Cloudhnologysstecociat
- 1. Trainer Profile LEO LOURDES (MBA IT Management, BoM Hons. HRM) Implementer of ISO 20000-1:2011 Certified in COBIT® 5 Certified in ISO 9001 Auditor (PECB) Certified in PRINCE2® in Project Management Certified in ITIL® Practitioner Certified in ITIL® Intermediate Certificate in IT Service Operation Certified in ITIL Information Security based on ISO/IEC 27002 Certified in ITIL for Cloud Computing Certified in ITIL IT Service Management Certified in Coaching and Calibration Skills for Call Center Certified in Delivering Learning / Teaching by City & Guilds, United Kingdom leo@thinkleosolutions.com +6012-311 6457 / +6016-349 1793 Experience: Management Representative (MR) ISO 20000-1: 2011 IT Service Management (Incident, Problem, Change) Manager Security, Compliance & Risk Management Senior CRM Delivery Analyst Certified Trainer Certified IT Auditor & Consultant
- 2. • Principles of Cloud Computing • Implementing and Managing Cloud • Using the Cloud • Security and Compliance • Evaluation of Cloud Computing: The Business Case Course Objectives
- 3. Overview
- 4. 1. The Principles of Cloud Computing
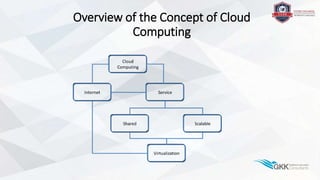
- 5. 1.1 The Concept of Cloud Computing
- 6. Overview of the Concept of Cloud Computing
- 7. 1.1.1 Five Characteristics • On-demand self-service • Resource pooling (multi-tenancy) • Rapid elasticity (flexibility, scalability) • Measured service (pay-per-use) • Broad network access ("any time, any place, any device”)
- 8. Cloud Computing: Some examples • For everyone: • Facebook, twitter (social media) • Wiki’s • Online games • Hotmail (webmail) • Dropbox • For business: • CRM • Backup services • ERP • Financial • Etc…
- 9. 1.1.2 Four Deployment models Public, Private, Community and Hybrid Clouds
- 10. Private Cloud: just another name for a data center? • resides on a private network that runs on (part of) a data center that is exclusively used by one organization; • owned, managed and run by either the organization itself, a third party or a combination of the two; • supports the organization’s business objectives in an economic sound way; • high security (compliance with legislation and regulations).
- 11. Public Cloud • Delivery of off-site services over the internet • Sharing of resources; ‘multi-tenancy’ means a lower level of security and privacy • Aimed at a wide audience • Compelling services like email and social media • Enables social networking and collaboration
- 12. Community Cloud • A type of shared private cloud • Delivers services to a specific group of organizations and/or individuals that share a common goal • Sharing of data, platforms and applications • Sharing of capital expenditure for otherwise (too) expensive facilities • 24/7 access and support • Shared service and support contracts • Economics of scale Examples: regional or national educational or research institutes, community centers, etc.
- 13. Hybrid Cloud • A mix of the above models; combining several Private and Public Cloud solutions from several providers into one (virtual) IT infrastructure • Choosing specific services for either Private or Public Cloud suitability is balancing: • security • privacy • compliance versus price
- 14. 1.1.3 Cloud Service Models • Software as a Service (SaaS) • The customer does not need to worry about the development and management of applications. • Platform as a Service (PaaS) • Not owning a computer platform, but being able to use it ‘on demand’ can save costs in ownership, management and maintenance. • Infrastructure as a Service (IaaS) • Rental of physical or virtual hardware like storage, servers or internet connectivity.
- 15. SaaS • Key characteristics: • Software hosted offsite • Software on demand • Software package • No modification of the software • Plug-in software: external software used with internal applications (Hybrid Cloud) • Vendor with advanced technical knowledge • User entangled with vendor • Examples: CRM, ERP, Billing and invoicing, Web Hosting, Etc.
- 16. PaaS • Key characteristics: • Mostly used for remote application development • Remote application support • Platform may have special features • Low development costs • Variants • Environment for software development • Hosting environment for applications • Online storage
- 17. IaaS • The background of IaaS can be found in the merger between IT and Telecom infrastructure and services in the past decade • Key characteristics: • Dynamic scaling • Desktop virtualization • Policy-based services • Examples of IaaS are hosting services supporting e- commerce, web hosting services that include broadband connections and storage.
