Towards a Model for Quantitative Reasoning
in Cognitive Nodes
Christian Facchini, Fabrizio Granelli
Department of Engineering and Computer Science (DISI) – University of Trento
Via Sommarive 14, I-38123 Trento, Italy
Email: {facchini,granelli}@disi.unitn.it
Abstract—Cognitive networks are proposed in the framework
of evolution of network architectures as novel paradigms to
provide autonomous in-network reasoning to support end-toend goals. While several approaches are available that propose
different approaches, still the problem of reasoning represents a
challenging issue. The paper aims at proposing a mathematical
model, based on fuzzy cognitive maps, to support and provide
a quantitative tool for implementing reasoning in nodes of
a cognitive network. In particular, the idea is to provide a
methodology to enable network nodes to represent the complex
interactions that happen within their protocol stacks and across
the network. The potential utility of the proposed scheme is
then preliminarily validated on a sample scenario, outlining good
results and relevant potential for future developments.
Index Terms—cognitive networks, network modeling, crosslayer modeling
I. I NTRODUCTION
Following the current evolution of communication networks,
the Future Internet is expected to become service-oriented
and to provide support for a wide variety of applications,
ranging from browsing and data transfer to more complex
and interactive applications that go far beyond the tripleplay service vision—e.g. data, voice and video—and including
augmented and virtual reality interactions, HDTV broadcasting
and video on demand, online gaming experience, etc.
However, different services are characterized by different
quality constraints on the communications infrastructure, yet
bound to the rigid layered architecture designed in the ’70s.
In such framework, performance assurance and optimization
represents a hard task, due to the fact that each protocol is
designed to work with different goals and without being aware
of the behavior of the other protocols either in the network as
well as within the same node.
Indeed, interactions among protocols at different layers
of the protocol stack can potentially jeopardize the overall
performance, and are difficult to quantify, foresee and control.
It is clear that single layer optimization does not represent a
suitable approach to provide controlled quality (being performance dependent on the interaction of all layers). Moreover,
cross-layering (as it is usually found in the literature) is not
going to be the ultimate solution, since it is often “static” and
This work has been partially supported by the Italian National Project:
Wireless multiplatfOrm mimo active access netwoRks for QoS-demanding
muLtimedia Delivery (WORLD), under grant number 2007R989S
focused on specific objectives, not considering the dynamics of
the networking infrastructure but also the variable and evolving
needs of the user applications and services.
In addition to ”internal” interactions described above, performance is heavily influenced by the complex interactions
among network elements (end-systems, routers, etc.), requiring
proper coordination of devices along the data path to support
QoS constraints.
Clearly, the need for suitable architectures to provide endto-end service-oriented performance control and optimization
is emerging as a central point in the design of the Future
Internet.
To this aim, a new networking paradigm has been recently
proposed in the literature, i.e. “cognitive networking” [1].
Cognitive networks are composed of intelligent nodes, capable
of reasoning about the environment they live in and acting in
order to meet a global end-to-end goal, while continuously
learning about the operating context and consequences of its
actions. Cognition should enable to reduce the complexity
of management of the network by supporting its dynamic
adaptation and self-configuration in order to support the timevarying requests of the users.
