0 ratings0% found this document useful (0 votes)
103 viewsPractical Ethical Hacking Course Outlines by Mohamed Fadel
Practical Ethical Hacking Course Outlines by Mohamed Fadel
Uploaded by
Mohamed Fadel KhaledThe document outlines a course on practical professional ethical hacking. It covers topics such as reconnaissance and information gathering, scanning networks and systems, network security, web application penetration testing, reverse engineering, exploit development, post-exploitation techniques, Windows hacking, password cracking, wireless cracking, and practice with vulnerable virtual machines. The goal is to teach ethical hacking techniques while maintaining ethical and legal practices.
Copyright:
© All Rights Reserved
Practical Ethical Hacking Course Outlines by Mohamed Fadel
Practical Ethical Hacking Course Outlines by Mohamed Fadel
Uploaded by
Mohamed Fadel Khaled0 ratings0% found this document useful (0 votes)
103 views3 pagesThe document outlines a course on practical professional ethical hacking. It covers topics such as reconnaissance and information gathering, scanning networks and systems, network security, web application penetration testing, reverse engineering, exploit development, post-exploitation techniques, Windows hacking, password cracking, wireless cracking, and practice with vulnerable virtual machines. The goal is to teach ethical hacking techniques while maintaining ethical and legal practices.
Original Description:
Practical Ethical Hacking Course Outlines By Eng. Mohamed Fadel
Copyright
© © All Rights Reserved
Share this document
Did you find this document useful?
Is this content inappropriate?
The document outlines a course on practical professional ethical hacking. It covers topics such as reconnaissance and information gathering, scanning networks and systems, network security, web application penetration testing, reverse engineering, exploit development, post-exploitation techniques, Windows hacking, password cracking, wireless cracking, and practice with vulnerable virtual machines. The goal is to teach ethical hacking techniques while maintaining ethical and legal practices.
Copyright:
© All Rights Reserved
0 ratings0% found this document useful (0 votes)
103 views3 pagesPractical Ethical Hacking Course Outlines by Mohamed Fadel
Practical Ethical Hacking Course Outlines by Mohamed Fadel
Uploaded by
Mohamed Fadel KhaledThe document outlines a course on practical professional ethical hacking. It covers topics such as reconnaissance and information gathering, scanning networks and systems, network security, web application penetration testing, reverse engineering, exploit development, post-exploitation techniques, Windows hacking, password cracking, wireless cracking, and practice with vulnerable virtual machines. The goal is to teach ethical hacking techniques while maintaining ethical and legal practices.
Copyright:
© All Rights Reserved
You are on page 1of 3
By Eng.
Mohamed Fadel
Practical Professional Ethical Hacking
• Introduction
• Theory and History
• Hacking vs Penetration Testing vs Red Teaming vs Vulnerability assessments
• Certifications
• Getting Started
o Network Basics
o Systems Basics
o Linux Basics
o Virtual Machines
o VMware vs VirtualBox
o Installing Kali Linux
o Linux Commands
o Bash Scripting Basics
• Reconnaissance an Information Gathering.
o Domain Harvesting
o WAF detection
o Google Hacking
o Enumeration and Mapping
o Open Source Intelligence
o Wireshark
• Scanning
o Port Scanning using NMAP
o Stealth Scans using NMAP
o Service Scanning using NMAP
o Vulnerability Scanning using Nessus and Nikto
• Network Security
o Sniffing using Wireshark
o Man in The Middle Attack
o Metasploit Framework
o Payload Creation using MSFvenom
o Reverse Shell and Bind Shell
o Exploiting Shellshock and Eternal Blue vulnerabilities
o Exploiting shares
• Web Applications Theory
By Eng. Mohamed Fadel
By Eng. Mohamed Fadel
• Web Application Penetration Testing
o Encoding vs Encryption vs Hashing vs Obfuscation
o HTTPS and Certificates overview
o Intercepting Proxy
o Burp Suite
o DVWA
o Lost? Then Let’s Recap
o Brute Force Using Burp Suite and Python
o Command Injection vulnerability
o Reflected and Stored XSS (Cross Site Scripting)
o CSRF (Cross Site Request Forgery)
o Steal cookies using BeeF
o File Upload vulnerability
o Error Based SQL Injection vulnerability
o Blind SQL Injection vulnerability
o File Inclusion vulnerability
• Learning Reverse Engineering
o Introduction to x86 Architecture (32bit architecture)
o Studying CPU
o Assembly Concepts
o Debugging and disassembly
• Learning Exploit Development
o What is Buffer Overflow?