- 18. 1.2 The evolution toward Cloud Computing
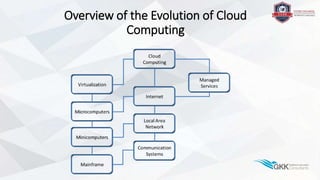
- 19. Overview of the Evolution of Cloud Computing
- 20. 1.2.1Historictimeline • Contributing factors to the existence of the Cloud • The development of the Internet • The move from Mainframe computing to the present day myriad of personal devices with connection to the Internet. • The development of computer networks • Time-line • Mainframe computers and terminals • Decentralized mini computers with terminals • Micro computers (PC) connected to a LAN with terminal emulation • Client-server architecture • Any device connected to the internet
- 21. 1.2.2 Network and Servers • Service forms • Dial up with modem • Dedicated leased-line • Uses • Dedicated terminal • Access to time sharing services • Special services on intelligent devices: • Terminal server (remote access) • Batch processing (job entry)
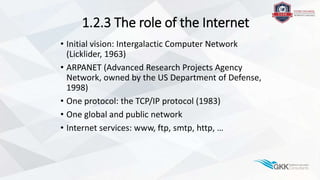
- 22. 1.2.3 The role of the Internet • Initial vision: Intergalactic Computer Network (Licklider, 1963) • ARPANET (Advanced Research Projects Agency Network, owned by the US Department of Defense, 1998) • One protocol: the TCP/IP protocol (1983) • One global and public network • Internet services: www, ftp, smtp, http, …
- 23. 1.2.4 Virtualization Not NEW! • Exists since the 1970s in mainframe environments Example: 1972 IBM VM/370
- 24. Six types of virtualization • Access virtualization (access from any device) • Application virtualization (platform and operating system independent) • Processing virtualization (one system becomes many) • Network virtualization (enables artificial views of the network) • Storage virtualization (enables sharing, concealing, etc.)
- 25. 1.2.5 Managed Services in the Cloud
- 26. • Advantages: • Accessibility everywhere • Shift of focus from IT to core business • No need for highly trained IT staff • Key Issues: • Performance • Compliance • Contingency
- 28. Overview of Cloud Computing Architectures
- 29. 1.3.1 Multipurpose Architecture • Key Characteristics - Virtualization - Multi-tiered - Interoperable layers - Open standards
- 30. Server Virtualization Architectures • Virtualization as the Operating System • Virtualization with a host Operating System
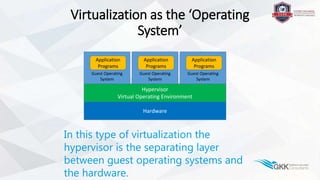
- 31. Virtualization as the ‘Operating System’ Hardware Hypervisor Virtual Operating Environment Guest Operating System Application Programs Guest Operating System Application Programs Guest Operating System Application Programs In this type of virtualization the hypervisor is the separating layer between guest operating systems and the hardware.
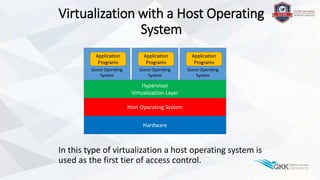
- 32. Virtualization with a Host Operating System In this type of virtualization a host operating system is used as the first tier of access control. Host Operating System Hypervisor Virtualization Layer Guest Operating System Application Programs Guest Operating System Application Programs Guest Operating System Application Programs Hardware
- 34. Multi-tenancy Architecture • Rationale: • ‘a large number of users, basically multi-tenants, makes the cloud platform most efficient in terms of usability of the application and ‘Do More With Less Resources’. (Rajan, 2011) • Key element (issue) is Security • Security needs to be ensured at all levels of the infrastructure • Examples: • Salesforce.com: a SaaS-based CRM application for various businesses using common framework and multi-tenancy model • Microsoft Dynamics CRM Online offering • Multi-tenancy IaaS/PaaS offerings from Amazon or IBM or Microsoft Azure
- 35. 1.3.2 Service Oriented Architectures • Service-Oriented Architecture (SOA) • an architectural style that supports service orientation. • Service orientation • a way of thinking in terms of services and service-based development and the outcomes of services. • Service • a logical representation of a repeatable business activity that has a specified outcome (e.g., check customer credit, provide weather data, consolidate drilling reports); • self-contained; • May be composed of other services; • a “black box” to consumers of the service. Source: Cloud working group, The Open Group.
