsupported OS: {os_name}')
+
+ template = _OS_TO_CLI_DIST_TEMPLATE[os_name]
+ return template.substitute(suffix=suffix, ext=ext)
+
+
+def get_cli_file_suffix(is_onedir: bool) -> str:
+ suffixes = []
+
+ if is_arm():
+ suffixes.append('-arm')
+ if is_onedir:
+ suffixes.append('-onedir')
+
+ return ''.join(suffixes)
+
+
+def write_hash_to_file(file_hash: str, output_path: str) -> None:
+ with open(output_path, 'w') as f:
+ f.write(file_hash)
+
+
+def write_hashes_db_to_file(hashes: DirHashes, output_path: str) -> None:
+ content = ''
+ for file_hash, file_path in hashes:
+ content += f'{file_hash} {file_path}\n'
+
+ with open(output_path, 'w') as f:
+ f.write(content)
+
+
+def get_cli_filename(is_onedir: bool) -> str:
+ return get_cli_file_name(get_cli_file_suffix(is_onedir))
+
+
+def get_cli_path(output_path: Path, is_onedir: bool) -> str:
+ return os.path.join(output_path, get_cli_filename(is_onedir))
+
+
+def get_cli_hash_filename(is_onedir: bool) -> str:
+ return get_cli_file_name(suffix=get_cli_file_suffix(is_onedir), ext=_HASH_FILE_EXT)
+
+
+def get_cli_hash_path(output_path: Path, is_onedir: bool) -> str:
+ return os.path.join(output_path, get_cli_hash_filename(is_onedir))
+
+
+def process_executable_file(input_path: Path, is_onedir: bool) -> str:
+ output_path = input_path.parent
+ hash_file_path = get_cli_hash_path(output_path, is_onedir)
+
+ if is_onedir:
+ hashes = get_hashes_of_every_file_in_the_directory(input_path)
+ normalized_hashes = normalize_hashes_db(hashes, input_path)
+ write_hashes_db_to_file(normalized_hashes, hash_file_path)
+ else:
+ file_hash = get_hash_of_file(input_path)
+ write_hash_to_file(file_hash, hash_file_path)
+
+ # for example rename cycode-cli to cycode-mac or cycode-mac-arm-onedir
+ os.rename(input_path, get_cli_path(output_path, is_onedir))
+
+ return get_cli_filename(is_onedir)
+
+
+def main() -> None:
+ parser = argparse.ArgumentParser()
+ parser.add_argument('input', help='Path to executable or directory')
+
+ args = parser.parse_args()
+ input_path = Path(args.input)
+ is_onedir = input_path.is_dir()
+
+ if get_os_name() == _WINDOWS and not is_onedir and input_path.suffix != _WINDOWS_EXECUTABLE_SUFFIX:
+ # add .exe on windows if was missed (to simplify GHA workflow)
+ input_path = input_path.with_suffix(_WINDOWS_EXECUTABLE_SUFFIX)
+
+ artifact_name = process_executable_file(input_path, is_onedir)
+
+ print(artifact_name) # noqa: T201
+
+
+if __name__ == '__main__':
+ main()
From 9fcd4ca99dbd4aa6091dd8d2c7d85d1eb0420327 Mon Sep 17 00:00:00 2001
From: Ilya Siamionau
Date: Wed, 10 Jan 2024 12:53:44 +0100
Subject: [PATCH 057/257] CM-31141 - Zip onedir CLI to attach to GitHub
releases (#191)
---
process_executable_file.py | 14 ++++++++++++++
1 file changed, 14 insertions(+)
diff --git a/process_executable_file.py b/process_executable_file.py
index eafeada3..84c4081a 100755
--- a/process_executable_file.py
+++ b/process_executable_file.py
@@ -12,10 +12,12 @@
import hashlib
import os
import platform
+import shutil
from pathlib import Path
from string import Template
from typing import List, Tuple, Union
+_ARCHIVE_FORMAT = 'zip'
_HASH_FILE_EXT = '.sha256'
_OS_TO_CLI_DIST_TEMPLATE = {
'darwin': Template('cycode-mac$suffix$ext'),
@@ -125,6 +127,14 @@ def get_cli_hash_path(output_path: Path, is_onedir: bool) -> str:
return os.path.join(output_path, get_cli_hash_filename(is_onedir))
+def get_cli_archive_filename(is_onedir: bool) -> str:
+ return get_cli_file_name(suffix=get_cli_file_suffix(is_onedir))
+
+
+def get_cli_archive_path(output_path: Path, is_onedir: bool) -> str:
+ return os.path.join(output_path, get_cli_archive_filename(is_onedir))
+
+
def process_executable_file(input_path: Path, is_onedir: bool) -> str:
output_path = input_path.parent
hash_file_path = get_cli_hash_path(output_path, is_onedir)
@@ -133,6 +143,10 @@ def process_executable_file(input_path: Path, is_onedir: bool) -> str:
hashes = get_hashes_of_every_file_in_the_directory(input_path)
normalized_hashes = normalize_hashes_db(hashes, input_path)
write_hashes_db_to_file(normalized_hashes, hash_file_path)
+
+ archived_file_path = get_cli_archive_path(output_path, is_onedir)
+ shutil.make_archive(archived_file_path, _ARCHIVE_FORMAT, input_path)
+ shutil.rmtree(input_path)
else:
file_hash = get_hash_of_file(input_path)
write_hash_to_file(file_hash, hash_file_path)
From 9da7d6d1e52dd21258c578808a0502e9d3cb905d Mon Sep 17 00:00:00 2001
From: Ilya Siamionau
Date: Wed, 10 Jan 2024 15:00:46 +0100
Subject: [PATCH 058/257] CM-31107 - Fix new CLI endpoints that should be
applied to SCA scans only (#190)
---
cycode/cli/commands/scan/code_scanner.py | 25 ++++---
cycode/cyclient/scan_client.py | 69 ++++++++++++-------
cycode/cyclient/scan_config_base.py | 10 ---
process_executable_file.py | 9 ++-
.../cyclient/mocked_responses/scan_client.py | 8 ++-
.../scan_config/test_default_scan_config.py | 6 --
.../scan_config/test_dev_scan_config.py | 6 --
7 files changed, 70 insertions(+), 63 deletions(-)
diff --git a/cycode/cli/commands/scan/code_scanner.py b/cycode/cli/commands/scan/code_scanner.py
index 753f1410..d700da55 100644
--- a/cycode/cli/commands/scan/code_scanner.py
+++ b/cycode/cli/commands/scan/code_scanner.py
@@ -439,7 +439,7 @@ def perform_scan_async(
scan_async_result = cycode_client.zipped_file_scan_async(zipped_documents, scan_type, scan_parameters)
logger.debug('scan request has been triggered successfully, scan id: %s', scan_async_result.scan_id)
- return poll_scan_results(cycode_client, scan_async_result.scan_id)
+ return poll_scan_results(cycode_client, scan_async_result.scan_id, scan_type)
def perform_commit_range_scan_async(
@@ -455,11 +455,14 @@ def perform_commit_range_scan_async(
)
logger.debug('scan request has been triggered successfully, scan id: %s', scan_async_result.scan_id)
- return poll_scan_results(cycode_client, scan_async_result.scan_id, timeout)
+ return poll_scan_results(cycode_client, scan_async_result.scan_id, scan_type, timeout)
def poll_scan_results(
- cycode_client: 'ScanClient', scan_id: str, polling_timeout: Optional[int] = None
+ cycode_client: 'ScanClient',
+ scan_id: str,
+ scan_type: str,
+ polling_timeout: Optional[int] = None,
) -> ZippedFileScanResult:
if polling_timeout is None:
polling_timeout = configuration_manager.get_scan_polling_timeout_in_seconds()
@@ -468,14 +471,14 @@ def poll_scan_results(
end_polling_time = time.time() + polling_timeout
while time.time() < end_polling_time:
- scan_details = cycode_client.get_scan_details(scan_id)
+ scan_details = cycode_client.get_scan_details(scan_type, scan_id)
if scan_details.scan_update_at is not None and scan_details.scan_update_at != last_scan_update_at:
last_scan_update_at = scan_details.scan_update_at
print_debug_scan_details(scan_details)
if scan_details.scan_status == consts.SCAN_STATUS_COMPLETED:
- return _get_scan_result(cycode_client, scan_id, scan_details)
+ return _get_scan_result(cycode_client, scan_type, scan_id, scan_details)
if scan_details.scan_status == consts.SCAN_STATUS_ERROR:
raise custom_exceptions.ScanAsyncError(
@@ -759,14 +762,14 @@ def _does_severity_match_severity_threshold(severity: str, severity_threshold: s
def _get_scan_result(
- cycode_client: 'ScanClient', scan_id: str, scan_details: 'ScanDetailsResponse'
+ cycode_client: 'ScanClient', scan_type: str, scan_id: str, scan_details: 'ScanDetailsResponse'
) -> ZippedFileScanResult:
if not scan_details.detections_count:
return init_default_scan_result(scan_id, scan_details.metadata)
- wait_for_detections_creation(cycode_client, scan_id, scan_details.detections_count)
+ wait_for_detections_creation(cycode_client, scan_type, scan_id, scan_details.detections_count)
- scan_detections = cycode_client.get_scan_detections(scan_id)
+ scan_detections = cycode_client.get_scan_detections(scan_type, scan_id)
return ZippedFileScanResult(
did_detect=True,
detections_per_file=_map_detections_per_file(scan_detections),
@@ -792,7 +795,9 @@ def _try_get_report_url(metadata_json: Optional[str]) -> Optional[str]:
return None
-def wait_for_detections_creation(cycode_client: 'ScanClient', scan_id: str, expected_detections_count: int) -> None:
+def wait_for_detections_creation(
+ cycode_client: 'ScanClient', scan_type: str, scan_id: str, expected_detections_count: int
+) -> None:
logger.debug('Waiting for detections to be created')
scan_persisted_detections_count = 0
@@ -800,7 +805,7 @@ def wait_for_detections_creation(cycode_client: 'ScanClient', scan_id: str, expe
end_polling_time = time.time() + polling_timeout
while time.time() < end_polling_time:
- scan_persisted_detections_count = cycode_client.get_scan_detections_count(scan_id)
+ scan_persisted_detections_count = cycode_client.get_scan_detections_count(scan_type, scan_id)
logger.debug(
f'Excepted {expected_detections_count} detections, got {scan_persisted_detections_count} detections '
f'({expected_detections_count - scan_persisted_detections_count} more; '
diff --git a/cycode/cyclient/scan_client.py b/cycode/cyclient/scan_client.py
index cf15798f..67291997 100644
--- a/cycode/cyclient/scan_client.py
+++ b/cycode/cyclient/scan_client.py
@@ -20,14 +20,35 @@ def __init__(
self.scan_cycode_client = scan_cycode_client
self.scan_config = scan_config
- self.SCAN_CONTROLLER_PATH = 'api/v1/cli-scan'
- self.DETECTIONS_SERVICE_CONTROLLER_PATH = 'api/v1/detections/cli'
+ self._SCAN_CONTROLLER_PATH = 'api/v1/scan'
+ self._SCAN_CONTROLLER_PATH_SCA = 'api/v1/cli-scan'
+
+ self._DETECTIONS_SERVICE_CONTROLLER_PATH = 'api/v1/detections'
+ self._DETECTIONS_SERVICE_CONTROLLER_PATH_SCA = 'api/v1/detections/cli'
+
self.POLICIES_SERVICE_CONTROLLER_PATH_V3 = 'api/v3/policies'
self._hide_response_log = hide_response_log
+ def get_scan_controller_path(self, scan_type: str) -> str:
+ if scan_type == consts.SCA_SCAN_TYPE:
+ return self._SCAN_CONTROLLER_PATH_SCA
+
+ return self._SCAN_CONTROLLER_PATH
+
+ def get_detections_service_controller_path(self, scan_type: str) -> str:
+ if scan_type == consts.SCA_SCAN_TYPE:
+ return self._DETECTIONS_SERVICE_CONTROLLER_PATH_SCA
+
+ return self._DETECTIONS_SERVICE_CONTROLLER_PATH
+
+ def get_scan_service_url_path(self, scan_type: str) -> str:
+ service_path = self.scan_config.get_service_name(scan_type)
+ controller_path = self.get_scan_controller_path(scan_type)
+ return f'{service_path}/{controller_path}'
+
def content_scan(self, scan_type: str, file_name: str, content: str, is_git_diff: bool = True) -> models.ScanResult:
- path = f'{self.scan_config.get_service_name(scan_type)}/{self.SCAN_CONTROLLER_PATH}/content'
+ path = f'{self.get_scan_service_url_path(scan_type)}/content'
body = {'name': file_name, 'content': content, 'is_git_diff': is_git_diff}
response = self.scan_cycode_client.post(
url_path=path, body=body, hide_response_content_log=self._hide_response_log
@@ -35,7 +56,7 @@ def content_scan(self, scan_type: str, file_name: str, content: str, is_git_diff
return self.parse_scan_response(response)
def get_zipped_file_scan_url_path(self, scan_type: str) -> str:
- return f'{self.scan_config.get_service_name(scan_type)}/{self.SCAN_CONTROLLER_PATH}/zipped-file'
+ return f'{self.get_scan_service_url_path(scan_type)}/zipped-file'
def zipped_file_scan(
self, scan_type: str, zip_file: InMemoryZip, scan_id: str, scan_parameters: dict, is_git_diff: bool = False
@@ -54,9 +75,7 @@ def zipped_file_scan(
def get_zipped_file_scan_async_url_path(self, scan_type: str) -> str:
async_scan_type = self.scan_config.get_async_scan_type(scan_type)
async_entity_type = self.scan_config.get_async_entity_type(scan_type)
-
- url_prefix = self.scan_config.get_scans_prefix()
- return f'{url_prefix}/{self.SCAN_CONTROLLER_PATH}/{async_scan_type}/{async_entity_type}'
+ return f'{self.get_scan_service_url_path(scan_type)}/{async_scan_type}/{async_entity_type}'
def zipped_file_scan_async(
self, zip_file: InMemoryZip, scan_type: str, scan_parameters: dict, is_git_diff: bool = False
@@ -77,9 +96,7 @@ def multiple_zipped_file_scan_async(
scan_parameters: dict,
is_git_diff: bool = False,
) -> models.ScanInitializationResponse:
- url_path = (
- f'{self.scan_config.get_scans_prefix()}/{self.SCAN_CONTROLLER_PATH}/{scan_type}/repository/commit-range'
- )
+ url_path = f'{self.get_scan_service_url_path(scan_type)}/{scan_type}/repository/commit-range'
files = {
'file_from_commit': ('multiple_files_scan.zip', from_commit_zip_file.read()),
'file_to_commit': ('multiple_files_scan.zip', to_commit_zip_file.read()),
@@ -91,11 +108,12 @@ def multiple_zipped_file_scan_async(
)
return models.ScanInitializationResponseSchema().load(response.json())
- def get_scan_details_path(self, scan_id: str) -> str:
- return f'{self.scan_config.get_scans_prefix()}/{self.SCAN_CONTROLLER_PATH}/{scan_id}'
+ def get_scan_details_path(self, scan_type: str, scan_id: str) -> str:
+ return f'{self.get_scan_service_url_path(scan_type)}/{scan_id}'
- def get_scan_details(self, scan_id: str) -> models.ScanDetailsResponse:
- response = self.scan_cycode_client.get(url_path=self.get_scan_details_path(scan_id))
+ def get_scan_details(self, scan_type: str, scan_id: str) -> models.ScanDetailsResponse:
+ path = self.get_scan_details_path(scan_type, scan_id)
+ response = self.scan_cycode_client.get(url_path=path)
return models.ScanDetailsResponseSchema().load(response.json())
def get_detection_rules_path(self) -> str:
@@ -150,10 +168,10 @@ def get_detection_rules(
# we are filtering rules by ids in-place for smooth migration when backend will be ready
return self._filter_detection_rules_by_ids(self.parse_detection_rules_response(response), detection_rules_ids)
- def get_scan_detections_path(self) -> str:
- return f'{self.scan_config.get_detections_prefix()}/{self.DETECTIONS_SERVICE_CONTROLLER_PATH}/detections'
+ def get_scan_detections_path(self, scan_type: str) -> str:
+ return f'{self.scan_config.get_detections_prefix()}/{self.get_detections_service_controller_path(scan_type)}'
- def get_scan_detections(self, scan_id: str) -> List[dict]:
+ def get_scan_detections(self, scan_type: str, scan_id: str) -> List[dict]:
params = {'scan_id': scan_id}
page_size = 200
@@ -166,8 +184,9 @@ def get_scan_detections(self, scan_id: str) -> List[dict]:
params['page_size'] = page_size
params['page_number'] = page_number
+ path = f'{self.get_scan_detections_path(scan_type)}/detections'
response = self.scan_cycode_client.get(
- url_path=self.get_scan_detections_path(),
+ url_path=path,
params=params,
hide_response_content_log=self._hide_response_log,
).json()
@@ -178,21 +197,19 @@ def get_scan_detections(self, scan_id: str) -> List[dict]:
return detections
- def get_get_scan_detections_count_path(self) -> str:
- return f'{self.scan_config.get_detections_prefix()}/{self.DETECTIONS_SERVICE_CONTROLLER_PATH}/count'
+ def get_get_scan_detections_count_path(self, scan_type: str) -> str:
+ return f'{self.get_scan_detections_path(scan_type)}/count'
- def get_scan_detections_count(self, scan_id: str) -> int:
+ def get_scan_detections_count(self, scan_type: str, scan_id: str) -> int:
response = self.scan_cycode_client.get(
- url_path=self.get_get_scan_detections_count_path(), params={'scan_id': scan_id}
+ url_path=self.get_get_scan_detections_count_path(scan_type), params={'scan_id': scan_id}
)
return response.json().get('count', 0)
def commit_range_zipped_file_scan(
self, scan_type: str, zip_file: InMemoryZip, scan_id: str
) -> models.ZippedFileScanResult:
- url_path = (
- f'{self.scan_config.get_service_name(scan_type)}/{self.SCAN_CONTROLLER_PATH}/commit-range-zipped-file'
- )
+ url_path = f'{self.get_scan_service_url_path(scan_type)}/commit-range-zipped-file'
files = {'file': ('multiple_files_scan.zip', zip_file.read())}
response = self.scan_cycode_client.post(
url_path=url_path, data={'scan_id': scan_id}, files=files, hide_response_content_log=self._hide_response_log
@@ -200,7 +217,7 @@ def commit_range_zipped_file_scan(
return self.parse_zipped_file_scan_response(response)
def get_report_scan_status_path(self, scan_type: str, scan_id: str) -> str:
- return f'{self.scan_config.get_service_name(scan_type)}/{self.SCAN_CONTROLLER_PATH}/{scan_id}/status'
+ return f'{self.get_scan_service_url_path(scan_type)}/{scan_id}/status'
def report_scan_status(self, scan_type: str, scan_id: str, scan_status: dict) -> None:
self.scan_cycode_client.post(url_path=self.get_report_scan_status_path(scan_type, scan_id), body=scan_status)
diff --git a/cycode/cyclient/scan_config_base.py b/cycode/cyclient/scan_config_base.py
index 0b791348..347d39ef 100644
--- a/cycode/cyclient/scan_config_base.py
+++ b/cycode/cyclient/scan_config_base.py
@@ -20,10 +20,6 @@ def get_async_entity_type(_: str) -> str:
# we are migrating to "zippedfile" entity type. will be used later
return 'repository'
- @abstractmethod
- def get_scans_prefix(self) -> str:
- ...
-
@abstractmethod
def get_detections_prefix(self) -> str:
...
@@ -39,9 +35,6 @@ def get_service_name(self, scan_type: str) -> str:
# sca and sast
return '5004'
- def get_scans_prefix(self) -> str:
- return '5004'
-
def get_detections_prefix(self) -> str:
return '5016'
@@ -56,8 +49,5 @@ def get_service_name(self, scan_type: str) -> str:
# sca and sast
return 'scans'
- def get_scans_prefix(self) -> str:
- return 'scans'
-
def get_detections_prefix(self) -> str:
return 'detections'
diff --git a/process_executable_file.py b/process_executable_file.py
index 84c4081a..ad4d702a 100755
--- a/process_executable_file.py
+++ b/process_executable_file.py
@@ -51,7 +51,12 @@ def get_hashes_of_every_file_in_the_directory(dir_path: Path) -> DirHashes:
hashes = []
for root, _, files in os.walk(dir_path):
- hashes.extend(get_hashes_of_many_files(root, files,))
+ hashes.extend(
+ get_hashes_of_many_files(
+ root,
+ files,
+ )
+ )
return hashes
@@ -60,7 +65,7 @@ def normalize_hashes_db(hashes: DirHashes, dir_path: Path) -> DirHashes:
normalized_hashes = []
for file_hash, file_path in hashes:
- relative_file_path = file_path[file_path.find(dir_path.name):]
+ relative_file_path = file_path[file_path.find(dir_path.name) :]
normalized_hashes.append((file_hash, relative_file_path))
# sort by file path
diff --git a/tests/cyclient/mocked_responses/scan_client.py b/tests/cyclient/mocked_responses/scan_client.py
index de1613c9..55528e8f 100644
--- a/tests/cyclient/mocked_responses/scan_client.py
+++ b/tests/cyclient/mocked_responses/scan_client.py
@@ -119,9 +119,9 @@ def get_scan_detections_count_response(url: str) -> responses.Response:
return responses.Response(method=responses.GET, url=url, json=json_response, status=200)
-def get_scan_detections_url(scan_client: ScanClient) -> str:
+def get_scan_detections_url(scan_client: ScanClient, scan_type: str) -> str:
api_url = scan_client.scan_cycode_client.api_url
- service_url = scan_client.get_scan_detections_path()
+ service_url = scan_client.get_scan_detections_path(scan_type)
return f'{api_url}/{service_url}'
@@ -168,7 +168,9 @@ def mock_scan_async_responses(
responses_module.add(get_scan_details_response(get_scan_details_url(scan_id, scan_client), scan_id))
responses_module.add(get_detection_rules_response(get_detection_rules_url(scan_client)))
responses_module.add(get_scan_detections_count_response(get_scan_detections_count_url(scan_client)))
- responses_module.add(get_scan_detections_response(get_scan_detections_url(scan_client), scan_id, zip_content_path))
+ responses_module.add(
+ get_scan_detections_response(get_scan_detections_url(scan_client, scan_type), scan_id, zip_content_path)
+ )
responses_module.add(get_report_scan_status_response(get_report_scan_status_url(scan_type, scan_id, scan_client)))
diff --git a/tests/cyclient/scan_config/test_default_scan_config.py b/tests/cyclient/scan_config/test_default_scan_config.py
index e0a84ad2..60b87436 100644
--- a/tests/cyclient/scan_config/test_default_scan_config.py
+++ b/tests/cyclient/scan_config/test_default_scan_config.py
@@ -10,12 +10,6 @@ def test_get_service_name() -> None:
assert default_scan_config.get_service_name('sast') == 'scans'
-def test_get_scans_prefix() -> None:
- default_scan_config = DefaultScanConfig()
-
- assert default_scan_config.get_scans_prefix() == 'scans'
-
-
def test_get_detections_prefix() -> None:
default_scan_config = DefaultScanConfig()
diff --git a/tests/cyclient/scan_config/test_dev_scan_config.py b/tests/cyclient/scan_config/test_dev_scan_config.py
index 3ea3127e..4a44ff14 100644
--- a/tests/cyclient/scan_config/test_dev_scan_config.py
+++ b/tests/cyclient/scan_config/test_dev_scan_config.py
@@ -10,12 +10,6 @@ def test_get_service_name() -> None:
assert dev_scan_config.get_service_name('sast') == '5004'
-def test_get_scans_prefix() -> None:
- dev_scan_config = DevScanConfig()
-
- assert dev_scan_config.get_scans_prefix() == '5004'
-
-
def test_get_detections_prefix() -> None:
dev_scan_config = DevScanConfig()
From b956ea56235158865c453ebfc53b040ecbfa14c4 Mon Sep 17 00:00:00 2001
From: Ilya Siamionau
Date: Wed, 10 Jan 2024 15:04:08 +0100
Subject: [PATCH 059/257] CM-31143 - Migrate from black to ruff format (#192)
---
.github/workflows/black.yml | 52 -----------
.github/workflows/ruff.yml | 6 +-
poetry.lock | 169 +++++-------------------------------
pyproject.toml | 28 ++----
4 files changed, 30 insertions(+), 225 deletions(-)
delete mode 100644 .github/workflows/black.yml
diff --git a/.github/workflows/black.yml b/.github/workflows/black.yml
deleted file mode 100644
index d8003685..00000000
--- a/.github/workflows/black.yml
+++ /dev/null
@@ -1,52 +0,0 @@
-name: Black (code formatter)
-
-on: [ pull_request, push ]
-
-jobs:
- black:
- runs-on: ubuntu-latest
-
- steps:
- - name: Run Cimon
- uses: cycodelabs/cimon-action@v0
- with:
- client-id: ${{ secrets.CIMON_CLIENT_ID }}
- secret: ${{ secrets.CIMON_SECRET }}
- prevent: true
- allowed-hosts: >
- files.pythonhosted.org
- install.python-poetry.org
- pypi.org
-
- - name: Checkout repository
- uses: actions/checkout@v3
-
- - name: Setup Python
- uses: actions/setup-python@v4
- with:
- python-version: 3.7
-
- - name: Load cached Poetry setup
- id: cached-poetry
- uses: actions/cache@v3
- with:
- path: ~/.local
- key: poetry-ubuntu-0 # increment to reset cache
-
- - name: Setup Poetry
- if: steps.cached-poetry.outputs.cache-hit != 'true'
- uses: snok/install-poetry@v1
- with:
- version: 1.5.1
-
- - name: Add Poetry to PATH
- run: echo "$HOME/.local/bin" >> $GITHUB_PATH
-
- - name: Install dependencies
- run: poetry install
-
- - name: Check code style of package
- run: poetry run black --check cycode
-
- - name: Check code style of tests
- run: poetry run black --check tests
diff --git a/.github/workflows/ruff.yml b/.github/workflows/ruff.yml
index 919f4f2d..73fcf08a 100644
--- a/.github/workflows/ruff.yml
+++ b/.github/workflows/ruff.yml
@@ -1,11 +1,10 @@
-name: Ruff (linter)
+name: Ruff (linter and code formatter)
on: [ pull_request, push ]
jobs:
ruff:
runs-on: ubuntu-latest
-
steps:
- name: Run Cimon
uses: cycodelabs/cimon-action@v0
@@ -47,3 +46,6 @@ jobs:
- name: Run linter check
run: poetry run ruff check .
+
+ - name: Run code style check
+ run: poetry run ruff format --check .
diff --git a/poetry.lock b/poetry.lock
index e4e96a4d..4a33ec57 100644
--- a/poetry.lock
+++ b/poetry.lock
@@ -40,56 +40,6 @@ files = [
[package.dependencies]
chardet = ">=3.0.2"
-[[package]]
-name = "black"
-version = "23.3.0"
-description = "The uncompromising code formatter."