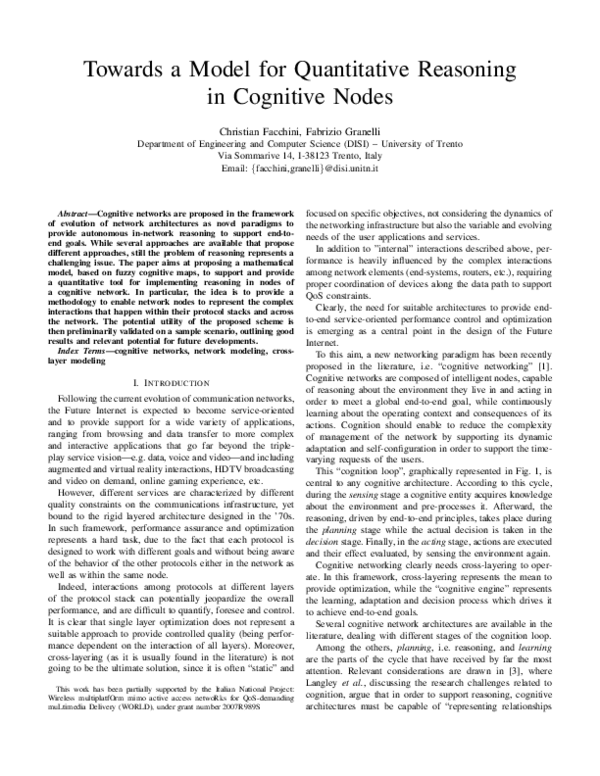
This “cognition loop”, graphically represented in Fig. 1, is
central to any cognitive architecture. According to this cycle,
during the sensing stage a cognitive entity acquires knowledge
about the environment and pre-processes it. Afterward, the
reasoning, driven by end-to-end principles, takes place during
the planning stage while the actual decision is taken in the
decision stage. Finally, in the acting stage, actions are executed
and their effect evaluated, by sensing the environment again.
Cognitive networking clearly needs cross-layering to operate. In this framework, cross-layering represents the mean to
provide optimization, while the “cognitive engine” represents
the learning, adaptation and decision process which drives it
to achieve end-to-end goals.
Several cognitive network architectures are available in the
literature, dealing with different stages of the cognition loop.
Among the others, planning, i.e. reasoning, and learning
are the parts of the cycle that have received by far the most
attention. Relevant considerations are drawn in [3], where
Langley et al., discussing the research challenges related to
cognition, argue that in order to support reasoning, cognitive
architectures must be capable of “representing relationships
�Sense
Env.
Plan
Learn
Act
Fig. 1.
Decide
The cognition loop (adapted from [2])
among beliefs”. In the authors’ opinion, such skill can be
developed by means of tools like Bayesian networks, neural
networks, and first order logic. A more practical perspective is
provided by Thomas et al. [1], who list some other machine
learning algorithms apt to be used for the reasoning process,
such as genetic algorithms, learning automata, and expert
systems. However, rather than giving some indications about
which particular technique should be used, they offer two
insightful guidelines: (i) they suggest that the choice of the
right technique (or techniques) largely depends on the problem
to be solved, and (ii) whatever the algorithm chosen, it needs
to converge before environmental conditions change. Also in
[4], the authors advance the idea that more than one reasoning
technique could be selected for a particular situation and
propose to equip cognitive networks with a whole set of tools,
rather than just a single tool. However, no explicit mention
is given on how to build such a set of tools. A remarkable
approach is provided in [5], where the use of fuzzy logic is
motivated by the idea of reproducing the way human beings
reason.
As correctly summarized in [2], the techniques used in
cognitive networks for reasoning purposes are limited in
number and often not justified over other available alternatives.
In addition, it appears that the cognitive networks proposed in
the literature, when addressing the reasoning problem, do not
explicitly consider cross-layer relations.
In this framework, the paper introduces the usage of graphlike structures, commonly known as fuzzy cognitive maps, to
explicitly represent cross-layer and network-wide interactions,
and use such information as a base for the reasoning process.
The remainder of this paper is organized as follows. We
begin Section II by describing the basics of fuzzy cognitive
maps. In Section III we analyze how this tool can be employed
to foster reasoning in a cognitive network node. Section IV
presents a possible application of FCMs in a cognitive node.
Finally, we draw our conclusions in Section V.
II. F UZZY C OGNITIVE M APS
Fuzzy cognitive maps (FCMs) were conceived in 1986 by
Kosko [6] as a means for modeling (possibly dynamical)
systems through the causal relationships that characterize
them.
Graphically, an FCM is rendered as a direct graph, in which
a node represents a generic concept (e.g. an event or a process)
and edges between any two concepts mean that there is a
causal relation between them, the cause being the node from
which the arrow starts.
Nodes and edges can in principle be fuzzy, in that they may
take any value in the continuous sets [0, 1] and [−1, 1], in order.