- 36. Cloud and SOA • Question: (Paul Krill) • ‘Can we build a datacenter infrastructure on SOA principles?’ • Answer: (Gerry Cuomo) • ‘Yes, and that's the cloud, so it's a service-oriented infrastructure,… It's taking that architectural principle of SOA and applying it to an infrastructure.’ ‘The cloud-SOA connection’ (Krill, 2009) • A service-oriented architecture is basically a collection of services that communicate with each other. • Connecting these services in many cases involves Web services using XML No Cloud without SOA!
- 37. 1.4 Benefits and limitations of Cloud Computing
- 38. Overview of the Drivers & Limitations
- 39. 1.4.1 Main benefits of Cloud Computing • Reduced Cost (the pay-per-use, economics of scale) • Automated (updates, security patches, backups,…) • On demand (Flexibility + Scalability = Elasticity) • More Mobility (accessible from any web enabled device) • Shared Resources (multi-tenancy) • Back to core business • More for less
- 40. 1.4.2 Cloud Computing Limitations • Internet access (no internet = no Cloud) • Security (how do you know?) • Privacy (what legislation or regulations?) • Vendor lock-in (staying with a provider to avoid the hassle of moving to another) Plus or Minus • Service Level Agreement • Do the clauses support your business? • If so it is a plus! (customer responsibility; it takes two to tango!)
- 41. 2. Implementing and Managing Cloud Computing
- 42. Overview of Implementing and Managing Cloud Computing
- 43. 2.1 Building a local Cloud environment
- 44. Overview of a Local Cloud Environment
- 45. Why own a local Cloud environment? • Private intranet becomes a private Cloud • Investment in existing infrastructure • Integration of legacy applications • Controlled by the own organization • Complete control • Internal Security
- 46. 2.1.1 Main Components and their interconnection
- 47. Main hardware components Baseline examples: • Local Area Network (LAN) • Switches, routers etc. • Blade server array (on which can run) • Database servers, application servers, web servers, etc. • User workstations • Thin client, PC, mobile devices • Storage • Storage Area Network (SAN) • Network Attached Storage (NAS) • Load balancer
- 48. Main software components Baseline examples: • Virtualization software • Cloud based application software • CRM, ERP, Financial, etc. • Database software • Middleware • Operating systems • Proprietory or Open Source
- 49. Architectural considerations (general) • Standard building blocks • Protocols • Vendor independent • Location independent • Security and Service Continuity • Multiple sites • Backup mechanisms • Data storage replication • High security components like firewalls, a DMZ and internet security software
- 50. Architectural considerations: Connection requirements • Speed • i.e., MPLS • Capacity • Availability (access at any time, from any place and from any device) • Secure inter-/intranet based access • VPN
- 51. 2.1.3 Risks of connecting a local Cloud Network to the Public Internet • “Are companies really willing to risk having all their information, data, privacy, and software handled in a virtual cloud—a place where they're most susceptible to hack attacks and cyber invasions?” Source: www.secpoint.com • Issues: • Provider responsibility: • Security of data • Privacy of data • The customer’s responsibility: • Check for compliance (legislation, regulations, International standards) • With whom do I share the Cloud?
