How to assign unowned disk in the netapp cluster 8.3
•Download as DOCX, PDF•
1 like•1,268 views
Here it has been described how to assign the disk which is unowned to the node in the netapp cluster mode 8.3 and how to enable the disk assign option shelf level and stack level
Report
Share
Report
Share
More Related Content
Similar to How to assign unowned disk in the netapp cluster 8.3
1Z0-053 Exam-Oracle Database 11g: Administration II 

Pass your 1Z0-053 Exam-Oracle Database 11g: Administration II visit@ https://www.troytec.com/1Z0-053-exams.html
General commands for navisphere cli

The document provides examples of commands for using the Navisphere CLI to manage various aspects of an EMC storage system, such as:
1. Listing front-end port speeds, rebooting the SP, getting disk and RAID group information, setting cache parameters, creating RAID groups, binding and modifying LUNs.
2. Creating storage groups, adding LUNs to storage groups and connecting hosts to storage groups.
3. Summarizing how to calculate the stripe size of a LUN based on the RAID type and number of disks in the RAID group.
Exam 1Z0-053 Oracle Database 11g: Administration II

Are you searching for easy and 100% original dumps and study material for Oracle Database 11g: Administration II? Visit@https://www.certmagic.com/1Z0-053-certification-practice-exams.html
#IT #Trainingmaterial #learningmaterial #oracle #oracledatabase #database11g #administration11 #oracleadministration #exam #dumps #discount
Storage memory

Disk memory provides large, non-volatile storage. It uses rotating platters coated with magnetic surfaces and read/write heads. Disk access time has four components - seek time to position the head, rotational latency to wait for the desired sector, transfer time to read/write data, and controller overhead time. RAID (redundant array of independent disks) uses multiple disks for performance, reliability, and availability. Popular RAID levels include RAID 1 which uses mirroring for redundancy, and RAID 5 which uses distributed parity blocks.
Faq on SnapDrive for UNIX NetApp

SnapDrive allows creation of different storage entities like LUNs, filesystems, host volumes, and disk groups. The document provides step-by-step instructions to create a LUN entity using SnapDrive. This involves first creating a LUN on the NetApp filer and then using local volume management tools like LVM to manage the LUN. Commands to create a LUN on the NetApp storage system darfas01 and volume centos_iscsi are shown.
Veritas Software Foundations

Volume manager software provides logical volume management and virtualization of storage disks. It optimizes storage usage, increases filesystem limits, and provides flexibility, capacity, speed and resilience through features like mirroring and striping. Virtualization is performed by either the storage device itself or a software layer on the host system. Hot spares and snapshotting provide fault tolerance and online backups.
disk structure and multiple RAID levels .ppt

RAID (Redundant Array of Independent Disks) is a technology that combines multiple disk drive components into a logical unit to improve performance and/or provide redundancy. It distributes data across multiple disks to increase performance and improve reliability. Different RAID levels offer varying degrees of performance and fault tolerance based on how data and redundant information are striped and mirrored across disks. Common RAID levels include RAID 0, 1, 5 and 6.
Give or take a block

This document provides an overview of block and inode allocation in IBM Spectrum Scale. It begins with relevant basics about Spectrum Scale including the cluster architecture, node roles, and the layers from disk to namespace. It then covers the two main allocation types: map-based allocation which is used for storage pools and filesets due to their static nature, and share-based allocation which is used for quotas given their more dynamic nature and administrator-initiated changes. Map-based allocation divides resources into regions that nodes can independently manage, while share-based allocation uses a quota sharing approach.
Vx vm

This document discusses layered volumes in VxVM. Layered volumes tolerate failure better and have greater redundancy than standard volumes. For example, a mirrored-striped layered volume has quicker recovery than a standard mirrored volume since each mirror covers less storage space. The document also discusses different types of layered volumes like mirror-striped and stripe-mirrored, how they provide redundancy and performance advantages over standard volumes, and some of their limitations.
Create Diskgroup Sqlplus Command

we will be creating new ASM diskgroup using SQLPLUS command while connected to ASM instance.
You must have an unused partition / disk on the server that can be used to create ASM diskgroup.
Full article link is here: https://www.support.dbagenesis.com/post/create-diskgroup-sqlplus-command
VMworld 2017 - Top 10 things to know about vSAN