However, it is often the case that FCMs have both concepts
and edges in the discrete sets {0, 1} and {−1, 0, 1}. Such
maps are better known as simple FCMs and are particularly
convenient for outlining quickly the behavior of a model. A
zero-valued concept denotes that the concept is ‘off’, ‘inactive’
or in a ‘low’-state, whereas a concept set to one means the
opposite. As for edges, a null value indicates that there is
no causal relation whatsoever, whereas positive and negative
values reveal a positive and a negative causality, respectively.
Also, no concept can cause itself, hence edges leaving and
entering the same node cannot exist.
The state of a system having n distinct concepts is a vector
of dimensions 1-by-n. In the inference process, this vector
is repeatedly multiplied by the FCM matrix and the result
thresholded each time, until it converges either to a fixed point
or to a limit cycle. Most notably, inference is guaranteed to
converge to either one of the two cases if concepts take value
in any finite discrete set [7].
FCMs have some strong points that make them favorable
when compared to other reasoning formalisms. With respect
to Bayesian networks, FCMs are more powerful, for they
allow for the presence of feedback loops. Although this
restrains us from using the inference techniques applicable
in loop-free structures, is not a major problem thanks to the
straightforward inference method peculiar to FCMs (based on
just multiplication and thresholding operations). Furthermore,
it may be questioned that also other techniques exists that can
approximate any dynamic system, such as neural networks.
However, in a neural network trained to model a particular
system, its inner configuration does not reproduce faithfully
the relationships occurring among the entities the system is
composed of. Conversely, FCMs rely on the causal relationships tying together system internals.
Another considerable advantage is the possibility of merging
together multiple FCMs: the combined FCM is a (possibly
weighted) sum of the original FCMs. This has its roots in the
primary purpose for which FCMs were created: to allow experts to represent their causal knowledge about some situation.
Different experts, however, may have different opinions about
the same matter, and thus may encode differently their beliefs,
hence drawing conflicting FCMs. Merging helps to smooth
discrepant biases and weights can be employed to give more
or less credit to each expert.
However, there exist some disadvantages as well. One
major drawback concerns the automatic synthesis of FCMs:
as pointed out in [8], inferring causality between events based
on observational data (without any a priori knowledge) is
�not immediate and it differs substantially from the process
of inferring a simple correlation. Another drawback regards
abductive reasoning, i.e. the process of stating which causes
are responsible for a given effect: such a task is shown to be
NP-hard [9].
Despite such problems, FCMs have been used in different
domains for many different purposes, including for instance
the creation of medical decision support systems [10] and the
simulation of virtual words [11]. The interested reader can find
a more thorough survey in [12].
III. F UZZY C OGNITIVE M APS FOR C OGNITIVE N ODES
FCMs represent a suitable model for dynamic systems and
can also represent (or embed) cross-layer and network-wide
interactions, thereby enabling a truly holistic approach to the
problem of cognition in intelligent networks. Moreover, FCMs
have an inherent mergeable property: potentially, combining
several FCMs allows to exchange knowledge.
The following paragraphs discuss issues related to the usage
of FCMs to support reasoning in cognitive nodes.
A. Reasoning
The purpose of a cognitive network is to enable end-to-end
performance optimization. As performance depends on several
interacting factors and parameters associated to different layers
of the protocol stack, the focus of the present work is on crosslayer interactions.
In this scenario, it appears logic to map concepts to communication protocol internals. To this end, we propose to
distinguish three classes of concepts. A first class comprises
the concepts related to quality-of-service metrics the system
pursues; concepts in this class may be ‘throughput’ and ‘endto-end delay’. A second class of concepts includes all the
concepts related to the environment in which the cognitive
entity is; concepts such as ‘bad channel conditions’ and
‘congestion’ belong to this category. A third class includes
the set of actions (or a subset) that each protocol can perform;
concepts like ‘use of RTS/CTS’ and ‘fragmentation’.
Mathematically, the system state vector s is composed of
three sub-vectors representing the three classes discussed before (q, e, a). This representation allows for the reformulation
of the tenets introduced in [1]: the FCM needs to converge
to a solution state s∗ = (q, e, a∗ ) by finding a vector a∗
such that the constraints expressed by q are satisfied before
environmental conditions e change.