- 52. Data Protection and Partitioning • Wall between data from different clients • Zoning • Hidden storage Protection across operating systems and virtual servers
- 53. 2.2. The principles of managing Cloud services
- 54. 2.2.1 IT Service Management Principles in a Cloud Environment Outsourcing to the Cloud means that the provider needs to be in control of the complete supply chain. Key areas of control: • IT governance; the customer needs to remain in control over his/her business processes • Business-IT alignment; the customer needs to make sure that the Cloud IT processes support his/her business in the short and long term
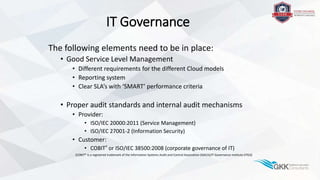
- 55. IT Governance The following elements need to be in place: • Good Service Level Management • Different requirements for the different Cloud models • Reporting system • Clear SLA’s with ‘SMART’ performance criteria • Proper audit standards and internal audit mechanisms • Provider: • ISO/IEC 20000:2011 (Service Management) • ISO/IEC 27001-2 (Information Security) • Customer: • COBIT® or ISO/IEC 38500:2008 (corporate governance of IT) (COBIT® is a registered trademark of the Information Systems Audit and Control Association (ISACA)/IT Governance Institute (ITGI))
- 56. 2.2.2 Managing Service Levels in a Cloud Environment ISO/IEC 20000:2011 quality specifications Component Consisting of Purpose Quality specifications Information System • People • Processes • Technology • Partners To manage information • Availability • Capacity • Performance • Security • Scalability • Adjustability • Portability Support • Changes, system restoration in case of failure • Maintenance To ensure performance according to the agreed requirements
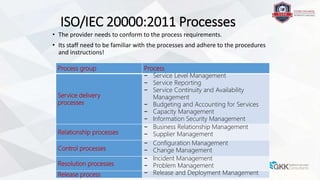
- 57. ISO/IEC 20000:2011 Processes • The provider needs to conform to the process requirements. • Its staff need to be familiar with the processes and adhere to the procedures and instructions! Process group Process Service delivery processes − Service Level Management − Service Reporting − Service Continuity and Availability Management − Budgeting and Accounting for Services − Capacity Management − Information Security Management Relationship processes − Business Relationship Management − Supplier Management Control processes − Configuration Management − Change Management Resolution processes − Incident Management − Problem Management Release process − Release and Deployment Management
- 58. Questions to ask the Cloud provider • How are audits performed? • Where are the servers located, and which legislation applies to the data? • What are the provisions when a service changes or ends (service life cycle and end of life)? • What are the provisions if we want to migrate to another provider (contract life cycle and end of life)?
- 59. 3. Using the Cloud
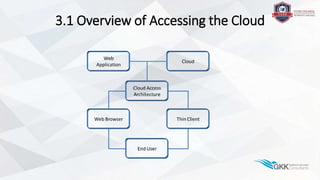
- 60. 3.1 Overview of Accessing the Cloud
- 61. 3.1.1 Accessing Web applications through a Web Browser • Basic ingredients: - “any” web enabled device - PC, laptop, tablet, smart phone, thin client - Internet browser - Internet connection - Provider, IP-address - Cloud based application - SaaS solution
- 62. 3.1.2 Cloud Web Access Architecture Basic ingredients: • Standard protocols (for each ISO-OSI layer) • Web enabled device • PC • Laptop • Tablet • Smart phone • And… (revival of the computer terminal) Thin Client • Internet access
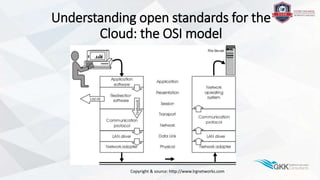
- 63. Understanding open standards for the Cloud: the OSI model Copyright & source: http://www.lrgnetworks.com
- 64. 3.1.3 The use of a Thin Client • A simple network enabled computer • No moving parts like a hard disk or DVD drive • Boots from the network • Benefits: • Lower costs; initial price and running costs • Simple; no moving parts • Better for the environment; they produce less heat and need less cooling, sometimes not even a fan • Heightened security; booting from the network with controlled access, no local data, etc. • Less chance of user errors
- 65. 3.2 Service providers using the Cloud
- 66. 3.2.1 Impact on Relationship Vendor Customer • The relationship between provider and customer changes • Customer intimacy: running the customer’s business • Running the whole supply chain • Requirement to demonstrate performance and compliance • New and clear SLA’s • Audit trail • Compliance to legislation, regulations and international audit standards
- 67. 3.2.2 Benefits and Risks of providing Cloud based Services • Benefits: business opportunities • New lease of life for “old” data centers (IaaS) • Better use of resources because of multi-tenancy • Economics of scale • Quickly develop and run applications in the same environment (PaaS) • Risks: challenges • Compliance - Standards, legislation and regulations • Performance - Availability, capacity, flexibility, scalability • Security • Privacy
- 68. 4. Security and Compliance
- 69. Overview of Security and Compliance
- 70. 4.1 Security risks and mitigating measures
- 71. 4.1.1 Security risks in the Cloud • Data breaches / loss • Shared technology vulnerabilities • Insecure application interfaces • Malicious insiders • Abuse of Cloud Services • Denial-of-Service • Account, service and traffic hijacking • Insufficient Due Diligence Copyright & Source: Cloud Security Alliance (CSA), paper: “Cloud Security Alliance The Notorious Nine: Cloud Computing Top Threats in 2013”.