o Windows 32bit Stack Based Buffer Overflow
o Immunity debugger
o Overwriting EIP
o Locating Bad Characters
o Endianness
o Local Exploitation of Windows Stack Based Buffer Overflow
o Remote Exploitation Windows Stack Based Buffer Overflow
o Linux 32bit Stack Based Buffer Overflow
o GNU Debugger
o DEP and ASLR
o Stack Canary and SafeSEH
• POST Exploitation
o Maintain Access
By Eng. Mohamed Fadel
By Eng. Mohamed Fadel
o Local Privilege Escalation
• Windows Hacking
o Active Directory
o Active Directory Enumeration
o Active Directory Authentication
o PowerShell for Enumeration
• Password Cracking
o Service Brute Force via Hydra
o John the Ripper Tool
• Wireless Cracking
o WEP
o WPA/WPA2
• Practice
o Solving Vulnhub machines!!
• Bug Hunting
• What now?
By Eng. Mohamed Fadel
You might also like
- 1 - 6th BMS Learning SyllabusDocument19 pages1 - 6th BMS Learning Syllabusviv.san1984No ratings yet
- Advanced Hacking TrainingDocument33 pagesAdvanced Hacking Trainingnanoblack88No ratings yet
- DCSC TopicsDocument7 pagesDCSC TopicsCE29Smit BhanushaliNo ratings yet
- Network Pentest Course 1692353982Document10 pagesNetwork Pentest Course 1692353982zulkufcetinNo ratings yet
- Powered by Ignite Technologies: Network Penetration TestingDocument9 pagesPowered by Ignite Technologies: Network Penetration TestingrberrospiNo ratings yet
- Network Pentest CourseDocument10 pagesNetwork Pentest Coursess1391161No ratings yet
- Red Team Course Content v1Document14 pagesRed Team Course Content v1happyfeet dashNo ratings yet
- Session 3Document63 pagesSession 3crazythings246No ratings yet
- Cise & CehDocument33 pagesCise & CehBalaji PaskantiNo ratings yet
- 07 - ScanningDocument16 pages07 - Scanningyeni nyimpen dataNo ratings yet
- VPN Rce's PDFDocument122 pagesVPN Rce's PDFAman MahendraNo ratings yet
- Ethical HackingDocument9 pagesEthical HackingobedNo ratings yet
- Hacking Phones From 2013 To 2016 (PDFDrive)Document64 pagesHacking Phones From 2013 To 2016 (PDFDrive)ramelNo ratings yet
- Thick Client Pentesting The-HackersMeetup Version1.0pptxDocument32 pagesThick Client Pentesting The-HackersMeetup Version1.0pptxProject Manager InvesicsNo ratings yet
- Fundamental Cyber Security TrainingDocument9 pagesFundamental Cyber Security TrainingKenjie SamaNo ratings yet
- Fundamental Cyber Security TrainingDocument9 pagesFundamental Cyber Security TrainingYılmazDeğirmenciNo ratings yet
- Advance Penetration Testing Kali Linux TrainingDocument4 pagesAdvance Penetration Testing Kali Linux TrainingReccio0% (1)
- Cise Level 2 - Exploit WritingDocument3 pagesCise Level 2 - Exploit WritingInnobuzz HRNo ratings yet
- Malware PDFDocument57 pagesMalware PDFgkpalokNo ratings yet
- Cisco RopDocument48 pagesCisco RopmzxbclNo ratings yet
- Windows & Training CenterDocument6 pagesWindows & Training CenterrearNo ratings yet
- Burpsuite Essential ContentDocument6 pagesBurpsuite Essential ContentAaron PreyNo ratings yet
- Burpsuite Essential Content 2Document6 pagesBurpsuite Essential Content 2Aaron Prey100% (1)
- All in One Ceh PDFDocument157 pagesAll in One Ceh PDFswarterrorNo ratings yet
- n10-008-19 - Applying Network Hardening TechniquesDocument26 pagesn10-008-19 - Applying Network Hardening TechniquesAdriani De Sa SierraNo ratings yet
- Roadmap AWS Course - 1Document1 pageRoadmap AWS Course - 1Samuel Alam RickyNo ratings yet
- Hack2Secure Web Application Security Testing Workshop LiveOnlineDocument5 pagesHack2Secure Web Application Security Testing Workshop LiveOnlineAnonymous Rp4du2No ratings yet