This means that the FCM is used to find which causes
generate a specific effect, or in more general words, to perform
abductive reasoning [3], which, as previously mentioned, is
shown to be a NP-hard problem [9]. However, this issue can
be mitigated, by noticing that the search space is reduced: only
the elements of a∗ are to be found, since both q and e are
given. Furthermore, as the cognitive node gains experience,
a parallel module could be employed to keep track of the
most likely combinations of a∗ , so that they can be evaluated
according to their probability. However, this issue is out of
scope of the paper and will be considered in future work on
the topic.
Another issue deals with the domain concepts are mapped
to. To begin, it is worth noting that the domain of some
concepts is clearly binary. For instance ‘fragmentation’ is a
dichotomy: either it is used or it is not. No other situation is
acceptable.
However, other concepts may not be well mapped to binary
sets. Let us suppose we want to use the concept ‘TCP
congestion window’. Clearly it is not possible to identify
situations where congestion window is used and situations
where it is not. Also, modeling situations in which the
congestion window is increasing or non-increasing may be
not precise enough. Rather, situations in which the congestion
window increases, decreases or remains stable are undoubtedly
more realistic. Such concepts may be expressed effectively by
trivalent variables, taking values in the set {−1, 0, 1} [7].
This reasoning can be extended even further, by taking into
account more levels: a hypothetical congestion window may
increase much, not so much, remain stable, decrease a little,
or decrease very much. Anyway, we cannot be sure that a nlevel concept leads to more accurate reasoning than a m-level
concept. Nor can we say anything about the accuracy of FCMs
with mixed concepts (e.g., binary and ternary), as, to the best
of our knowledge, they have not been studied in the literature.
It is clearly preferable to have a mapping of a small number
of concepts to a small number of levels, since the inference
process is assured to converge within lc steps, c and l being
the number of concepts and the number of levels, in order [7].
Also, the fact itself of mapping virtually boundless concepts
to bounded sets may be problematic. For instance ‘end-to-end
delay’ has a trivial lower bound, yet no upper bound at all.
Even if a simple piecewise-linear mapping were adopted, so to
set to the boundary value all the values higher than a threshold,
the problem would concern how to correctly choose such a
threshold.
Another question is whether it is possible to comprise
mutually exclusive concepts. This is the case, for instance, of
a node equipped with two different implementations of TCP,
which clearly cannot be used at the same time. In such case we
could resort to the formalism used in Competitive FCMs [10],
in which such concepts are linked to each other by means
of totally negative edges: this way when either one of the
concepts is triggered, the other is deactivated.
B. Learning
Cognitive nodes must perform continuous learning—
making it possible to spot which concepts are causally related
to one another and which are not. Redundant concepts could
also be detected.
One of the simplest algorithms to learn, i.e. to update an
FCM, is Differential Hebbian Learning (DHL), derived from
the observation that human beings infer causality when they
witness some variation between two variables [13]. According
to this learning algorithm, the variation of edge fij is updated
proportionally to the product of the time derivatives of the
�concepts Ci and Cj : derivatives encode changes and the
product correlates these changes. Formally, the variation of
such edge at time step t is given by:
t−1
t
= −fij
+ Ċit Ċjt
f˙ij
(1)
Where the dot notation indicates the derivatives. The first
term in the right-hand side of (1) is necessary to set to zero
an edge when there is no variation in the relative concepts.
Accordingly, the edge fij at step t is computed as the value
it had at time step t − 1 plus the variation:
t−1
t
t
fij
= fij
+ f˙ij
= Ċit Ċjt
(2)
Also, a parameter η to modify the responsiveness of the
learning algorithm can be defined. This parameter, called
“learning rate”, usually belongs to the set (0, 1] and smooths
the edge variation: values close to zero result in a slowly
changing FCM, while values close to unity produce a highly
responsive FCM. Hence, the final equation is:
�
�
t−1
t−1
t
(3)
= fij
+ η −fij
+ Ċit Ċjt
fij
C. The Proposed Approach
Summarizing the discussion above, in order to implement
FCMs within cognitive nodes it is necessary to follow three
steps:
1) To identify which specific variables of the various communication protocols could be of interest for the intended
application. In particular, concepts should be categorized
according to what they represent: everything that can be
tuned should belong to the ‘action’ class, everything that
cannot be controlled directly and conveys a QoS-related
meaning should belong to the ‘QoS’ class, and everything
else (basically variables that cannot be controlled and are
not QoS-related) should belong to the ‘environment’ class.