-optional = false
-python-versions = ">=3.7"
-files = [
- {file = "black-23.3.0-cp310-cp310-macosx_10_16_arm64.whl", hash = "sha256:0945e13506be58bf7db93ee5853243eb368ace1c08a24c65ce108986eac65915"},
- {file = "black-23.3.0-cp310-cp310-macosx_10_16_universal2.whl", hash = "sha256:67de8d0c209eb5b330cce2469503de11bca4085880d62f1628bd9972cc3366b9"},
- {file = "black-23.3.0-cp310-cp310-macosx_10_16_x86_64.whl", hash = "sha256:7c3eb7cea23904399866c55826b31c1f55bbcd3890ce22ff70466b907b6775c2"},
- {file = "black-23.3.0-cp310-cp310-manylinux_2_17_x86_64.manylinux2014_x86_64.whl", hash = "sha256:32daa9783106c28815d05b724238e30718f34155653d4d6e125dc7daec8e260c"},
- {file = "black-23.3.0-cp310-cp310-win_amd64.whl", hash = "sha256:35d1381d7a22cc5b2be2f72c7dfdae4072a3336060635718cc7e1ede24221d6c"},
- {file = "black-23.3.0-cp311-cp311-macosx_10_16_arm64.whl", hash = "sha256:a8a968125d0a6a404842fa1bf0b349a568634f856aa08ffaff40ae0dfa52e7c6"},
- {file = "black-23.3.0-cp311-cp311-macosx_10_16_universal2.whl", hash = "sha256:c7ab5790333c448903c4b721b59c0d80b11fe5e9803d8703e84dcb8da56fec1b"},
- {file = "black-23.3.0-cp311-cp311-macosx_10_16_x86_64.whl", hash = "sha256:a6f6886c9869d4daae2d1715ce34a19bbc4b95006d20ed785ca00fa03cba312d"},
- {file = "black-23.3.0-cp311-cp311-manylinux_2_17_x86_64.manylinux2014_x86_64.whl", hash = "sha256:6f3c333ea1dd6771b2d3777482429864f8e258899f6ff05826c3a4fcc5ce3f70"},
- {file = "black-23.3.0-cp311-cp311-win_amd64.whl", hash = "sha256:11c410f71b876f961d1de77b9699ad19f939094c3a677323f43d7a29855fe326"},
- {file = "black-23.3.0-cp37-cp37m-macosx_10_16_x86_64.whl", hash = "sha256:1d06691f1eb8de91cd1b322f21e3bfc9efe0c7ca1f0e1eb1db44ea367dff656b"},
- {file = "black-23.3.0-cp37-cp37m-manylinux_2_17_x86_64.manylinux2014_x86_64.whl", hash = "sha256:50cb33cac881766a5cd9913e10ff75b1e8eb71babf4c7104f2e9c52da1fb7de2"},
- {file = "black-23.3.0-cp37-cp37m-win_amd64.whl", hash = "sha256:e114420bf26b90d4b9daa597351337762b63039752bdf72bf361364c1aa05925"},
- {file = "black-23.3.0-cp38-cp38-macosx_10_16_arm64.whl", hash = "sha256:48f9d345675bb7fbc3dd85821b12487e1b9a75242028adad0333ce36ed2a6d27"},
- {file = "black-23.3.0-cp38-cp38-macosx_10_16_universal2.whl", hash = "sha256:714290490c18fb0126baa0fca0a54ee795f7502b44177e1ce7624ba1c00f2331"},
- {file = "black-23.3.0-cp38-cp38-macosx_10_16_x86_64.whl", hash = "sha256:064101748afa12ad2291c2b91c960be28b817c0c7eaa35bec09cc63aa56493c5"},
- {file = "black-23.3.0-cp38-cp38-manylinux_2_17_x86_64.manylinux2014_x86_64.whl", hash = "sha256:562bd3a70495facf56814293149e51aa1be9931567474993c7942ff7d3533961"},
- {file = "black-23.3.0-cp38-cp38-win_amd64.whl", hash = "sha256:e198cf27888ad6f4ff331ca1c48ffc038848ea9f031a3b40ba36aced7e22f2c8"},
- {file = "black-23.3.0-cp39-cp39-macosx_10_16_arm64.whl", hash = "sha256:3238f2aacf827d18d26db07524e44741233ae09a584273aa059066d644ca7b30"},
- {file = "black-23.3.0-cp39-cp39-macosx_10_16_universal2.whl", hash = "sha256:f0bd2f4a58d6666500542b26354978218a9babcdc972722f4bf90779524515f3"},
- {file = "black-23.3.0-cp39-cp39-macosx_10_16_x86_64.whl", hash = "sha256:92c543f6854c28a3c7f39f4d9b7694f9a6eb9d3c5e2ece488c327b6e7ea9b266"},
- {file = "black-23.3.0-cp39-cp39-manylinux_2_17_x86_64.manylinux2014_x86_64.whl", hash = "sha256:3a150542a204124ed00683f0db1f5cf1c2aaaa9cc3495b7a3b5976fb136090ab"},
- {file = "black-23.3.0-cp39-cp39-win_amd64.whl", hash = "sha256:6b39abdfb402002b8a7d030ccc85cf5afff64ee90fa4c5aebc531e3ad0175ddb"},
- {file = "black-23.3.0-py3-none-any.whl", hash = "sha256:ec751418022185b0c1bb7d7736e6933d40bbb14c14a0abcf9123d1b159f98dd4"},
- {file = "black-23.3.0.tar.gz", hash = "sha256:1c7b8d606e728a41ea1ccbd7264677e494e87cf630e399262ced92d4a8dac940"},
-]
-
-[package.dependencies]
-click = ">=8.0.0"
-mypy-extensions = ">=0.4.3"
-packaging = ">=22.0"
-pathspec = ">=0.9.0"
-platformdirs = ">=2"
-tomli = {version = ">=1.1.0", markers = "python_version < \"3.11\""}
-typed-ast = {version = ">=1.4.2", markers = "python_version < \"3.8\" and implementation_name == \"cpython\""}
-typing-extensions = {version = ">=3.10.0.0", markers = "python_version < \"3.10\""}
-
-[package.extras]
-colorama = ["colorama (>=0.4.3)"]
-d = ["aiohttp (>=3.7.4)"]
-jupyter = ["ipython (>=7.8.0)", "tokenize-rt (>=3.2.0)"]
-uvloop = ["uvloop (>=0.15.2)"]
-
[[package]]
name = "certifi"
version = "2023.11.17"
@@ -462,17 +412,6 @@ build = ["blurb", "twine", "wheel"]
docs = ["sphinx"]
test = ["pytest (<5.4)", "pytest-cov"]
-[[package]]
-name = "mypy-extensions"
-version = "1.0.0"
-description = "Type system extensions for programs checked with the mypy type checker."
-optional = false
-python-versions = ">=3.5"
-files = [
- {file = "mypy_extensions-1.0.0-py3-none-any.whl", hash = "sha256:4392f6c0eb8a5668a69e23d168ffa70f0be9ccfd32b5cc2d26a34ae5b844552d"},
- {file = "mypy_extensions-1.0.0.tar.gz", hash = "sha256:75dbf8955dc00442a438fc4d0666508a9a97b6bd41aa2f0ffe9d2f2725af0782"},
-]
-
[[package]]
name = "packaging"
version = "23.2"
@@ -506,24 +445,6 @@ files = [
{file = "pefile-2023.2.7.tar.gz", hash = "sha256:82e6114004b3d6911c77c3953e3838654b04511b8b66e8583db70c65998017dc"},
]
-[[package]]
-name = "platformdirs"
-version = "4.0.0"
-description = "A small Python package for determining appropriate platform-specific dirs, e.g. a \"user data dir\"."
-optional = false
-python-versions = ">=3.7"
-files = [
- {file = "platformdirs-4.0.0-py3-none-any.whl", hash = "sha256:118c954d7e949b35437270383a3f2531e99dd93cf7ce4dc8340d3356d30f173b"},
- {file = "platformdirs-4.0.0.tar.gz", hash = "sha256:cb633b2bcf10c51af60beb0ab06d2f1d69064b43abf4c185ca6b28865f3f9731"},
-]
-
-[package.dependencies]
-typing-extensions = {version = ">=4.7.1", markers = "python_version < \"3.8\""}
-
-[package.extras]
-docs = ["furo (>=2023.7.26)", "proselint (>=0.13)", "sphinx (>=7.1.1)", "sphinx-autodoc-typehints (>=1.24)"]
-test = ["appdirs (==1.4.4)", "covdefaults (>=2.3)", "pytest (>=7.4)", "pytest-cov (>=4.1)", "pytest-mock (>=3.11.1)"]
-
[[package]]
name = "pluggy"
version = "1.2.0"
@@ -745,28 +666,28 @@ tests = ["coverage (>=6.0.0)", "flake8", "mypy", "pytest (>=7.0.0)", "pytest-asy
[[package]]
name = "ruff"
-version = "0.0.277"
-description = "An extremely fast Python linter, written in Rust."
+version = "0.1.11"
+description = "An extremely fast Python linter and code formatter, written in Rust."
optional = false
python-versions = ">=3.7"
files = [
- {file = "ruff-0.0.277-py3-none-macosx_10_7_x86_64.whl", hash = "sha256:3250b24333ef419b7a232080d9724ccc4d2da1dbbe4ce85c4caa2290d83200f8"},
- {file = "ruff-0.0.277-py3-none-macosx_10_9_x86_64.macosx_11_0_arm64.macosx_10_9_universal2.whl", hash = "sha256:3e60605e07482183ba1c1b7237eca827bd6cbd3535fe8a4ede28cbe2a323cb97"},
- {file = "ruff-0.0.277-py3-none-manylinux_2_17_aarch64.manylinux2014_aarch64.whl", hash = "sha256:7baa97c3d7186e5ed4d5d4f6834d759a27e56cf7d5874b98c507335f0ad5aadb"},
- {file = "ruff-0.0.277-py3-none-manylinux_2_17_armv7l.manylinux2014_armv7l.whl", hash = "sha256:74e4b206cb24f2e98a615f87dbe0bde18105217cbcc8eb785bb05a644855ba50"},
- {file = "ruff-0.0.277-py3-none-manylinux_2_17_i686.manylinux2014_i686.whl", hash = "sha256:479864a3ccd8a6a20a37a6e7577bdc2406868ee80b1e65605478ad3b8eb2ba0b"},
- {file = "ruff-0.0.277-py3-none-manylinux_2_17_ppc64.manylinux2014_ppc64.whl", hash = "sha256:468bfb0a7567443cec3d03cf408d6f562b52f30c3c29df19927f1e0e13a40cd7"},
- {file = "ruff-0.0.277-py3-none-manylinux_2_17_ppc64le.manylinux2014_ppc64le.whl", hash = "sha256:f32ec416c24542ca2f9cc8c8b65b84560530d338aaf247a4a78e74b99cd476b4"},
- {file = "ruff-0.0.277-py3-none-manylinux_2_17_s390x.manylinux2014_s390x.whl", hash = "sha256:14a7b2f00f149c5a295f188a643ac25226ff8a4d08f7a62b1d4b0a1dc9f9b85c"},
- {file = "ruff-0.0.277-py3-none-manylinux_2_17_x86_64.manylinux2014_x86_64.whl", hash = "sha256:a9879f59f763cc5628aa01c31ad256a0f4dc61a29355c7315b83c2a5aac932b5"},
- {file = "ruff-0.0.277-py3-none-musllinux_1_2_aarch64.whl", hash = "sha256:f612e0a14b3d145d90eb6ead990064e22f6f27281d847237560b4e10bf2251f3"},
- {file = "ruff-0.0.277-py3-none-musllinux_1_2_armv7l.whl", hash = "sha256:323b674c98078be9aaded5b8b51c0d9c424486566fb6ec18439b496ce79e5998"},
- {file = "ruff-0.0.277-py3-none-musllinux_1_2_i686.whl", hash = "sha256:3a43fbe026ca1a2a8c45aa0d600a0116bec4dfa6f8bf0c3b871ecda51ef2b5dd"},
- {file = "ruff-0.0.277-py3-none-musllinux_1_2_x86_64.whl", hash = "sha256:734165ea8feb81b0d53e3bf523adc2413fdb76f1264cde99555161dd5a725522"},
- {file = "ruff-0.0.277-py3-none-win32.whl", hash = "sha256:88d0f2afb2e0c26ac1120e7061ddda2a566196ec4007bd66d558f13b374b9efc"},
- {file = "ruff-0.0.277-py3-none-win_amd64.whl", hash = "sha256:6fe81732f788894a00f6ade1fe69e996cc9e485b7c35b0f53fb00284397284b2"},
- {file = "ruff-0.0.277-py3-none-win_arm64.whl", hash = "sha256:2d4444c60f2e705c14cd802b55cd2b561d25bf4311702c463a002392d3116b22"},
- {file = "ruff-0.0.277.tar.gz", hash = "sha256:2dab13cdedbf3af6d4427c07f47143746b6b95d9e4a254ac369a0edb9280a0d2"},
+ {file = "ruff-0.1.11-py3-none-macosx_10_12_x86_64.macosx_11_0_arm64.macosx_10_12_universal2.whl", hash = "sha256:a7f772696b4cdc0a3b2e527fc3c7ccc41cdcb98f5c80fdd4f2b8c50eb1458196"},
+ {file = "ruff-0.1.11-py3-none-macosx_10_12_x86_64.whl", hash = "sha256:934832f6ed9b34a7d5feea58972635c2039c7a3b434fe5ba2ce015064cb6e955"},
+ {file = "ruff-0.1.11-py3-none-manylinux_2_17_aarch64.manylinux2014_aarch64.whl", hash = "sha256:ea0d3e950e394c4b332bcdd112aa566010a9f9c95814844a7468325290aabfd9"},
+ {file = "ruff-0.1.11-py3-none-manylinux_2_17_armv7l.manylinux2014_armv7l.whl", hash = "sha256:9bd4025b9c5b429a48280785a2b71d479798a69f5c2919e7d274c5f4b32c3607"},
+ {file = "ruff-0.1.11-py3-none-manylinux_2_17_i686.manylinux2014_i686.whl", hash = "sha256:e1ad00662305dcb1e987f5ec214d31f7d6a062cae3e74c1cbccef15afd96611d"},
+ {file = "ruff-0.1.11-py3-none-manylinux_2_17_ppc64.manylinux2014_ppc64.whl", hash = "sha256:4b077ce83f47dd6bea1991af08b140e8b8339f0ba8cb9b7a484c30ebab18a23f"},
+ {file = "ruff-0.1.11-py3-none-manylinux_2_17_ppc64le.manylinux2014_ppc64le.whl", hash = "sha256:c4a88efecec23c37b11076fe676e15c6cdb1271a38f2b415e381e87fe4517f18"},
+ {file = "ruff-0.1.11-py3-none-manylinux_2_17_s390x.manylinux2014_s390x.whl", hash = "sha256:5b25093dad3b055667730a9b491129c42d45e11cdb7043b702e97125bcec48a1"},
+ {file = "ruff-0.1.11-py3-none-manylinux_2_17_x86_64.manylinux2014_x86_64.whl", hash = "sha256:231d8fb11b2cc7c0366a326a66dafc6ad449d7fcdbc268497ee47e1334f66f77"},
+ {file = "ruff-0.1.11-py3-none-musllinux_1_2_aarch64.whl", hash = "sha256:09c415716884950080921dd6237767e52e227e397e2008e2bed410117679975b"},
+ {file = "ruff-0.1.11-py3-none-musllinux_1_2_armv7l.whl", hash = "sha256:0f58948c6d212a6b8d41cd59e349751018797ce1727f961c2fa755ad6208ba45"},
+ {file = "ruff-0.1.11-py3-none-musllinux_1_2_i686.whl", hash = "sha256:190a566c8f766c37074d99640cd9ca3da11d8deae2deae7c9505e68a4a30f740"},
+ {file = "ruff-0.1.11-py3-none-musllinux_1_2_x86_64.whl", hash = "sha256:6464289bd67b2344d2a5d9158d5eb81025258f169e69a46b741b396ffb0cda95"},
+ {file = "ruff-0.1.11-py3-none-win32.whl", hash = "sha256:9b8f397902f92bc2e70fb6bebfa2139008dc72ae5177e66c383fa5426cb0bf2c"},
+ {file = "ruff-0.1.11-py3-none-win_amd64.whl", hash = "sha256:eb85ee287b11f901037a6683b2374bb0ec82928c5cbc984f575d0437979c521a"},
+ {file = "ruff-0.1.11-py3-none-win_arm64.whl", hash = "sha256:97ce4d752f964ba559c7023a86e5f8e97f026d511e48013987623915431c7ea9"},
+ {file = "ruff-0.1.11.tar.gz", hash = "sha256:f9d4d88cb6eeb4dfe20f9f0519bd2eaba8119bde87c3d5065c541dbae2b5a2cb"},
]
[[package]]
@@ -829,56 +750,6 @@ files = [
{file = "tomli-2.0.1.tar.gz", hash = "sha256:de526c12914f0c550d15924c62d72abc48d6fe7364aa87328337a31007fe8a4f"},
]
-[[package]]
-name = "typed-ast"
-version = "1.5.5"
-description = "a fork of Python 2 and 3 ast modules with type comment support"
-optional = false
-python-versions = ">=3.6"
-files = [
- {file = "typed_ast-1.5.5-cp310-cp310-macosx_10_9_x86_64.whl", hash = "sha256:4bc1efe0ce3ffb74784e06460f01a223ac1f6ab31c6bc0376a21184bf5aabe3b"},
- {file = "typed_ast-1.5.5-cp310-cp310-macosx_11_0_arm64.whl", hash = "sha256:5f7a8c46a8b333f71abd61d7ab9255440d4a588f34a21f126bbfc95f6049e686"},
- {file = "typed_ast-1.5.5-cp310-cp310-manylinux_2_17_aarch64.manylinux2014_aarch64.whl", hash = "sha256:597fc66b4162f959ee6a96b978c0435bd63791e31e4f410622d19f1686d5e769"},
- {file = "typed_ast-1.5.5-cp310-cp310-manylinux_2_17_x86_64.manylinux2014_x86_64.whl", hash = "sha256:d41b7a686ce653e06c2609075d397ebd5b969d821b9797d029fccd71fdec8e04"},
- {file = "typed_ast-1.5.5-cp310-cp310-musllinux_1_1_aarch64.whl", hash = "sha256:5fe83a9a44c4ce67c796a1b466c270c1272e176603d5e06f6afbc101a572859d"},
- {file = "typed_ast-1.5.5-cp310-cp310-musllinux_1_1_x86_64.whl", hash = "sha256:d5c0c112a74c0e5db2c75882a0adf3133adedcdbfd8cf7c9d6ed77365ab90a1d"},
- {file = "typed_ast-1.5.5-cp310-cp310-win_amd64.whl", hash = "sha256:e1a976ed4cc2d71bb073e1b2a250892a6e968ff02aa14c1f40eba4f365ffec02"},
- {file = "typed_ast-1.5.5-cp311-cp311-macosx_10_9_x86_64.whl", hash = "sha256:c631da9710271cb67b08bd3f3813b7af7f4c69c319b75475436fcab8c3d21bee"},
- {file = "typed_ast-1.5.5-cp311-cp311-macosx_11_0_arm64.whl", hash = "sha256:b445c2abfecab89a932b20bd8261488d574591173d07827c1eda32c457358b18"},
- {file = "typed_ast-1.5.5-cp311-cp311-manylinux_2_17_aarch64.manylinux2014_aarch64.whl", hash = "sha256:cc95ffaaab2be3b25eb938779e43f513e0e538a84dd14a5d844b8f2932593d88"},
- {file = "typed_ast-1.5.5-cp311-cp311-manylinux_2_17_x86_64.manylinux2014_x86_64.whl", hash = "sha256:61443214d9b4c660dcf4b5307f15c12cb30bdfe9588ce6158f4a005baeb167b2"},
- {file = "typed_ast-1.5.5-cp311-cp311-musllinux_1_1_aarch64.whl", hash = "sha256:6eb936d107e4d474940469e8ec5b380c9b329b5f08b78282d46baeebd3692dc9"},
- {file = "typed_ast-1.5.5-cp311-cp311-musllinux_1_1_x86_64.whl", hash = "sha256:e48bf27022897577d8479eaed64701ecaf0467182448bd95759883300ca818c8"},
- {file = "typed_ast-1.5.5-cp311-cp311-win_amd64.whl", hash = "sha256:83509f9324011c9a39faaef0922c6f720f9623afe3fe220b6d0b15638247206b"},
- {file = "typed_ast-1.5.5-cp36-cp36m-macosx_10_9_x86_64.whl", hash = "sha256:44f214394fc1af23ca6d4e9e744804d890045d1643dd7e8229951e0ef39429b5"},
- {file = "typed_ast-1.5.5-cp36-cp36m-manylinux_2_17_aarch64.manylinux2014_aarch64.whl", hash = "sha256:118c1ce46ce58fda78503eae14b7664163aa735b620b64b5b725453696f2a35c"},
- {file = "typed_ast-1.5.5-cp36-cp36m-manylinux_2_17_x86_64.manylinux2014_x86_64.whl", hash = "sha256:be4919b808efa61101456e87f2d4c75b228f4e52618621c77f1ddcaae15904fa"},
- {file = "typed_ast-1.5.5-cp36-cp36m-musllinux_1_1_aarch64.whl", hash = "sha256:fc2b8c4e1bc5cd96c1a823a885e6b158f8451cf6f5530e1829390b4d27d0807f"},
- {file = "typed_ast-1.5.5-cp36-cp36m-musllinux_1_1_x86_64.whl", hash = "sha256:16f7313e0a08c7de57f2998c85e2a69a642e97cb32f87eb65fbfe88381a5e44d"},
- {file = "typed_ast-1.5.5-cp36-cp36m-win_amd64.whl", hash = "sha256:2b946ef8c04f77230489f75b4b5a4a6f24c078be4aed241cfabe9cbf4156e7e5"},
- {file = "typed_ast-1.5.5-cp37-cp37m-macosx_10_9_x86_64.whl", hash = "sha256:2188bc33d85951ea4ddad55d2b35598b2709d122c11c75cffd529fbc9965508e"},
- {file = "typed_ast-1.5.5-cp37-cp37m-manylinux_2_17_aarch64.manylinux2014_aarch64.whl", hash = "sha256:0635900d16ae133cab3b26c607586131269f88266954eb04ec31535c9a12ef1e"},
- {file = "typed_ast-1.5.5-cp37-cp37m-manylinux_2_17_x86_64.manylinux2014_x86_64.whl", hash = "sha256:57bfc3cf35a0f2fdf0a88a3044aafaec1d2f24d8ae8cd87c4f58d615fb5b6311"},
- {file = "typed_ast-1.5.5-cp37-cp37m-musllinux_1_1_aarch64.whl", hash = "sha256:fe58ef6a764de7b4b36edfc8592641f56e69b7163bba9f9c8089838ee596bfb2"},
- {file = "typed_ast-1.5.5-cp37-cp37m-musllinux_1_1_x86_64.whl", hash = "sha256:d09d930c2d1d621f717bb217bf1fe2584616febb5138d9b3e8cdd26506c3f6d4"},
- {file = "typed_ast-1.5.5-cp37-cp37m-win_amd64.whl", hash = "sha256:d40c10326893ecab8a80a53039164a224984339b2c32a6baf55ecbd5b1df6431"},
- {file = "typed_ast-1.5.5-cp38-cp38-macosx_10_9_x86_64.whl", hash = "sha256:fd946abf3c31fb50eee07451a6aedbfff912fcd13cf357363f5b4e834cc5e71a"},
- {file = "typed_ast-1.5.5-cp38-cp38-macosx_11_0_arm64.whl", hash = "sha256:ed4a1a42df8a3dfb6b40c3d2de109e935949f2f66b19703eafade03173f8f437"},
- {file = "typed_ast-1.5.5-cp38-cp38-manylinux_2_17_aarch64.manylinux2014_aarch64.whl", hash = "sha256:045f9930a1550d9352464e5149710d56a2aed23a2ffe78946478f7b5416f1ede"},
- {file = "typed_ast-1.5.5-cp38-cp38-manylinux_2_17_x86_64.manylinux2014_x86_64.whl", hash = "sha256:381eed9c95484ceef5ced626355fdc0765ab51d8553fec08661dce654a935db4"},
- {file = "typed_ast-1.5.5-cp38-cp38-musllinux_1_1_aarch64.whl", hash = "sha256:bfd39a41c0ef6f31684daff53befddae608f9daf6957140228a08e51f312d7e6"},
- {file = "typed_ast-1.5.5-cp38-cp38-musllinux_1_1_x86_64.whl", hash = "sha256:8c524eb3024edcc04e288db9541fe1f438f82d281e591c548903d5b77ad1ddd4"},
- {file = "typed_ast-1.5.5-cp38-cp38-win_amd64.whl", hash = "sha256:7f58fabdde8dcbe764cef5e1a7fcb440f2463c1bbbec1cf2a86ca7bc1f95184b"},
- {file = "typed_ast-1.5.5-cp39-cp39-macosx_10_9_x86_64.whl", hash = "sha256:042eb665ff6bf020dd2243307d11ed626306b82812aba21836096d229fdc6a10"},
- {file = "typed_ast-1.5.5-cp39-cp39-macosx_11_0_arm64.whl", hash = "sha256:622e4a006472b05cf6ef7f9f2636edc51bda670b7bbffa18d26b255269d3d814"},
- {file = "typed_ast-1.5.5-cp39-cp39-manylinux_2_17_aarch64.manylinux2014_aarch64.whl", hash = "sha256:1efebbbf4604ad1283e963e8915daa240cb4bf5067053cf2f0baadc4d4fb51b8"},
- {file = "typed_ast-1.5.5-cp39-cp39-manylinux_2_17_x86_64.manylinux2014_x86_64.whl", hash = "sha256:f0aefdd66f1784c58f65b502b6cf8b121544680456d1cebbd300c2c813899274"},
- {file = "typed_ast-1.5.5-cp39-cp39-musllinux_1_1_aarch64.whl", hash = "sha256:48074261a842acf825af1968cd912f6f21357316080ebaca5f19abbb11690c8a"},
- {file = "typed_ast-1.5.5-cp39-cp39-musllinux_1_1_x86_64.whl", hash = "sha256:429ae404f69dc94b9361bb62291885894b7c6fb4640d561179548c849f8492ba"},
- {file = "typed_ast-1.5.5-cp39-cp39-win_amd64.whl", hash = "sha256:335f22ccb244da2b5c296e6f96b06ee9bed46526db0de38d2f0e5a6597b81155"},
- {file = "typed_ast-1.5.5.tar.gz", hash = "sha256:94282f7a354f36ef5dbce0ef3467ebf6a258e370ab33d5b40c249fa996e590dd"},
-]
-
[[package]]
name = "types-pyyaml"
version = "6.0.12.12"
@@ -935,4 +806,4 @@ testing = ["big-O", "flake8 (<5)", "jaraco.functools", "jaraco.itertools", "more
[metadata]
lock-version = "2.0"
python-versions = ">=3.7,<3.13"
-content-hash = "9c77c886972dc6da818e14a175507a87fe32c773824ef40ee3fab9c0725e9fe4"
+content-hash = "9cefba1b9ec5491f9578c4b142c62535e9d551aebb7dade52fd4920d9ad6bcd6"
diff --git a/pyproject.toml b/pyproject.toml
index 272e3bb2..87bdd11f 100644
--- a/pyproject.toml
+++ b/pyproject.toml
@@ -52,8 +52,7 @@ pyinstaller = ">=5.13.2,<5.14.0"
dunamai = ">=1.18.0,<1.19.0"
[tool.poetry.group.dev.dependencies]
-black = ">=23.3.0,<23.4.0"
-ruff = "0.0.277"
+ruff = "0.1.11"
[tool.pytest.ini_options]
log_cli = true
@@ -68,26 +67,6 @@ fix-shallow-repository=true
vcs = "git"
style = "pep440"
-[tool.black]
-line-length = 120
-skip-string-normalization=true
-target-version = ['py37']
-include = '\.pyi?$'
-exclude = '''
-(
- /(
- \.git
- | \.mypy_cache
- | .idea
- | .pytest_cache
- | venv
- | htmlcov
- | build
- | dist
- )/
-)
-'''
-
[tool.ruff]
extend-select = [
"E", # pycodestyle errors
@@ -125,6 +104,8 @@ ignore = [
"ANN003", # Missing type annotation for `**kwargs`
"ANN101", # Missing type annotation for `self` in method
"ANN102", # Missing type annotation for `cls` in classmethod
+ "ANN401", # Dynamically typed expressions (typing.Any)
+ "ISC001", # Conflicts with ruff format
]
[tool.ruff.flake8-quotes]
@@ -136,6 +117,9 @@ inline-quotes = "single"
"tests/*.py" = ["S101", "S105"]
"cycode/*.py" = ["BLE001"]
+[tool.ruff.format]
+quote-style = "single"
+
[build-system]
requires = ["poetry-core>=1.0.0", "poetry-dynamic-versioning>=1.0.0,<2.0.0"]
build-backend = "poetry_dynamic_versioning.backend"
From 908f5b852481694e1756691776ea4899db0a9d24 Mon Sep 17 00:00:00 2001
From: morsa4406 <104304449+morsa4406@users.noreply.github.com>
Date: Wed, 10 Jan 2024 17:04:24 +0200
Subject: [PATCH 060/257] CM-31147 - Add support reading existing restore file
from directory for gradle (#193)
---
.../maven/base_restore_maven_dependencies.py | 27 ++++++++++++-------
.../sca/maven/restore_gradle_dependencies.py | 4 +++
.../sca/maven/restore_maven_dependencies.py | 3 +++
3 files changed, 25 insertions(+), 9 deletions(-)
diff --git a/cycode/cli/files_collector/sca/maven/base_restore_maven_dependencies.py b/cycode/cli/files_collector/sca/maven/base_restore_maven_dependencies.py
index 064b9eeb..d15e1ef0 100644
--- a/cycode/cli/files_collector/sca/maven/base_restore_maven_dependencies.py
+++ b/cycode/cli/files_collector/sca/maven/base_restore_maven_dependencies.py
@@ -4,7 +4,7 @@
import click
from cycode.cli.models import Document
-from cycode.cli.utils.path_utils import get_file_dir, join_paths
+from cycode.cli.utils.path_utils import get_file_content, get_file_dir, join_paths
from cycode.cli.utils.shell_executor import shell
from cycode.cyclient import logger
@@ -39,6 +39,23 @@ def get_manifest_file_path(self, document: Document) -> str:
else document.path
)
+ def try_restore_dependencies(self, document: Document) -> Optional[Document]:
+ manifest_file_path = self.get_manifest_file_path(document)
+ restore_file_path = build_dep_tree_path(document.path, self.get_lock_file_name())
+
+ if self.verify_restore_file_already_exist(restore_file_path):
+ restore_file_content = get_file_content(restore_file_path)
+ else:
+ restore_file_content = execute_command(
+ self.get_command(manifest_file_path), manifest_file_path, self.command_timeout
+ )
+
+ return Document(restore_file_path, restore_file_content, self.is_git_diff)
+
+ @abstractmethod
+ def verify_restore_file_already_exist(self, restore_file_path: str) -> bool:
+ pass
+
@abstractmethod
def is_project(self, document: Document) -> bool:
pass
@@ -50,11 +67,3 @@ def get_command(self, manifest_file_path: str) -> List[str]:
@abstractmethod
def get_lock_file_name(self) -> str:
pass
-
- def try_restore_dependencies(self, document: Document) -> Optional[Document]:
- manifest_file_path = self.get_manifest_file_path(document)
- return Document(
- build_dep_tree_path(document.path, self.get_lock_file_name()),
- execute_command(self.get_command(manifest_file_path), manifest_file_path, self.command_timeout),
- self.is_git_diff,
- )
diff --git a/cycode/cli/files_collector/sca/maven/restore_gradle_dependencies.py b/cycode/cli/files_collector/sca/maven/restore_gradle_dependencies.py
index ef975ba5..21fdb7c3 100644
--- a/cycode/cli/files_collector/sca/maven/restore_gradle_dependencies.py
+++ b/cycode/cli/files_collector/sca/maven/restore_gradle_dependencies.py
@@ -1,3 +1,4 @@
+import os
from typing import List
import click
@@ -22,3 +23,6 @@ def get_command(self, manifest_file_path: str) -> List[str]:
def get_lock_file_name(self) -> str:
return BUILD_GRADLE_DEP_TREE_FILE_NAME
+
+ def verify_restore_file_already_exist(self, restore_file_path: str) -> bool:
+ return os.path.isfile(restore_file_path)
diff --git a/cycode/cli/files_collector/sca/maven/restore_maven_dependencies.py b/cycode/cli/files_collector/sca/maven/restore_maven_dependencies.py
index 0e21df12..d9c117e6 100644
--- a/cycode/cli/files_collector/sca/maven/restore_maven_dependencies.py
+++ b/cycode/cli/files_collector/sca/maven/restore_maven_dependencies.py
@@ -29,6 +29,9 @@ def get_command(self, manifest_file_path: str) -> List[str]:
def get_lock_file_name(self) -> str:
return join_paths('target', MAVEN_CYCLONE_DEP_TREE_FILE_NAME)
+ def verify_restore_file_already_exist(self, restore_file_path: str) -> bool:
+ return False
+
def try_restore_dependencies(self, document: Document) -> Optional[Document]:
restore_dependencies_document = super().try_restore_dependencies(document)
manifest_file_path = self.get_manifest_file_path(document)
From c6091e2a8f73d6e1083b8a6b00ca16a792bc8a4e Mon Sep 17 00:00:00 2001
From: Ilya Siamionau
Date: Thu, 11 Jan 2024 11:00:50 +0100
Subject: [PATCH 061/257] CM-31107 - Fix detections endpoint suffix for SCA
(#194)
---
cycode/cyclient/scan_client.py | 14 ++++++++++----
tests/cyclient/mocked_responses/scan_client.py | 2 +-
2 files changed, 11 insertions(+), 5 deletions(-)
diff --git a/cycode/cyclient/scan_client.py b/cycode/cyclient/scan_client.py
index 67291997..2b62ef62 100644
--- a/cycode/cyclient/scan_client.py
+++ b/cycode/cyclient/scan_client.py
@@ -171,6 +171,13 @@ def get_detection_rules(
def get_scan_detections_path(self, scan_type: str) -> str:
return f'{self.scan_config.get_detections_prefix()}/{self.get_detections_service_controller_path(scan_type)}'
+ def get_scan_detections_list_path(self, scan_type: str) -> str:
+ suffix = ''
+ if scan_type == consts.SCA_SCAN_TYPE:
+ suffix = '/detections'
+
+ return f'{self.get_scan_detections_path(scan_type)}{suffix}'
+
def get_scan_detections(self, scan_type: str, scan_id: str) -> List[dict]:
params = {'scan_id': scan_id}
@@ -184,9 +191,8 @@ def get_scan_detections(self, scan_type: str, scan_id: str) -> List[dict]:
params['page_size'] = page_size
params['page_number'] = page_number
- path = f'{self.get_scan_detections_path(scan_type)}/detections'
response = self.scan_cycode_client.get(
- url_path=path,
+ url_path=self.get_scan_detections_list_path(scan_type),
params=params,
hide_response_content_log=self._hide_response_log,
).json()
@@ -197,12 +203,12 @@ def get_scan_detections(self, scan_type: str, scan_id: str) -> List[dict]:
return detections
- def get_get_scan_detections_count_path(self, scan_type: str) -> str:
+ def get_scan_detections_count_path(self, scan_type: str) -> str:
return f'{self.get_scan_detections_path(scan_type)}/count'
def get_scan_detections_count(self, scan_type: str, scan_id: str) -> int:
response = self.scan_cycode_client.get(
- url_path=self.get_get_scan_detections_count_path(scan_type), params={'scan_id': scan_id}
+ url_path=self.get_scan_detections_count_path(scan_type), params={'scan_id': scan_id}
)
return response.json().get('count', 0)
diff --git a/tests/cyclient/mocked_responses/scan_client.py b/tests/cyclient/mocked_responses/scan_client.py
index 55528e8f..b632dc3b 100644
--- a/tests/cyclient/mocked_responses/scan_client.py
+++ b/tests/cyclient/mocked_responses/scan_client.py
@@ -109,7 +109,7 @@ def get_scan_details_response(url: str, scan_id: Optional[UUID] = None) -> respo
def get_scan_detections_count_url(scan_client: ScanClient) -> str:
api_url = scan_client.scan_cycode_client.api_url
- service_url = scan_client.get_get_scan_detections_count_path()
+ service_url = scan_client.get_scan_detections_count_path()
return f'{api_url}/{service_url}'
From 1468484dcb81ea5361c518392fa201ba419db100 Mon Sep 17 00:00:00 2001
From: "dependabot[bot]" <49699333+dependabot[bot]@users.noreply.github.com>
Date: Thu, 11 Jan 2024 11:09:41 +0100
Subject: [PATCH 062/257] Bump gitpython from 3.1.40 to 3.1.41 (#195)
Bumps [gitpython](https://github.com/gitpython-developers/GitPython) from 3.1.40 to 3.1.41.