In this session Cormac Hogan and I go over the top 10 things to know about vSAN. This is based on two years of questions/answers from our field and customers. Useful for any VMware vSAN customer!
#STO1264BU #STO1264BE
Disk reports predicted failure event

A predictive failure alert was reported for disk 1c.xx.xx in NetApp cluster node Cluster-02. The disk reported a predicted failure event. If a matching spare disk is available, rapid RAID recovery will begin by copying the data from the pre-failed disk to the spare. If no spares are available, the disk will eventually fail and cause the RAID group to degrade until a spare is available to reconstruct the data. Proactive assignment of a partner node's spare disk is recommended.
Disk Management.pdf

This document provides an overview of disk management. It begins by explaining the difference between discs and disks, with discs referring to optical media like CDs and DVDs that are removable, while disks refer to magnetic hard drives and drives that are not removable. It then covers disk terminology like cylinders, tracks, and sectors. Next, it describes disk structure including platters, tracks, read/write heads, and cylinders. The document discusses disk scheduling algorithms like first-come first-served, shortest seek time first, and scan. Finally, it lists some common disk management operations and tools.
Disk Management

Disk Management is a system utility for managing hard disks and the volumes, or partitions, that they contain.
Disk Management enables you to perform most disk-related tasks without shutting down the system or interrupting users; most configuration changes take effect immediately.
Simplified tasks and intuitive user interface. Disk Management is easy to use. Menus that are accessible from the right mouse button display the tasks you can perform on the selected object, and wizards guide you through creating partitions or volumes and initializing or converting disks.
Hazelcast sunum

Hazelcast is an open source in-memory data grid based on Java. It provides distributed map, set, queue, topic, and lock data structures that allow for data to be stored in memory and partitioned across a cluster of nodes. Clients can interact with the data structures without needing to know the details of the cluster setup. Hazelcast is used by many companies for caching, computing, and messaging workloads. It has both open source and paid enterprise editions that provide additional features like WAN replication and security.
RAC.docx

The document provides instructions for stopping and starting various Oracle components in a RAC environment using srvctl commands. It also describes useful ASM commands for creating, dropping, mounting and checking disk groups as well as administering ASM from the operating system level using asmcmd.
Wido den Hollander - 10 ways to break your Ceph cluster

Wido den Hollander - 10 ways to break your Ceph cluster. Presentation from CloudStack / Ceph day, Thursday, April 19, London
Mirroring the root_disk under solaris SVM

This document outlines steps to mirror the boot disk and partitions across two disks for redundancy. It involves:
1. Creating metadatabases and metamirrors for the root disk (/), swap, and partitions across the two disks.
2. Configuring /etc/vfstab to reference the new metadevices instead of physical disks.
3. Editing /etc/system to set mirrored_root_flag=1 to allow booting from the mirror if 50% of databases are available.
4. Rebooting and attaching the remaining submirrors, then verifying sync progress and boot device configuration.
Raid : Redundant Array of Inexpensive Disks

RAID (Redundant Array of Inexpensive Disks) systems allow for combining multiple physical disks into a single logical disk for the purposes of data redundancy, performance, and reliability. There are several RAID levels that offer different tradeoffs between these factors. RAID level 5 stripes both data and parity information across all disks, allowing writes to occur in parallel for improved performance compared to RAID level 4 which dedicates one disk solely to parity data. RAID level 1 mirrors all data onto a second disk for full data redundancy but at double the storage cost.
Nycbsdcon14

