Remote VPN
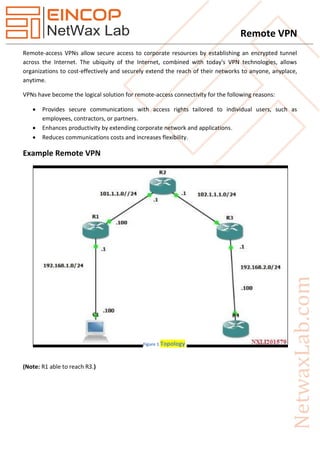
- 1. Remote VPN Remote-access VPNs allow secure access to corporate resources by establishing an encrypted tunnel across the Internet. The ubiquity of the Internet, combined with today's VPN technologies, allows organizations to cost-effectively and securely extend the reach of their networks to anyone, anyplace, anytime. VPNs have become the logical solution for remote-access connectivity for the following reasons: Provides secure communications with access rights tailored to individual users, such as employees, contractors, or partners. Enhances productivity by extending corporate network and applications. Reduces communications costs and increases flexibility. Example Remote VPN (Note: R1 able to reach R3.) Figure 1 Topology
- 2. Remote VPN R3 (Server) crypto isakmp policy 1 authentication pre-share encryption 3des group 2 hash sha lifetime 1800 exit crypto ipsec transform-set tset esp-sha-hmac esp-3des exit ip local pool pool1 192.168.100.1 192.168.100.254 crypto isakmp client configuration group Test key cisco domain cisco.com save-password pool pool1 exit crypto dynamic-map DMAP 10 set transform-set tset reverse-route exit crypto map CMAP 10 ipsec-isakmp dynamic DMAP crypto map CMAP isakmp authorization list default crypto map CMAP client authentication list defualt aaa new-model aaa authentication login default local aaa authorization network default local username cisco password cisco int f0/0 crypto map CMAP exit
- 3. Remote VPN R1 (Client) crypto ipsec client ezvpn EZvpn mode client connect auto peer 102.1.1.100 group Test key cisco username cisco password cisco int f0/0 crypto ipsec client ezvpn Ezvpn outside exit int f0/1 crypto ipsec client ezvpn Ezvpn inside exit