- [Release notes](https://github.com/gitpython-developers/GitPython/releases)
- [Changelog](https://github.com/gitpython-developers/GitPython/blob/main/CHANGES)
- [Commits](https://github.com/gitpython-developers/GitPython/compare/3.1.40...3.1.41)
---
updated-dependencies:
- dependency-name: gitpython
dependency-type: direct:production
...
Signed-off-by: dependabot[bot]
Co-authored-by: dependabot[bot] <49699333+dependabot[bot]@users.noreply.github.com>
---
poetry.lock | 20 +++++++++++++++-----
1 file changed, 15 insertions(+), 5 deletions(-)
diff --git a/poetry.lock b/poetry.lock
index 4a33ec57..79530954 100644
--- a/poetry.lock
+++ b/poetry.lock
@@ -1,4 +1,4 @@
-# This file is automatically @generated by Poetry 1.6.1 and should not be changed by hand.
+# This file is automatically @generated by Poetry 1.7.1 and should not be changed by hand.
[[package]]
name = "altgraph"
@@ -304,13 +304,13 @@ smmap = ">=3.0.1,<6"
[[package]]
name = "gitpython"
-version = "3.1.40"
+version = "3.1.41"
description = "GitPython is a Python library used to interact with Git repositories"
optional = false
python-versions = ">=3.7"
files = [
- {file = "GitPython-3.1.40-py3-none-any.whl", hash = "sha256:cf14627d5a8049ffbf49915732e5eddbe8134c3bdb9d476e6182b676fc573f8a"},
- {file = "GitPython-3.1.40.tar.gz", hash = "sha256:22b126e9ffb671fdd0c129796343a02bf67bf2994b35449ffc9321aa755e18a4"},
+ {file = "GitPython-3.1.41-py3-none-any.whl", hash = "sha256:c36b6634d069b3f719610175020a9aed919421c87552185b085e04fbbdb10b7c"},
+ {file = "GitPython-3.1.41.tar.gz", hash = "sha256:ed66e624884f76df22c8e16066d567aaa5a37d5b5fa19db2c6df6f7156db9048"},
]
[package.dependencies]
@@ -318,7 +318,7 @@ gitdb = ">=4.0.1,<5"
typing-extensions = {version = ">=3.7.4.3", markers = "python_version < \"3.8\""}
[package.extras]
-test = ["black", "coverage[toml]", "ddt (>=1.1.1,!=1.4.3)", "mock", "mypy", "pre-commit", "pytest", "pytest-cov", "pytest-instafail", "pytest-subtests", "pytest-sugar"]
+test = ["black", "coverage[toml]", "ddt (>=1.1.1,!=1.4.3)", "mock", "mypy", "pre-commit", "pytest (>=7.3.1)", "pytest-cov", "pytest-instafail", "pytest-mock", "pytest-sugar", "sumtypes"]
[[package]]
name = "idna"
@@ -585,6 +585,7 @@ files = [
{file = "PyYAML-6.0.1-cp310-cp310-manylinux_2_17_aarch64.manylinux2014_aarch64.whl", hash = "sha256:69b023b2b4daa7548bcfbd4aa3da05b3a74b772db9e23b982788168117739938"},
{file = "PyYAML-6.0.1-cp310-cp310-manylinux_2_17_s390x.manylinux2014_s390x.whl", hash = "sha256:81e0b275a9ecc9c0c0c07b4b90ba548307583c125f54d5b6946cfee6360c733d"},
{file = "PyYAML-6.0.1-cp310-cp310-manylinux_2_17_x86_64.manylinux2014_x86_64.whl", hash = "sha256:ba336e390cd8e4d1739f42dfe9bb83a3cc2e80f567d8805e11b46f4a943f5515"},
+ {file = "PyYAML-6.0.1-cp310-cp310-musllinux_1_1_x86_64.whl", hash = "sha256:326c013efe8048858a6d312ddd31d56e468118ad4cdeda36c719bf5bb6192290"},
{file = "PyYAML-6.0.1-cp310-cp310-win32.whl", hash = "sha256:bd4af7373a854424dabd882decdc5579653d7868b8fb26dc7d0e99f823aa5924"},
{file = "PyYAML-6.0.1-cp310-cp310-win_amd64.whl", hash = "sha256:fd1592b3fdf65fff2ad0004b5e363300ef59ced41c2e6b3a99d4089fa8c5435d"},
{file = "PyYAML-6.0.1-cp311-cp311-macosx_10_9_x86_64.whl", hash = "sha256:6965a7bc3cf88e5a1c3bd2e0b5c22f8d677dc88a455344035f03399034eb3007"},
@@ -592,8 +593,15 @@ files = [
{file = "PyYAML-6.0.1-cp311-cp311-manylinux_2_17_aarch64.manylinux2014_aarch64.whl", hash = "sha256:42f8152b8dbc4fe7d96729ec2b99c7097d656dc1213a3229ca5383f973a5ed6d"},
{file = "PyYAML-6.0.1-cp311-cp311-manylinux_2_17_s390x.manylinux2014_s390x.whl", hash = "sha256:062582fca9fabdd2c8b54a3ef1c978d786e0f6b3a1510e0ac93ef59e0ddae2bc"},
{file = "PyYAML-6.0.1-cp311-cp311-manylinux_2_17_x86_64.manylinux2014_x86_64.whl", hash = "sha256:d2b04aac4d386b172d5b9692e2d2da8de7bfb6c387fa4f801fbf6fb2e6ba4673"},
+ {file = "PyYAML-6.0.1-cp311-cp311-musllinux_1_1_x86_64.whl", hash = "sha256:e7d73685e87afe9f3b36c799222440d6cf362062f78be1013661b00c5c6f678b"},
{file = "PyYAML-6.0.1-cp311-cp311-win32.whl", hash = "sha256:1635fd110e8d85d55237ab316b5b011de701ea0f29d07611174a1b42f1444741"},
{file = "PyYAML-6.0.1-cp311-cp311-win_amd64.whl", hash = "sha256:bf07ee2fef7014951eeb99f56f39c9bb4af143d8aa3c21b1677805985307da34"},
+ {file = "PyYAML-6.0.1-cp312-cp312-macosx_10_9_x86_64.whl", hash = "sha256:855fb52b0dc35af121542a76b9a84f8d1cd886ea97c84703eaa6d88e37a2ad28"},
+ {file = "PyYAML-6.0.1-cp312-cp312-macosx_11_0_arm64.whl", hash = "sha256:40df9b996c2b73138957fe23a16a4f0ba614f4c0efce1e9406a184b6d07fa3a9"},
+ {file = "PyYAML-6.0.1-cp312-cp312-manylinux_2_17_x86_64.manylinux2014_x86_64.whl", hash = "sha256:6c22bec3fbe2524cde73d7ada88f6566758a8f7227bfbf93a408a9d86bcc12a0"},
+ {file = "PyYAML-6.0.1-cp312-cp312-musllinux_1_1_x86_64.whl", hash = "sha256:8d4e9c88387b0f5c7d5f281e55304de64cf7f9c0021a3525bd3b1c542da3b0e4"},
+ {file = "PyYAML-6.0.1-cp312-cp312-win32.whl", hash = "sha256:d483d2cdf104e7c9fa60c544d92981f12ad66a457afae824d146093b8c294c54"},
+ {file = "PyYAML-6.0.1-cp312-cp312-win_amd64.whl", hash = "sha256:0d3304d8c0adc42be59c5f8a4d9e3d7379e6955ad754aa9d6ab7a398b59dd1df"},
{file = "PyYAML-6.0.1-cp36-cp36m-macosx_10_9_x86_64.whl", hash = "sha256:50550eb667afee136e9a77d6dc71ae76a44df8b3e51e41b77f6de2932bfe0f47"},
{file = "PyYAML-6.0.1-cp36-cp36m-manylinux_2_17_aarch64.manylinux2014_aarch64.whl", hash = "sha256:1fe35611261b29bd1de0070f0b2f47cb6ff71fa6595c077e42bd0c419fa27b98"},
{file = "PyYAML-6.0.1-cp36-cp36m-manylinux_2_17_s390x.manylinux2014_s390x.whl", hash = "sha256:704219a11b772aea0d8ecd7058d0082713c3562b4e271b849ad7dc4a5c90c13c"},
@@ -610,6 +618,7 @@ files = [
{file = "PyYAML-6.0.1-cp38-cp38-manylinux_2_17_aarch64.manylinux2014_aarch64.whl", hash = "sha256:a0cd17c15d3bb3fa06978b4e8958dcdc6e0174ccea823003a106c7d4d7899ac5"},
{file = "PyYAML-6.0.1-cp38-cp38-manylinux_2_17_s390x.manylinux2014_s390x.whl", hash = "sha256:28c119d996beec18c05208a8bd78cbe4007878c6dd15091efb73a30e90539696"},
{file = "PyYAML-6.0.1-cp38-cp38-manylinux_2_17_x86_64.manylinux2014_x86_64.whl", hash = "sha256:7e07cbde391ba96ab58e532ff4803f79c4129397514e1413a7dc761ccd755735"},
+ {file = "PyYAML-6.0.1-cp38-cp38-musllinux_1_1_x86_64.whl", hash = "sha256:49a183be227561de579b4a36efbb21b3eab9651dd81b1858589f796549873dd6"},
{file = "PyYAML-6.0.1-cp38-cp38-win32.whl", hash = "sha256:184c5108a2aca3c5b3d3bf9395d50893a7ab82a38004c8f61c258d4428e80206"},
{file = "PyYAML-6.0.1-cp38-cp38-win_amd64.whl", hash = "sha256:1e2722cc9fbb45d9b87631ac70924c11d3a401b2d7f410cc0e3bbf249f2dca62"},
{file = "PyYAML-6.0.1-cp39-cp39-macosx_10_9_x86_64.whl", hash = "sha256:9eb6caa9a297fc2c2fb8862bc5370d0303ddba53ba97e71f08023b6cd73d16a8"},
@@ -617,6 +626,7 @@ files = [
{file = "PyYAML-6.0.1-cp39-cp39-manylinux_2_17_aarch64.manylinux2014_aarch64.whl", hash = "sha256:5773183b6446b2c99bb77e77595dd486303b4faab2b086e7b17bc6bef28865f6"},
{file = "PyYAML-6.0.1-cp39-cp39-manylinux_2_17_s390x.manylinux2014_s390x.whl", hash = "sha256:b786eecbdf8499b9ca1d697215862083bd6d2a99965554781d0d8d1ad31e13a0"},
{file = "PyYAML-6.0.1-cp39-cp39-manylinux_2_17_x86_64.manylinux2014_x86_64.whl", hash = "sha256:bc1bf2925a1ecd43da378f4db9e4f799775d6367bdb94671027b73b393a7c42c"},
+ {file = "PyYAML-6.0.1-cp39-cp39-musllinux_1_1_x86_64.whl", hash = "sha256:04ac92ad1925b2cff1db0cfebffb6ffc43457495c9b3c39d3fcae417d7125dc5"},
{file = "PyYAML-6.0.1-cp39-cp39-win32.whl", hash = "sha256:faca3bdcf85b2fc05d06ff3fbc1f83e1391b3e724afa3feba7d13eeab355484c"},
{file = "PyYAML-6.0.1-cp39-cp39-win_amd64.whl", hash = "sha256:510c9deebc5c0225e8c96813043e62b680ba2f9c50a08d3724c7f28a747d1486"},
{file = "PyYAML-6.0.1.tar.gz", hash = "sha256:bfdf460b1736c775f2ba9f6a92bca30bc2095067b8a9d77876d1fad6cc3b4a43"},
From 7978be2c8bb91681510a95dca922a496a11b714e Mon Sep 17 00:00:00 2001
From: Ilya Siamionau
Date: Tue, 16 Jan 2024 11:23:45 +0100
Subject: [PATCH 063/257] CM-31321 - Fix multiprocessing module in packaged CLI
with Python 3.12 on macOS (#196)
---
cycode/cli/main.py | 7 +++++++
1 file changed, 7 insertions(+)
diff --git a/cycode/cli/main.py b/cycode/cli/main.py
index b27c98e2..dd2d1fa7 100644
--- a/cycode/cli/main.py
+++ b/cycode/cli/main.py
@@ -1,4 +1,11 @@
+from multiprocessing import freeze_support
+
from cycode.cli.commands.main_cli import main_cli
if __name__ == '__main__':
+ # DO NOT REMOVE OR MOVE THIS LINE
+ # this is required to support multiprocessing in executables files packaged with PyInstaller
+ # see https://pyinstaller.org/en/latest/common-issues-and-pitfalls.html#multi-processing
+ freeze_support()
+
main_cli()
From 19b32271f3bfbbccff56e46ce31a0fa77fce266a Mon Sep 17 00:00:00 2001
From: morsa4406 <104304449+morsa4406@users.noreply.github.com>
Date: Wed, 17 Jan 2024 17:49:10 +0200
Subject: [PATCH 064/257] CM-31412 - Fix severity sorting for unknown severity
(#197)
* CM-31412 [cli] - SCA- fix advisory severity is missing throw exception in sorted detections
---
cycode/cli/models.py | 9 +++++++++
cycode/cli/printers/tables/sca_table_printer.py | 2 +-
2 files changed, 10 insertions(+), 1 deletion(-)
diff --git a/cycode/cli/models.py b/cycode/cli/models.py
index d60801df..4c6b725b 100644
--- a/cycode/cli/models.py
+++ b/cycode/cli/models.py
@@ -2,6 +2,7 @@
from enum import Enum
from typing import Dict, List, NamedTuple, Optional, Type
+from cycode.cyclient import logger
from cycode.cyclient.models import Detection
@@ -42,6 +43,14 @@ def try_get_value(name: str) -> any:
return Severity[name].value
+ @staticmethod
+ def get_member_weight(name: str) -> any:
+ weight = Severity.try_get_value(name)
+ if weight is None:
+ logger.debug(f'missing severity in enum: {name}')
+ return -2
+ return weight
+
class CliError(NamedTuple):
code: str
diff --git a/cycode/cli/printers/tables/sca_table_printer.py b/cycode/cli/printers/tables/sca_table_printer.py
index e9c0e937..702a7514 100644
--- a/cycode/cli/printers/tables/sca_table_printer.py
+++ b/cycode/cli/printers/tables/sca_table_printer.py
@@ -74,7 +74,7 @@ def __group_by(detections: List[Detection], details_field_name: str) -> Dict[str
@staticmethod
def __severity_sort_key(detection: Detection) -> int:
severity = detection.detection_details.get('advisory_severity')
- return Severity.try_get_value(severity)
+ return Severity.get_member_weight(severity)
def _sort_detections_by_severity(self, detections: List[Detection]) -> List[Detection]:
return sorted(detections, key=self.__severity_sort_key, reverse=True)
From 825b5a3106837ab99a5eb484f482e6f660d2afdb Mon Sep 17 00:00:00 2001
From: Ilya Siamionau
Date: Mon, 22 Jan 2024 11:45:02 +0100
Subject: [PATCH 065/257] CM-31407 - Add new fields to scan parameters (#198)
---
cycode/cli/commands/scan/code_scanner.py | 23 +++++++++++++++--------
1 file changed, 15 insertions(+), 8 deletions(-)
diff --git a/cycode/cli/commands/scan/code_scanner.py b/cycode/cli/commands/scan/code_scanner.py
index d700da55..047d0631 100644
--- a/cycode/cli/commands/scan/code_scanner.py
+++ b/cycode/cli/commands/scan/code_scanner.py
@@ -140,11 +140,13 @@ def _get_scan_documents_thread_func(
severity_threshold = context.obj['severity_threshold']
command_scan_type = context.info_name
+ scan_parameters['aggregation_id'] = str(_generate_unique_id())
+
def _scan_batch_thread_func(batch: List[Document]) -> Tuple[str, CliError, LocalScanResult]:
local_scan_result = error = error_message = None
detections_count = relevant_detections_count = zip_file_size = 0
- scan_id = str(_get_scan_id())
+ scan_id = str(_generate_unique_id())
scan_completed = False
try:
@@ -269,6 +271,9 @@ def scan_documents(
is_commit_range: bool = False,
scan_parameters: Optional[dict] = None,
) -> None:
+ if not scan_parameters:
+ scan_parameters = get_default_scan_parameters(context)
+
progress_bar = context.obj['progress_bar']
if not documents_to_scan:
@@ -309,7 +314,7 @@ def scan_commit_range_documents(
local_scan_result = error_message = None
scan_completed = False
- scan_id = str(_get_scan_id())
+ scan_id = str(_generate_unique_id())
from_commit_zipped_documents = InMemoryZip()
to_commit_zipped_documents = InMemoryZip()
@@ -570,12 +575,18 @@ def get_default_scan_parameters(context: click.Context) -> dict:
'report': context.obj.get('report'),
'package_vulnerabilities': context.obj.get('package-vulnerabilities'),
'license_compliance': context.obj.get('license-compliance'),
+ 'command_type': context.info_name,
}
def get_scan_parameters(context: click.Context, paths: Tuple[str]) -> dict:
scan_parameters = get_default_scan_parameters(context)
+ if not paths:
+ return scan_parameters
+
+ scan_parameters['paths'] = paths
+
if len(paths) != 1:
# ignore remote url if multiple paths are provided
return scan_parameters
@@ -584,11 +595,7 @@ def get_scan_parameters(context: click.Context, paths: Tuple[str]) -> dict:
if remote_url:
# TODO(MarshalX): remove hardcode in context
context.obj['remote_url'] = remote_url
- scan_parameters.update(
- {
- 'remote_url': remote_url,
- }
- )
+ scan_parameters['remote_url'] = remote_url
return scan_parameters
@@ -749,7 +756,7 @@ def _report_scan_status(
logger.debug('Failed to report scan status, %s', {'exception_message': str(e)})
-def _get_scan_id() -> UUID:
+def _generate_unique_id() -> UUID:
return uuid4()
From d374c4daa43d21e75a0c769ce5253d8cfdb39174 Mon Sep 17 00:00:00 2001
From: Ilya Siamionau
Date: Tue, 23 Jan 2024 11:34:41 +0100
Subject: [PATCH 066/257] CM-29444 - Add caching of access token (#199)
---
cycode/cli/commands/auth/auth_command.py | 2 +-
cycode/cli/commands/auth/auth_manager.py | 2 +-
.../commands/configure/configure_command.py | 2 +-
.../cli/user_settings/credentials_manager.py | 42 ++++++++---
cycode/cli/user_settings/jwt_creator.py | 24 ++++++
cycode/cyclient/cycode_token_based_client.py | 69 ++++++++++++-----
.../configure/test_configure_command.py | 12 +--
tests/conftest.py | 19 ++++-
tests/cyclient/test_token_based_client.py | 75 +++++++++++++++++--
9 files changed, 201 insertions(+), 46 deletions(-)
create mode 100644 cycode/cli/user_settings/jwt_creator.py
diff --git a/cycode/cli/commands/auth/auth_command.py b/cycode/cli/commands/auth/auth_command.py
index 51eb212b..87171441 100644
--- a/cycode/cli/commands/auth/auth_command.py
+++ b/cycode/cli/commands/auth/auth_command.py
@@ -50,7 +50,7 @@ def authorization_check(context: click.Context) -> None:
return
try:
- if CycodeTokenBasedClient(client_id, client_secret).api_token:
+ if CycodeTokenBasedClient(client_id, client_secret).get_access_token():
printer.print_result(passed_auth_check_res)
return
except (NetworkError, HttpUnauthorizedError):
diff --git a/cycode/cli/commands/auth/auth_manager.py b/cycode/cli/commands/auth/auth_manager.py
index 11fbf751..829164c2 100644
--- a/cycode/cli/commands/auth/auth_manager.py
+++ b/cycode/cli/commands/auth/auth_manager.py
@@ -75,7 +75,7 @@ def get_api_token_polling(self, session_id: str, code_verifier: str) -> 'ApiToke
raise AuthProcessError('session expired')
def save_api_token(self, api_token: 'ApiToken') -> None:
- self.credentials_manager.update_credentials_file(api_token.client_id, api_token.secret)
+ self.credentials_manager.update_credentials(api_token.client_id, api_token.secret)
def _build_login_url(self, code_challenge: str, session_id: str) -> str:
app_url = self.configuration_manager.get_cycode_app_url()
diff --git a/cycode/cli/commands/configure/configure_command.py b/cycode/cli/commands/configure/configure_command.py
index 5f9bad0e..5fe695ac 100644
--- a/cycode/cli/commands/configure/configure_command.py
+++ b/cycode/cli/commands/configure/configure_command.py
@@ -48,7 +48,7 @@ def configure_command() -> None:
credentials_updated = False
if _should_update_value(current_client_id, client_id) or _should_update_value(current_client_secret, client_secret):
credentials_updated = True
- _CREDENTIALS_MANAGER.update_credentials_file(client_id, client_secret)
+ _CREDENTIALS_MANAGER.update_credentials(client_id, client_secret)
if config_updated:
click.echo(_get_urls_update_result_message())
diff --git a/cycode/cli/user_settings/credentials_manager.py b/cycode/cli/user_settings/credentials_manager.py
index 02653f6d..c302fc96 100644
--- a/cycode/cli/user_settings/credentials_manager.py
+++ b/cycode/cli/user_settings/credentials_manager.py
@@ -4,15 +4,19 @@
from cycode.cli.config import CYCODE_CLIENT_ID_ENV_VAR_NAME, CYCODE_CLIENT_SECRET_ENV_VAR_NAME
from cycode.cli.user_settings.base_file_manager import BaseFileManager
-from cycode.cli.utils.yaml_utils import read_file
+from cycode.cli.user_settings.jwt_creator import JwtCreator
class CredentialsManager(BaseFileManager):
HOME_PATH: str = Path.home()
CYCODE_HIDDEN_DIRECTORY: str = '.cycode'
FILE_NAME: str = 'credentials.yaml'
+
CLIENT_ID_FIELD_NAME: str = 'cycode_client_id'
CLIENT_SECRET_FIELD_NAME: str = 'cycode_client_secret'
+ ACCESS_TOKEN_FIELD_NAME: str = 'cycode_access_token'
+ ACCESS_TOKEN_EXPIRES_IN_FIELD_NAME: str = 'cycode_access_token_expires_in'
+ ACCESS_TOKEN_CREATOR_FIELD_NAME: str = 'cycode_access_token_creator'
def get_credentials(self) -> Tuple[str, str]:
client_id, client_secret = self.get_credentials_from_environment_variables()
@@ -28,21 +32,37 @@ def get_credentials_from_environment_variables() -> Tuple[str, str]:
return client_id, client_secret
def get_credentials_from_file(self) -> Tuple[Optional[str], Optional[str]]:
- credentials_filename = self.get_filename()
- try:
- file_content = read_file(credentials_filename)
- except FileNotFoundError:
- return None, None
-
+ file_content = self.read_file()
client_id = file_content.get(self.CLIENT_ID_FIELD_NAME)
client_secret = file_content.get(self.CLIENT_SECRET_FIELD_NAME)
return client_id, client_secret
- def update_credentials_file(self, client_id: str, client_secret: str) -> None:
- credentials = {self.CLIENT_ID_FIELD_NAME: client_id, self.CLIENT_SECRET_FIELD_NAME: client_secret}
+ def update_credentials(self, client_id: str, client_secret: str) -> None:
+ file_content_to_update = {self.CLIENT_ID_FIELD_NAME: client_id, self.CLIENT_SECRET_FIELD_NAME: client_secret}
+ self.write_content_to_file(file_content_to_update)
+
+ def get_access_token(self) -> Tuple[Optional[str], Optional[float], Optional[JwtCreator]]:
+ file_content = self.read_file()
+
+ access_token = file_content.get(self.ACCESS_TOKEN_FIELD_NAME)
+ expires_in = file_content.get(self.ACCESS_TOKEN_EXPIRES_IN_FIELD_NAME)
+
+ creator = None
+ hashed_creator = file_content.get(self.ACCESS_TOKEN_CREATOR_FIELD_NAME)
+ if hashed_creator:
+ creator = JwtCreator(hashed_creator)
+
+ return access_token, expires_in, creator
- self.get_filename()
- self.write_content_to_file(credentials)
+ def update_access_token(
+ self, access_token: Optional[str], expires_in: Optional[float], creator: Optional[JwtCreator]
+ ) -> None:
+ file_content_to_update = {
+ self.ACCESS_TOKEN_FIELD_NAME: access_token,
+ self.ACCESS_TOKEN_EXPIRES_IN_FIELD_NAME: expires_in,
+ self.ACCESS_TOKEN_CREATOR_FIELD_NAME: str(creator) if creator else None,
+ }
+ self.write_content_to_file(file_content_to_update)
def get_filename(self) -> str:
return os.path.join(self.HOME_PATH, self.CYCODE_HIDDEN_DIRECTORY, self.FILE_NAME)
diff --git a/cycode/cli/user_settings/jwt_creator.py b/cycode/cli/user_settings/jwt_creator.py
new file mode 100644
index 00000000..e3778f92
--- /dev/null
+++ b/cycode/cli/user_settings/jwt_creator.py
@@ -0,0 +1,24 @@
+from cycode.cli.utils.string_utils import hash_string_to_sha256
+
+_SEPARATOR = '::'
+
+
+def _get_hashed_creator(client_id: str, client_secret: str) -> str:
+ return hash_string_to_sha256(_SEPARATOR.join([client_id, client_secret]))
+
+
+class JwtCreator:
+ def __init__(self, hashed_creator: str) -> None:
+ self._hashed_creator = hashed_creator
+
+ def __str__(self) -> str:
+ return self._hashed_creator
+
+ @classmethod
+ def create(cls, client_id: str, client_secret: str) -> 'JwtCreator':
+ return cls(_get_hashed_creator(client_id, client_secret))
+
+ def __eq__(self, other: 'JwtCreator') -> bool:
+ if not isinstance(other, JwtCreator):
+ return NotImplemented
+ return str(self) == str(other)
diff --git a/cycode/cyclient/cycode_token_based_client.py b/cycode/cyclient/cycode_token_based_client.py
index c73999fb..d13ce62d 100644
--- a/cycode/cyclient/cycode_token_based_client.py
+++ b/cycode/cyclient/cycode_token_based_client.py
@@ -2,35 +2,52 @@
from typing import Optional
import arrow
+from requests import Response
-from .cycode_client import CycodeClient
+from cycode.cli.user_settings.credentials_manager import CredentialsManager
+from cycode.cli.user_settings.jwt_creator import JwtCreator
+from cycode.cyclient.cycode_client import CycodeClient
class CycodeTokenBasedClient(CycodeClient):
- """Send requests with api token"""
+ """Send requests with JWT."""
def __init__(self, client_id: str, client_secret: str) -> None:
super().__init__()
self.client_secret = client_secret
self.client_id = client_id
- self._api_token = None
- self._expires_in = None
+ self._credentials_manager = CredentialsManager()
+ # load cached access token
+ access_token, expires_in, creator = self._credentials_manager.get_access_token()
+
+ self._access_token = self._expires_in = None
+ if creator == JwtCreator.create(client_id, client_secret):
+ # we must be sure that cached access token is created using the same client id and client secret.
