Structured NERC CIP Process Improvement Using Six Sigma
- 2. MISO Overview 2 MISO Reliability Coordination Area, June 2013 • Independent • Non-profit • 2001 – Reliability Coordinator • 2005 – Energy Markets • 2009 – Ancillary Services • 2012 – Independent Coordinator of Transmission for Entergy Region • Large Footprint – Midwest and Southern Regions
- 3. Current Scope of Operations as of June 1, 2013 • Generation Capacity – 131,522 MW (market - Midwest) – 205,759 MW (reliability – Midwest + Southern regions) • Historic Peak Load (Midwest Region) (July 23, 2012) – 98,576 MW (market) – 133,368 MW (reliability) • 65,250 miles of transmission (Midwest Region) – 15,752 Southern Region – 49,528 Midwest Region • Midwest Region: 11 states, 1 Canadian province • Southern Region: 4 states (AR, LA, MS, TX) (reliability only until Southern Region market integration in December 2013) 3
- 4. Speaker • Chris Unton – Currently: Sr. Manager, IT Compliance – Past roles include: • Identity & Access Management • Disaster Recovery & Problem Management • Enterprise Systems Management / Network Operations Center • Data Networking – Education • BS Computer Science – Rose-Hulman Institute of Technology • MBA – Indiana University Kelley School of Business 4
- 5. Disclaimer • Any views and opinions represented are those of Chris Unton and do not necessarily reflect those of MISO • Many of the activities described are in-flight rather than complete. Your mileage may vary. 5
- 6. Agenda • Process Driven Approach to Compliance • Ownership • Six Sigma • Program Structure • Process Improvement Tools • Governance and Execution 6
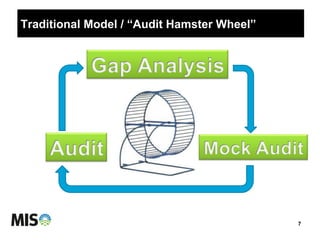
- 7. Traditional Model / “Audit Hamster Wheel” 7
- 8. Process Driven Approach • Traditional Model does not drive behavior towards: – Real-time compliance – Security driven compliance – Harmonization of approach across regulatory needs (NERC, FERC, SSAE 16, SOx) • Process Based approach drives behavior towards: – Baking in compliance evidence as a natural part of the process – Ownership of the necessary activities – Documentation of control objectives & activities – Metrics to assess performance 8
- 9. Ownership Detail (Visual) 9 Requirement Owner Process Owner Activity (Control) Owner Executive Oversight • 65 processes which support CIP compliance • Majority (34 of 65) of the processes have more than three teams (or more than one division) involved in the core execution of the process • Clearly defined roles & responsibilities of ownership are critical to success – Process ownership in particular
- 10. 10 CIP ROLES (Arrows denote evidence flow) IT Compliance • Accountable for oversight to MISO’s compliance with CIP requirements. • Supports the Requirement Owner by assisting with MISO’s interpretation of the CIP requirements. • Validates that the processes under the Requirement Owner do meet compliance with the standard. • Communicates changes/updates/ guidance to standards and requirements to the Requirement Owners. • Validates sufficiency of supporting evidence to demonstrate compliance. • Drives MISO’s CIP Compliance Program Requirement Owner • Accountable for assuring MISO’s compliance with that particular requirement. • Interprets what the requirement truly means to MISO and devises MISO’s response to support compliance with that requirement (with assistance of support teams). • Identifies the processes needed to support compliance and gathers the appropriate people (process owners) together to ensure an end-to-end solution with no gaps. The requirement owner likely is also a process owner or manages process owners. • Looks forward to ensure MISO adapts to changing regulations appropriately, while also designing solutions that support the objective of the regulation. • Gathers evidence from process owners for self- assessments and audits, to make sure the evidence is in line with the expectations of the requirement. • Drives the creation of RSAW narrative that describes MISO’s compliance approach. • First person to be interviewed by auditors who are evaluating MISO’s compliance with that requirement. • If compliance issues arise, the requirement owner is accountable (coordinating with Compliance Services and other support staff) for the content of self-reports and mitigation plans to restore compliance with that requirement. Process Owner • Functional responsibility for the operation of a process that supports one or more compliance requirements. • Designs solid, robust processes that support operational excellence and security/compliance needs. Recognizes inputs (upstream impacts) and outputs (downstream impacts) of the process. • Responds to self-assessments and provides evidence (upon request) to the requirement owner demonstrating effective process operation. • Identifies key activities (controls) within the process and assigns personnel to execute those control activities. • Subject matter expert in his/her area of responsibility. This person uses multiple sources (compliance support staff, internal peers, industry counterparts, conferences, and training) to continually improve the process he/she owns. Activity / Control Owner • Responsible for a particular component of an overall process. • Executes an activity according to procedure. • Understands how activity execution fits into the larger process. • Generates evidence as part of the activity execution, or assures that automated activities produce the expected output. • Provides the evidence to downstream activities. During self- assessments or audit preparation, the control owner provides evidence to the process owner if it cannot be directly queried by the process owner.
