Security enhancements for popular GCP services
- 1. Security enhancements Oct 12, 2022 Bangalore for popular GCP services
- 2. Runcy Oommen Director, Software Engineering SonicWall
- 3. 01 Generic cloud security intro 02 Shared responsibility model Contents 03 Hardening of GCP services
- 4. Cloud Security refers to a broad set of policies, technologies, applications and controls utilized to protect virtualized IP, data, applications, services and infrastructure of cloud computing Let's define "cloud security" Reference: https://en.wikipedia.org/wiki/Cloud_computing_security
- 5. IT infrastructure & landscape has undergone a paradigm shift…
- 8. Shouldn't cloud security differ from traditional network security?
- 9. Important facets of cloud Ubiquitous The cloud is always reachable from anywhere, any time, any device Scalable You can add features and thousands of users without breaking a sweat Integrated Security and other services talk to each other for full visibility
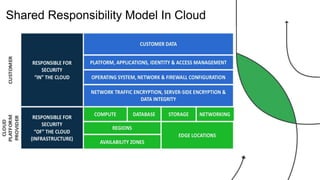
- 10. Shared Responsibility Model In Cloud
- 11. © 2019, Amazon Web Services, Inc. or its Affiliates. All rights reserved.
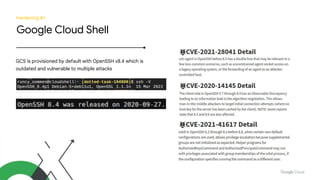
- 12. Hardening #1 Google Cloud Shell GCS is provisioned by default with OpenSSH v8.4 which is outdated and vulnerable to multiple attacks
- 13. What's the solution? Upgrade to OpenSSH v9.1 or later!
- 15. © 2019, Amazon Web Services, Inc. or its Affiliates. All rights reserved. SITUATION RIGHT NOW!
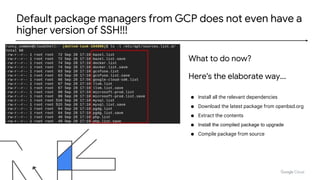
- 16. Default package managers from GCP does not even have a higher version of SSH!!! ● Install all the relevant dependencies ● Download the latest package from openbsd.org ● Extract the contents ● Install the compiled package to upgrade ● Compile package from source What to do now? Here's the elaborate way...
- 17. Get the scripts - https://tinyurl.com/cloudshellupdate
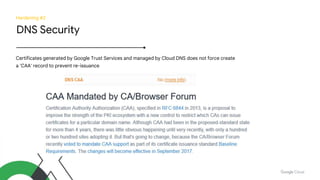
- 19. Hardening #2 DNS Security Certificates generated by Google Trust Services and managed by Cloud DNS does not force create a 'CAA' record to prevent re-issuance
- 20. What's the solution? Create an entry in Cloud DNS for CAA record Run a scan (Qualys online SSL should be sufficient)
- 21. YAYYY!!!
- 22. Hardening #3 Google App Engine Support for TLS 1.0/1.1 and TLS 1.2 with weak cipher suites by default to ensure backward compatibility with older clients
- 23. What's the solution? 1. Create a custom policy that supports just TLS 1.2 and strong cipher suites 2. Now, attach these withe cloud LB that will serve the traffic for the App Engine
- 25. Hardening #4 Google Cloud Functions Incorrect or non-existent input validations, might lead to elevated privileges in FaaS configuration ● Sub-process invocation at will from the execution context ● Access function handler of serverless function ● Execution of system commands at will ● Access to /tmp to manipulate contents during exec time ● Full internet access from within the FaaS environment
- 27. Exploit example Functionality Cv filtering app that accepts PDF file to perform text analysis Assumption Users will provide legitimate PDF filenames for processing Weakness Filename embedded into shell for direct shell command invocations
- 28. Sub-process invocation at will from the execution context Access to /tmp to manipulate contents during exec time
- 29. Let's do some "monkey patching" Why it's needed? Extend the behavior of modules, classes or methods without actual modification of source code What is it? Technique to dynamically update the behavior of a piece of code When to use? • Extend or modify behavior at runtime of librarires/methods • During testing of mock behavior of librarie, modules, objects • Quickly fix issues, if we don't have resources to roll proper fix
- 30. ● Eclipsed the original definition of os.system() with a custom one ● Create a new safe_system which is known only by us ● Repeat this for other definitions that are not required to be supported for your FaaS