+ # because client id and client secret could be passed via command, via env vars or via config file.
+ # we must not use cached access token if client id or client secret was changed.
+ self._access_token = access_token
+ self._expires_in = arrow.get(expires_in) if expires_in else None
+
+ self._lock = Lock()
- self.lock = Lock()
+ def get_access_token(self) -> str:
+ with self._lock:
+ self.refresh_access_token_if_needed()
+ return self._access_token
+
+ def invalidate_access_token(self, in_storage: bool = False) -> None:
+ self._access_token = None
+ self._expires_in = None
- @property
- def api_token(self) -> str:
- # TODO(MarshalX): This property performs HTTP request to refresh the token. This must be the method.
- with self.lock:
- self.refresh_api_token_if_needed()
- return self._api_token
+ if in_storage:
+ self._credentials_manager.update_access_token(None, None, None)
- def refresh_api_token_if_needed(self) -> None:
- if self._api_token is None or self._expires_in is None or arrow.utcnow() >= self._expires_in:
- self.refresh_api_token()
+ def refresh_access_token_if_needed(self) -> None:
+ if self._access_token is None or self._expires_in is None or arrow.utcnow() >= self._expires_in:
+ self.refresh_access_token()
- def refresh_api_token(self) -> None:
+ def refresh_access_token(self) -> None:
auth_response = self.post(
url_path='api/v1/auth/api-token',
body={'clientId': self.client_id, 'secret': self.client_secret},
@@ -39,9 +56,12 @@ def refresh_api_token(self) -> None:
)
auth_response_data = auth_response.json()
- self._api_token = auth_response_data['token']
+ self._access_token = auth_response_data['token']
self._expires_in = arrow.utcnow().shift(seconds=auth_response_data['expires_in'] * 0.8)
+ jwt_creator = JwtCreator.create(self.client_id, self.client_secret)
+ self._credentials_manager.update_access_token(self._access_token, self._expires_in.timestamp(), jwt_creator)
+
def get_request_headers(self, additional_headers: Optional[dict] = None, without_auth: bool = False) -> dict:
headers = super().get_request_headers(additional_headers=additional_headers)
@@ -51,5 +71,20 @@ def get_request_headers(self, additional_headers: Optional[dict] = None, without
return headers
def _add_auth_header(self, headers: dict) -> dict:
- headers['Authorization'] = f'Bearer {self.api_token}'
+ headers['Authorization'] = f'Bearer {self.get_access_token()}'
return headers
+
+ def _execute(
+ self,
+ *args,
+ **kwargs,
+ ) -> Response:
+ response = super()._execute(*args, **kwargs)
+
+ # backend returns 200 and plain text. no way to catch it with .raise_for_status()
+ if response.status_code == 200 and response.content in {b'Invalid JWT Token\n\n', b'JWT Token Needed\n\n'}:
+ # if cached token is invalid, try to refresh it and retry the request
+ self.refresh_access_token()
+ response = super()._execute(*args, **kwargs)
+
+ return response
diff --git a/tests/cli/commands/configure/test_configure_command.py b/tests/cli/commands/configure/test_configure_command.py
index 4c42971b..c5ae2b9c 100644
--- a/tests/cli/commands/configure/test_configure_command.py
+++ b/tests/cli/commands/configure/test_configure_command.py
@@ -35,7 +35,7 @@ def test_configure_command_no_exist_values_in_file(mocker: 'MockerFixture') -> N
)
mocked_update_credentials = mocker.patch(
- 'cycode.cli.user_settings.credentials_manager.CredentialsManager.update_credentials_file'
+ 'cycode.cli.user_settings.credentials_manager.CredentialsManager.update_credentials'
)
mocked_update_api_base_url = mocker.patch(
'cycode.cli.user_settings.config_file_manager.ConfigFileManager.update_api_base_url'
@@ -80,7 +80,7 @@ def test_configure_command_update_current_configs_in_files(mocker: 'MockerFixtur
)
mocked_update_credentials = mocker.patch(
- 'cycode.cli.user_settings.credentials_manager.CredentialsManager.update_credentials_file'
+ 'cycode.cli.user_settings.credentials_manager.CredentialsManager.update_credentials'
)
mocked_update_api_base_url = mocker.patch(
'cycode.cli.user_settings.config_file_manager.ConfigFileManager.update_api_base_url'
@@ -110,7 +110,7 @@ def test_set_credentials_update_only_client_id(mocker: 'MockerFixture') -> None:
# side effect - multiple return values, each item in the list represents return of a call
mocker.patch('click.prompt', side_effect=['', '', client_id_user_input, ''])
mocked_update_credentials = mocker.patch(
- 'cycode.cli.user_settings.credentials_manager.CredentialsManager.update_credentials_file'
+ 'cycode.cli.user_settings.credentials_manager.CredentialsManager.update_credentials'
)
# Act
@@ -133,7 +133,7 @@ def test_configure_command_update_only_client_secret(mocker: 'MockerFixture') ->
# side effect - multiple return values, each item in the list represents return of a call
mocker.patch('click.prompt', side_effect=['', '', '', client_secret_user_input])
mocked_update_credentials = mocker.patch(
- 'cycode.cli.user_settings.credentials_manager.CredentialsManager.update_credentials_file'
+ 'cycode.cli.user_settings.credentials_manager.CredentialsManager.update_credentials'
)
# Act
@@ -166,7 +166,7 @@ def test_configure_command_update_only_api_url(mocker: 'MockerFixture') -> None:
mocked_update_api_base_url.assert_called_once_with(api_url_user_input)
-def test_configure_command_should_not_update_credentials_file(mocker: 'MockerFixture') -> None:
+def test_configure_command_should_not_update_credentials(mocker: 'MockerFixture') -> None:
# Arrange
client_id_user_input = ''
client_secret_user_input = ''
@@ -179,7 +179,7 @@ def test_configure_command_should_not_update_credentials_file(mocker: 'MockerFix
# side effect - multiple return values, each item in the list represents return of a call
mocker.patch('click.prompt', side_effect=['', '', client_id_user_input, client_secret_user_input])
mocked_update_credentials = mocker.patch(
- 'cycode.cli.user_settings.credentials_manager.CredentialsManager.update_credentials_file'
+ 'cycode.cli.user_settings.credentials_manager.CredentialsManager.update_credentials'
)
# Act
diff --git a/tests/conftest.py b/tests/conftest.py
index dc1a84fe..821a0289 100644
--- a/tests/conftest.py
+++ b/tests/conftest.py
@@ -1,8 +1,10 @@
from pathlib import Path
+from typing import Optional
import pytest
import responses
+from cycode.cli.user_settings.credentials_manager import CredentialsManager
from cycode.cyclient.client_creator import create_scan_client
from cycode.cyclient.cycode_token_based_client import CycodeTokenBasedClient
from cycode.cyclient.scan_client import ScanClient
@@ -29,9 +31,22 @@ def scan_client() -> ScanClient:
return create_scan_client(_CLIENT_ID, _CLIENT_SECRET, hide_response_log=False)
+def create_token_based_client(
+ client_id: Optional[str] = None, client_secret: Optional[str] = None
+) -> CycodeTokenBasedClient:
+ CredentialsManager.FILE_NAME = 'unit-tests-credentials.yaml'
+
+ if client_id is None:
+ client_id = _CLIENT_ID
+ if client_secret is None:
+ client_secret = _CLIENT_SECRET
+
+ return CycodeTokenBasedClient(client_id, client_secret)
+
+
@pytest.fixture(scope='session')
def token_based_client() -> CycodeTokenBasedClient:
- return CycodeTokenBasedClient(_CLIENT_ID, _CLIENT_SECRET)
+ return create_token_based_client()
@pytest.fixture(scope='session')
@@ -57,4 +72,4 @@ def api_token_response(api_token_url: str) -> responses.Response:
@responses.activate
def api_token(token_based_client: CycodeTokenBasedClient, api_token_response: responses.Response) -> str:
responses.add(api_token_response)
- return token_based_client.api_token
+ return token_based_client.get_access_token()
diff --git a/tests/cyclient/test_token_based_client.py b/tests/cyclient/test_token_based_client.py
index b5d824f4..4c3dd4c5 100644
--- a/tests/cyclient/test_token_based_client.py
+++ b/tests/cyclient/test_token_based_client.py
@@ -2,30 +2,31 @@
import responses
from cycode.cyclient.cycode_token_based_client import CycodeTokenBasedClient
-from tests.conftest import _EXPECTED_API_TOKEN
+from tests.conftest import _EXPECTED_API_TOKEN, create_token_based_client
@responses.activate
-def test_api_token_new(token_based_client: CycodeTokenBasedClient, api_token_response: responses.Response) -> None:
+def test_access_token_new(token_based_client: CycodeTokenBasedClient, api_token_response: responses.Response) -> None:
responses.add(api_token_response)
- api_token = token_based_client.api_token
+ api_token = token_based_client.get_access_token()
assert api_token == _EXPECTED_API_TOKEN
@responses.activate
-def test_api_token_expired(token_based_client: CycodeTokenBasedClient, api_token_response: responses.Response) -> None:
+def test_access_token_expired(
+ token_based_client: CycodeTokenBasedClient, api_token_response: responses.Response
+) -> None:
responses.add(api_token_response)
- # this property performs HTTP req to refresh the token. IDE doesn't know it
- token_based_client.api_token # noqa: B018
+ token_based_client.get_access_token()
# mark token as expired
token_based_client._expires_in = arrow.utcnow().shift(hours=-1)
# refresh token
- api_token_refreshed = token_based_client.api_token
+ api_token_refreshed = token_based_client.get_access_token()
assert api_token_refreshed == _EXPECTED_API_TOKEN
@@ -35,3 +36,63 @@ def test_get_request_headers(token_based_client: CycodeTokenBasedClient, api_tok
expected_headers = {**token_based_client.MANDATORY_HEADERS, **token_based_headers}
assert token_based_client.get_request_headers() == expected_headers
+
+
+@responses.activate
+def test_access_token_cached(
+ token_based_client: CycodeTokenBasedClient, api_token_response: responses.Response
+) -> None:
+ # save to cache
+ responses.add(api_token_response)
+ token_based_client.get_access_token()
+
+ # load from cache
+ client2 = create_token_based_client()
+ assert client2._access_token == token_based_client._access_token
+ assert client2._expires_in == token_based_client._expires_in
+
+
+@responses.activate
+def test_access_token_cached_creator_changed(
+ token_based_client: CycodeTokenBasedClient, api_token_response: responses.Response
+) -> None:
+ # save to cache
+ responses.add(api_token_response)
+ token_based_client.get_access_token()
+
+ # load from cache with another client id and client secret
+ client2 = create_token_based_client('client_id2', 'client_secret2')
+ assert client2._access_token is None
+ assert client2._expires_in is None
+
+
+@responses.activate
+def test_access_token_invalidation(
+ token_based_client: CycodeTokenBasedClient, api_token_response: responses.Response
+) -> None:
+ # save to cache
+ responses.add(api_token_response)
+ token_based_client.get_access_token()
+
+ expected_access_token = token_based_client._access_token
+ expected_expires_in = token_based_client._expires_in
+
+ # invalidate in runtime
+ token_based_client.invalidate_access_token()
+ assert token_based_client._access_token is None
+ assert token_based_client._expires_in is None
+
+ # load from cache
+ client2 = create_token_based_client()
+ assert client2._access_token == expected_access_token
+ assert client2._expires_in == expected_expires_in
+
+ # invalidate in storage
+ client2.invalidate_access_token(in_storage=True)
+ assert client2._access_token is None
+ assert client2._expires_in is None
+
+ # load from cache again
+ client3 = create_token_based_client()
+ assert client3._access_token is None
+ assert client3._expires_in is None
From 2c1bc3516c0759e60d2f8f81d9cd328e481d1834 Mon Sep 17 00:00:00 2001
From: Ilya Siamionau
Date: Tue, 23 Jan 2024 11:37:11 +0100
Subject: [PATCH 067/257] CM-31596 - Enable GitHub output in ruff workflow
(#200)
---
.github/workflows/ruff.yml | 2 +-
1 file changed, 1 insertion(+), 1 deletion(-)
diff --git a/.github/workflows/ruff.yml b/.github/workflows/ruff.yml
index 73fcf08a..a7f86c2b 100644
--- a/.github/workflows/ruff.yml
+++ b/.github/workflows/ruff.yml
@@ -45,7 +45,7 @@ jobs:
run: poetry install
- name: Run linter check
- run: poetry run ruff check .
+ run: poetry run ruff check --output-format=github .
- name: Run code style check
run: poetry run ruff format --check .
From b44d406f71419061891df1382bff3bd1d86f55f6 Mon Sep 17 00:00:00 2001
From: Ilya Siamionau
Date: Tue, 23 Jan 2024 11:49:27 +0100
Subject: [PATCH 068/257] CM-31598 - Use absolute imports instead of relative
ones (#201)
---
cycode/cyclient/__init__.py | 2 +-
cycode/cyclient/auth_client.py | 5 ++---
cycode/cyclient/cycode_client.py | 4 ++--
cycode/cyclient/cycode_client_base.py | 4 +---
cycode/cyclient/cycode_dev_based_client.py | 4 ++--
cycode/cyclient/scan_client.py | 2 +-
pyproject.toml | 3 +++
7 files changed, 12 insertions(+), 12 deletions(-)
diff --git a/cycode/cyclient/__init__.py b/cycode/cyclient/__init__.py
index 7018a231..9bea26e9 100644
--- a/cycode/cyclient/__init__.py
+++ b/cycode/cyclient/__init__.py
@@ -1,4 +1,4 @@
-from .config import logger
+from cycode.cyclient.config import logger
__all__ = [
'logger',
diff --git a/cycode/cyclient/auth_client.py b/cycode/cyclient/auth_client.py
index 626d4ff9..91f43ad1 100644
--- a/cycode/cyclient/auth_client.py
+++ b/cycode/cyclient/auth_client.py
@@ -3,9 +3,8 @@
from requests import Response
from cycode.cli.exceptions.custom_exceptions import HttpUnauthorizedError, NetworkError
-
-from . import models
-from .cycode_client import CycodeClient
+from cycode.cyclient import models
+from cycode.cyclient.cycode_client import CycodeClient
class AuthClient:
diff --git a/cycode/cyclient/cycode_client.py b/cycode/cyclient/cycode_client.py
index dfbd2269..eded92da 100644
--- a/cycode/cyclient/cycode_client.py
+++ b/cycode/cyclient/cycode_client.py
@@ -1,5 +1,5 @@
-from . import config
-from .cycode_client_base import CycodeClientBase
+from cycode.cyclient import config
+from cycode.cyclient.cycode_client_base import CycodeClientBase
class CycodeClient(CycodeClientBase):
diff --git a/cycode/cyclient/cycode_client_base.py b/cycode/cyclient/cycode_client_base.py
index d804b8cb..a1fb68bb 100644
--- a/cycode/cyclient/cycode_client_base.py
+++ b/cycode/cyclient/cycode_client_base.py
@@ -6,9 +6,7 @@
from cycode import __version__
from cycode.cli.exceptions.custom_exceptions import HttpUnauthorizedError, NetworkError
from cycode.cli.user_settings.configuration_manager import ConfigurationManager
-from cycode.cyclient import logger
-
-from . import config
+from cycode.cyclient import config, logger
def get_cli_user_agent() -> str:
diff --git a/cycode/cyclient/cycode_dev_based_client.py b/cycode/cyclient/cycode_dev_based_client.py
index f325bd6e..347797c3 100644
--- a/cycode/cyclient/cycode_dev_based_client.py
+++ b/cycode/cyclient/cycode_dev_based_client.py
@@ -1,7 +1,7 @@
from typing import Dict, Optional
-from .config import dev_tenant_id
-from .cycode_client_base import CycodeClientBase
+from cycode.cyclient.config import dev_tenant_id
+from cycode.cyclient.cycode_client_base import CycodeClientBase
"""
Send requests with api token
diff --git a/cycode/cyclient/scan_client.py b/cycode/cyclient/scan_client.py
index 2b62ef62..1318217d 100644
--- a/cycode/cyclient/scan_client.py
+++ b/cycode/cyclient/scan_client.py
@@ -10,7 +10,7 @@
from cycode.cyclient.cycode_client_base import CycodeClientBase
if TYPE_CHECKING:
- from .scan_config_base import ScanConfigBase
+ from cycode.cyclient.scan_config_base import ScanConfigBase
class ScanClient:
diff --git a/pyproject.toml b/pyproject.toml
index 87bdd11f..40e28317 100644
--- a/pyproject.toml
+++ b/pyproject.toml
@@ -113,6 +113,9 @@ docstring-quotes = "double"
multiline-quotes = "double"
inline-quotes = "single"
+[tool.ruff.lint.flake8-tidy-imports]
+ban-relative-imports = "all"
+
[tool.ruff.per-file-ignores]
"tests/*.py" = ["S101", "S105"]
"cycode/*.py" = ["BLE001"]
From ff8016c5292a2535bbda47efb201b82234394fc7 Mon Sep 17 00:00:00 2001
From: Ilya Siamionau
Date: Tue, 23 Jan 2024 14:56:30 +0100
Subject: [PATCH 069/257] CM-31613 - Add contributing guidelines (#202)
---
CONTRIBUTING.md | 164 ++++++++++++++++++++++++++++++++++++++++++++++++
1 file changed, 164 insertions(+)
create mode 100644 CONTRIBUTING.md
diff --git a/CONTRIBUTING.md b/CONTRIBUTING.md
new file mode 100644
index 00000000..a3e324ca
--- /dev/null
+++ b/CONTRIBUTING.md
@@ -0,0 +1,164 @@
+
+
+
+
+## How to contribute to Cycode CLI
+
+The minimum version of Python that we support is 3.7.
+We recommend using this version for local development.
+But it’s fine to use a higher version without using new features from these versions.
+We prefer 3.8 because it comes with the support of Apple Silicon, and it is as low as possible.
+
+The project is under Poetry project management.
+To deal with it, you should install it on your system:
+
+Install Poetry (feel free to use Brew, etc):
+
+```shell
+curl -sSL https://install.python-poetry.org | python - -y
+```
+
+Add Poetry to PATH if required.
+
+Add a plugin to support dynamic versioning from Git Tags:
+
+```shell
+poetry self add "poetry-dynamic-versioning[plugin]"
+```
+
+Install dependencies of the project:
+
+```shell
+poetry install
+```
+
+Check that the version is valid (not 0.0.0):
+
+```shell
+poetry version
+```
+
+You are ready to write code!
+
+To run the project use:
+
+```shell
+poetry run cycode
+```
+
+or main entry point in an activated virtual environment:
+
+```shell
+python cycode/cli/main.py
+```
+
+### Code linting and formatting
+
+We use `ruff` and `ruff format`.
+It is configured well, so you don’t need to do anything.
+You can see all enabled rules in the `pyproject.toml` file.
+Both tests and the main codebase are checked.
+Try to avoid type annotations like `Any`, etc.
+
+GitHub Actions will check that your code is formatted well. You can run it locally:
+
+```shell
+# lint
+poetry run ruff .
+# format
+poetry run ruff format .
+```
+
+Many rules support auto-fixing. You can run it with the `--fix` flag.
+
+### Branching and versioning
+
+We use the `main` branch as the main one.
+All development should be done in feature branches.
+When you are ready create a Pull Request to the `main` branch.
+
+Each commit in the `main` branch will be built and published to PyPI as a pre-release!
+Such builds could be installed with the `--pre` flag. For example:
+
+```shell
+pip install --pre cycode
+```
+
+Also, you can select a specific version of the pre-release:
+
+```shell
+pip install cycode==1.7.2.dev6
+```
+
+We are using [Semantic Versioning](https://semver.org/) and the version is generated automatically from Git Tags. So,
+when you are ready to release a new version, you should create a new Git Tag. The version will be generated from it.
+
+Pre-release versions are generated on distance from the latest Git Tag. For example, if the latest Git Tag is `1.7.2`,
+then the next pre-release version will be `1.7.2.dev1`.
+
+We are using GitHub Releases to create Git Tags with changelogs.
+For changelogs, we are using a standard template
+of [Automatically generated release notes](https://docs.github.com/en/repositories/releasing-projects-on-github/automatically-generated-release-notes).
+
+### Testing
+
+We are using `pytest` for testing. You can run tests with:
+
+```shell
+poetry run pytest
+```
+
+The library used for sending requests is [requests](https://github.com/psf/requests).
+To mock requests, we are using the [responses](https://github.com/getsentry/responses) library.
+All requests must be mocked.
+
+To see the code coverage of the project, you can run:
+
+```shell
+poetry run coverage run -m pytest .
+```
+
+To generate the HTML report, you can run:
+
+```shell
+poetry run coverage html
+```
+
+The report will be generated in the `htmlcov` folder.
+
+### Documentation
+
+Keep [README.md](README.md) up to date.
+All CLI commands are documented automatically if you add a docstring to the command.
+Clean up the changelog before release.
+
+### Publishing
+
+New versions are published automatically on the new GitHub Release.
+It uses the OpenID Connect publishing mechanism to upload on PyPI.
+
+[Homebrew formula](https://formulae.brew.sh/formula/cycode) is updated automatically on the new PyPI release.
+
+The CLI is also distributed as executable files for Linux, macOS, and Windows.
+It is powered by [PyInstaller](https://pyinstaller.org/) and the process is automated by GitHub Actions.
+These executables are attached to GitHub Releases as assets.
+
+To pack the project locally, you should run:
+
+```shell
+poetry build
+```
+
+It will create a `dist` folder with the package (sdist and wheel). You can install it locally:
+
+```shell
+pip install dist/cycode-{version}-py3-none-any.whl
+```
+
+To create an executable file locally, you should run:
+
+```shell
+poetry run pyinstaller pyinstaller.spec
+```
+
+It will create an executable file for **the current platform** in the `dist` folder.