- 72. 4.1.2 Measures mitigating Security Risks • Risk: • Data breaches/loss • Shared technology vulnerabilities • Insecure application interfaces • Malicious insiders • Abuse of Cloud Services • Unknown risk profile and account • Account, service and traffic hijacking • Insufficient Due Diligence • Mitigation: • Authentication, audit, authorization, etc. • Operations procedures, operational security practices, etc. • Design for security, etc. • HR vetting procedures, etc. • Validation of credentials, active monitoring of traffic, etc. • SLA structures, Cloud provider compliance audits • Strong authentication, active monitoring, etc. • Assess the financial health of the Cloud service provider Copyright & Source: Cloud Security Alliance (CSA), paper: ‘Cloud Security Alliance “Top Threats to Cloud Computing” Version 1.0 (2010)’ and “Cloud Security Alliance The Notorious Nine: Cloud Computing Top Threats in 2013” Controls are added in the Notorious Nine instead of mitigating measures.
- 73. 4.2 Managing identity and privacy
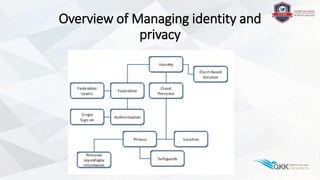
- 74. Overview of Managing identity and privacy
- 75. 4.2.1 Authentication • Non-Cloud authentication • Simple authentication using user-id and password • Active directory authentication • Uses your active directory account credentials • Uses Kerberos protocol (no transmission of readable data) • Authentication in the Cloud • Active directory authentication (VMware plays the role of the domain controller and/or security server) • LDAP (Lightweight Directory Access Protocol) or Kerberos
- 76. Triple-A Authentication • Authentication • Triple identification, what/who you • Know (password) • Have (token/smart card) • Are (fingerprint or retina scan) • Authorization • leveled • Accountability • periodic logs & audit data
- 77. 4.2.2. Main aspects of Identity Management • Typical characteristics of an Identity Management system are: • Role management; IT implementation of a business role. • Role hierarchy; a representation of an organization chart. • Separation of duties. • Group management; permissions are not given to people but to roles. • Self-service functions. • Password synchronization. • Digital Identity; presence and location determine available services and capabilities.
- 78. Single sign-on (SSO) for web services • Problem: Security infrastructure in the Cloud is distributed • Solution: Single sign-on (SSO) • All distributed elements consolidated on an SSO-server • Credentials are offered by AD-account, token or smart card • Uses SOAP protocol
- 79. 4.2.3 Privacy, compliance issues and safeguards in Cloud Computing • Issues • Handling of Personal Identifiable Information (PII) • Compliance to international privacy legislation and regulations • Safeguards • Effective Access Control and Audit • Secure Cloud Storage • Secure Network Infrastructure
- 80. Personal Identifiable Information (PII) • Forms of identification: SSN, passport, fingerprints • Occupational: job title, company name • Financial: bank numbers, credit records • Health care: insurance, genetic • Online activity: log-ins • Demographic: ethnicity • Contact: phone, e-mail
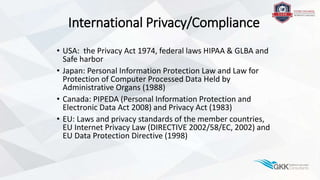
- 81. International Privacy/Compliance • USA: the Privacy Act 1974, federal laws HIPAA & GLBA and Safe harbor • Japan: Personal Information Protection Law and Law for Protection of Computer Processed Data Held by Administrative Organs (1988) • Canada: PIPEDA (Personal Information Protection and Electronic Data Act 2008) and Privacy Act (1983) • EU: Laws and privacy standards of the member countries, EU Internet Privacy Law (DIRECTIVE 2002/58/EC, 2002) and EU Data Protection Directive (1998)
- 82. Safeguards • Effective Access Control and Audit • Single sign-on (SSO) • Strong authentication: password & biometric measure • Review on audit logs • Secure Cloud Storage • Encryption • Integrity by mechanisms as hashing • Secure Network Infrastructure • Encryption protocols against leakage • Integrity protocols (digital signatures) against modification • Consult a lawyer, specialized in international legislation • Know where (which country) your data is
- 83. 5. Evaluation of Cloud Computing
- 84. 5.1 The business case
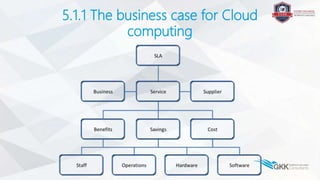
- 85. 5.1.1 The business case for Cloud computing
- 86. Business drivers • Flexibility • Time-to-market (TTM) • Costs • TCO • CAPEX vs. OPEX • TCAO • Service Level Agreements (SLA) • Performance, Security, Availability, Scalability, … • Architecture • Integration (PaaS), migration • Green(er) computing
- 87. Compelling feature: quicker time-to- market But… • Can the cloud provide the resources faster than when hosted locally in your company? • What do we give up? • What do we gain? • Is your organization willing to compromise? • Are the organization, employees, IT staff, other interested parties willing to make the change without delay?