- 11. Six Sigma 11 • Six Sigma is a fact–based, data–driven philosophy of quality improvement that values defect prevention over defect detection. It drives customer satisfaction and bottom-line results by reducing variation and waste, thereby promoting a competitive advantage. It applies anywhere variation and waste exist, and every employee should be involved. • In simple terms, Six Sigma quality performance means no more than 3.4 defects per million opportunities. • Methodology that takes an objective view of current performance and structured approach to measurably improve performance
- 12. DMAIC 12
- 13. Program Structure • Techniques (Comprehensive Review) 1. Identify/validate current requirement owners 2. Map requirements to processes 3. Identify/validate process owners 4. Identify areas that need improvement (health check) • Attributes: ownership, documentation, monitoring, complexity, automation • Mechanisms: survey, past performance, expert assessment 5. Analysis and Improvement • Kaizen events: Process (re)design, RACI, Policy and Procedures, Evidence, Automation / Tool Integration opportunities 6. Control – structure for on-going self-assessment and measurement • Training 1. End-to-end requirement & process awareness 2. Effective self-assessment (control design & execution) 3. Process improvement • Technology Integration 1. Utilize available tools 2. Schedule process improvement activities to coincide with tool deployment where appropriate • Team 1. Concerted effort from a diverse skillset (projecting ~6000 hours of internal effort over 16 months) 2. Some consistent program support personnel, some subject matter experts as needed 13
- 14. Process Improvement Tools • Kaizen Events • Process Mapping • SIPOC • Data Analysis • Piloting • Workflow • Automation 14
- 15. Kaizen Events • Short duration (weeks), high intensity mini-project • Focuses on the Analyze & Improve phases of the DMAIC cycle • Produces evidence that can be used for the Control phase going forward – Business Process Diagrams, procedures, RACI matrix 15 • Cross-functional team makes improvements in a methodological way – Led by process owner – Supported by a Six Sigma black belt
- 16. Process Mapping • Visualize current & future processes • Gain common understanding • Identify pain points • Speeds training/ adoption 16
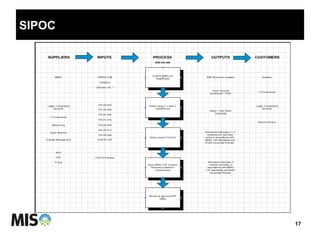
- 17. SIPOC 17
- 18. Data Analysis • Asset based – How many CIP cyber assets do we have? – How many backup types? – How many baseline configurations? • Process based – How many server commissions do we execute each year? – How many firewall rule updates? – How many significant changes? • Reduce Complexity • Align effort with volume
- 19. Piloting • Take the new process through a trial run on real data during the Kaizen event • Demonstrates operational as well as compliance benefits • Provides a chance to change or tweak a process • Offers insight into the time and training required for a full roll-out
- 20. Workflow • Many of the CIP processes require a sequence of steps to be executed (including multiple teams) – Ex: Security Controls Testing 1) Determine if the change is significant 2) Test the security impact of the change 3) Link the production work to the pre-production testing • Remedy ticketing system has been our workflow engine of choice • Other options exist – Sharepoint – Lombardi Teamworks – Calendar reminders
- 21. Automation • Philosophy: process first, automation second • Sometimes, automation is essential to achieve a robust, efficient process • Process areas we’ve explored or are planning for automation: – Compliance training at onboarding – Quarterly entitlement reviews – Change monitoring – Cyber Security event log review
- 22. Training / Awareness • Online Learning Management System – Quick, 10-15 minute slide decks with voice over – Wide reach (some 200 person audiences) – Employees familiar with the system already – Repository that future employees can access • Face to face sessions at team meetings – In-depth knowledge transfer – Interactive – Time intensive • “Plugged In” Communications – News items, short story features 22
- 23. Steering Committee Program Governance 23 Executive Sponsors Program Lead Ongoing MISO Governance Committees
- 24. Capability MATURITY Highly MatureImmature TIME Named requirement owners Evidence mapped to requirements Process orientation for compliance Processes mapped Processes comprehensive Manage to metrics Internal self assessments are audit comprehensive Processes optimized for efficiency Proactive adoption of future standards Controls documented Processes deliver Six Sigma quality Workflow automation Interpretations documented Compliance is a by-product of security
- 25. Execution • Ensure process has trackable metrics built in – Quantity – Timeliness – Completeness • Maintain a robust internal assessment process • Don’t forget to update QRSAW narratives – these should be living and breathing as the process changes 25
- 26. Contact Info • Chris Unton – crunton@misoenergy.org 26