As an example, let us suppose we want to model the
behavior of TCP over the wireless medium. Some concepts
that can be used are: the TCP congestion window, the packet
error probability, and the throughput. If we are allowed to
drive the congestion window, then such a concept belongs to
the ‘action’ class. No direct control can be exercised on the
error probability, which should therefore be classified as an
‘environment’ concept. Finally, the throughput represents a
measure of the performance and should belong to the ‘QoS’
class. If we label the concepts with the letters w, e, and t,
in order, the resulting preliminary FCM will be:
⎞
⎛
0
fwe fwt
0
fet ⎠
(4)
F ′ = ⎝few
ftw fte
0
It should be noticed that the elements on the diagonal are
set to zero by default, as concepts cannot cause themselves.
Instead, all the other elements can be non-zero, at least in
principle.
2) To define the domain of each variable, avoiding continuous sets and keeping discrete sets as small as possible (or
else being prepared to increased computational complexity).
In finding the right domain for boundless concepts, it could
be of help to think of a threshold, so that greater (or lower)
values entail the same causality as the threshold value.
With respect to the example we have introduced in 1),
the domain of the TCP congestion window could be the
discrete set {−1, 0, 1}, useful to represent situations when
the window increases, decreases or remains stable. The error
probability could instead be mapped to the discrete set
{0, 1}, indicating absence or presence of errors; however,
a proper threshold has to be chosen (for instance, according
to the transmission modulation used), so to distinguish
values of the error rate that affect the system behavior from
values that do not affect it. Finally, the same domain could
be apt for representing the throughput: the lowest value
indicates non-satisfactory situations, the highest a favorable
situations.
3) To design and implement the algorithm for building and
updating the FCM, embedding into the matrix any available
a priori knowledge. As it will be shown in the next section,
the choice and configuration of the algorithm is critical for
achieving good results.
For instance, the fact that the throughput does not cause
changes in neither one of the other concepts is translated
by setting to zero the last row of the FCM in 4. The possible
final version of the FCM can then be written as follows:
⎞
⎛
0
fwe fwt
0
fet ⎠
(5)
F ′′ = ⎝few
0
0
0
It should be noted that the first two points are more similar
to a pre-processing stage, rather than the reasoning stage itself.
However, the two stages cannot be separated from one another
and have to be accomplished in a jointly fashion.
IV. T EST C ASE
In order to provide a preliminary validation of the proposed
approach, this section proposes its application in a sample
scenario.
The test case is based on the data produced for the experiments in [14], where the performance of a VoIP Wi-Fi system
is investigated. More specifically, experiments are conducted
to measure how many VoIP calls the system supports given
specific quality constraints, as a function of four inputs at
different layers, e.g. data rate at physical layer, maximum
number of retransmissions and packet error rate at MAC layer,
voice packet interval at application layer.
The first step is to classify the concepts. Physical data rate,
voice packet interval and maximum number of retransmission
all belong to the ‘action’ class. The only output, i.e. the number
of calls supported, is also the only concept in the ‘QoS’
class. Packet error rate depends on uncontrollable parameters
(i.e. behaviour of the wireless link, modulation, etc.), therefore
it is classified in the ‘environment’ set.
The second step is concerned with finding suitable domains
for the concepts. All concepts in the data base can be mapped
to a binary domain: either we have a high physical data rate
�p
r
d
i
t
Fig. 2. The FCM adopted in the test case. p, d, r, i, and t stand for
packet error rate, physical data rate, maximum number of retransmissions,
voice packet interval, and throughput, respectively.
or a low one, either we have a long voice packet interval or a
short one, and so on. To further distinguish between highand low-concepts we have decided to keep all the entries
that are unambiguously high or low. For instance, in the
case of physical data rate, only the entries at 11 or 1 Mb/s,
corresponding to the maximum and the minimum, have been
held (values of 2 and 5.5 Mb/s have been deleted). Also, the
number of calls has been filtered and mapped to the domain
{0, 1}, equivalent to low- and high-throughput situations.