From a672f84ea051d6d1fcd6353524fdce806cae8e6c Mon Sep 17 00:00:00 2001
From: saramontif
Date: Thu, 25 Jan 2024 09:00:30 +0200
Subject: [PATCH 070/257] CM-30564 - Add support for report command in secret
scanning (#203)
* CM-30564-Add support for report command in secret scanning
* CM-30564-formatting
* CM-30564-formatting
* CM-30564-formatting
* CM-30564-formatting
* CM-30564-fix review
* CM-30564-fix
---
cycode/cli/commands/scan/code_scanner.py | 88 ++++++++++++++-----
cycode/cyclient/models.py | 13 +++
cycode/cyclient/scan_client.py | 43 ++++++---
cycode/cyclient/scan_config_base.py | 16 +++-
.../cyclient/mocked_responses/scan_client.py | 15 ++++
.../scan_config/test_default_scan_config.py | 1 +
.../scan_config/test_dev_scan_config.py | 1 +
tests/cyclient/test_scan_client.py | 20 ++++-
tests/test_code_scanner.py | 30 +++++++
9 files changed, 189 insertions(+), 38 deletions(-)
diff --git a/cycode/cli/commands/scan/code_scanner.py b/cycode/cli/commands/scan/code_scanner.py
index 047d0631..78ea8ca9 100644
--- a/cycode/cli/commands/scan/code_scanner.py
+++ b/cycode/cli/commands/scan/code_scanner.py
@@ -1,4 +1,3 @@
-import json
import logging
import os
import sys
@@ -99,6 +98,10 @@ def set_issue_detected_by_scan_results(context: click.Context, scan_results: Lis
set_issue_detected(context, any(scan_result.issue_detected for scan_result in scan_results))
+def _should_use_scan_service(scan_type: str, scan_parameters: Optional[dict] = None) -> bool:
+ return scan_type == consts.SECRET_SCAN_TYPE and scan_parameters is not None and scan_parameters['report'] is True
+
+
def _enrich_scan_result_with_data_from_detection_rules(
cycode_client: 'ScanClient', scan_type: str, scan_result: ZippedFileScanResult
) -> None:
@@ -148,14 +151,21 @@ def _scan_batch_thread_func(batch: List[Document]) -> Tuple[str, CliError, Local
scan_id = str(_generate_unique_id())
scan_completed = False
+ should_use_scan_service = _should_use_scan_service(scan_type, scan_parameters)
try:
logger.debug('Preparing local files, %s', {'batch_size': len(batch)})
zipped_documents = zip_documents(scan_type, batch)
zip_file_size = zipped_documents.size
-
scan_result = perform_scan(
- cycode_client, zipped_documents, scan_type, scan_id, is_git_diff, is_commit_range, scan_parameters
+ cycode_client,
+ zipped_documents,
+ scan_type,
+ scan_id,
+ is_git_diff,
+ is_commit_range,
+ scan_parameters,
+ should_use_scan_service,
)
_enrich_scan_result_with_data_from_detection_rules(cycode_client, scan_type, scan_result)
@@ -194,6 +204,7 @@ def _scan_batch_thread_func(batch: List[Document]) -> Tuple[str, CliError, Local
zip_file_size,
command_scan_type,
error_message,
+ should_use_scan_service,
)
return scan_id, error, local_scan_result
@@ -315,14 +326,13 @@ def scan_commit_range_documents(
local_scan_result = error_message = None
scan_completed = False
scan_id = str(_generate_unique_id())
-
from_commit_zipped_documents = InMemoryZip()
to_commit_zipped_documents = InMemoryZip()
try:
progress_bar.set_section_length(ScanProgressBarSection.SCAN, 1)
- scan_result = init_default_scan_result(scan_id)
+ scan_result = init_default_scan_result(cycode_client, scan_id, scan_type)
if should_scan_documents(from_documents_to_scan, to_documents_to_scan):
logger.debug('Preparing from-commit zip')
from_commit_zipped_documents = zip_documents(scan_type, from_documents_to_scan)
@@ -428,8 +438,9 @@ def perform_scan(
is_git_diff: bool,
is_commit_range: bool,
scan_parameters: dict,
+ should_use_scan_service: bool = False,
) -> ZippedFileScanResult:
- if scan_type in (consts.SCA_SCAN_TYPE, consts.SAST_SCAN_TYPE):
+ if scan_type in (consts.SCA_SCAN_TYPE, consts.SAST_SCAN_TYPE) or should_use_scan_service:
return perform_scan_async(cycode_client, zipped_documents, scan_type, scan_parameters)
if is_commit_range:
@@ -439,12 +450,20 @@ def perform_scan(
def perform_scan_async(
- cycode_client: 'ScanClient', zipped_documents: 'InMemoryZip', scan_type: str, scan_parameters: dict
+ cycode_client: 'ScanClient',
+ zipped_documents: 'InMemoryZip',
+ scan_type: str,
+ scan_parameters: dict,
) -> ZippedFileScanResult:
scan_async_result = cycode_client.zipped_file_scan_async(zipped_documents, scan_type, scan_parameters)
logger.debug('scan request has been triggered successfully, scan id: %s', scan_async_result.scan_id)
- return poll_scan_results(cycode_client, scan_async_result.scan_id, scan_type)
+ return poll_scan_results(
+ cycode_client,
+ scan_async_result.scan_id,
+ scan_type,
+ scan_parameters.get('report'),
+ )
def perform_commit_range_scan_async(
@@ -460,13 +479,16 @@ def perform_commit_range_scan_async(
)
logger.debug('scan request has been triggered successfully, scan id: %s', scan_async_result.scan_id)
- return poll_scan_results(cycode_client, scan_async_result.scan_id, scan_type, timeout)
+ return poll_scan_results(
+ cycode_client, scan_async_result.scan_id, scan_type, scan_parameters.get('report'), timeout
+ )
def poll_scan_results(
cycode_client: 'ScanClient',
scan_id: str,
scan_type: str,
+ should_get_report: bool = False,
polling_timeout: Optional[int] = None,
) -> ZippedFileScanResult:
if polling_timeout is None:
@@ -483,7 +505,7 @@ def poll_scan_results(
print_debug_scan_details(scan_details)
if scan_details.scan_status == consts.SCAN_STATUS_COMPLETED:
- return _get_scan_result(cycode_client, scan_type, scan_id, scan_details)
+ return _get_scan_result(cycode_client, scan_type, scan_id, scan_details, should_get_report)
if scan_details.scan_status == consts.SCAN_STATUS_ERROR:
raise custom_exceptions.ScanAsyncError(
@@ -735,6 +757,7 @@ def _report_scan_status(
zip_size: int,
command_scan_type: str,
error_message: Optional[str],
+ should_use_scan_service: bool = False,
) -> None:
try:
end_scan_time = time.time()
@@ -751,7 +774,7 @@ def _report_scan_status(
'scan_type': scan_type,
}
- cycode_client.report_scan_status(scan_type, scan_id, scan_status)
+ cycode_client.report_scan_status(scan_type, scan_id, scan_status, should_use_scan_service)
except Exception as e:
logger.debug('Failed to report scan status, %s', {'exception_message': str(e)})
@@ -769,37 +792,49 @@ def _does_severity_match_severity_threshold(severity: str, severity_threshold: s
def _get_scan_result(
- cycode_client: 'ScanClient', scan_type: str, scan_id: str, scan_details: 'ScanDetailsResponse'
+ cycode_client: 'ScanClient',
+ scan_type: str,
+ scan_id: str,
+ scan_details: 'ScanDetailsResponse',
+ should_get_report: bool = False,
) -> ZippedFileScanResult:
if not scan_details.detections_count:
- return init_default_scan_result(scan_id, scan_details.metadata)
+ return init_default_scan_result(cycode_client, scan_id, scan_type, should_get_report)
wait_for_detections_creation(cycode_client, scan_type, scan_id, scan_details.detections_count)
scan_detections = cycode_client.get_scan_detections(scan_type, scan_id)
+
return ZippedFileScanResult(
did_detect=True,
detections_per_file=_map_detections_per_file(scan_detections),
scan_id=scan_id,
- report_url=_try_get_report_url(scan_details.metadata),
+ report_url=_try_get_report_url_if_needed(cycode_client, should_get_report, scan_id, scan_type),
)
-def init_default_scan_result(scan_id: str, scan_metadata: Optional[str] = None) -> ZippedFileScanResult:
+def init_default_scan_result(
+ cycode_client: 'ScanClient', scan_id: str, scan_type: str, should_get_report: bool = False
+) -> ZippedFileScanResult:
return ZippedFileScanResult(
- did_detect=False, detections_per_file=[], scan_id=scan_id, report_url=_try_get_report_url(scan_metadata)
+ did_detect=False,
+ detections_per_file=[],
+ scan_id=scan_id,
+ report_url=_try_get_report_url_if_needed(cycode_client, should_get_report, scan_id, scan_type),
)
-def _try_get_report_url(metadata_json: Optional[str]) -> Optional[str]:
- if metadata_json is None:
+def _try_get_report_url_if_needed(
+ cycode_client: 'ScanClient', should_get_report: bool, scan_id: str, scan_type: str
+) -> Optional[str]:
+ if not should_get_report:
return None
try:
- metadata_json = json.loads(metadata_json)
- return metadata_json.get('report_url')
- except json.JSONDecodeError:
- return None
+ report_url_response = cycode_client.get_scan_report_url(scan_id, scan_type)
+ return report_url_response.report_url
+ except Exception as e:
+ logger.debug('Failed to get report url: %s', str(e))
def wait_for_detections_creation(
@@ -856,9 +891,18 @@ def _get_file_name_from_detection(detection: dict) -> str:
if detection['category'] == 'SAST':
return detection['detection_details']['file_path']
+ if detection['category'] == 'SecretDetection':
+ return _get_secret_file_name_from_detection(detection)
+
return detection['detection_details']['file_name']
+def _get_secret_file_name_from_detection(detection: dict) -> str:
+ file_path: str = detection['detection_details']['file_path']
+ file_name: str = detection['detection_details']['file_name']
+ return os.path.join(file_path, file_name)
+
+
def _does_reach_to_max_commits_to_scan_limit(commit_ids: List[str], max_commits_count: Optional[int]) -> bool:
if max_commits_count is None:
return False
diff --git a/cycode/cyclient/models.py b/cycode/cyclient/models.py
index aef9748d..98185707 100644
--- a/cycode/cyclient/models.py
+++ b/cycode/cyclient/models.py
@@ -171,6 +171,19 @@ def __init__(
self.err = err
+@dataclass
+class ScanReportUrlResponse:
+ report_url: str
+
+
+class ScanReportUrlResponseSchema(Schema):
+ report_url = fields.String()
+
+ @post_load
+ def build_dto(self, data: Dict[str, Any], **_) -> 'ScanReportUrlResponse':
+ return ScanReportUrlResponse(**data)
+
+
class ScanDetailsResponseSchema(Schema):
class Meta:
unknown = EXCLUDE
diff --git a/cycode/cyclient/scan_client.py b/cycode/cyclient/scan_client.py
index 1318217d..30f45fd5 100644
--- a/cycode/cyclient/scan_client.py
+++ b/cycode/cyclient/scan_client.py
@@ -30,7 +30,9 @@ def __init__(
self._hide_response_log = hide_response_log
- def get_scan_controller_path(self, scan_type: str) -> str:
+ def get_scan_controller_path(self, scan_type: str, should_use_scan_service: bool = False) -> str:
+ if should_use_scan_service:
+ return self._SCAN_CONTROLLER_PATH
if scan_type == consts.SCA_SCAN_TYPE:
return self._SCAN_CONTROLLER_PATH_SCA
@@ -42,9 +44,9 @@ def get_detections_service_controller_path(self, scan_type: str) -> str:
return self._DETECTIONS_SERVICE_CONTROLLER_PATH
- def get_scan_service_url_path(self, scan_type: str) -> str:
- service_path = self.scan_config.get_service_name(scan_type)
- controller_path = self.get_scan_controller_path(scan_type)
+ def get_scan_service_url_path(self, scan_type: str, should_use_scan_service: bool = False) -> str:
+ service_path = self.scan_config.get_service_name(scan_type, should_use_scan_service)
+ controller_path = self.get_scan_controller_path(scan_type, should_use_scan_service)
return f'{service_path}/{controller_path}'
def content_scan(self, scan_type: str, file_name: str, content: str, is_git_diff: bool = True) -> models.ScanResult:
@@ -72,13 +74,22 @@ def zipped_file_scan(
return self.parse_zipped_file_scan_response(response)
+ def get_scan_report_url(self, scan_id: str, scan_type: str) -> models.ScanReportUrlResponse:
+ response = self.scan_cycode_client.get(url_path=self.get_scan_report_url_path(scan_id, scan_type))
+ return models.ScanReportUrlResponseSchema().build_dto(response.json())
+
def get_zipped_file_scan_async_url_path(self, scan_type: str) -> str:
async_scan_type = self.scan_config.get_async_scan_type(scan_type)
async_entity_type = self.scan_config.get_async_entity_type(scan_type)
- return f'{self.get_scan_service_url_path(scan_type)}/{async_scan_type}/{async_entity_type}'
+ scan_service_url_path = self.get_scan_service_url_path(scan_type, True)
+ return f'{scan_service_url_path}/{async_scan_type}/{async_entity_type}'
def zipped_file_scan_async(
- self, zip_file: InMemoryZip, scan_type: str, scan_parameters: dict, is_git_diff: bool = False
+ self,
+ zip_file: InMemoryZip,
+ scan_type: str,
+ scan_parameters: dict,
+ is_git_diff: bool = False,
) -> models.ScanInitializationResponse:
files = {'file': ('multiple_files_scan.zip', zip_file.read())}
response = self.scan_cycode_client.post(
@@ -109,7 +120,10 @@ def multiple_zipped_file_scan_async(
return models.ScanInitializationResponseSchema().load(response.json())
def get_scan_details_path(self, scan_type: str, scan_id: str) -> str:
- return f'{self.get_scan_service_url_path(scan_type)}/{scan_id}'
+ return f'{self.get_scan_service_url_path(scan_type, should_use_scan_service=True)}/{scan_id}'
+
+ def get_scan_report_url_path(self, scan_id: str, scan_type: str) -> str:
+ return f'{self.get_scan_service_url_path(scan_type, should_use_scan_service=True)}/reportUrl/{scan_id}'
def get_scan_details(self, scan_type: str, scan_id: str) -> models.ScanDetailsResponse:
path = self.get_scan_details_path(scan_type, scan_id)
@@ -222,11 +236,18 @@ def commit_range_zipped_file_scan(
)
return self.parse_zipped_file_scan_response(response)
- def get_report_scan_status_path(self, scan_type: str, scan_id: str) -> str:
- return f'{self.get_scan_service_url_path(scan_type)}/{scan_id}/status'
+ def get_report_scan_status_path(self, scan_type: str, scan_id: str, should_use_scan_service: bool = False) -> str:
+ return f'{self.get_scan_service_url_path(scan_type, should_use_scan_service)}/{scan_id}/status'
- def report_scan_status(self, scan_type: str, scan_id: str, scan_status: dict) -> None:
- self.scan_cycode_client.post(url_path=self.get_report_scan_status_path(scan_type, scan_id), body=scan_status)
+ def report_scan_status(
+ self, scan_type: str, scan_id: str, scan_status: dict, should_use_scan_service: bool = False
+ ) -> None:
+ self.scan_cycode_client.post(
+ url_path=self.get_report_scan_status_path(
+ scan_type, scan_id, should_use_scan_service=should_use_scan_service
+ ),
+ body=scan_status,
+ )
@staticmethod
def parse_scan_response(response: Response) -> models.ScanResult:
diff --git a/cycode/cyclient/scan_config_base.py b/cycode/cyclient/scan_config_base.py
index 347d39ef..1e63673d 100644
--- a/cycode/cyclient/scan_config_base.py
+++ b/cycode/cyclient/scan_config_base.py
@@ -1,9 +1,11 @@
from abc import ABC, abstractmethod
+from cycode.cli import consts
+
class ScanConfigBase(ABC):
@abstractmethod
- def get_service_name(self, scan_type: str) -> str:
+ def get_service_name(self, scan_type: str, should_use_scan_service: bool = False) -> str:
...
@staticmethod
@@ -16,7 +18,9 @@ def get_async_scan_type(scan_type: str) -> str:
return scan_type.upper()
@staticmethod
- def get_async_entity_type(_: str) -> str:
+ def get_async_entity_type(scan_type: str) -> str:
+ if scan_type == consts.SECRET_SCAN_TYPE:
+ return 'ZippedFile'
# we are migrating to "zippedfile" entity type. will be used later
return 'repository'
@@ -26,7 +30,9 @@ def get_detections_prefix(self) -> str:
class DevScanConfig(ScanConfigBase):
- def get_service_name(self, scan_type: str) -> str:
+ def get_service_name(self, scan_type: str, should_use_scan_service: bool = False) -> str:
+ if should_use_scan_service:
+ return '5004'
if scan_type == 'secret':
return '5025'
if scan_type == 'iac':
@@ -40,7 +46,9 @@ def get_detections_prefix(self) -> str:
class DefaultScanConfig(ScanConfigBase):
- def get_service_name(self, scan_type: str) -> str:
+ def get_service_name(self, scan_type: str, should_use_scan_service: bool = False) -> str:
+ if should_use_scan_service:
+ return 'scans'
if scan_type == 'secret':
return 'secret'
if scan_type == 'iac':
diff --git a/tests/cyclient/mocked_responses/scan_client.py b/tests/cyclient/mocked_responses/scan_client.py
index b632dc3b..a3117f55 100644
--- a/tests/cyclient/mocked_responses/scan_client.py
+++ b/tests/cyclient/mocked_responses/scan_client.py
@@ -79,6 +79,20 @@ def get_scan_details_url(scan_id: Optional[UUID], scan_client: ScanClient) -> st
return f'{api_url}/{service_url}'
+def get_scan_report_url(scan_id: Optional[UUID], scan_client: ScanClient, scan_type: str) -> str:
+ api_url = scan_client.scan_cycode_client.api_url
+ service_url = scan_client.get_scan_report_url_path(str(scan_id), scan_type)
+ return f'{api_url}/{service_url}'
+
+
+def get_scan_report_url_response(url: str, scan_id: Optional[UUID] = None) -> responses.Response:
+ if not scan_id:
+ scan_id = uuid4()
+ json_response = {'report_url': f'https://app.domain/on-demand-scans/{scan_id}'}
+
+ return responses.Response(method=responses.GET, url=url, json=json_response, status=200)
+
+
def get_scan_details_response(url: str, scan_id: Optional[UUID] = None) -> responses.Response:
if not scan_id:
scan_id = uuid4()
@@ -182,3 +196,4 @@ def mock_scan_responses(
)
responses_module.add(get_detection_rules_response(get_detection_rules_url(scan_client)))
responses_module.add(get_report_scan_status_response(get_report_scan_status_url(scan_type, scan_id, scan_client)))
+ responses_module.add(get_scan_report_url_response(get_scan_report_url(scan_id, scan_client, scan_type)))
diff --git a/tests/cyclient/scan_config/test_default_scan_config.py b/tests/cyclient/scan_config/test_default_scan_config.py
index 60b87436..e659f71f 100644
--- a/tests/cyclient/scan_config/test_default_scan_config.py
+++ b/tests/cyclient/scan_config/test_default_scan_config.py
@@ -8,6 +8,7 @@ def test_get_service_name() -> None:
assert default_scan_config.get_service_name('iac') == 'iac'
assert default_scan_config.get_service_name('sca') == 'scans'
assert default_scan_config.get_service_name('sast') == 'scans'
+ assert default_scan_config.get_service_name('secret', True) == 'scans'
def test_get_detections_prefix() -> None:
diff --git a/tests/cyclient/scan_config/test_dev_scan_config.py b/tests/cyclient/scan_config/test_dev_scan_config.py
index 4a44ff14..7419b002 100644
--- a/tests/cyclient/scan_config/test_dev_scan_config.py
+++ b/tests/cyclient/scan_config/test_dev_scan_config.py
@@ -8,6 +8,7 @@ def test_get_service_name() -> None:
assert dev_scan_config.get_service_name('iac') == '5026'
assert dev_scan_config.get_service_name('sca') == '5004'
assert dev_scan_config.get_service_name('sast') == '5004'
+ assert dev_scan_config.get_service_name('secret', should_use_scan_service=True) == '5004'
def test_get_detections_prefix() -> None:
diff --git a/tests/cyclient/test_scan_client.py b/tests/cyclient/test_scan_client.py
index 69d657b2..0b92a0bf 100644
--- a/tests/cyclient/test_scan_client.py
+++ b/tests/cyclient/test_scan_client.py
@@ -15,7 +15,12 @@
from cycode.cli.models import Document
from cycode.cyclient.scan_client import ScanClient
from tests.conftest import ZIP_CONTENT_PATH
-from tests.cyclient.mocked_responses.scan_client import get_zipped_file_scan_response, get_zipped_file_scan_url
+from tests.cyclient.mocked_responses.scan_client import (
+ get_scan_report_url,
+ get_scan_report_url_response,
+ get_zipped_file_scan_response,
+ get_zipped_file_scan_url,
+)
def zip_scan_resources(scan_type: str, scan_client: ScanClient) -> Tuple[str, InMemoryZip]:
@@ -60,6 +65,19 @@ def test_zipped_file_scan(scan_type: str, scan_client: ScanClient, api_token_res
assert zipped_file_scan_response.scan_id == str(expected_scan_id)
+@pytest.mark.parametrize('scan_type', config['scans']['supported_scans'])
+@responses.activate
+def test_get_scan_report_url(scan_type: str, scan_client: ScanClient, api_token_response: responses.Response) -> None:
+ scan_id = uuid4()
+ url = get_scan_report_url(scan_id, scan_client, scan_type)
+
+ responses.add(api_token_response) # mock token based client
+ responses.add(get_scan_report_url_response(url, scan_id))
+
+ scan_report_url_response = scan_client.get_scan_report_url(str(scan_id), scan_type)
+ assert scan_report_url_response.report_url == 'https://app.domain/on-demand-scans/{scan_id}'.format(scan_id=scan_id)
+
+
@pytest.mark.parametrize('scan_type', config['scans']['supported_scans'])
@responses.activate
def test_zipped_file_scan_unauthorized_error(
diff --git a/tests/test_code_scanner.py b/tests/test_code_scanner.py
index 6eb494e9..f18e5c02 100644
--- a/tests/test_code_scanner.py
+++ b/tests/test_code_scanner.py
@@ -1,9 +1,39 @@
import os
+from uuid import uuid4
+import pytest
+import responses
+
+from cycode.cli.commands.scan.code_scanner import _try_get_report_url_if_needed
+from cycode.cli.config import config
from cycode.cli.files_collector.excluder import _is_relevant_file_to_scan
+from cycode.cyclient.scan_client import ScanClient
from tests.conftest import TEST_FILES_PATH
+from tests.cyclient.mocked_responses.scan_client import get_scan_report_url, get_scan_report_url_response
def test_is_relevant_file_to_scan_sca() -> None:
path = os.path.join(TEST_FILES_PATH, 'package.json')
assert _is_relevant_file_to_scan('sca', path) is True
+
+
+@pytest.mark.parametrize('scan_type', config['scans']['supported_scans'])
+def test_try_get_report_url_if_needed_return_none(scan_type: str, scan_client: ScanClient) -> None:
+ scan_id = uuid4().hex
+ result = _try_get_report_url_if_needed(scan_client, False, scan_id, 'secret')
+ assert result is None
+
+
+@pytest.mark.parametrize('scan_type', config['scans']['supported_scans'])
+@responses.activate
+def test_try_get_report_url_if_needed_return_result(
+ scan_type: str, scan_client: ScanClient, api_token_response: responses.Response
+) -> None:
+ scan_id = uuid4()
+ url = get_scan_report_url(scan_id, scan_client, scan_type)
+ responses.add(api_token_response) # mock token based client
+ responses.add(get_scan_report_url_response(url, scan_id))
+
+ scan_report_url_response = scan_client.get_scan_report_url(str(scan_id), scan_type)
+ result = _try_get_report_url_if_needed(scan_client, True, str(scan_id), scan_type)
+ assert result == scan_report_url_response.report_url
From 3c217c4c48f0779d43f0afb4ca371fa6794fccf9 Mon Sep 17 00:00:00 2001
From: saramontif
Date: Thu, 25 Jan 2024 14:21:05 +0200
Subject: [PATCH 071/257] CM-30564 - Update README for --report option (#204)
CM-30564-Update readme
---
README.md | 2 +-
1 file changed, 1 insertion(+), 1 deletion(-)
diff --git a/README.md b/README.md
index 301e8944..792b7323 100644
--- a/README.md
+++ b/README.md
@@ -324,7 +324,7 @@ When using this option, the scan results from this scan will appear in the knowl
### Report Option
> [!NOTE]
-> This option is only available to SCA scans.
+> This option is only available to SCA and Secret scans.
To push scan results tied to the [SCA policies](https://docs.cycode.com/docs/sca-policies) found in the Repository scan to Cycode, add the argument `--report` to the scan command.
From df11e477e242843a35effa8b68653197c7e9f4ce Mon Sep 17 00:00:00 2001
From: Ilya Siamionau
Date: Thu, 25 Jan 2024 16:48:30 +0100
Subject: [PATCH 072/257] CM-31729 - Support arrow dependency since the first
stable version (#205)
---
poetry.lock | 23 +++++++++--------------
pyproject.toml | 2 +-
2 files changed, 10 insertions(+), 15 deletions(-)
diff --git a/poetry.lock b/poetry.lock
index 79530954..661b39b7 100644
--- a/poetry.lock
+++ b/poetry.lock
@@ -499,15 +499,20 @@ hook-testing = ["execnet (>=1.5.0)", "psutil", "pytest (>=2.7.3)"]
[[package]]
name = "pyinstaller-hooks-contrib"
-version = "2023.10"
+version = "2024.0"
description = "Community maintained hooks for PyInstaller"
optional = false
python-versions = ">=3.7"
files = [
- {file = "pyinstaller-hooks-contrib-2023.10.tar.gz", hash = "sha256:4b4a998036abb713774cb26534ca06b7e6e09e4c628196017a10deb11a48747f"},
- {file = "pyinstaller_hooks_contrib-2023.10-py2.py3-none-any.whl", hash = "sha256:6dc1786a8f452941245d5bb85893e2a33632ebdcbc4c23eea41f2ee08281b0c0"},
+ {file = "pyinstaller-hooks-contrib-2024.0.tar.gz", hash = "sha256:a7118c1a5c9788595e5c43ad058a7a5b7b6d59e1eceb42362f6ec1f0b61986b0"},
+ {file = "pyinstaller_hooks_contrib-2024.0-py2.py3-none-any.whl", hash = "sha256:469b5690df53223e2e8abffb2e44d6ee596e7d79d4b1eed9465123b67439875a"},
]
+[package.dependencies]
+importlib-metadata = {version = ">=4.6", markers = "python_version < \"3.10\""}
+packaging = ">=22.0"
+setuptools = ">=42.0.0"
+
[[package]]
name = "pytest"
version = "7.3.2"
@@ -585,7 +590,6 @@ files = [
{file = "PyYAML-6.0.1-cp310-cp310-manylinux_2_17_aarch64.manylinux2014_aarch64.whl", hash = "sha256:69b023b2b4daa7548bcfbd4aa3da05b3a74b772db9e23b982788168117739938"},
{file = "PyYAML-6.0.1-cp310-cp310-manylinux_2_17_s390x.manylinux2014_s390x.whl", hash = "sha256:81e0b275a9ecc9c0c0c07b4b90ba548307583c125f54d5b6946cfee6360c733d"},
{file = "PyYAML-6.0.1-cp310-cp310-manylinux_2_17_x86_64.manylinux2014_x86_64.whl", hash = "sha256:ba336e390cd8e4d1739f42dfe9bb83a3cc2e80f567d8805e11b46f4a943f5515"},
- {file = "PyYAML-6.0.1-cp310-cp310-musllinux_1_1_x86_64.whl", hash = "sha256:326c013efe8048858a6d312ddd31d56e468118ad4cdeda36c719bf5bb6192290"},
{file = "PyYAML-6.0.1-cp310-cp310-win32.whl", hash = "sha256:bd4af7373a854424dabd882decdc5579653d7868b8fb26dc7d0e99f823aa5924"},
{file = "PyYAML-6.0.1-cp310-cp310-win_amd64.whl", hash = "sha256:fd1592b3fdf65fff2ad0004b5e363300ef59ced41c2e6b3a99d4089fa8c5435d"},
{file = "PyYAML-6.0.1-cp311-cp311-macosx_10_9_x86_64.whl", hash = "sha256:6965a7bc3cf88e5a1c3bd2e0b5c22f8d677dc88a455344035f03399034eb3007"},
@@ -593,15 +597,8 @@ files = [
{file = "PyYAML-6.0.1-cp311-cp311-manylinux_2_17_aarch64.manylinux2014_aarch64.whl", hash = "sha256:42f8152b8dbc4fe7d96729ec2b99c7097d656dc1213a3229ca5383f973a5ed6d"},
{file = "PyYAML-6.0.1-cp311-cp311-manylinux_2_17_s390x.manylinux2014_s390x.whl", hash = "sha256:062582fca9fabdd2c8b54a3ef1c978d786e0f6b3a1510e0ac93ef59e0ddae2bc"},
{file = "PyYAML-6.0.1-cp311-cp311-manylinux_2_17_x86_64.manylinux2014_x86_64.whl", hash = "sha256:d2b04aac4d386b172d5b9692e2d2da8de7bfb6c387fa4f801fbf6fb2e6ba4673"},
- {file = "PyYAML-6.0.1-cp311-cp311-musllinux_1_1_x86_64.whl", hash = "sha256:e7d73685e87afe9f3b36c799222440d6cf362062f78be1013661b00c5c6f678b"},
{file = "PyYAML-6.0.1-cp311-cp311-win32.whl", hash = "sha256:1635fd110e8d85d55237ab316b5b011de701ea0f29d07611174a1b42f1444741"},
{file = "PyYAML-6.0.1-cp311-cp311-win_amd64.whl", hash = "sha256:bf07ee2fef7014951eeb99f56f39c9bb4af143d8aa3c21b1677805985307da34"},
- {file = "PyYAML-6.0.1-cp312-cp312-macosx_10_9_x86_64.whl", hash = "sha256:855fb52b0dc35af121542a76b9a84f8d1cd886ea97c84703eaa6d88e37a2ad28"},
- {file = "PyYAML-6.0.1-cp312-cp312-macosx_11_0_arm64.whl", hash = "sha256:40df9b996c2b73138957fe23a16a4f0ba614f4c0efce1e9406a184b6d07fa3a9"},
- {file = "PyYAML-6.0.1-cp312-cp312-manylinux_2_17_x86_64.manylinux2014_x86_64.whl", hash = "sha256:6c22bec3fbe2524cde73d7ada88f6566758a8f7227bfbf93a408a9d86bcc12a0"},
- {file = "PyYAML-6.0.1-cp312-cp312-musllinux_1_1_x86_64.whl", hash = "sha256:8d4e9c88387b0f5c7d5f281e55304de64cf7f9c0021a3525bd3b1c542da3b0e4"},
- {file = "PyYAML-6.0.1-cp312-cp312-win32.whl", hash = "sha256:d483d2cdf104e7c9fa60c544d92981f12ad66a457afae824d146093b8c294c54"},
- {file = "PyYAML-6.0.1-cp312-cp312-win_amd64.whl", hash = "sha256:0d3304d8c0adc42be59c5f8a4d9e3d7379e6955ad754aa9d6ab7a398b59dd1df"},
{file = "PyYAML-6.0.1-cp36-cp36m-macosx_10_9_x86_64.whl", hash = "sha256:50550eb667afee136e9a77d6dc71ae76a44df8b3e51e41b77f6de2932bfe0f47"},
{file = "PyYAML-6.0.1-cp36-cp36m-manylinux_2_17_aarch64.manylinux2014_aarch64.whl", hash = "sha256:1fe35611261b29bd1de0070f0b2f47cb6ff71fa6595c077e42bd0c419fa27b98"},
{file = "PyYAML-6.0.1-cp36-cp36m-manylinux_2_17_s390x.manylinux2014_s390x.whl", hash = "sha256:704219a11b772aea0d8ecd7058d0082713c3562b4e271b849ad7dc4a5c90c13c"},
@@ -618,7 +615,6 @@ files = [
{file = "PyYAML-6.0.1-cp38-cp38-manylinux_2_17_aarch64.manylinux2014_aarch64.whl", hash = "sha256:a0cd17c15d3bb3fa06978b4e8958dcdc6e0174ccea823003a106c7d4d7899ac5"},
{file = "PyYAML-6.0.1-cp38-cp38-manylinux_2_17_s390x.manylinux2014_s390x.whl", hash = "sha256:28c119d996beec18c05208a8bd78cbe4007878c6dd15091efb73a30e90539696"},
{file = "PyYAML-6.0.1-cp38-cp38-manylinux_2_17_x86_64.manylinux2014_x86_64.whl", hash = "sha256:7e07cbde391ba96ab58e532ff4803f79c4129397514e1413a7dc761ccd755735"},
- {file = "PyYAML-6.0.1-cp38-cp38-musllinux_1_1_x86_64.whl", hash = "sha256:49a183be227561de579b4a36efbb21b3eab9651dd81b1858589f796549873dd6"},
{file = "PyYAML-6.0.1-cp38-cp38-win32.whl", hash = "sha256:184c5108a2aca3c5b3d3bf9395d50893a7ab82a38004c8f61c258d4428e80206"},
{file = "PyYAML-6.0.1-cp38-cp38-win_amd64.whl", hash = "sha256:1e2722cc9fbb45d9b87631ac70924c11d3a401b2d7f410cc0e3bbf249f2dca62"},
{file = "PyYAML-6.0.1-cp39-cp39-macosx_10_9_x86_64.whl", hash = "sha256:9eb6caa9a297fc2c2fb8862bc5370d0303ddba53ba97e71f08023b6cd73d16a8"},
@@ -626,7 +622,6 @@ files = [
{file = "PyYAML-6.0.1-cp39-cp39-manylinux_2_17_aarch64.manylinux2014_aarch64.whl", hash = "sha256:5773183b6446b2c99bb77e77595dd486303b4faab2b086e7b17bc6bef28865f6"},
{file = "PyYAML-6.0.1-cp39-cp39-manylinux_2_17_s390x.manylinux2014_s390x.whl", hash = "sha256:b786eecbdf8499b9ca1d697215862083bd6d2a99965554781d0d8d1ad31e13a0"},
{file = "PyYAML-6.0.1-cp39-cp39-manylinux_2_17_x86_64.manylinux2014_x86_64.whl", hash = "sha256:bc1bf2925a1ecd43da378f4db9e4f799775d6367bdb94671027b73b393a7c42c"},
- {file = "PyYAML-6.0.1-cp39-cp39-musllinux_1_1_x86_64.whl", hash = "sha256:04ac92ad1925b2cff1db0cfebffb6ffc43457495c9b3c39d3fcae417d7125dc5"},
{file = "PyYAML-6.0.1-cp39-cp39-win32.whl", hash = "sha256:faca3bdcf85b2fc05d06ff3fbc1f83e1391b3e724afa3feba7d13eeab355484c"},
{file = "PyYAML-6.0.1-cp39-cp39-win_amd64.whl", hash = "sha256:510c9deebc5c0225e8c96813043e62b680ba2f9c50a08d3724c7f28a747d1486"},
{file = "PyYAML-6.0.1.tar.gz", hash = "sha256:bfdf460b1736c775f2ba9f6a92bca30bc2095067b8a9d77876d1fad6cc3b4a43"},
@@ -816,4 +811,4 @@ testing = ["big-O", "flake8 (<5)", "jaraco.functools", "jaraco.itertools", "more
[metadata]
lock-version = "2.0"
python-versions = ">=3.7,<3.13"
-content-hash = "9cefba1b9ec5491f9578c4b142c62535e9d551aebb7dade52fd4920d9ad6bcd6"
+content-hash = "fcbb52402ab9e081fbc204e4224e1bc0ec4466ea10f27597cb6259d60b473229"
diff --git a/pyproject.toml b/pyproject.toml
index 40e28317..8e76e284 100644
--- a/pyproject.toml
+++ b/pyproject.toml
@@ -34,7 +34,7 @@ pyyaml = ">=6.0,<7.0"
marshmallow = ">=3.15.0,<3.21.0"
pathspec = ">=0.11.1,<0.12.0"
gitpython = ">=3.1.30,<3.2.0"
-arrow = ">=0.17.0,<1.3.0"
+arrow = ">=1.0.0,<1.3.0"
binaryornot = ">=0.4.4,<0.5.0"
texttable = ">=1.6.7,<1.8.0"
requests = ">=2.24,<3.0"
From 0d6cbac53d460f951426ea78b29ced9ad0b5e6f5 Mon Sep 17 00:00:00 2001
From: saramontif
Date: Thu, 25 Jan 2024 18:07:13 +0200
Subject: [PATCH 073/257] CM-30564 - Print report URLs at the end of the table
instead of the column (#207)
* CM-30564-Change report table printer
* CM-30564-Change report table printer
* CM-30564-fix
---
cycode/cli/printers/tables/sca_table_printer.py | 10 ----------
cycode/cli/printers/tables/table_printer.py | 7 +------
cycode/cli/printers/tables/table_printer_base.py | 10 ++++++++++
3 files changed, 11 insertions(+), 16 deletions(-)
diff --git a/cycode/cli/printers/tables/sca_table_printer.py b/cycode/cli/printers/tables/sca_table_printer.py
index 702a7514..268f8614 100644
--- a/cycode/cli/printers/tables/sca_table_printer.py
+++ b/cycode/cli/printers/tables/sca_table_printer.py
@@ -160,16 +160,6 @@ def _enrich_table_with_values(table: Table, detection: Detection) -> None:
table.set(CVE_COLUMNS, detection_details.get('vulnerability_id'))
table.set(LICENSE_COLUMN, detection_details.get('license'))
- @staticmethod
- def _print_report_urls(local_scan_results: List['LocalScanResult']) -> None:
- report_urls = [scan_result.report_url for scan_result in local_scan_results if scan_result.report_url]
- if not report_urls:
- return
-
- click.echo('Report URLs:')
- for report_url in report_urls:
- click.echo(f'- {report_url}')
-
@staticmethod
def _print_summary_issues(detections_count: int, title: str) -> None:
click.echo(f'⛔ Found {detections_count} issues of type: {click.style(title, bold=True)}')
diff --git a/cycode/cli/printers/tables/table_printer.py b/cycode/cli/printers/tables/table_printer.py
index 2aa2ca4e..6afd9e66 100644
--- a/cycode/cli/printers/tables/table_printer.py
+++ b/cycode/cli/printers/tables/table_printer.py
@@ -25,7 +25,6 @@
VIOLATION_LENGTH_COLUMN = column_builder.build(name='Violation Length')
VIOLATION_COLUMN = column_builder.build(name='Violation')
SCAN_ID_COLUMN = column_builder.build(name='Scan ID')
-REPORT_URL_COLUMN = column_builder.build(name='Report URL')
COLUMN_WIDTHS_CONFIG: ColumnWidthsConfig = {
SECRET_SCAN_TYPE: {
@@ -59,13 +58,12 @@ def _print_results(self, local_scan_results: List['LocalScanResult']) -> None:
for local_scan_result in local_scan_results:
for document_detections in local_scan_result.document_detections:
- report_url = local_scan_result.report_url if local_scan_result.report_url else 'N/A'
for detection in document_detections.detections:
- table.set(REPORT_URL_COLUMN, report_url)
table.set(SCAN_ID_COLUMN, local_scan_result.scan_id)
self._enrich_table_with_values(table, detection, document_detections.document)
self._print_table(table)
+ self._print_report_urls(local_scan_results)
def _get_table(self) -> Table:
table = Table()
@@ -85,9 +83,6 @@ def _get_table(self) -> Table:
table.add(VIOLATION_LENGTH_COLUMN)
table.add(VIOLATION_COLUMN)
- if self.context.obj.get('report'):
- table.add(REPORT_URL_COLUMN)
-
return table
def _enrich_table_with_values(self, table: Table, detection: Detection, document: Document) -> None:
diff --git a/cycode/cli/printers/tables/table_printer_base.py b/cycode/cli/printers/tables/table_printer_base.py
index 10a94e55..9b6e8ac7 100644
--- a/cycode/cli/printers/tables/table_printer_base.py
+++ b/cycode/cli/printers/tables/table_printer_base.py
@@ -56,3 +56,13 @@ def _print_results(self, local_scan_results: List['LocalScanResult']) -> None:
def _print_table(table: 'Table') -> None:
if table.get_rows():
click.echo(table.get_table().draw())
+
+ @staticmethod
+ def _print_report_urls(local_scan_results: List['LocalScanResult']) -> None:
+ report_urls = [scan_result.report_url for scan_result in local_scan_results if scan_result.report_url]
+ if not report_urls:
+ return
+
+ click.echo('Report URLs:')
+ for report_url in report_urls:
+ click.echo(f'- {report_url}')
From 9465e88a339eda2292f1be0ebddac3635b85fe59 Mon Sep 17 00:00:00 2001
From: anna-aleksandrowicz
<135120640+anna-aleksandrowicz@users.noreply.github.com>
Date: Thu, 25 Jan 2024 18:36:51 +0200
Subject: [PATCH 074/257] Updated report examples and replaced the full example
with an image in the README (#206)
Co-authored-by: Ilya Siamionau
---
README.md | 43 ++++----------------------------------
images/sca_report_url.png | Bin 0 -> 205022 bytes
2 files changed, 4 insertions(+), 39 deletions(-)
create mode 100644 images/sca_report_url.png
diff --git a/README.md b/README.md
index 792b7323..bf205c58 100644
--- a/README.md
+++ b/README.md
@@ -329,56 +329,21 @@ When using this option, the scan results from this scan will appear in the knowl
To push scan results tied to the [SCA policies](https://docs.cycode.com/docs/sca-policies) found in the Repository scan to Cycode, add the argument `--report` to the scan command.
