Implementing Responsible Design in a Connnected World
- 1. IMPLEMENTING RESPONSIBLE DESIGN IN A CONNECTED WORLD IoT Design Manifesto WORKSHOP 4-12-2015 Thingscon Amsterdam
- 4. WHY
- 5. Peak of inflated expectations Technology trigger Trough of Disillusionment Plateau of Productivity Slope of enlightenment
- 7. MANIFESTO 10 Principles Open for discussion A tool for conversation Guideline
- 8. WHY THIS WORKSHOP? • Identify the situation of designing in the IoT world • Develop techniques and strategies for how the manifesto’s principles can be implemented • Develop practical guidelines for promoting responsible design within the IoT • Achieve this by “doing” … practice what we preach
- 9. PROGRAMME TODAY Who we are, why we have a manifesto, what is this workshop for? (5 min) Participant introductions (5 min) Manifesto re-cap (5 min) Super pressure cooker concept design session (60 min) • Breakup & mix into groups (5 min) • Check the briefs (10 min) • Design your concept (10 min - for real …) • Showtime 1! (20 min) • Refine the concept with the manifesto (30 min) • Showtime! 2 (20 min) Conclusions & discussion ( … min)
- 10. INTRODUCTIONS! Who? What? Why? Favourite Star Wars character?
- 11. RECAP MANIFESTO
- 12. DON’T BELIEVE THE HYPEI
- 13. We pledge to be skeptical of the cult of the new — just slapping the Internet onto a product isn’t the answer. Monetising only through connectivity rarely guarantees sustainable commercial success. DON’T BELIEVE THE HYPEI
- 14. WE DESIGN USEFUL THINGSII
- 15. Value comes from products that are purposeful. Our commitment is to design products that have a meaningful impact on people’s lives; IoT technologies are merely tools to enable that. WE DESIGN USEFUL THINGSII
- 16. WE AIM FOR THE WIN-WIN-WINIII
- 17. A complex web of stakeholders is forming around IoT products: from users, to businesses, and everyone in between. We design so that there is a win for everybody in this elaborate exchange. WE AIM FOR THE WIN-WIN-WINIII
- 18. WE KEEP EVERYONE AND EVERY THING SECURE IV
- 19. With connectivity comes the potential for external security threats executed through the product itself, which comes with serious consequences. We are committed to protecting our users from these dangers, whatever they may be. WE KEEP EVERYONE AND EVERY THING SECURE IV
- 20. WE BUILD AND PROMOTE A CULTURE OF PRIVACY V
- 21. Equally severe threats can also come from within. Trust is violated when personal information gathered by the product is handled carelessly. We build and promote a culture of integrity where the norm is to handle data with care. WE BUILD AND PROMOTE A CULTURE OF PRIVACY V
- 22. WE ARE DELIBERATE ABOUT WHAT DATA WE COLLECT VI
- 23. This is not the business of hoarding data; we only collect data that serves the utility of the product and service. Therefore, identifying what those data points are must be conscientious and deliberate. WE ARE DELIBERATE ABOUT WHAT DATA WE COLLECT VI
- 24. WE MAKE THE PARTIES ASSOCIATED WITH AN IOT PRODUCT EXPLICIT VII
- 25. IoT products are uniquely connected, making the flow of information among stakeholders open and fluid. This results in a complex, ambiguous, and invisible network. Our responsibility is to make the dynamics among those parties more visible and understandable to everyone. WE MAKE THE PARTIES ASSOCIATED WITH AN IOT PRODUCT EXPLICIT VII
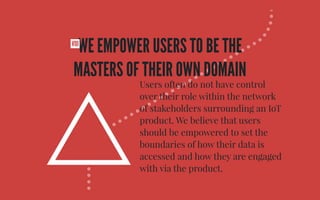
- 26. WE EMPOWER USERS TO BE THE MASTERS OF THEIR OWN DOMAIN VIII
- 27. • Users often do not have control over their role within the network of stakeholders surrounding an IoT product. We believe that users should be empowered to set the boundaries of how their data is accessed and how they are engaged with via the product. WE EMPOWER USERS TO BE THE MASTERS OF THEIR OWN DOMAIN VIII
- 28. WE DESIGN THINGS FOR THEIR LIFETIMEIX
- 29. Currently physical products and digital services tend to be built to have different lifespans. In an IoT product features are codependent, so lifespans need to be aligned. We design products and their services to be bound as a single, durable entity. WE DESIGN THINGS FOR THEIR LIFETIMEIX
- 30. IN THE END, WE ARE HUMAN BEINGS.X
- 31. Design is an impactful act. With our work, we have the power to effect relationships between people and technology, as well as among people. We don’t use this influence to only make profits or create robot overlords; instead, it is our responsibility to use design to help people, communities, and societies thrive. IN THE END, WE ARE HUMAN BEINGS.X
- 32. CONCLUDING We pledge to be skeptical of the cult of the new — just slapping the Internet onto a product isn’t the answer. Monetizing only through connectivity rarely guarantees sustainable commercial success. The world is becoming increasingly connected. This offers opportunities for designers, engineers and entrepreneurs to create unprecedented products and services. Yet, a connected world also brings new questions and challenges to the table. This manifesto serves as a code of conduct for everyone involved in developing the Internet of Things, outlining 10 principles to help create balanced and honest products in a burgeoning field with many unknowns. WE DON’T BELIEVE THE HYPE I With connectivity comes the potential for external security threats executed through the product itself, which comes with serious WE KEEP EVERYONE AND EVERY THING SECURE IV A complex web of stakeholders is forming around IoT products: from users, to WE AIM FOR THE WIN-WIN-WIN III Value comes from products that are purposeful. Our commitment is to design WE DESIGN USEFUL THINGS II IOT DESIGN MANIFESTOFirst drafted by a number of design professionals, this manifesto is intended to be a living document that the larger community of peers working within the IoT field can contribute to and improve upon. This manifesto is a living document, we seek your input to help it grow. Please discuss, contribute, remix, and test the boundaries of these principles. www.iotmanifesto.org v1.0 · May 2015