This document discusses ZFS management tools available in FreeNAS and PC-BSD operating systems. It provides an overview of ZFS features like pools, RAIDZ levels, datasets, snapshots, and properties. It describes how to perform tasks like creating pools and datasets, adding disks, enabling SLOG and L2ARC caches, taking and restoring snapshots, scheduling scrubs, and managing boot environments in both FreeNAS and PC-BSD. The document aims to help users understand and utilize the key ZFS functionality provided by these FreeBSD-based operating systems.
Similar to How to assign unowned disk in the netapp cluster 8.3 (20)
1Z0-053 Exam-Oracle Database 11g: Administration II 

1Z0-053 Exam-Oracle Database 11g: Administration II
Exam 1Z0-053 Oracle Database 11g: Administration II

Exam 1Z0-053 Oracle Database 11g: Administration II
Wido den Hollander - 10 ways to break your Ceph cluster

Wido den Hollander - 10 ways to break your Ceph cluster
More from Saroj Sahu
How to shutdown the Netapp SAN 8.3 and 9.2 version

Here it has been described the step by step process "how to shutdown or power down of the Netapp Cluster mode system version 8.3 onwards
How to Shutdown Netapp Cluster Mode Storage System with Multi-Node Cluster (6...

Here we have explain step by step how to shutdown the Netapp storage System with Multi-Node Cluster (6 nodes cluster with ontap version 9.1P14 with model FAS8200, AFF8040 & AFF8020)
How to assign the disks in Netapp storage cluster mode 8.X

Here we have described how to assign the disks which are in unassigned state in netapp cluster mode storage system and explained in which scenario we have to assign the disks.
Use of administrative privilege levels in netapp cluster 8.x

Here it has been described how to user the administrative privileges in command mode in Netapp cluster mode 8.x
How to access the Netapp cluster mode 8.2 through CLI (command mode)

This document provides 3 methods for accessing a NetApp cluster mode storage system through the command line interface (CLI).
Method 1 involves connecting a laptop directly to the storage system's serial port using PuTTY software and logging in with username "admin". Method 2 allows using telnet or RSH by first cloning the firewall policy and enabling those services, but they are insecure. Method 3, which is recommended, uses SSH to securely access the storage system by hostname or IP and log in as "admin". The document provides instructions for downloading PuTTY and checking which CLI services are enabled or disabled.
Unable to access the net app cluster mode 9.2 san through gui after power mai...

Unable to access the NetApp storage system 9.2 cluster mode due to cluster management LIF down and http service was disable. Here we have mentioned the real time issue which we have faced and solution has been given step by stem by using the command mode. Hope it can be useful for NetApp Administrators
Volume migration from one aggregate to other without impacting the applicatio...

How to migrate a volume from one aggregate to another in the cluster mode Netapp storage system with version 9.2 without any impact to the production
Uable to do ssh from the RedHat Linux machine to Netapp filer 7 mode storage ...

Unable to access Netapp Filer by ssh from the RedHat Linux machine throwing the error message as "Unable to negotiate with 10.150.10.10 port 22: no matching cipher found. Their offer: 3des-cbc
How to work seamlessly in your vm without pressing host key again and again

How to work seamlessly in your oracle VM which is installed with Cent OS or RedHat Linux? You can copy and past from your local machine to the VM without any difficulties. (HOST KEY is not required) (Guest editions CD image installation in Oracle VM (Cent OS, RedHat Linux
How to enable efficiency (deduplication and compression in netapp cluster mod...

This step by step implementation of deduplication and compression will make you easy to implement in your environment on the volume of Netapp storage. we will get lot of space savings which will benefit for customer and business can grow beyond our limitation.
How to see the event and audit logs through ( gui and cli) in cluster ontap n...

With the help of this document, we can check the logs in NetApp storage. It will very helpful for troubleshooting of the issues. we can easily take the decision to act on the current issue by analysing the logs.
How to see the log files through ( gui and cli) in cluster ontap netapp stora...