`cycode scan -t sca --report repository ~/home/git/codebase`
+`cycode scan -t secret --report repository ~/home/git/codebase`
+
or:
`cycode scan --scan-type sca --report repository ~/home/git/codebase`
+`cycode scan --scan-type secret --report repository ~/home/git/codebase`
When using this option, the scan results from this scan will appear in the On-Demand Scans section of Cycode. To get to this page, click the link that appears after the printed results:
> :warning: **NOTE**
> You must be an `owner` or an `admin` in Cycode to view this page.
-```bash
-Scan Results: (scan_id: e04e06e5-6dd8-474f-b409-33bbee67270b)
-⛔ Found issue of type: Security vulnerability in package 'vyper' referenced in project '': Multiple evaluation of contract address in call in vyper (rule ID: d003b23a-a2eb-42f3-83c9-7a84505603e5) in file: ./requirements.txt ⛔
-
-1 | PyYAML~=5.3.1
-2 | vyper==0.3.1
-3 | cleo==1.0.0a5
-
-⛔ Found issue of type: Security vulnerability in package 'vyper' referenced in project '': Integer bounds error in Vyper (rule ID: d003b23a-a2eb-42f3-83c9-7a84505603e5) in file: ./requirements.txt ⛔
-
-1 | PyYAML~=5.3.1
-2 | vyper==0.3.1
-3 | cleo==1.0.0a5
-
-⛔ Found issue of type: Security vulnerability in package 'pyyaml' referenced in project '': Improper Input Validation in PyYAML (rule ID: d003b23a-a2eb-42f3-83c9-7a84505603e5) in file: ./requirements.txt ⛔
-
-1 | PyYAML~=5.3.1
-2 | vyper==0.3.1
-3 | cleo==1.0.0a5
+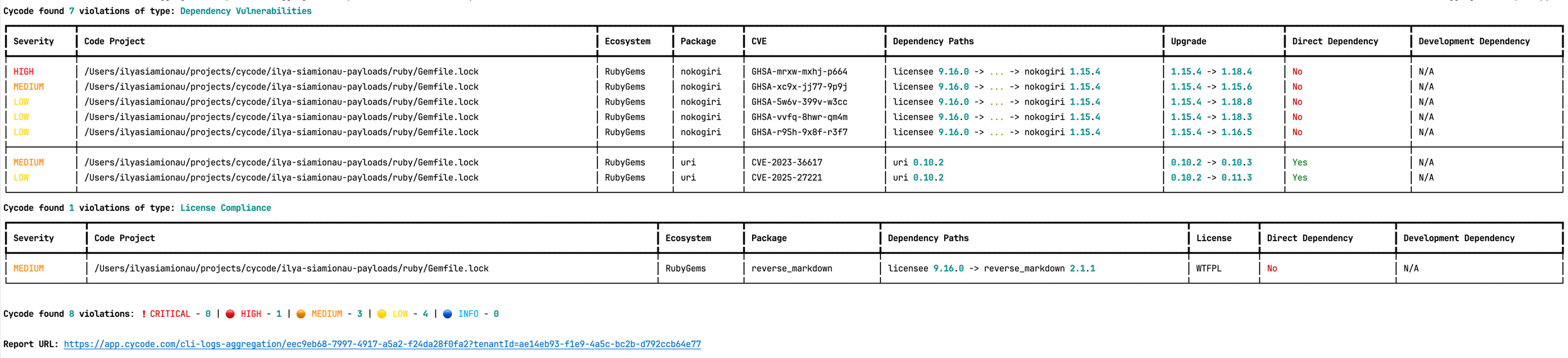
-⛔ Found issue of type: Security vulnerability in package 'cleo' referenced in project '': cleo is vulnerable to Regular Expression Denial of Service (ReDoS) (rule ID: d003b23a-a2eb-42f3-83c9-7a84505603e5) in file: ./requirements.txt ⛔
-
-2 | vyper==0.3.1
-3 | cleo==1.0.0a5
-4 |
-
-⛔ Found issue of type: Security vulnerability in package 'vyper' referenced in project '': Incorrect Comparison in Vyper (rule ID: d003b23a-a2eb-42f3-83c9-7a84505603e5) in file: ./requirements.txt ⛔
-
-1 | PyYAML~=5.3.1
-2 | vyper==0.3.1
-3 | cleo==1.0.0a5
-
-⛔ Found issue of type: Security vulnerability in package 'vyper' referenced in project '': Buffer Overflow in vyper (rule ID: d003b23a-a2eb-42f3-83c9-7a84505603e5) in file: ./requirements.txt ⛔
-
-1 | PyYAML~=5.3.1
-2 | vyper==0.3.1
-3 | cleo==1.0.0a5
-
-Report URL: https://app.cycode.com/on-demand-scans/617ecc3d-9ff2-493e-8be8-2c1fecaf6939
-```
The report page will look something like below:
diff --git a/images/sca_report_url.png b/images/sca_report_url.png
new file mode 100644
index 0000000000000000000000000000000000000000..f438180ec80aa9f8f44c6588b15d7256467fcf42
GIT binary patch
literal 205022
zcmeFZcT`i`);11^(vBdYAfkZMR7#{sZ=!-Use;rXy@T{31Z-I7NbkLal+YnqkP?d2
z&_XXl2uKMrqMNyLa_8?%w6m^Y(ObcC)9TcOf8N%%n9M>%sE@Mb0@;h0DE}g4Ri#9(#7-N%^@O=awSJGG*W^W0#e`I2}gmK7Pab`5ncg
zhH&yNW{LzUn-cq4)_57dfR}^6E^~1|S>=!^Dk}0hr?yWO`c*yrr|+|10@G6#GMj|e
z<-~5y^9S3e4%E9t@NV4K7>+!y1^a{WMeCVd}Dvgo5hE<5aF|LrFZowgX~X
zGC3w6SVS8IpQbJUYSDNS?~~d6o;GzQ>Vw`w5Vv%#<#l>y#PC{3%g_eqe2${XO60+Q
z>T*Y##*_Kw`ucU$#y-b^m_+_p=+ovMt^=hd8_1pF3Yiq1+Yh#fbucWm5_PKGArkQn
zvM}ifgtLjJN_TwzAcV8$MtI$ej5yatksVG)6|OEI?RXqR)#Uq${whf9M&dV>)+jC8
z{b>OPXEp~mV+w8T_I6TWKtM73)gVH<`(18|7;fh8nN4ES6kY@|3IpY-!~HmaN$SPX
zi{^X-=}?^})-H-`aa2aR)Z^i7-)X*eQB6_MEK(_iGtu7Liaw)7$;lTX$wNKO!&G_d
zRqjQ%)AB0(Qw)sZyo(oQD9yS!yqGO0rB$SVoMP(Yxkw56B=d`+n1}ZB9lJMFH|}i3
zG1^g^s`&QO?S~U`&t1Rt?gh(LCBEnTxfne$Bl<_G_&l>8CO;&7nOo0bRIs^Mo&E@B
z2z{-8i>~-{`A1PV`mrZxwizNnX)WFhl+9#d?=oMcZ$6_$Fa3pmiPMW)ffn{sP>+H?
zB0=3bH%j041Lw_i7hY(p(CJs`-!JtxI$KUT@p|hXQtfQMRi08_trLCvYbiDP+>VhY
zC#hiB;M>6xtt_F`$fzBa1vRF;o{@!Hc2V@-Xl-Mk*yP`Oo9d>0wfM3R?byqfsLd}?
z)=Jj3kAo_?CfQKY(cc7YO>CrX18g~K**_{yJ=vyaj5Perv2^)qgbbS~tI3<$SMu-V
zV^Q7Fi%QGhhT;
zT8n+WaAKzzZS;rvzI#Xj_wVEG%O<4f)q3}Wa195)Y1XsQaz6|~l
zey|pEp>N?u1Fa(OqW+?Xn#hD;ex10zMQjhf`@1SJtg9>uG7IP3mXdh
z=r|a$304T9uEOI*;uLv8H2hPa=R4`oU3cpb?!VJ--%oo%Yob8BtZ&?AOU#Ac&*Gu+
zkfx}rsCu>LPUT##f~J*8_KlpI;A;@oPB5wdc{$bHh>DLId3W+mo)|oh$bWy$r1n9r
zey#3aJ&R7?-5d9vGYsC3^4d4l<#~VfZrtZugZJ04>9NZQTZ68fdD(mlz3{kOkN=*1
zQ9or;#!c38mvXCestL>T6eDn1UqwqPe??MRmLaEMNvV9
zo7>}?<7wj)W6|Tt(%F3Z@{-b?ari_9BBWGzGGG#14K9H6P`Ii{KMtu5|w(UAke$&}Wc@hfdLqan3jYC)Q9`v*@4tS6WePxxA!;S%O~4u>B4U(S0#H^MpZT&hg9yE8CDXj
zq|KVlA<$YV^Ni$F)U?a&w`t>9#_wf^JjV{lkL07WDv+1jB>Z!>-M1ysx>Mve>+QH@
zy^UL~4?LLzMn2vD5|bVy+(V3c@ldivrX=*?i=j(H!W)-1N<_^>FQ?oU9p*R_W%o`0
zo2!Y0NuFyWsxYHt_GS~q&h-Eg_8L}{$u!n0Rx`FIJ3aetHYR(;YSK!mLp0E~J+z}K
zi0Rg&G&ctkpShk%$0XfIP@nX8(#?c5h*ad`m?zoclWqEmc~?>?!Wk
zo2NyXjzunVUOsPefgt=anc{WBj->GJ-;Gu4NPOFru#|(7SoVnyjaINXnpuLpA?Lh=Y
zirliiv1`uK=$kb4VSD-=vVUO)HW)M;Z;&=RH@bu-&1S%z?C;y}1_;kSt(q%;w)=4T
z;mFV@df2;3%bB*uonwPEqiK^hvx&!51|4O=-qMZ%yId)XXG0!g*>;KTu}!->VKv0T
z+pV|PXg<=^F)GMkeERW#{TKv|{J?a9`#3li68Q5$Z+wi|?97Z@QfoqRvz3vuzvPh<
zRt#%fb@tm?Jm(tc``8yN`75BXXgrksa`){~;$h<165of9r1jI^rRS|*7+ew25P4BG
zQl$upZc~$N!)>C&{_K*(CCBoi{wxt$bp;cz9XxLCfR&w^-O5tCU1qMclK82pR4YL4
zxqPcA-l{XW`v6dbY8$wU7?WX(dYJ#Q95EPvHiL6ey2?|E=s^rIOwlnp5ScZvLi!`!
z72gLBVdSt@?dULk|CRMD&QQuwMdA`MfX0UA%&zxN%)C|yc0Fv8SVrT@ZNtT;m=I<}
zdc5{@koARN^b4sMj*)Yb9!h6JkF8S`3Hz~8%AHZ?6?m0}Al0OH|8bkcfz*x1*!SHa
zH7k0nhaEQwhU>#yh~pYv;@Uo9aIbVPUi!22!h%Ow$>Gk=kP0lC^$u&Sa$#s{y6|!7
z;a;!cammndd`^z8J>*kp*)Nx$P;|y_Q{=)}Cxrdu%gQu;idVuiS1H4rA}M*)PpNF4
z32zScFV1FmI#RZN-33{mZV6Fyqj2(~*p
z><&~aiMaH_J}+~s+>lu6ORUFtDckwSkn?sRE<7>E(nQeQA7@gt;X8W(etl>ESi?a_
zhvFu1PD?>ed5PjQa7GDyl_)v?>s*cUI>o6!uTxP_L^@MY|MQuL!13f02YgS;{Ns2k
z;WY&f@D~g44a}wb>uCmy+*5y@pBe}5QQR@StDylL4Q;*c?LB;)JbeR*Z1;c*bY2fk
zeJCi{_)or+8U}nnf%hYvjUM|x*3p);^>i0~V&`dNFB<6Xb@Cnxg+Mvr)ZO0q2~VKA
zn}?5FpyIVZpO6F2PcDP5@%;ISudCv<$2xjEcRjuBd89;diQc-VM9;&+qu_1lAZKt-
z?VrVgzZ9=I`TBavfj|KP0ippCqMqK4ATe24Sug^c)X&>nPubMo3{@E>{gP@Z;ATiNf
zp#OR|P*maMs+^v4puL;vJ!f}d%z!$SWMytC{Q3O<@6Nw!{BI>6|Er|9>@Au9Ui81+
z`u`Sv#cJiUz0)DRl;|QEnCO3ZOh4fKSs8DF!yJHkcxs9YF7#oth_6}V2
zS*BlU@}IGd`r~ZfA1r5V({3fh+*8GDInLPLQgz@}W9_?@TzA2i+tjQ#q3V2+{Y{qm
zhPOv+gkkKu#m4-G(rgD7TbVP4+H4s{4z=w1?6hEm!WK3Z&d%`NSEZn&KBw{@|MZ@7
z;#rjY@{)s=C!B)nKm7?8ROz~Xmh$h_d`+dxkL{uZ@877Gf{NN=?9AWjt_nqjFi_Sp
z;)&FM+}V@i0lMq{ACK{$v(o#&-Ti&}`rq08J=q3?`7Kp7blUlaRn_6vBh3tUoph;3
zt$A-se5DAY(SYmJG$r
zzokARWT@`bSZKvTt@fd2N{)?YB%CkQX2;Q`yIt05eh{(n;5O3BaKh%`VL47Mqg(*x
zkxLsLZ7AZ#%I`IDpS>*N6is=f`)qmJZl^iA13Rx@A;$EV0x6}9=zh;$fo@u`8cY@Y
zBBUG3r8xd`>5Gw%hu5|fX0T$ov^!C-l+B@VshHEv
zhN@yVHLp6!j5v4=8vN-p)E8$nkq^f{LLo!SG1%?A^v3y*PQCHG>gB-jv@D|i=Yt&m
z){;!v+QURDWgG@BPBeLfclD}aq+lp!(p-Axi6ZfEY^!nB;{Zz@%OM$M1+Ax%P~Wms
z<^0NL95UPqZiSsavD~{bhy0_{$slm`>pwX1zeRIy&{Vgm6Mq!Mwt@_^tZHpuHNlD<
z&O_85>n2IrI#w71s5ltYp9+$gX>cw$ns(%#s4|y^q8n$+p_67p-ii+E>@r)W1%xF3
z8D~L1%!CQPChd*j&q3*hQZgP!K9JrSEqV`$K5~>}?YR<=nGmL9(B_XG*O5l93X6mp
zRKE>9KJ05*+6}|XV-j-+d>e9@&hLuS{!>qAFexwsKXYI1ofqR}CE1szdholjnoexT
z?&5Nhklb4fogWcOZIwX>>;83%8+ufuNHD=B2NbT|@3qz>~`_95_~Vd%~)dqalw%747R>Fkd`e
zR=@{nxw(9F-HhLaQ~$ca@&Nh$doEYd
zDzo2eygFN*`Q%gTRg0%EnU7==UI>@KdZVQakcVQ2;cPVeL1%8QT_4MZ3x#s7lfqEk
zdIp|@D`dOY<;V9t5=w@3zxz5)+^AYI@aLk6USPE!$}jCuM5>QnK`oZc9sDgg8PwCK
z_&!4kx5^6YozFr%#+W#fJWRI_+05ORzyU=aVSvc^>wg;7*ayk58sGapv!%%sC%qV4
zH0tt6;_i4#6R;}WI*ZKOdPd6aH_%3j$yG@%qt>dWIv1fFn`Q}C9WFX5m2~T)LTnZG
z5+xP<1zaXz$SqU%z=2Jd0@fk@L8GzfjPSF~$@FSpJ1kURx*i*3}o)b=!GH`-a530=gz+mkAeW@PuZOv9NRm
zqC)$Y{|mE@ZBFRwg#K0q!peX%%Qt!E*VhB>@0frB8V7kVVBVI$zI6eX`aq)#a>#Qa
z9F<}ftby5{HWaaJ9Y09Q<;0l=%8z==QdOfG^HGE@ehQQ4c
zyJMA(OXZG#6c82X{Ab;_1|)_L!Lx6*KpjRz;x42KG|}KZX0$PsMMOLmm=D^x0;tf1
zu3`y?0X<-eO^8p)EHCh88o*!Ce|FDq{tm
z3p9itDbZBCW~*v%cA2Q0PFHa~n6rLf#hG5o0X54Ae-Lz?)fau*sz&k?g5^y|aFN;Z
zq|jDIz=FQHWk`uj$K9rOYif%PeuHQZuh2gJlu|&q3<-UWSLZ6*Y1!bK_!?!`IV6V)
zJfLkJ0xMU>$8@naFl`y9UDA_itoWhu^Xbl+Oq8!#&xv-1F~q=Yl-Oe
z#}^LQbR4D6*v2XnkmtP6hIUzAs3$q0NBRZou|usMwxH_)L}oAK)a?P%Z&~r&bn3b@
z7VzHjocVF{sz4$?bdn2S_S(4W(ThKVL?|Z*wZoxwbskQ20*f>EmaApg0iu%HqDCqL
zA<#R+&}rpdY`@uW@6v5<`@scq2MYTYJmJ=%GwGJNMwUEPtsZl^j0-||dfQ`81~a10
zUA7A$<7>kog^B5rdG
z=>6)4vTNr7OYAy5A(6e}k<&nIJ`GrY$MLwUciU~_jsSpz4=#v>zv*OYND=B5fmDaG
zwFwX5HrAKUSmZqY#<6uY>lwgaqC|{^5bj2EE6*?NqH18(#oB4h9Xpd%88g6ABHH`s
z12$#cmVEfER+iee$SwUmxA-_018tBfh?BUjg&_?N3gCWU%@V?X
zx!v(b!R&7P!O;Ah_2tnzdo9?MIDKc7fQb8@1mQ&H;xA~`WDTOG;%vj-H_i%9&-Rf{
z?ZfReWooAl;UM+iQliuq2x0HU{$Q;%vmS()H#o&(&31%Vm9AzM!cuR$CQG;7jbz*c
zL2z1u7k2$J!;xP2*jdtYV@|DYPdS8ikVD!d0R6eWaNxR*xwGH>4zORrSg-y23>-J+
zpoh}ptfT9|ynA5A4Ry;j5(RE>phHkqO-DPFOp1qkyIi-*$-cAiSNDKnJUs*{TgV}-
z3R=xuw)#G;KP*Oue2IFsFcjyl0ZRgPm%*BGaN@e`Mked^(Ys8FtFrytxL0%`!yJ$M
z+Pz{0JxEKT-`th!xMgDt=U2@LK(9g&UYqPvb6$6MJ5Nj>c8EMEH7lGcQuA9%fg)m?
zO5plc@xc(Bv*KQtXz&(J88Jro9!l>4508!2D1wKZNvet~+>q}Q$3%U|DB1hq*H}|5
zyd!8{ygsH<-m)*60N}&XM0op!~h4uRfA7z0+-HcplZz%t?k~2P@>TMGp
z{je!1!=v>^-L|-d2Cjam;mv7{A!TV!S!K75jBwWg{Q~WbTq9*=z(a66SUU?77T`fF
z%u|2GAADgQ-F2($6PRxuRZeC0AU>KSeWBJy0ag}=_l4U~K``w>2L$xo+d^~?G6iR&
z$wNLEk{`Cr+-jh!V_4-64K$JiKs^WJ21x9EgXI`U@IrQbi^Db-78Oc2c?!MuT`R<+Nw=wN3OCCtU
zea=7um=EL~+LooDg%{=fhxm8InSZk>My|ZgfT7|GiNdCJ_jc>xqCv6utJ}yVEDY(E
zruKWl)|>ubj8{kS<~2;8PD;5wZ)AmlIMtyGYt#4d)@lvO@l~7y4IIds_9L}MkC}UE
z`~sqPRV5lYre~tO-MPfwUpF5$TDq&XC*Qu5E^SgVpHq2hKuO+GN$<9Kz+KP!Qu64<
zB{Q`<$@*A6jUXnuA3PJaw(1x_BMNai&j@gcnWzoBn1
z0Z6;714xwL;fOjOML>H(4%G4*CG33FIAni@Ea0=HNAu|x57gNe_r9_wMfsuxIHnEN
z_CCZ@@uziN^*i1y5n|0PvkKni_x!3B5XynkSF>>&FzRQnwx`zOxHGCF-d}TNWQ^LP
z0!%(e>@0URL{SOz=JmfRNzm3yW^rU)+=)Ijquike(E)$Lx6dnLq=+BZDOu%ou)cw{&V
zz{6|mcft+^rIVskMf$ER8C$gxBk7_rTQf1e%6?l${KS?1Bq94pp6A_zt~}J3iERVP
zMoyZ0D#AMY#5p+3)VMsN_zL1$3x+bRZS6Z1;^HT!9doJ*xuF_BJ_Q225aRrtIAIln
zUW-<9PjL*9qAb!>d+Mj2fvNUf@ZfQOc;w#k1s}g=fDrdC*KuC=#HOK5)$~Y&gW)8F
zSw7x`jZ4In=3yIaQIYD+q5(L2I~&|-+D(RierF->XFnqX+*ADQjm%pnXZa91cvn{c
zYz6rBy?r>1RG(75T1^xDeNZxZJkH-Wk&egsWT~LFYLJ?E=;jwD<-@QJRV(%x65u0Q
z@+0nPc-Jh(^zRN5j$kspd~N6jq{+Ci5ngL1Y&A?%Efyr%Crjw%jr~;t+3RMX??^sG
z;u7XKdvUIvhp5L0T5T
z>O4&dQFwaLgcERA7FWds*ugCz1#3Fb)cXd(_ZM6AKd&yH8Wkg%qh;Na&8FBH4Oqa}
znBbZFJzE^o;5_AymEGWCg`IZe;dYeV?%uQ|0+kl9kgM#&Exudbc|0axBN6M`fwr5C
z#aoq<1CE{?6IcAlJh>a9Ne=z;`lk4UgcvXP=dpwlw6<3o3E)Wxq42M85Nta(Y!0yf
z?o>Wh@WdFs?HE1Rn|Ct8%ezSS=Pg*rS5ii(d(R}tUb@{6cA$FRF=Bwc@R?VoSn)G7
zBPA=DnP%c|wY#jFC-ku`T~BggZlYrxCy(z<@yH{zPjirKnKxUYjZZ>id6q7xgr
zn~3QuJR)m;W82g9#1VP>507U!AaxDdw0pt9+c-hq!I|J2>#}NM3^S{51+#y`
zdB6TZ*|J6*3$iA5Dp-&G~{#*4KOq*
zYGtKTto^)M)**P`lZa|KQFgD3^
z^i5J9qVn!Wy0FG^|7f#E-g$B6bfd03r0=d;TS|PGz2ue`?lUhkBYdSxPF%G$s#O>f
z{V`)(>u9ssI|Z`X6%nzo#etm<@f0~&lhO8awZ?VgcTnu$W7PmV+cNosweye`?cO)N
z)p=3pa~$Yn&kL`6Bhds*H=PJDZq<8Dmwe%|b6tS7m`
zsx~k_*(+C-n?qhwf^9gpcmcL}kvKmbFqwFSE`(jYN*S_nn&VZ|(^J(a@XlQgI*6mC
zF~aOFEHIT`lyZ9vWAel~=(p-kQcB`%^$$Lk$+Ay=rXU#KFiLaID%)wCEz2}emBL62iE%Z`Sm
z>VG(e;zI(U<>_n<^{^U0_A(vKs(=W@D6D(H=R`CEx-XanQdaH1qQ+{`Nrm?hF)6bf
zcG^rvvwFF!{TOE{6toANd>u8FcIrnnxwq)P`n;GZbn_sOl<4O4F1Pv#gL$4NqPRpu@YUxuoAvfsvvaMGk^_5B?;Fdtm|Ch@-1(w+duvl4l$3;n(l1dx-Nc)AVyQo@mto
zz?D(KeWu)V;G0)j;0cZ3?Ao%L?N-@>>#*c{xUb4Cum{e$Gi1%%ycZ!T0MyW;r@*HP
zkBn;?0Pg53UY2fu3L_y60JU6=Onj2?Zho2s#fV8Ip(VH{U
zCIPl*94b>!OyUa
z!OM3n565R~Cg3R|6GA$1-}jS*4!tFAf`8T8bZfG1H;gh|`p|XfUn_eo>)Vb4s0O!J)7ENtB>t}b*Oq%~}
zs^2LAFn|^U5TwJ!PcMiB?$AShNT+u5rz!DEjz$UbT<$o!W=8rJUJE$wmmS*tPqz!e
z{3jwN3%E4I)+GI)f>9u#K=AWuLpOHa)PQqOnMSc|3@b}((G^0`geZw2FZLumxrbfQ
z^8>eOb8?0iv6&EU6RRNmZ%>Vb!@ZFQWI7rF9oJL7AEKCHBS4oK=AMLEik9AXDZj&!<3P%CpsWAYhOSRJz#jz6Y
zfo>I#{w<-P{mR@++nmhvgK4+jDi%F&rK^yeNV4vFbd0+H{!sdTN@{M+t7FtFa8=MV
z{^9-LJkmGn7k#!PfY%?(?{IIM|2=z1!8=jQ)_XO#?#zJ)Gphx&LJGsMi|&WNI^=&~
z@t8@W6cF6Z0pJQ>oR#`6UT0OUF2myhBOV>R5dB=xGoy{ng;rFz_75FpC!QH-rA%BJ
zx$mylqSmXlS(r%J*P^gAO3-I_x9$UY^?YLuzxiupjBa5)mwmL$@uGH)o}IYj97rcK
z9kMk^Tq`^)%0||@i$dg6wPDFaOy~JHk%hupL3iawV*ihJ7UA<4FO>4-hKvTnv;}>Z
zCmeM26mYU~T+TL!0X{R~=;kMXkA#DsY%K$mC8GyqG5_ty5bjenjDKu@KJIZ>j>t;-
zbzkPEjK%=MA8CtB$XhFd8>
zoKXP&hpYhN$+swu`ShjEJpeTi)kWIXBS9_?WLFXA`84Ex;rzTkZ8x3~re`2!RMqd@
zAORC5?3}
z5!`7?3d81fU{ZY6w?G?1V=TS5f#3uAYR#Hh$PxQ79ORhMlM+0XDH}ZB-m)$>%-|3g
zUjmc*Gy{H^Q@kKXiAW6bsOmvaSiumx@1CEk=AUYqvOC4dKc%WR7o+L1_(;b3wsV);
zRmwz-Q`M1-SGH)*FneX0eqpg&J2U&TWEKcy)pQ*qZ4H!px;V(q<
ztqqS0d&HQNWHxd#%%K1|Dc0ND)7ZIvy;a<-HtLel0T8>|;wo3Rd_dNJ&;=coU+^))
z?=cuIzg0c;kl}3eP{6i-OGqjJyLan{m3FQ{f&ny*K}nf(LECC9#z--PFWamd3H7Jv
zUZ1K4wf|HNK+HEp{X_$7T;}UjTu6+!PFq?t>Vi2*6}2!3atWUL_$0!X0Fa8?RqNU2
z1`p}l-J;G{N6vSIgiL1wu1{FY>ZS7}%q!JcWpiR=EdLN~pT-s_`iPaWnd`QT(XWpU
zhb8-P#v`$yeLF~&Jv`YNcbgh315|?s`!82#R1qEI$wbwc0<_IB>|W@}`_;}Vcp%`x
zH2$O!y~?1`v=G+Tc4O@KaxzpNMnr|Xx~mnC4&Sz6gpiHnp1ZbcEux9_MU-Z
zrLi0}1&1(FOLC8+z(sSe`p#6eVrMF`DBHa;>tF&Ayxu_GY#LUw(4B!5goVcX2X9$Q
zJ8|g9n|rG_3oOb7zXXJ`9-6(o4!>R?Ubm*k>Hgt1g&@KS`Lsz_V$rNWd-o|CiUg&wni7`k`&!~-6tzRbJk0bT}gZPbMaGrr-zf*OxlO`FxS
zO`W=KP$H^`jY+OAQNbq>qjvt>>1>GmY$K-g*+kx58i>_?-O)fwRFPQV8c;=$T+^nGhCfC+X@A=z)x=fP6bvk^x`XlwG{ixB<&uZ
zS7$Oym_LH-KY$FHH(-jdOC50&tSrBm4x;x)MGc57cbE-_xi@nm-5C@+LqdpKMJ1@W
zyPXw+M9*|AVQ4kLud(NzfyofuDH7b7y#s5QWeZ-f
zzpH~Yb`;^IL~kOG
zT^Kp6agc!PcFQsDf>Ki#C%wA?8C9Tbw&K0MQ5}_k!@bgHV`yHRL+p_ioZz9P=B&0tt^y;!&=nU-ugX6%~y%;a}#+kK~kUX$>@he1>30m^
zXoNhv!7w+hsM?;3?yoF@|2d7}`aK@rMKh`6;BV&@w{p>k86k~hAnvLAOvLW6;|MTU
zUSxLActEVgK!d`N!f{(r-P{1@vWWa>4!LVn{fBx8x~K=co!_%FVa2pi-;qrwQL}m=
z11S+FA$D$~69)dCSv!yyK$0Wku}qaKXIy|04T-Qn>ORG!u;>ZmrE4pT3-2q*37c84
zqEek(JwvS(XKj>_Ys+~N2vWQ$ePoc;$ST9RH?UtdUx7^-g9pj)jCGf3$!
