A Customizable Dropper Tool targeting Windows.
- BlackHat Asia, 2024 - Call For Tools
- BlackHat USA, 2024 - Call For Tools
- BlackHat SecTor, 2024 - Call For Tools
- Thanks a lot to Soumyadeep Da aka @SoumyadeepBas12 for encouraging me to apply for these conferences, else I wouldn't have done it :)
- Thanks a lot to Faran aka @Chrollo_l33t for helping me to create the Slides and PPT for the presentation for this tool :)
- Indirect Dynamic Syscall. (MITRE ATT&CK TTP: T1106)
- SSN + Syscall address sorting via Modified TartarusGate approach
- Remote Process Injection via APC Early Bird to CUT OFF telemetry Catching by EDR. (MITRE ATT&CK TTP: T1055.004)
- Spawns a sacrificial Process as the target process, not disrupting already open processes in the environment.
- ACG(Arbitrary Code Guard)/BlockDll mitigation policy on spawned sacrificial process.
- PPID spoofing (MITRE ATT&CK TTP: T1134.004)
- Api and Dll resolving from TIB (Directly via offset (from TIB) -> TEB -> PEB -> resolve Nt Api) (MITRE ATT&CK TTP: T1106)
- Cursed Nt API hashing (MITRE ATT&CK ID: S0574)
- Disables Event Log via killing EventLog Service Threads (MITRE ATT&CK TTP: T1562.002)
Disadv: If threads are resumed, all events that occurred during the suspension of Event Logger, get logged Again!
So, thought of killing them instead!
"It's more Invasive than suspension, but the decision is always up to the operator. Besides, killing threads get logged on the kernel level" - @SEKTOR7net
While Killing only those threads in the indirect syscall implant, was facing an error. I was unable to get the "eventlog" SubProcessTag Value. So thought of killing all threads, i.e. killing the whole process (responsible svchost.exe). Yeah creating an IOC!.
Directly via VS compiler:
Also add /MT compiler flag! => To statically links CRT functions together in a binary (Yeah, U guessed it, it bloats the implant)
- Also via compile.bat (prefer option 1.)
./compile.bat
PS C:> .\x64\Release\indirect.exe
[!] Wrong!
[->] Syntax: .\x64\Release\indirect.exe <PPID to spoof>
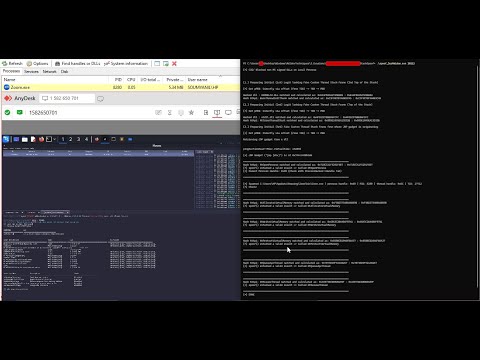
DarkWidow.mp4
- PPID spoofing (Emotet method)
- Much Stealthier Use Case of EventLog Disabling!
-
TIB:
-
GS and FS register:
-
PEB LDR structure:
-
TIB -> TEB -> PEB -> Resolve Nt API and API hashing
-
https://stackoverflow.com/questions/41277888/iterating-over-peb-dllname-shows-only-exe-name
-
https://doxygen.reactos.org/d7/d55/ldrapi_8c_source.html#l01124
-
labs.cognisys.group, a blog by @D1rkMtr
-
A pic of the snippet from the above link, which I used here to resolve API dynamically without HardCoding Offsets:

-
The Api hashing code that I applied:
-
#include <stdint.h>
#include <stdio.h>
#include <Windows.h>
DWORD64 djb2(const char* str)
{
DWORD64 dwHash = 0x7734773477347734;
int c;
while (c = *str++)
dwHash = ((dwHash << 0x5) + dwHash) + c;
return dwHash;
}
int main(int argc, char** argv)
{
if (argc < 2)
{
printf("[!] Wrong!\n");
printf("[->] Syntax: .\\%s <NTFuncName>\n\n", argv[0]);
return 1;
}
const char* string = argv[1];
DWORD64 hashvalue = djb2(string);
printf("Hash Value: 0x%llX\n", hashvalue);
return 0;
}
-
ACG(Arbitrary Code Guard)/BlockDll mitigation policy:
- links:
- Protecting Your Malware by @xpn
- Wraith by @winterknife
- spawn and HOLLOW by @0xBoku

-
PPID Spoofing Detection:
- PPID Spoofing Detect by @spotheplanet
- If got time, I will be adding a detection Portion to this portion! -> [Remaining..............................................!]
-
Moneta Detection and PESieve Detection:\
-
How Thread Stack Looks of the Implant Process:
| Implant Process | Legit Cmd process |
|---|---|
 |
 |
It follows that by executing the return instruction in the memory of the ntdll.dll in the indirect syscall POC, the return address can be successfully spoofed, the ntdll.dll can be placed at the top of the call stack and the EDR will interpret a higher legitimacy. - @VirtualAllocEx from DirectSyscall Vs Indirect Syscall
Also thanks to, @peterwintrsmith!
- Instrumentation CallBack Evasion: Used this POC - syscall-detect by winternl_t
- EventLogger Config, I used:
-
Killing Event Log Threads:
- rto-win-evasion by @SEKTOR7net
- Phant0m by @hlldz
- Goblin by @winterknife
- disabling-windows-event-logs-by-suspending-eventlog-service-threads by @spotheplanet
From here:

To here:

- This Method, Ended up causing errors in indirect syscall implementation. So, I ended up killing all those threads present within responsible svchost.exe (reason: Go up).
- Case 1: When Darkwidow executed under normal privilege
No Critical Alerts gets created except One Low Severity Log!
- Case 2: When Darkwidow executed under Admin privilege
One Low Severity Log => APC Injection (Like Before)
Another one which is a Medium Severity Log occured for setting
SeDebugPrivilege.
To get around this Event Logging Detection, I added the concept of Synthetic Frame Thread Stack Spoofing into it.
This is how stack looks after applying synthetic frame thread stack spoofing.
This is the NT api Thread Stack
This is the shellcode (btw, this is not custom made, this is Havoc Shellcode :)) thread stack.
For shellcode development, I have used havoc and this below configuration:
Newly Created Thread Start Address Spoofing was not really required in this project cause within APC Injection technique, APC hijacks the execution of an already and legit running thread. Thanks to @C5pider!
Now Status On Event Logs ?
No logs got generated. I also have removed the Event Logger Killing part from the DarkWidow V2, which decreases down the Event generation too!
- Porting this version to C++ Clang Compiler, which would help us to perform LLVM obfuscation.
- Upgrading to NtCreateUserProcess() to perform indirect syscall and stack spoofing.
- Applying Manual Load Library capability for bypassing Image Load Kernel Callbacks.
- Applying Module Stomping capability.
- Encrypted shellcode Injection to avoid Kernel triggered memory scans (Caro-Kann).
- @SEKTOR7net
- @peterwintrsmith
- @Jean_Maes_1994
- @D1rkMtr
- @spotheplanet
- @0xBoku
- @Sh0ckFR
- @winterknife
- @monnappa22
- @xpn
- @hlldz
- @d_tranman�
- @SoumyadeepBas12
- @jack_halon
- @KlezVirus
- @C5pider
I hope I didn't miss someone!