- 88. TCO ‘and all that stuff’ Statement: into the Cloud lowers your TCO of IT • Is this true or are you just redistributing costs? • Capital costs are lowered significantly, but are replaced by subscriptions, pay-per-use, expensive support contracts, etc. (CAPEX becomes OPEX) • We need to compare what we are paying now to the Cloud scenario • Not only as a snap-shot, bu also as a long term video
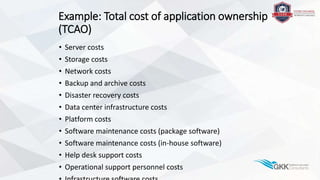
- 89. Example: Total cost of application ownership (TCAO) • Server costs • Storage costs • Network costs • Backup and archive costs • Disaster recovery costs • Data center infrastructure costs • Platform costs • Software maintenance costs (package software) • Software maintenance costs (in-house software) • Help desk support costs • Operational support personnel costs
- 90. 5.1.2 Operational and staffing benefits • Operational benefits (examples): • Managed services • Self-service (unmanaged services) • instant server deployment • software licensing without impact on CAPEX • uptimes are guaranteed • Backups as a service (always off-site) • Staffing benefits (examples): • Less IT staff (less wages to be paid) • Lower recruitment, HR and training costs • Lower employee benefits
- 92. Overview of Evaluating Cloud Computing Implementations
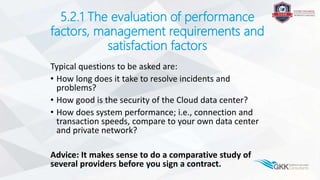
- 93. 5.2.1 The evaluation of performance factors, management requirements and satisfaction factors Typical questions to be asked are: • How long does it take to resolve incidents and problems? • How good is the security of the Cloud data center? • How does system performance; i.e., connection and transaction speeds, compare to your own data center and private network? Advice: It makes sense to do a comparative study of several providers before you sign a contract.
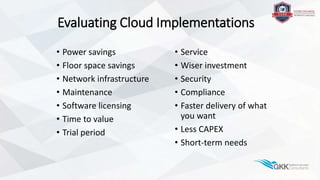
- 94. Evaluating Cloud Implementations • Power savings • Floor space savings • Network infrastructure • Maintenance • Software licensing • Time to value • Trial period • Service • Wiser investment • Security • Compliance • Faster delivery of what you want • Less CAPEX • Short-term needs
- 95. Performance, Requirements and Satisfaction Try before you buy! • Demand a trial period! • Do not commit until you are certain it works the way you want, especially when considering a completely new software package or completely new service!
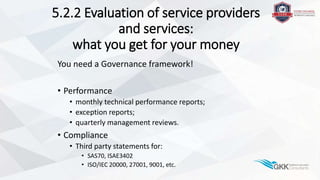
- 96. 5.2.2 Evaluation of service providers and services: what you get for your money You need a Governance framework! • Performance • monthly technical performance reports; • exception reports; • quarterly management reviews. • Compliance • Third party statements for: • SAS70, ISAE3402 • ISO/IEC 20000, 27001, 9001, etc.
- 97. END