zwm7k%%dYT7@3nrL_r~9kTl&G@8NDk%91?s26d|N%3(NlmVP-?_=Il!c?Qv9@-u*X7
zN3ja~Z#wnxH9qB+!MZKHnaHRtjBu_4%0_*#q4#_?Lh
z$`lYEAl6OO;g;WqMD5VR05mpUVBQD>wq|T-vh9s#04<7-ovwGJNru1o`dQTmPD|Eb
z=9C~}VdS%ywE!NMsz#agYb9#C$h`)Lv5>pbICQ*V>damasac%{4L>TVfp5=IYDtl!dY{ap=4&Dk!
zNzUkw@3kGAM9(|=1Tuc13-j{sNKb|)XMlcBu@8^$OSEDt
zV2T!?j2w>3Yu*A^mX19k_zZ4su_vFY0gT>2y*$;G?$xyq#FPm3fR7mmi=?p6(!(yUe2n&9)<+qWzao?JrA{bN~sT|{OM`#
zs-3o2@P>h@L_Lj%)poz@-~zFCqT+z)Br?-z>jn+r~Grt=6$9M5VS
zI$<9~8Kd&kCCN6YtoW^`W6C|?GLA!;DmahkrPnIBFO((D#}~}QZa4wxg0SCL`wYl(
z07wjoU_|fHuT|Mu_QXPuIm~tgb%JJw#{i#w9j>pQdUpoFQkWw`_CU7cP<_WsAs2Da
zUm;@^z}|iQrc8Htl;`}IWER6KQ8TA^jsbei8Lt7TV#+lS9L*mWt(oAEFu<}=p
zpoHKJQCu6~3hw7H<#Ob5N=ENi;Xi@=Cw8ywg(~85MT6&*&=?=(84Jj--YWu;w+rHD
zp1;gNT7MR^{q~Z5Ba{db^v8Fu?I-?ZvEC>Ku$iW3>t-=YPQr1>mmLMb;2y95ZyC@(
z$&VIly{?m$X|SOLel03EGQ3BI5+S|}J$wB2l8%|$H{TaqpD9x!J{KP5r&CpfT7O(y
z*e%ZRcz0d~-7rS*J9GBZ`Nx8rM;f!SoKcV;d65oLUN_M}DVF|wa59iDP-yliq4pq{
z)MA<}zjz!iJ^wQ+1hciqR+Z~aSN=!rxAqY=&b7<>V`$|Q-nRn?+NxL?kUe-TWJ=|n
z@pN_$Rti7{LMs3mvcCY4(-J|Q^z&ByP{dL=3Wy@>GhLAz59w`r_WceG4)X-x`x6%e
zkR#NS@t~4k(52q%#q|z@qdOqlUM11?pPy9#P8)py@b@)6(VQjrc1tG#SGa4Nb~dPa
z@p;#g^Lmct;-h{+$|9D)>k;rTug}71jTvb&liLUo!V34PPL}Xcz!i0AN!G+M$!~w`
z@^(&~9tE;gI36P=GoIZjJl}Vgt0@Rx-|)$;k0_o}*#<;`LeRVKL7m^dJ+#P6J33pNc%3mTE!uI72jMbrZr-KU1#qeY9HFi0h>8g40f!yVc(B
z;+rEOS5h{gZIFXDvK%+td4gTHlp^s_vmR}OO(_^F2+qV?BZ%OX2FqWOCVN@$
z1Fmo}e<^auBpcb7s0L6Ry1%p-#S@^^PiFbR58^?$nz6g$`OkhSKDW&IO~<3_f>Rv3
zKrSC|mDPSy`gg22^d~H~OsXoqY+WS1;x%-j;J((uoa$}Klbn}H?XuSb>wD;RE86$Q
z6(-es!E4?{$sm)86cNK2g&MO)RS}DJ)!PdNZCf*KIWDzJY#c$Y5(A~xTL1*WI;4fW
zLVLJEn%^Hhgg-$8I;5XkD;VVgAd4*~$gdaT5t{wfLKRA($JbeVH$~)u81^GFi70V2
zU7*f%+k5qaXD6M9k${R;6^wM;Pc2;zOv2+d=GPte0Bcdyx>a65H4ASABsEQXnEGuQ
zkisPO(ZVW~$JDR)YGmMnPB`?>)E6L3S#%O70jsh4R%o9~HUp5)_-bEb65UTj26oXy
zgft~Wvp>UFoKmts>iE)B*5w+y;DdFj^O#y1PeGTrm??m1P8}?FHg9ByjDNUcNR{z^
z1xRE2F(`2-6$lB&&^}cYM)DM(w=FcqkaS=
z!C|f75a$mI3#L(TC5MzVsyKoS(nj1mQXDg%z83#v<*%=iy{5ow%UX$ALqJ_kFhCsN
z=(e-Xai`~41Pxc|0K5D)JZi(-v*QtQT^hExp#`~$NfT)yMpoKVH70Q+O}Q2bSUzdhc}nx^qr*UCLX8^}kkUZ>B`?lukYeu9QiS-nO#r-QDK%sJn~FqZh+n61Kq%(iJu5DO;(^-C!<&{U}w7~-hm{r_$Y1U
z7cq2}ZqpTg`$5bEf#td7D#m>sPDw)jd`TyDI9o3)L0LkAKD0_{BM5waoTd*?qRalU
zys9Ix_}E_F%2^jkA9%VLd_!LHPO3{qRbzkKZlO>wbcQga`psjYhUYr#K)M*%AvJzA
z$)bYZ8Rj5qZQrS#JHY<&8kS#TSPmt;d%3UmxhW4~nB6MylXEb?W7;9(#sR-9#H#bH7d{|Xd7-h+BF1EgnO|ceqe8Sj=^9D?*W!yL
zy5iW!1{TDkEErvw$+{LKeyvVo&Faxk9$!&BWb~*W$fLV{P$AJ6IA1>}--i>$LY5k@
zVk5nWHGXq!F3$y;QbNh@m($~
zFL7rNc^D!{m%XU+PW(WT854IT=4Sqg-w1#XN*G1PRWh)+?mY}kp
z6egb5P;XAY5(L}p$qXv=8E&%;6
zBL6{O=nHNdA-)AzVJj4fTg>L38b`vwtxubzPWNnF_Sj|2By~PJFf8qdOw-gvyQt^s
zRRn~EPc$qm>p^SBwx9++9<2=I611ah07rbjx1_E!WAr+#4JI=NP?s5wEkL8Z|G0RI
z$1!9;+N_%H5|bOqFGC0rUfi;VwRzJO`1P!HhKuoSnxkQJSNh-N?$l5|AbE#L8Pmsl
zp}9N*&D4^U8@ZC^L$Q`3M7uyvER>)bjx*5tw!R~`{{D*DF`$Q{!=ZgG(kR4#drAx?HYFDa=Iu=xNXenX$D{nq5~6zD;af`Z
z8oO1^buEbq{XnEUx?wKor8*FHE16sAeX!@>R_X}&xt?31v124VbwGtDFjwG=26vL$WlU~hf
zrG~r0=A74Z3W>d-$p!#7Kjj}Y6lhQ`m+OnN(rd6)w7op`?<`wN+5F&bz3)G
zIy7qr(sSBW!j6z<%2G$nk@xTGWH4WYQrqWqOjg-!%1Mx<}v~3ylPAb?p;>r2o0oyMa^U8UbXdw3#c>EO#h@hWsi&w$KsWOv!a4fQO6bar#og^6EDMxl2{Vpur;J5>|GV
z_vZ{@^p#1hcjygCjgYtyw#_dCAS1gEeP@69RTUA{i=Lr%8{f``Wk1{RQ^8pQW}x)i
zYNj9&%E7PjksJ5C|0LHpMc6cs{36fY~C
zlgx^Wk@9+>fsPR9QT~0GENFTuG+p}9+4T(+XS$?*xyFlWW3GgOYP*1S!3mQZvnu1t
z$3<)+;G$$n&%DMT7>G+xJ?PQdL9=R8=pW>aMP2*nLLca63IO?Gt*D4Nf7doCFPWlkq=NAa5f6-$?0QQUT
z9u*LVa}&Zo^gf%|niz6DNZ{)4Z9V9wUj?|uE7ejF;|v1Pj|^#$h3g8+s!;JelOpNT
zz--^v*EvOraIow!69LzniJ0e27_joq6whXtkKNcP1-M(=&vgt;=R}TF9&-bPQ|UcQ
zx?gjEpF2@$THnqya+-ndx`dp|P(I-PZp?+hDx+_vL;!i3v6mEsearEVjzz4uU@Up9
z0lPbnQxzs4%=f!YxSF*8nX>x#yY$S!?unTlCmdngWimB>tA2y)kxx%&wV5zDFFkGK
zntiV2ft}j-58E
zqPX;ubsQj1Qn26YnuoN;ONGvPAxqo&k+>TrnfYg!xVATB|CvGi>pyPp%|$c+(m~h-
zhV}Apa9AFj4p~Jc{kEY9-X%g<&$X(p+RX7lUYy?
ztE{9P$ZH5vCy#1@$~ul_glecM5kYS+`JJY!=1gj`lLxm4*17<>>Sit8MJXjw!pZ;%
zb}}CcNfA-Mw~^|EI?R=#e#hAC&t(3*W@2kXvqoxIKqJoV1qU*n$2Il^8F*mm&)qv_
zP#1eOGPp=;#)%R|2
zZrEws=IVvkjo!agnkN=$cTo7_sNakA{`=Hpgn;d^#7RZmxh#J_6aO$hg?;*2)
zpU_e;urmhLv?J^NcS`s20`2DFVf#DVcvXn>=e#Uoe#7y9t27tT?gNV2i~l}{|K7QO
zSDpWo;4Kqi*Tr#FNX+HGQ+l8FoL3gjo9^F>&Hej?>cN1ef$&87tp1(SasSvYBK(_K
zum9>WaQ44T`ahoQ|LY~)8+v2yum1(`|K{>O*-8s+Z~8E4cH48_0_uU38?H8uQn9D|
z9tLn~*Uz5lXq6{a7BG4ro2r@fxkQ9RhquwmMJ38(@-tOob&7~@EV*Q7Vbi1c6jae7
zD&&c&&)a{3CvD(~{z`VuSHN|U3K{Y1+vO1XPt16>}6qfE}4h(;!xgdgRkyt!~9!*|8yFR4xf>
zqn*6?{#>II*SatjW-jl%rCw8@VPZzpf+z3^M|DU}0;_*G7h!fGms~cHzSexMG?enV
zW~RnA<{ThuZ-8FM8a&|wI`o2q2v!^y?|B3Ct`HRW4f7%#b%=VUXk2ZQww=2=geEsf=}^(S{=VC3Gp=`IJW|DR{AXZ`QB-nHKKzUy9At=~_Mz4x`h*XKK2pYP`jDM3FIu#2Pwte84#
zn1no>5*fptAwUHX1v*oVo+@lxie-n*_d`+Ta0lA;=PNc7O-JAU`I0h4^M6f;%o?B?
z;7bVQXx~F}&y3-e+psK%f>Wl_b_cR(cPgPz3|0#I_bUy}Y9nC|RpQgU;ha%7g1A7o*$;MRU+B!eN4g6eG|tPC`}gyaQ?Co!UnN
zAK$(`V0-Mp)?eqJ>%aB?&Gj#91Ew^ye#R?OLNDsscat;zjH_IJYxz?LK56S9hQ*xm
z1)e{Fpcr2X9&ENu7rxu5_m!T#hk-S20j4YH_M4Z7Pv@{YdgYu`-nmuxuY%oTG-B5!xuhubRL{p{~x%Cvc>-
zgBUpN!n0;vH0u;-M`K>RsISJ}QeB*e>qHEb1Zy3{RnNCTilC)ghbS0V!s1gW0_
zKWlu&+0cZ$g*^B=OYk7NQeM*5-fgx&bo=}8kS{ZT!`d%fhFH;OYhS2r188k%=lKC#
zK1f_0owYd%fa4HAGbt&>H{dru2dF7^BTt6=3!ejH&is&fSQ;Rhv^p9qEvfn^57GP!
zGTvR5O6@20ckcLmiNl2eVT?i|afbxj5t$5y!yCXeURD7cztb#oJ1;-qnsMmCz6!8p
zlUtL~k4a_kQn_mo2Qby)PM$mf2?+qrcRtECKL@LG72q)!VPw+Pq_o91q`KFh^w`>W
zhP!O5cy|HcbNu3KLoEPhDj%IT3jv6612-$WQDUolaw_j4_Ry%r3GfmOgAf^wOFqEa
z@LvsI1w%r{!WtTX-WmGOcQ(ME>JA^49=gX_nY%O5nRW+WBAbFbec*t)XL8{Ib#_+h
zy^+J*7jtj>5X;#0RO?(BZvkZb(1E)|crI+EXDb`=N$UXs?Y#479z4@qu!xU!a)BGz
zf7t>&U!gH!FYuZ>V^QQk}
z-v5)m@}E8ZZvx8yhk=Znqyg2WY+*Ue50pa3bifxWd2N=ri+6NuG91&GX!*x0M+msV
zI=>pf_sFWVi8HK}MXt-W1U|XM!wG~Y+Q27Atj_~(HA*)K$+Vmw0r?t#lqpC*Dv%LS
zmm1xkjLHzsD08bdJx916YX}sX3-5HMJ{v0p;b10Liy)3ZSu~w#N@PssCT+P*TDnTz
zE5lp5hAT4?r{Emte<()m@&VworBlTYYnp+8%I>=46##t6)4(^{5qZ}KsSm7gN4uSS
zJcszNR)SEc$MnEDZd&+x+lOd`WIZf$!&qg{fuJDC%Q7&g=TEA0+5CP%HpW=QO?KU2
zd;4W``tBzByAU}e&@6Bj5Q2<-X@SKN)y#X^4v9yXei~;sHtk`UXZ6*-bgX|aH2G+|
z{$;L$2?fYSbhp1fZ=9~5xSsmDaLeIH5XBs?iFDTB2T{zs-G}+OPTT{mSVW}h%_kKQ
z@yneI=D7~EJ3z=Yh`;+2xZ7_gvg@9JyB*o_;W0u=8W!;|k=w9UeSf;T>>{Kr`0DYW
zpe0o7)%T^8pR2P+1&$x}WgK0q!yq|^fZCl7
zk^^I^Q+_CPO?9>+e>WCifvV6R@k#4M7+$Ae9Ag$`q>h5ei}tz{m3H(#s4<@%05qsO
z)4jQOnxmu!MK*)~Q}ph4Z}h7v9%b=10^z}{T=wt75>Sfn0h}tUUY=;1EH1lt0I;3H
zm9z3&RqmuG`WOLYN>TY;z1kS4ZHSXIKfm#iRsQ)@obwK56qAgBkj8JE>EwmNWm5E{
zx$LO)(vl55&6grZ1#NVIhkGcem?q;`8tYPjfjVr(bM33mAjakKm9~HnFd}>^5mLVSY
zo0Zi@lI01qIzJJz?GVXzjm`jivmBb}%}r6f+z^Ie6z{1DWPjuwDKgq^dU9;D0`EZkBWCCGe
zsJjrH_8`oE<@XQ7N5Up|h%W6=?@>V0Q9-=jIb9OJ&09(hU*6O-
zWwa;&#<9na1CB{R6bT3CnPq;kU*LJJ02Q>B5p*nmv!;maUbb+;D?6XRHcT=fhfZvM
zzDq+Oip5&`86v;7HS&WeEzuXy@4-RfC(DvmW2EnCF6d+OW=E5E>V-5C2edK*x+<5E
zy6u_NcHTn(LF9LN*WcW+43{%K3TeJ-fY_oOHkRPoI!8W*`@$fPBII~SZYoy-c`oG4TPm440k{x{T7t4dgojv$C(VqV
zztOh7!1-lYc
zq!Aml4X|s6Q2kn-`$jaVlt+?IDeSuSs3$>i!c-d=9uvn3ifzcyW|&Lgze9o!43%A#
zeH`%dY;yN9w#UY3%I*alvEm(>W_NN$up}b`*dh!-UUvaT)9N~e0_~l8Yu@dUL
z9xUnw6#Eu|5()9!#d16~M!^MNco_)m1gkth@aF|8B|N8mb|#G?oTII5`(h5CrRmkK
zcSjFx0V%{>cqwwS>X`DUtsfq<$t80edIs12><8QE)-n>jjL|-o0$xg(kHd@7!glo3
z6I}}XBx$1v)At73Z!hR@2pOYc$YC7Ko|3iXu+AQHb8^^oaMtU3lA=%Hc)dgBTjW=l
z0j4_ykAh|}E1O;NokEATf)i)9Mj?U{4zUDSNOC{?n2wD*<@g@3K1F(Kz&`yEntg*T
z)p+<@bU=+4%}oogIm;TeuDr)=_?3R6fFs5u6?h-)i!Rd);+gl}b*3NU_P9m3Mpd6%
zZn`(er-YV5A!Lt9-^{-Yi>JzIB}rYLWD~w_JDMKFt35~}niuK-7GJZ!YZ)N8+Q}C2
zeWWa-+uA23W+1Cg?{x>zkuvBFkfu>vY(Ebd`2%yma`qUXG;^VNXYdun_>ns#qjn=a
ze&-nMSv7CE!-wawls9Uu9)2zD0XWTa;WYnXb%DZaj%IQ<3}sJAE)(kuo0XR3>qlRe
zDlEl1L@@TU&;pJ8*)T-DTu&;dx2=!AMDDTAQNe7?*)VgzdSKwE-T-fP1GIE)+Vcxa
zK7zFpiU!<*gODh5RamzY@920=ms&)D{_BF4dStiO5TJ4_v!8&*XO-jInHfI*;&;LE
zzh-vV>k~4}2XCe}6`wK#a)*kw5vN|P|5`LPzZaJ*%%ZJmwSm}Ra!Q0pGP-L<3Du<`
zGU*H{?Y)1kQbj*2UoUHY6bqClMKecBBB~(luh+JmWd_g@dwSYw8AgG$;f`y;Y}zWV
z0n%Y_G;$Wv(6pWH&WI#8*s1d{k36}Wpw4vz{oz*!DNG76s^lsG)8L0%US!G`obi9A
zGXUAi3+R443l4`Gh=;PVp{|!UJMsZ|A1lXupyqd5UU;HLD}yQIROFpiXM!$DczXyE3A{ZJv#>aq$C;Ec14}mlT$UoE5
z)tFYM{9UsF6thhn!t>T(13n>y@c{6ALbe^f+iN5+P&AT?$Xs1u-
zI4@{rS*Ctk+-}$;sxbvPw_)b>@siFfK*gxXf2K5jFksm6SyjG)I4c+Q}KWaa@m>v1Q2+?a=T6!
zaWgM}t}N53e$2HOB;Y=ioR8?olD1BTDZ4D<$}yZ54kFIT;+kmHg}*&@WeW~mMh-n%57h6`$Bc@
ztbm?HLX%agOsn+DFM6={iKT%X<35%PWSFHG@_LC*EO-faH(2cXde{0J}+vQfDm5=IVwwz
z40a}Ef?BD$reQ=3^rQAM3#fmk0N&t$H)wCGSZ?+0cMo0;xe`J62BZMIq%P;e1`TJA
zrp$oC{#2&G!9Y~)cKd!bZ~}CMh|TpUzXKvuYrbnQAc{G*)>qSjXCs`O!S%OUOXw%O
z?m5-EWLovxhDawspz*IwTmSUjh1n#W+Ibp?h?lr*$^nesw-xFdhY@+gCX9EtA(uZt
zIKC7?3TO~tRxC9tRf9IL>t#uMEpnH`9IBvicJYp82k53nzEroBh4W_n#*kB?%WXgA
z8?#7Cv*>6^mp*XBopM;VOjeM;>mMh4OAaoBr%|x%n?G%zL4R6fBP!5K!?S|!ER4uI
zOERW-<0Y;S!3MxDKJqM6FjbJ=Hj>SP&M+r7u)Y*3w0kvnW0uxg0=X}Qok%P|`cDt9
zfTHv(kJNCepH1>uLa&obMny5+VGHP|upD%3Odjl2(v3-)bMbMjNtWlr7|YONE=6dMTObhWS#kX}Dp=v(
z`A#FGfbV;6tJ+55P0u!HY_&|ReKh{RT^cweb>?CJ4odc}SC7{LjYs_{b
zzinIfE`6Yx&{kIE_CyWii<&O+3zkgle{-`3Y?DRQ-VK&a@Bn`L*-c@@{HtHUXNtV<1o%WjQNPTD}U3
z{g70)Ke>13FD~^N8KG&qvG?wq88Rt;pk?7<47RyM$^o6437Md5acfIAvLto#
zD?Otk&Y_2tQ9BGbWpV-9w5@n`BuF0XKK{O72KVz9;X4ykj7G@U^dZ_awCRG=Eh0}2
z_EHihyZZ1NwcdJQof(AGPfiy2`>D(F9(>%Ue37B;E>km(OfjqO$`mI;Dk^hu$b3+Q
znm1iC{Bl={rGzXBsBKu;=iVE<6ES1*t0iHO=o^_g~
zjfPw=BB=ny0`Z!WkP~??1Hx~PHb>w0?kqt!O}`Q`mIc<9{)!@O#qN}x%&u+uPO(i~U
zgc5St!CCA8W8X5^18j^%{%8f#d;Ir{ApVlE^HK?Fwn69-6<@dnX}1z|p5ivJ
zsmoLKe3p_-Hj#>i(6OB?wtXoJlZ`Q#%z&sqEyj=nl#OZLliGRj5h3#!z5uxSfe_7D
zIjcp$XR00a!?k=UEJ}&3zP)Sfc}=0{j{E_^SFS)Wx4LR1Odi;E5-H1zW2ilNu@`RP
zfBs{KBGeb=|IlXPm0+%mqmHaEi3z{ZPj|Xp
z-~{xO%3G!j`nyXV04gsmG@JN>3p^pU&NX6YU6NP@Q)bT<6EZNXRFCLXR}S6suOqky
z&j*|PS6wUz==|j=3uti!V{tJ+m6X1#JR+n<5dV8MbVlHExV+|<+sVQE?tQ@0X0Xyj
zD%xncVX~P0j!DTz+pr%^l7vN1_cq1yir0v)Pt<3eW>it&l@&A1(n7mtA-BYCl$)0<
zgmVt^TRw;?0V4`IJyOQ34vV>|b=z;fjMJgNTz?bmZ87-=fNI;LDd$PxApeoSc
zHPuAGh^rNtm4+<}4C0e{a;1|Udytv#jWp6p{epW_XQQ@?4U}zBELHn*=4QNt^J%SJ
zr8vAqUanCF6|xmw$CeFM?_`TGOFfyVwo|pfuxmiv>9_3aA$XWRAQ!oHD8(oOk;hdR
zR*>@TUio+ZKI76k-@+_vkt<(mEa3{2lIG`&NwDlZatb`U3%cE|se&a8j>m~C`2w`{
zy%@cIF#Zesj2~Ts=|Q5CMs<6BL^Z&!cL^2Q*7uE;v5yO&U4CDSt}~bF+;lu(?}b>v
z3b#$Tfj?xVSs23>Wu^(n7gs1g1^i-p=0!YUdRE2Yj822I`qezW$LD>NqS*_IWO;q&
z=-r5ZtVAHXn{k9u=+F7#f5jKqr-r@cfyOm((*V$O*Tja%l35c*%Q%PVcsNRH|F@ti
zC9!H5L`b)h8n|$gQIHn
zT%gOFU_#WH8Riv%ImhhEOH{QIK!jg*eOcc?E1{Em5%DY%)R2Xp^Wci>v@D5_n>xWE
zq*RX{!pOI!6op|e8HFKpFh^_rUgr;M&|Js@?Z97mHtFuZt;7}hoEUUBq}G+2Vq@b4DdEIngBO=c|^c-tRhb
z>o$z7^VTA%8Wk0O74M}JTx&+4^zQ=T?mykQvTMw95(rjq=TdS!IB
zd{zzZR{_EN@k!jwx`7T0EYOLqR?(itMf{o-mH-0
zfh+7%mH&dj`&vdfos|3XAsnN*e*zBSym(!y@JFAAbYmXKz&SAYH)aFzHX7gNBM#`;
zAf}mrlS_o4ZNEIMz2&OXAz4yCjba-qpZPUWRq@qh3pF$Oy>5xAsKCw78~9#;lfuAL
z56`h?1H`uNzr)V?UD-6=kpg@VDLHl#QN;CKv$o<*n}OClpryPf5!TQE2Y8RuejdrS
z2lqErqD-J6x4NaP6+M6AMrHiS!VYG9&>50ls=p%G9mP4g+);yj=<7u|({YzQUdS}GfzwmYkgmohl{`!%W{^!qdZefb8Ou`~^Y66b;=eUC?kv@D$GK-Xo
z2X8VP<1mJshH<5A^v^9(@GUSR-v4U=N#4yOrP7Q0=Nzv?%E6d39hetkFPr9Wh$Zzdke9|-HDjjr4I~L?$P(Ls;&=H3Hw_oN#nzS-conlh&J>9C
zmWvDMaaFR=qb4e(4nD-RJ%QsWsy5+2Z+7@isaOn1liqo{*9p(K?N9s43=8oFJUTgX{
zXcj4QN`Su!Ul}`
zMPMw&8pLPzmKLu=p7f{ZL_!r0VmRHO~A>*ne&
zF&zw|%HVV>Jj2wS8%K32e(^u(chSxJYJ_|QMNOig5y^mD)IF7kSfC4cej$1}&~P>}
zA_n)8x{nGP?Dl!DP%5EK>ntTFAh8p+x2yp9hitkuHc8qLy;H^O11-2oo?5CsbKMD*
zz<}X|oow1~oBMw|$iGM;wze|$gOsmE~
zISG8tnL(v7sFO`jU3Q&uZ!Cq}i~l4K5v+f@fg(0`5DHKXvR#=akK)m-E(?D=0BF*i
zVnmPrjh(a~ueB_1#Ei|7v{_*%5o98U)Jq~gPXt0WaM)Da(!(}lKf@+{K70A1hjrGf-d=sfBb;>3p-tfaf=7-3x}4)j$m%@i2Lc&JM)V3Bd8O!