How to see the logs in cluster data on tap storage system through the graphical user interface and the command line interface.
Snapshot technology Netapp storage

NetApp snapshot technology works by preserving the inode map at the time a snapshot is created and continuing to change the inode map on the active file system, while keeping the older version for the snapshot. Snapshots can be created quickly in just a few seconds without impacting performance and up to 255 snapshots can be created per volume, providing point-in-time copies of data.
SAN High availability (Netapp Storage) 

High availability ensures that network services and data are accessible at all times by configuring storage systems in high availability pairs. When a network interface fails, negotiated failover can trigger an automatic failover of the storage system to prevent loss of connectivity. Enabling negotiated failover and selecting which network interfaces to include allows the storage system to fail over to the other node. The benefits of high availability include uninterrupted data access, and the ability to perform nondisruptive upgrades to storage system components like motherboards, adapters, disks and interfaces.
3PAR: HOW TO CHANGE THE IP ADDRESS OF HP 3PAR SAN

The document provides steps to change the IP address of a HP 3PAR SAN. It outlines logging into the SAN through Putty using default credentials. It then details using the 'setnet' command to change the IP address, netmask, and gateway. The 'shownet' command confirms the new network settings. Login to the SP console allows changing additional settings like the hostname through interactive menus.
Aggregate standard for Netapp storage 7 mode 

1. Storage teams create aggregates using naming conventions like aggr0, aggr1 to provision storage. They decide the configuration including the RAID type, number of disks, and disk size.
2. When creating an aggregate, factors like recovery speed, data assurance, and storage space must be considered. Larger RAID groups improve performance but increase risk of data loss if multiple disks fail, while smaller groups reduce this risk but decrease performance.
3. Guidelines for RAID group sizing depend on disk type, with ATA/SATA generally having smaller groups than FC/SAS. The default sizes balance speed, protection, and space utilization, though the maximum sizes allow flexibility based on needs.
San1 cifs nfs_snapshot

CIFS, also known as SMB, is a protocol that allows file sharing across different operating systems on a network. It runs over TCP/IP and uses SMB to enable file and printer sharing between Windows clients. To set up CIFS sharing on a NetApp storage system, you configure CIFS and SMB, create a CIFS share, and map the share as a network drive on Windows clients.
SAN BASICS..Why we will go for SAN?

Direct attached storage (DAS) involves connecting storage devices like hard disk drives directly to a server without a storage network. This provides exclusive access to the disks for the server but has limitations in scalability and availability. Storage area networks (SANs) address these issues by connecting multiple servers and storage devices via a high-speed dedicated network using fiber channel technology. This allows for centralized management of storage that can be dynamically allocated and accessed simultaneously by multiple servers.
How to shutdown and power up of the netapp cluster mode storage system

This slide will guide you how to shutdown and power up of the Netapp cluster mode storage system in command mode. (It will depict you environmental shutdown process (SAN environment in a DataCenter)
Netapp Deduplication concepts

NetApp deduplication provides block-level deduplication within flexible volumes to reduce storage capacity needs. It works at the 4KB block level on active file systems and can be configured to run automatically or manually. Deduplication uses fingerprints that are unique digital signatures for blocks. During deduplication, fingerprints are compared and any duplicate blocks are replaced with a pointer to the existing data block to save space. Up to 4% additional space may be needed in a volume and up to 3% in an aggregate for deduplication metadata.
More from Saroj Sahu (20)
How to shutdown the Netapp SAN 8.3 and 9.2 version

How to shutdown the Netapp SAN 8.3 and 9.2 version
How to Shutdown Netapp Cluster Mode Storage System with Multi-Node Cluster (6...

How to Shutdown Netapp Cluster Mode Storage System with Multi-Node Cluster (6...
How to assign the disks in Netapp storage cluster mode 8.X

How to assign the disks in Netapp storage cluster mode 8.X
Use of administrative privilege levels in netapp cluster 8.x

Use of administrative privilege levels in netapp cluster 8.x
How to access the Netapp cluster mode 8.2 through CLI (command mode)

How to access the Netapp cluster mode 8.2 through CLI (command mode)
Unable to access the net app cluster mode 9.2 san through gui after power mai...