Finally, step three deals with the actual implementation of
the FCM. The a priori knowledge we have embedded in the
FCM regards the number of calls and the packet error rate
concepts. We assume that the number of calls cannot cause any
other concept, as they represent the ”output” of the system:
this is translated by setting to zero all the elements in the
row corresponding to the number of calls. Also, it makes
more sense that packet error rate implies some change in
the other concepts, rather than the other way round. This
means that no edges in the FCM point to the packet error
rate concept; instead, the packet error rate concept points to
all the others. Ultimately, physical data rate, maximum number
of retransmissions, and voice packet interval are controllable
parameters and thereby can be assumed as independent from
one another. The resulting FCM is depicted in Fig. 2. Its
mathematical equivalent is:
⎞
⎛
0
0
0
0 fdt
⎜ 0
0
0
0 frt ⎟
⎟
⎜
⎜
0
0
0 fit ⎟
(6)
F =⎜ 0
⎟
⎝fpd fpr fpi 0 fpt ⎠
0
0
0
0
0
An important feature of this particular FCM is that no
loops are present. This, in particular, means that the inference
process converges in just one step.
To validate the FCM, we shuffled the data base, in order
(i) to avoid that similar situations were placed in the same
area, and (ii) to randomize the experiment.
We started by implementing the algorithm for updating the
FCM at each step. Results are presented in Fig. 3, where the
effect of only two causes, namely the physical data rate and
the number of retransmissions, has been studied (for clarity’s
sake). In each subfigure the graph at the top shows what the
real throughput is (continuous line) and what the throughput
is according to the FCM (dashed line). The graph in the
middle depicts how reliable is such predicted throughput, by
performing the XNOR operation between the real data and the
predicted data: if the FCM predicts a high throughput (or low
throughput) and the real throughput is actually high (or low)
the graph shows a high logical value (correct prediction); in
the opposite case, the graph shows a low logical value (wrong
prediction). The graph at the bottom shows how the edge of
the FCM vary as a function of time: a continuous adaptation of
the FCM leads to a worse performance and a more unstable
FCM. Better results can be achieved by changing the FCM
edges only when prediction fails.
However, this assumes some external knowledge, capable of
comparing what has been forecast to what actually happened,
thereby enabling or disabling the DHL algorithm.
A more thorough situation is reproduced in Fig. 5, where
the effects of all the causes are investigated at the same time.
Notably, the number of calls has been mapped as a threevalued concept, meaning the FCM could predict not only
low- and high-throughput values, but medium values as well.
Due to the greater complexity, predictions are less accurate,
and heavily depend on the thresholds used for the mapping
operation.
The impact of different values for the learning rate parameter η is investigated in Fig. 4. Apparently, for the specific
scenario, a less dynamic FCM (η ∈ [0.1, 0.4]) is able to
achieve better results than a more dynamic FCM. Fig. 4
shows the evolution of the performance as a function of the
learning rate parameter η. Specifically, it shows what is the
performance obtained guessing the throughput value by means
of the FCM (continuous line) and that obtained by applying
a static decision, e.g. deciding that the throughput availability
is always high (dashed line).
V. C ONCLUSIONS
The paper proposes a novel tool to support reasoning in
cognitive nodes, using the Fuzzy Cognitive Maps framework
able to represent information about correlation among operating parameters at different layers—thus providing a way to
embed information about cross-layer interactions within the
cognitive cycle of a node.
However, the paper only represents the first step in the direction of enabling quantitative reasoning in cognitive networks.
As a next step, ongoing work is focused on evaluating the
ability of cognitive nodes to merge the FCM provided by
neighboring nodes and assess costs and benefits associated:
even if it is straightforward to combine multiple maps with
one another [13], it is not that obvious that this operation
will lead to greater performance achievements. Moreover, a
particular format that unambiguously represent FCMs has to
be devised, as well as a proper signaling method for their
exchange. Finally, in order for this tool to be implemented in
real networks, its effectiveness has to be improved: reasoning
has to be able to include not only intra-flow interactions but
also inter-flow and inter-nodes interactions.