ziMB46gC6<~vO3dCmTgA;ZuN49_q-PyvObzu`J*j5oa$4T!tSGc1lkN$?P?Lu@vPgV
zxH6``!nsI+dXF~*`oO7#NQA8BM6xHO&Aw6gytQBEkEI`465JuNSX7J3Tr<&treE>(wrOk6`!`~1{d$oQ<5t=$iQmu{R(|nH0ZIV4-0=4?0
z5t>L*g?lS{5RPTvf9Ow-@OPeA7!Xvq3U+JHkcD=)fr7C^)SJL40|4E+2M+mSukHj5
zem0S*Fb-%s`O&0iwMI`zjs56W65I%+C-8I;vsh-
z&7KhW9ZUMtrhe!fr*2tTA*JTwIyN&HdYso!AeG|Xn*nwjzKE!R3LD%BpvhXT7w@xk
z$v5Fco8X2fMPPU3feFiPF3kKM0$WYF|NoBJVGGN_=k6RZMX$_E85|h3Ph@TVFFU^F
zkH$`l&L+V}jEGs*}hn74S!aU)NCs3zlr~>^0FHd&r3krQtW50=TC7{QOKiIDze7_I5{+Hz0qWZ=8TELD(OFA1zv^nka(+F*e;{
z5SXrh9!kn-eEr>%TRjylDYBX0WH+JIsx-V&R$PL**)qv)q|z-fWv&U6cIboL8{ps90hZ}=SAsdI(DM^1rd>6N2laV%U<97-2;)4
zk42DUd~^dSOVg;};PDm1OdX0xCLeWO{vD(_B0e&fiRKHq9KFFpx1XcYl2|
zPP+R5+GT)Ej0+VdNnqBqdI{ZMm6SX9a?nU)_&eUT6!I+)w!Zu0i*+j&<>cBH3LCg7
zcyV=#V;RnYjikV5?nmeO;)<{ui`cg7^~I=c1gXm77o`KFXf)GCy%8{;B{EQH
z#+e^k7R7!%9x#JrOXt_#mnC(D7dU@kI3H`*GnW}cbdF}*%RnY*q$%V*h*I;e4!BbA
z#?g^?2lm^HsdXjI>NcN-N%2+{b+)KM3|{z>=v4^%#%`bJTX388l!NU342Yt&m0(HCF8V!c=}?6FJ7eaP{d=
zIev8V@oW#&aoDs^UJO0D1kwt#CE|RM6|{(yh8V*n~@J
zYTs=Ta9S6N{EXbCYUgszX`9+wYF2gDeEA;1IS+5ibq^#SjP`xr;{sTVr}G4MOt|IS
zl6rpVxaRL&m_EOBlP%kMono+0Qq(7au4Uc#oO6pgp(mboXA*g-^z-T9p;*gKUG|QA
zU20LWG-x#>t%oGFC`B*omah6x;iONHe_h;CwUS;@fu|ZnQT9x0=sq55QrtM{Q(Y4f
zqrbBIH4!0qAi&&~?{a=oG6p8=E4jlG7M@r?X8bYQn;$w6S**pcPl1l4$-6`QOQ$yK
zO+kryktPd#0gdtzE8y(#K&>f@oAoA$+pM?rV51%$i!<6;-fhW5__q5#N-h!iBmPKMQ#T+YPH+AsEA{n
zgpoEN%w^LG$ewhUjVQeg-GJ7t*^W$;6;c3FqU(;-Z
zwYFdzKd_MuIoNp$5zkn-^Lk(IKW!&w{Q
za~ouLjJ|CftmMqMbht9Eq!EzC^x-M`OIM`m!Gg<9r=%p)AOuYXTIS_qg_AJ0+@XalX|=v
z+sv*y(X=XWGue2B>|OWKW2KjNdNW5sh0n?V&O3D8TWPKbEu)Yqtqprz_lBbVdXPu?
z#QXSL(hp`=>J=dYlQh@@Z$~#372JFLz6s~8157+D(V=p#+L!ar;E{#uTOlLg-s{0h
zYSE*JiMd1CO5A(VY~Z&U{jpB*uV{mfqso@Cg;-I;1E0sY@JvI&(kVQK0rcYSa}PGi
zJ#}7uW1qAu@q1-nK3(wi@1XJm*C|zmuKVI)xa41x@!Kq;HVhe?gmXgluNhCEAtMCE
zAJ@|BEcVQ^K|ycrm_It%DOE0O1o=6zUgDf7#xsPFFNAbR4po^!t<2S^@9D8&pFTSi
zst+q!jtxNOfyCqJkRwEyfhgqt2gkSZQ1`{X#vbm3eud(?dZXuXIip#fNMK`|cPQ=i
z+vb%+p}04mRZC+n#EVEjR5419NRUhBI*@1LZ>s<@@g;9H|g%EpmI(_;=Jg@*J*8)`Lb4h;Q
zUtLqqR~MyAu;g*U+i@^PlTA(^Su*Ag9WDaG7k4*G?(qcTX{plZ6Nh7^nYtgO=>W)Y
zklaf2jo0XdP72ywi*)9vZPef^24_xr3k8(dn#^xFRK;k^b_)bTC=4(X>dkoD`|_Ex
zsaxNl5;>rTXkm%0!vq{XMQ{zAvY0z%25xBD;LfdtgxkD&VUWabpLOeJ9Z6POxdXR)
zHJyRjUdIHG8Iw^-uiudetWiOK1o8*1qEdlxE`D8>|Vzx#oL
zf;w#5_2g`U%%YLv;nM{9)E+Y++jthW3LrRl
zFqk0Tq3DvT+l
z*_Bd&AWBzvky7VmJX?#A0H#nAfgLuzTlQaUq0=!`ZU1mUr+}(Ik=1UdIxoK4|Fw!HPDuo{%jaiKz6gT1Y%2Wo_L~U3dH!&@*u5(63GWhzL3;&17RIRnxZj~+93hG05Ay928
z?%U{1;~LDV?%G!?QGB0HJY7_iJq^@%!b8IoJJN%ld!6#X-8d5nMC|DXa|kzH!+C-_
zRpVHpttcz$?$2jcwEh|a$%HM91}f7l6v0@n9_R4Qit^6X!H>Q2IK(ec$m|CtmSj@n
zr7#Of2L?h~FGuc;r;@m`4@bmT4XcXEUubqcwp!RzT^B2vM?pwA~_FNsOPPPxJ0nDul6
zLM9=nkjaRfrvYo_C#_#!be@`PRe4V>BD(AN%j#IPe{M8+iI)w_lXP45Tr6M?fd
zXMw?`Y+nr@oi=_@|LD2Pvnnumzs$-@D8F-*b9>uu3bJDtsdsEA5c+n;T%#f6UxX#j
z*P?JB8Rd7IiH^!oY`^8Vd9^bZ%IAFiGOLO&h(7j-Z5prTLAuC{bnkZ;9X5@PDf%ZO
zDWIR=cgv{RTuTB7uA;+39m}U@r=3t$d
zv4PPwHJ`WV(BD2|uBIaS(^`Wor?P6BSLA!=W1P`usxQZKY$fYopsMW`E)D%~0zCqM
z+k+N5qp~FFd2$BHxgR>{JwSPAm;+U@rvA$$19S|5=`(Ses2x2xk?gnfBiL%|Juqa=
z=cI(%P|)h1oVR#7fULoY6)Kbg@z5lA2oPC>`VCSIzP*A{xF
zeos%x-}}CB{^5xc(E9UM=1M`~`V(MU5U`y4d!?4*k&%%^;cmm016P<|!L*~wMhtYi
zbs?VsJDEp~C%7U$L6=9L9MH=-u6RVD>QpaCsk7mX_Ns5>p4g%$ZPvMG#uZ<0Qr->cNeNBp+G|f4|NGBLKb9Q|LA8Fnfy^xPu~R6@8P9A1A0uin=(lNx-dHMpb16
zhMZ(--`hiL#4p)h`&s>qaB8SUxAjll6$>RfG0wIDxj$;Rt}`?9cWkTjKnXZOH(F@F
zQ$7u*y>J*Ob>b00K^okG5BK^GaGP
z2LvA&wsGU?;7hNCpxfrC%yaF6ms@gJI3LctDJxRKaxKy7v5Yc)p%4Q2Sesdq5CEhA
zd<*6a>#c)13{RrRweIy)1xp}pp1U#Pke|Fg({vZMuc9}26$8ris$ND0Iw|1X+SXzT
z%$iafB-;F?lBU?zp2VpchuW)c_pGGZ^13WB%8?!}P*wPRz`1LMZMr_>+d_%mpqO$dGn=
zpoUHerO0BrUxoh0eQV{Xd!dEvQfxpfL3TGPrT)fwGRw1sC5;mu<=$TWoro54nkn2&
z!WnVy#k9OehW&-LD%ut@olw(Ek}-><(uf`IhP=K5nhpW+3OK>7DK>_Frr-9ytbDqB
zGk4O57gobUbtlE<;ik1FQvN^&;~qFy4jZN#e`al4FUX)l=!#0#^Wpic`^;(-AyxGc
z9(AuIVvYMVK=Qx=GsV>879`@GZa~rn#JnSg-A3-ae@X_kj%WeQ77s+6
z&D>Xh_Cx1I{cB80*iF1$Scq4Np96&(6*A}BBEM}e$OC}_lPlVq>+*$hNbc?yO86y?N=S{M0KPoxU2gqMi`Ew|u$RHY`ca
z@b>Jt#EpNj`^2jF?b{7jv9V^-L;k3X!$eb;)(D94O9MJM*C;ZeP^_3&LAAb5ygMv2s%IZ(Nc#0u_Zx1#2-yd!qq}EOv@E@t2xRs~S8hS~*9h-)`w;aY3n+xoonl4ZH`yIM
zr#w?Kd~ecgppIAh=H!(Wvmb!k{*>tL4u*gg4T51X2||ZFelwbAo40)IKbnANO;iF%
zDxPgq`9Lh_)CnX_P)4LHv)w%8676ElZmgX=eQM67i_B+itpun!!z(vdLR|yIXXhzU
z{^|IgZavnkwjI$^mtR-Hklu5kQFWpu!6FTvDF!29@k96DEovy#S>;dXwJ^BKI$)4x
zBDrhqW#N1k+Zkk{qObG>>C>lnp9IHjqi4J?(BK(g|J{6LD-;RQ?5P6W>RKTs!_>NO
zx()y305rJULKi>PPWmDivbgv?mL)&&igm)2I}>cSdVPcmqB2d?3xhkvZKzka!?E5<
z9ZC(1B?q?0mVz3t4uhQ8l7Ev7uA+$O-^RD&Q3>B^$R;+&aRMuwISo%LAcX9*CJB&`|%)S7B5j$K=NiwM$i@V3QLw18!8htvS=-2rstReni{xFBaiy|0*F
z2Jj7&QzV-fi!_-15*LjgZbO;h3G&!@C>lut8~g>0T7<^ngqTy^xLt$qXR#3tga3$s
z99w8lP@c|=%71DB#C^lD=a)U&22ajP;|fMj&vVDRX$FIIWRCFi;?sGXvVu|{0i@f*AB{EmZQHNUKBGxqTpWIrg24#&T+4Kp>fi%wE$
zEN}x1!dnf|b%lFpL`_5}Va)A_JJdS}?APu>Wr
z@S569Dm&dgh!qLP8laO^sPE{9GUtC(N)IFxg+GMlGSo^*pSS6z;(3~j2p{3#i&rcE
z+V9)V?5xv9ORXi?H(h+CR!rUnzf
zk?x>|rigLltTP2Tf{(xvxB@qzJy6WB*)dIUWoyTf9MHm>h6ii-$$E9Qt!l{#KB=zoIQJOLACv+0X;ix0rYu&x$l|IxD^)Pzyh1m4J|2`ygB%Y(
z-rv#5ce1^U>fN+1*yDXT+@9)Uy+WlS-@C>REIIh4lPGt3&TqQ0C~?*L)p_DR9ZHG0
z>_z!!*Mi?1@i*$hk2GB!QKbI3GjvU%mmAxZasrs;UegTV#_m~S6bHN_VFw#pENS1)
zDaTbF)5R*u#itcPyGkt_#);uKPq`MX$|JnOg)
zQ=`0Tm%O9EJ$wI>_xo6Yf�YTYI{#)in_IiSO|N6KqSaR04+2ks?PhO4}l!Y9{gh
z63Ke9Y{WL}6CGN&9PS<!o&{+u&Z=LUDmF@x9w=)h+Hvb@*l46D
z5XA}+D`@dWIKRB#)bTCtoTtLEI#mImhz$;xqL-p^RD1v{?6lF}itL|QpE3!}m&{Q|
zz(W7E`pg&qu=pa#K^q)Ebmf#axB^AVmHJVf_ml-BNBhWeLeyX_Q6?Kecpe%<2;+E9
zaE)Fc{YUJhKl70_^|Ra=oD<05$^$`n29O6V@bLCHouMW+;g(fmJO*VUv4t4#R>%az
zKqLcpA!h>nD~upA$C0L?g>oQk&5_L^$G@+;%zVGG%<27`ThFsMsD9d?@apw({X~(&
z=AF#6Lk-p>O{L36LCqU&cXs~(cb}GjPL`Y9tt|)B{+dyrlonJJ6
zw+|3F&#nYX=*UdBKlpt>Uv@%RFVz{Am6jxL3R7Qk2p!68+!sQra#G*LK9Escg99{d
z`3psodymF!yE<1ZkhkBmPbCj)w~*w;{?S4+j!~)tB_F|aT2tdulZU(-e6jW}Q$w?h
z1~3_H6NV<}TX-;6cX7+kV59|D?zHROd`u{e0M)^DKTP$+_Ux_tY+5oC*eGAc6cIi-
zT&pr|s@WNuux}mg%D3Z9xBd{YxDES&`s@CH+j|E5pJZB?HrJ5>xAEkQtFfFW4tDOD
z0pHscKQ9$8b-}^qs^vrS&%(3@kk4zbrwj4+q9!@M(pT)UOVioSuz&jcheyRVY`W@nn8e<{HFCxNUD{}Oq+qPr;B3qx%q&zpd(Z>mSZ?RbBei!*Q
zjf)=Bs#+#$C<_jkT@S?tA8<5@vnoMdJrTK(4P#mlgQk5;N{mkivtIgEh`*lPS2BZ$
zhZ?W7?E-H7E2WR6UKfP2AROGhdyn|1NdS{SLAHsynJmg{A@bH+(4W
zLibHE9$qU+Ah2V-$@@B|(|V#j`~-^@dQW{l|I=!2gz+h_S^C({Ai
zDGH0OH`(@BeT;t^Y=|0e*+!ZSilM>@py*ixS}_w@s*(rVHGpyiy<5k$L7pB}rCRz9
z9mv>l@XbbE95NsK5KNMffAiQ1q#EME)9*>wqNKK9U&!)IqrE1wYaXhP30#VRuh)KD
zn7npPeFnE7W%twu$tHZLx5i8LACr^V5_IqVX3ft)4+zFQyL0Z#D|IV)-BGG!do*}L
z9J{PNimx~9{YBpsm`PInl99$o_erddvZd*Ljf5tNWTB2&l&iw)=a+USd0_piFI
z!`CTMF$RW1+prcVY5?%(D?XtW+wUaaDvzueUoLd)x
zrzaotyP@X%+eN@noZ9y1edRak9FXEyU&Sk~o}7)?@;z7iF6MzA``$zCtG$j@u{agV
zuL&zY@Ed>g!UDZtx72R@WaEfa)=_85$%HJ!b^Pi!<9v$(Zxsjcinp#yPu{sk6>JCr
z-WNEX>Yqm7U!C|5HX2Irw9UxPuwKv0!@bg$ad8`VAd9VbQrx#1p88_Ei}$=usz7%S
z)a$i(3rk$=k3)$%ILfILw}y^-@N{x-;tcp
z=TXi;JqI6Fmu#;_UifdiqQ?J1o@bi8@?G}OL*UC^X{}-tw1R2C9lA>d!F$Fi
zX--_%{zNPJC6WTJeCfou9m&E9)~d*!1SK-71j_K*Yk
zeivU3l$gEm5%>G;X1v~unDd?`+zufBHZdS4&A9fLR5tGs=2(!jjp_@=e+
zc{E^A5IzgF6DAq{om4?sgkc*&U&jhV4Dt}b+t*@BmczEFWI0d`?1tiDEMpz)cm>UY
z#tC7_by7P91J@wQ*zvaUR-6s$Kq{bhIFlAhc)AFCtWgkth=JF^T5+O!s=wqfuZiw#zh-2^o|RwEB9
zen2>qa~mqal8c@@bzoTXj-I&~Jfkkpi@k_j#F-V{?Vl!g`IT#+9jJB(#4;cu+wm#i
z+9-j=VQ?d2i*|Y2^f!RIzpK6Hv@km|+y74FIHnD9vT!Je_3t4?a{X!y&;+_7Wwmac
zG)_uL?Dpwq3t9++j~lqMU*L9;Y|+LRL^a;NxEDK(8K!xORwJRY@SdePN9sHkUq_Ff
zz*;7Zm}FiS*=%>*Y0pk(7~@f8LD+HV49WBGIG&gXc{Wp?1oy;!sYqOJ|VC+`AiaKp0kC0
zg$U1ylFZ9T8M(M#`38dtl^}RB2A(g3BKOhy0?O-=^y0t<;tO0ZI&6n#4S2Hu+ik}$
z&JkUiR)p)tb}Yd?Z8HX4XKz1RzeaXXc1y^Sj6m+xC~%Nv`qs<4BUo+mtqu6b3!lrxmczu%b>(Sj-bvQ-1gRktog@w@hP9(7rCpQG
zqm8=g1Vp7nKWK93N!?)BAmsrp!o$LXgFyl=weaM$!R~0qwhrVr}Rf*Fcx0Zsa{c#CJdwooNWkeFItp2kN
zLOi`(z@a05jQO36`!pip6xnbO^OV{I_)luDf}JB2{QgAQ>Q;Q?q)9Ptm6VICU`)OF
z`CD9oL;w;Z8?||Ow|vlC#l8}{Cl^2$L%@baA+A2ijjG$h%|Ls)o3?}WftP0*Cvt~p
z7k6b}?7M%Rfyn?2l&81i9Ns6Br`B+bnQjwlvA3**6G`AW=po=H$SvpV;0MMv
z|4Vrhs#qi-#RG^4LZ3It_v!_f*b4y}#uPMjfvI7xTZg0?`Yr6GhcQg;*|wZfMMTFj
zqn8MNN`7lK-jj3du&$*#Ld{G|k3Ug)lEq2@>o;A$k
zDVIHgFPdX9&aa!Sy$+g%E021}dzB>p{|MA%Ot_%d4-V(oE1RpXz6*weEjFDESWzB0
zoToQwKsXK$0~b2$RIk_+#?WHRbk6jj8W)6P3rl+ivFz(+Wq~Ytmb|@dB-K5iq(4R%
zhPBYhd$TVa_0S0{%raOBRlqtf52!IP?Ahr+j}Uka>FN`34y2RxTIjY=4pzH-_+>7(
z7h^A3uvCbxn#(%kf?+>~Js8rZ_4w-muG_zpku9VFwyQ-f_!j`$ltAAX0Qpr_-_k!&
zUH<@i9ir?X+kb=m9`$dlPBH|Ua0AUmq#yqVsjJs^NuRiIJ7E3er@wX1M0&}H&dC0b_-3DfO2XF+Qa0CWu;w*IzLqSy#x!FnGYXB
z=KmLa-x=0axUFeHK~Yo?Q2|jAP^uy-MTv@tfPhNxHbg|K6hTPDhJt`nrADdJ5_*Rq
z2nbP--ih=QdI^w_WY)%W?%bJYo@eek^KZx&!@rZ|DJ3_fr?lLyq>d
zT$Cffw`_8j`6L;w)LvTI0oaN|NpP=vSU%dmq`iBnp3-EJi!27lC2p(F$X*Mr;YQQaycCLz$
zyNC}&ZU-I)@x}kjk8j!j*!vy*SAXk2eZ!B#&num`?$=cM7r*#FeMEWxLH_^r*MIfL
z50{`evg2gbn}2Twkgt1Qc}D)EV|fINA@~mPJD4e|H(Yt)2eeUxhb*aVykS
zPM6ys{MX+8KObQIn>pIY{{0o);I(6utcm6GewlyE4FBE;AFlELVFfoGfbvxRhDt~T
z{_T~NHHq8&FYTZIWd&KJVK+r@eAE2@@DcU}S6Tm^jr@-rxxc%-Uw-qBq$B^nIfFys
z`1enl;T&Gvf23+5+1@v4K{Hsuf;TU&A&sZon2J2#>>jS&P;cadXezb<6_
zH`C>Y-jt6a)d)2Itxas#MWGrI-*$c&jsf9lfUh>4c|Nan+i~0bNcug7hof_NApGtx
z&aZJuBd3?V^dkI0#0k-UB)$8iPoU~%CkUNmd%AlpmT?HPHunvnhY}2~^HHI6{8~kYCYMBLTfSN!yV;mz~
z%zwk3?fOwTz>l@bTfDh=4x)>`G}dZt?{AfOq#4(Nm(D5J2QIsOWp_CvK+E(NCnPO=
zUJf~!pV+YGjX2~;yYU)n+W@;^jLUL}t)=z$g!l>!Bjf3T8Jaf(nada^k9c0kU1wn}
zBkkSCi5Som+adGA^!`WX7YLc+x39>n0hX)Lq_0HtlEjF@tj9F#t0}f4O;wE4$oMy6
z+#IZx!;vBKQ~{PnlwsF5H)w@KZF8zZDj#_FPiJk6EOZx!MeKvJ~CLbfvwL
ze2?;+Qi)s(cI}?Ohw5&7?lM2)Lw{rpnpOD{sHt}R)@~dMHQqgg@)#CDE5L6tyH8vw
zgg7PW`fa``frZhaw8mh5NE?0N;Z#KUaR@%=4`A;-emWwxDfH}1fyH!j+IKE37SJhD
z^7sWhWc(gX8Yv*a4lwS2m~;Y@M?fog;bVZuv6UGnV`e2wfVooh?SN&}9)aR$V8BT`
z<{-ZyAfEZ1(^I<8I!B|<5~DudaJu3AHxO`YbESgH*)D_&dEAqpI4@L*NXzkoidf?~
z49-1iV3iOOOP5~}S~$2gSak5ZDPKGmSJtHWemR+0bf0h3DRBTRPJ4gg^b25io>eSG
zT49ecwV%ml^C9?SS~WEXj|sSseVLn!pWHj#u6rm>64PD~YJ)KiB3QXaOcT)aL0A?N
zt#A33Z}O=R)#`wJ>iTWQnKg(9Rk5>AM-@onqUu~C$SmrIk5|1>Ye$~`@nU`9T1qzk
zMqrQ$TVV{Zb4LFg-m^z4zK=HMFkE-a(zV(jvADtBOJvKjV&b8x`Uh5UM+=j@#j4c4
zm^zWlip=iIfd1?b*~5qy*f(H%@PCm5oyr%kC4>CopP=PPVo~99xUyKxcMzHCew9|%
zfR{ckzWS0+XK_unAr^#QNm~Lyr1bMM13x+f>iYu%w)VC@KKRjxJ{XYGhk>ta_D%v4
zXyz)GdB9`xob8j~AyUubd$rt{<%+Aey
z!jY18kZFmc8MbUSc>ph#dFU~`@oD?p#kA>SR*=Udm9Lg?x!Y!qL|BiQHg(zAbYa`J
z+eq75uZ>%yuJ0*vAx;p8X*R1N7;f75kfp*QmaZ&w8!{pFLKj}}l%eq=-pF&;y)`2Z
z&bzIbKA)f=L+6y2zXz_`*gZ2|>_Lde_2LzPg~-1R?AZ5c<|u|Sx?(1KdJ_sc7musL
z?~Hy|qhKS{qaoh!X=tQC>(YN;W24s+X`=Y};OEJ;RWLwK#JM>z4$tpU_*6Dj;r-ULT^uOXo&@HE
zK4F5^n-G-S3qy*j15Cu)gXa)Lt(oj>}|4MYP5Mw9M|RBnB(z;P(w)$txm)=K)(-YHxur
zsIPc8Hzd?JhjiOl4tAIIqQ}059klDw+6Pw5@xNPf*;2aQaMvlzhO?dbgZe-fX1U9u
zW3C-(Uw1W21^xl1(Qji=^K+C-gF;K`>=%cRLj~0@F9JCA$i$7g?U8z(&<z!J+T(ueHMZbKdwOKL*D`kk%+4*yE&mi_F;}2gT1O6-
z!mLZRS@oQ>F6ni4QokEU0)3{t=!ol9a)AkFGM&4&UZL6!S73+KDcF9VM%M3b3yRBYl~lW(CZ8N*!H5u$;%LJ8
z%GdJRw}$twN7l!X_A^WEt89OA-AOUeXNte>tbiD8e%NB0*|VuKj$;k|?!dO1Nr%l}
zh=CnrXHISFw?qn<^X&SAOgY^#r*F*B?!K*|)28$>
z7w%zav+PY{+WaqE@wAa;qpH|zFedEL%jBdnj1hhl3k1SOhkw7JBgFYb%S_v-I0kAh
zOIfSIzNh2jpa8FonFGNF_=A)rFZ!(YfyUf^(c7N>#J2vTx`kA)_i8au!GqDF5-N2+
z!}GK?Uip;-P`UyS(NPfVyYQiCLVZxV=F+`tPfBN!h~*+c8w!)=i%1nArK|(A5$2Q~
zMqx>@r#Gm$B-a#PI_v!Mg`2Jn_p3R7Ua(jHtO#jSe`g?67NgKL8X9VNz}vd!yp479
zb>pX>bzsuG124t$ZB=rxQ_!H6Iqhch^LN)2sieHMGRkSM7nOSu5-Xgtx~4g#J^Dtw
z<{DAEp5AEzG#$EWcX!yuAd302u&oK9V!PO4u&dGU^J$UlY=l42^1EX81w28LlDgdw
zn;5E+WP+ga*Vn9pUs5Wa4Vm1fPRCJ#mO;6#+50!G8`*UYfLO#WaI^#Z-lOH_*f#>Z
zRN2bi$=O)$t*u@|awb~2bsyB*Z5Q~^izAC$c^~g~y^YAk`9&1rbq||*hqbK=3wCmJ
z*Yp>O65`Ltp-uE(Ccmt#;xXqVSAgXChlqGBdXn&u+D{kvFy^YxOcmszYB}1^d^r{l
z&v=!_>u|qON!?QE4gK|=OduOuaWnvKFtl4wQL@8a^2BwXfXi
z*>r)@ajz5!7s_Cy{i?=Vaa3;)`)kL*U)$YplKf8PJb%7(-8RG`^+M>gTwgOEyVpvt
z3gtsVJFme?esxop-lT&?q@t($OyOt@nQIWt#80H#xfenMDth@BK`Qh6x0kyV_g|25
znx_x&5U!b=>Zuf66@W(1sRmK0l@LEE`Z^B(eD3d8vT_fU`Eg5kFYDb<$YeJ-50dPL
zVR`5>D_XO=m+`*xcJzwROe)ich`LT2Cx)*40-QZMH=UV78gWijmy5+zruvBvw)d+l
z)hV;d*f6Km3lT(S%3F%qaP5}_nDZF^xiZLh~`)3u0vBX!_zB36c{*=8ZDCXB#&;WjjHOfPn>t$ED
z&cEv418g^Mea>6!MISF|kgZ_CfoRc_k2s&?SO%z)2jCl@)^3%HFUq_bDwynt`FX0Q
zW2`ifAD6yX8}=*ev&)uQcFBVBX#YH9P`3#Kk-!IrA4HyOhs#C)p#ZW$qtj_7$;f+!%JEL(~Y
zj&&)xsK;Flr-UAx+J0+@h$*eiykUV*`r@$KnhU%nLRTB6%TB?4#IaTXb{VaArj0SI
z5XR6kUbGXv+=|9aqtipVGAE9K^%4-!Tc&4MRMOg!9%86_Cf6uI-a0Y|DhBGGt!S1t
z*lBB9h~8dtC+oNN7r_y7Q-zft!&R%cc2`4et2J5ERzpGzTEQ
z_DeB6w=f~o;x&Fcsml(K+%G!n)z9sB`y$~@PFb6;llCFBw%+z2;#l|Dmd9~l7ScD$
z*nC#N+j=-ji-BGn6bP`jZ`E9kEk}+m&pv%Aj_cfLN;Xy*d$Voyi_?>|jiiq%hYrZ~
z3|I9+0Pc~bEevpPcoZfC`oTc(Z`3Lq6QB
zICh`UotZd4)vq*flzwb@o<1yv312ImF{pn&-33sdUMfBwV=aN7&%c@|2h
z^I{sUU-X2Gp=lLYi%x%#50S!Bj*qS0hf43%cIcqRCl%3uS}HahL#`Fux*&5YU3a5S
zXvvM&*rsN64M`?~>pjC>Do4hxf+RWCU1R=!BPC3nps1Y>=+&#v!o2bGNQzK6jIU%|
zV~8$=iRaHaG}HC>cw2|4V(*371PQ*KB6=*wL6`>-9utNwmBAnU<>iS6O}Q8zjNsJ;QRQ>`NgqSGH(gkraEV
zYp0Ly)$07Lo4yn|U7S^c$c)wSu=9E>ZX{z8nGtc6#00i$UuuYQYlCnLg<-9$1KK?pjZ|cP88Hp=&tc`uW
zwZ&VZu#DP@?;-*P7LG!%y$CKe+O;55JNrr5$Dq%8fuWUt@;l`Qer!{r*~pp@_Yj@U
z3{wvm6CP8vdOW>QLFDn1n%}z}g?yXAp