Unable to access the net app cluster mode 9.2 san through gui after power mai...
Volume migration from one aggregate to other without impacting the applicatio...

Volume migration from one aggregate to other without impacting the applicatio...
Uable to do ssh from the RedHat Linux machine to Netapp filer 7 mode storage ...

Uable to do ssh from the RedHat Linux machine to Netapp filer 7 mode storage ...
How to work seamlessly in your vm without pressing host key again and again

How to work seamlessly in your vm without pressing host key again and again
How to enable efficiency (deduplication and compression in netapp cluster mod...

How to enable efficiency (deduplication and compression in netapp cluster mod...
How to see the event and audit logs through ( gui and cli) in cluster ontap n...

How to see the event and audit logs through ( gui and cli) in cluster ontap n...
How to see the log files through ( gui and cli) in cluster ontap netapp stora...

How to see the log files through ( gui and cli) in cluster ontap netapp stora...
How to shutdown and power up of the netapp cluster mode storage system

How to shutdown and power up of the netapp cluster mode storage system
Recently uploaded
find out more about the role of autonomous vehicles in facing global challenges

accommodate the strengths, weaknesses, threats and opportunities of autonomous vehicles
20240704 QFM023 Engineering Leadership Reading List June 2024

Everything that I found interesting about engineering leadership last month
BLOCKCHAIN FOR DUMMIES: GUIDEBOOK FOR ALL

Blockchain technology is transforming industries and reshaping the way we conduct business, manage data, and secure transactions. Whether you're new to blockchain or looking to deepen your knowledge, our guidebook, "Blockchain for Dummies", is your ultimate resource.
“Intel’s Approach to Operationalizing AI in the Manufacturing Sector,” a Pres...

“Intel’s Approach to Operationalizing AI in the Manufacturing Sector,” a Pres...Edge AI and Vision Alliance
For the full video of this presentation, please visit: https://www.edge-ai-vision.com/2024/07/intels-approach-to-operationalizing-ai-in-the-manufacturing-sector-a-presentation-from-intel/
Tara Thimmanaik, AI Systems and Solutions Architect at Intel, presents the “Intel’s Approach to Operationalizing AI in the Manufacturing Sector,” tutorial at the May 2024 Embedded Vision Summit.
AI at the edge is powering a revolution in industrial IoT, from real-time processing and analytics that drive greater efficiency and learning to predictive maintenance. Intel is focused on developing tools and assets to help domain experts operationalize AI-based solutions in their fields of expertise.
In this talk, Thimmanaik explains how Intel’s software platforms simplify labor-intensive data upload, labeling, training, model optimization and retraining tasks. She shows how domain experts can quickly build vision models for a wide range of processes—detecting defective parts on a production line, reducing downtime on the factory floor, automating inventory management and other digitization and automation projects. And she introduces Intel-provided edge computing assets that empower faster localized insights and decisions, improving labor productivity through easy-to-use AI tools that democratize AI.Recent Advancements in the NIST-JARVIS Infrastructure

Recent advancements in the NIST-JARVIS infrastructure: JARVIS-Overview, JARVIS-DFT, AtomGPT, ALIGNN, JARVIS-Leaderboard
[Talk] Moving Beyond Spaghetti Infrastructure [AOTB] 2024-07-04.pdf![[Talk] Moving Beyond Spaghetti Infrastructure [AOTB] 2024-07-04.pdf](data:image/gif;base64,R0lGODlhAQABAIAAAAAAAP///yH5BAEAAAAALAAAAAABAAEAAAIBRAA7)
![[Talk] Moving Beyond Spaghetti Infrastructure [AOTB] 2024-07-04.pdf](data:image/gif;base64,R0lGODlhAQABAIAAAAAAAP///yH5BAEAAAAALAAAAAABAAEAAAIBRAA7)
Kief Morris rethinks the infrastructure code delivery lifecycle, advocating for a shift towards composable infrastructure systems. We should shift to designing around deployable components rather than code modules, use more useful levels of abstraction, and drive design and deployment from applications rather than bottom-up, monolithic architecture and delivery.
Performance Budgets for the Real World by Tammy Everts

