Surviving in a Digital World
- 1. Surviving in a Digital World Anupam Saraph, Ph.D.
- 2. Overview ❖ Digital Experience ❖ Your Exposure and Risks ❖ Strategies for Minimising Your Risk
- 4. Exhibit 1
- 5. Exhibit 2
- 6. Exhibit 3
- 7. Exhibit 4
- 8. Exhibit 5
- 9. Exhibit 6
- 10. Exhibit 7
- 11. Exhibit 8
- 12. Exhibit 9
- 13. Exhibit 10
- 14. Exhibit 11
- 15. Exhibit 12 15
- 16. Exhibit 13 16
- 17. Exhibit 14 17
- 18. Exhibit 15
- 19. Exhibit 16
- 20. Exhibit 17
- 21. Your Exposure and Risks
- 24. Trust ❖ Confidentiality: ensuring privacy, restricted access ❖ Integrity: ensuring fidelity, honesty ❖ Authentication: prove as genuine and ❖ Non-repudiation: legally ensure person cannot reject the transaction/information
- 25. Cybercrime ❖ Traditional forms of crime such as fraud or forgery, though committed over electronic communication networks and information systems; ❖ The publication of illegal content over electronic media (e.g., child sexual abuse material or incitement to racial hatred); ❖ Crimes unique to electronic networks, e.g., attacks against information systems, denial of service and hacking. Source: European Commission. Towards a general policy on the fight against cyber crime, May 2007. COM(2007) 267 final, http://eur-lex.europa.eu/LexUriServ/LexUriServ.do? uri=COM:2007:0267:FIN:EN:PDF
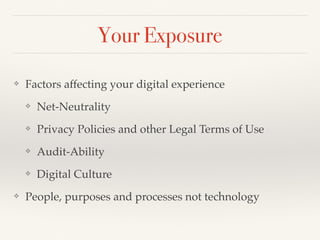
- 26. Your Exposure ❖ Factors affecting your digital experience ❖ Net-Neutrality ❖ Privacy Policies and other Legal Terms of Use ❖ Audit-Ability ❖ Digital Culture ❖ People, purposes and processes not technology
- 27. Net-Neutrality ❖ Access is fair, just, unrestricted and non-monopolised ❖ Access agnostic to the media and content consumed by its customers across the network
- 28. Privacy Policy ❖ Right to Opt-Out: your ability to prevent the sharing of your data with third parties ❖ Data Retention: your right to be forgotten ❖ Safeguards: policies to prevent unauthorized access
- 29. Audit-Ability ❖ Ability to trace back a transaction to persons ❖ Ability to ensure transacting parties cannot deny transaction
- 30. Digital Culture ❖ Etiquette in transactions ❖ Hygiene during transactions ❖ Privacy and Safety
- 31. Your Risks ❖ Access Failure, Corruption, Theft Resulting from ❖ Obsolescence ❖ Loss of Rights ❖ Loss of Identity ❖ Loss of Assets
- 32. Strategies for Minimising Your Risk
- 33. Protection from Obsolescence ❖ Use Open-Source formats to store digital assets ❖ Upgrade backups to current media ❖ Avoid digital platforms that evolve fast ❖ Avoid using technology for the sake of technology
- 34. Protection from Unfair Practices ❖ Choose Opt-Out wherever possible ❖ Avoid digital platforms that lack Privacy ❖ Avoid digital platforms with unfair Terms of Use ❖ File complaint for deficiency of service and unfair trade practice or under the 2(g) & 2(r) of the Consumer Protection Act, 1986 see http://ncdrc.nic.in ❖ Telecom regulations available here http:// www.trai.gov.in/content/VerReg/112_0_3.aspx
- 35. Protecting your Identity ❖ Opt-Out wherever a Single ID wants to run your life ❖ Avoid digital platforms that lack Privacy ❖ Avoid digital platforms that have no human help ❖ Use 2 step-Authentication
- 36. Protecting your Digital Assets ❖ Create an inventory of your digital assets ❖ Do a periodic audit of your digital exposure ❖ Avoid digital platforms that evolve fast
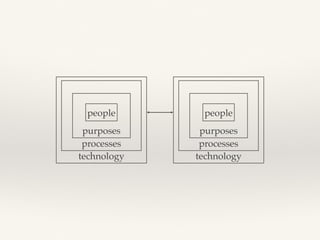
- 37. Your Purposes ❖ Interacting with people ❖ Collaborating on shared purposes ❖ Following agreed process to accomplish shared purposes ❖ Not digitising life, events or transactions
- 38. Questions?