SierraVMI Virtual Mobile Infrastructure (VMI). Android-based VDI.
- 1. Virtual Mobile Infrastructure Protect Your Mobile Apps
- 2. BYOD Access Is a Reality 95% of organizations allow employee-owned devices “in some way shape or form”1 44% of job seekers prefer employers that support BYOD policies2 $950 - $3,150 per U.S. employee per year can be saved by implementing a BYOD program through increased productivity3 1 Cisco IBSG Horizons Study 2 http://www.informationweek.com/mobile/6-risks-your-byod-policy-must-address/d/d-id/1107451?page_number=1 3 Dell Global BYOD Survey 2013 4 Ovum Multi-Market BYOD Survey 2013
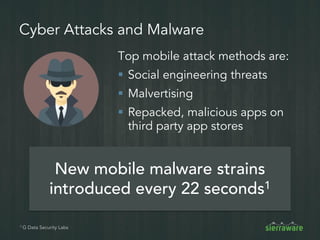
- 3. Mobile Devices Introduce Risk Insider Abuse Accidental Data Exposure Cyber Attack Physical Theft
- 4. VDI Isn’t the Solution for BYOD Expensive VDI Shortcomings – Not designed for touch – No multimedia redirection – No access to camera, printer, video, GPS Total cost for Microsoft VDI, Citrix, and hardware is $1,000+ per user1 Not designed for cellular edge, 3G networks 1 Microsoft Desktop OS $187 per user, Citrix $300/user Requires High Bandwidth Designed for Windows
- 5. Risks of Uncontrolled Devices Weak Encryption No support for strong authentication Unpatched application Stores PHI on phone No auditing of user access Unpatched phone OS In violation of HIPAA compliance requirements
- 6. Virtual Mobile Infrastructure There is a solution…
- 7. Virtual Mobile Infrastructure (VMI) VMI is a service that hosts mobile apps or full operating systems on remote servers Provide remote access to: Android, Apple iOS and Windows Phone with client apps Any HTML 5-enabled device Centralize app management to: Eliminate need to install and upgrade apps on every device
- 8. SierraVMI Deployment SierraVMI hosting Android applications Authentication Server Laptop Tablet Phone
- 9. SierraVMI Keeps Business Data Safe SierraVMI Shields Mobile Data 4096-bit ECDHE Encryption Dual factor authentication SierraVMI: • Records mobile app access • Stores app data securely in the data center • IT can centrally upgrade mobile apps End user
- 10. Architecture #1: Mobile App Virtualization VMI Security Gateway Clients Authentication Server Benefits Very high density Apps can share resources like GPU Easy to manage No need for expensive storage Considerations Cannot define hardware resources per session 64-bit Android Multi User Extensions User 1 User 3 User 2 HW Offload Engines
- 11. Authentication Server Architecture #2: Android LXC Container VMI Security Gateway Clients Benefits Each user can install their own apps Android equivalent to desktop virtualization Considerations Low density LXC Android Work Space1 Android Work Space n
- 12. Access Control Audit Control SierraVMI and the 5 Pillars of Mobile Security How SierraVMI addresses mobile security requirements for compliance Transmission Security Integrity Person or Entity Authentication Enforce consistent multi-factor authentication for all apps Granularly control access; back up files on server to prevent accidental deletion Centrally manage access controls for all apps; assign policies based on LDAP/AD groups Audit mobile activity with detailed logs and session recordings Use 4096-bit encryption and client cert authentication for all mobile apps
- 13. Monitor User and Application Activity Dashboard of system status Detailed logs of user activity Geo-tracking
- 14. User Monitoring Record user sessions for forensics Allow admins to view up to 8 live sessions
- 15. Prevent Data Loss Watermarking deters users from photographing screens – Watermark all content including documents, video, pictures with no additional overhead Anti-screen capture prevents users from taking screenshots With VMI, no data is downloaded to the phone – Users cannot copy and paste text
- 16. Securely Store and Distribute Content Share sensitive videos using multi-media redirection – Ensure users do not capture or download files – Watermark images & videos Store files on data center servers, not users’ devices
- 17. Strong Authentication Prevent unauthorized access with: – Client certificates – One-time password (sent via text message) – Restricting access based on geographic location – Brute force login protection Ensure only legitimate users access your data
- 18. Single Sign-on to Ease Management Integrate with LDAP, Active Directory or SAML Access email, calendar, contacts, and business apps without needing to re- authenticate Automate app provisioning Reduce IT helpdesk calls due to forgotten passwords Improve user experience by eliminating extra login steps IT Cost ReductionDirectory Services Integration
- 19. Centralized data storage Prevent data loss from device theft Centralized patch management Eliminate concerns of devices with vulnerable or unpatched software Regularly scan Android server for viruses and vulnerabilities Simplify and Secure Mobile App Management
- 20. Before VMI With VMI Companies rely on heavy-handed MDM features like remote wipe to prevent data loss Each app has different encryption and authentication capabilities Limited ability to monitor mobile user access to business apps Remote VPN access to network resources difficult to restrict or audit Companies must develop mobile apps for iOS, Android, Windows Phone, Blackberry Data is never downloaded to mobile devices All apps support multi-factor auth, strong encryption & SSO Optional logging and video recording of privileged users Granular control and monitoring of remote access from mobile apps Companies can develop an app for Android and support all devices
- 21. Mobile Business Applications Healthcare Finance Utilities Travel Retail Wireless Doctors can view and update patient data from a tablet Financial advisors can provide clients investment info Technicians can access outage data and maps Sales assistants can ring up sales on the store floor Flight attendants can view flight status and rebook passengers Service providers offering value added hosting service.
- 22. Mobile Security Checklist 4096 Bit SSL Prevent data breaches and leaks Privacy and data loss Address regulations such as SOX and FINRA Secure remote access Address NIST SP 800-53 and ISO/IEC 27002