Performance budgets have been around for more than ten years. Over those years, we’ve learned a lot about what works, what doesn’t, and what we need to improve. In this session, Tammy revisits old assumptions about performance budgets and offers some new best practices. Topics include:
• Understanding performance budgets vs. performance goals
• Aligning budgets with user experience
• Pros and cons of Core Web Vitals
• How to stay on top of your budgets to fight regressions
What's New in Copilot for Microsoft365 May 2024.pptx

This is a slide deck that showcases the updates in Microsoft Copilot for May 2024
UiPath Community Day Kraków: Devs4Devs Conference

We are honored to launch and host this event for our UiPath Polish Community, with the help of our partners - Proservartner!
We certainly hope we have managed to spike your interest in the subjects to be presented and the incredible networking opportunities at hand, too!
Check out our proposed agenda below 👇👇
08:30 ☕ Welcome coffee (30')
09:00 Opening note/ Intro to UiPath Community (10')
Cristina Vidu, Global Manager, Marketing Community @UiPath
Dawid Kot, Digital Transformation Lead @Proservartner
09:10 Cloud migration - Proservartner & DOVISTA case study (30')
Marcin Drozdowski, Automation CoE Manager @DOVISTA
Pawel Kamiński, RPA developer @DOVISTA
Mikolaj Zielinski, UiPath MVP, Senior Solutions Engineer @Proservartner
09:40 From bottlenecks to breakthroughs: Citizen Development in action (25')
Pawel Poplawski, Director, Improvement and Automation @McCormick & Company
Michał Cieślak, Senior Manager, Automation Programs @McCormick & Company
10:05 Next-level bots: API integration in UiPath Studio (30')
Mikolaj Zielinski, UiPath MVP, Senior Solutions Engineer @Proservartner
10:35 ☕ Coffee Break (15')
10:50 Document Understanding with my RPA Companion (45')
Ewa Gruszka, Enterprise Sales Specialist, AI & ML @UiPath
11:35 Power up your Robots: GenAI and GPT in REFramework (45')
Krzysztof Karaszewski, Global RPA Product Manager
12:20 🍕 Lunch Break (1hr)
13:20 From Concept to Quality: UiPath Test Suite for AI-powered Knowledge Bots (30')
Kamil Miśko, UiPath MVP, Senior RPA Developer @Zurich Insurance
13:50 Communications Mining - focus on AI capabilities (30')
Thomasz Wierzbicki, Business Analyst @Office Samurai
14:20 Polish MVP panel: Insights on MVP award achievements and career profiling
AC Atlassian Coimbatore Session Slides( 22/06/2024)

This is the combined Sessions of ACE Atlassian Coimbatore event happened on 22nd June 2024
The session order is as follows:
1.AI and future of help desk by Rajesh Shanmugam
2. Harnessing the power of GenAI for your business by Siddharth
3. Fallacies of GenAI by Raju Kandaswamy
How RPA Help in the Transportation and Logistics Industry.pptx

Revolutionize your transportation processes with our cutting-edge RPA software. Automate repetitive tasks, reduce costs, and enhance efficiency in the logistics sector with our advanced solutions.
Pigging Solutions Sustainability brochure.pdf

Sustainability requires ingenuity and stewardship. Did you know Pigging Solutions pigging systems help you achieve your sustainable manufacturing goals AND provide rapid return on investment.
How? Our systems recover over 99% of product in transfer piping. Recovering trapped product from transfer lines that would otherwise become flush-waste, means you can increase batch yields and eliminate flush waste. From raw materials to finished product, if you can pump it, we can pig it.
The Increasing Use of the National Research Platform by the CSU Campuses

CIO Council
Cal Poly Humboldt
September 22, 2023
@Call @Girls Thiruvananthapuram 🚒 XXXXXXXXXX 🚒 Priya Sharma Beautiful And Cu...