�(a)
Fig. 4. Impact of the learning parameter η on the prediction reliability.
Confidence intervals computed with p = 0.995, DoF= 49.
(b)
Fig. 3. Performance achieved enabling the FCM update: a) at each step, and
b) only in case of prediction errors. The subgraph in the middle shows that,
by updating the FCM only when errors occur, predictions are more reliable.
η = 0.5.
Fig. 5.
R EFERENCES
[1] R. W. Thomas, L. A. DaSilva, and A. B. MacKenzie, “Cognitive networks,” in First International Symposium on New Frontiers in Dynamic
Spectrum Access Networks (DySPAN 2005), Nov. 2005, pp. 352–360.
[2] C. Fortuna and M. Mohorčič, “Trends in the development of communication networks: Cognitive networks,” Computer Networks, vol. 53,
no. 9, pp. 1354–1376, 2009.
[3] P. Langley, J. E. Laird, and S. Rogers, “Cognitive architectures: Research
issues and challenges,” Cognitive Systems Research, vol. 10, no. 2, pp.
141–160, 2009.
[4] P. Mähönen, M. Petrova, J. Riihijarvi, and M. Wellens, “Cognitive
wireless networks: Your network just became a teenager,” in Proc. of the
25th Conf. on Computer Communications (INFOCOM 2006), Barcelona,
Spain, 2006.
[5] N. Baldo and M. Zorzi, “Cognitive network access using fuzzy decision
making,” in IEEE International Conference on Communications (ICC
’07), Jun. 2007, pp. 6504–6510.
[6] B. Kosko, “Fuzzy cognitive maps,” Int. J. Man-Mach. Stud., vol. 24,
no. 1, pp. 65–75, 1986.
[7] A. K. Tsadiras, “Comparing the inference capabilities of binary, trivalent
and sigmoid fuzzy cognitive maps,” Information Sciences, vol. 178,
no. 20, pp. 3880–3894, 2008, special Issue on Industrial Applications
[8]
[9]
[10]
[11]
[12]
[13]
[14]
Throughput as a three-valued concept. η = 0.1.
of Neural Networks, 10th Engineering Applications of Neural Networks
2007.
D. Fletcher, D. Nguyen, and K. Cios, “Autonomous synthesis of
fuzzy cognitive maps from observational data: Preliminaries,” in IEEE
Aerospace Conference, 2005, pp. 1–9.
Y. Miao and Z.-Q. Liu, “On causal inference in fuzzy cognitive maps,”
IEEE Trans. Fuzzy Syst., vol. 8, no. 1, pp. 107–119, 2000.
C. D. Stylios, V. C. Georgopoulos, G. A. Malandraki, and S. Chouliara, “Fuzzy cognitive map architectures for medical decision support
systems,” Applied Soft Computing, vol. 8, no. 3, pp. 1243–1251, 2008,
forging the Frontiers – Soft Computing.
J. A. Dickerson and B. Kosko, “Virtual worlds as fuzzy cognitive maps,”
in IEEE Virtual Reality Annual International Symposium, Seattle, WA,
USA, 1993, pp. 471–477.
J. Aguilar, “A survey about fuzzy cognitive maps papers,” International
Journal of Computational Cognition, vol. 3, pp. 27–33, 2005.
B. Kosko, Neural Network and Fuzzy Systems. Prentice-Hall, 1992,
ch. Synaptic Dynamics I: Unsupervised Learning, pp. 152–159.
F. Granelli, D. Kliazovich, J. Hui, and M. Devetsikiotis, “Performance
optimization of single-cell voice over WiFi communications using
quantitative cross-layering analysis,” in Managing Traffic Performance in
Converged Networks, ser. Lecture Notes in Computer Science. Springer
Berlin, 2007, vol. 4516/2007, pp. 386–397.
�
 Fabrizio Granelli
Fabrizio Granelli