- 33. PRESSURE COOKER! Split up - let’s make groups You’ll be assigned a role - act like it Let’s do this super fast …
- 35. Brief #1 Local greengrocers team up w/ Ultimaker® to build new retail model. Brief #2 Carpenters union create open source kitchen based on usage data. Brief #4 Waste processors want to bid for clean waste from urban households Brief #3 Salvation army wants to tap into the resource of expiring food Brief #6 A national political party wants kitchen table that strengthens family ties. Brief #5 Hospital commissions nearby amateur chefs to make hospital food
- 36. MAKE IT YOUR OWN How can we create / design / improve a …….……….. for ….……….. to …..…………
- 37. DEFINE What will you be designing? (service, thing, … etc ) It can be “evil” - there are no no no limits! What does this mean for your role / profession in the process? Draw it ! (advertisement poster)
- 38. HOW? Where will your concept be used? Sketch the context of the physical space (2D)
- 39. HOW? Add your solution, users and other actors and play out the actual use / behaviour In three marvellous dimensions! Explain to group (2 min max!)
- 40. SHOWTIME!
- 41. ADD MANIFESTO!
- 42. Concept DesignVerify Implement IOT DESIGN MANIFESTO CHEATSHEET This is the IoT Design Manifesto cheatsheet. It aims to make the principles of the manifesto actionable. How to use this?The principles of the manifesto work on different abstraction levels. So when you design a product, you would address conceptual issues first, and become more specific toward implementation. Then iterate once more to account for interrelated issues. 1. Concept What is the raison-d’être ? Why is it connected? What value do we create? 2. Design How should it work? How would people interact? How would it show… 3. Implementation What do we need to develop? How do we account for privacy? I. WE DON’T BELIEVE THE HYPEImagine, your product would be advertise without any mentioning of connectedness data, the internet or smartness. What would it be that would trigger a customer? II. WE DESIGN USEFUL THINGSThis is basically a challenge of good design. What kind of untapped potential is there in this product? What would’ve been impossible 10 years ago, but would now suddenly be possible? What needs can the product cater for that it couldn’t do before? III. WE AIM FOR THE WIN-WIN-WINIoT products are connected. Not only to the web or a service, but through that service to anyone involved in creating it.Who is involved with the product, and what is to gain from being connected? And if one stakeholder clearly wins, how’s that of value to the other stakeholders? IV. WE KEEP EVERYONE AND EVERY THINGSECUREWhat are the scenarios you can think of, where security is at stake. And what are the potential points where security can be breached? On product level, service level? Or does your product put other products around it at risk?V. WE BUILD AND PROMOTE A CULTUREOF PRIVACYThis is an organisational issue. Privacy is a complex matter and you need to align everyone working on a product or service to have a common notion and policy relevant to the context of your business. When drafting your policy, try to ‘be’ your customer, and push for extreme scenarios like company acquisitions, security breaches, partner company bankruptcies, potential outsourcing of processing and storing data, etc. etc. VI. WE ARE DELIBERATE ABOUT WHATDATA WE COLLECTWhat is the minimal amount of data we need to process to make this product work? And what data could be of use for the current user, future users, or future versions of a product? How could a product become a better version of themselves? How could other products work better through data from your product? If any data stream doesn’t server any of these purposes, why bother to collect or store it? VII. WE MAKE THE PARTIES ASSOCIATED WITH AN IOT PRODUCT EXPLICITHow will your user know who is involved with your product? When, in the process of bringing this product into her/his life, will she/he understand that the product is an element of a greater network with more parties involved? VIII. WE EMPOWER USERS TO BE THE MASTERS OF TH
- 43. Concept
- 44. A complex web of stakeholders is forming around IoT products: from users, to businesses, and everyone in between. We design so that there is a win for everybody in this elaborate exchange. WE AIM FOR THE WIN-WIN-WINIII
- 45. Design
- 46. Users often do not have control over their role within the network of stakeholders surrounding an IoT product. We believe that users should be empowered to set the boundaries of how their data is accessed and how they are engaged with via the product. WE EMPOWER USERS TO BE THE MASTERS OF THEIR OWN DOMAIN VIII
- 47. Implementation
- 48. This is not the business of hoarding data; we only collect data that serves the utility of the product and service. Therefore, identifying what those data points are must be conscientious and deliberate. WE ARE DELIBERATE ABOUT WHAT DATA WE COLLECT VI
- 50. DISCUSS What happened? How did the manifesto help / obstruct / influence your group? We would like to know how you plan on using or implementing what you’ve learned? What point in your development / design process would you go back to the points in the manifesto?
- 51. WE SPIED WITH OUR LITTLE EYES… TBD during the workshop
- 52. THANKS - YOU’RE ALL AWESOME!