@Call @Girls Thiruvananthapuram 🚒 XXXXXXXXXX 🚒 Priya Sharma Beautiful And Cute Girl any Time
For Ad post Mail : adityaroy0215@gmail.com
How to Avoid Learning the Linux-Kernel Memory Model

The Linux-kernel memory model (LKMM) is a powerful tool for developing highly concurrent Linux-kernel code, but it also has a steep learning curve. Wouldn't it be great to get most of LKMM's benefits without the learning curve?
This talk will describe how to do exactly that by using the standard Linux-kernel APIs (locking, reference counting, RCU) along with a simple rules of thumb, thus gaining most of LKMM's power with less learning. And the full LKMM is always there when you need it!
GDG Cloud Southlake #34: Neatsun Ziv: Automating Appsec

The lecture titled "Automating AppSec" delves into the critical challenges associated with manual application security (AppSec) processes and outlines strategic approaches for incorporating automation to enhance efficiency, accuracy, and scalability. The lecture is structured to highlight the inherent difficulties in traditional AppSec practices, emphasizing the labor-intensive triage of issues, the complexity of identifying responsible owners for security flaws, and the challenges of implementing security checks within CI/CD pipelines. Furthermore, it provides actionable insights on automating these processes to not only mitigate these pains but also to enable a more proactive and scalable security posture within development cycles.
The Pains of Manual AppSec:
This section will explore the time-consuming and error-prone nature of manually triaging security issues, including the difficulty of prioritizing vulnerabilities based on their actual risk to the organization. It will also discuss the challenges in determining ownership for remediation tasks, a process often complicated by cross-functional teams and microservices architectures. Additionally, the inefficiencies of manual checks within CI/CD gates will be examined, highlighting how they can delay deployments and introduce security risks.
Automating CI/CD Gates:
Here, the focus shifts to the automation of security within the CI/CD pipelines. The lecture will cover methods to seamlessly integrate security tools that automatically scan for vulnerabilities as part of the build process, thereby ensuring that security is a core component of the development lifecycle. Strategies for configuring automated gates that can block or flag builds based on the severity of detected issues will be discussed, ensuring that only secure code progresses through the pipeline.
Triaging Issues with Automation:
This segment addresses how automation can be leveraged to intelligently triage and prioritize security issues. It will cover technologies and methodologies for automatically assessing the context and potential impact of vulnerabilities, facilitating quicker and more accurate decision-making. The use of automated alerting and reporting mechanisms to ensure the right stakeholders are informed in a timely manner will also be discussed.
Identifying Ownership Automatically:
Automating the process of identifying who owns the responsibility for fixing specific security issues is critical for efficient remediation. This part of the lecture will explore tools and practices for mapping vulnerabilities to code owners, leveraging version control and project management tools.
Three Tips to Scale the Shift Left Program:
Finally, the lecture will offer three practical tips for organizations looking to scale their Shift Left security programs. These will include recommendations on fostering a security culture within development teams, employing DevSecOps principles to integrate security throughout the development
Recently uploaded (20)
find out more about the role of autonomous vehicles in facing global challenges

find out more about the role of autonomous vehicles in facing global challenges
20240704 QFM023 Engineering Leadership Reading List June 2024

20240704 QFM023 Engineering Leadership Reading List June 2024
“Intel’s Approach to Operationalizing AI in the Manufacturing Sector,” a Pres...