- Chapter 02 - Information Gathering - HandoutDocument104 pagesChapter 02 - Information Gathering - HandoutWayne WayneNo ratings yet
- Professional Ethical Hacker Course Outline: Module 00 - Setup LabDocument10 pagesProfessional Ethical Hacker Course Outline: Module 00 - Setup LabNaàmi SamiNo ratings yet
- Pentesting CourseDocument4 pagesPentesting CourseRayyan SayyedNo ratings yet
- Recon MTL 2017 MazewalkerDocument48 pagesRecon MTL 2017 MazewalkerpaulNo ratings yet
- Analyzing and Reverse Engineering Antivirus SignatureDocument154 pagesAnalyzing and Reverse Engineering Antivirus SignaturenicolasvNo ratings yet
- CEH Exam Blueprint v4.0: EC-CouncilDocument5 pagesCEH Exam Blueprint v4.0: EC-CouncilGustavoBuschNo ratings yet
- CEH Exam Blueprint v4.0: EC-CouncilDocument10 pagesCEH Exam Blueprint v4.0: EC-CouncilAnderson SilvaNo ratings yet
- Session HijackingDocument13 pagesSession HijackingHaneesha ReddyNo ratings yet
- Hacking Training ModuleDocument15 pagesHacking Training ModuleCharith MadusankaNo ratings yet
- Ethical Hacking: Presented By: CYBER SHIELDDocument19 pagesEthical Hacking: Presented By: CYBER SHIELDHaval AbdulkarimNo ratings yet
- Application Hacking Though The Eyes of An AttackerDocument32 pagesApplication Hacking Though The Eyes of An AttackerKurt McLarenNo ratings yet
- Cyber SecurityDocument18 pagesCyber Securitypostbox.bankinggNo ratings yet
- UrviShrivastava (8 0) PDFDocument3 pagesUrviShrivastava (8 0) PDFswaroopa RaniNo ratings yet
- Cybersecurity Zero To Hero With Cyberchef: Jonathan GlassDocument59 pagesCybersecurity Zero To Hero With Cyberchef: Jonathan GlassAb DouNo ratings yet
- Cyber Security Curriculum Quantum Learnings 2020Document2 pagesCyber Security Curriculum Quantum Learnings 2020DhruveeNo ratings yet
- ch02 SWDocument33 pagesch02 SWNam NguyenNo ratings yet
- OK S02 Zoltan Balazs Sandbox Mapping BotconfDocument35 pagesOK S02 Zoltan Balazs Sandbox Mapping BotconfrealalienrealNo ratings yet
- Sourcefire BRKSEC-1030Document112 pagesSourcefire BRKSEC-1030Raja AthiNo ratings yet
- Docker Kubernetes Training ScheduleDocument2 pagesDocker Kubernetes Training Schedulechandrashekar_ganesanNo ratings yet
- Kali Linux For Learning Hands On Security: The Quieter You Become, The More You Can HearDocument21 pagesKali Linux For Learning Hands On Security: The Quieter You Become, The More You Can HearNIckNo ratings yet
- T1-001 IPv6 SecurityDocument36 pagesT1-001 IPv6 Securityธนวรรณ โภคาอนนต์No ratings yet
- Becoming The Hacker - Adrian PruteanuDocument405 pagesBecoming The Hacker - Adrian PruteanuValber OliveiraNo ratings yet
- Some Topics: - Exponential Tricks - Denial-Of-Service Attacks (No Time For It Today)Document7 pagesSome Topics: - Exponential Tricks - Denial-Of-Service Attacks (No Time For It Today)postscriptNo ratings yet
- Dynamic Malware Analysis Workshop: Counterfeiting The Pipes With FakenetDocument50 pagesDynamic Malware Analysis Workshop: Counterfeiting The Pipes With FakenetirshadNo ratings yet
- SOAP UI On Demand Videos SyllabusDocument6 pagesSOAP UI On Demand Videos SyllabusashfaqdhanakwalaNo ratings yet
- Report Po Price BreakupDocument8 pagesReport Po Price BreakupLavanyaNo ratings yet
- IPv6Security SlidesDocument191 pagesIPv6Security SlidesConcha SolerNo ratings yet
- Kali Linux Course RequirementsDocument4 pagesKali Linux Course Requirementsمیاں حمدانNo ratings yet
- The Future of Exploitation SlidesDocument48 pagesThe Future of Exploitation SlidesDan Antoche-AlbişorNo ratings yet
- Ethical Hacking Master ClassesDocument24 pagesEthical Hacking Master ClassesDeku IgniteNo ratings yet
