Abstract
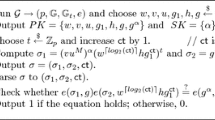
Schnorr’s identification and signature schemes [10], [11] are efficient, discrete log-based protocols. Moreover, preprocessing algorithms are proposed that significantly speed up the computations of the prover (resp. signer). Therefore, this preprocessing greatly enhances the suitability for implementation on a smart card. The preprocessing algorithms can be used for other (discrete log-based) signature schemes as well.
The security of the preprocessing depends on a parameterk; the required storage is linear ink. In [10] and [11] the valuek=8 is suggested, for which the level of security is conjectured to be 272 [11].
In this paper an attack on these preprocessing algorithms is presented. This attack retrieves the secret key in about (k!)2 steps, using in the order of\(\tfrac{1}{2}\sqrt {2\pi (k - 1)k!} \) consecutive signatures or transcripts of identifications. Fork=8, this amounts to about 231 steps and 700 signatures.
This attack is applicable to Brickell-McCurley, ElGamal, and DSS signatures as well, if the same preprocessing algorithm is used.
Article PDF
Similar content being viewed by others
Avoid common mistakes on your manuscript.
References
E. F. Brickell and K. S. McCurley, An interactive identification scheme based on discrete logarithms and factoring,Journal of Cryptology 5(1) (1992), 29–39.
D. Chaum, J.-H. Evertse, and J. van de Graaf, An improved protocol for demonstration possession of discrete logarithms and some generalizations,Advances in Cryptology—Proceedings of Eurocrypt '87 (D. Chaum and W. L. Price, eds.), Lecture Notes in Computer Science, vol. 304, Springer-Verlag, Berlin, 1988, pp. 127–141.
W. Diffie and M. E. Hellman, New directions in cryptography,IEEE Transactions on Information Theory 22(6) (1976), 644–654.
T. ElGamal, A public key cryptosystem and a signature scheme based on discrete logarithms,IEEE Transactions on Information Theory 31(4) (1985), 469–472.
U. Feige, A. Fiat, and A. Shamir, Zero knowledge proofs of identity,Journal of Cryptology 1(1) (1988), 77–95.
C. G. Günther, An identity-based key-exchange protocol,Advances in Cryptology—Proceedings of Eurocrypt '89 (J.-J. Quisquater and J. Vandewalle, eds.), Lecture Notes in Computer Science, vol. 434, Springer-Verlag, Berlin, 1990, pp. 29–37.
National Institute of Technology and Standards,Specifications for the Digital Signature Standard (DSS), Federal Information Processing Standards Publication XX, U.S. Department of Commerce, February 1, 1993.
J. J. Quisquater and L. S. Guillou, A practical zero-knowledge protocol fitted to security microprocessor minimizing both transmission and memory,Advances in Cryptology—Proceedings of Eurocrypt '88 (C. G. Günther, ed.), Lecture Notes in Computer Science, vol. 330, Springer-Verlag, Berlin, 1988, pp. 123–128.
P. de Rooij, On the security of the Schnorr scheme using preprocessing,Advances in Cryptology—Proceedings of Eurocrypt '91 (D. W. Davies, ed.), Lecture Notes in Computer Science, vol. 547, Springer-Verlag, Berlin, 1991, pp. 71–80.
C. P. Schnorr, Efficient identification and signatures for smart cards,Advances in Cryptology—Proceedings of Crypto '89 (G. Brassard, ed.), Lecture Notes in Computer Science, vol. 435, Springer-Verlag, Berlin, 1990, pp. 239–251.
C. P. Schnorr, Efficient signature generation by smart cards.Journal of Cryptology 4(3) (1991), 161–174.
Author information
Authors and Affiliations
Additional information
Communicated by Ivan B. Damg»rd
Rights and permissions
About this article
Cite this article
de Rooij, P. On Schnorr’s preprocessing for digital signature schemes. J. Cryptology 10, 1–16 (1997). https://doi.org/10.1007/s001459900016
Received:
Revised:
Issue Date:
DOI: https://doi.org/10.1007/s001459900016