“Intel’s Approach to Operationalizing AI in the Manufacturing Sector,” a Pres...
Recent Advancements in the NIST-JARVIS Infrastructure

Recent Advancements in the NIST-JARVIS Infrastructure
[Talk] Moving Beyond Spaghetti Infrastructure [AOTB] 2024-07-04.pdf![[Talk] Moving Beyond Spaghetti Infrastructure [AOTB] 2024-07-04.pdf](data:image/gif;base64,R0lGODlhAQABAIAAAAAAAP///yH5BAEAAAAALAAAAAABAAEAAAIBRAA7)
![[Talk] Moving Beyond Spaghetti Infrastructure [AOTB] 2024-07-04.pdf](data:image/gif;base64,R0lGODlhAQABAIAAAAAAAP///yH5BAEAAAAALAAAAAABAAEAAAIBRAA7)
[Talk] Moving Beyond Spaghetti Infrastructure [AOTB] 2024-07-04.pdf
Performance Budgets for the Real World by Tammy Everts

Performance Budgets for the Real World by Tammy Everts
WhatsApp Image 2024-03-27 at 08.19.52_bfd93109.pdf

WhatsApp Image 2024-03-27 at 08.19.52_bfd93109.pdf
What's New in Copilot for Microsoft365 May 2024.pptx

What's New in Copilot for Microsoft365 May 2024.pptx
Cookies program to display the information though cookie creation

Cookies program to display the information though cookie creation
AC Atlassian Coimbatore Session Slides( 22/06/2024)

AC Atlassian Coimbatore Session Slides( 22/06/2024)
How RPA Help in the Transportation and Logistics Industry.pptx

How RPA Help in the Transportation and Logistics Industry.pptx
The Increasing Use of the National Research Platform by the CSU Campuses

The Increasing Use of the National Research Platform by the CSU Campuses
@Call @Girls Thiruvananthapuram 🚒 XXXXXXXXXX 🚒 Priya Sharma Beautiful And Cu...

@Call @Girls Thiruvananthapuram 🚒 XXXXXXXXXX 🚒 Priya Sharma Beautiful And Cu...
How to Avoid Learning the Linux-Kernel Memory Model

How to Avoid Learning the Linux-Kernel Memory Model
GDG Cloud Southlake #34: Neatsun Ziv: Automating Appsec

GDG Cloud Southlake #34: Neatsun Ziv: Automating Appsec
How to assign unowned disk in the netapp cluster 8.3
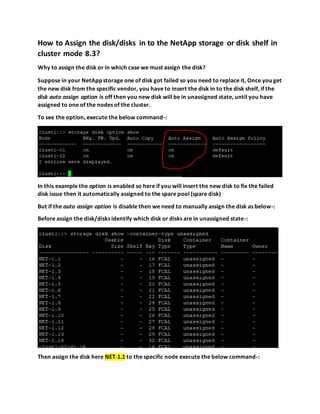
- 1. How to Assign the disk/disks in to the NetApp storage or disk shelf in cluster mode 8.3? Why to assign the disk or in which case we must assign the disk? Suppose in your NetApp storage one of disk got failed so you need to replace it, Once you get the new disk from the specific vendor, you have to insert the disk in to the disk shelf, if the disk auto assign option is off then you new disk will be in unassigned state, until you have assigned to one of the nodes of the cluster. To see the option, execute the below command-: In this example the option is enabled so here if you will insert the new disk to fix the failed disk issue then it automatically assigned to the spare pool (spare disk) But if the auto assign option is disable then we need to manually assign the disk as below-: Before assign the disk/disks identify which disk or disks are in unassigned state-: Then assign the disk here NET-1.1 to the specific node execute the below command-:
- 2. The disk NET-1.1 has been assigned to the node clust1-01 To see the owner of the disk, execute the below command-: The disk is owned by the node clust1-01 If you want to set up automatic ownership assignment at the stack or shelf level. The above command * (star) indicates on all nodes in the cluster. Now, all the nodes are enabled with the auto assign of the disks Configure automatic ownership assignment at the shelf level-: Configure automatic turn off ownership assignment of the disks in the shelf level
- 3. Note-:You have the disk shelf whose disks are owned by one node and another shelf on the same loop who disks are owned by different nodes then in this case you need to configure automatic disk ownership at the shelf level for all the node in the cluster. Thank you!! Saroj Senior Storage Specialist (NCDA and AWS Certified)