- Web Penetration Testing with Kali Linux - Second EditionFrom EverandWeb Penetration Testing with Kali Linux - Second EditionNo ratings yet
- AD162186401538en GB0501Document2 pagesAD162186401538en GB0501EKNo ratings yet
- Electrical Systems and Power Electronics For Aircraft ApplicationsDocument16 pagesElectrical Systems and Power Electronics For Aircraft ApplicationsJulian ManiboNo ratings yet
- NewStudioNPVS Brochure 220726 EN FINALDocument2 pagesNewStudioNPVS Brochure 220726 EN FINALmining engineerNo ratings yet
- ARM Assembly Language Programming: OutlineDocument36 pagesARM Assembly Language Programming: OutlineSlim ShadyNo ratings yet
- Flownex ModulesBrochureDocument4 pagesFlownex ModulesBrochureSrashmiNo ratings yet
- CCP Signals & SystemsDocument7 pagesCCP Signals & Systemssagar manjrekarNo ratings yet
- 70mai Dashcam M200 (Magyar Kézikönyv)Document45 pages70mai Dashcam M200 (Magyar Kézikönyv)kovacsg.markNo ratings yet
- Oracle E-Business Suite Performance Guide (Doc ID 1672174.1)Document44 pagesOracle E-Business Suite Performance Guide (Doc ID 1672174.1)SaurabhNo ratings yet
- Host Lh750 PDFDocument114 pagesHost Lh750 PDFReynaldo MacarioNo ratings yet
- Reference UnbalancedDocument30 pagesReference UnbalancedVictor Luiz MerlinNo ratings yet
- Cube QuickCall Client API PDFDocument28 pagesCube QuickCall Client API PDFParag KapoorNo ratings yet
- No Des 3Document2 pagesNo Des 3pedjaNo ratings yet
- WhatsappDocument13 pagesWhatsappjbhamar100% (3)
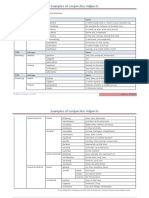
- Examples of Conjunctive Adjuncts: Type Sub-Type ItemsDocument2 pagesExamples of Conjunctive Adjuncts: Type Sub-Type Itemsmkss11_kli053100% (2)
- BTC Autopilot MethodDocument4 pagesBTC Autopilot MethodlittlemeNo ratings yet
- THE THE: Sapphirean's Sapphirean'sDocument6 pagesTHE THE: Sapphirean's Sapphirean'sLynux Lewis DoteNo ratings yet
- Induction Generator in Wind Power Systems: Yu ZouDocument44 pagesInduction Generator in Wind Power Systems: Yu ZouSherif M. DabourNo ratings yet
- An Introduction To Programming For Medical Image Analysis With The Visualization Toolkit Version 2 (Updated For VTK 5.2)Document283 pagesAn Introduction To Programming For Medical Image Analysis With The Visualization Toolkit Version 2 (Updated For VTK 5.2)Chih-Yao HsiehNo ratings yet
- KB5060Document2 pagesKB5060Thug FamilyNo ratings yet
- Homework Set No. 5, Numerical Computation: 1. Bisection MethodDocument4 pagesHomework Set No. 5, Numerical Computation: 1. Bisection MethodkelbmutsNo ratings yet
- Chapter 6 The Impact of ICT in TrainingDocument5 pagesChapter 6 The Impact of ICT in TrainingTs. Dr. Zulkifli Mohd SidiNo ratings yet
- SM N900 Tshoo 7Document76 pagesSM N900 Tshoo 7pkpgkh100% (1)
- Gates Belt DriveDocument70 pagesGates Belt Drivehardcore78No ratings yet
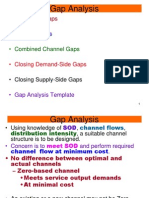
- Gap Analysis: - Sources of GapsDocument19 pagesGap Analysis: - Sources of GapsBloomingdale Uttara100% (1)
- Viza Travel Sponsorship Proposal 1Document13 pagesViza Travel Sponsorship Proposal 1api-312675890No ratings yet
- IC8451-2M - by WWW - EasyEngineering.net 1 PDFDocument12 pagesIC8451-2M - by WWW - EasyEngineering.net 1 PDFSuryaNo ratings yet
- Mum FNF - Google SearchDocument1 pageMum FNF - Google SearchSammy WilliamsNo ratings yet
- Implementation of Milkrun in An Automobile Manufacturing Industry IJERTV3IS061232Document6 pagesImplementation of Milkrun in An Automobile Manufacturing Industry IJERTV3IS061232Soufiane AbdellaouiNo ratings yet